Traffic Grooming for Survivable WDM Networks Shared Protection
Traffic Grooming for Survivable WDM Networks – Shared Protection Kevin Su University of Texas at San Antonio 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 1
Outline • Introduction • Motivation • System Model – Grooming Node Architecture – Network Model • Proposed Schemes – Protection-at-lightpath (PAL) level – Mixed protection-at-connection (MPAC) level – Separated protection-at-connection (SPAC) level • Heuristic Algorithms • Performance Evaluation 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 2

Introduction • WDM: stands for wavelength division multiplexing, it is a technology that divides the bandwidth of an optical fiber into many non-overlapping wavelengths, so that multiple communication channels can operate simultaneously on different wavelengths. – Increases the transmission capacity of optical fibers. – Allows simultaneously transmission of multiple wavelengths within a single fiber. – Up to 320 wavelengths per fiber; per wavelength, 10 Gb/s, STS-192 (OC-192), today; expected to grow to 40 Gb/s, STS-768(OC-768), soon. 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 3
Introduction • Traffic Grooming: refers to problem of efficiently packing lowspeed connections onto high-capacity lightpaths to better utilize network resourses. – The bandwidth requirement of a typical connection request is between STS-1 (51. 84 Mb/s) and STS-192(full wavelength) • Protection: is a proactive procedure in which spare capacity is reserved during connection setup. – Working path: a path that carries traffic during normal operation – Backup path: a path over which the connection is rerouted when a working path fails – Single Failure (single-fiber failure, single-node failure) ---0 -----0 ------0 --- – Dedicated Protection – Shared Protection 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 4
Introduction 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 5
Motivation • Survivable Traffic Grooming – Efficiently utilize the network resources (traffic grooming) – A failure of a network element can cause the failure of several lightpaths, thereby leading to large data and revenue loss (protection) • Static Case • Dynamic Case 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 6
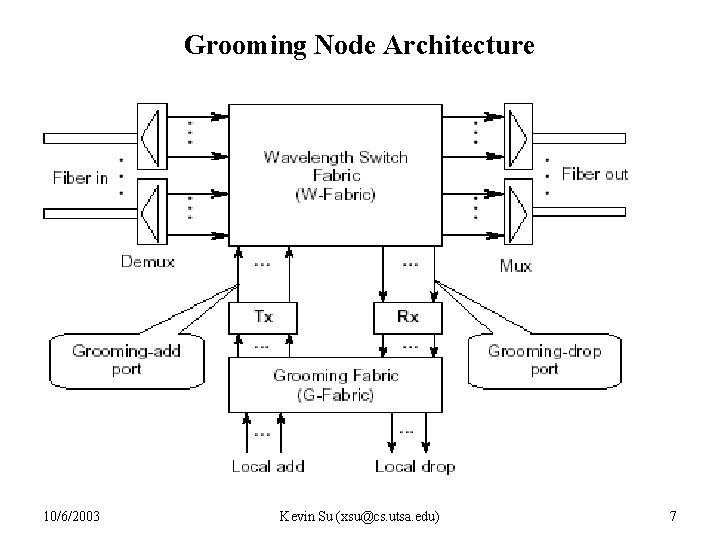
Grooming Node Architecture 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 7
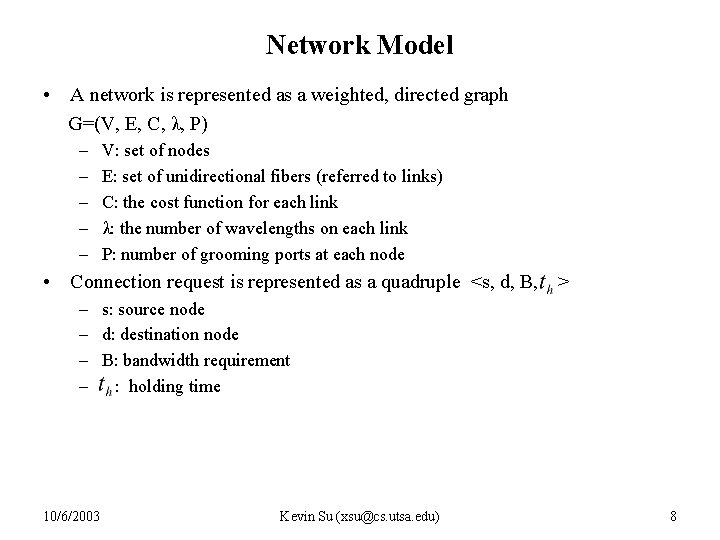
Network Model • A network is represented as a weighted, directed graph G=(V, E, C, λ, P) – – – V: set of nodes E: set of unidirectional fibers (referred to links) C: the cost function for each link λ: the number of wavelengths on each link P: number of grooming ports at each node • Connection request is represented as a quadruple <s, d, B, > – s: source node – d: destination node – B: bandwidth requirement – : holding time 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 8
