Towards Continuous and Passive Authentication via Touch Biometrics
Towards Continuous and Passive Authentication via Touch Biometrics An Experimental Study on Smartphones Hui Xu, Yangfan Zhou, Michael R. Lyu The Chinese University of Hong Kong huixu@cuhk. hku. hk
1. Motivation
1. Motivation Scenario Who is the user ? physical access Malicious Attacker Personal Device Vision: A smartphone should exclusively serve its owner by recognizing its current user.
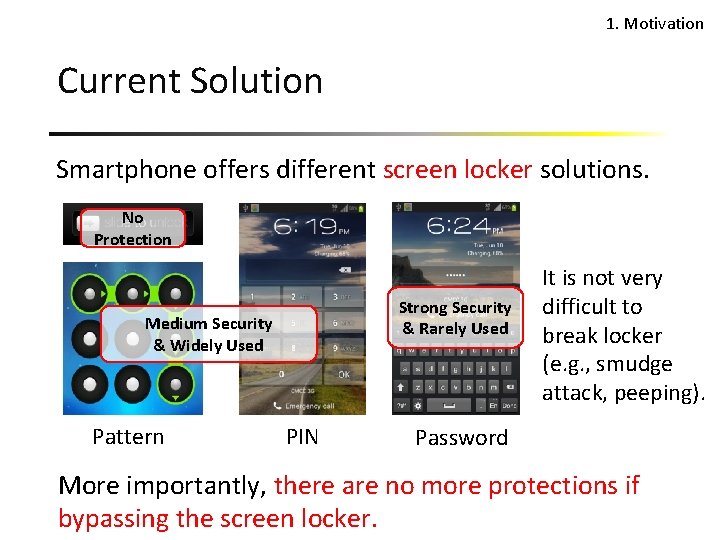
1. Motivation Current Solution Smartphone offers different screen locker solutions. No Protection Strong Security & Rarely Used Medium Security & Widely Used Pattern PIN It is not very difficult to break locker (e. g. , smudge attack, peeping). Password More importantly, there are no more protections if bypassing the screen locker.
1. Motivation Continuous and Passive Continuous: The smartphone can authenticate its current user from time to time (whenever there is interaction), not just when unlocking screen. Passive: The authentication is done in the background without any prompt for credentials, which is non-intrusive.
