Top 10 Banking Fraud Practical Discussion of Fraud
Top 10 Banking Fraud Practical Discussion of Fraud Schemes by Bank Insiders and How to Prevent Fraud from Occurring 4/11/2563 Top 10 Banking Fraud ไพรช ศรวไลฤทธ pairat@tisco. th 1
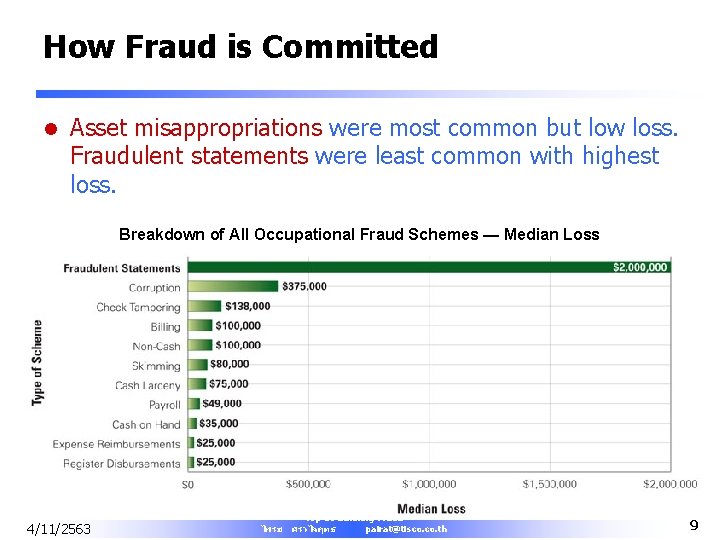
How Fraud is Committed l Asset misappropriations were most common but low loss. Fraudulent statements were least common with highest loss. Breakdown of All Occupational Fraud Schemes — Median Loss 4/11/2563 Top 10 Banking Fraud ไพรช ศรวไลฤทธ pairat@tisco. th 9
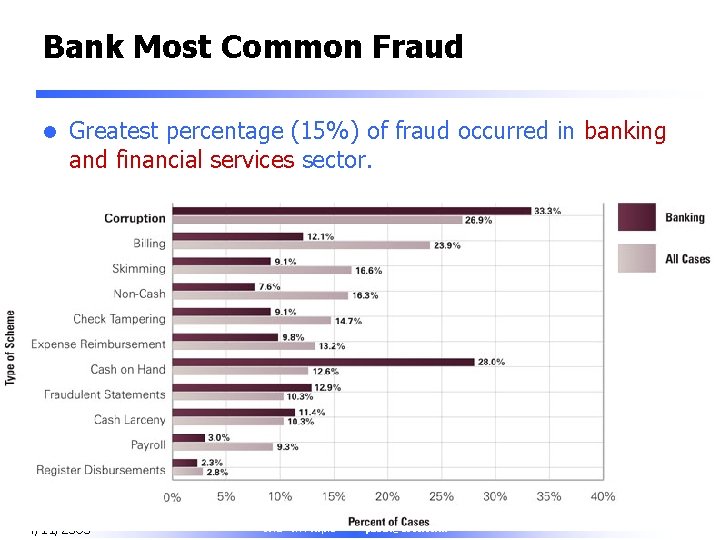
Bank Most Common Fraud l Greatest percentage (15%) of fraud occurred in banking and financial services sector. 4/11/2563 Top 10 Banking Fraud ไพรช ศรวไลฤทธ pairat@tisco. th 10

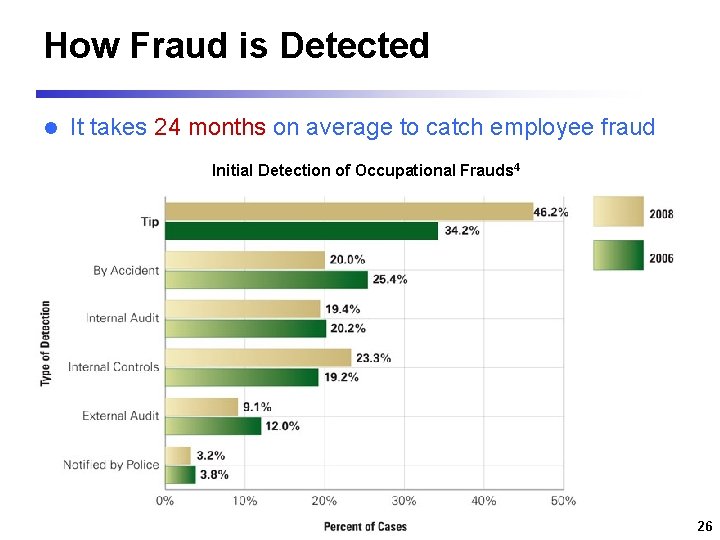
How Fraud is Detected l It takes 24 months on average to catch employee fraud Initial Detection of Occupational Frauds 4 4/11/2563 26
Key Indicators of Fraud l l l l l Tips / Complaints Missing / Alteration of documents Duplicate / Unreasonable expenses or reimbursements Failure of certain employees to take vacations Failure to follow up on past-due receivables Unusual write-offs of receivables Employees on the payroll not sign up for benefits Excessive purchase of products or services Common phone numbers / addresses of payees or customers 4/11/2563 27
Key Indicators of Fraud (Continued) l Cash shortages / overages l Stale items on bank reconciliations l Unexplained adjustments / Journal entries l Unusual financial statement relationships i. e. – Increased revenue vs. decreased receivable – Increased revenue vs. decreased inventory purchase – Increased inventory vs. decreased purchase or A/P Significant increases or decreases in account balances l Significant changes in liquidity, leverage, profitability or turnover ratios l 4/11/2563 28
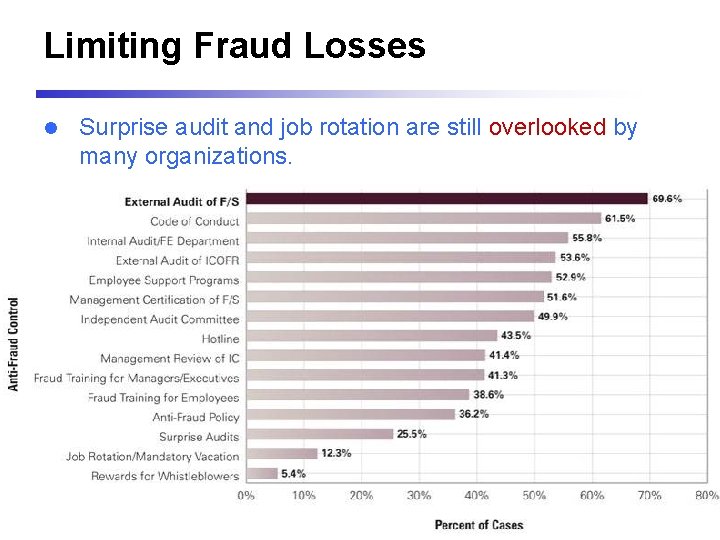
