Transport Layer Instructor Mohsen Afsharchi Office E122 Email
![Rdt 2. 0: channel with bit errors [stop & wait protocol] r Assumptions m Rdt 2. 0: channel with bit errors [stop & wait protocol] r Assumptions m](https://slidetodoc.com/presentation_image_h2/41b60a56d3512ad5162886eacd109dfc/image-5.jpg)
![GBN: sender extended FSM rdt_send(data) L base=1 nextseqnum=1 if (nextseqnum < base+N) { sndpkt[nextseqnum] GBN: sender extended FSM rdt_send(data) L base=1 nextseqnum=1 if (nextseqnum < base+N) { sndpkt[nextseqnum]](https://slidetodoc.com/presentation_image_h2/41b60a56d3512ad5162886eacd109dfc/image-24.jpg)
![Selective repeat sender data from above : receiver pkt n in [rcvbase, rcvbase+N-1] r Selective repeat sender data from above : receiver pkt n in [rcvbase, rcvbase+N-1] r](https://slidetodoc.com/presentation_image_h2/41b60a56d3512ad5162886eacd109dfc/image-29.jpg)
- Slides: 32
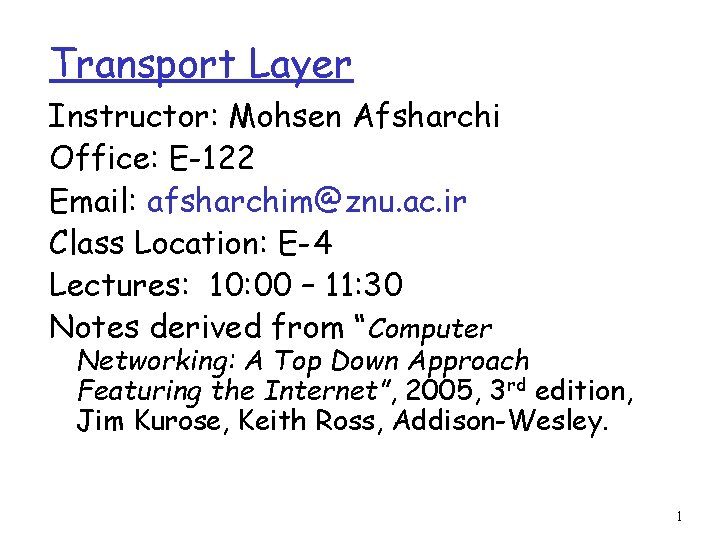
Transport Layer Instructor: Mohsen Afsharchi Office: E-122 Email: afsharchim@znu. ac. ir Class Location: E-4 Lectures: 10: 00 – 11: 30 Notes derived from “Computer Networking: A Top Down Approach Featuring the Internet”, 2005, 3 rd edition, Jim Kurose, Keith Ross, Addison-Wesley. 1
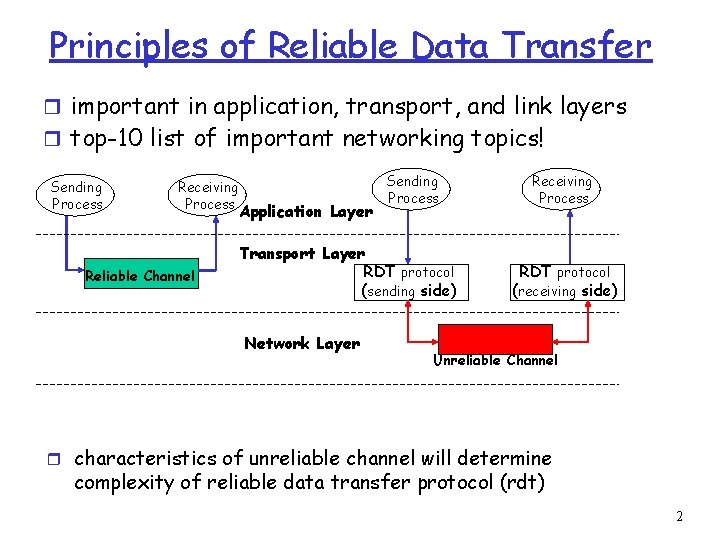
Principles of Reliable Data Transfer r important in application, transport, and link layers r top-10 list of important networking topics! Sending Process Receiving Process Reliable Channel Application Layer Sending Process Transport Layer RDT protocol (sending side) Network Layer Receiving Process RDT protocol (receiving side) Unreliable Channel r characteristics of unreliable channel will determine complexity of reliable data transfer protocol (rdt) 2
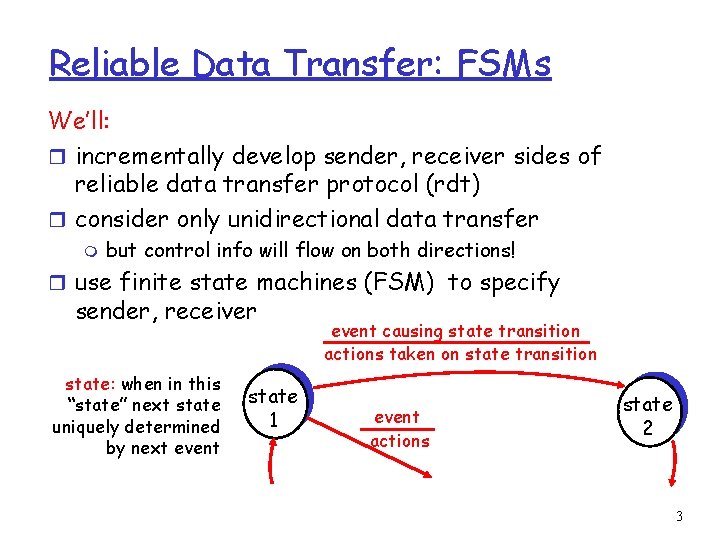
