Token Based Authorization of GMPLS Networks By Leon
Token Based Authorization of GMPLS Networks By: Leon Gommans, Paola Grosso, Fred Wan, Cees de Laat, Marten Hoekstra, Li Xu University of Amsterdam
Why are tokens a useful concept to implement with GMPLS networks? -Enables fast link access at network ingress - Deals with complex authorization process separately and in advance. - Can be linked to reservations. - Allows multi-domain support: Network egress generates token for next domain. - Tokens support both billing and pre-paid models. T T T T.
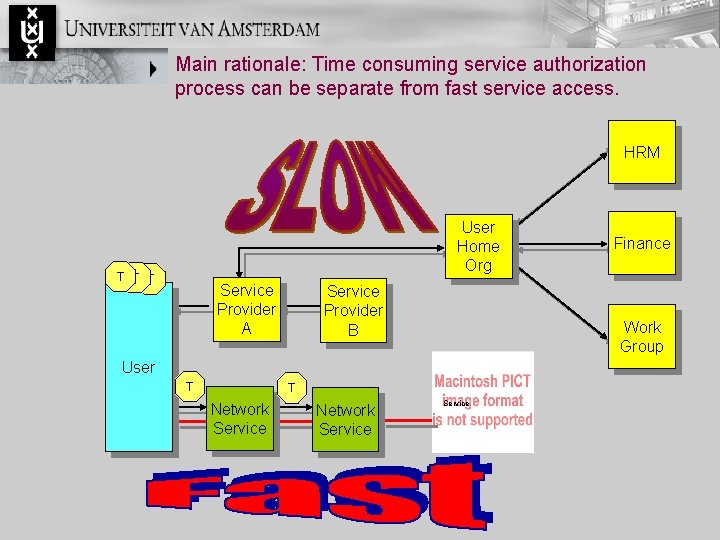
Main rationale: Time consuming service authorization process can be separate from fast service access. HRM User Home Org T T T Service Provider A Service Provider B Work Group User T T Network Service Finance Service

