TRILL MPLSBASED ETHERNET VPN Kingston Smiler Mohammed Umair
TRILL MPLS-BASED ETHERNET VPN Kingston Smiler, Mohammed Umair, Shaji Ravindranathan, Lucy Yong, Donald Eastlake draft-muks-trill-transport-over-mpls-01 draft-muks-trill-evpn-00
Overview • This Presentation covers providing Ethernet L 2 VPN service using TRILL. • There are multiple L 2 VPN technologies already available e. g VPLS, BGP e. VPN etc. • VPLS is widely used in service provider networks, whereas BGP e. VPN is widely used as a data center interconnect technology with MPLS / Vx. LAN tunnel. • This draft introduces a new L 2 VPN technology using TRILL VTSD / VPTS. • TRILL e. VPN can be an alternate to both VPLS and BGP e. VPN. • In some case it provides more benefit, which neither of these technologies can meet, without any additional capability. 2

KEY TERMINOLOGIES AND INTRODUCTION
VPTS model (Virtual Private TRILL Service) • VPTS is similar to what VPLS does for a bridge domain. VPLS provides virtual private LAN service for different customers. This model provide Virtual Private TRILL service (VPTS) for different TRILL tenants. • PE routers are replaced with TIR. A TIR is capable of running both the VPLS and TRILL Protocols. i. e (TIR = MPLS PE + TRILL RBridge). • A new kind of switch domain, called VTSD (Virtual TRILL Switch Domain), replaces the VSI (bridge) in VPLS. • The VTSD act as a Virtual RBridge inside TIR – One VTSD per tenant / VPLS domain. – The