Tools to help GDPR compliance Albert Portugal Brugada

Tools to help GDPR compliance Albert Portugal Brugada Responsable Administració Electrònica (CSUC) albert. portugal@csuc. cat
Compliance in general • • • Get Familiar With GDPR regulation. Identify what personal data are you processing. Define how to handle the personal data. Implement appropriate measures. Demonstrate your compliance.
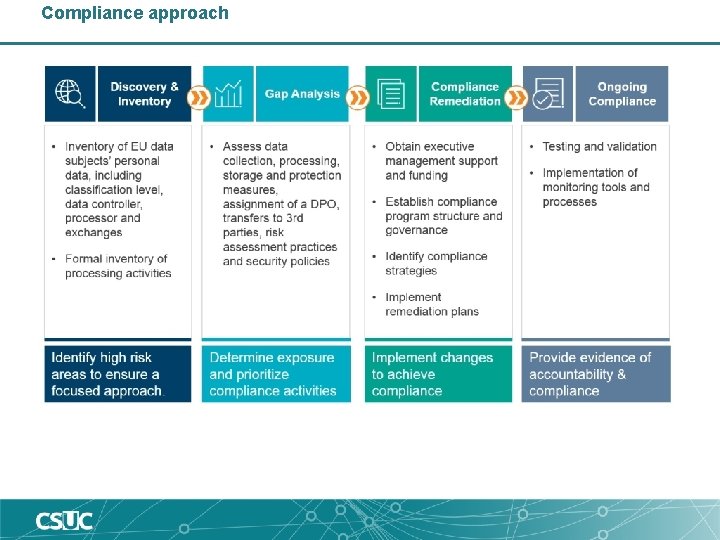
Compliance approach

Step 1
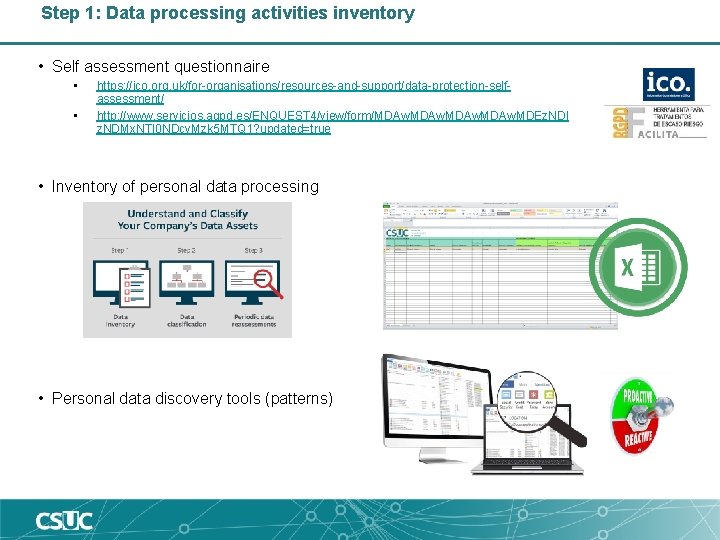
Step 1: Data processing activities inventory • Self assessment questionnaire • • https: //ico. org. uk/for-organisations/resources-and-support/data-protection-selfassessment/ http: //www. servicios. agpd. es/ENQUEST 4/view/form/MDAw. MDEz. NDI z. NDMx. NTI 0 NDcy. Mzk 5 MTQ 1? updated=true • Inventory of personal data processing • Personal data discovery tools (patterns)
Step 2