Functional overview SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcement Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B
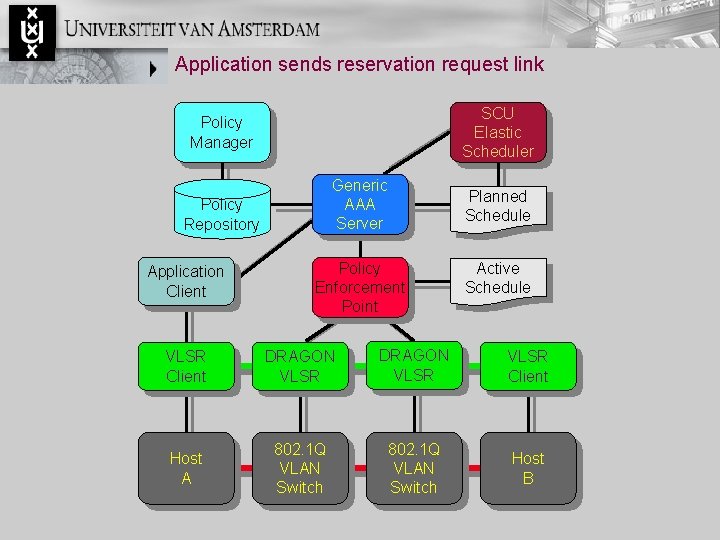
Application sends reservation request link SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcement Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B
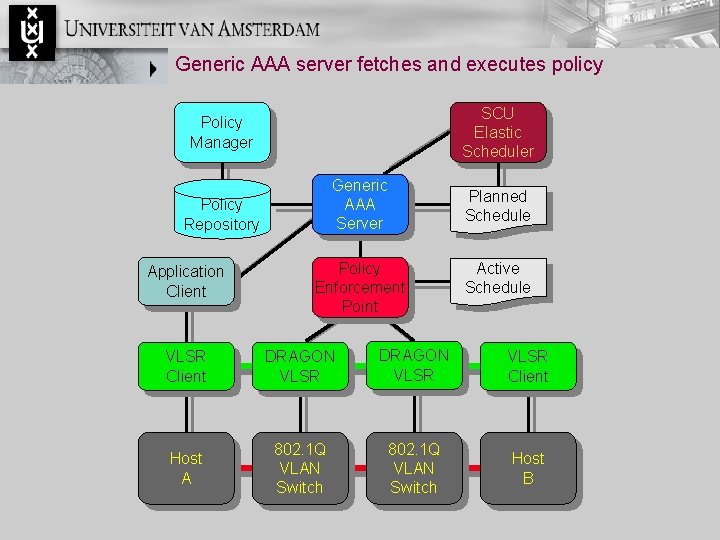
Generic AAA server fetches and executes policy SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcement Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B
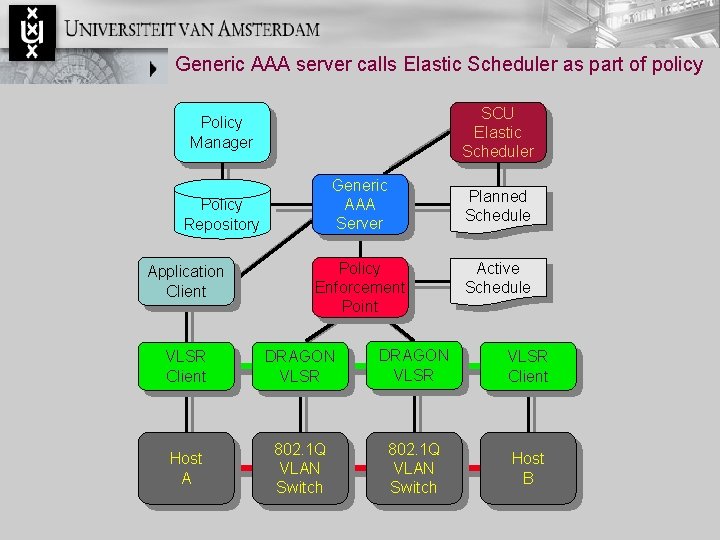
Generic AAA server calls Elastic Scheduler as part of policy SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcement Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B
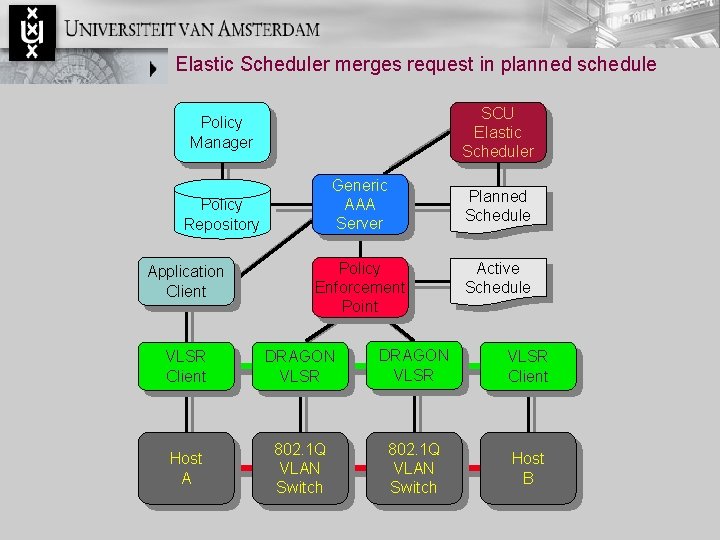