Reliable Data Transfer: FSMs We’ll: r incrementally develop sender, receiver sides of reliable data transfer protocol (rdt) r consider only unidirectional data transfer m but control info will flow on both directions! r use finite state machines (FSM) to specify sender, receiver state: when in this “state” next state uniquely determined by next event state 1 event causing state transition actions taken on state transition event actions state 2 3
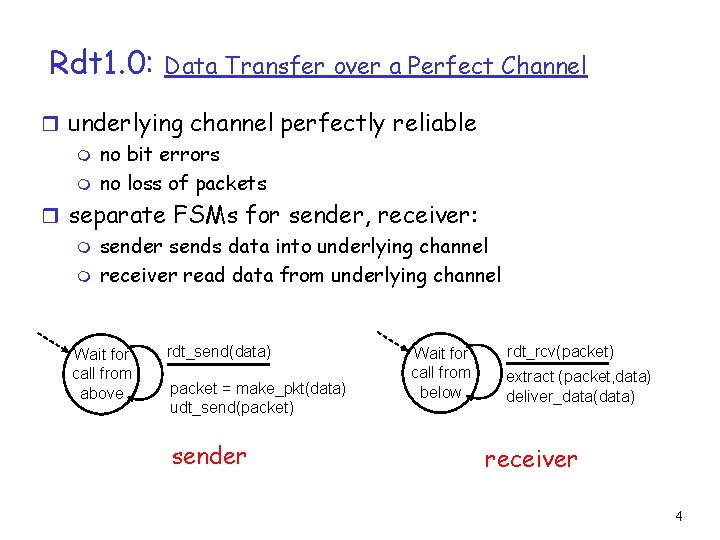
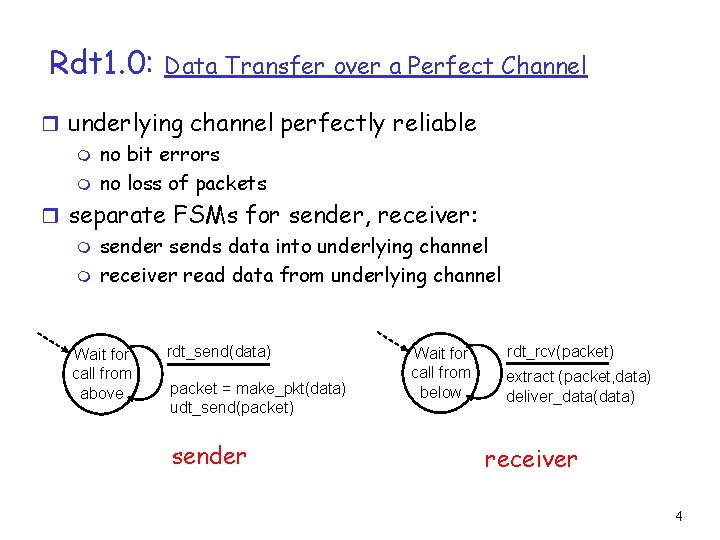
Rdt 1. 0: Data Transfer over a Perfect Channel r underlying channel perfectly reliable m no bit errors m no loss of packets r separate FSMs for sender, receiver: m sender sends data into underlying channel m receiver read data from underlying channel Wait for call from above rdt_send(data) packet = make_pkt(data) udt_send(packet) sender Wait for call from below rdt_rcv(packet) extract (packet, data) deliver_data(data) receiver 4
![Rdt 2 0 channel with bit errors stop wait protocol r Assumptions m Rdt 2. 0: channel with bit errors [stop & wait protocol] r Assumptions m](https://slidetodoc.com/presentation_image_h2/41b60a56d3512ad5162886eacd109dfc/image-5.jpg)
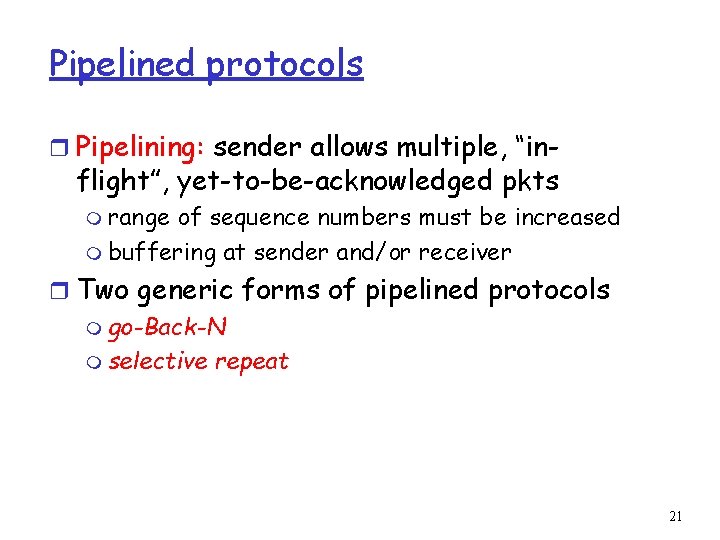
Rdt 2. 0: channel with bit errors [stop & wait protocol] r Assumptions m All packets are received m Packets may be corrupted (i. e. , bits may be flipped) m Checksum to detect bit errors r How to recover from errors? Use ARQ mechanism m acknowledgements (ACKs): receiver explicitly tells sender that packet received correctly m negative acknowledgements (NAKs): receiver explicitly tells sender that packet had errors m sender retransmits pkt on receipt of NAK r What about error correcting codes? 5
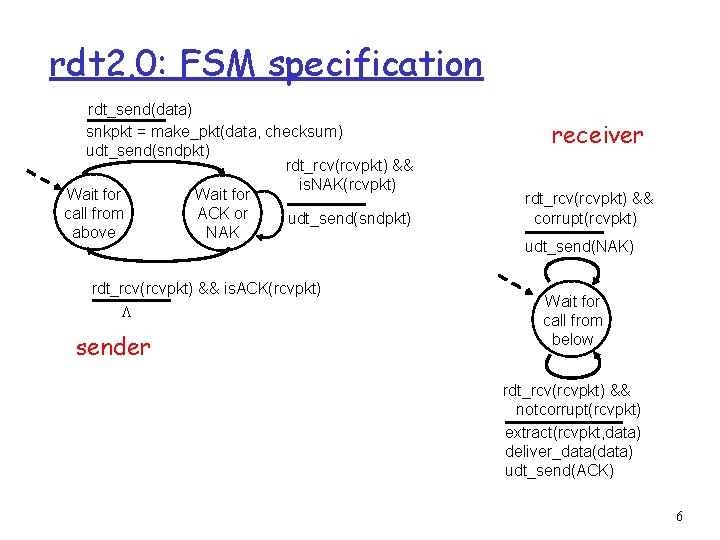
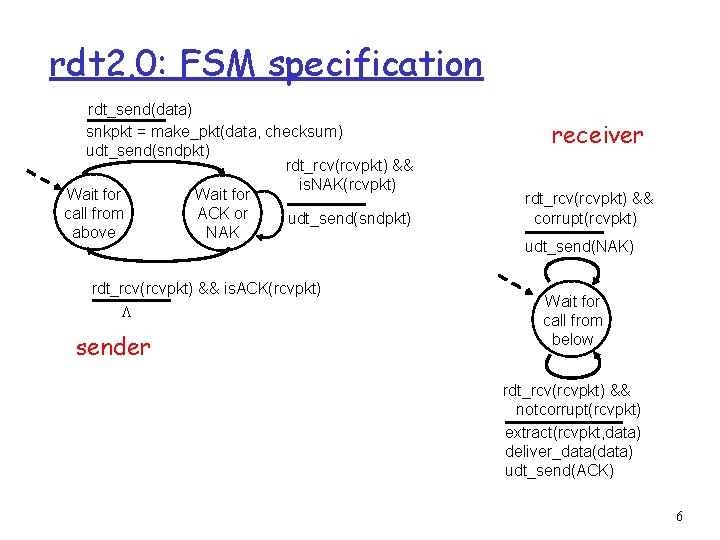
