Time Crypt Encrypted Data Stream Processing at Scale
- Slides: 24
Time. Crypt- Encrypted Data Stream Processing at Scale with Cryptographic Access Control Lukas Burkhalter, Anwar Hithnawi, Alexander Viand, Hossein Shafagh, Sylvia Ratnasamy, NSDI ’ 20 Minhyeok Kang Network Convergence and Security Laboratory mhkang@mmlab. snu. ac. kr Network Convergence & Security Lab.
Outline • Introduction • Time. Crypt • Evaluation • Summary Network Convergence & Security Lab. 2 / 24
Introduction
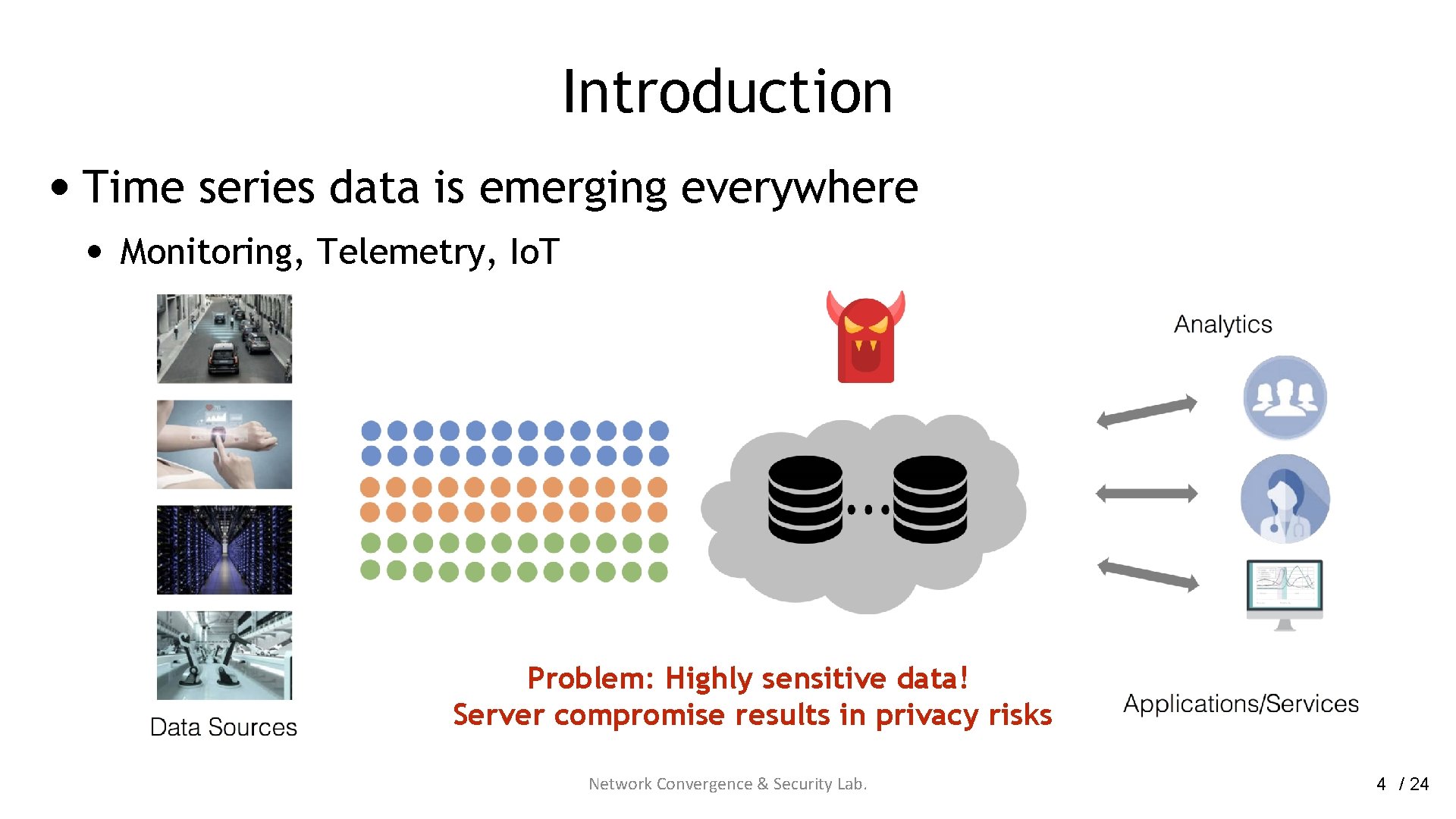
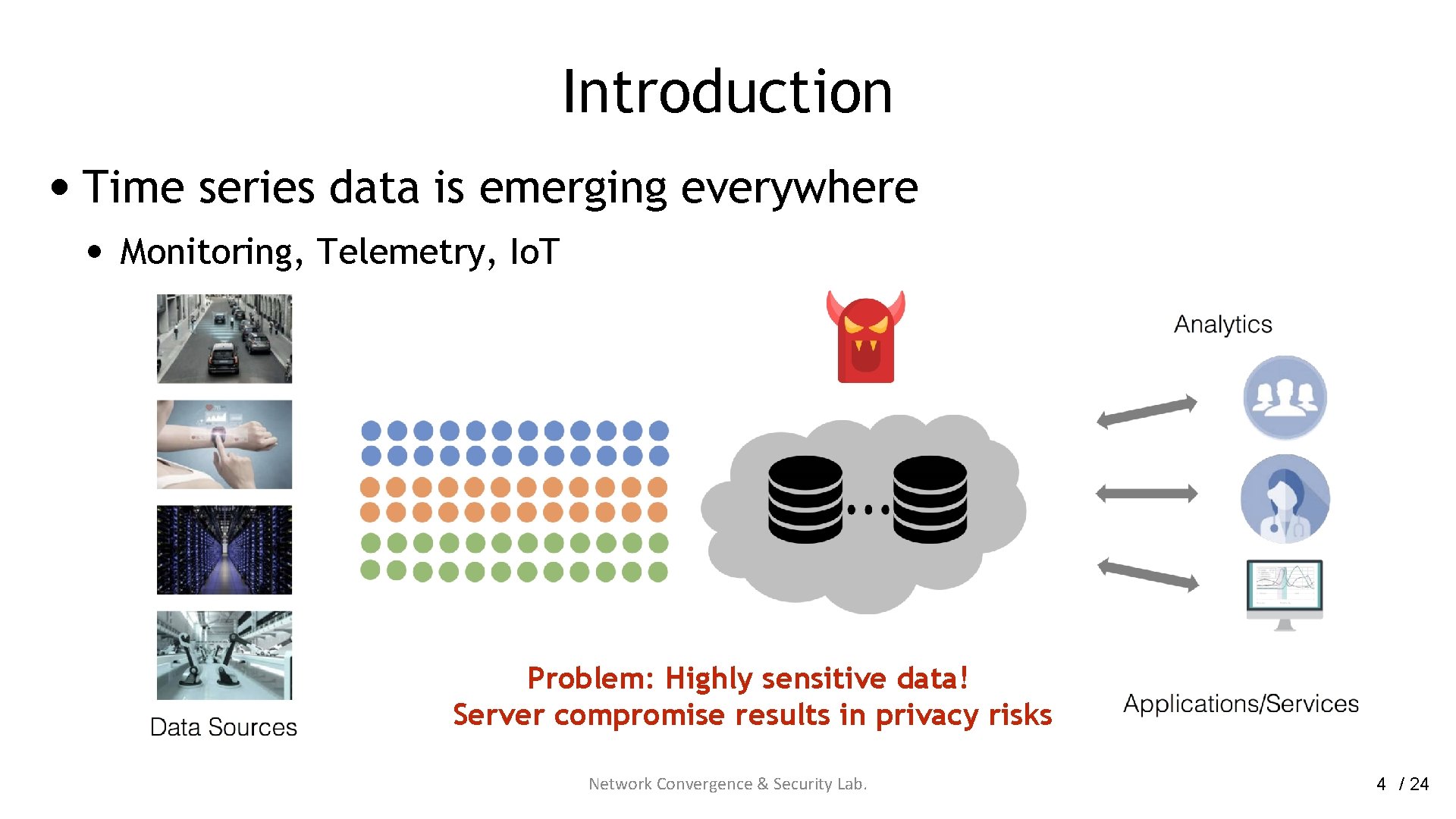
Introduction • Time series data is emerging everywhere • Monitoring, Telemetry, Io. T Problem: Highly sensitive data! Server compromise results in privacy risks Network Convergence & Security Lab. 4 / 24