Limiting Fraud Losses l Surprise audit and job rotation are still overlooked by many organizations. 4/11/2563 29
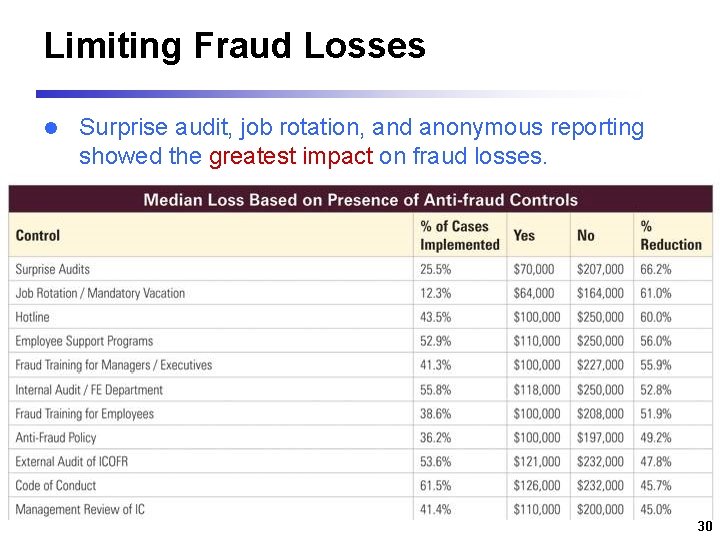
Limiting Fraud Losses l Surprise audit, job rotation, and anonymous reporting showed the greatest impact on fraud losses. 4/11/2563 30
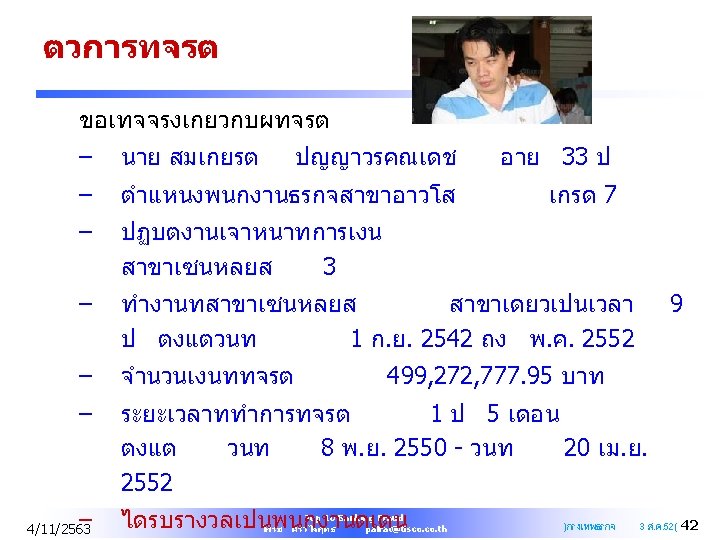
Bank Case Symptoms l l l Supervisory override, unusually large transactions or with no apparent business purpose Journal voucher contain only one signature, containing incorrect information, fund transfer between different customers' accounts Deposit slip with missing information, depositor names incomplete or not match with passbook or acct name. Frequent, large deposit/withdrawal in Executive account Deposits and withdrawals on same account on same day or in a short period of time Bank checks used to transfer between accounts / checks with altered date. 4/11/2563 31
Symptoms. . . More l l l l Purported customer signature on withdrawal voucher and checks Large negative balances in slush accts or customer accts Deposit slip of customer funds between accts of different customers Deposits of customer check where cash was received back CDs closed prematurely with proceeds put into low interest account, sometimes with penalty Customer not presented when account was opened, closed or transacted Mailing of customer statement to Executive address 4/11/2563 32

Bank Fraud Trend l l l l Fraud financial cost may be three or more times the value of loss amount Fraud is not static. It evolves with each new measures implemented New opportunities for employee fraud are emerging Criminals thwart rules-based systems “Silo” mentality weakens fraud detection Top management are moving toward an enterprise focus on anti-fraud systems Regulatory expectations are increasing Solutions require commitment, investment, and talent 4/11/2563 33