rdt 2. 0: FSM specification rdt_send(data) snkpkt = make_pkt(data, checksum) udt_send(sndpkt) rdt_rcv(rcvpkt) && is. NAK(rcvpkt) Wait for call from ACK or udt_send(sndpkt) above NAK rdt_rcv(rcvpkt) && is. ACK(rcvpkt) L sender receiver rdt_rcv(rcvpkt) && corrupt(rcvpkt) udt_send(NAK) Wait for call from below rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) extract(rcvpkt, data) deliver_data(data) udt_send(ACK) 6
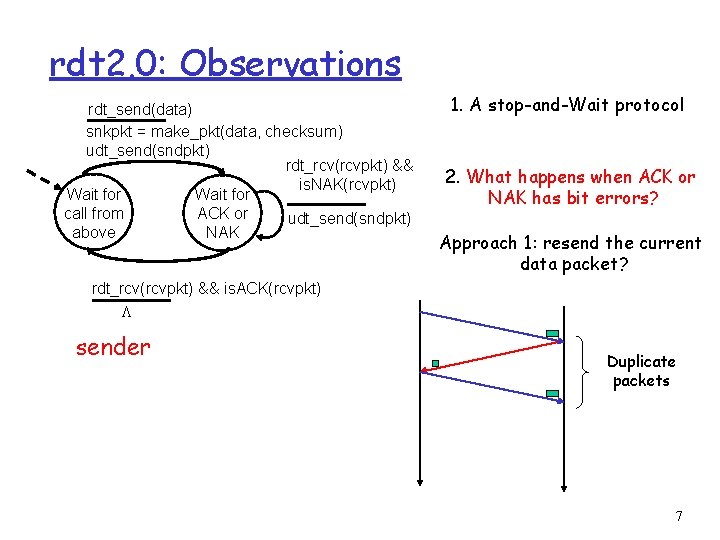
rdt 2. 0: Observations rdt_send(data) snkpkt = make_pkt(data, checksum) udt_send(sndpkt) rdt_rcv(rcvpkt) && is. NAK(rcvpkt) Wait for call from ACK or udt_send(sndpkt) above NAK 1. A stop-and-Wait protocol 2. What happens when ACK or NAK has bit errors? Approach 1: resend the current data packet? rdt_rcv(rcvpkt) && is. ACK(rcvpkt) L sender Duplicate packets 7
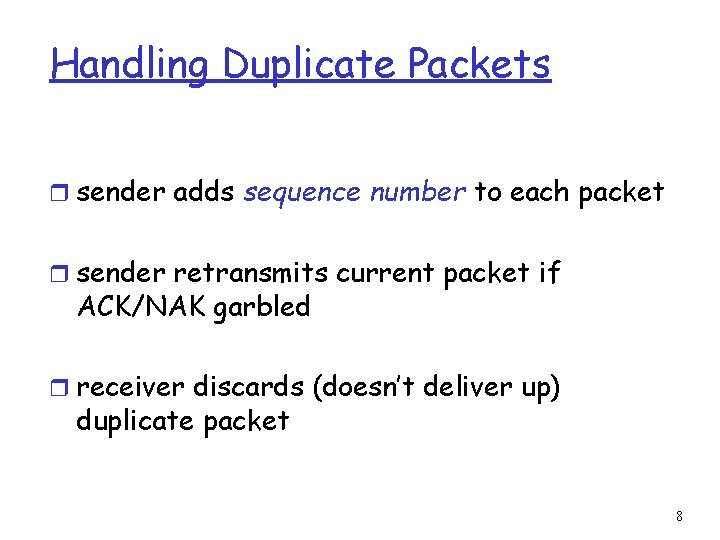
Handling Duplicate Packets r sender adds sequence number to each packet r sender retransmits current packet if ACK/NAK garbled r receiver discards (doesn’t deliver up) duplicate packet 8
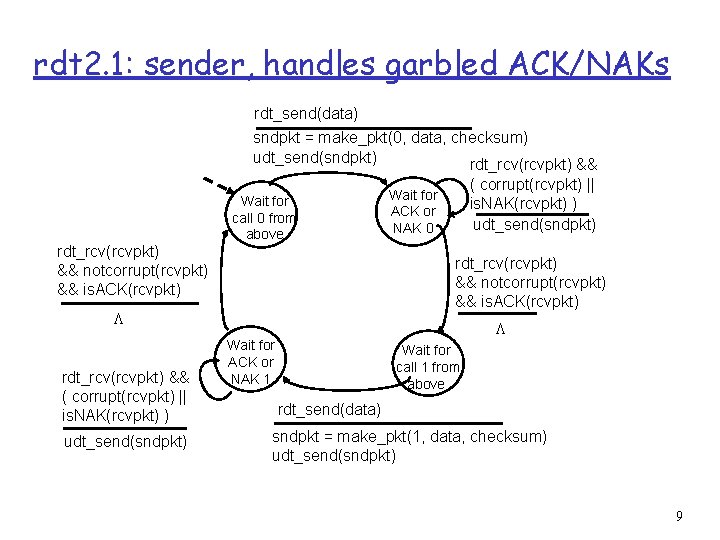
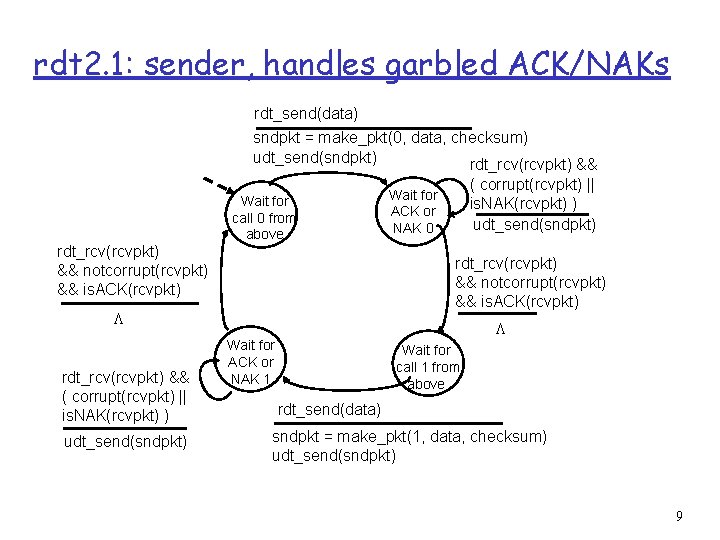
rdt 2. 1: sender, handles garbled ACK/NAKs rdt_send(data) sndpkt = make_pkt(0, data, checksum) udt_send(sndpkt) rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && is. ACK(rcvpkt) Wait for call 0 from above rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && is. ACK(rcvpkt) L rdt_rcv(rcvpkt) && ( corrupt(rcvpkt) || is. NAK(rcvpkt) ) udt_send(sndpkt) Wait for ACK or NAK 0 L Wait for ACK or NAK 1 Wait for call 1 from above rdt_send(data) sndpkt = make_pkt(1, data, checksum) udt_send(sndpkt) 9
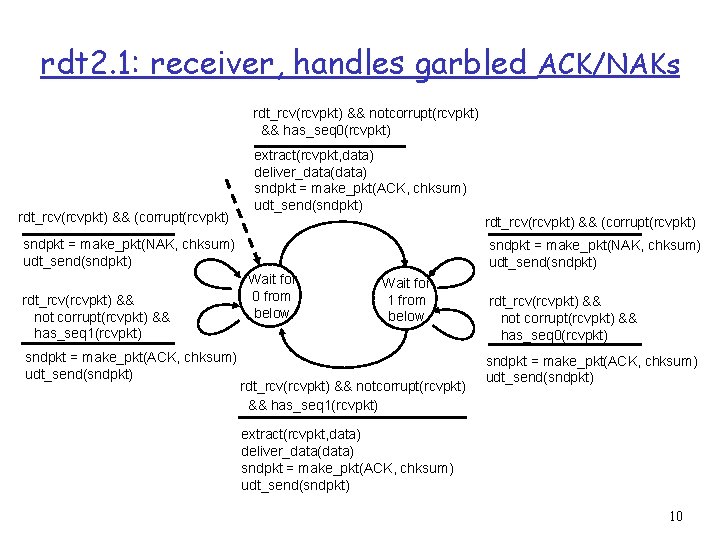
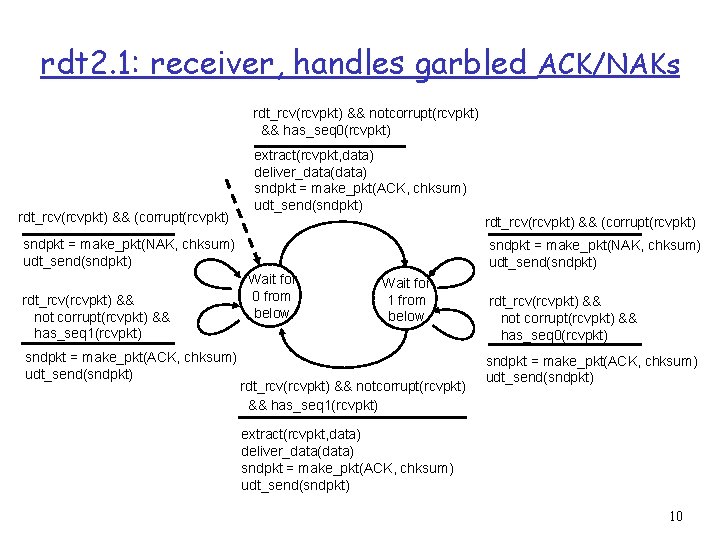
rdt 2. 1: receiver, handles garbled ACK/NAKs rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && has_seq 0(rcvpkt) rdt_rcv(rcvpkt) && (corrupt(rcvpkt) extract(rcvpkt, data) deliver_data(data) sndpkt = make_pkt(ACK, chksum) udt_send(sndpkt) rdt_rcv(rcvpkt) && (corrupt(rcvpkt) sndpkt = make_pkt(NAK, chksum) udt_send(sndpkt) rdt_rcv(rcvpkt) && not corrupt(rcvpkt) && has_seq 1(rcvpkt) sndpkt = make_pkt(ACK, chksum) udt_send(sndpkt) sndpkt = make_pkt(NAK, chksum) udt_send(sndpkt) Wait for 0 from below Wait for 1 from below rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && has_seq 1(rcvpkt) rdt_rcv(rcvpkt) && not corrupt(rcvpkt) && has_seq 0(rcvpkt) sndpkt = make_pkt(ACK, chksum) udt_send(sndpkt) extract(rcvpkt, data) deliver_data(data) sndpkt = make_pkt(ACK, chksum) udt_send(sndpkt) 10
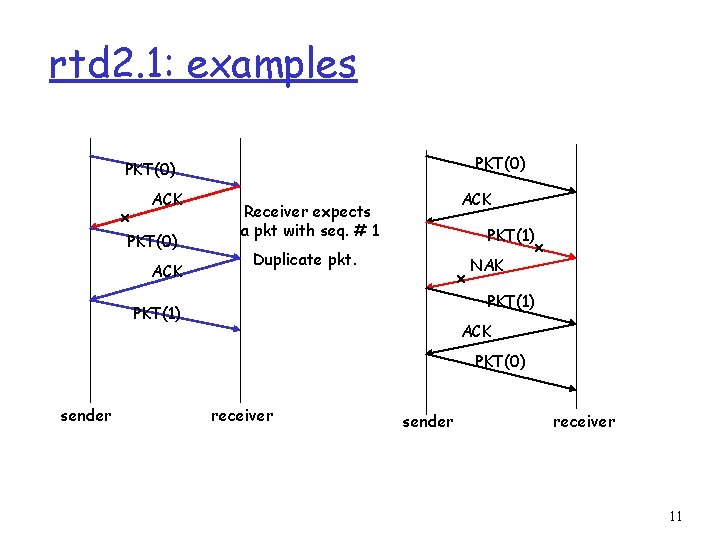
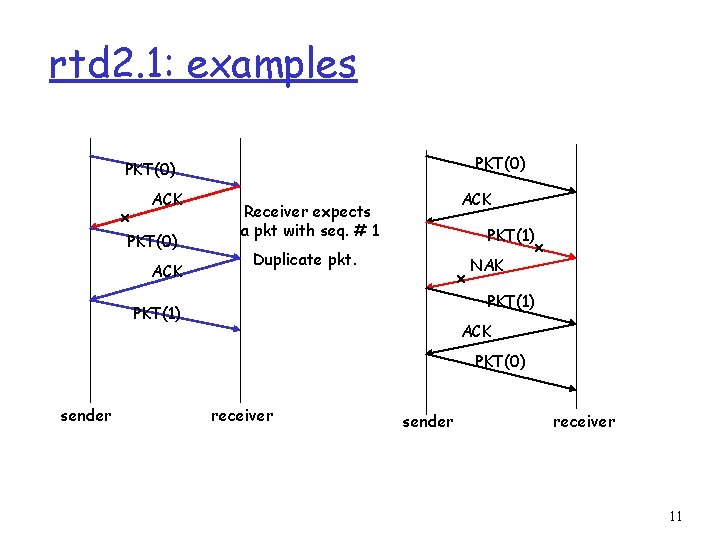
rtd 2. 1: examples PKT(0) x ACK PKT(0) ACK Receiver expects a pkt with seq. # 1 PKT(1) Duplicate pkt. x NAK x PKT(1) ACK PKT(0) sender receiver 11
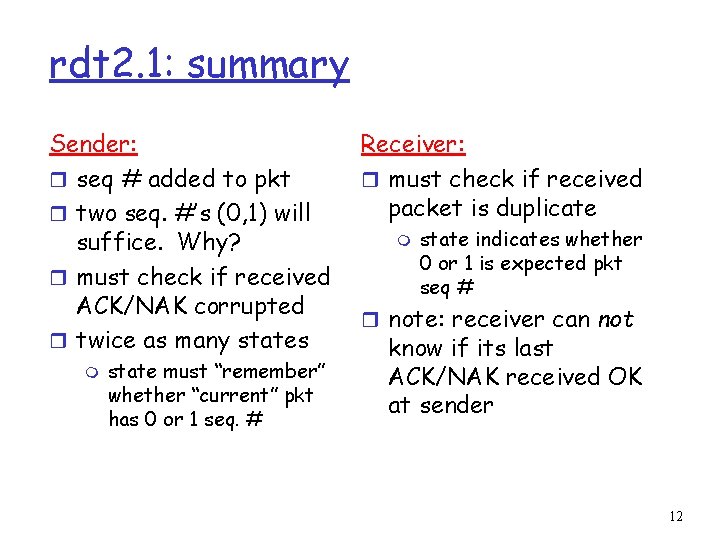
rdt 2. 1: summary Sender: r seq # added to pkt r two seq. #’s (0, 1) will suffice. Why? r must check if received ACK/NAK corrupted r twice as many states m state must “remember” whether “current” pkt has 0 or 1 seq. # Receiver: r must check if received packet is duplicate m state indicates whether 0 or 1 is expected pkt seq # r note: receiver can not know if its last ACK/NAK received OK at sender 12
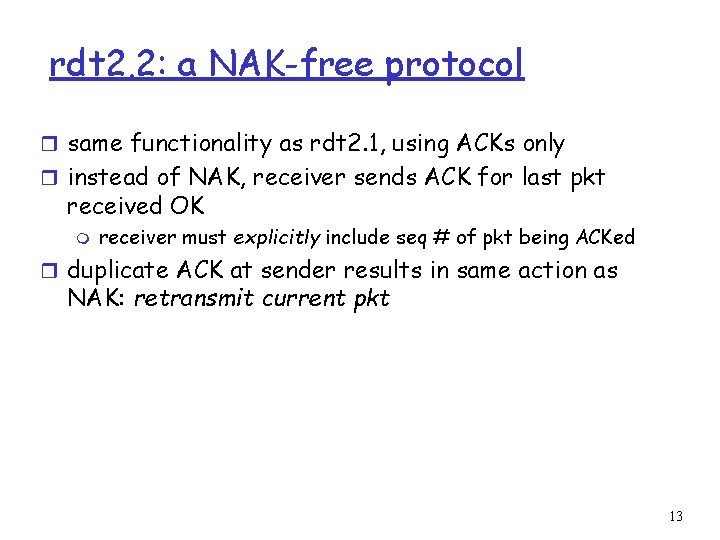
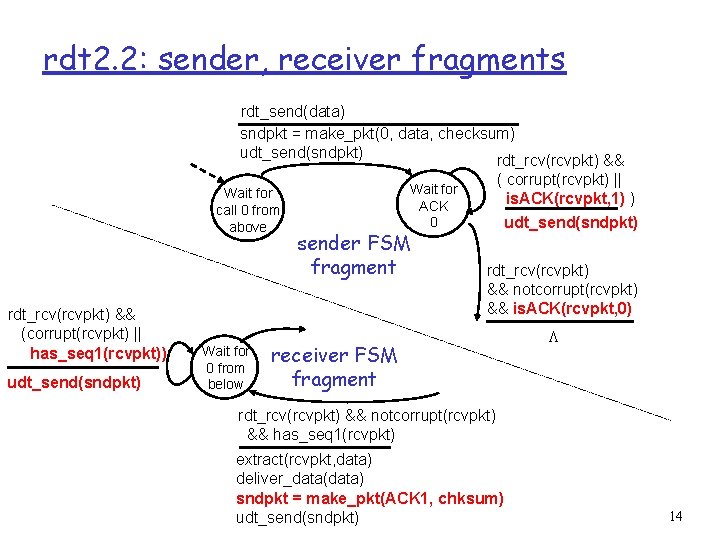
rdt 2. 2: a NAK-free protocol r same functionality as rdt 2. 1, using ACKs only r instead of NAK, receiver sends ACK for last pkt received OK m receiver must explicitly include seq # of pkt being ACKed r duplicate ACK at sender results in same action as NAK: retransmit current pkt 13
rdt 2. 2: sender, receiver fragments rdt_send(data) sndpkt = make_pkt(0, data, checksum) udt_send(sndpkt) rdt_rcv(rcvpkt) && Wait for call 0 from above rdt_rcv(rcvpkt) && (corrupt(rcvpkt) || has_seq 1(rcvpkt)) udt_send(sndpkt) Wait for 0 from below ( corrupt(rcvpkt) || is. ACK(rcvpkt, 1) ) udt_send(sndpkt) Wait