Tracing Cyber Attacks Areej AlBataineh 372021 Tracing Cyber
Tracing Cyber Attacks Areej Al-Bataineh 3/7/2021 Tracing Cyber Attacks 1
Tracing cyber attacks from the practical perspective Zhiqiang Gao and Nirwan Ansari Communications Magazine, IEEE May 2005 http: //www. comsoc. org/tutorials/Ansari 3/7/2021 Tracing Cyber Attacks 2
Outline l l l l Introduction IP Traceback Objective Classification of IP Traceback Schemes Evaluation of Representative Schemes Conclusion Future Work 3/7/2021 Tracing Cyber Attacks 3
Introduction l l Denial of service (Do. S/DDo. S) attacks Disrupt legitimate access Costs victims financial and productivity loss Why Easy to conduct? l l l Prevalence of attack tools Stateless nature of Internet Address Spoofing (Anonymous Attacks) l l 3/7/2021 Gain illegitimate access Hide attack source Tracing Cyber Attacks 4
Intrusion Countermeasure l Prevention l l l Detection Mitigation l l Source/Network/Victim-based Rate limiting/statistical/path-based Response IP Traceback 3/7/2021 Tracing Cyber Attacks 5
IP Traceback l Objective l l Locate the actual source of attack packets Difficult l l Source Address Spoofing Many attack sources (DDo. S) l l l 3/7/2021 Host in stepping stone chain Reflector Zombie Tracing Cyber Attacks 6