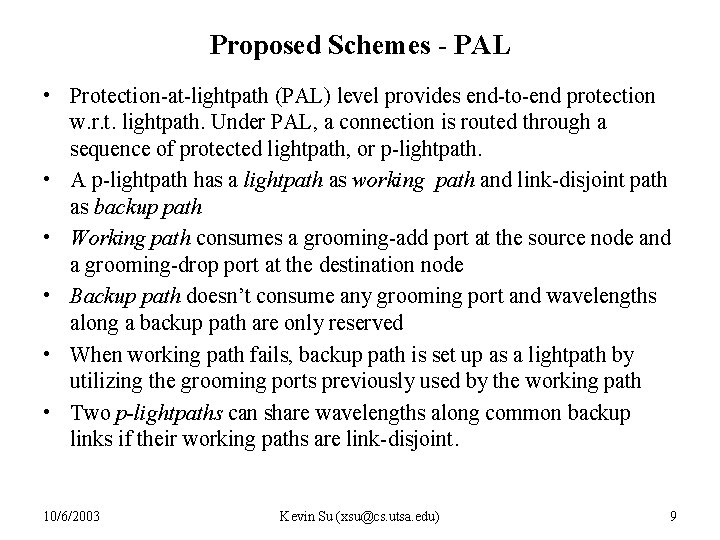
Proposed Schemes - PAL • Protection-at-lightpath (PAL) level provides end-to-end protection w. r. t. lightpath. Under PAL, a connection is routed through a sequence of protected lightpath, or p-lightpath. • A p-lightpath has a lightpath as working path and link-disjoint path as backup path • Working path consumes a grooming-add port at the source node and a grooming-drop port at the destination node • Backup path doesn’t consume any grooming port and wavelengths along a backup path are only reserved • When working path fails, backup path is set up as a lightpath by utilizing the grooming ports previously used by the working path • Two p-lightpaths can share wavelengths along common backup links if their working paths are link-disjoint. 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 9
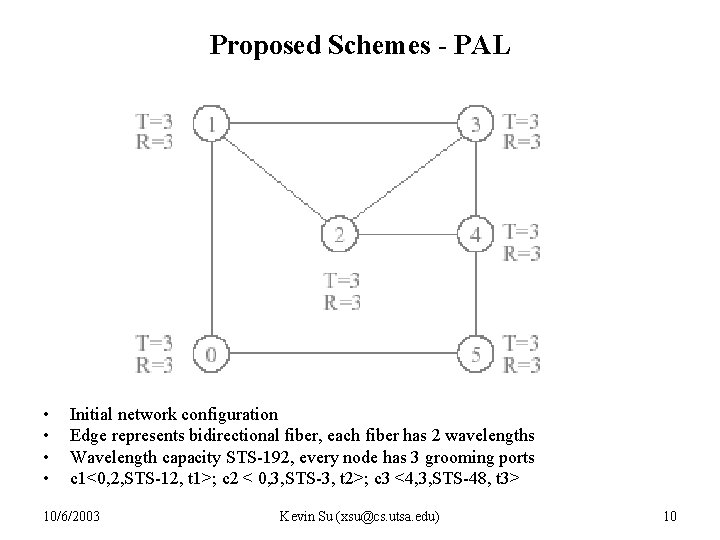
Proposed Schemes - PAL • • Initial network configuration Edge represents bidirectional fiber, each fiber has 2 wavelengths Wavelength capacity STS-192, every node has 3 grooming ports c 1<0, 2, STS-12, t 1>; c 2 < 0, 3, STS-3, t 2>; c 3 <4, 3, STS-48, t 3> 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 10
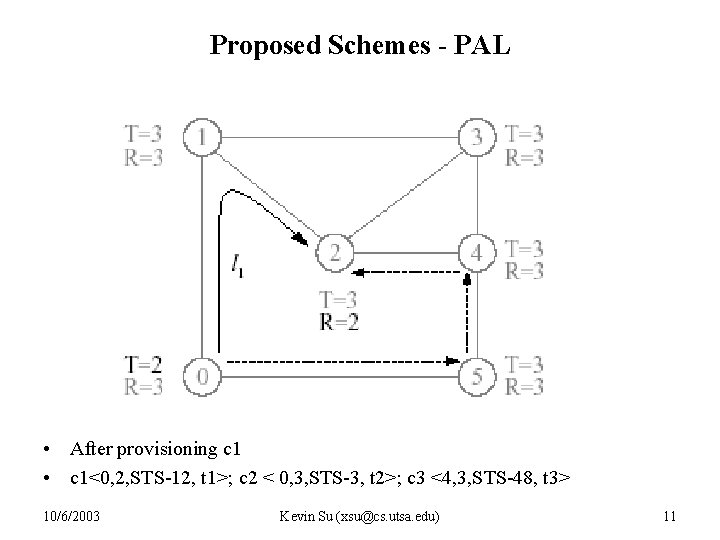