for ACK 0 sender FSM fragment rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && is. ACK(rcvpkt, 0) receiver FSM fragment L rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && has_seq 1(rcvpkt) extract(rcvpkt, data) deliver_data(data) sndpkt = make_pkt(ACK 1, chksum) udt_send(sndpkt) 14
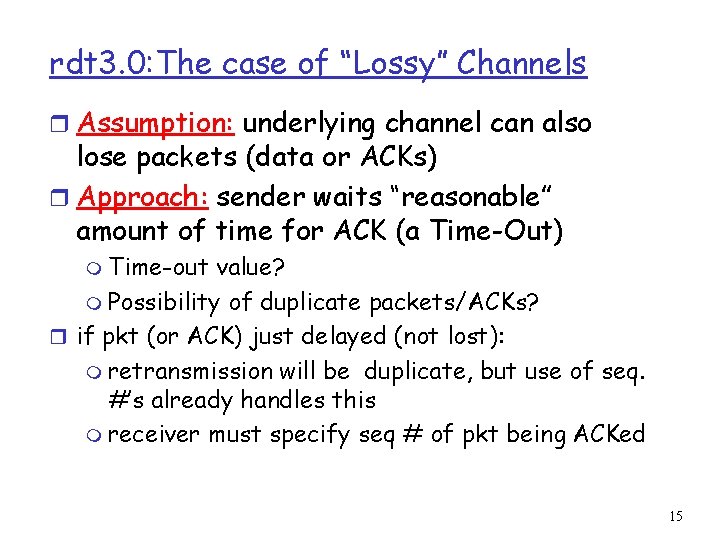
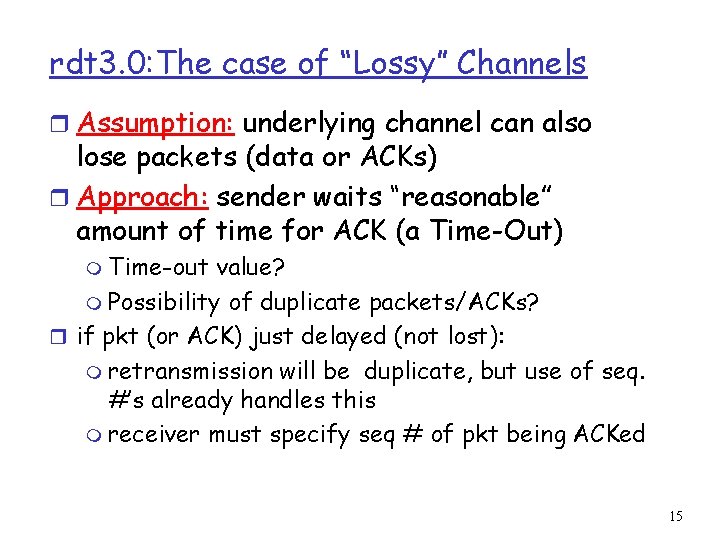
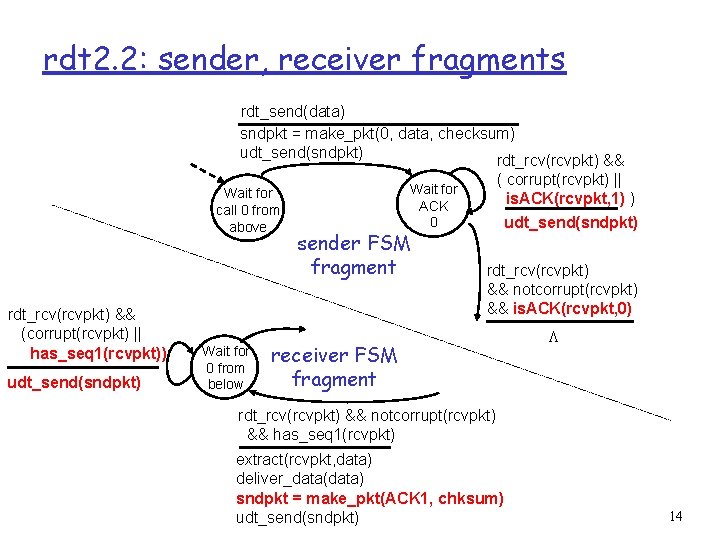
rdt 3. 0: The case of “Lossy” Channels r Assumption: underlying channel can also lose packets (data or ACKs) r Approach: sender waits “reasonable” amount of time for ACK (a Time-Out) m Time-out value? m Possibility of duplicate packets/ACKs? r if pkt (or ACK) just delayed (not lost): m retransmission will be duplicate, but use of seq. #’s already handles this m receiver must specify seq # of pkt being ACKed 15
rdt 3. 0 sender rdt_send(data) sndpkt = make_pkt(0, data, checksum) udt_send(sndpkt) start_timer rdt_rcv(rcvpkt) L rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && is. ACK(rcvpkt, 1) rdt_rcv(rcvpkt) && ( corrupt(rcvpkt) || is. ACK(rcvpkt, 0) ) timeout udt_send(sndpkt) start_timer rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) && is. ACK(rcvpkt, 0) stop_timer timeout udt_send(sndpkt) start_timer L Wait for ACK 0 Wait for call 0 from above L rdt_rcv(rcvpkt) && ( corrupt(rcvpkt) || is. ACK(rcvpkt, 1) ) Wait for ACK 1 Wait for call 1 from above rdt_send(data) rdt_rcv(rcvpkt) L sndpkt = make_pkt(1, data, checksum) udt_send(sndpkt) start_timer 16
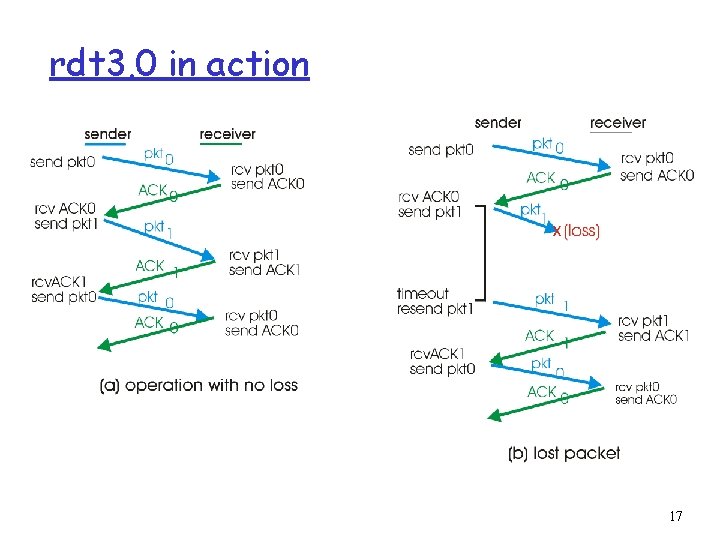
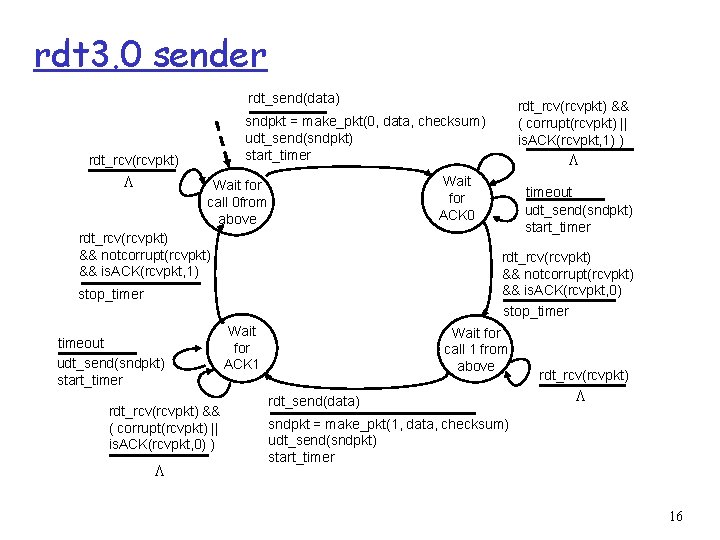
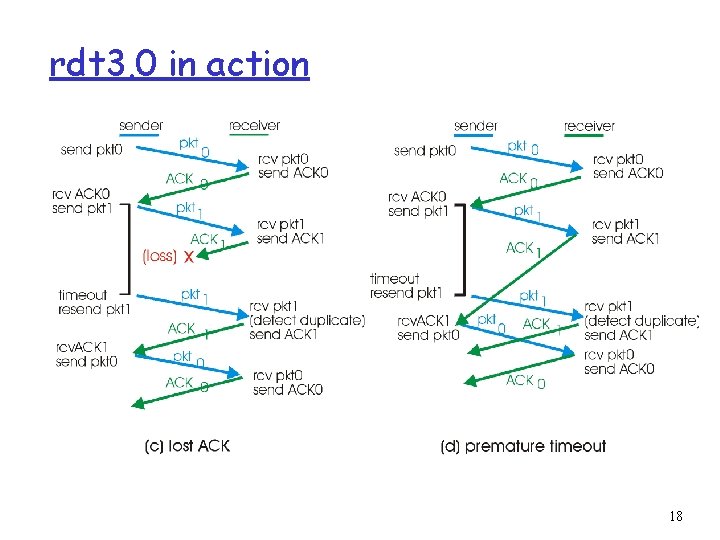
rdt 3. 0 in action 17
rdt 3. 0 in action 18
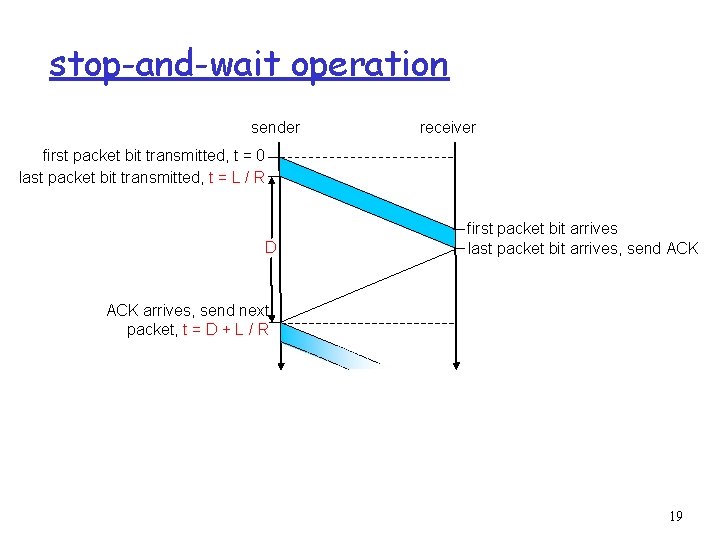
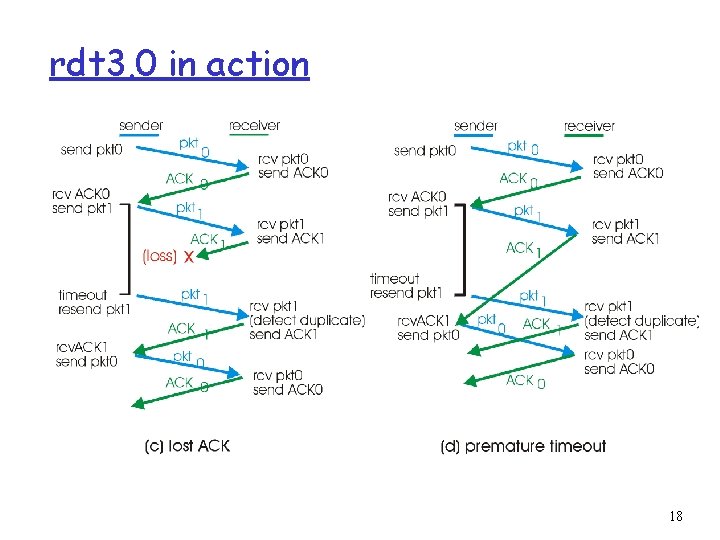
stop-and-wait operation sender receiver first packet bit transmitted, t = 0 last packet bit transmitted, t = L / R D first packet bit arrives last packet bit arrives, send ACK arrives, send next packet, t = D + L / R 19
