Topology Design of Structured Campus Networks by Habib
Topology Design of Structured Campus Networks by Habib Youssef Sadiq M. Sait Salman A. Khan Department of Computer Engineering King Fahd University of Petroleum and Minerals 1
Outline l l Introduction & Problem Statement Proposed Algorithm » » l l Simulated Evolution Fuzzy Evaluation Scheme Selection Fuzzy Allocation Scheme Experiments and Results Conclusion 2
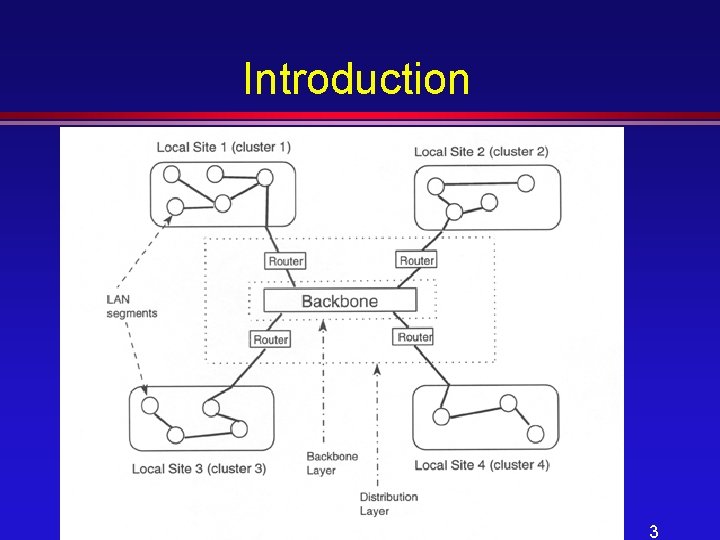
Introduction 3
Introduction l Important objectives of good topology » Monetary Cost » Average network delay » Number of hops between any source-destination pair l Conflicting nature of the objectives 4
Constraints l Limitation of capacity on links l Limitation of ports on networking devices l Another possible constraint is that the designer might like to enforce certain hierarchies on network devices. l Topology is a tree 5
Proposed Algorithm- The Fuzzy Simulated Algorithm 6
