Trojan Horse Program Presented by Lori Agrawal Agenda
Trojan Horse Program Presented by : Lori Agrawal
Agenda n n n What is Trojan Horse program? Who are the targets? How it gets spread? Impact of Trojan Horse Attack Control of hackers over files Ways to avoid this attack
Continue: n n n n Detection of attack How to remove Trojan from system Example: Sub. Seven Capabilities of Sub. Seven Program Parts of Sub. Seven A real Trojan Horse Threat Conclusion
What is Trojan Horse Program? n n Trojan Horse is one of the today’s most serious threat to computer security. A malicious security-breaking program disguised as something benign. A executable program Once infected, it is controlled totally by a hacker.
Who are the most targets? n n The home computers Reasons u u u Private Content Availability Defendless status
How it gets spread? n n n Email attachments Sending files in chat rooms Infected computer can attack other computer
Impact of Trojan Horse Attack n n n Complete access to victim’s system Delete and alter files Access to Administrator privileges Other computer get infected An infected computer can be targeted by any user.
Control of hackers over files n n n Alter user’s private documents such as bank statement, credit card statement, password file, mortgage payments files. Access files remotely as they own it Access of chat history
Ways to avoid this attack n n n Don’t download from unknown source Need to be aware of hidden extension Don’t use automatically get file feature Don’t type a command or go to web site told by a stranger Remove unnecessary services and file shares
Detection of attack n n n Hard to detect whether a computer is infected or not Not listed under process list of ALT+Ctrl+Delete key To detect, one can scan his computer for open port
How to remove Trojan from system n By getting clean re-installation n Anti-Trojan Software
Example: Sub. Seven n n Trojan Horse program that attacks computer running on Window 9. x platform. More popular than other types as it provides more options.
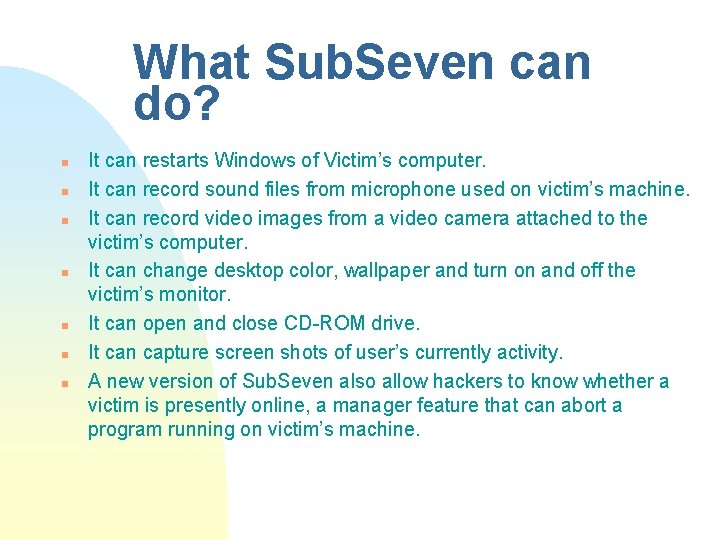
What Sub. Seven can do? n n n n It can restarts Windows of Victim’s computer. It can record sound files from microphone used on victim’s machine. It can record video images from a video camera attached to the victim’s computer. It can change desktop color, wallpaper and turn on and off the victim’s monitor. It can open and close CD-ROM drive. It can capture screen shots of user’s currently activity. A new version of Sub. Seven also allow hackers to know whether a victim is presently online, a manager feature that can abort a program running on victim’s machine.