Objectives l Grasp global view l l Classify Traceback schemes Select typical schemes Focus on practicality Foundation for l l 3/7/2021 Developing efficient schemes And Effective schemes Tracing Cyber Attacks 7
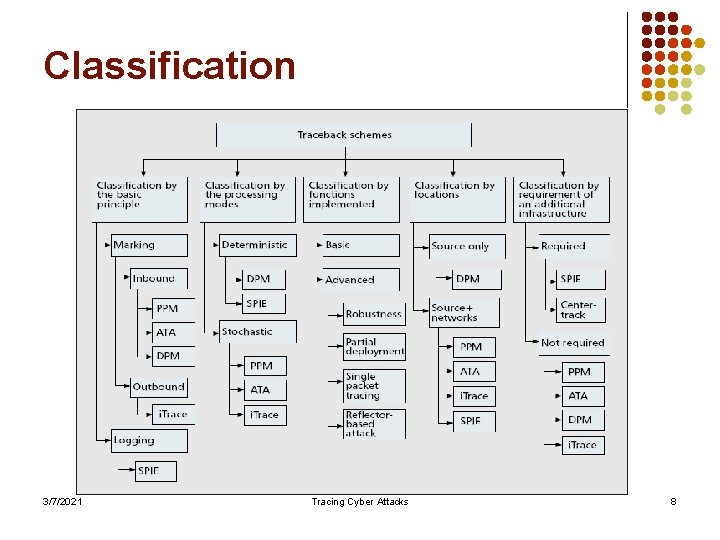
Classification 3/7/2021 Tracing Cyber Attacks 8
Evaluation Metrics l l Based on Practicality Minimum number of packets required for path reconstruction l l The computational overhead l l Good design minimize it Effectiveness under partial deployment l l The less the better Deployment implies more cost Robustness l 3/7/2021 The ability to perform tracing reliably under adverse conditions Tracing Cyber Attacks 9
Representative Schemes l Probabilisic Packet Marking (PPM) Savage et al (2001) l ICMP traceback (i. Trace) Bellovin (2000) l Source Path Isolation Engine (SPIE) Snoeren et al (2002) l Algebraic-bases Traceback Approach (ATA) Dean et al (2002) l Determinnistic Packet Marking (DPM) Belenky and Ansari (2003) l Overlay-based solution (Center-Track) Stone (2000) 3/7/2021 Tracing Cyber Attacks 10
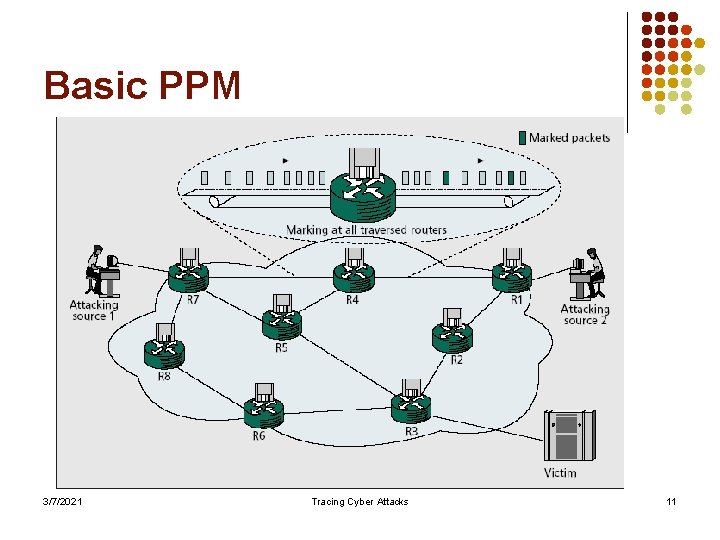
Basic PPM 3/7/2021 Tracing Cyber Attacks 11
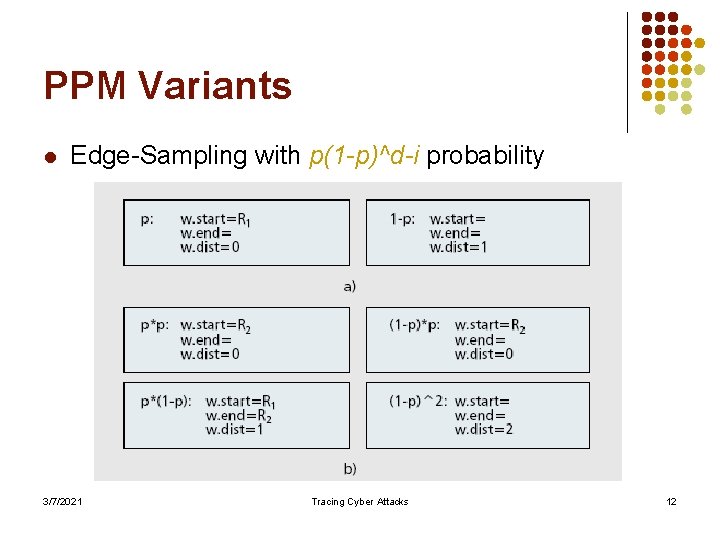