VTSD maintains all the information maintained by the RBridge for only that tenant. – Forms adjacency with • Other VTSD in the same VPLS domain. • RBridge in the TRILL sites. – VTSD should take care of segregating one customer traffic with other. • No need to run Split Horizon in the provider PSN network, as TRILL takes care of Loop free topology using Distribution Trees. • VLAN and MCast pruning of TRILL protocol take care of pruning the Distribution tree. July 2015 4
VTSD Introduction • According to “draft-muks-trill-transport-over-mpls-01”, a VTSD is logical RBridge inside TIR. • It should be capable of performing all the operations a standard TRILL Switch should, one such Operation is the Appointed Forwarder mechanism. • The other operation of Standard TRILL switch is support for multiple parallel links, Multipathing across such parallel connections can be freely done for unicast TRILL Data traffic on a per-flow basis but is restricted for multi-destination traffic. 5
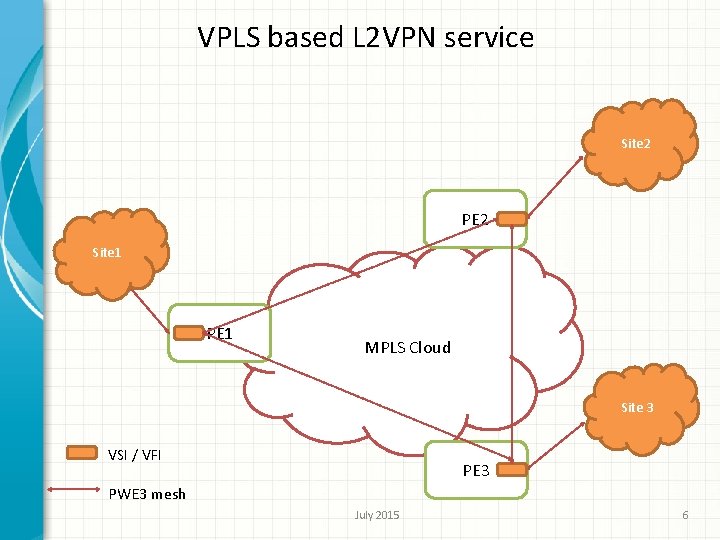
VPLS based L 2 VPN service Site 2 PE 2 Site 1 PE 1 MPLS Cloud Site 3 VSI / VFI PE 3 PWE 3 mesh July 2015 6
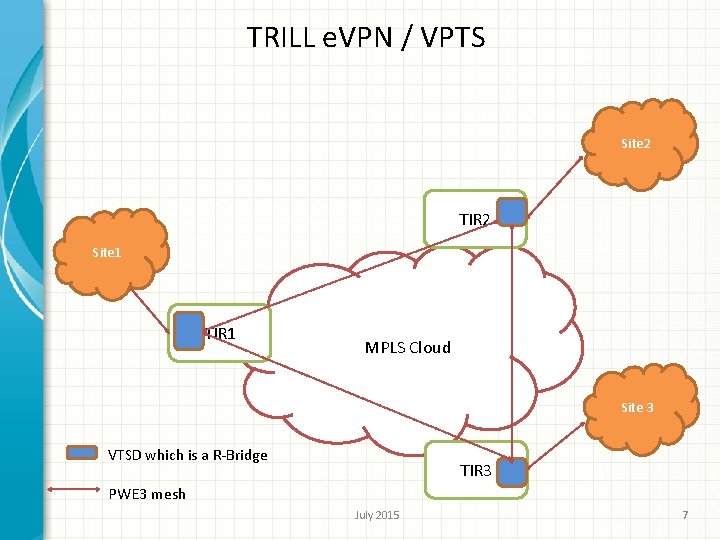
TRILL e. VPN / VPTS Site 2 TIR 2 Site 1 TIR 1 MPLS Cloud Site 3 VTSD which is a R-Bridge TIR 3 PWE 3 mesh July 2015 7
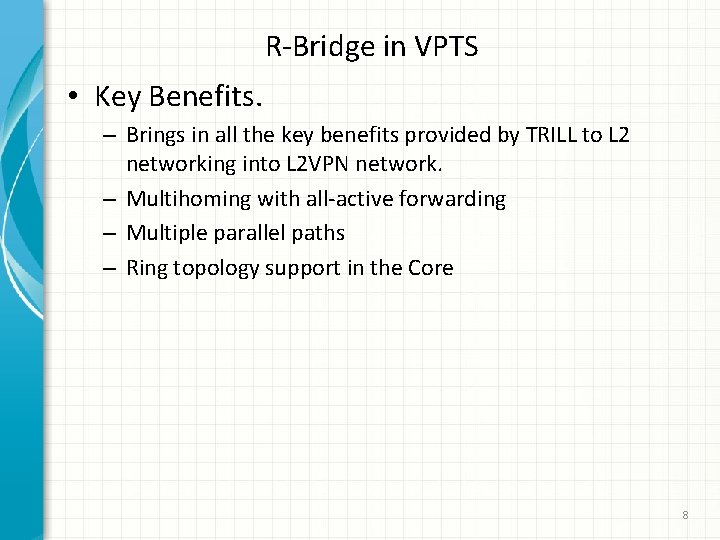