Step 2: Content management system (GDPR) • Content management system to provide information to internal participants. • Document models • Privacy by design & default guides / rules • Internal meetings & presentations • Data Processing • Inventory • Procedures
Step 2: Content management system (GDPR) • Data processing details (mandatory) • 1. Project identification • • • 1. 1 Sponsors 1. 2 Participants 1. 3 Data processors & data controllers • 2. Goals and purposes • • 2. 1 Purposes of the processing 2. 2 Lawfulness of processing 2. 3 Necessity and proportionality 2. 4 Data subjects affected • 3. Information lifecycle • • 3. 1 Input 3. 2 Storage 3. 3 Access 3. 4 Erasure • 4. Layer analysis • • • 4. 1 Key procedures 4. 2 Conceptual data model 4. 3 Agents 4. 4 Information flow 4. 5 Technologies
Step 2: Content management system (GDPR) • Risk assessment (mandatory) • 1. Project context • 2. Goals and objectives • 3. Methodology used • 4. Potential risk scenarios • 5. Analysis • 6. Conclusions and recommendations • PIA necessity (mandatory) • 1. Project identification • Evaluation team • 2. Necessity analysis • Motivation • 3. Risk assessment
Step 2: Content management system (GDPR) • Privacy impact assessment • 1. Project identification • Evaluation team • 2. Executive briefing • 3. PIA result and necessity • 4. Detailed project description • Data processing • Necessity and proportionality • 5. Result of data protection authorities’ questions • 6. Identification and risk management • 7. Conclusions • Final analysis • Recommendations • Measures to implement • PIA public report • • • 1. Introduction 2. Description 3. Questions to third parties 4. Risk management 5. Contact information for further information Transparency portal
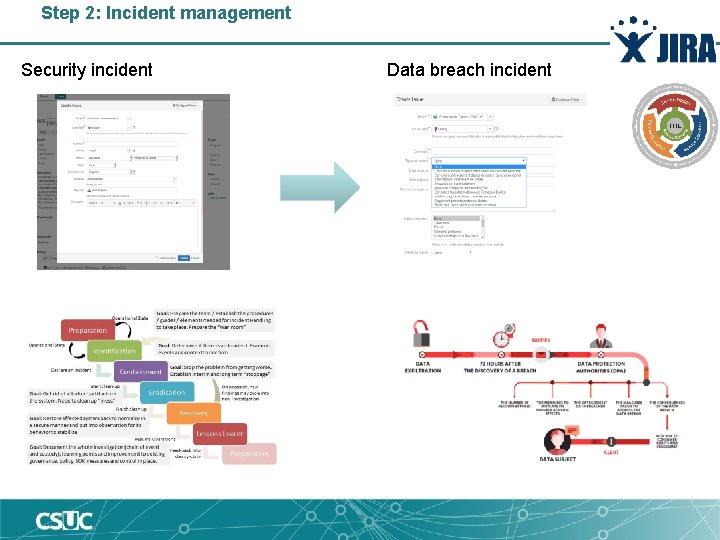
Step 2: Incident management Security incident Data breach incident