Purpose l Given the optimization parameters and constraints, we have to design a Spanning Tree Topology to satisfy all the constraints and optimize desired objectives. 7
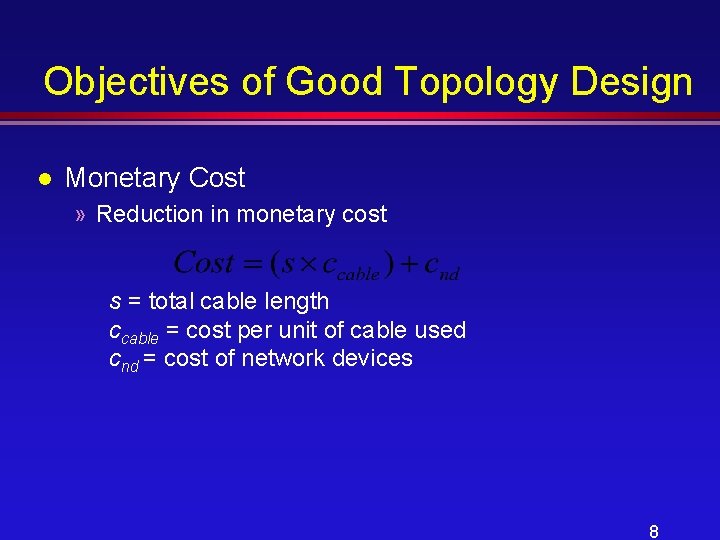
Objectives of Good Topology Design l Monetary Cost » Reduction in monetary cost s = total cable length ccable = cost per unit of cable used cnd = cost of network devices 8
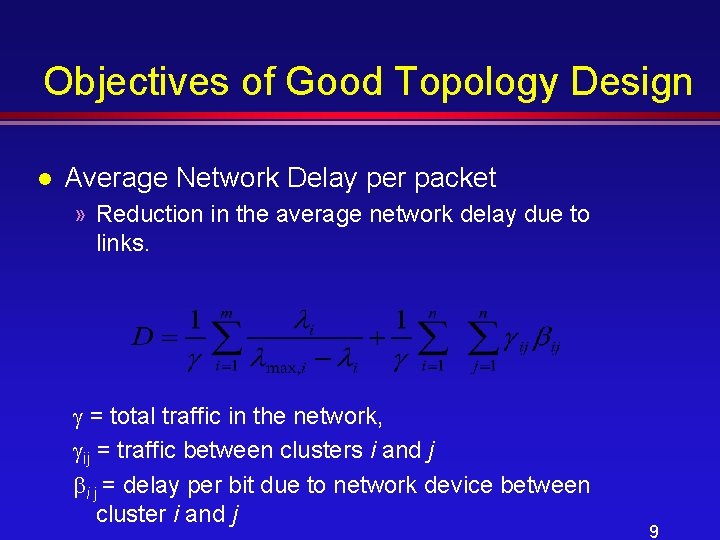
Objectives of Good Topology Design l Average Network Delay per packet » Reduction in the average network delay due to links. = total traffic in the network, ij = traffic between clusters i and j i j = delay per bit due to network device between cluster i and j 9

Objectives of Good Topology Design l Maximum hops between any sourcedestination pair. » This includes the networking devices due to which processing delays are encountered. 10
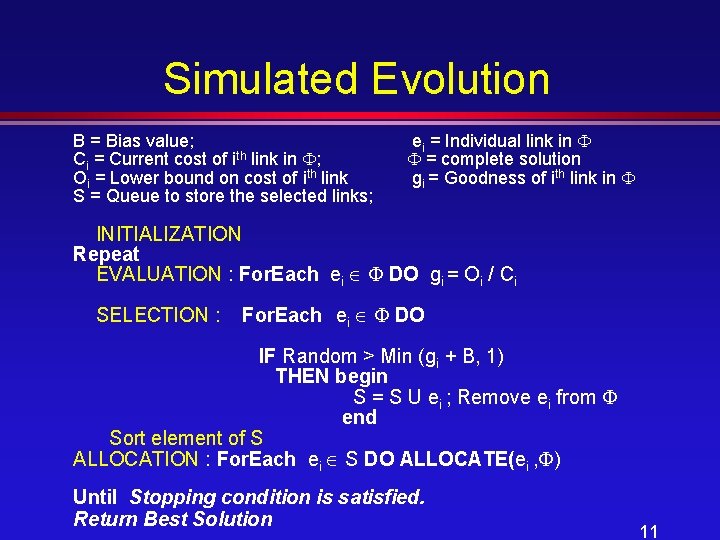