Proposed Schemes - PAL • After provisioning c 1 • c 1<0, 2, STS-12, t 1>; c 2 < 0, 3, STS-3, t 2>; c 3 <4, 3, STS-48, t 3> 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 11

Proposed Schemes - PAL • After provisioning c 2 • c 1<0, 2, STS-12, t 1>; c 2 < 0, 3, STS-3, t 2>; c 3 <4, 3, STS-48, t 3> 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 12
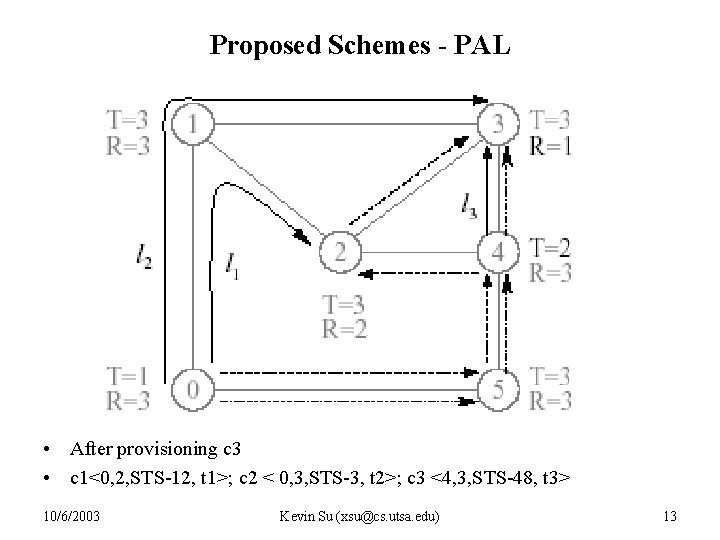
Proposed Schemes - PAL • After provisioning c 3 • c 1<0, 2, STS-12, t 1>; c 2 < 0, 3, STS-3, t 2>; c 3 <4, 3, STS-48, t 3> 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 13
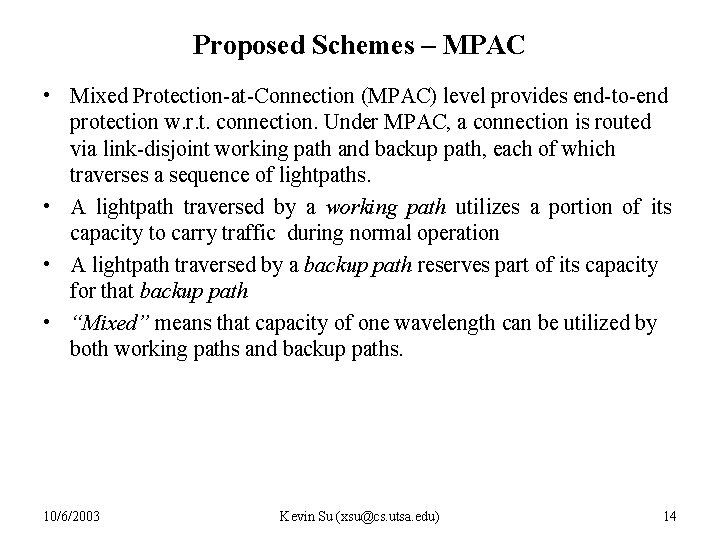
Proposed Schemes – MPAC • Mixed Protection-at-Connection (MPAC) level provides end-to-end protection w. r. t. connection. Under MPAC, a connection is routed via link-disjoint working path and backup path, each of which traverses a sequence of lightpaths. • A lightpath traversed by a working path utilizes a portion of its capacity to carry traffic during normal operation • A lightpath traversed by a backup path reserves part of its capacity for that backup path • “Mixed” means that capacity of one wavelength can be utilized by both working paths and backup paths. 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 14
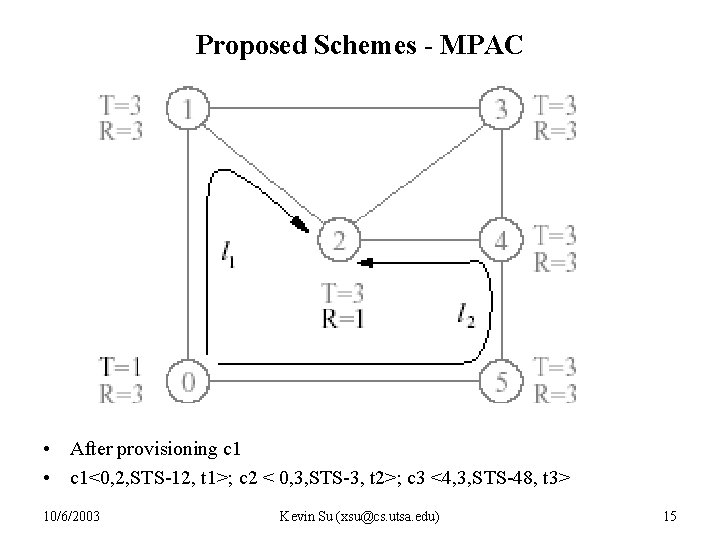
Proposed Schemes - MPAC • After provisioning c 1 • c 1<0, 2, STS-12, t 1>; c 2 < 0, 3, STS-3, t 2>; c 3 <4, 3, STS-48, t 3> 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 15