Elastic Scheduler merges request in planned schedule SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcement Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B
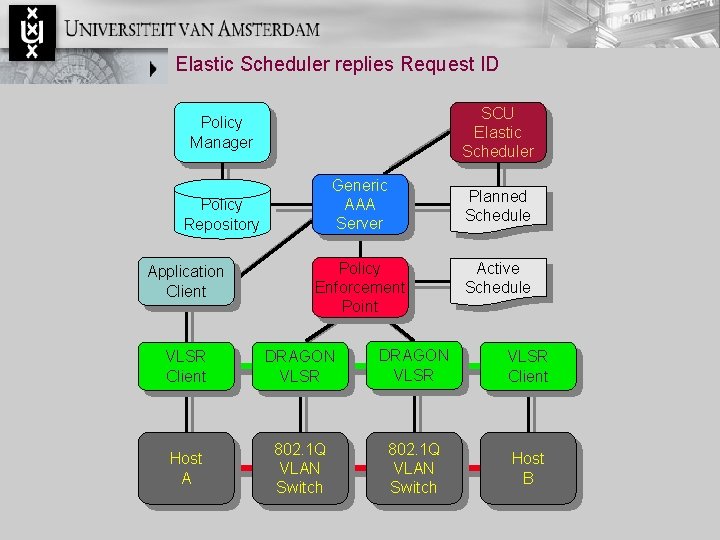
Elastic Scheduler replies Request ID SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcement Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B
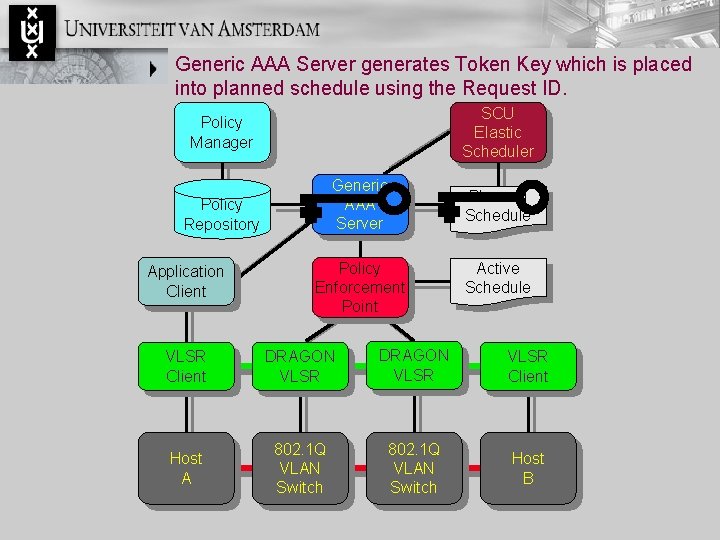
Generic AAA Server generates Token Key which is placed into planned schedule using the Request ID. SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcement Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B
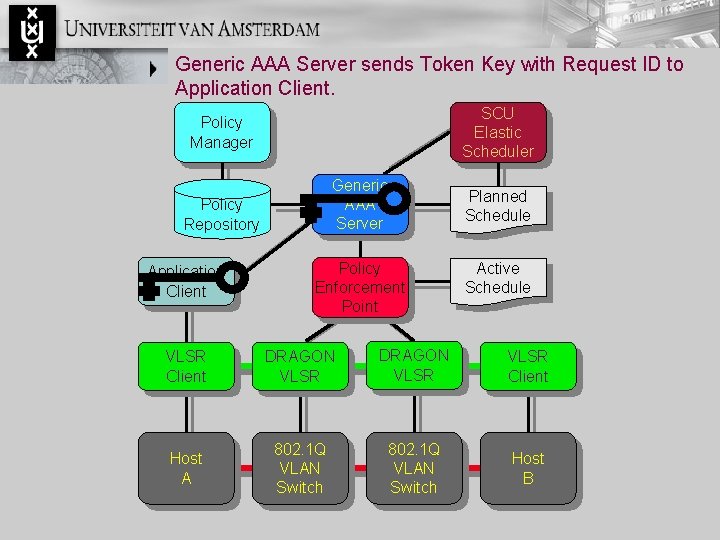
Generic AAA Server sends Token Key with Request ID to Application Client. SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcement Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B
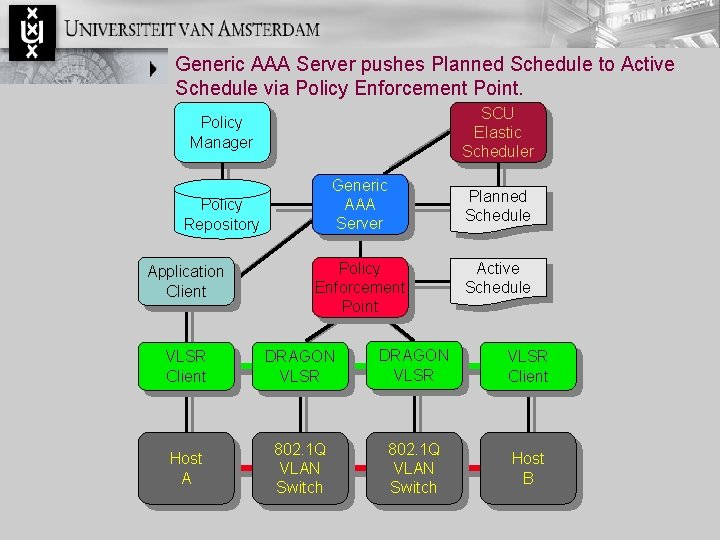
