Tor Bruce Maggs relying on materials from http
Tor Bruce Maggs relying on materials from http: //www. torproject. org
2
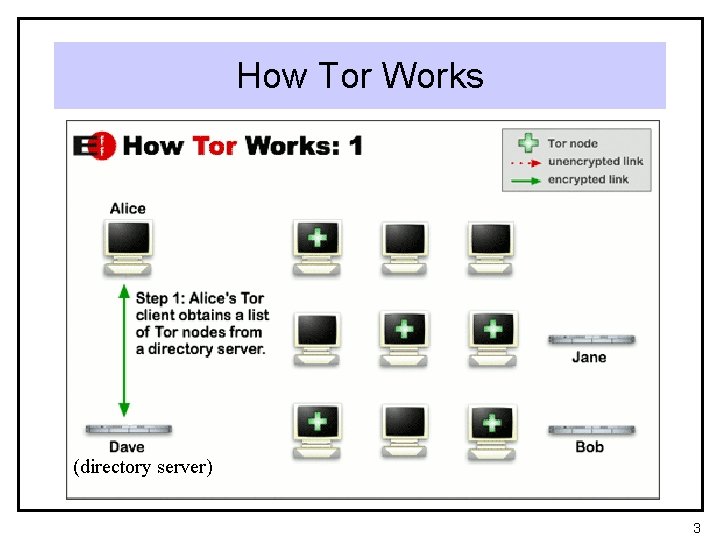
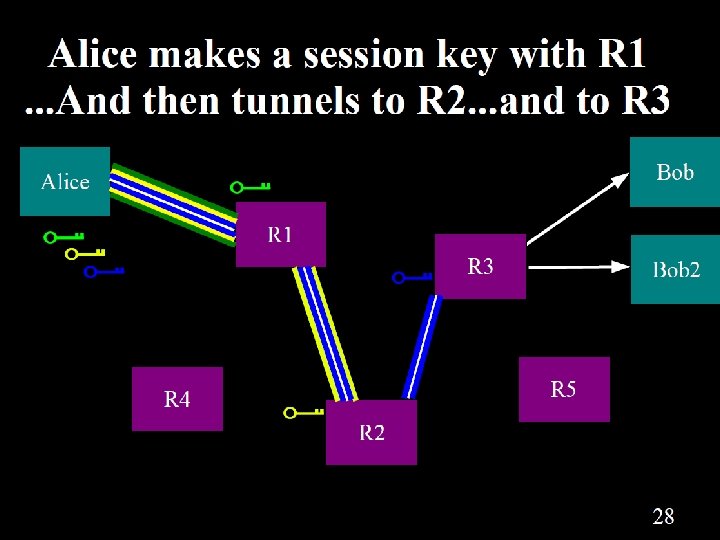
How Tor Works (directory server) 3
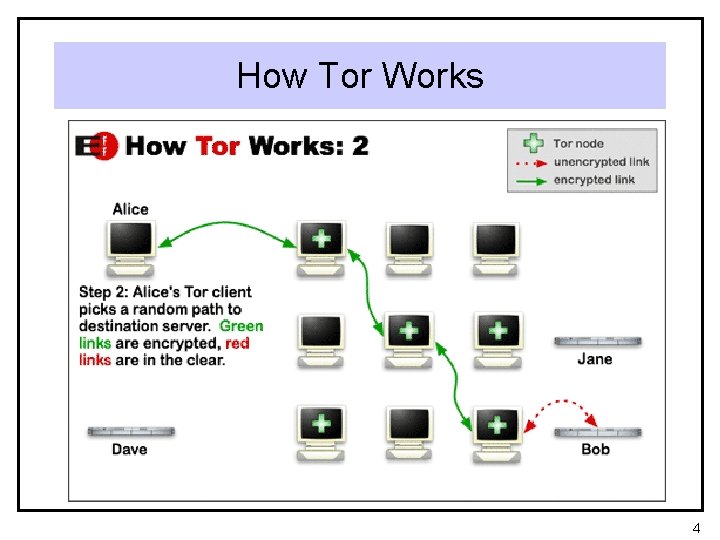
How Tor Works 4
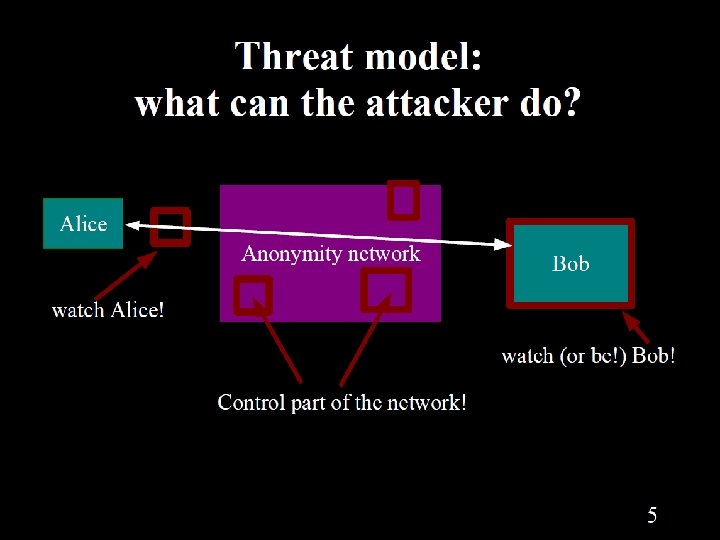
5
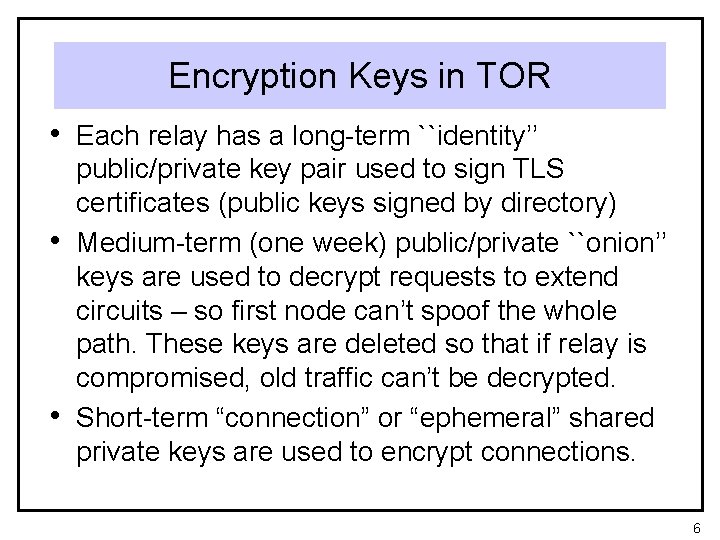