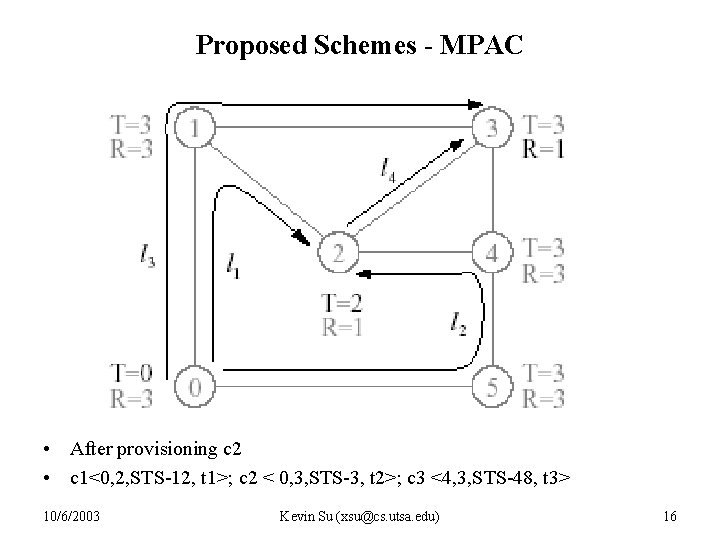
Proposed Schemes - MPAC • After provisioning c 2 • c 1<0, 2, STS-12, t 1>; c 2 < 0, 3, STS-3, t 2>; c 3 <4, 3, STS-48, t 3> 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 16

Proposed Schemes - MPAC • After provisioning c 3 • c 1<0, 2, STS-12, t 1>; c 2 < 0, 3, STS-3, t 2>; c 3 <4, 3, STS-48, t 3> 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 17
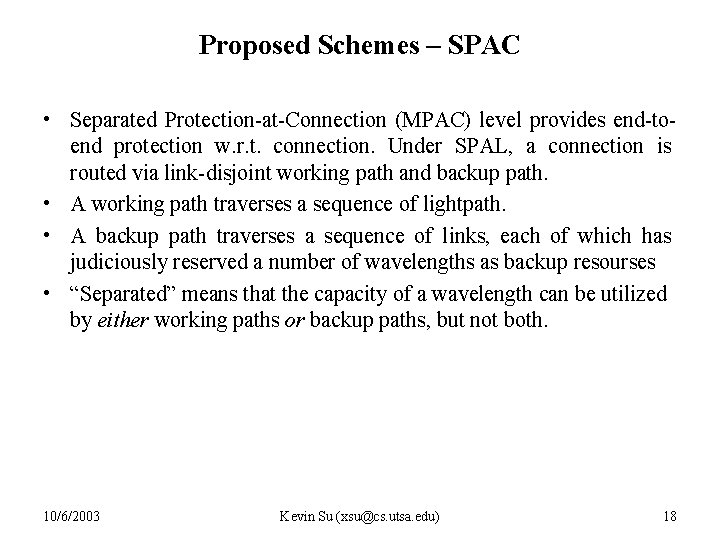
Proposed Schemes – SPAC • Separated Protection-at-Connection (MPAC) level provides end-toend protection w. r. t. connection. Under SPAL, a connection is routed via link-disjoint working path and backup path. • A working path traverses a sequence of lightpath. • A backup path traverses a sequence of links, each of which has judiciously reserved a number of wavelengths as backup resourses • “Separated” means that the capacity of a wavelength can be utilized by either working paths or backup paths, but not both. 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 18
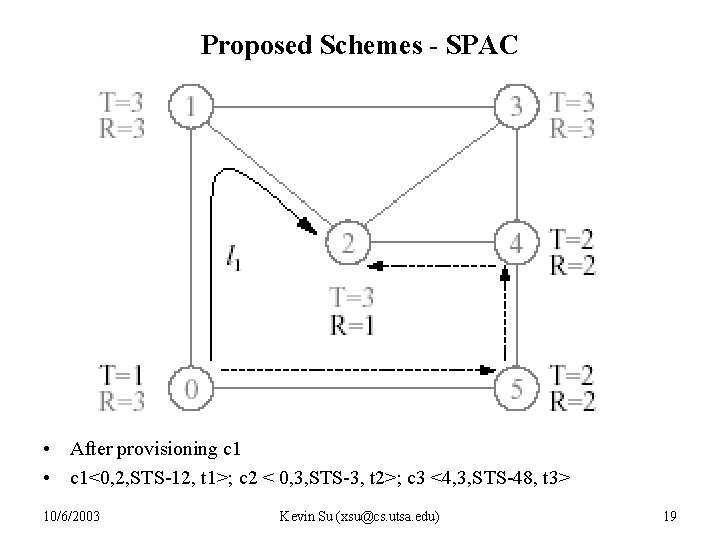
Proposed Schemes - SPAC • After provisioning c 1 • c 1<0, 2, STS-12, t 1>; c 2 < 0, 3, STS-3, t 2>; c 3 <4, 3, STS-48, t 3> 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 19
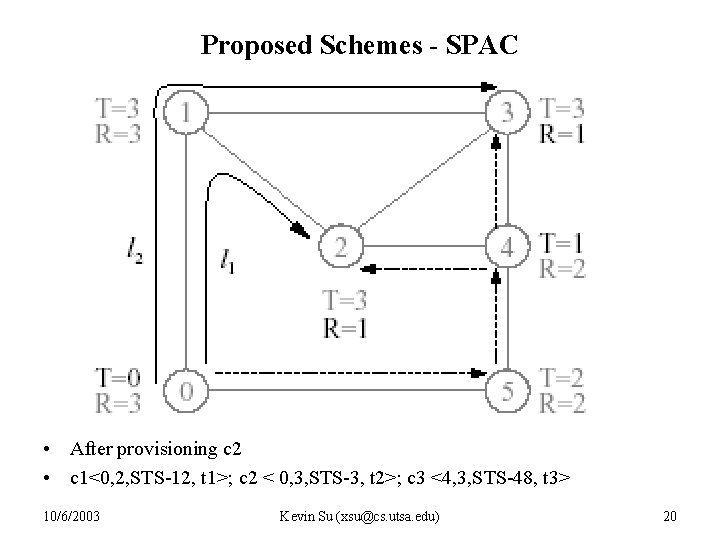