PPM Variants l Edge-Sampling with p(1 -p)^d-i probability 3/7/2021 Tracing Cyber Attacks 12
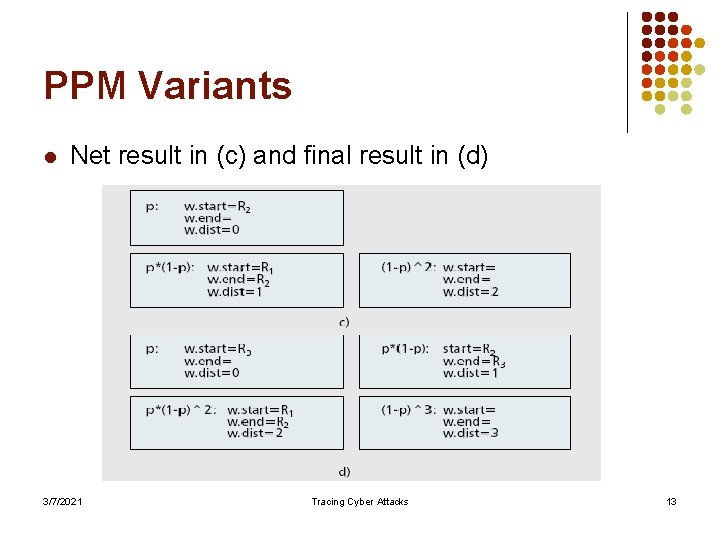
PPM Variants l Net result in (c) and final result in (d) 3/7/2021 Tracing Cyber Attacks 13
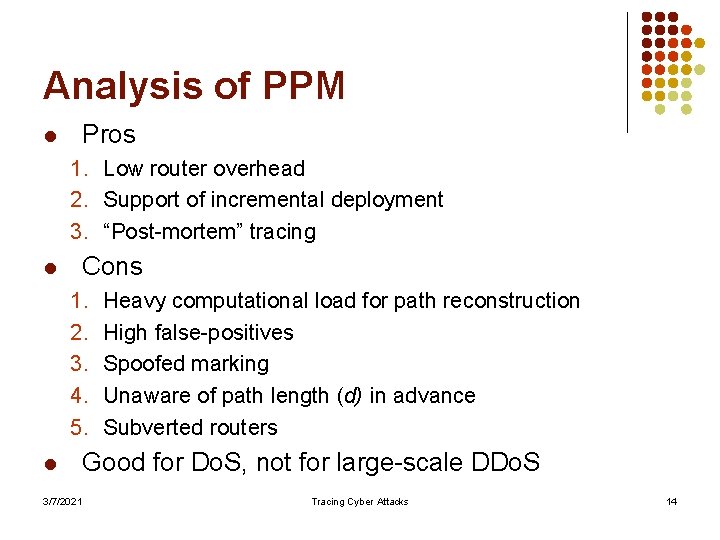
Analysis of PPM Pros l 1. Low router overhead 2. Support of incremental deployment 3. “Post-mortem” tracing Cons l 1. 2. 3. 4. 5. l 3/7/2021 Heavy computational load for path reconstruction High false-positives Spoofed marking Unaware of path length (d) in advance Subverted routers Good for Do. S, not for large-scale DDo. S Tracing Cyber Attacks 14
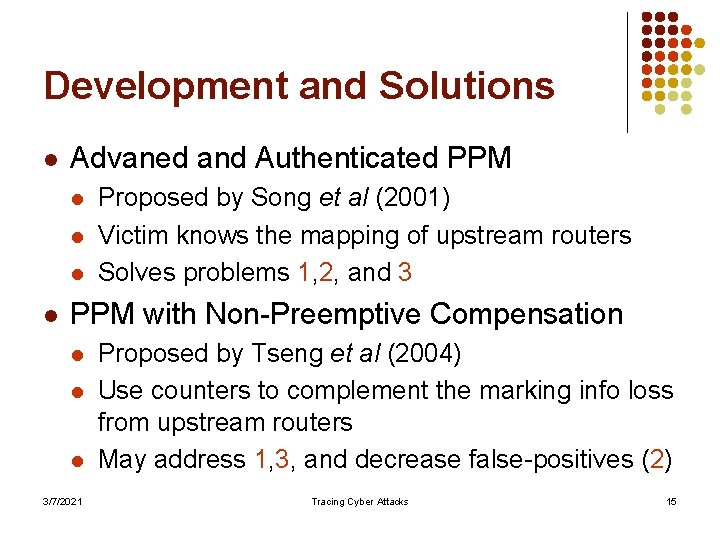
Development and Solutions l Advaned and Authenticated PPM l l Proposed by Song et al (2001) Victim knows the mapping of upstream routers Solves problems 1, 2, and 3 PPM with Non-Preemptive Compensation l l l 3/7/2021 Proposed by Tseng et al (2004) Use counters to complement the marking info loss from upstream routers May address 1, 3, and decrease false-positives (2) Tracing Cyber Attacks 15
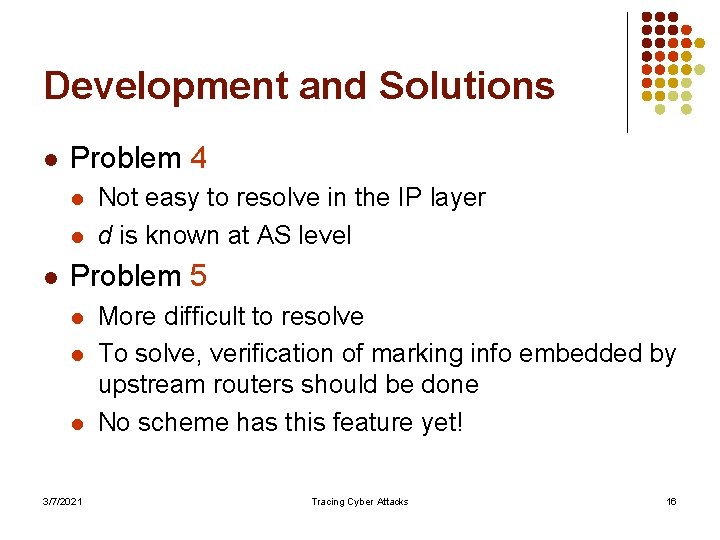
Development and Solutions l Problem 4 l l l Not easy to resolve in the IP layer d is known at AS level Problem 5 l l l 3/7/2021 More difficult to resolve To solve, verification of marking info embedded by upstream routers should be done No scheme has this feature yet! Tracing Cyber Attacks 16