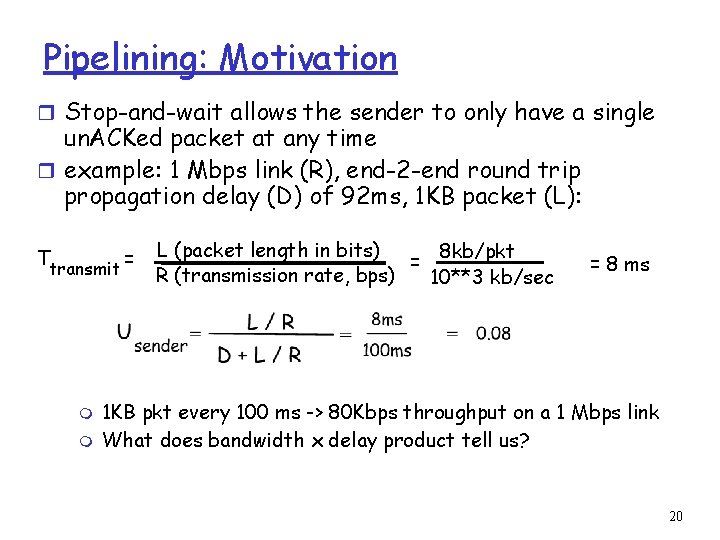
Pipelining: Motivation r Stop-and-wait allows the sender to only have a single un. ACKed packet at any time r example: 1 Mbps link (R), end-2 -end round trip propagation delay (D) of 92 ms, 1 KB packet (L): Ttransmit = m m L (packet length in bits) 8 kb/pkt = R (transmission rate, bps) 10**3 kb/sec = 8 ms 1 KB pkt every 100 ms -> 80 Kbps throughput on a 1 Mbps link What does bandwidth x delay product tell us? 20
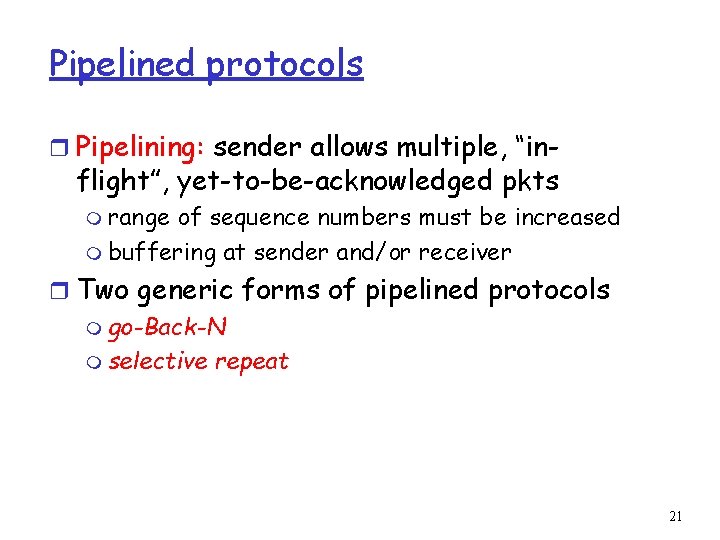
Pipelined protocols r Pipelining: sender allows multiple, “in- flight”, yet-to-be-acknowledged pkts m range of sequence numbers must be increased m buffering at sender and/or receiver r Two generic forms of pipelined protocols m go-Back-N m selective repeat 21
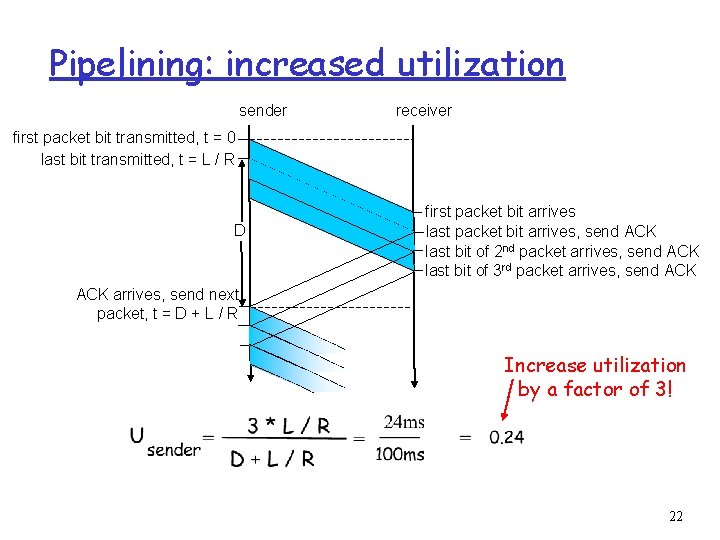
Pipelining: increased utilization sender receiver first packet bit transmitted, t = 0 last bit transmitted, t = L / R D first packet bit arrives last packet bit arrives, send ACK last bit of 2 nd packet arrives, send ACK last bit of 3 rd packet arrives, send ACK arrives, send next packet, t = D + L / R Increase utilization by a factor of 3! 22
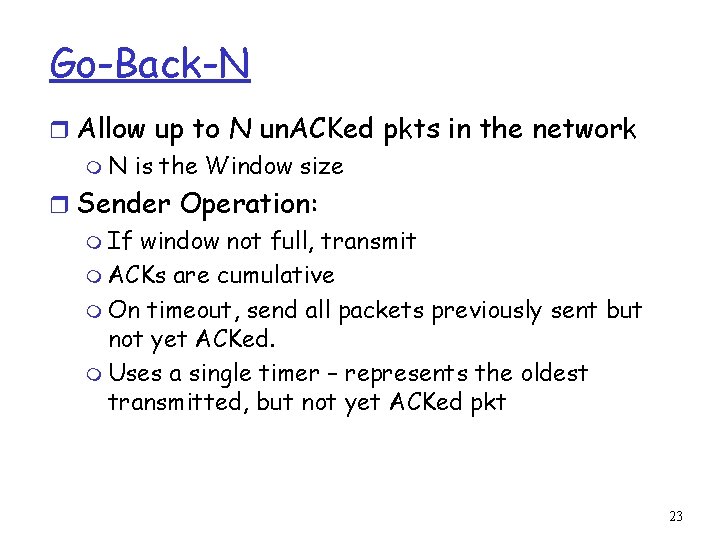
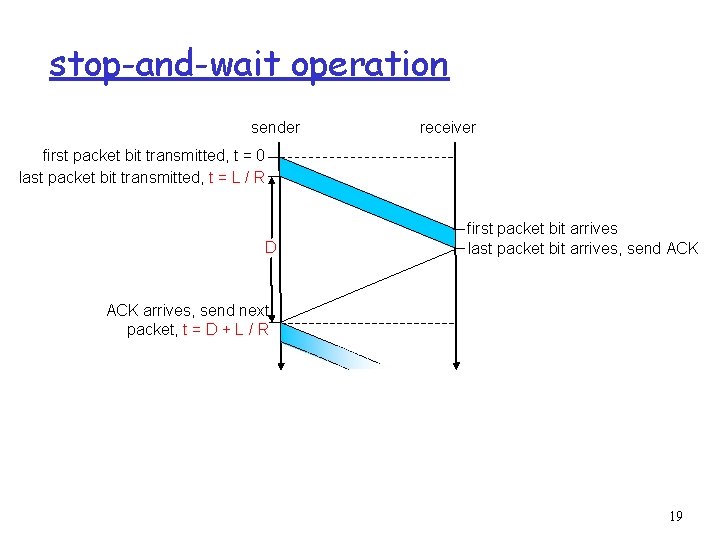
Go-Back-N r Allow up to N un. ACKed pkts in the network m N is the Window size r Sender Operation: m If window not full, transmit m ACKs are cumulative m On timeout, send all packets previously sent but not yet ACKed. m Uses a single timer – represents the oldest transmitted, but not yet ACKed pkt 23
![GBN sender extended FSM rdtsenddata L base1 nextseqnum1 if nextseqnum baseN sndpktnextseqnum GBN: sender extended FSM rdt_send(data) L base=1 nextseqnum=1 if (nextseqnum < base+N) { sndpkt[nextseqnum]](https://slidetodoc.com/presentation_image_h2/41b60a56d3512ad5162886eacd109dfc/image-24.jpg)