Generic AAA Server pushes Planned Schedule to Active Schedule via Policy Enforcement Point. SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcement Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B
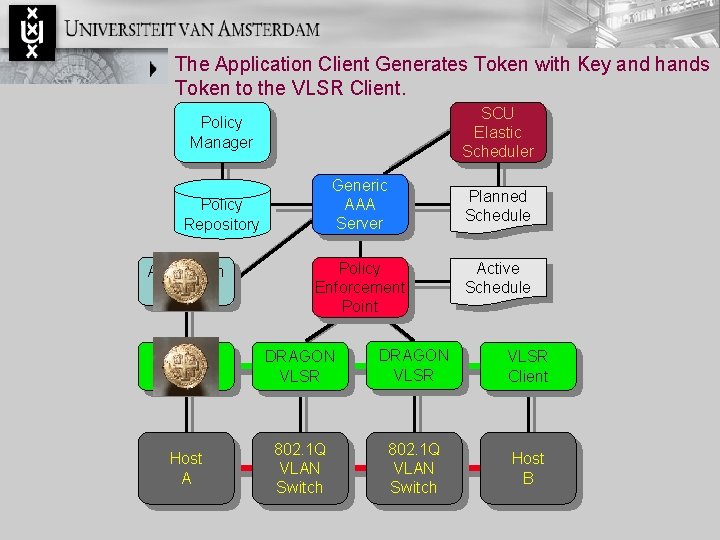
The Application Client Generates Token with Key and hands Token to the VLSR Client. SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcement Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B
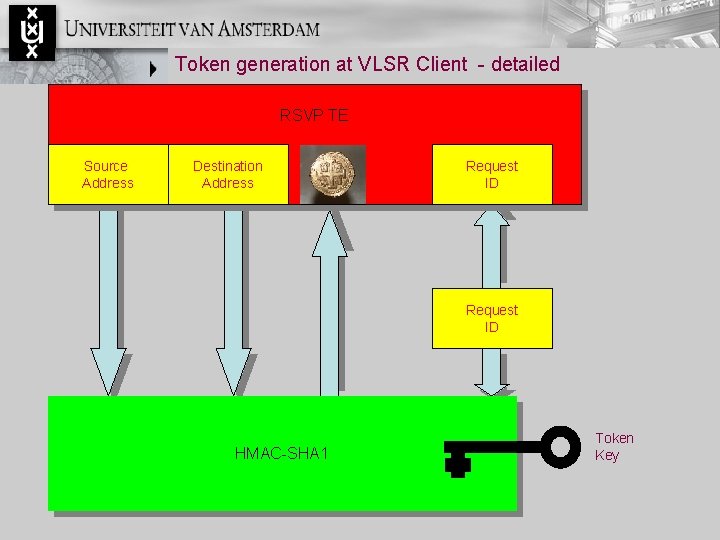
Token generation at VLSR Client - detailed RSVP TE Source Address Destination Address Request ID HMAC-SHA 1 Token Key
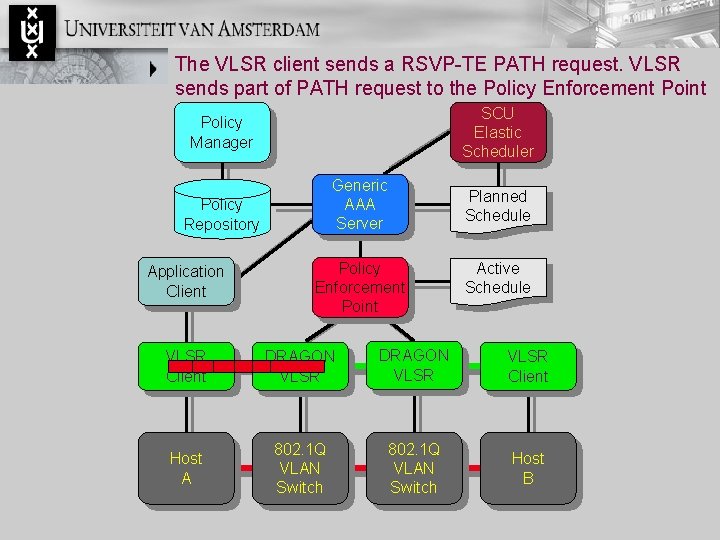
The VLSR client sends a RSVP-TE PATH request. VLSR sends part of PATH request to the Policy Enforcement Point SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcement Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B