Simulated Evolution B = Bias value; Ci = Current cost of ith link in ; Oi = Lower bound on cost of ith link S = Queue to store the selected links; ei = Individual link in = complete solution gi = Goodness of ith link in INITIALIZATION Repeat EVALUATION : For. Each ei DO gi = Oi / Ci SELECTION : For. Each ei DO IF Random > Min (gi + B, 1) THEN begin S = S U ei ; Remove ei from end Sort element of S ALLOCATION : For. Each ei S DO ALLOCATE(ei , ) Until Stopping condition is satisfied. Return Best Solution 11
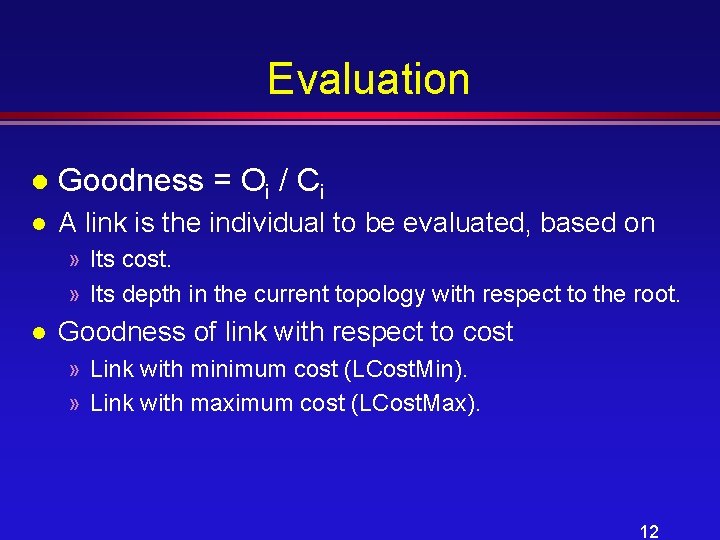
Evaluation l Goodness = Oi / Ci l A link is the individual to be evaluated, based on » Its cost. » Its depth in the current topology with respect to the root. l Goodness of link with respect to cost » Link with minimum cost (LCost. Min). » Link with maximum cost (LCost. Max). 12
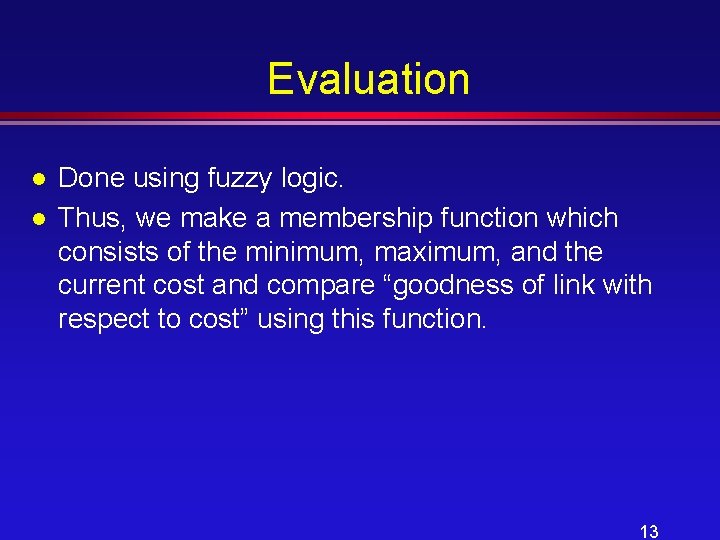