1. Motivation Why Touch Biometrics Question: How do we recognize a friend passively? Blabla … Answer: Through the information we received from our ears, eyes (i. e. , the interfaces). Touchscreen is the dominant human-to-smartphone interface.
2. Touch-based Authentication Approach
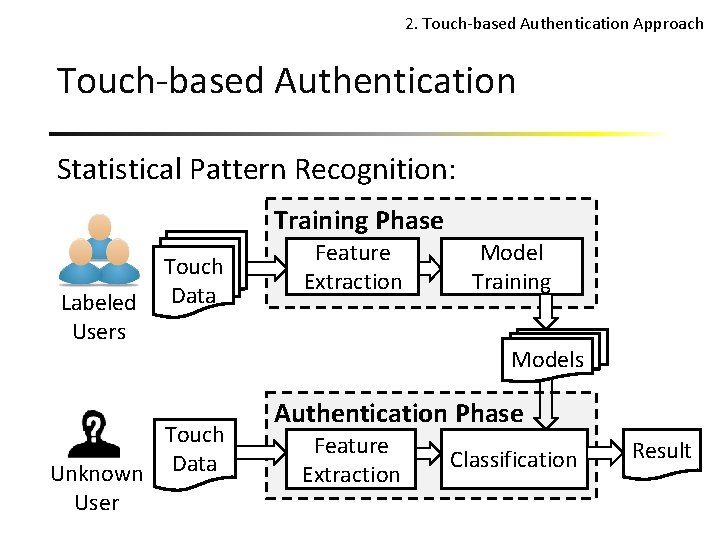
2. Touch-based Authentication Approach Touch-based Authentication Statistical Pattern Recognition: Training Phase Labeled Users Touch Data Touch Unknown Data User Feature Extraction Model Training Models Authentication Phase Feature Extraction Classification Result
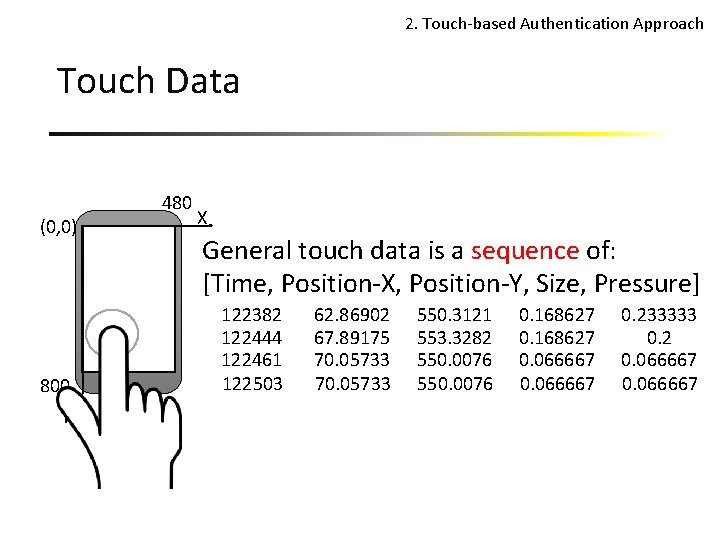
2. Touch-based Authentication Approach Touch Data (0, 0) 800 Y 480 X General touch data is a sequence of: [Time, Position-X, Position-Y, Size, Pressure] 122382 122444 122461 122503 62. 86902 67. 89175 70. 05733 550. 3121 553. 3282 550. 0076 0. 168627 0. 066667 0. 233333 0. 2 0. 066667