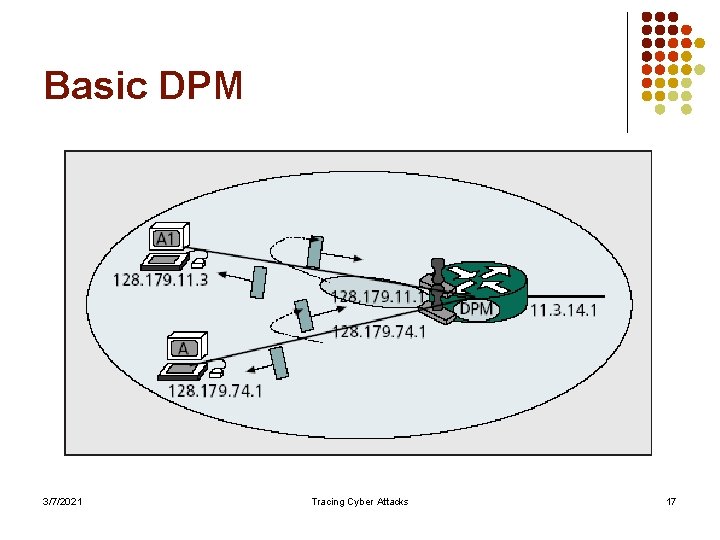
Basic DPM 3/7/2021 Tracing Cyber Attacks 17
Analysis of DPM l Pros l l l Effectively handles Do. S attack Path construction is simpler Cons l l 3/7/2021 High false positives for DDo. S attack Cannot identify the ingress router if attacker uses different source IP addresses for each packet Tracing Cyber Attacks 18
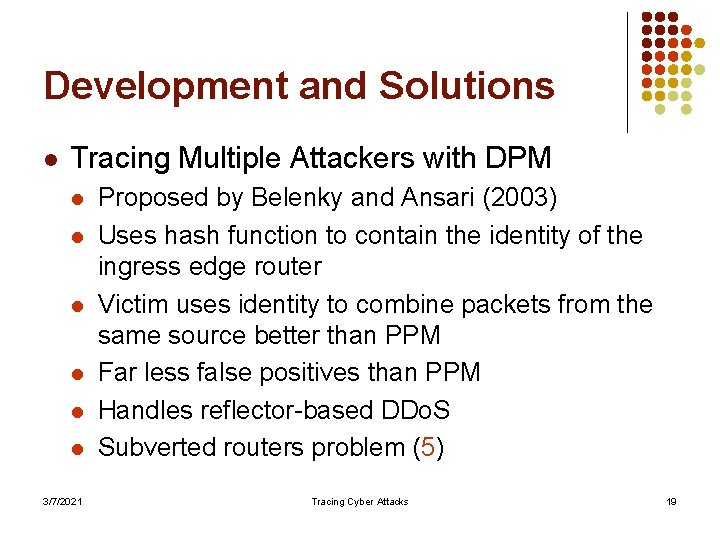
Development and Solutions l Tracing Multiple Attackers with DPM l l l 3/7/2021 Proposed by Belenky and Ansari (2003) Uses hash function to contain the identity of the ingress edge router Victim uses identity to combine packets from the same source better than PPM Far less false positives than PPM Handles reflector-based DDo. S Subverted routers problem (5) Tracing Cyber Attacks 19
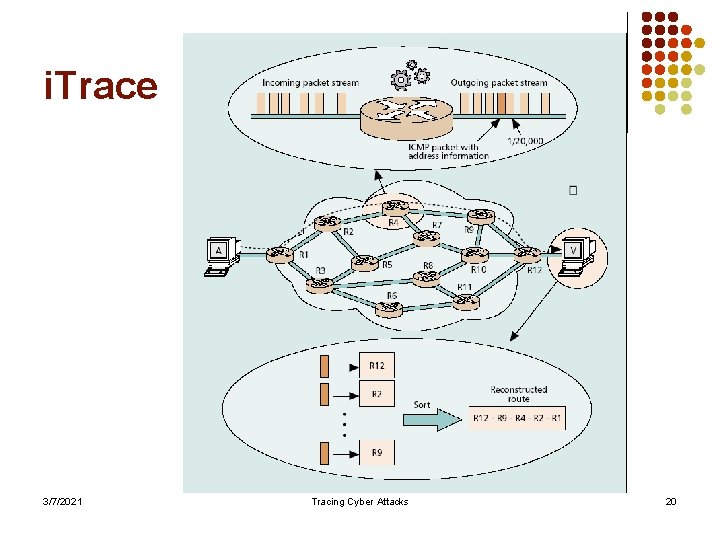
i. Trace 3/7/2021 Tracing Cyber Attacks 20
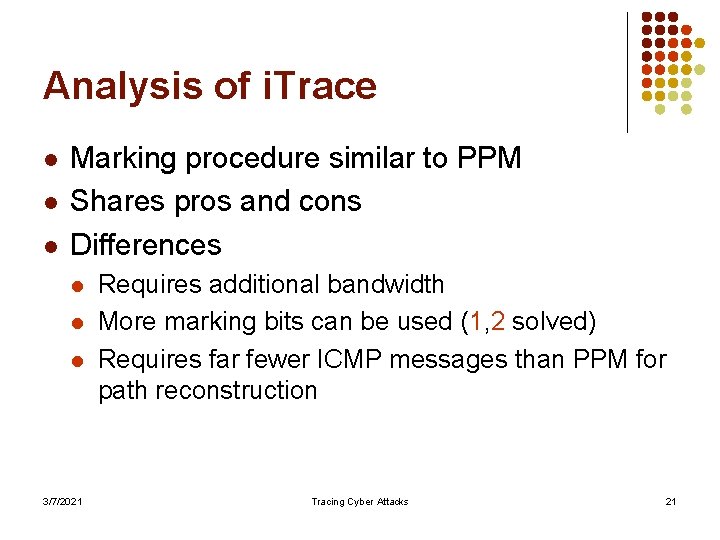
Analysis of i. Trace l l l Marking procedure similar to PPM Shares pros and cons Differences l l l 3/7/2021 Requires additional bandwidth More marking bits can be used (1, 2 solved) Requires far fewer ICMP messages than PPM for path reconstruction Tracing Cyber Attacks 21