Insider Threat “Deliberate misuse by those who are authorized to use computer and networks. ” l Insiders include employees, contactors, consultants, temporary helper, personnel from third-party business partner, etc. l 4/11/2563 34
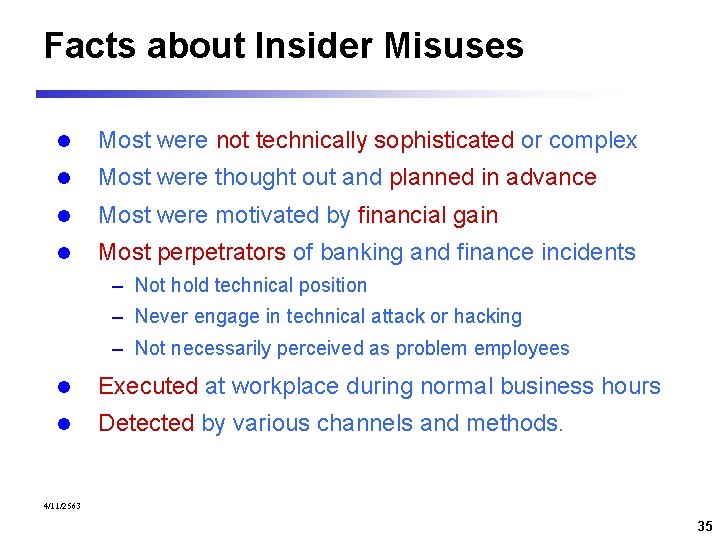
Facts about Insider Misuses l Most were not technically sophisticated or complex l Most were thought out and planned in advance l Most were motivated by financial gain l Most perpetrators of banking and finance incidents – Not hold technical position – Never engage in technical attack or hacking – Not necessarily perceived as problem employees l Executed at workplace during normal business hours l Detected by various channels and methods. 4/11/2563 35
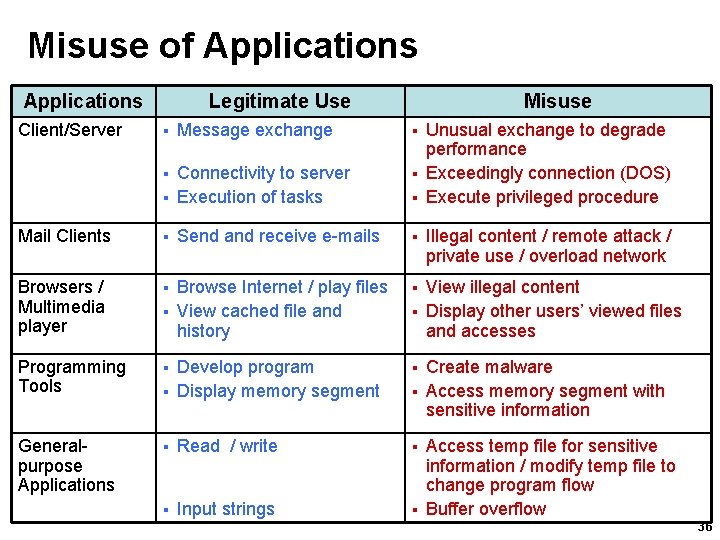
Misuse of Applications Client/Server Legitimate Use § Message exchange Connectivity to server § Execution of tasks § Mail Clients § Browsers / Multimedia player Programming Tools § Generalpurpose Applications § Read / write § Input strings 4/11/2563 Misuse Unusual exchange to degrade performance § Exceedingly connection (DOS) § Execute privileged procedure § Send and receive e-mails § § Browse Internet / play files § View cached file and history § Develop program § Display memory segment § Illegal content / remote attack / private use / overload network View illegal content § Display other users’ viewed files and accesses Create malware § Access memory segment with sensitive information Access temp file for sensitive information / modify temp file to change program flow § Buffer overflow § 36
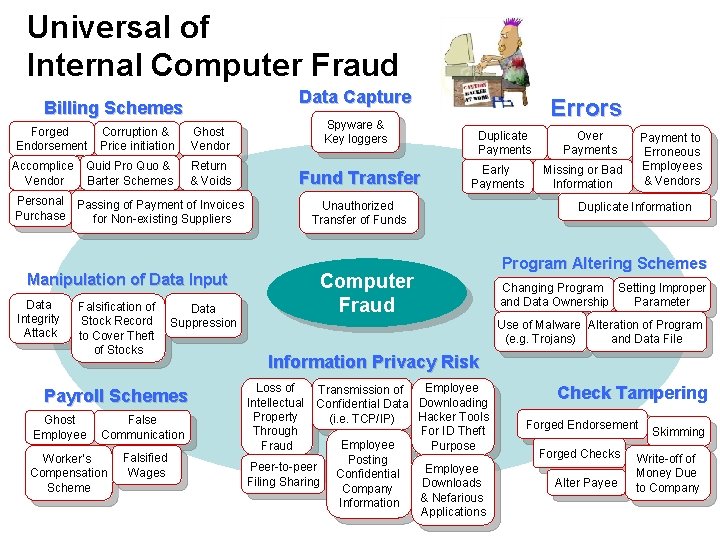
Universal of Internal Computer Fraud Data Capture Billing Schemes Forged Endorsement Accomplice Vendor Corruption & Price initiation Ghost Vendor Quid Pro Quo & Barter Schemes Return & Voids Spyware & Key loggers Fund Transfer Personal Passing of Payment of Invoices Purchase for Non-existing Suppliers Falsification of Stock Record to Cover Theft of Stocks Ghost Employee