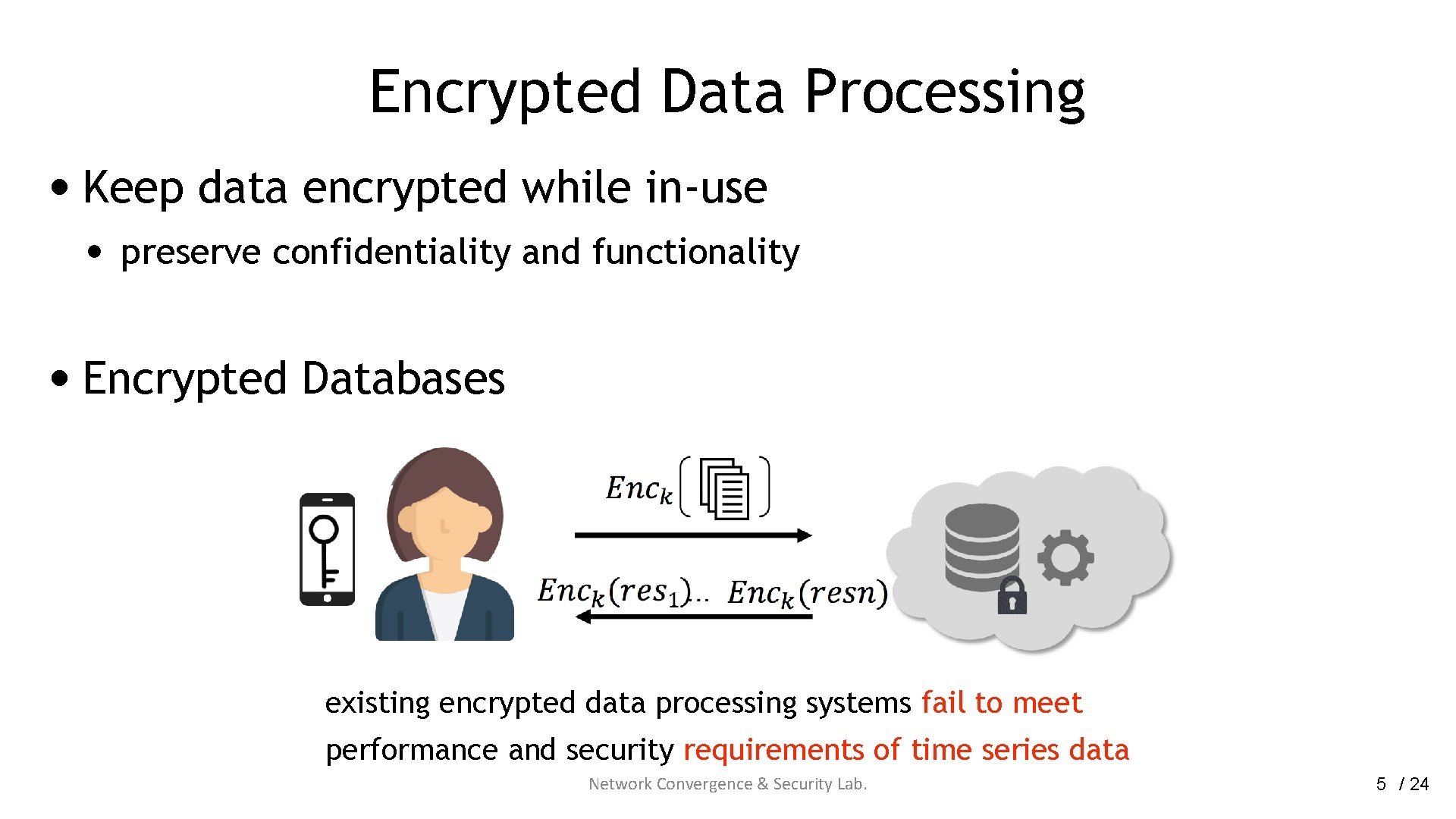
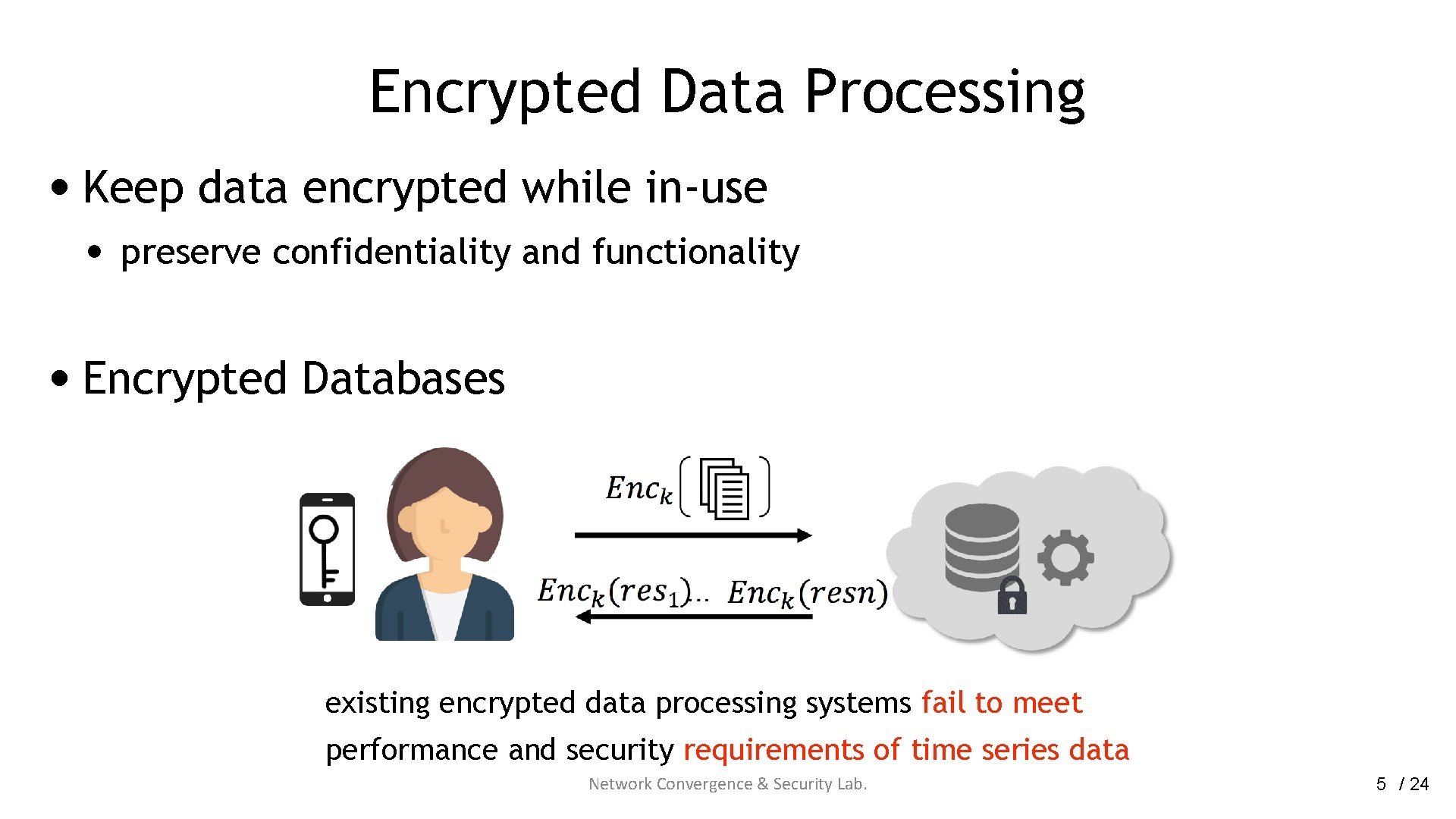
Encrypted Data Processing • Keep data encrypted while in-use • preserve confidentiality and functionality • Encrypted Databases existing encrypted data processing systems fail to meet performance and security requirements of time series data Network Convergence & Security Lab. 5 / 24