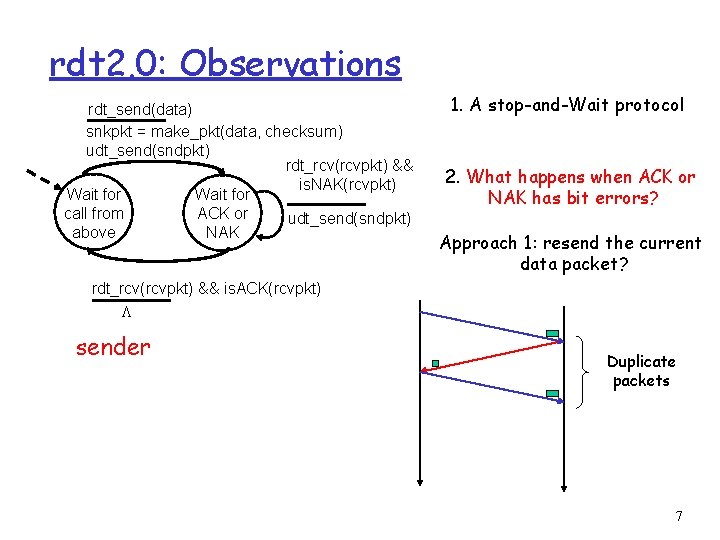
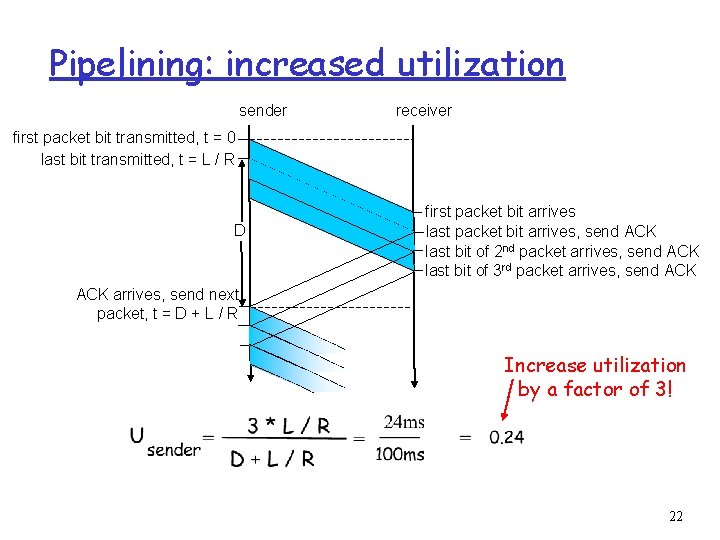
GBN: sender extended FSM rdt_send(data) L base=1 nextseqnum=1 if (nextseqnum < base+N) { sndpkt[nextseqnum] = make_pkt(nextseqnum, data, chksum) udt_send(sndpkt[nextseqnum]) if (base == nextseqnum) start_timer nextseqnum++ } else refuse_data(data) Wait rdt_rcv(rcvpkt) && corrupt(rcvpkt) timeout start_timer udt_send(sndpkt[base]) udt_send(sndpkt[base+1]) … udt_send(sndpkt[nextseqnum-1]) rdt_rcv(rcvpkt) && notcorrupt(rcvpkt) base = getacknum(rcvpkt)+1 If (base == nextseqnum) stop_timer else start_timer 24
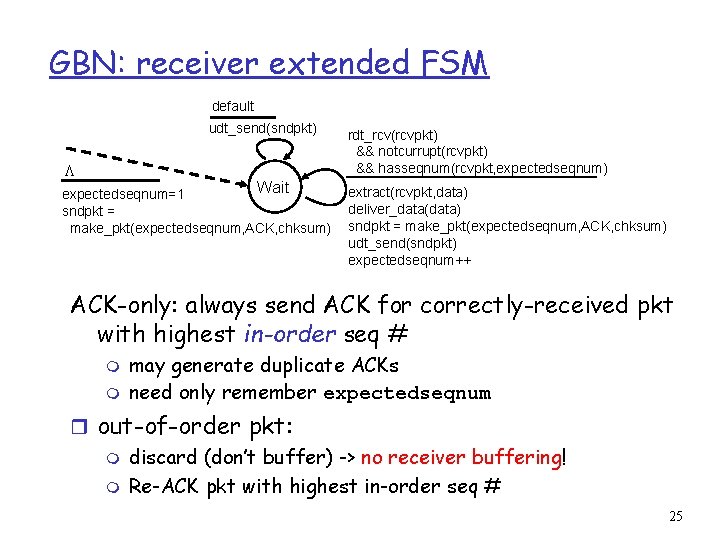
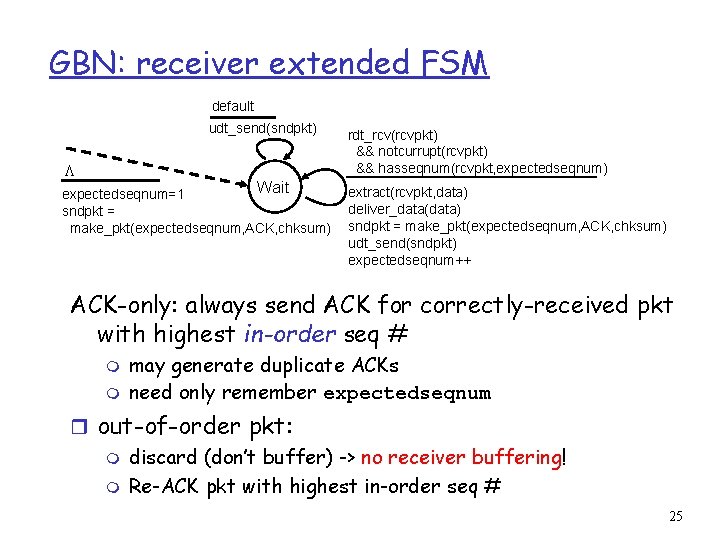
GBN: receiver extended FSM default udt_send(sndpkt) L Wait expectedseqnum=1 sndpkt = make_pkt(expectedseqnum, ACK, chksum) rdt_rcv(rcvpkt) && notcurrupt(rcvpkt) && hasseqnum(rcvpkt, expectedseqnum) extract(rcvpkt, data) deliver_data(data) sndpkt = make_pkt(expectedseqnum, ACK, chksum) udt_send(sndpkt) expectedseqnum++ ACK-only: always send ACK for correctly-received pkt with highest in-order seq # m m may generate duplicate ACKs need only remember expectedseqnum r out-of-order pkt: m discard (don’t buffer) -> no receiver buffering! m Re-ACK pkt with highest in-order seq # 25
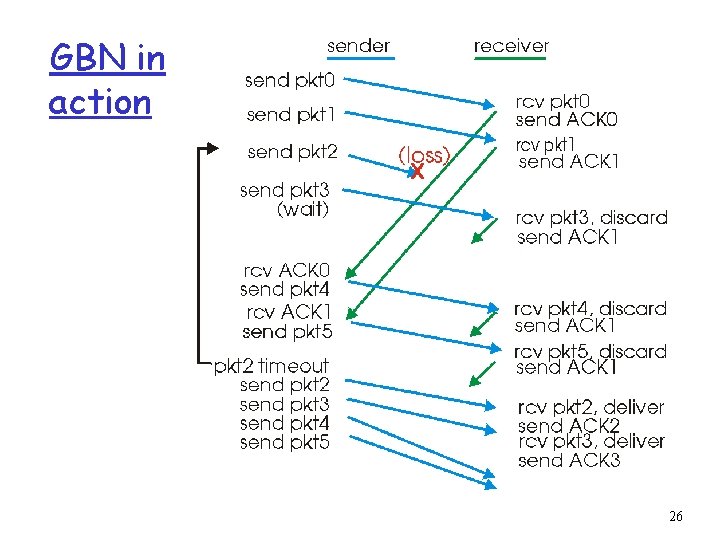
GBN in action 26
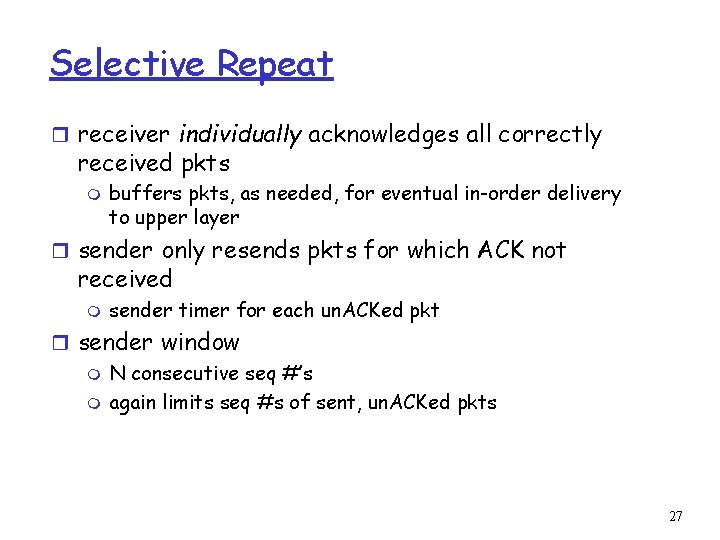
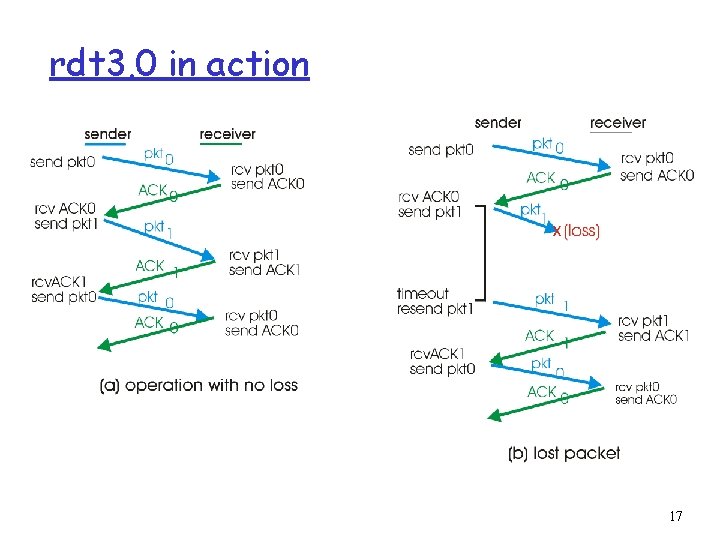
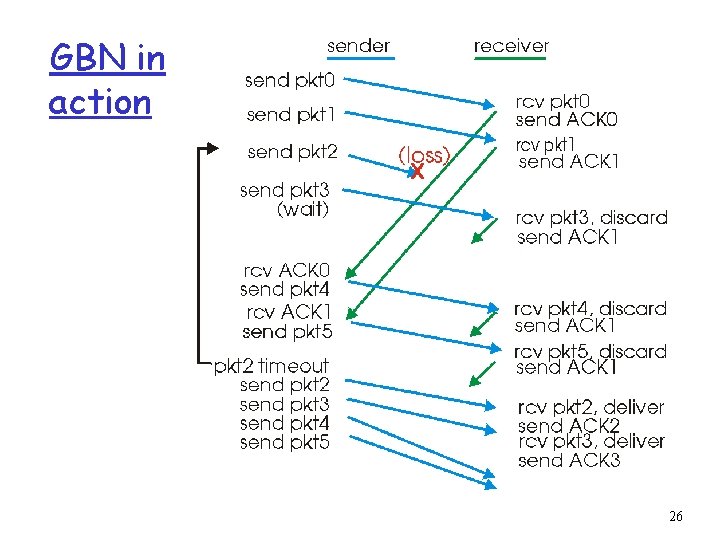
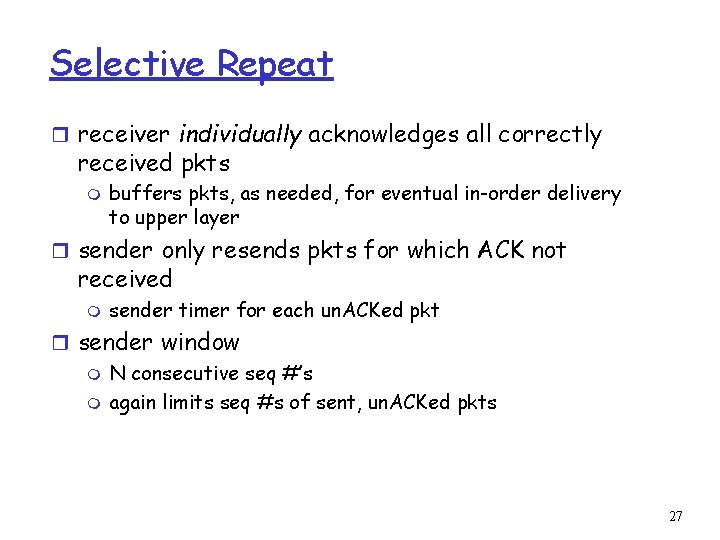
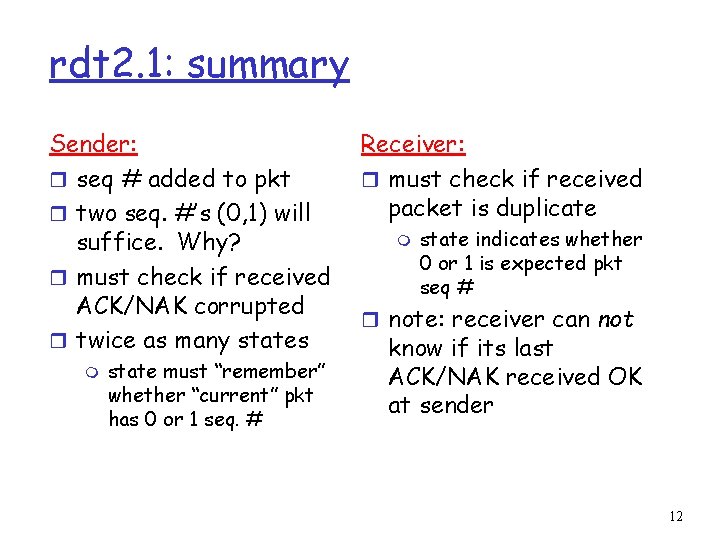
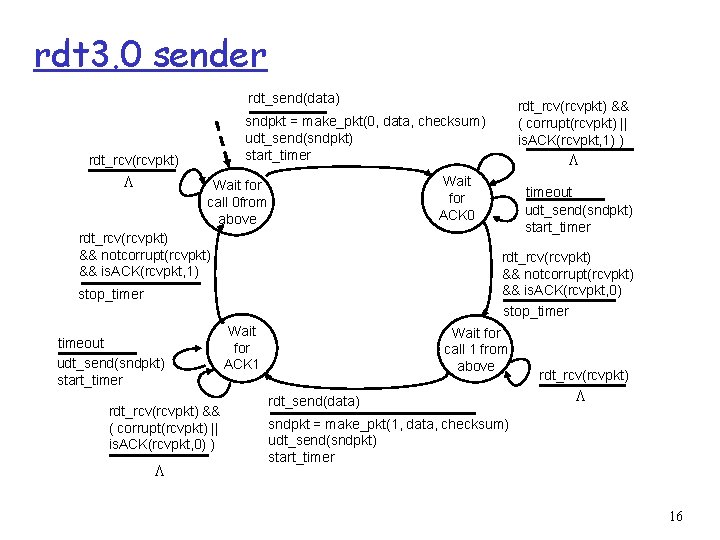
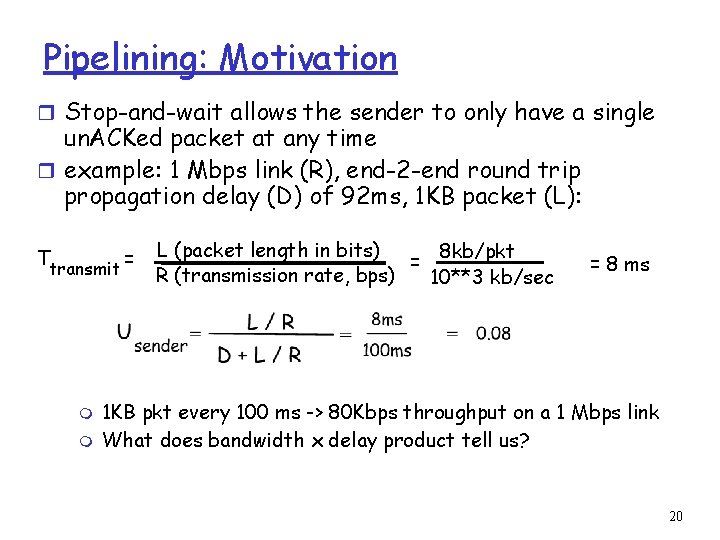
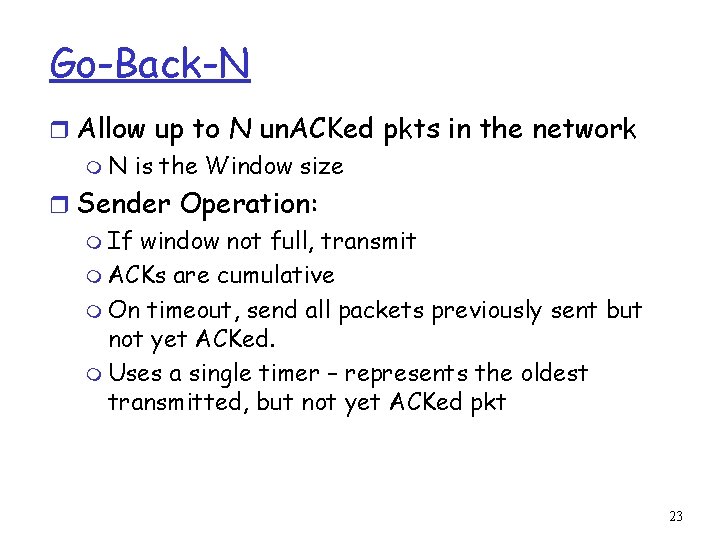