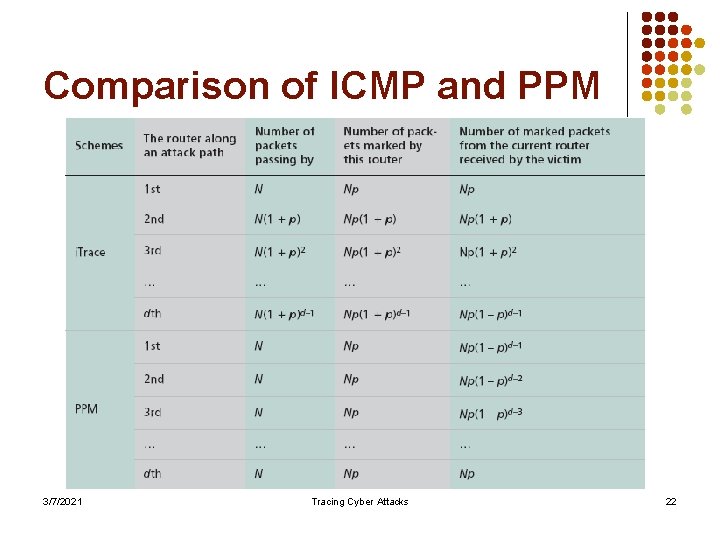
Comparison of ICMP and PPM 3/7/2021 Tracing Cyber Attacks 22
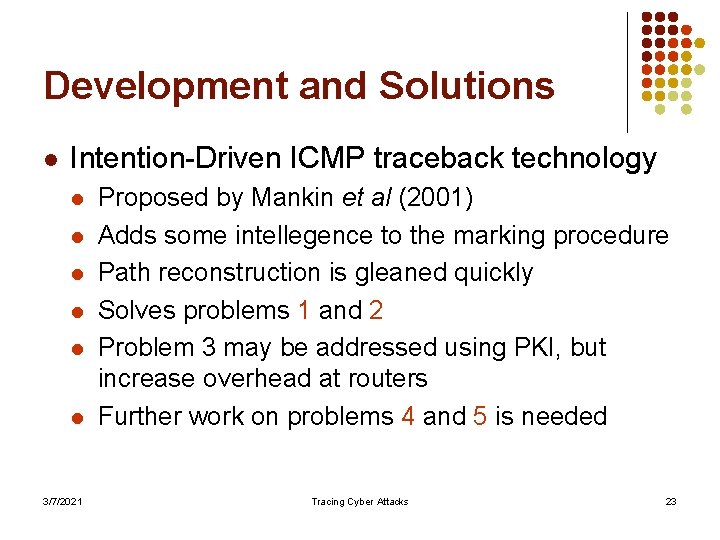
Development and Solutions l Intention-Driven ICMP traceback technology l l l 3/7/2021 Proposed by Mankin et al (2001) Adds some intellegence to the marking procedure Path reconstruction is gleaned quickly Solves problems 1 and 2 Problem 3 may be addressed using PKI, but increase overhead at routers Further work on problems 4 and 5 is needed Tracing Cyber Attacks 23
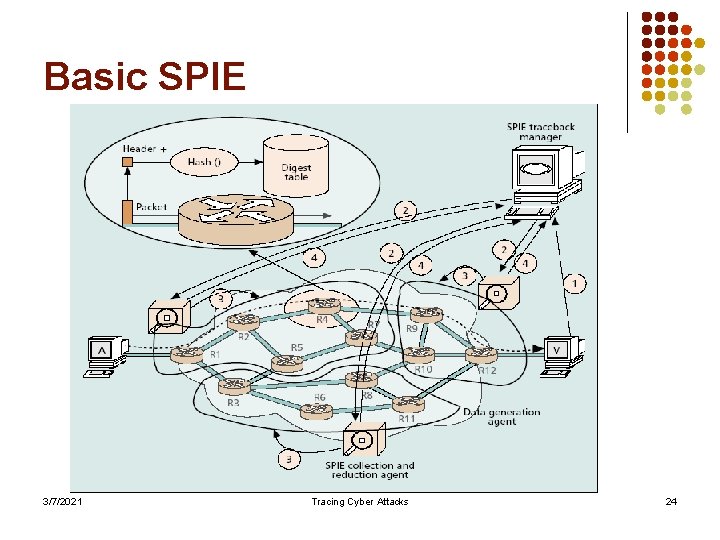
Basic SPIE 3/7/2021 Tracing Cyber Attacks 24
Analysis of SPIE l l Deterministic logging scheme Pros l l Cons l l Supports advanced functions like single packet tracing, transformed packet tracing (wireless) Requires additional infrastructure Incurs very heavy computational, management, and storage overhead Not scalable Limited applicability 3/7/2021 Tracing Cyber Attacks 25
Development and Solutions l Large-scale IP traceback l l 3/7/2021 Proposed by Li et al (2004) Logging scheme by sampling Construct attack tree by correlating samples Scale well for 5000 attack sources Tracing Cyber Attacks 26