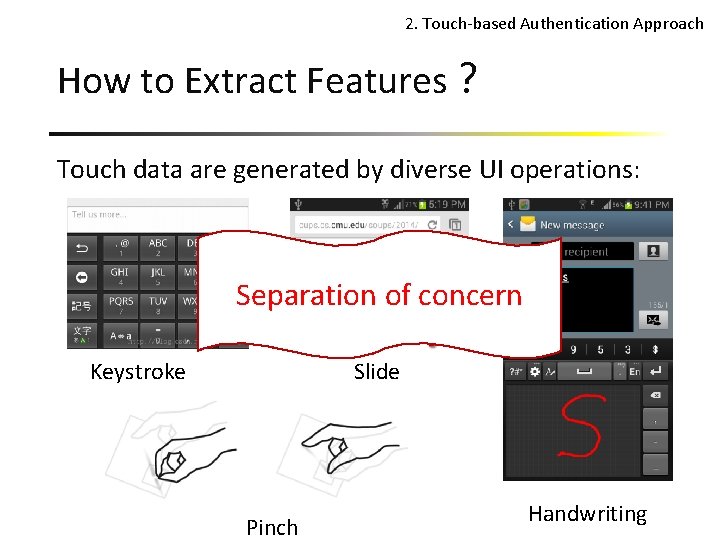
2. Touch-based Authentication Approach How to Extract Features? Touch data are generated by diverse UI operations: Separation of concern Keystroke Slide Pinch Handwriting
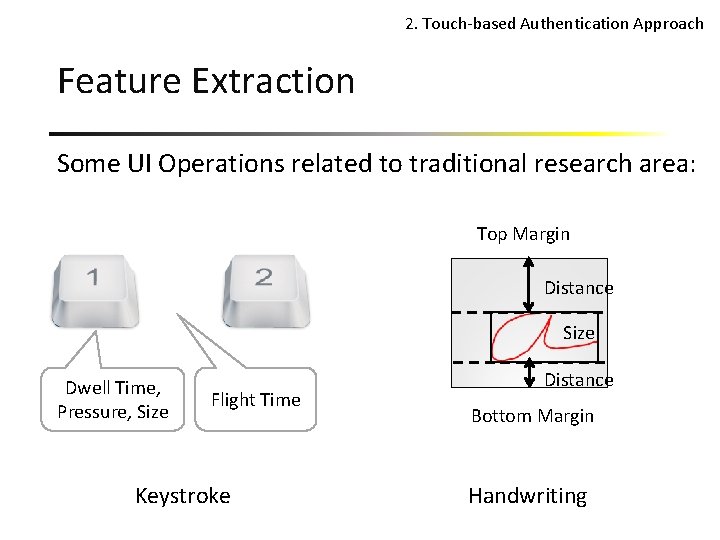
2. Touch-based Authentication Approach Feature Extraction Some UI Operations related to traditional research area: Top Margin Distance Size Dwell Time, Pressure, Size Flight Time Keystroke Distance Bottom Margin Handwriting
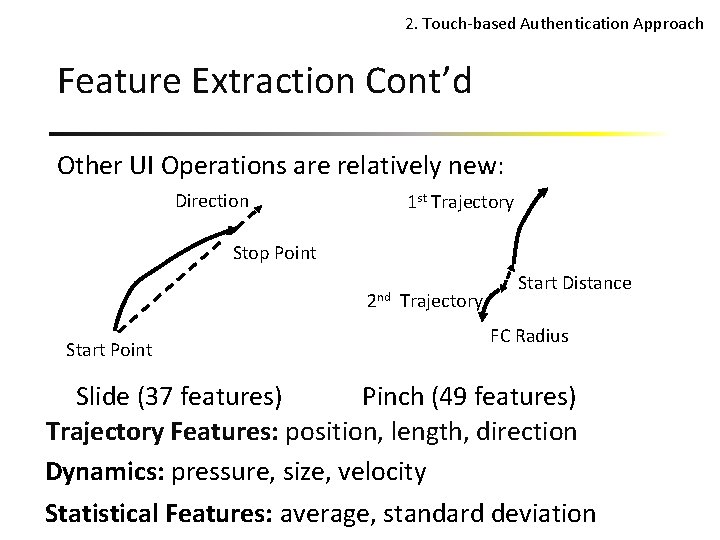
2. Touch-based Authentication Approach Feature Extraction Cont’d Other UI Operations are relatively new: Direction 1 st Trajectory Stop Point 2 nd Start Point Trajectory Start Distance FC Radius Pinch (49 features) Slide (37 features) Trajectory Features: position, length, direction Dynamics: pressure, size, velocity Statistical Features: average, standard deviation
3. Experimental Study
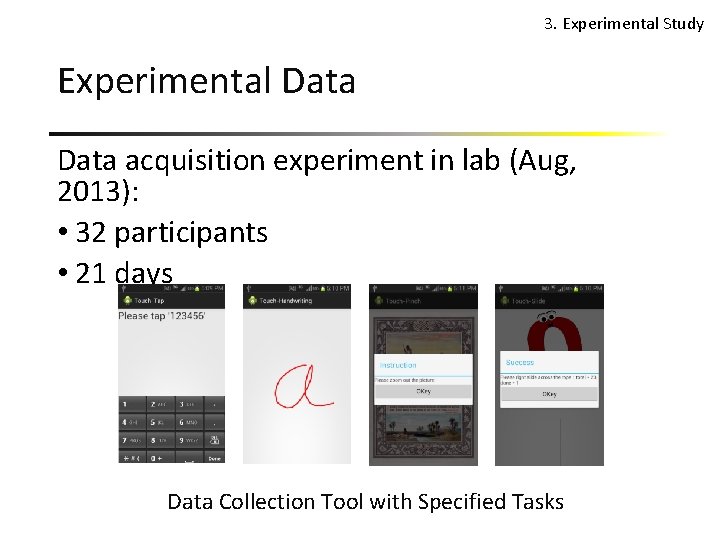