R-Bridge in VPTS • Key Benefits. – Brings in all the key benefits provided by TRILL to L 2 networking into L 2 VPN network. – Multihoming with all-active forwarding – Multiple parallel paths – Ring topology support in the Core 8
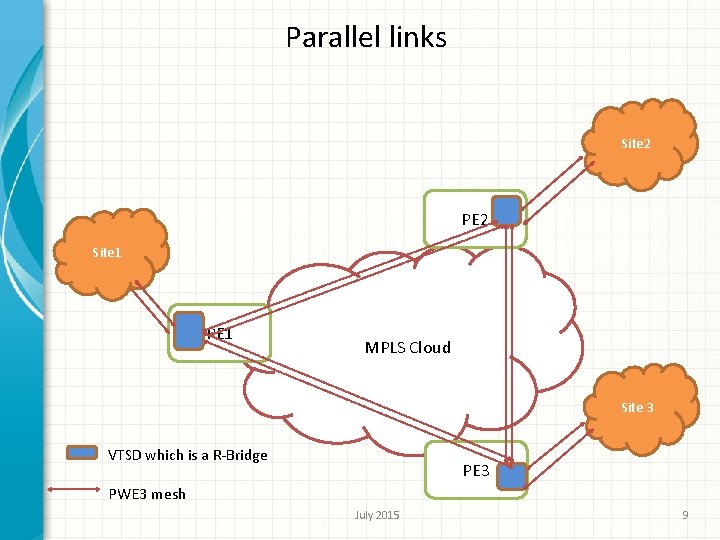
Parallel links Site 2 PE 2 Site 1 PE 1 MPLS Cloud Site 3 VTSD which is a R-Bridge PE 3 PWE 3 mesh July 2015 9
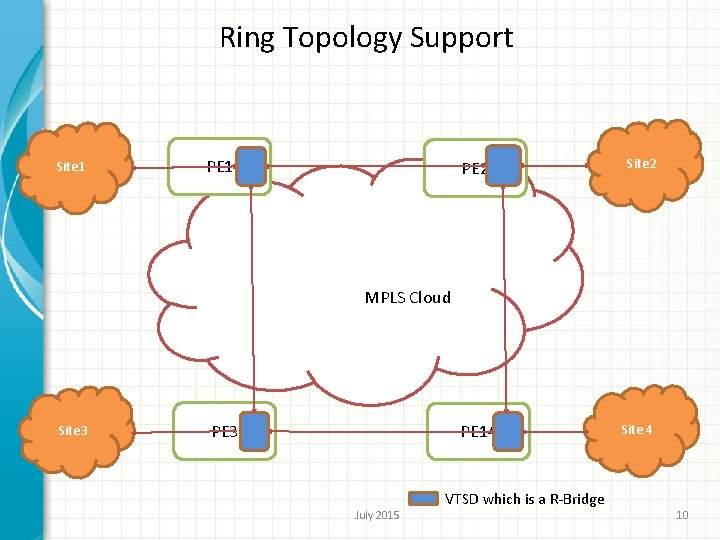
Ring Topology Support Site 1 PE 2 Site 2 PE 14 Site 4 MPLS Cloud Site 3 PE 3 July 2015 VTSD which is a R-Bridge 10
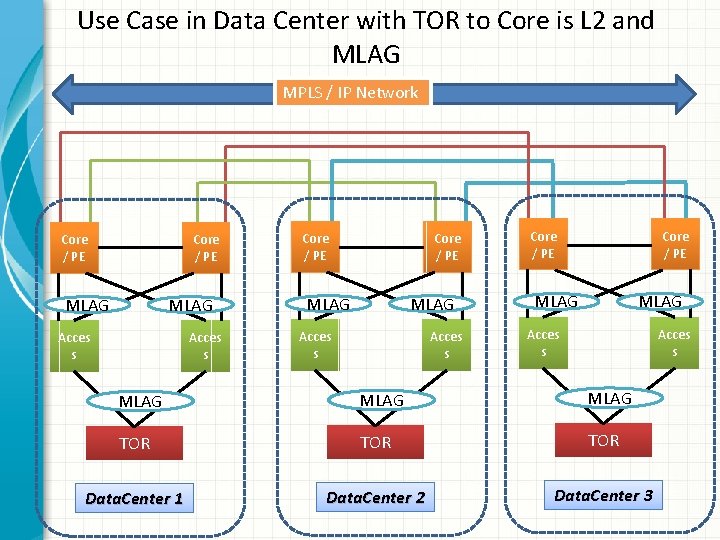
Use Case in Data Center with TOR to Core is L 2 and MLAG MPLS / IP Network Core / PE MLAG Acces s Core / PE MLAG Acces s MLAG TOR TOR Data. Center 1 Data. Center 2 Data. Center 3
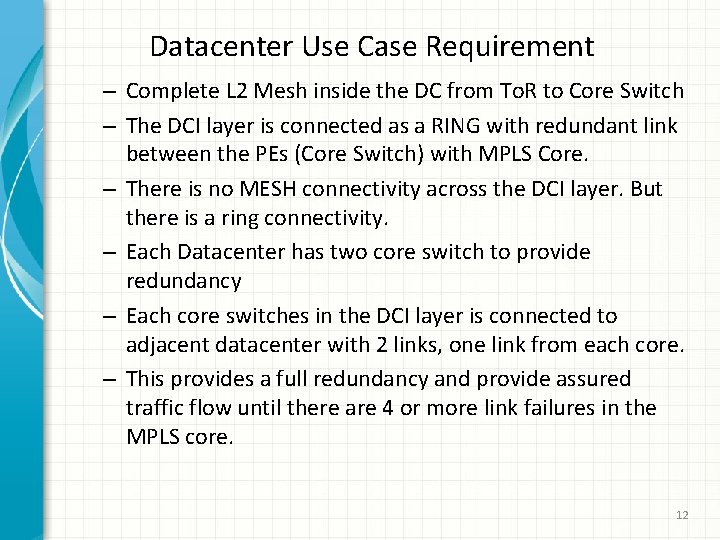
Datacenter Use Case Requirement – Complete L 2 Mesh inside the DC from To. R to Core Switch – The DCI layer is connected as a RING with redundant link between the PEs (Core Switch) with MPLS Core. – There is no MESH connectivity across the DCI layer. But there is a ring connectivity. – Each Datacenter has two core switch to provide redundancy – Each core switches in the DCI layer is connected to adjacent datacenter with 2 links, one link from each core. – This provides a full redundancy and provide assured traffic flow until there are 4 or more link failures in the MPLS core. 12
BUM traffic flow MPLS / IP Network Core / PE MLAG Acces s Core / PE MLAG Acces s MLAG TOR TOR Data. Center 1 Data. Center 2 Data. Center 3
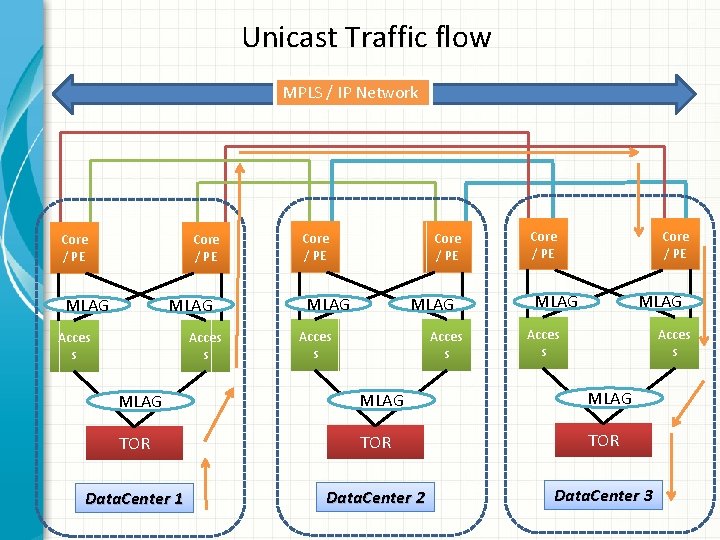