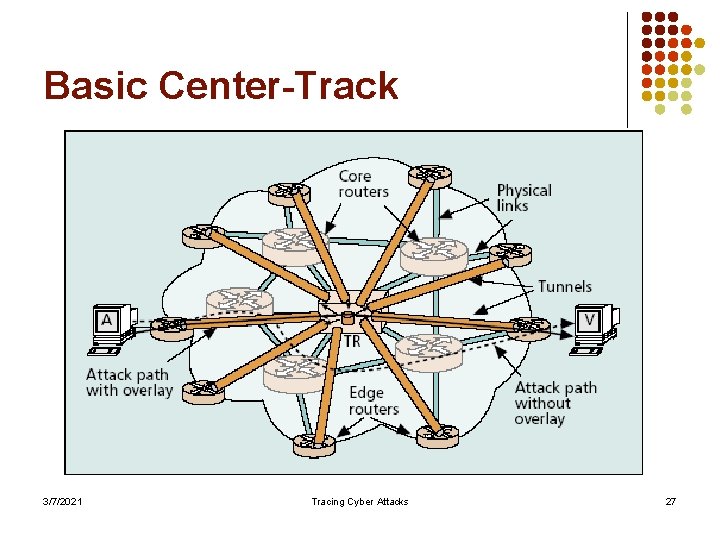
Basic Center-Track 3/7/2021 Tracing Cyber Attacks 27
Analysis of Center-Track l Pros l l Cons l l Handles DDo. S Enforces heavy management burden on the network Wears out network resources (bandwidth, processing capability) due to tunnels maintenance Not scalable Limited applicability 3/7/2021 Tracing Cyber Attacks 28
Development and Solutions l Secure Overlay Service (SOS) l l l 3/7/2021 Associative defensive method Proactive approach Employ intensive filtering and anonymity Effectively mitigate DDo. S attacks No false positives Low chance for compromised routers Tracing Cyber Attacks 29
Conclusion/Future Work l l l l IP Traceback technology is only the first step toward tackling Do. S/DDos attacks Ideal tracing scheme trade-offs Identify indirect sources of DDo. S Identify attackers who use stepping stone Integrating IDS with tracebak Automatic traceback Scalability 3/7/2021 Tracing Cyber Attacks 30
Future Work l l l Identify indirect sources of DDo. S Identify attackers who use stepping stone Integrating IDS with tracebak Automatic traceback Scalability 3/7/2021 Tracing Cyber Attacks 31
Questions? 3/7/2021 Tracing Cyber Attacks 32
- Slides: 32