Encryption Keys in TOR • Each relay has a long-term ``identity’’ • • public/private key pair used to sign TLS certificates (public keys signed by directory) Medium-term (one week) public/private ``onion’’ keys are used to decrypt requests to extend circuits – so first node can’t spoof the whole path. These keys are deleted so that if relay is compromised, old traffic can’t be decrypted. Short-term “connection” or “ephemeral” shared private keys are used to encrypt connections. 6
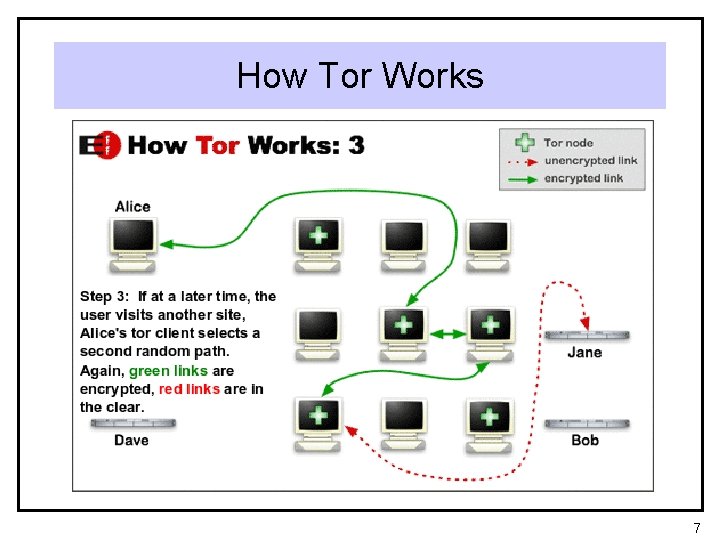
How Tor Works 7
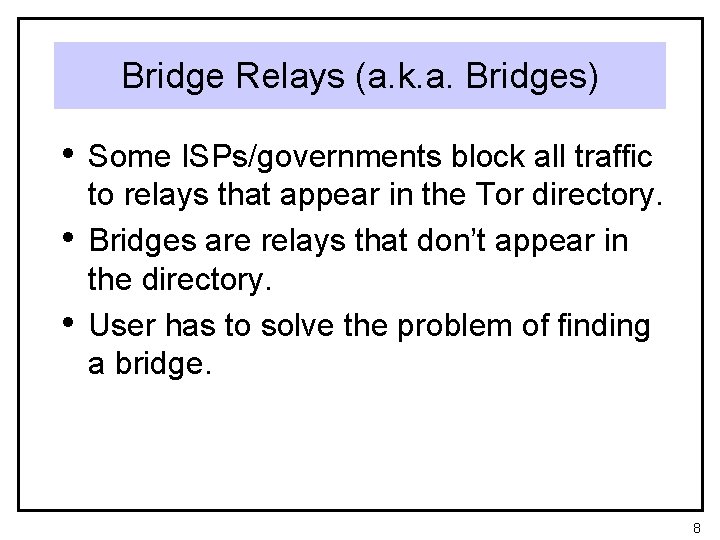
Bridge Relays (a. k. a. Bridges) • Some ISPs/governments block all traffic • • to relays that appear in the Tor directory. Bridges are relays that don’t appear in the directory. User has to solve the problem of finding a bridge. 8
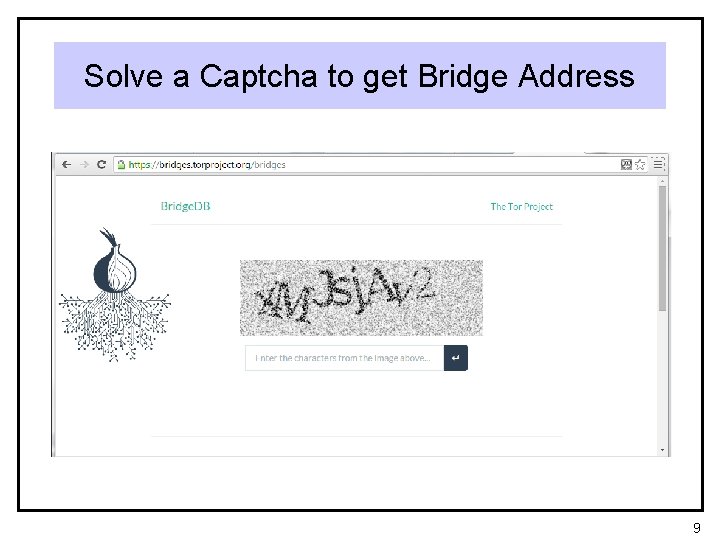