3. Experimental Study Experimental Data acquisition experiment in lab (Aug, 2013): • 32 participants • 21 days Data Collection Tool with Specified Tasks
3. Experimental Study Biometric Properties* • Universality: every person has the characteristic • Collectability: the characteristic can be collected in numbers • Distinctiveness: each two person should be sufficiently different • Permanence: the characteristic should be stable over a period of time * A. K. Jain et al. , An introduction to biometric recognition, 2004
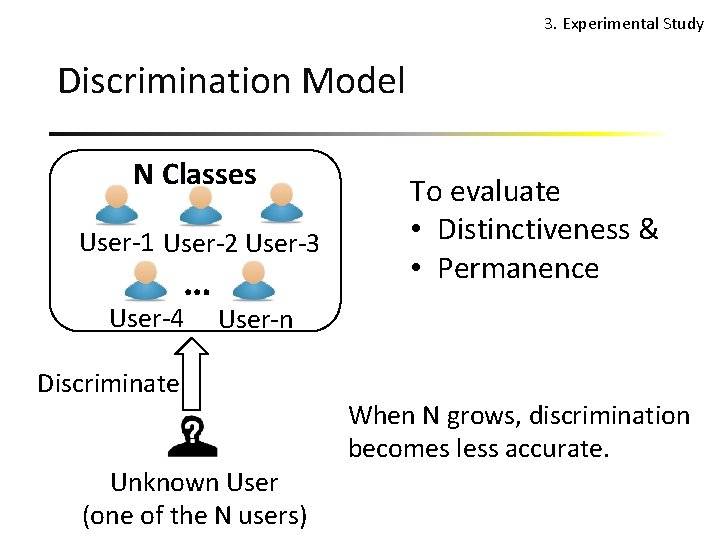
3. Experimental Study Discrimination Model N Classes User-1 User-2 User-3 … User-4 To evaluate • Distinctiveness & • Permanence User-n Discriminate Unknown User (one of the N users) When N grows, discrimination becomes less accurate.
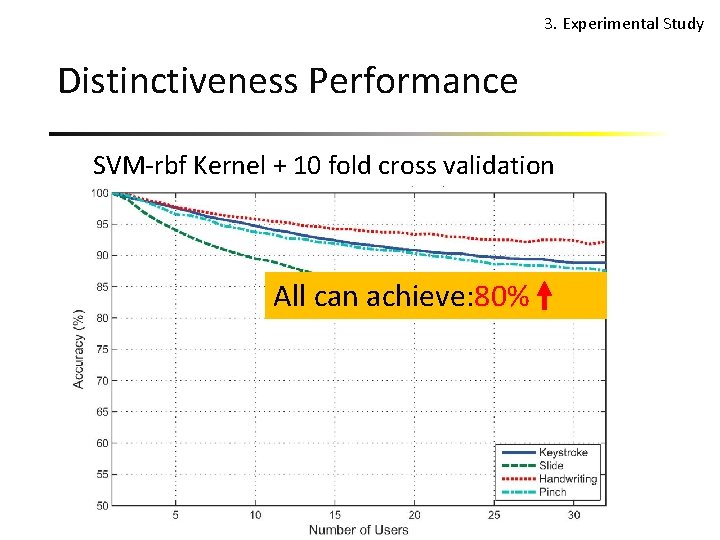
3. Experimental Study Distinctiveness Performance SVM-rbf Kernel + 10 fold cross validation All can achieve: 80%
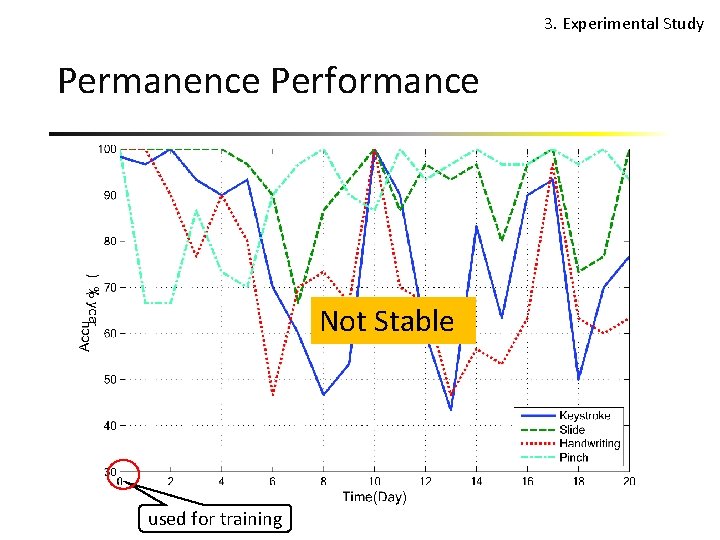