False Communication Worker’s Compensation Scheme 4/11/2563 Falsified Wages Early Payments Computer Fraud Data Suppression Payroll Schemes Duplicate Payments Unauthorized Transfer of Funds Manipulation of Data Input Data Integrity Attack Errors Over Payments Payment to Erroneous Employees & Vendors Missing or Bad Information Duplicate Information Program Altering Schemes Changing Program Setting Improper and Data Ownership Parameter Use of Malware Alteration of Program (e. g. Trojans) and Data File Information Privacy Risk Employee Transmission of Downloading Confidential Data Hacker Tools (i. e. TCP/IP) For ID Theft Employee Purpose Posting Peer-to-peer Employee Confidential Filing Sharing Downloads Company & Nefarious Information Applications Loss of Intellectual Property Through Fraud Check Tampering Forged Endorsement Forged Checks Alter Payee Skimming Write-off of Money Due to Company 3737
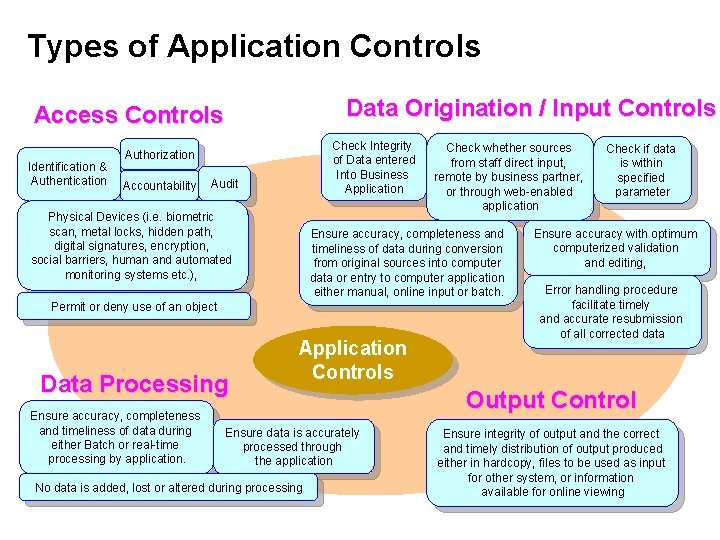
Types of Application Controls Data Origination / Input Controls Access Controls Identification & Authentication Check Integrity of Data entered Into Business Application Authorization Accountability Audit Physical Devices (i. e. biometric scan, metal locks, hidden path, digital signatures, encryption, social barriers, human and automated monitoring systems etc. ), Ensure accuracy, completeness and timeliness of data during conversion from original sources into computer data or entry to computer application either manual, online input or batch. Permit or deny use of an object Data Processing Ensure accuracy, completeness and timeliness of data during either Batch or real-time processing by application. Application Controls Ensure data is accurately processed through the application No data is added, lost or altered during processing 4/11/2563 Check whether sources from staff direct input, remote by business partner, or through web-enabled application