Evaluation l l Done using fuzzy logic. Thus, we make a membership function which consists of the minimum, maximum, and the current cost and compare “goodness of link with respect to cost” using this function. 13
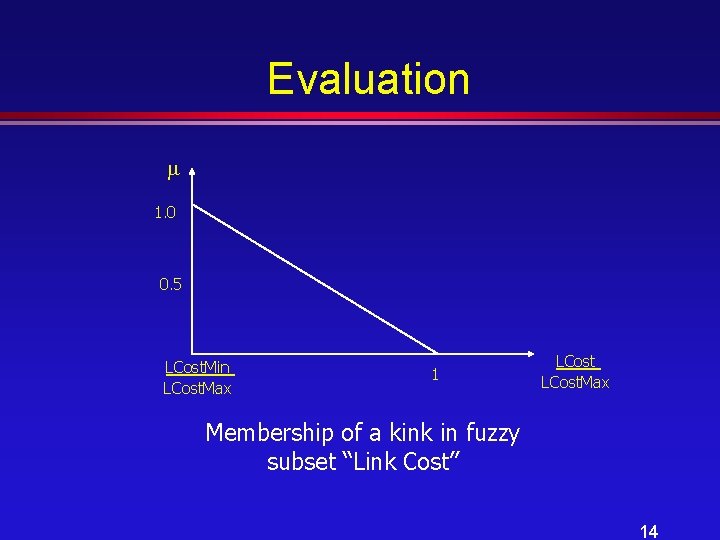
Evaluation 1. 0 0. 5 LCost. Min LCost. Max 1 LCost. Max Membership of a kink in fuzzy subset “Link Cost” 14
Evaluation l Goodness of link with respect to depth » Minimum depth of link =1 (LDepth. Min) » Maximum depth of link = (1. 5) *Max. depth of any link in the first generation OR Maximum of 7 (LDepth. Max) 15
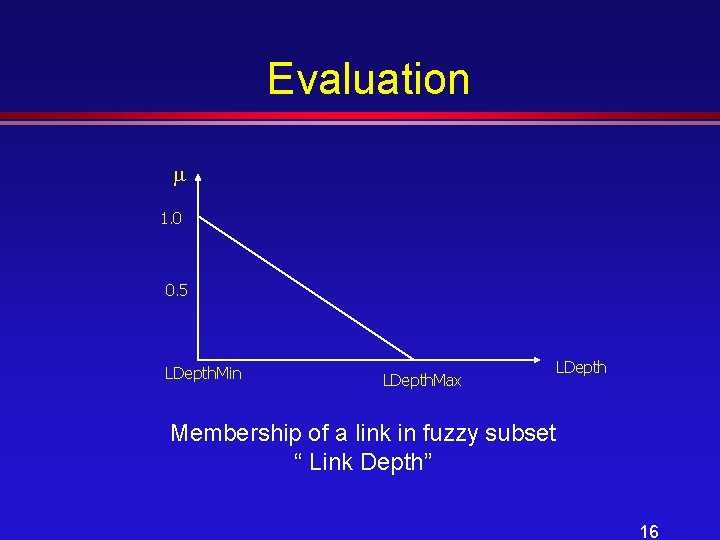
Evaluation 1. 0 0. 5 LDepth. Min LDepth. Max LDepth Membership of a link in fuzzy subset “ Link Depth” 16
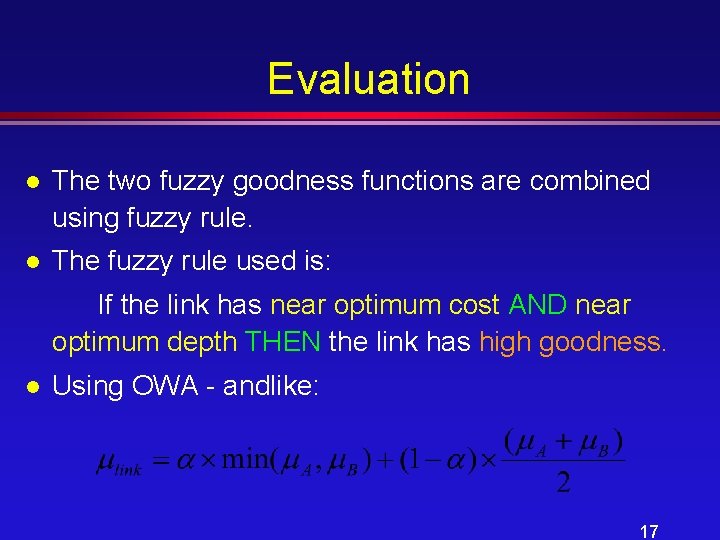
Evaluation l The two fuzzy goodness functions are combined using fuzzy rule. l The fuzzy rule used is: If the link has near optimum cost AND near optimum depth THEN the link has high goodness. l Using OWA - andlike: 17