Requirements • Scalability and interactivity • • • High throughput writes Large volumes of data Low-Latency interactive queries • Overhead of the crypto primitives in encrypted data processing needs to be low Network Convergence & Security Lab. 6 / 24
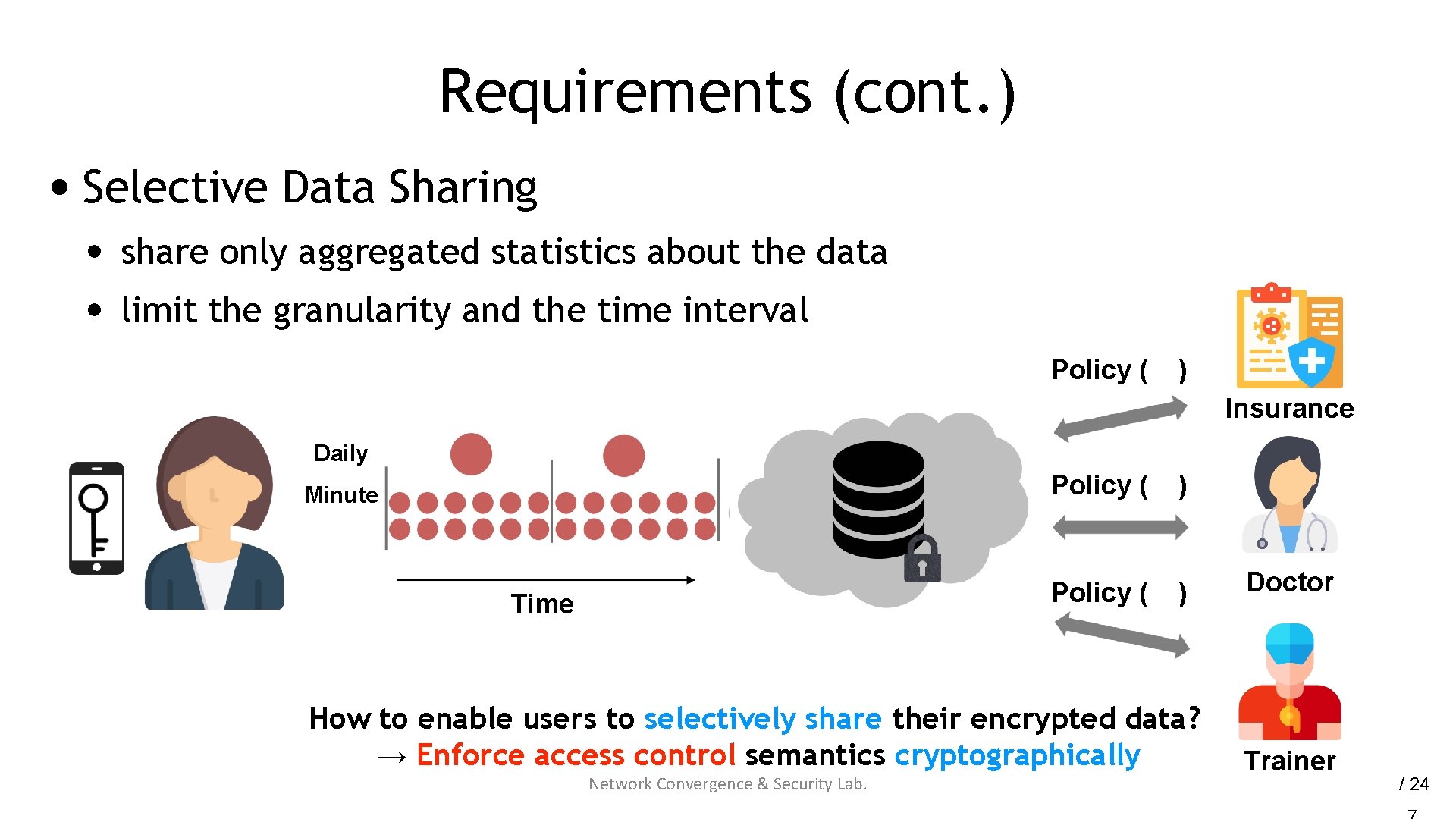
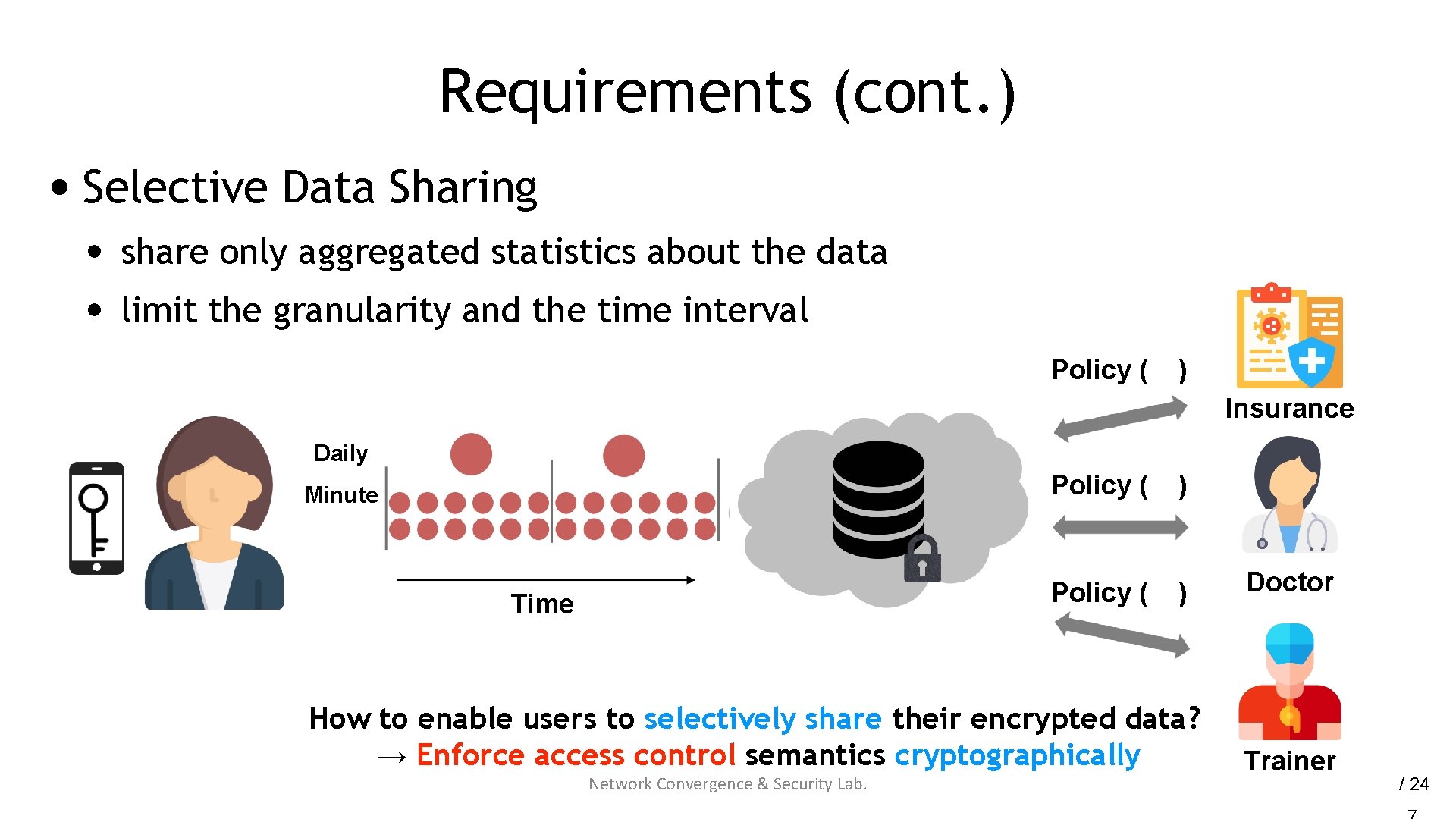