3. Experimental Study Permanence Performance Not Stable used for training
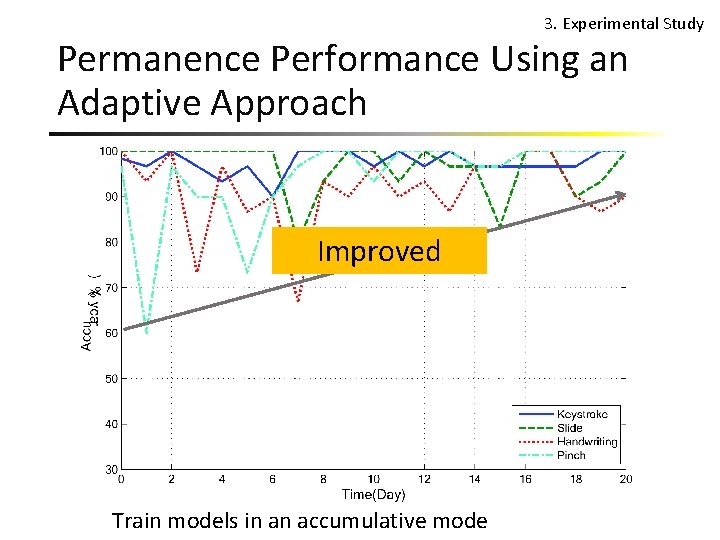
3. Experimental Study Permanence Performance Using an Adaptive Approach Improved Train models in an accumulative mode
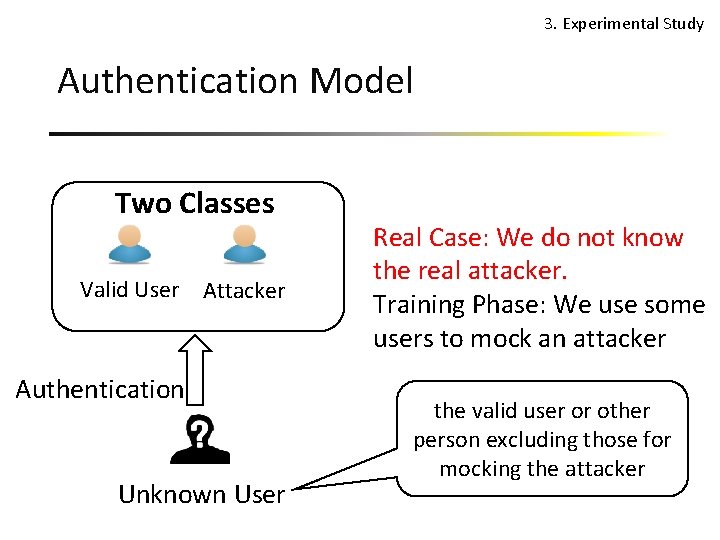
3. Experimental Study Authentication Model Two Classes Valid User Attacker Authentication Unknown User Real Case: We do not know the real attacker. Training Phase: We use some users to mock an attacker the valid user or other person excluding those for mocking the attacker
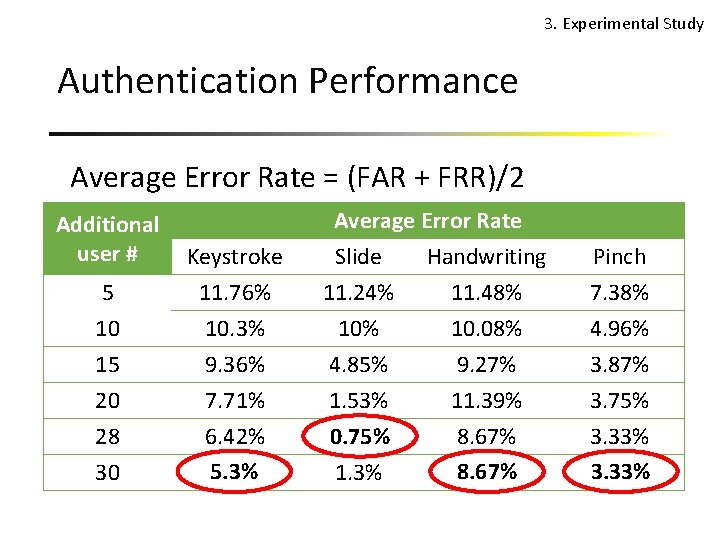
3. Experimental Study Authentication Performance Average Error Rate = (FAR + FRR)/2 Additional user # 5 10 Keystroke 11. 76% 10. 3% 15 20 28 30 9. 36% 7. 71% 6. 42% 5. 3% Average Error Rate Slide Handwriting 11. 24% 11. 48% 10. 08% 4. 85% 1. 53% 0. 75% 1. 3% 9. 27% 11. 39% 8. 67% Pinch 7. 38% 4. 96% 3. 87% 3. 75% 3. 33%
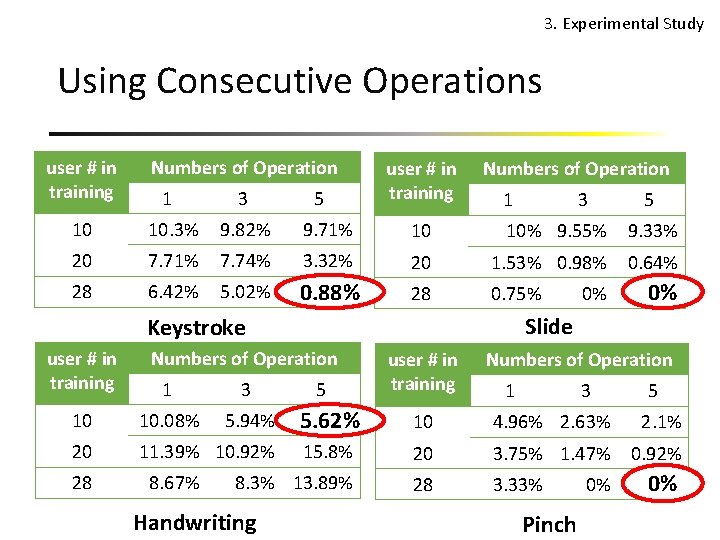