Token validation at Policy Enforcement Point - detailed RSVP TE Source Address Destination Address Active Schedule Table Request ID Token verify Time slot verify HMAC-SHA 1
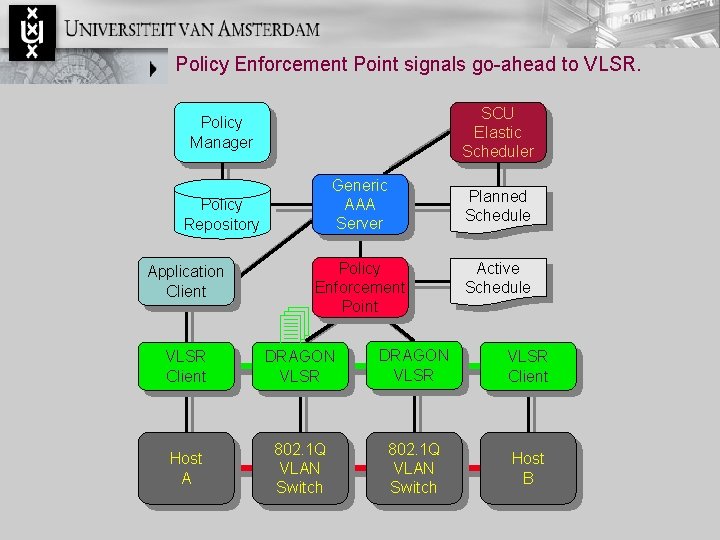
Policy Enforcement Point signals go-ahead to VLSR. SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcement Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B
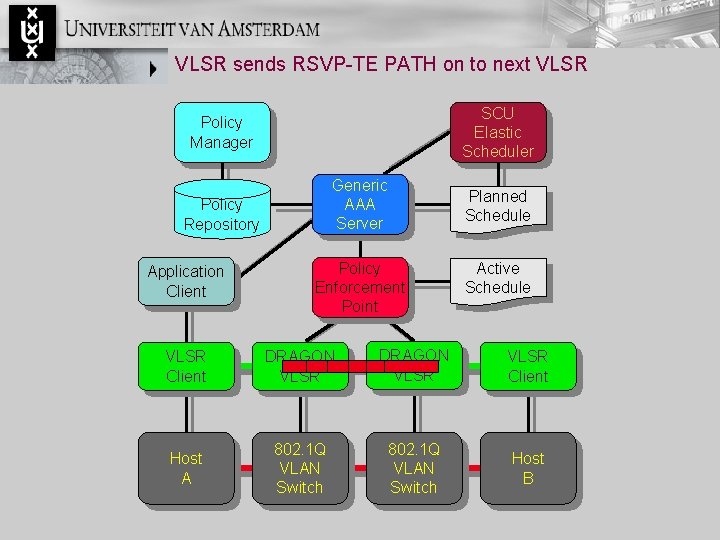
VLSR sends RSVP-TE PATH on to next VLSR SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcement Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B
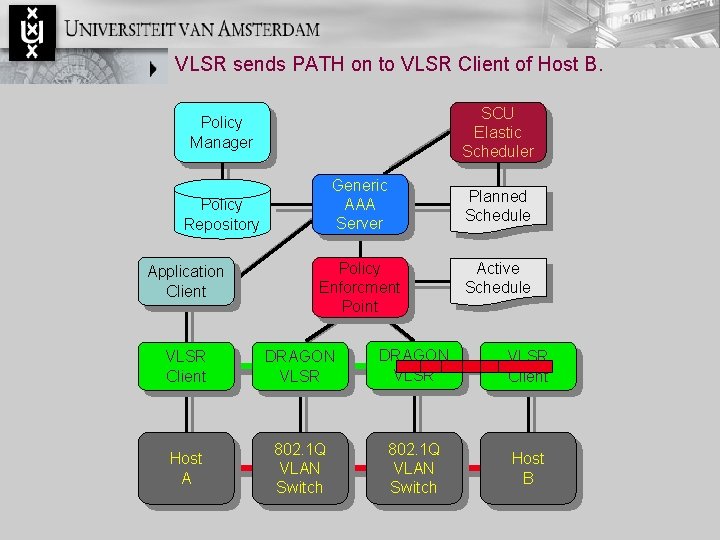
VLSR sends PATH on to VLSR Client of Host B. SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcment Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B
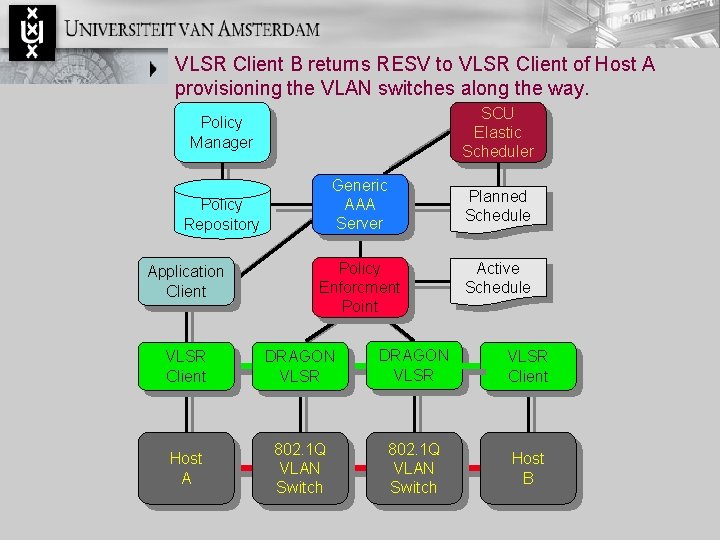