Requirements (cont. ) • Selective Data Sharing • • share only aggregated statistics about the data limit the granularity and the time interval Policy ( ) Insurance Daily Policy ( Minute Policy ( Time ) ) How to enable users to selectively share their encrypted data? → Enforce access control semantics cryptographically Network Convergence & Security Lab. Doctor Trainer / 24
Time. Crypt
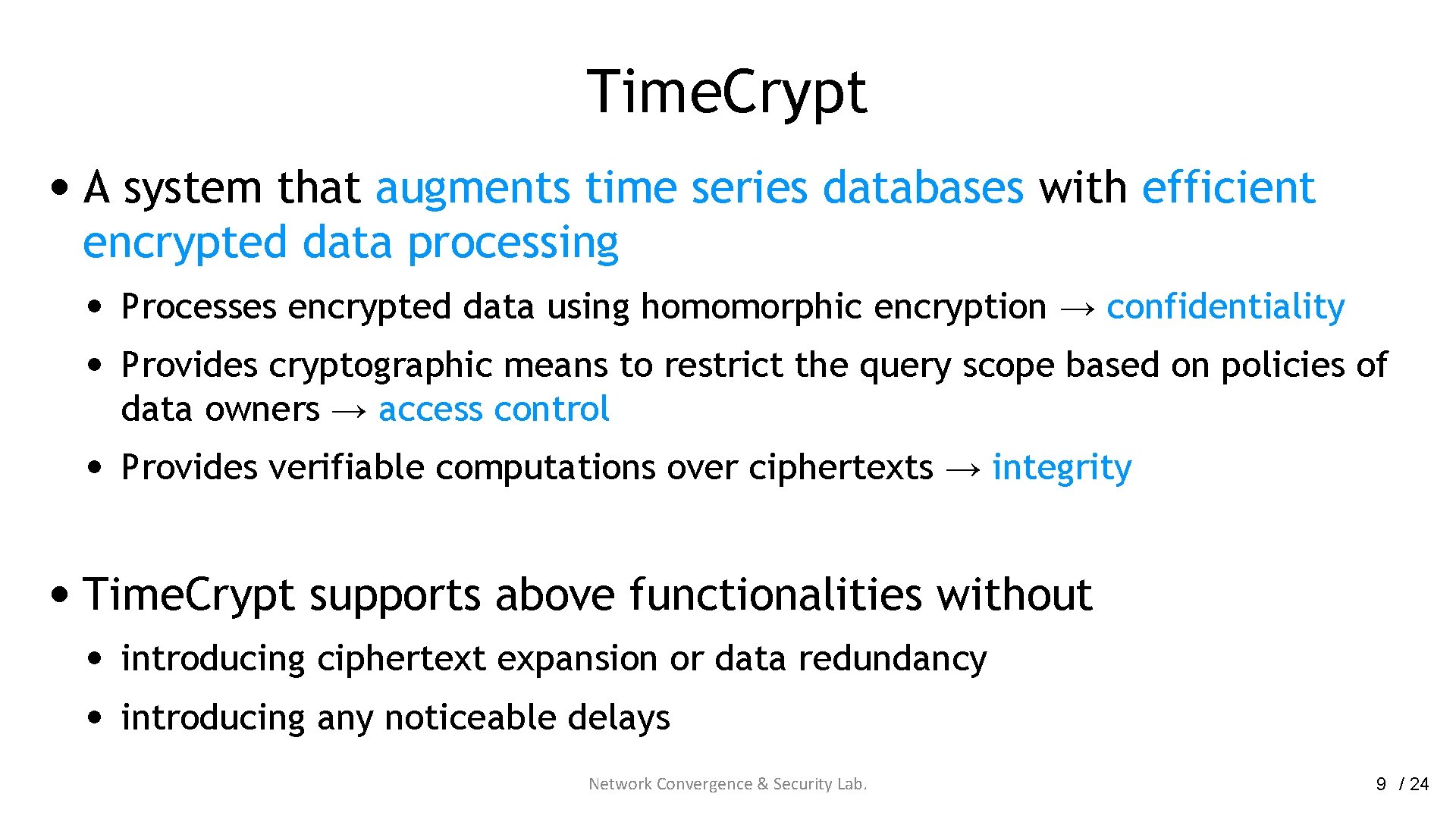
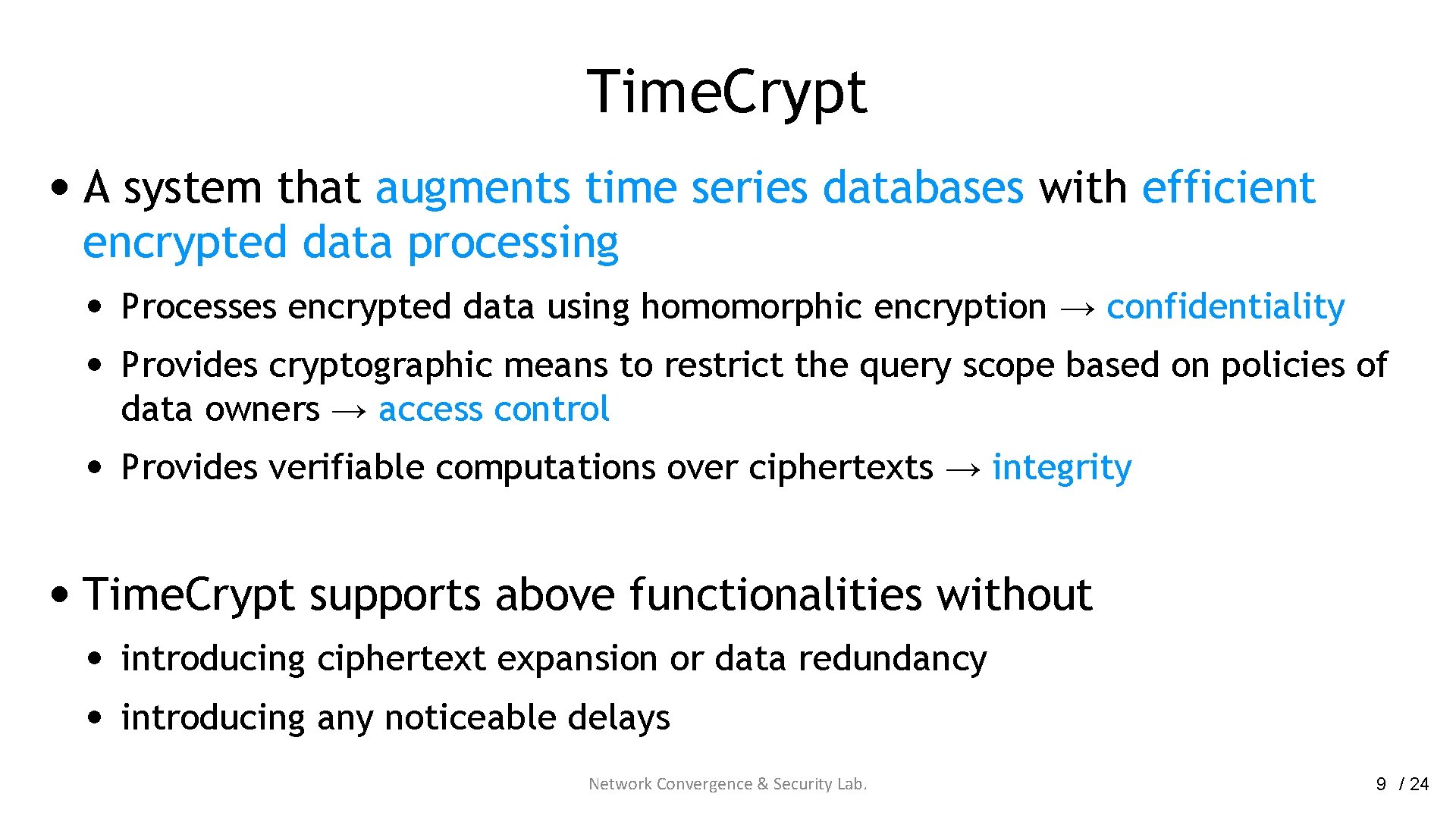
Time. Crypt • A system that augments time series databases with efficient encrypted data processing • Processes encrypted data using homomorphic encryption → confidentiality • Provides cryptographic means to restrict the query scope based on policies of data owners → access control • Provides verifiable computations over ciphertexts → integrity • Time. Crypt supports above functionalities without • • introducing ciphertext expansion or data redundancy introducing any noticeable delays Network Convergence & Security Lab. 9 / 24
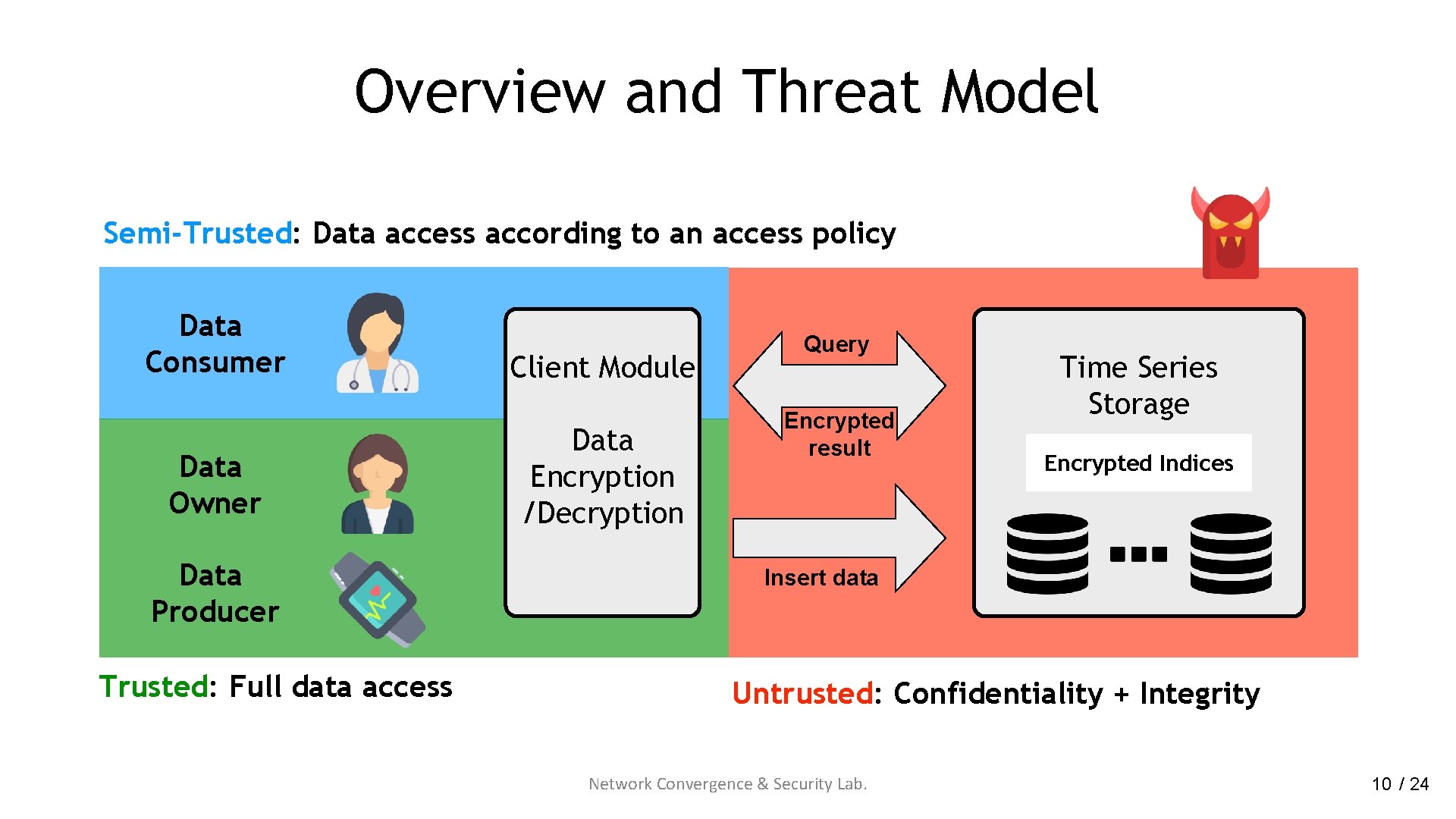
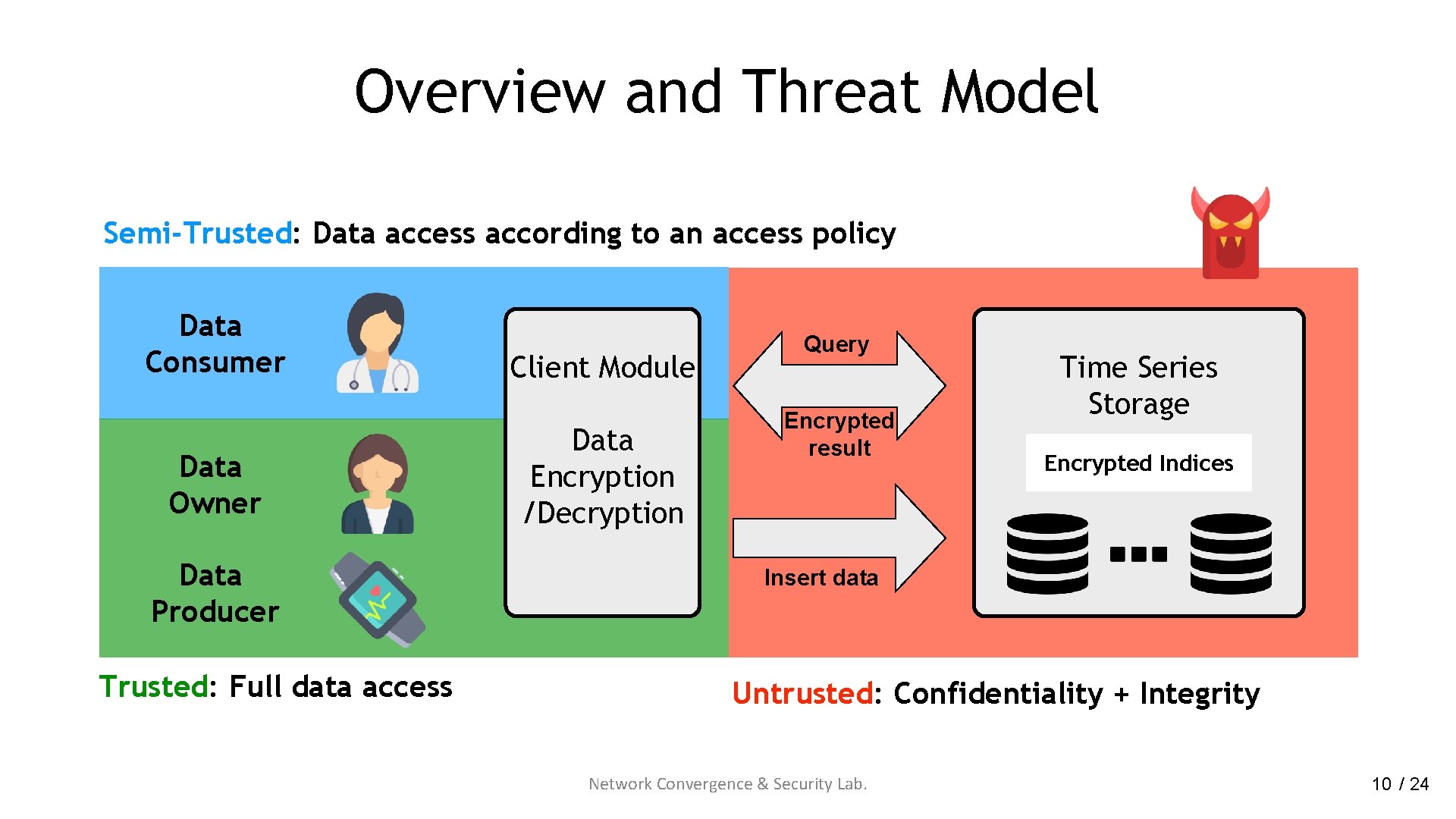