Unicast Traffic flow MPLS / IP Network Core / PE MLAG Acces s Core / PE MLAG Acces s MLAG TOR TOR Data. Center 1 Data. Center 2 Data. Center 3
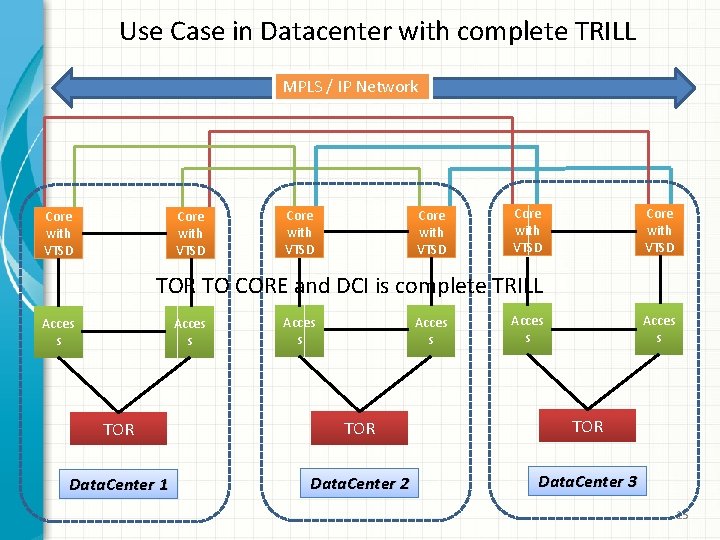
Use Case in Datacenter with complete TRILL MPLS / IP Network Core with VTSD Core with VTSD TOR TO CORE and DCI is complete TRILL Acces s Acces s TOR TOR Data. Center 1 Data. Center 2 Data. Center 3 15
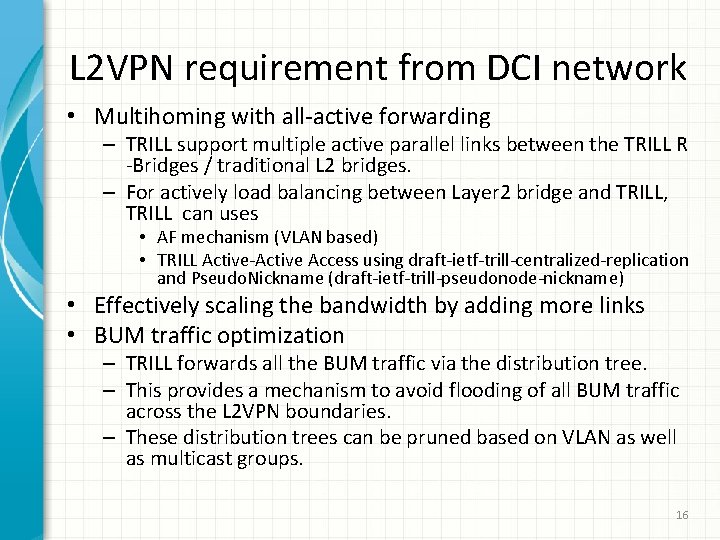
L 2 VPN requirement from DCI network • Multihoming with all-active forwarding – TRILL support multiple active parallel links between the TRILL R -Bridges / traditional L 2 bridges. – For actively load balancing between Layer 2 bridge and TRILL, TRILL can uses • AF mechanism (VLAN based) • TRILL Active-Active Access using draft-ietf-trill-centralized-replication and Pseudo. Nickname (draft-ietf-trill-pseudonode-nickname) • Effectively scaling the bandwidth by adding more links • BUM traffic optimization – TRILL forwards all the BUM traffic via the distribution tree. – This provides a mechanism to avoid flooding of all BUM traffic across the L 2 VPN boundaries. – These distribution trees can be pruned based on VLAN as well as multicast groups. 16
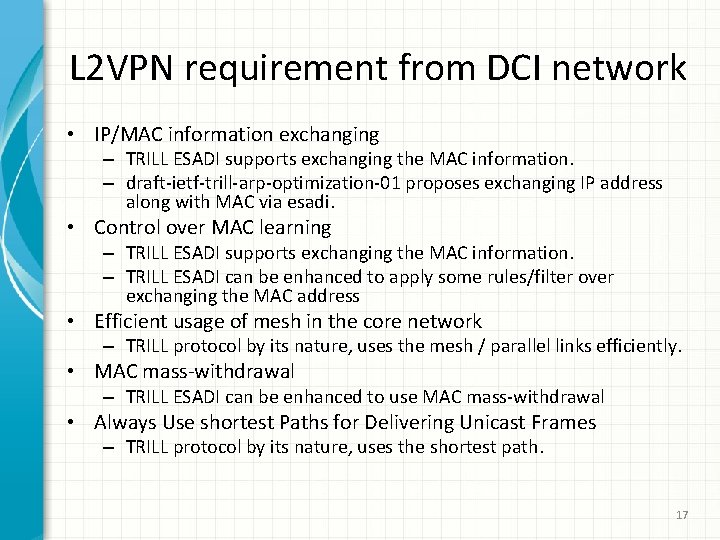