Proposed Schemes - SPAC • After provisioning c 2 • c 1<0, 2, STS-12, t 1>; c 2 < 0, 3, STS-3, t 2>; c 3 <4, 3, STS-48, t 3> 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 20
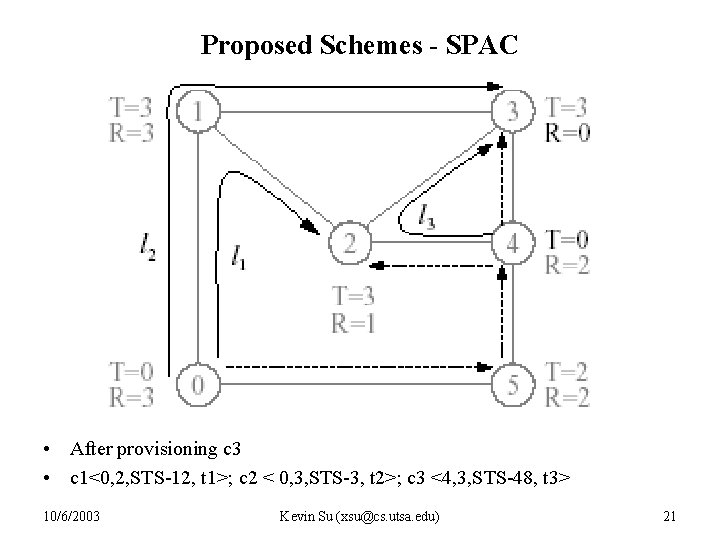
Proposed Schemes - SPAC • After provisioning c 3 • c 1<0, 2, STS-12, t 1>; c 2 < 0, 3, STS-3, t 2>; c 3 <4, 3, STS-48, t 3> 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 21

Proposed Schemes 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 22

Heuristic Algorithm • It is NP-complete to provision a connection request with shared protection. • The Author proposed heuristic for MPAC, SPAC, PAL • MPAC – Backup-sharing measuring Every lightpath is associated with a conflict set to identify the sharing potential between paths. conflict set for lightpath can be represented as an integer set { } where represents the amount of traffic that will be rerouted on lightpath when link e fails. The amount of backup capacity reserved on lightpath is thus – Route computation • Enumerates K candidate working paths • For each candidate working path, computes a disjoint minimal-cost path as backup path based on some cost function • Selects the path pair of minimal cost 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 23
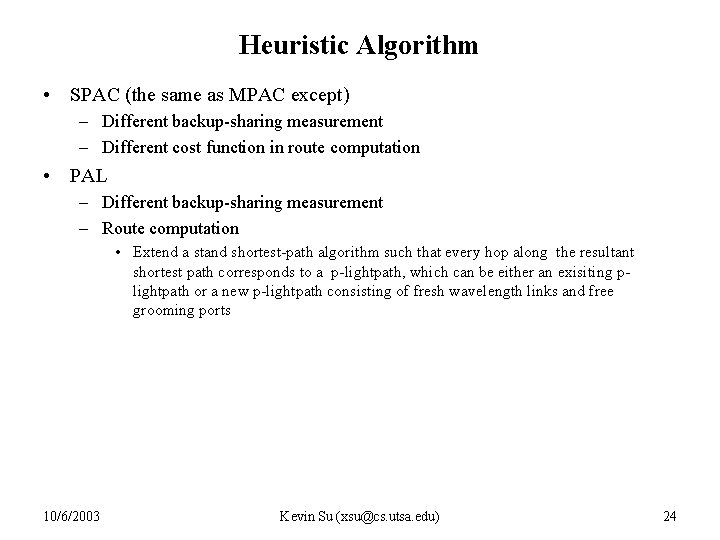