Check if data is within specified parameter Ensure accuracy with optimum computerized validation and editing, Error handling procedure facilitate timely and accurate resubmission of all corrected data Output Control Ensure integrity of output and the correct and timely distribution of output produced either in hardcopy, files to be used as input for other system, or information available for online viewing 3838
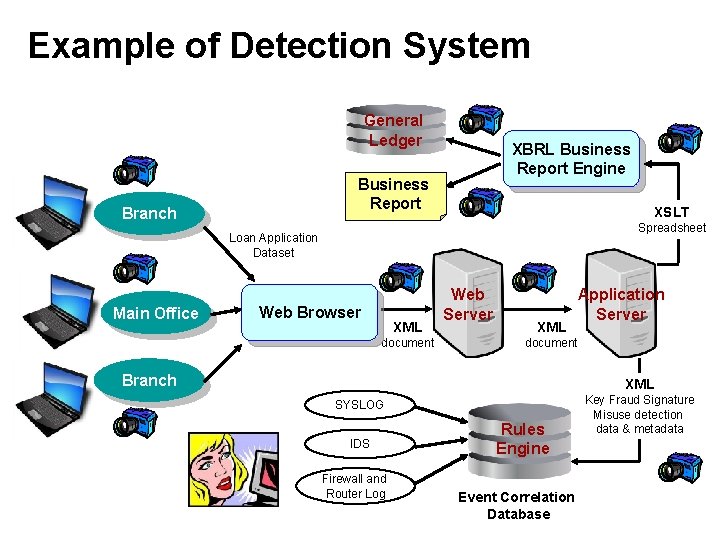
Example of Detection System General Ledger XBRL Business Report Engine Business Report Branch XSLT Spreadsheet Loan Application Dataset Main Office Web Browser XML document Web Server XML document Branch XML SYSLOG IDS 4/11/2563 Application Server Firewall and Router Log Rules Engine Event Correlation Database Key Fraud Signature Misuse detection data & metadata 3939
Managing Insider Threat l l l l l 4/11/2563 Strong authentication / biometric technologies Role-based access granted on a need-to-have basis Rotate job function / event log reading Place server and sensitive equipment in secured area Restrict physical access / lock / alarm test Wear badge / background check Default password / unused port / log-off on absence Encrypt sensitive data stored on user hard drives Store sensitive document in secured space Never issue password over unsecured channels Top 10 Banking Fraud ไพรช ศรวไลฤทธ pairat@tisco. th 55
Aware of Warning Signs l Rogue access point / wireless / remote l Disgruntled employee l A user accesses database or area of network they have never accessed before l Download spike 4/11/2563 Top 10 Banking Fraud ไพรช ศรวไลฤทธ pairat@tisco. th 56
Fraud Prevention Checklist l l l l l Good internal control Employee fraud awareness training / hotline Analytical review / surprise fraud audits Review company contracts Perception of detection / management oversight Proactive fraud policy and program / prosecution Mandatory vacations / periodic job rotation Screen job applicants Information security review / limit access / audit trail Management climate / employee support program 4/11/2563 Top 10 Banking Fraud ไพรช ศรวไลฤทธ pairat@tisco. th 57