Selection l Based on the goodness found in the evaluation phase, link(s) is (are) selected to be removed from the topology. l Done using » Variable bias Bk = 1 - Gk-1 where Gk-1 is the average goodness of links in K-1 st iteration 18
Allocation l Moves are made and the gain in cost of the overall topology is calculated based on » Monetary cost of the topology » Average network delay per packet » Maximum number of hops between any sourcedestination pair. 19
Allocation l For Monetary Cost, the minimum and maximum bounds are calculated as follows: » Minimum : from Esau-Williams algorithm with all the constraints fully relaxed. (TCost. Min) » Maximum : we find it from the very first generation. (TCost. Max) 20
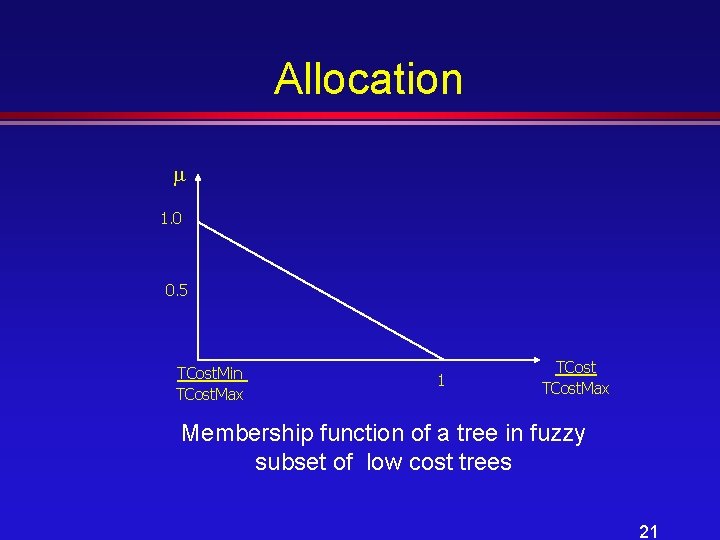
Allocation 1. 0 0. 5 TCost. Min TCost. Max 1 TCost. Max Membership function of a tree in fuzzy subset of low cost trees 21