L 2 VPN requirement from DCI network • IP/MAC information exchanging – TRILL ESADI supports exchanging the MAC information. – draft-ietf-trill-arp-optimization-01 proposes exchanging IP address along with MAC via esadi. • Control over MAC learning – TRILL ESADI supports exchanging the MAC information. – TRILL ESADI can be enhanced to apply some rules/filter over exchanging the MAC address • Efficient usage of mesh in the core network – TRILL protocol by its nature, uses the mesh / parallel links efficiently. • MAC mass-withdrawal – TRILL ESADI can be enhanced to use MAC mass-withdrawal • Always Use shortest Paths for Delivering Unicast Frames – TRILL protocol by its nature, uses the shortest path. 17
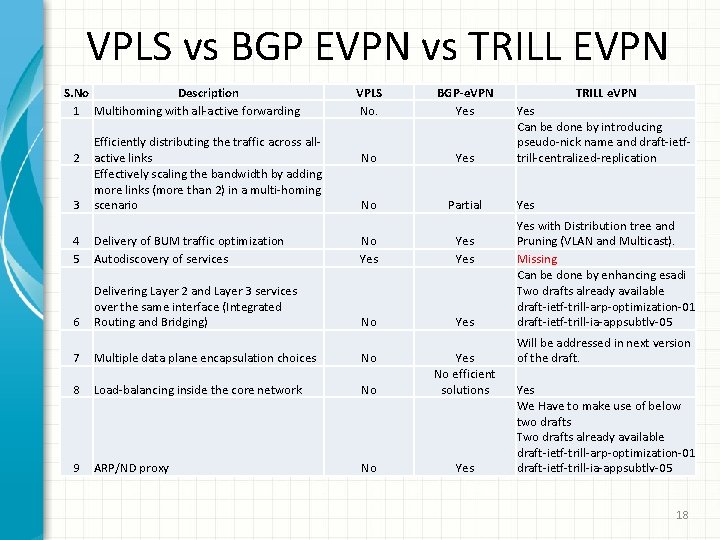
VPLS vs BGP EVPN vs TRILL EVPN S. No Description 1 Multihoming with all-active forwarding 2 3 Efficiently distributing the traffic across allactive links Effectively scaling the bandwidth by adding more links (more than 2) in a multi-homing scenario VPLS No. BGP-e. VPN Yes No Partial 4 5 Delivery of BUM traffic optimization Autodiscovery of services No Yes Yes 6 Delivering Layer 2 and Layer 3 services over the same interface (Integrated Routing and Bridging) No Yes 7 Multiple data plane encapsulation choices No 8 Load-balancing inside the core network No Yes No efficient solutions 9 ARP/ND proxy No Yes TRILL e. VPN Yes Can be done by introducing pseudo-nick name and draft-ietftrill-centralized-replication Yes with Distribution tree and Pruning (VLAN and Multicast). Missing Can be done by enhancing esadi Two drafts already available draft-ietf-trill-arp-optimization-01 draft-ietf-trill-ia-appsubtlv-05 Will be addressed in next version of the draft. Yes We Have to make use of below two drafts Two drafts already available draft-ietf-trill-arp-optimization-01 draft-ietf-trill-ia-appsubtlv-05 18