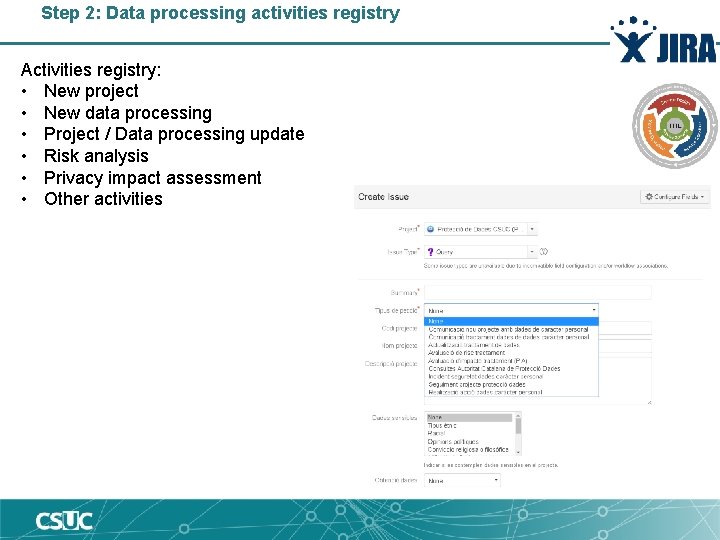
Step 2: Data processing activities registry Activities registry: • New project • New data processing • Project / Data processing update • Risk analysis • Privacy impact assessment • Other activities
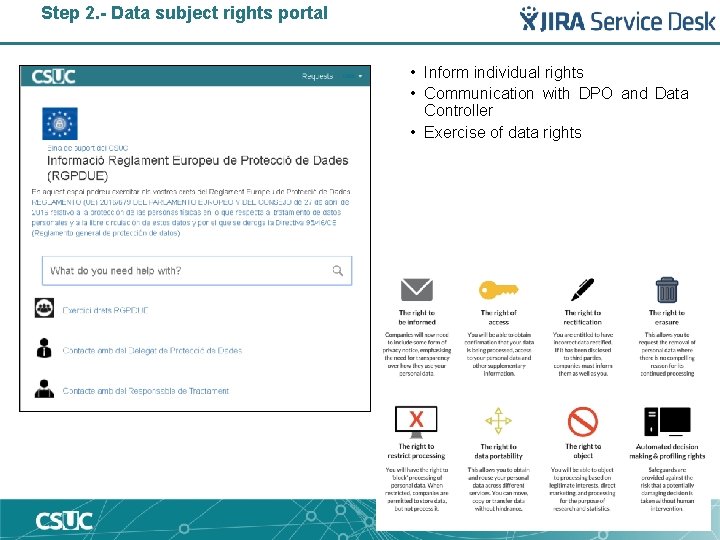
Step 2. - Data subject rights portal • Inform individual rights • Communication with DPO and Data Controller • Exercise of data rights
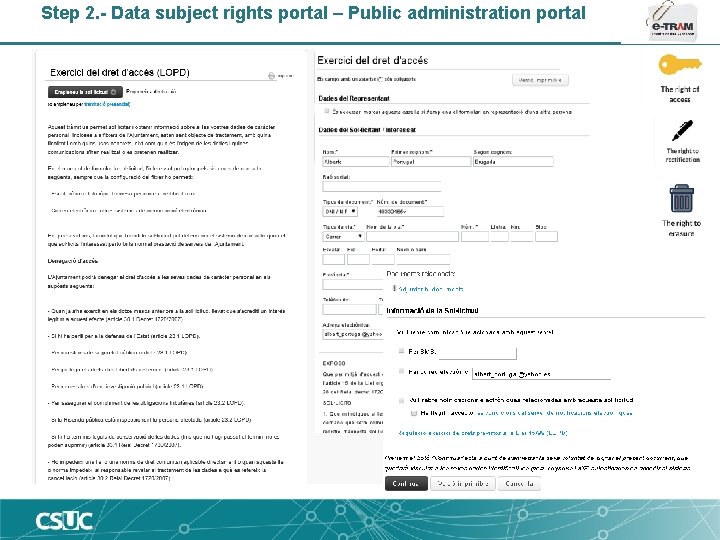
Step 2. - Data subject rights portal – Public administration portal
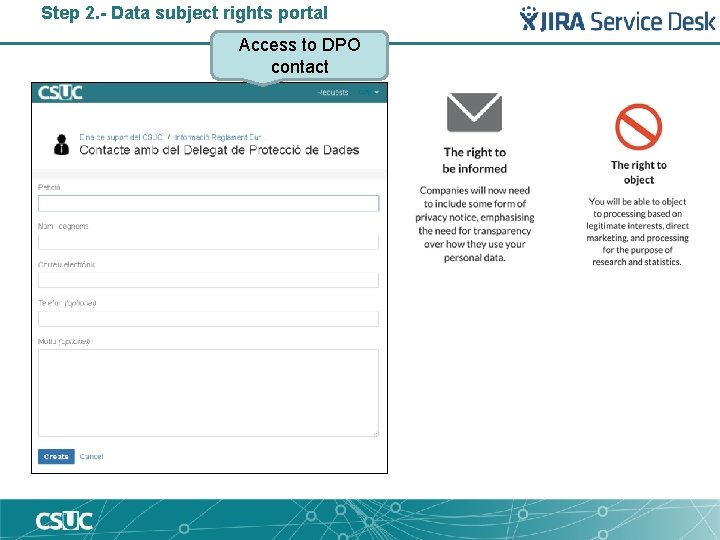
Step 2. - Data subject rights portal Access to DPO contact
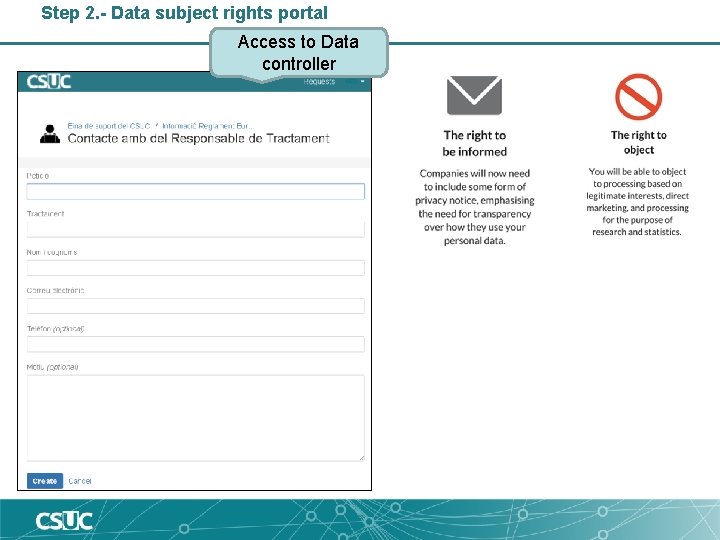
Step 2. - Data subject rights portal Access to Data controller
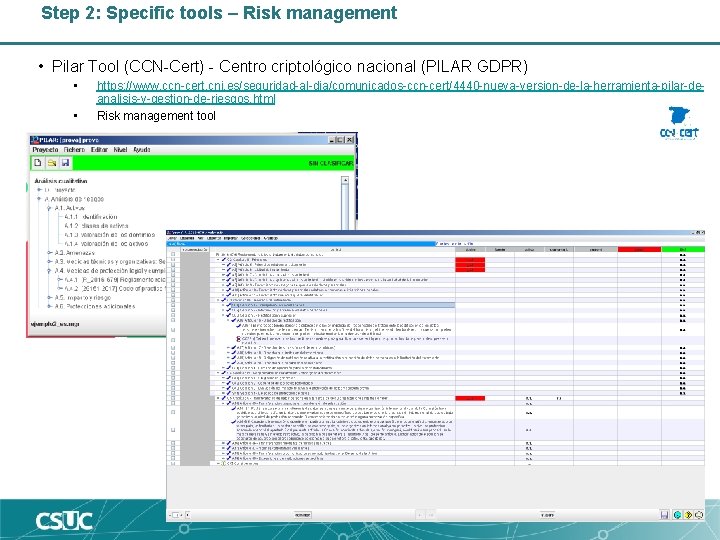
Step 2: Specific tools – Risk management • Pilar Tool (CCN-Cert) - Centro criptológico nacional (PILAR GDPR) • • https: //www. ccn-cert. cni. es/seguridad-al-dia/comunicados-ccn-cert/4440 -nueva-version-de-la-herramienta-pilar-deanalisis-y-gestion-de-riesgos. html Risk management tool