Allocation l For Average Network Delay, the minimum and maximum bounds are calculated as follows: » Minimum : delay when all the nodes are connected directly to the center (TDelay. Min). » Maximum : initial solution (TDelay. Max). 22
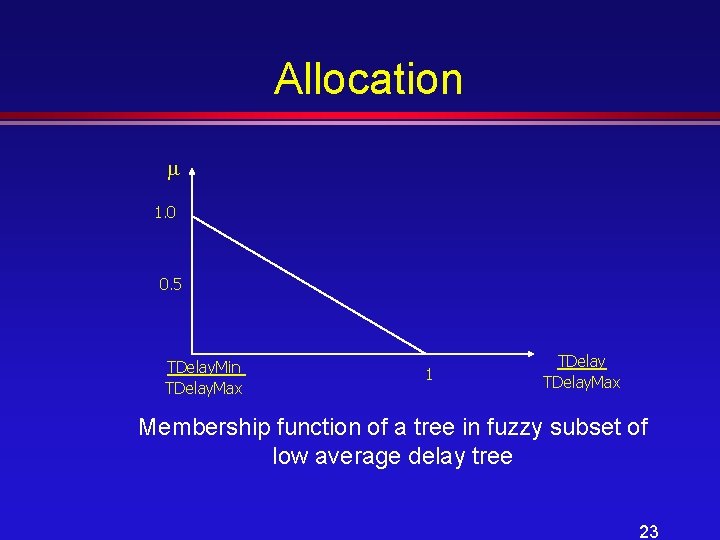
Allocation 1. 0 0. 5 TDelay. Min TDelay. Max 1 TDelay. Max Membership function of a tree in fuzzy subset of low average delay tree 23
Allocation l For Maximum number of hops, the minimum and maximum bounds are calculated as follows: » minimum : 1 hop (THops. Min). » maximum : initial solution (THops. Max). 24
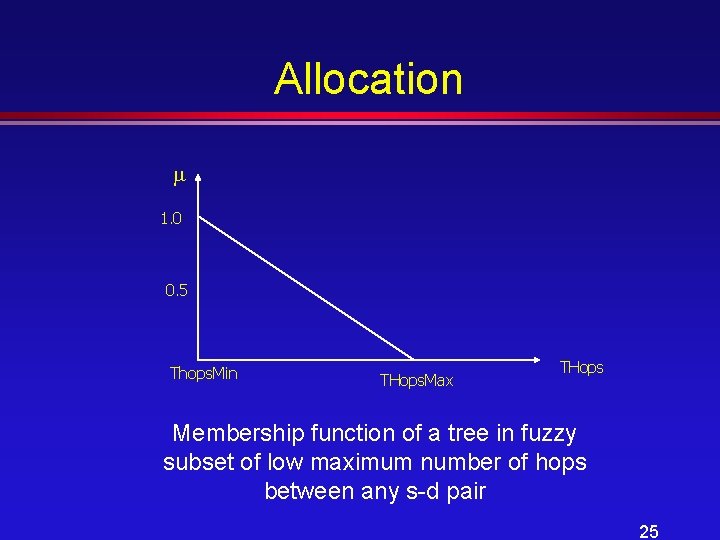
Allocation 1. 0 0. 5 Thops. Min THops. Max THops Membership function of a tree in fuzzy subset of low maximum number of hops between any s-d pair 25
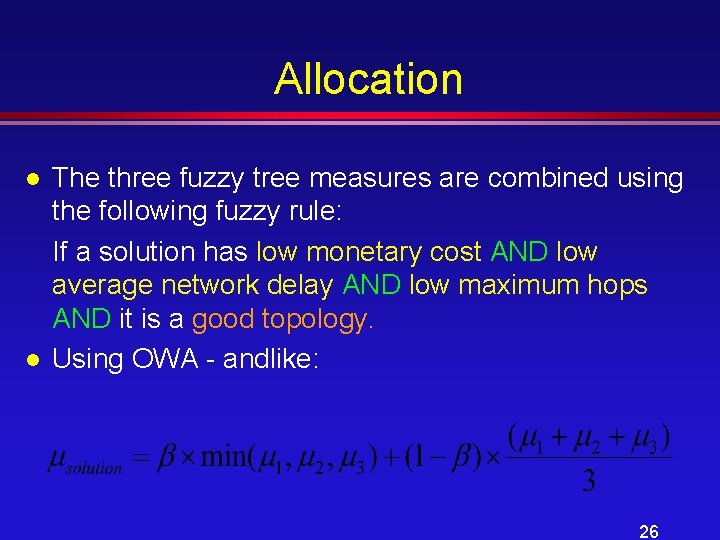
Allocation l l The three fuzzy tree measures are combined using the following fuzzy rule: If a solution has low monetary cost AND low average network delay AND low maximum hops AND it is a good topology. Using OWA - andlike: 26