Solve a Captcha to get Bridge Address 9

10
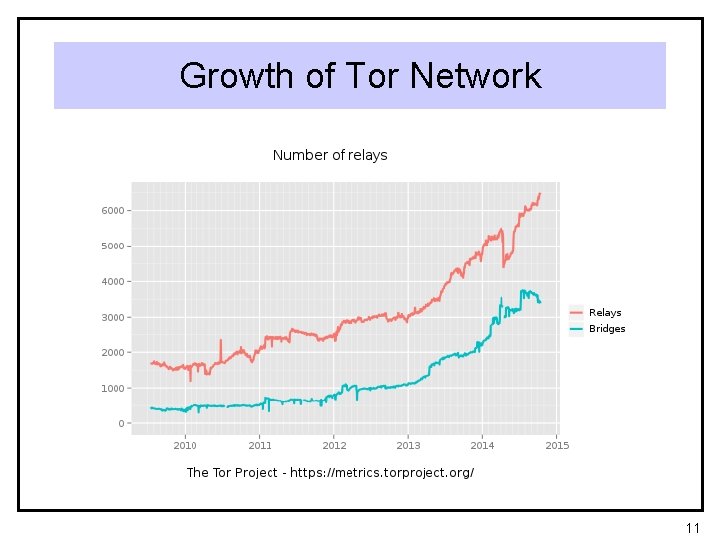
Growth of Tor Network 11
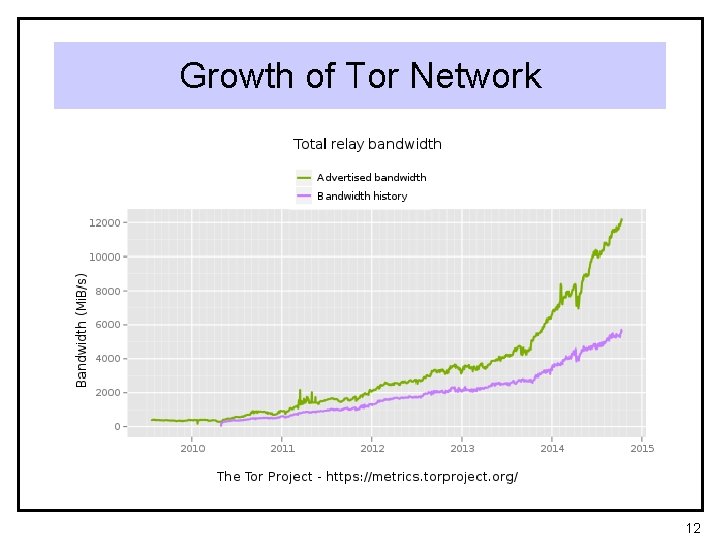
Growth of Tor Network 12
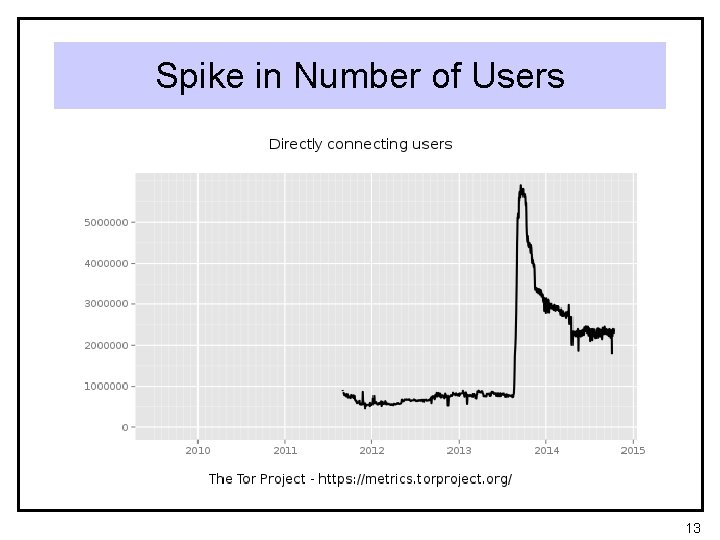
Spike in Number of Users 13
Possible Explanation for Spike • Botnet “Mevade. A” a. k. a. “Sefnit” a. k. a. “SBC” is using Tor for connectivity • http: //blog. fox-it. com/2013/09/05/largebotnet-cause-of-recent-tor-networkoverload/ 14