Selective Repeat r receiver individually acknowledges all correctly received pkts m buffers pkts, as needed, for eventual in-order delivery to upper layer r sender only resends pkts for which ACK not received m sender timer for each un. ACKed pkt r sender window m N consecutive seq #’s m again limits seq #s of sent, un. ACKed pkts 27
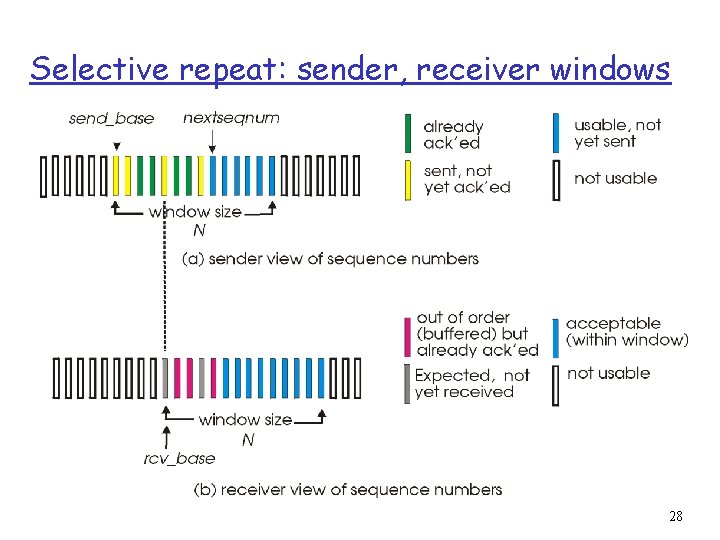
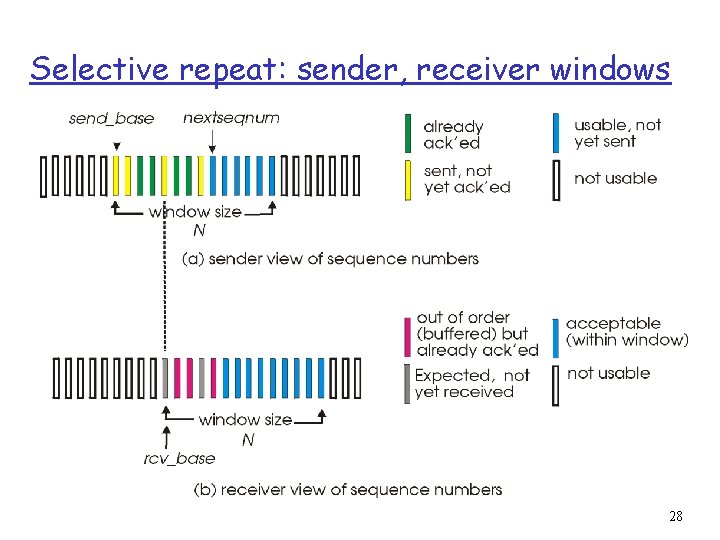
Selective repeat: sender, receiver windows 28
![Selective repeat sender data from above receiver pkt n in rcvbase rcvbaseN1 r Selective repeat sender data from above : receiver pkt n in [rcvbase, rcvbase+N-1] r](https://slidetodoc.com/presentation_image_h2/41b60a56d3512ad5162886eacd109dfc/image-29.jpg)
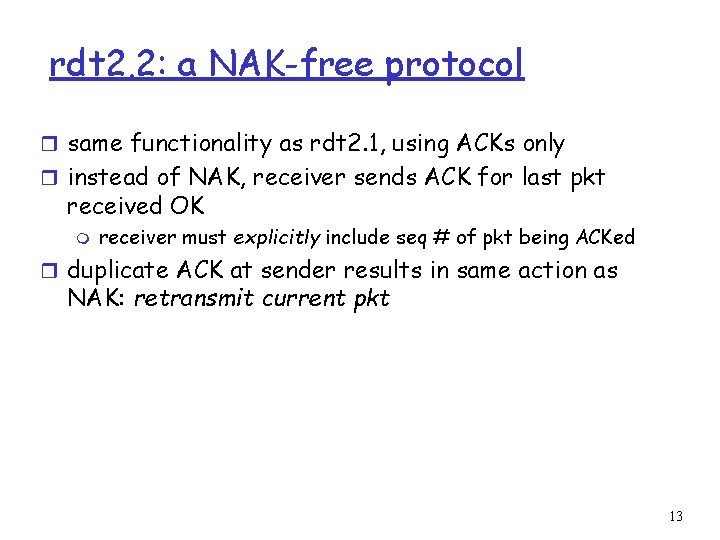
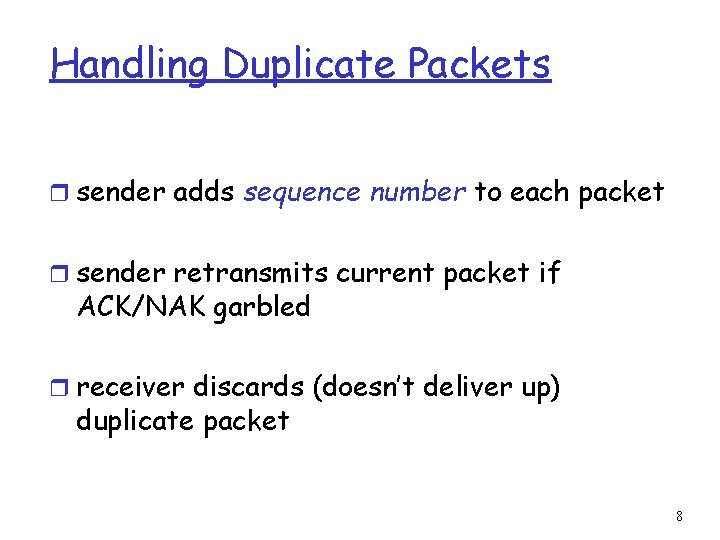
Selective repeat sender data from above : receiver pkt n in [rcvbase, rcvbase+N-1] r if next available seq # in r send ACK(n) timeout(n): r in-order: deliver (also window, send pkt r resend pkt n, restart timer ACK(n) in [sendbase, sendbase+N]: r mark pkt n as received r if n smallest un. ACKed pkt, advance window base to next un. ACKed seq # r out-of-order: buffer deliver buffered, in-order pkts), advance window to next not-yet-received pkt n in [rcvbase-N, rcvbase-1] r ACK(n) otherwise: r ignore 29
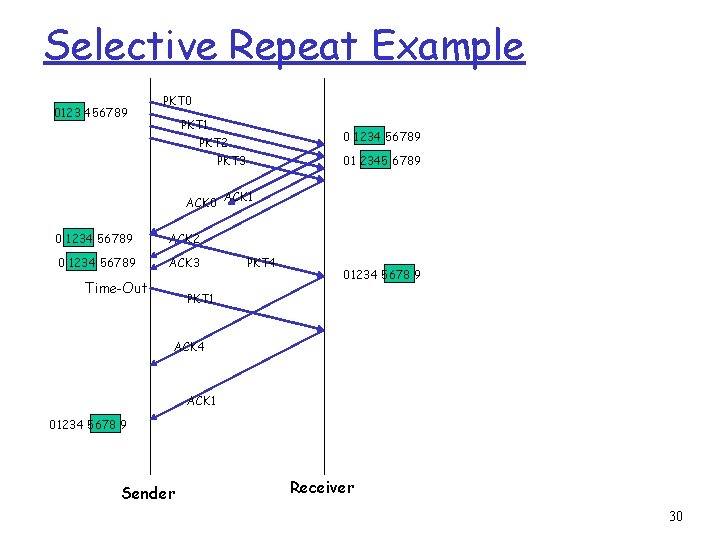
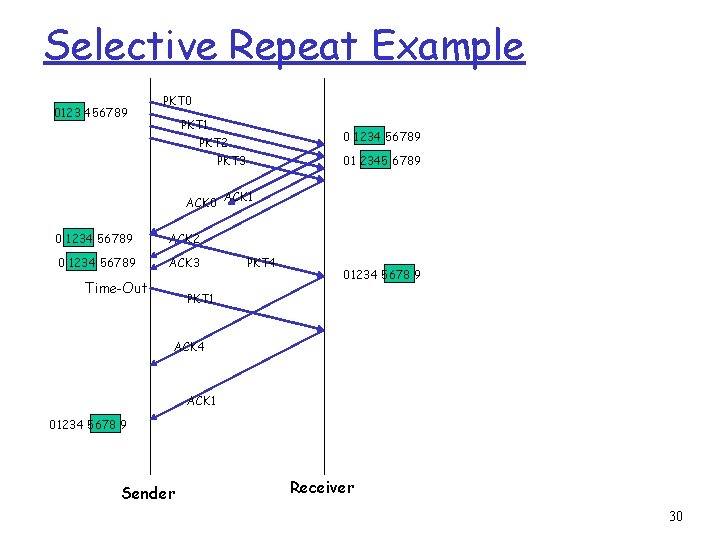
Selective Repeat Example 0123 456789 PKT 0 PKT 1 0 1234 56789 PKT 2 PKT 3 01 2345 6789 ACK 0 ACK 1 0 1234 56789 ACK 2 0 1234 56789 ACK 3 Time-Out PKT 4 01234 5678 9 PKT 1 ACK 4 ACK 1 01234 5678 9 Sender Receiver 30
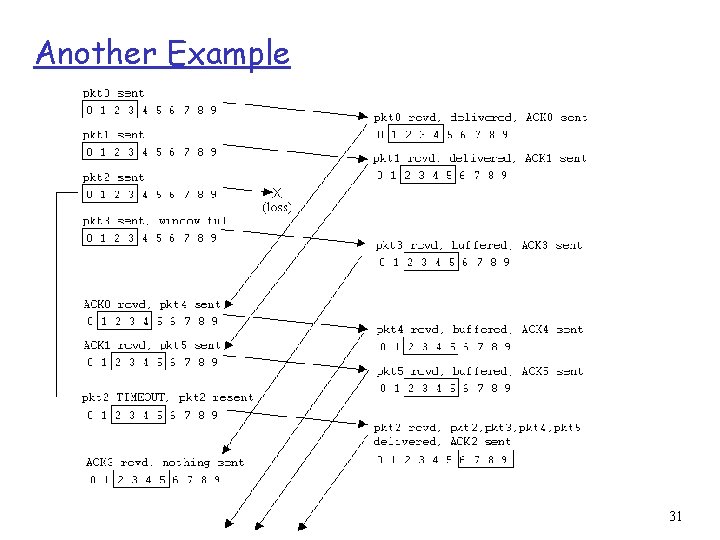
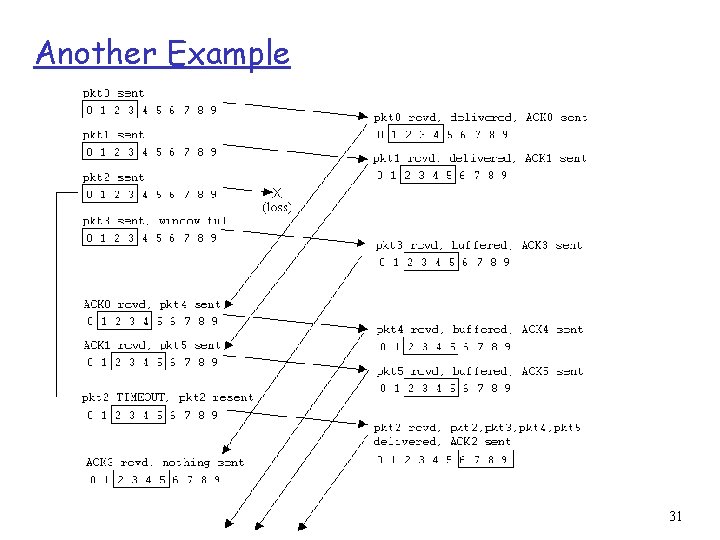
Another Example 31
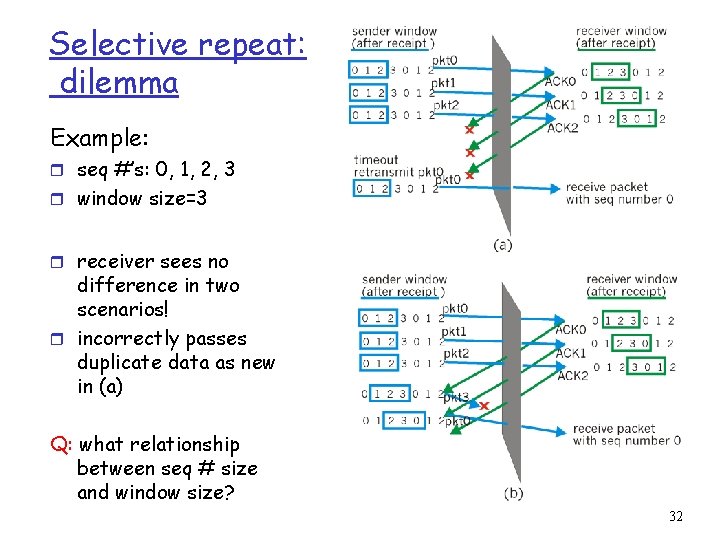
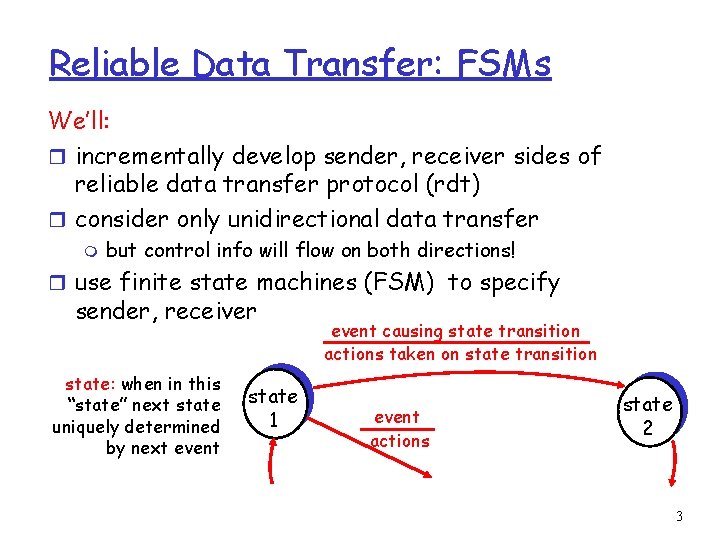
Selective repeat: dilemma Example: r seq #’s: 0, 1, 2, 3 r window size=3 r receiver sees no difference in two scenarios! r incorrectly passes duplicate data as new in (a) Q: what relationship between seq # size and window size? 32