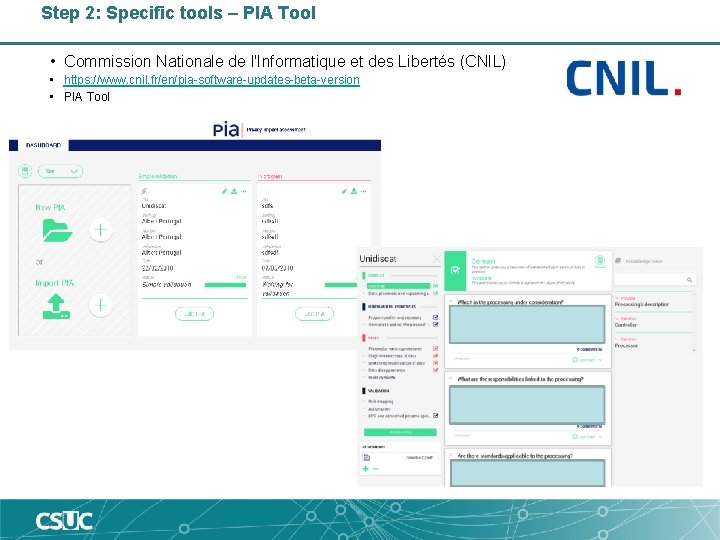
Step 2: Specific tools – PIA Tool • Commission Nationale de l'Informatique et des Libertés (CNIL) • https: //www. cnil. fr/en/pia-software-updates-beta-version • PIA Tool
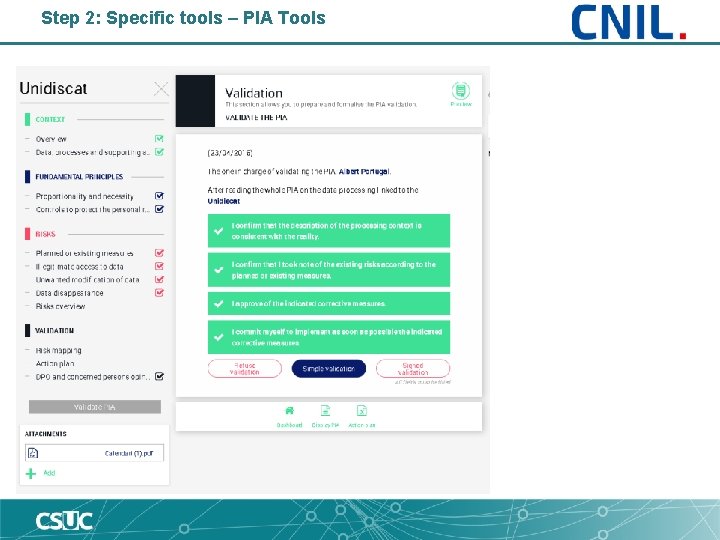
Step 2: Specific tools – PIA Tools
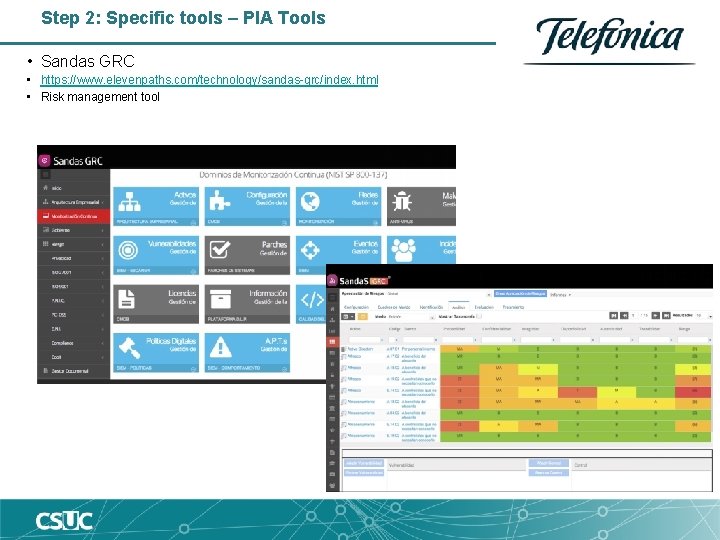
Step 2: Specific tools – PIA Tools • Sandas GRC • https: //www. elevenpaths. com/technology/sandas-grc/index. html • Risk management tool
Step 2: Specific tools – GDPR management • One Trust • https: //onetrust. com/
Step 3
Step 3: Privacy by design
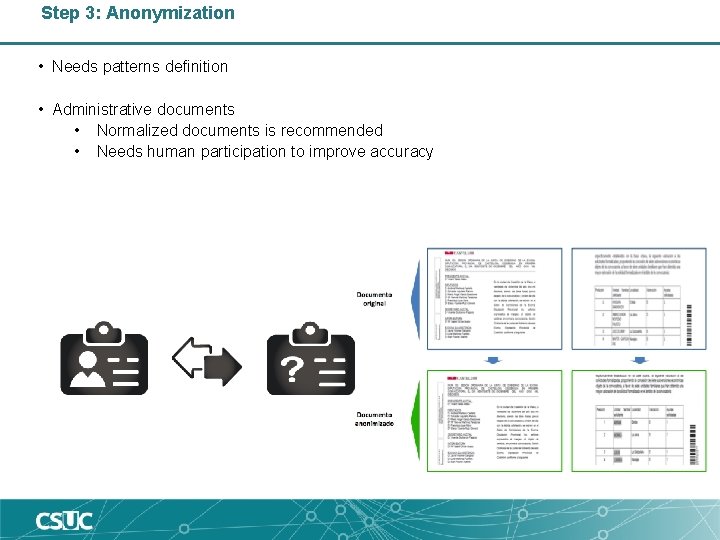
Step 3: Anonymization • Needs patterns definition • Administrative documents • Normalized documents is recommended • Needs human participation to improve accuracy