VLSR Client B returns RESV to VLSR Client of Host A provisioning the VLAN switches along the way. SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcment Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B
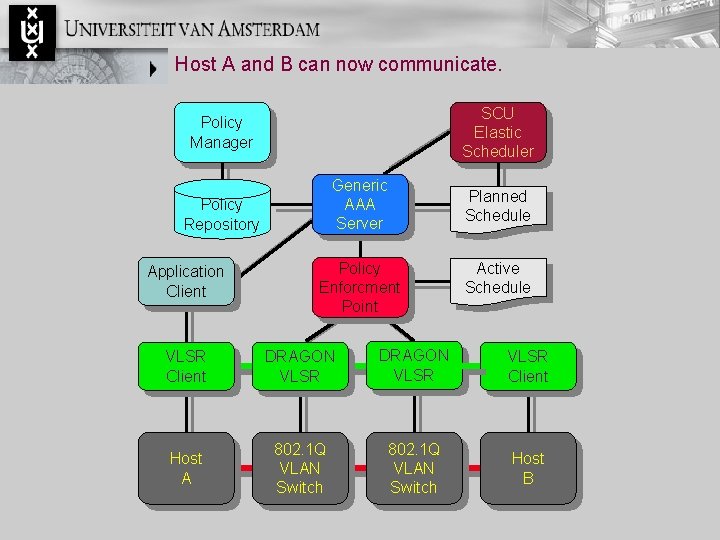
Host A and B can now communicate. SCU Elastic Scheduler Policy Manager Generic AAA Server Policy Repository Application Client Policy Enforcment Point Planned Schedule Active Schedule VLSR Client DRAGON VLSR Client Host A 802. 1 Q VLAN Switch Host B

Acknowledgement. Santa Clara University: Elastic Scheduler Sumit Naiksatam, Cameron Boehmer, Silvia Figueira Internet 2: Conceptual Input regarding authorization models John Vollbrecht DRAGON Project: GMPLS control plane Chris Tracey SARA: Network Testbed Ronald van der Pol. .

Thank you for watching
- Slides: 23