15
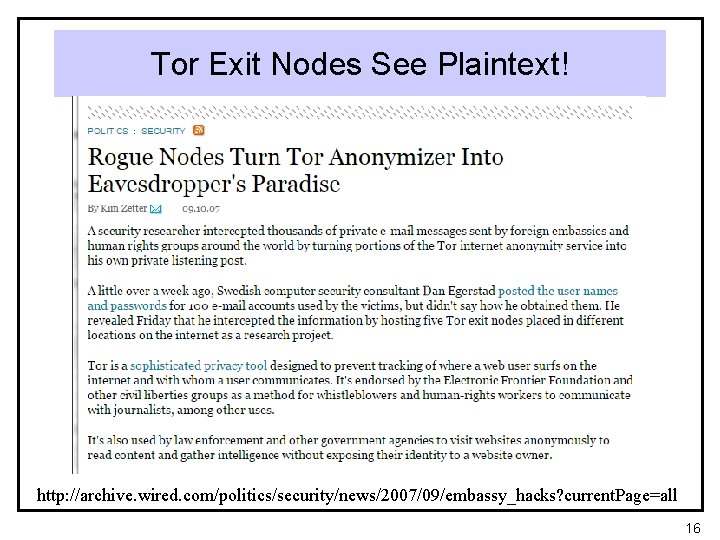
Tor Exit Nodes See Plaintext! http: //archive. wired. com/politics/security/news/2007/09/embassy_hacks? current. Page=all 16
Tor Browser 17
Tor Browser 18
19
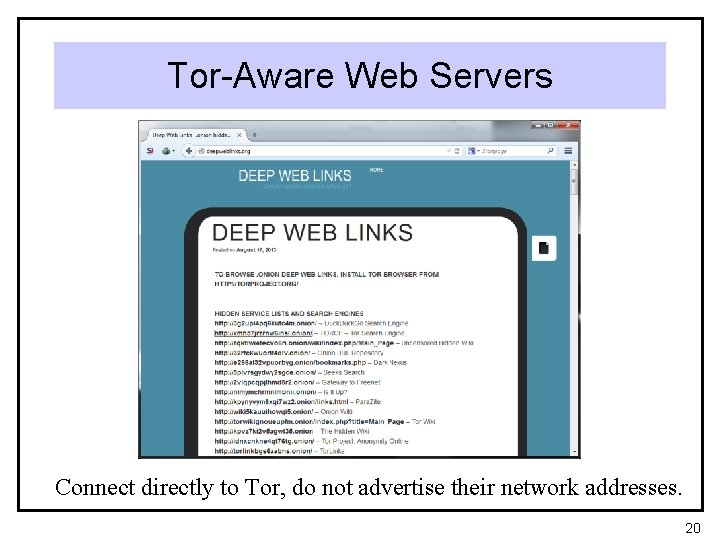
Tor-Aware Web Servers Connect directly to Tor, do not advertise their network addresses. 20
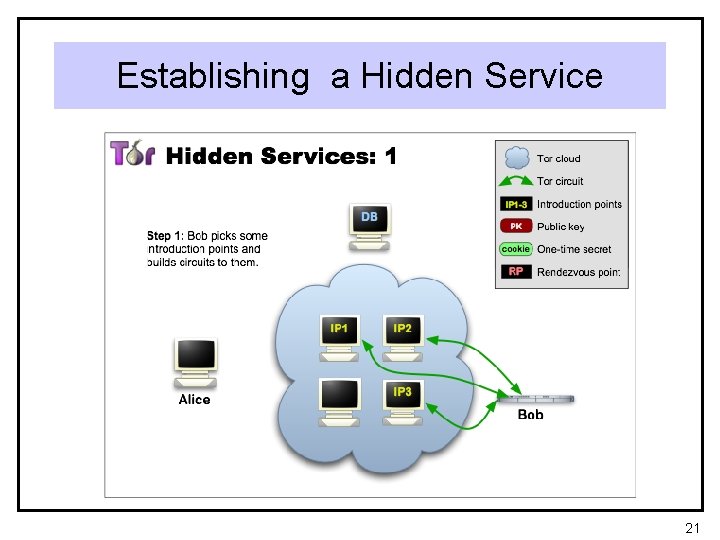