Heuristic Algorithm • SPAC (the same as MPAC except) – Different backup-sharing measurement – Different cost function in route computation • PAL – Different backup-sharing measurement – Route computation • Extend a stand shortest-path algorithm such that every hop along the resultant shortest path corresponds to a p-lightpath, which can be either an exisiting plightpath or a new p-lightpath consisting of fresh wavelength links and free grooming ports 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 24
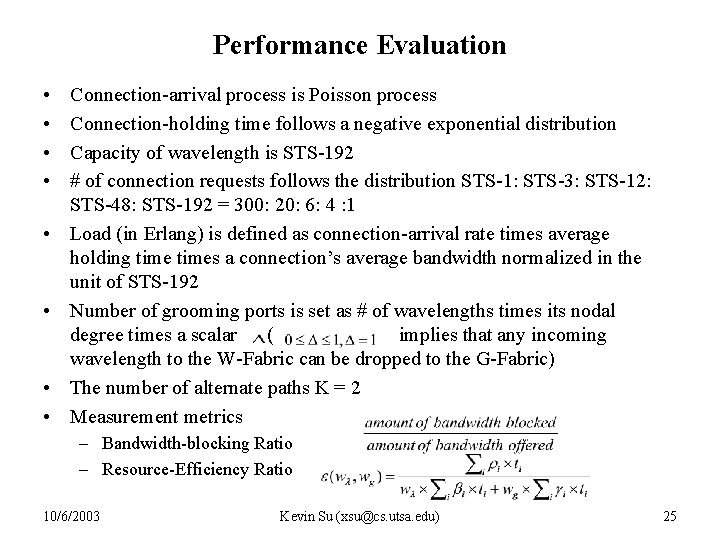
Performance Evaluation • • Connection-arrival process is Poisson process Connection-holding time follows a negative exponential distribution Capacity of wavelength is STS-192 # of connection requests follows the distribution STS-1: STS-3: STS-12: STS-48: STS-192 = 300: 20: 6: 4 : 1 Load (in Erlang) is defined as connection-arrival rate times average holding times a connection’s average bandwidth normalized in the unit of STS-192 Number of grooming ports is set as # of wavelengths times its nodal degree times a scalar ( implies that any incoming wavelength to the W-Fabric can be dropped to the G-Fabric) The number of alternate paths K = 2 Measurement metrics – Bandwidth-blocking Ratio – Resource-Efficiency Ratio 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 25
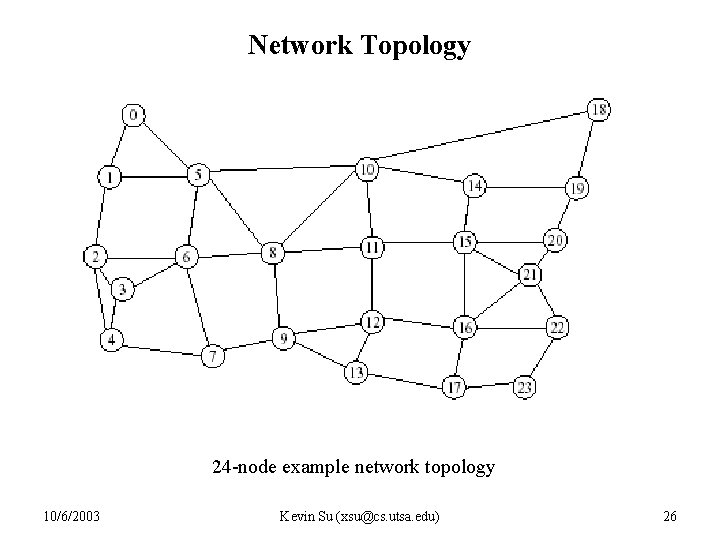
Network Topology 24 -node example network topology 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 26
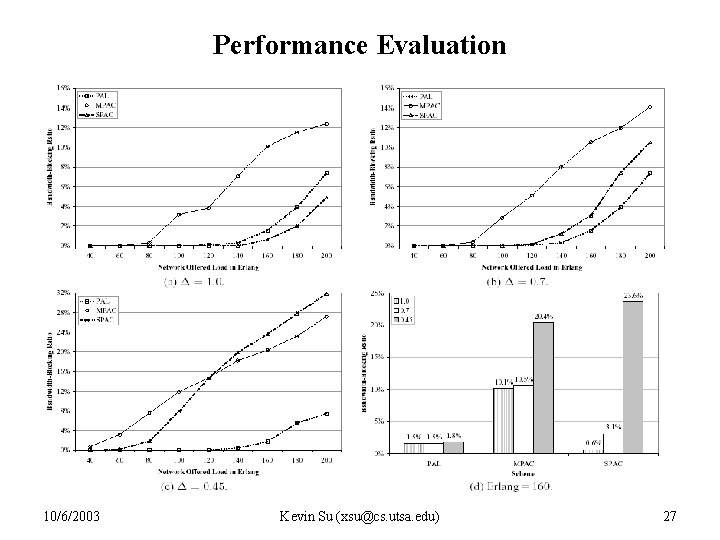