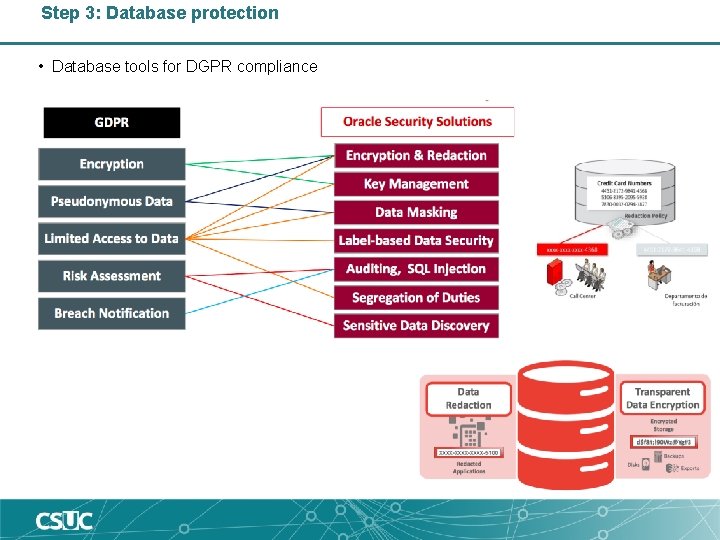
Step 3: Database protection • Database tools for DGPR compliance
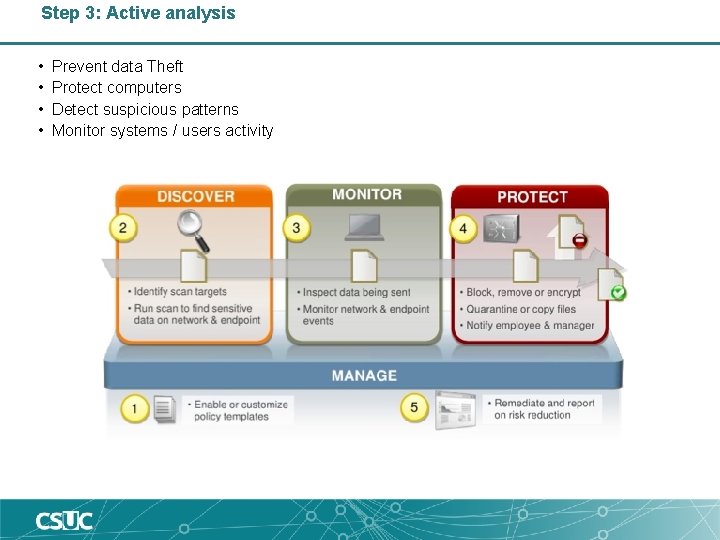
Step 3: Active analysis • • Prevent data Theft Protect computers Detect suspicious patterns Monitor systems / users activity
Step 3: Electronic evidence tools • Blockchain technology • • Timestamp Transaction data Hash of previous block Distributed computing system • Data collections: • • • Consents Users activities related to personal data Processing personal data activities Contracts … • Uses: • • Store Retrieve Investigate incidents Demostrate

Step 3: Application analysis tools • • • Penetration testing Vulnerability scanning tools Web application testing Software testing tools Source code analysis
Step 4
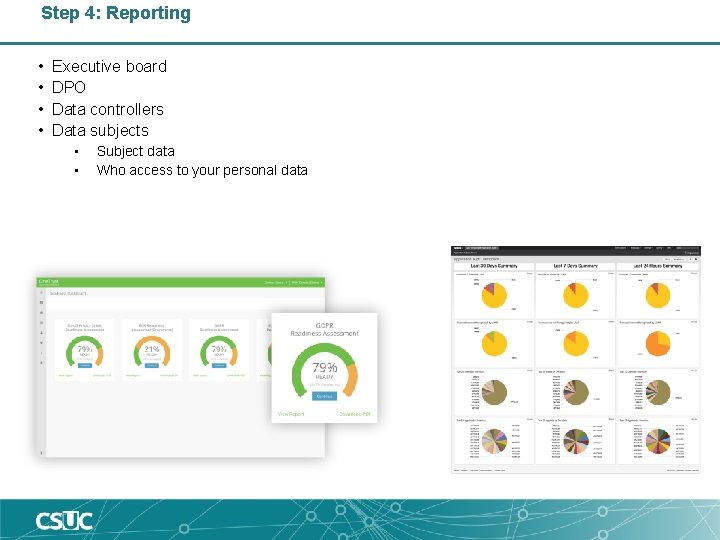
Step 4: Reporting • • Executive board DPO Data controllers Data subjects • • Subject data Who access to your personal data
- Slides: 30