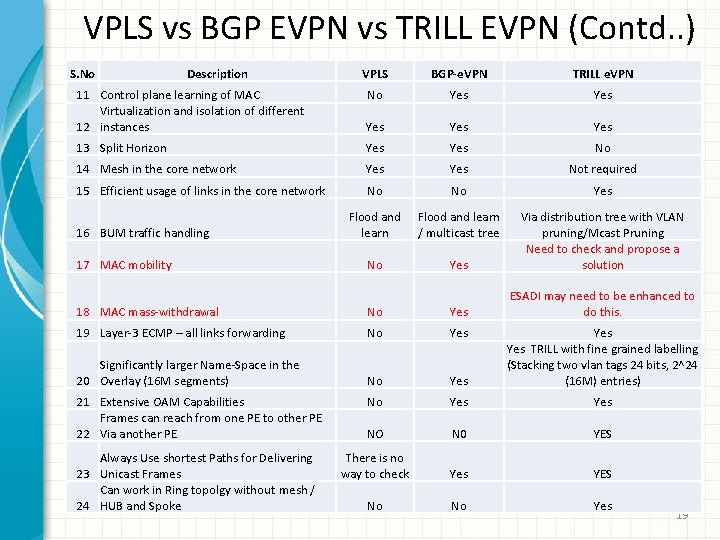
VPLS vs BGP EVPN vs TRILL EVPN (Contd. . ) S. No Description VPLS BGP-e. VPN TRILL e. VPN 11 Control plane learning of MAC Virtualization and isolation of different 12 instances No Yes Yes Yes 13 Split Horizon Yes No 14 Mesh in the core network Yes Not required 15 Efficient usage of links in the core network No No Yes Flood and learn / multicast tree No Yes Via distribution tree with VLAN pruning/Mcast Pruning Need to check and propose a solution ESADI may need to be enhanced to do this. 16 BUM traffic handling 17 MAC mobility 18 MAC mass-withdrawal No Yes 19 Layer-3 ECMP – all links forwarding No Yes Significantly larger Name-Space in the 20 Overlay (16 M segments) No Yes Yes TRILL with fine grained labelling (Stacking two vlan tags 24 bits, 2^24 (16 M) entries) No Yes NO N 0 YES There is no way to check Yes YES No No Yes 21 Extensive OAM Capabilities Frames can reach from one PE to other PE 22 Via another PE Always Use shortest Paths for Delivering 23 Unicast Frames Can work in Ring topolgy without mesh / 24 HUB and Spoke 19
Next Step Need to identify micro-level gaps in TRILL to provide efficient e. VPN support. The drafts needs more work. Comments welcome. 20
- Slides: 20