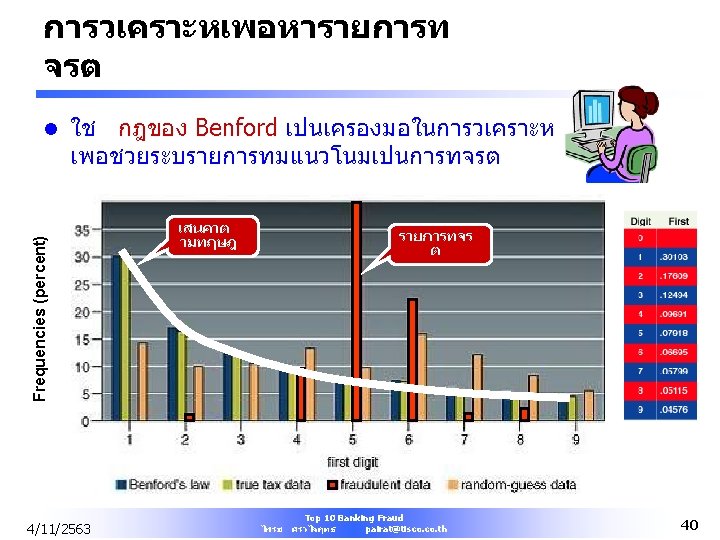
Summary Auditor's roles in combating fraud l l l l l Promote culture of honesty and high ethics Assess and mitigate the risk of fraud Ensure control adequacy and effectiveness Use data mining and statistical analysis tools Analyze financial statements reports Being alert on predication of fraud Ensure investigations are properly conducted Ensure proper follow-up actions are taken Develop your anti-fraud knowledge and skills 4/11/2563 Top 10 Banking Fraud ไพรช ศรวไลฤทธ pairat@tisco. th 58
About the ACFE l l l The Association of Certified Fraud Examiners Start 1988 Provide anti-fraud training and education Over 50, 000 members in 125 countries Administrate the Certified Fraud Examiner (CFE) designation- a certification program for fraud practitioners recognized by U. S. Department of Defense and FBI More than 20, 000 CFE’s worldwide (5 Thais) $55 Membership Fee l More information about ACFE l http: //www. acfe. com 4/11/2563 Top 10 Banking Fraud ไพรช ศรวไลฤทธ pairat@tisco. th 59
About CFE Exam l l l Covers 4 areas – Criminology & Ethics – Financial Transactions – Fraud Investigation – Legal Elements of Fraud 4 Exam sections of 125 questions each (75%) Administered via computer / must complete each section in one sitting (2. 6 hr) Complete all and return to ACFE in 30 days Must pass Qualifying Points System (40/50) $250 Application Fee 4/11/2563 Top 10 Banking Fraud ไพรช ศรวไลฤทธ pairat@tisco. th 60
Q&A PAIRAT SRIVILAIRIT SVP Head of Internal Audit TISCO Financial Group Public Company Limited Mobile : +668 1903 1457 Office : +66 2633 7821 Email : pairat@tisco. th 4/11/2563 Top 10 Banking Fraud ไพรช ศรวไลฤทธ pairat@tisco. th 61
- Slides: 61