Allocation l What is our move ? » For each selected link, maximum 10 moves are tried (valid or invalid) – Five greedy – Five random » Pick the move which gives the maximum gain among all the moves. 27
Tabu Search l Diversifies the search by imposing restrictions on the search process, preventing it from moving in certain directions. 28
Experiments and Results 29
Assumptions l l The number of segments is known a priori and nodes have already been assigned to segments. The location of a segment (or of a local site) is represented by its (x, y) coordinates with respect to some reference point. A node is either 10/100 base. T Ethernet or Token Ring Type. A local site is made of 10/100 Base. T Ethernet segments or all Token Ring segments. 30
Assumptions l l The backbone is assumed to be running on Fast Ethernet using fiber optic cable. Within a local site, only Category 5 cable is used, while between two local sites, only fiber optic cable is used. Class C networks are assumed. Therefore, we limit the number of nodes per cluster to at most 254. Hubs, switches, routers, and other networking devices cannot be placed in any location. There are designated location to do so. 31
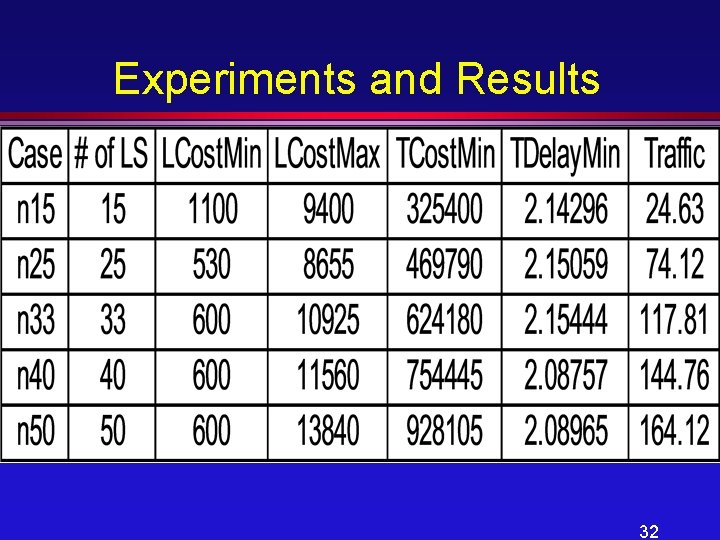
Experiments and Results 32
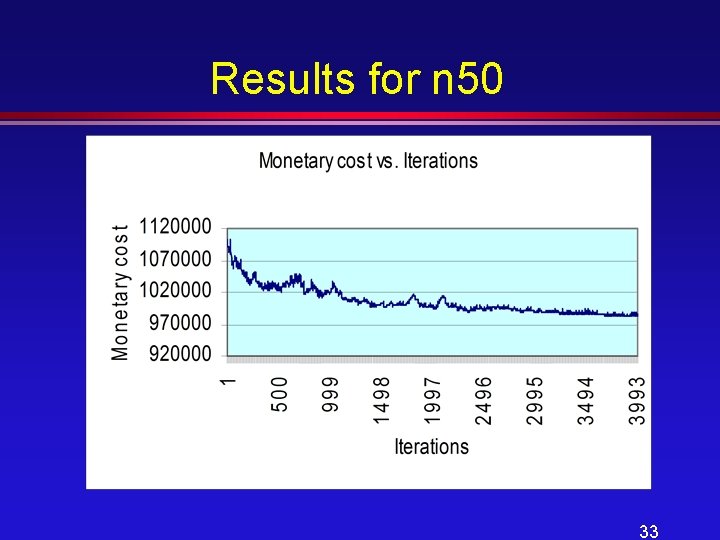
Results for n 50 33
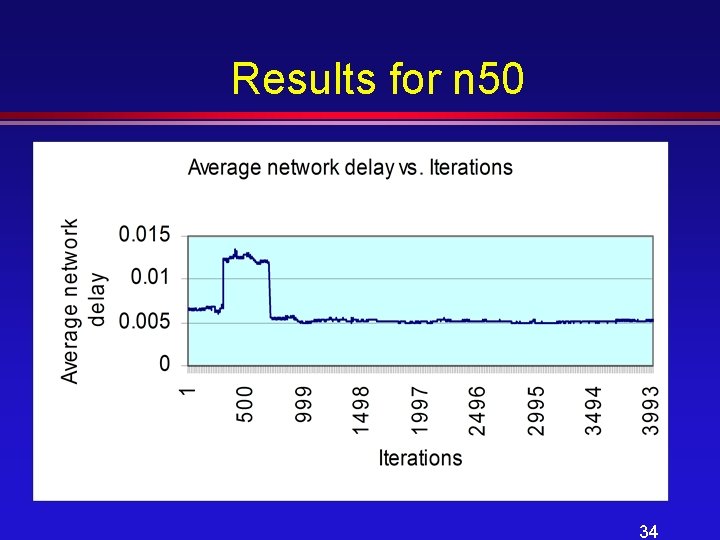
Results for n 50 34
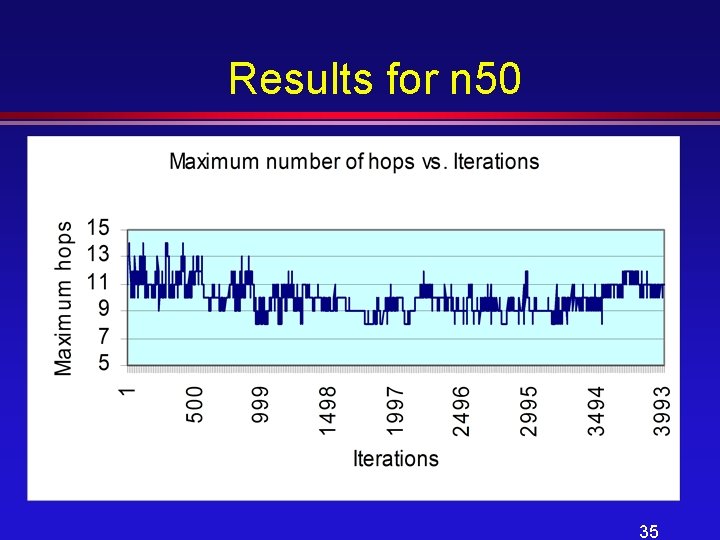
Results for n 50 35
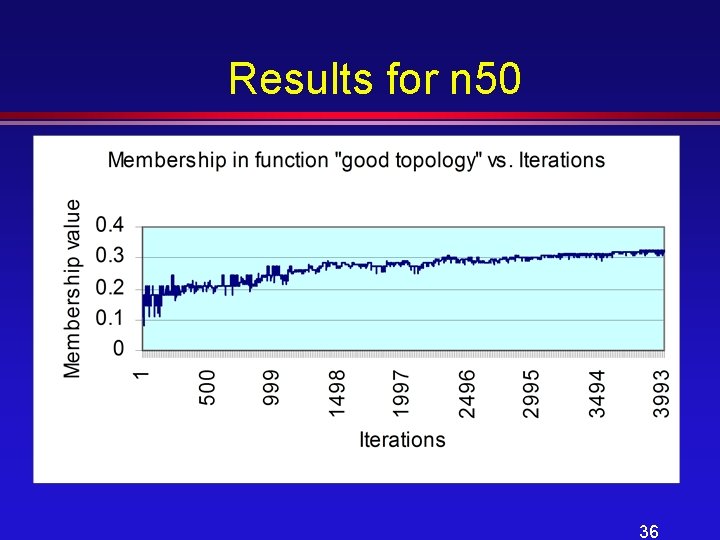
Results for n 50 36
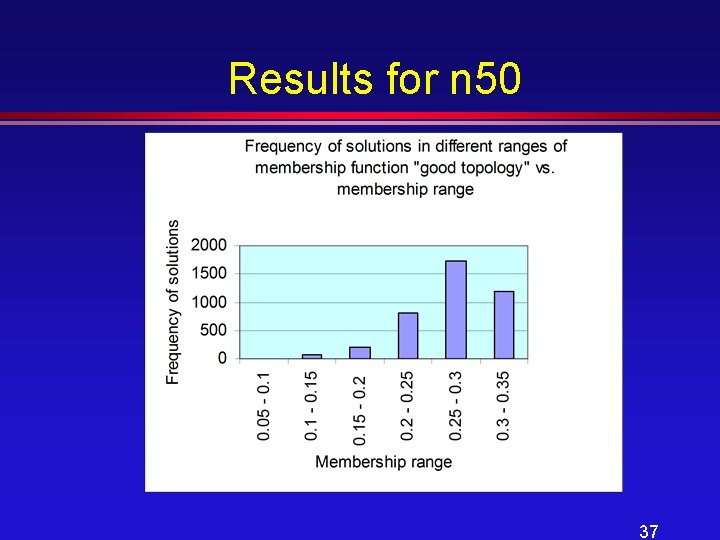
Results for n 50 37
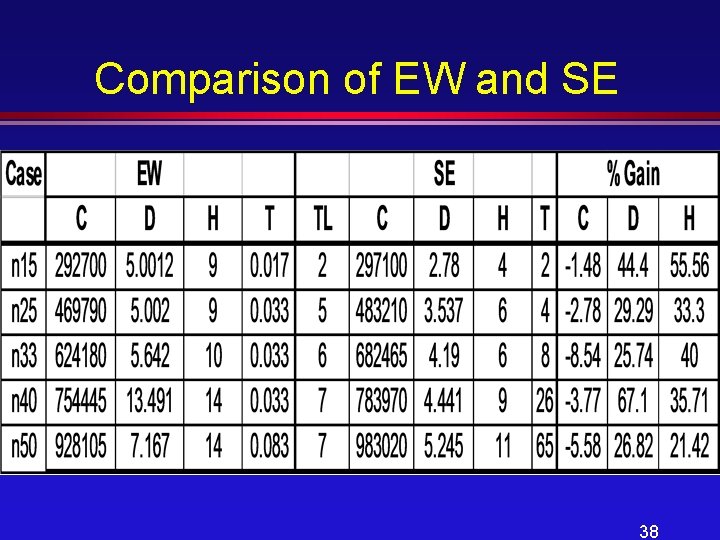
Comparison of EW and SE 38
Conclusion l The proposed algorithm was successfully applied to the problem considered in this research and performs better than Esau-William Algorithm, a widely used constructive algorithm. 39
40
- Slides: 40