Establishing a Hidden Service 21
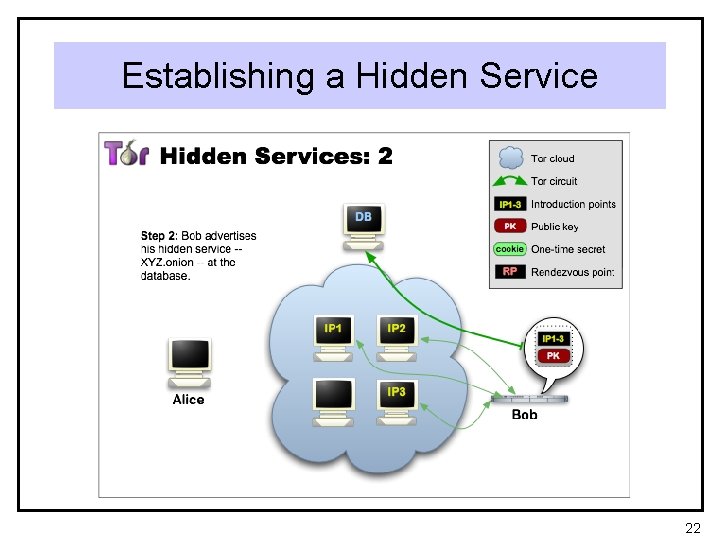
Establishing a Hidden Service 22
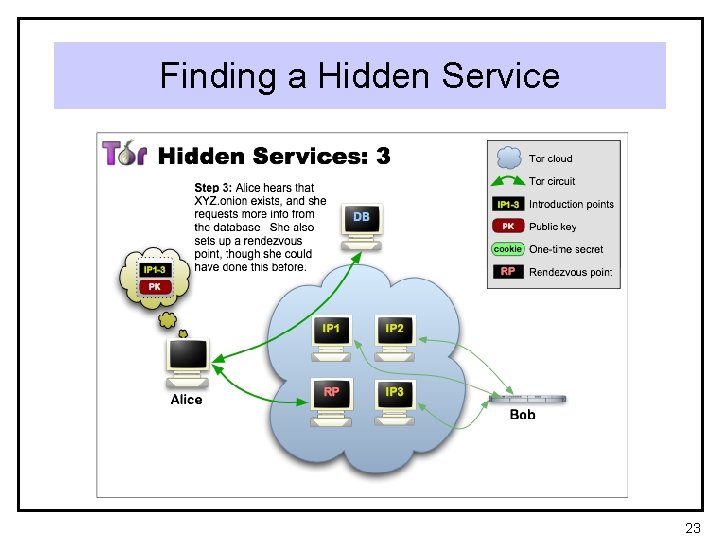
Finding a Hidden Service 23
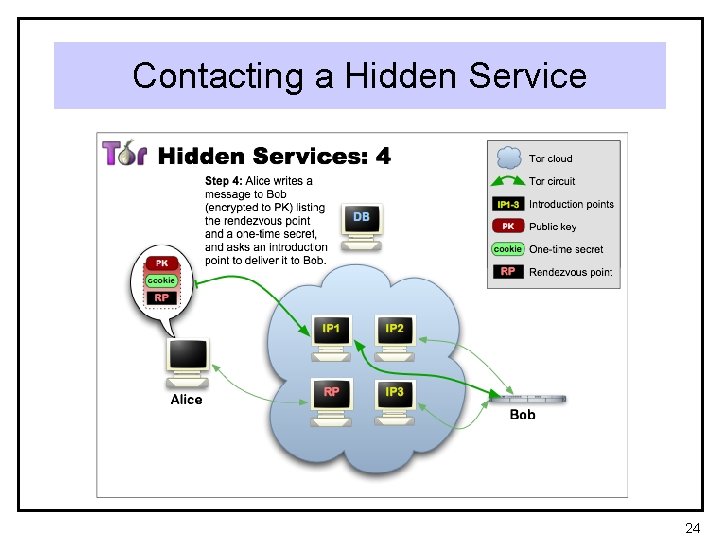
Contacting a Hidden Service 24
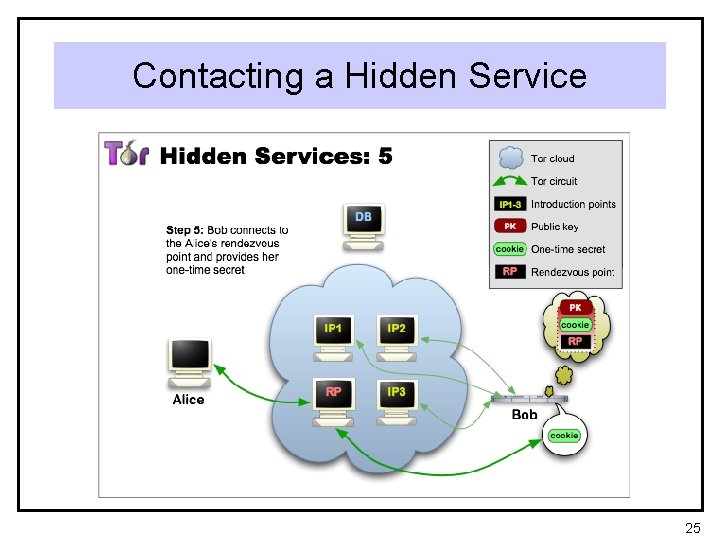
Contacting a Hidden Service 25
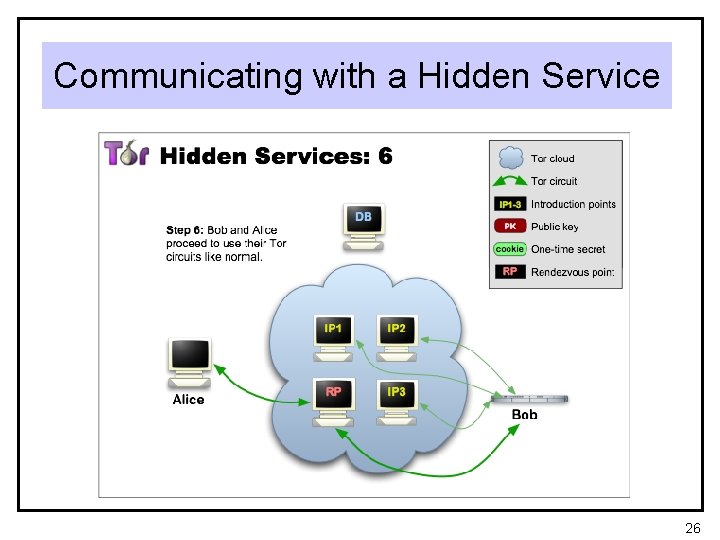
Communicating with a Hidden Service 26