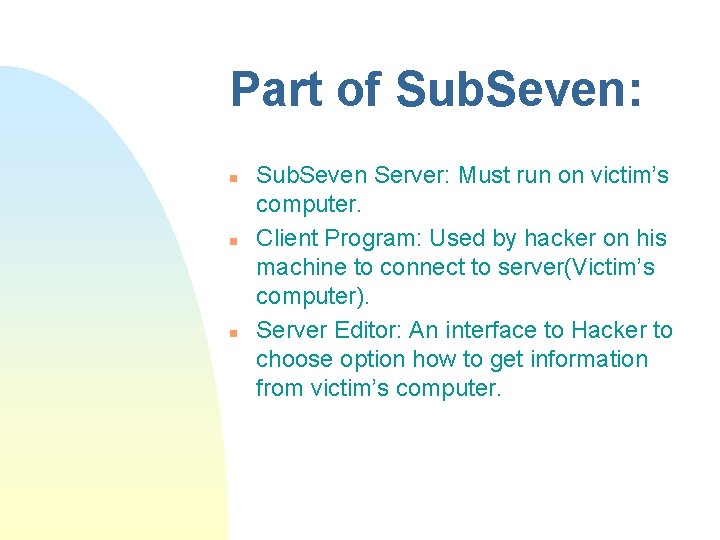
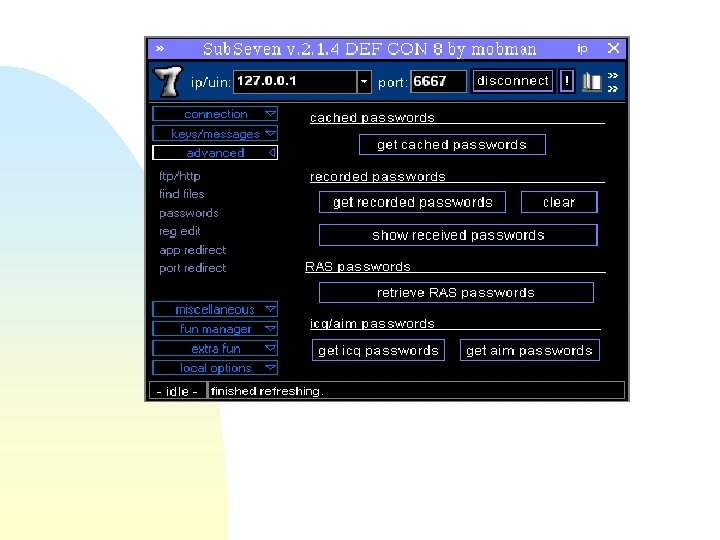
Part of Sub. Seven: n n n Sub. Seven Server: Must run on victim’s computer. Client Program: Used by hacker on his machine to connect to server(Victim’s computer). Server Editor: An interface to Hacker to choose option how to get information from victim’s computer.
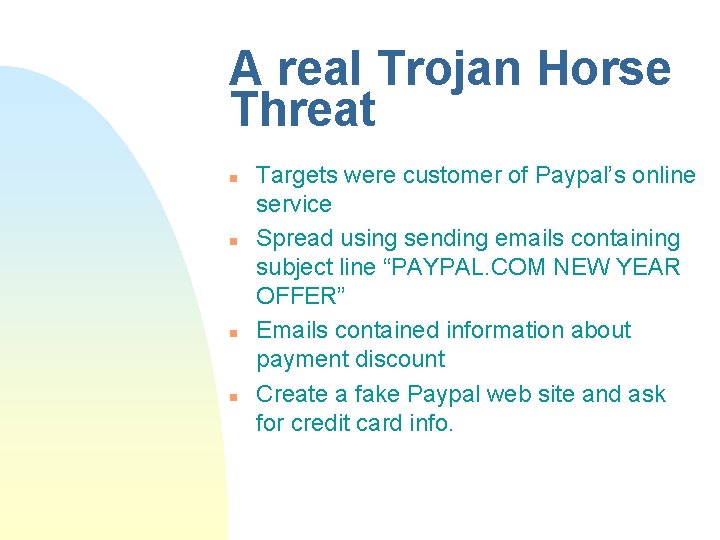
A real Trojan Horse Threat n n Targets were customer of Paypal’s online service Spread using sending emails containing subject line “PAYPAL. COM NEW YEAR OFFER” Emails contained information about payment discount Create a fake Paypal web site and ask for credit card info.
Conclusion n n Serious network security problem Once infected, computer is totally controlled by hacker. Hard to detect whether a computer is infected or not. Hard to recover.
Any Questions?
- Slides: 18