Performance Evaluation 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 27
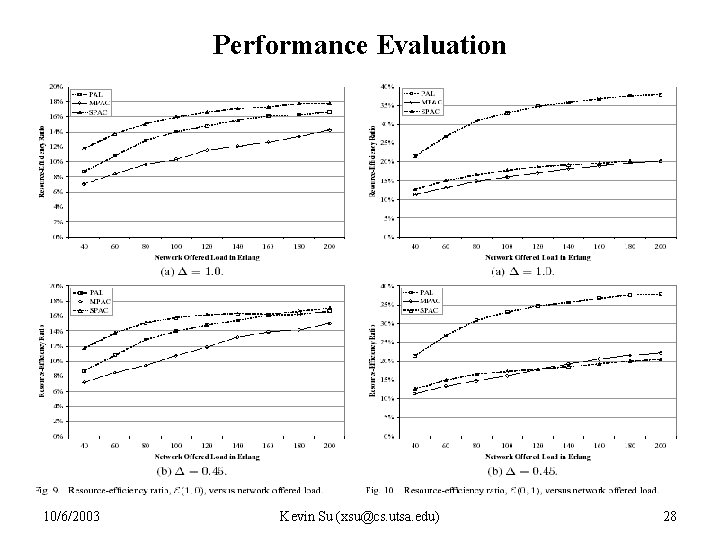
Performance Evaluation 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 28
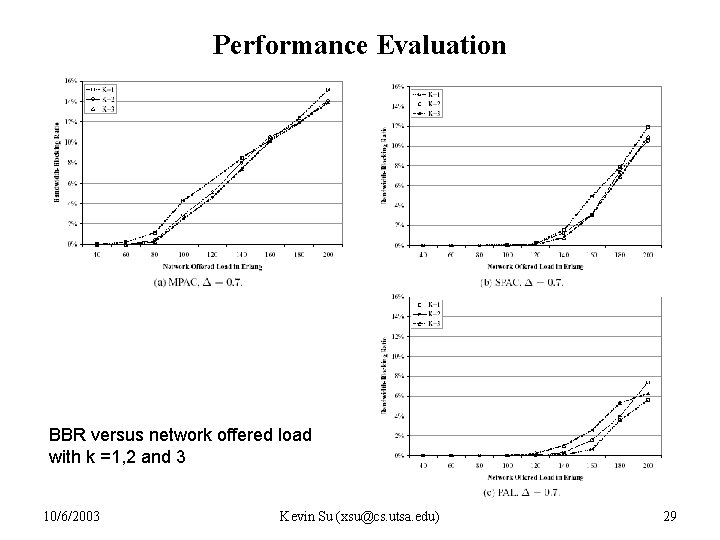
Performance Evaluation BBR versus network offered load with k =1, 2 and 3 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 29
Conclusion and Future Work • Investigate the survivable traffic-grooming problem in dynamic case – PAL, MPAC, SPAC – Findings: • It is beneficial to groom working paths and backup paths separately as in PAL and SPAC • Separately protecting each individual connection yields the best performance when the number of ports is suffcient • Protecting each specific lightpath achieves the best performance when the # of grooming ports is moderate or small • Future work – Considering the residual connection holding time 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 30
References • C. Ou, K. Zhu, H. Zang, L. H. Sahasrabuddhe, and B. Mukherjee. “Traffic Grooming for Survivable WDM Networks – Shared Protection”. Accepted to IEEE Journal of Selected Area in Communication 2004. • H. Zhu, H. Zang, K. Zhu, and B. Mukherjee, “A novel, generic graph model for traffic grooming in heterogeneous WDM mesh networks” IEEE/ACM Trans. Neworking, vol. 11 pp. 285 -299, Apr. 2003 10/6/2003 Kevin Su (xsu@cs. utsa. edu) 31
- Slides: 31