3. Experimental Study Using Consecutive Operations user # in training Numbers of Operation 1 3 5 10 10. 3% 9. 82% 9. 71% 10 10% 9. 55% 9. 33% 20 7. 71% 7. 74% 3. 32% 20 1. 53% 0. 98% 0. 64% 28 6. 42% 5. 02% 0. 88% 28 0. 75% Numbers of Operation 1 3 10 10. 08% 5. 94% 20 11. 39% 10. 92% 28 8. 67% 0% 0% Slide Keystroke user # in training 0% 5 user # in training Numbers of Operation 1 3 5 5. 62% 10 4. 96% 2. 63% 2. 1% 15. 8% 20 3. 75% 1. 47% 0. 92% 8. 3% 13. 89% 28 3. 33% Handwriting Pinch 0% 0% 0%
Conclusion Touch biometrics is: • Distinctive • Not stable -> Adaptive approach • Promising authentication accuracy
Future Work 1. Improve accuracy (e. g. , via more features, trying other classifiers) 2. Develop touch-based authentication software • Best practice (e. g. , adaptive method, combination of consecutive operations) • Approach to handle noise and new input • Performance issues (e. g. , speed, overhead) 3. Conduct experimental study outside of the lab
Thank You! Questions? Project Website: http: //www. cudroid. com/urmajesty
- Slides: 25