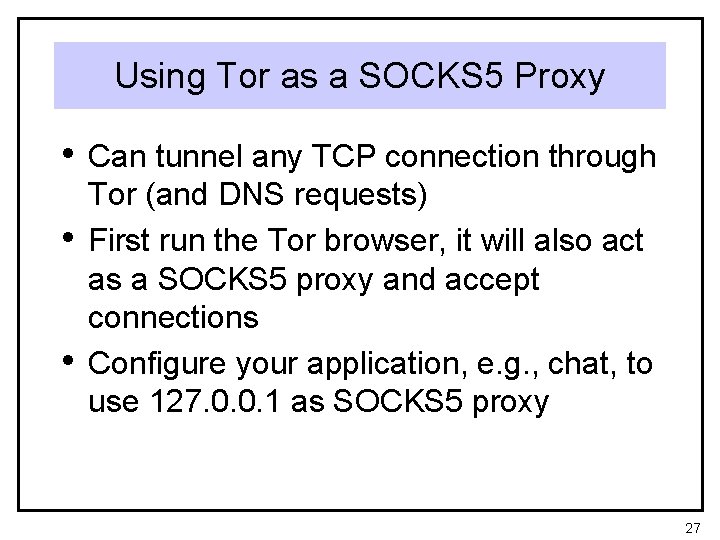
Using Tor as a SOCKS 5 Proxy • Can tunnel any TCP connection through • • Tor (and DNS requests) First run the Tor browser, it will also act as a SOCKS 5 proxy and accept connections Configure your application, e. g. , chat, to use 127. 0. 0. 1 as SOCKS 5 proxy 27
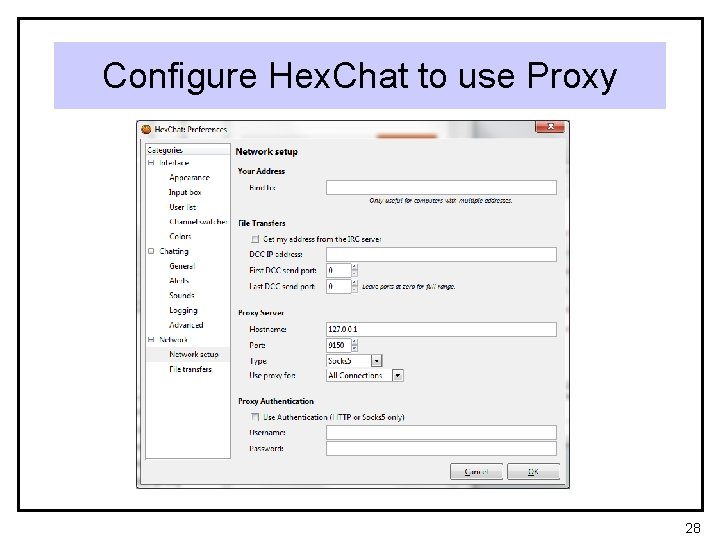
Configure Hex. Chat to use Proxy 28
Now Chatting through Tor 29

4 30
- Slides: 30