Overview and Threat Model Semi-Trusted: Data access according to an access policy Data Consumer Data Owner Data Producer Trusted: Full data access Client Module Data Encryption /Decryption Query Encrypted result Time Series Storage Encrypted Indices Insert data Untrusted: Confidentiality + Integrity Network Convergence & Security Lab. 10 / 24
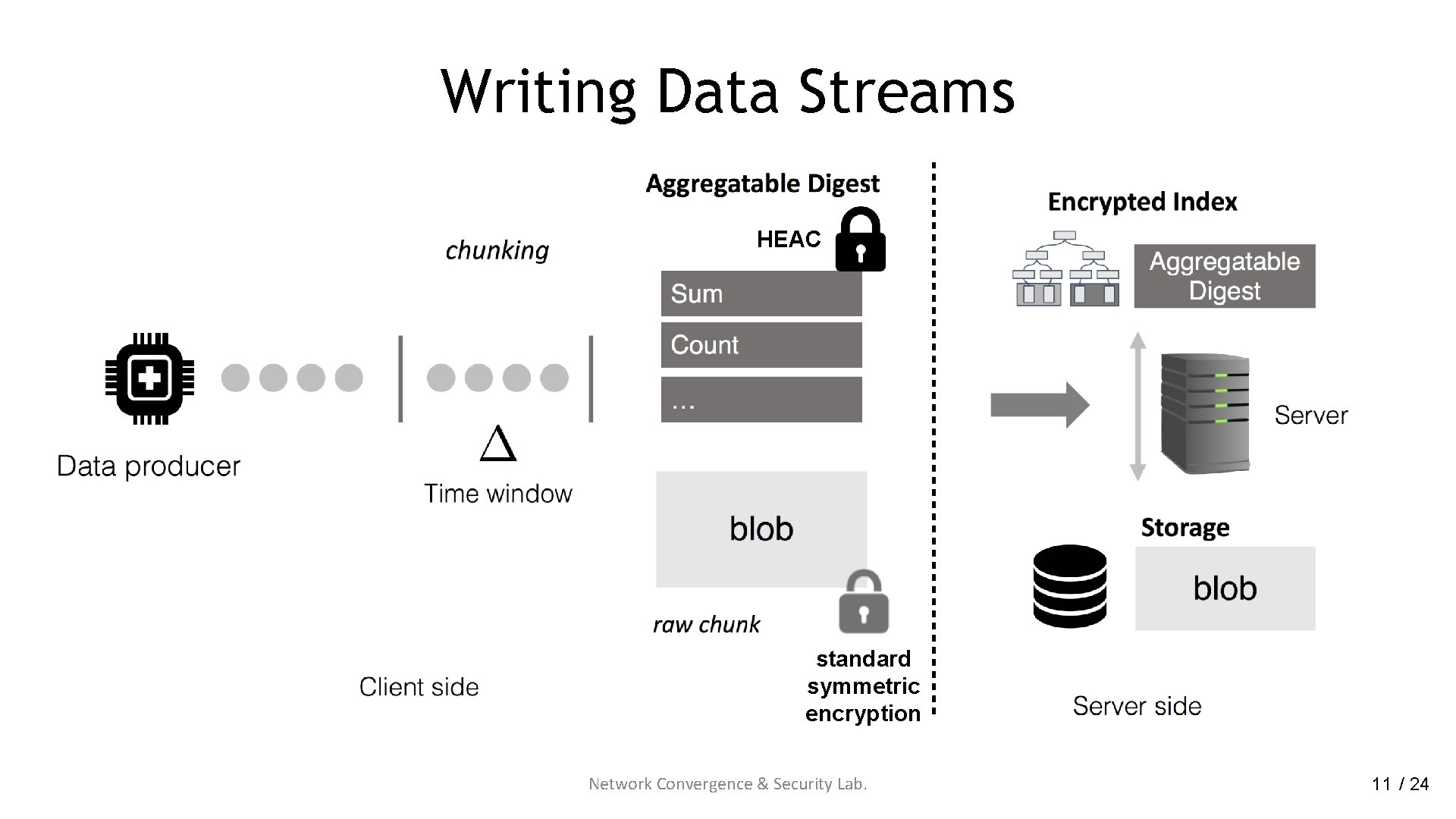
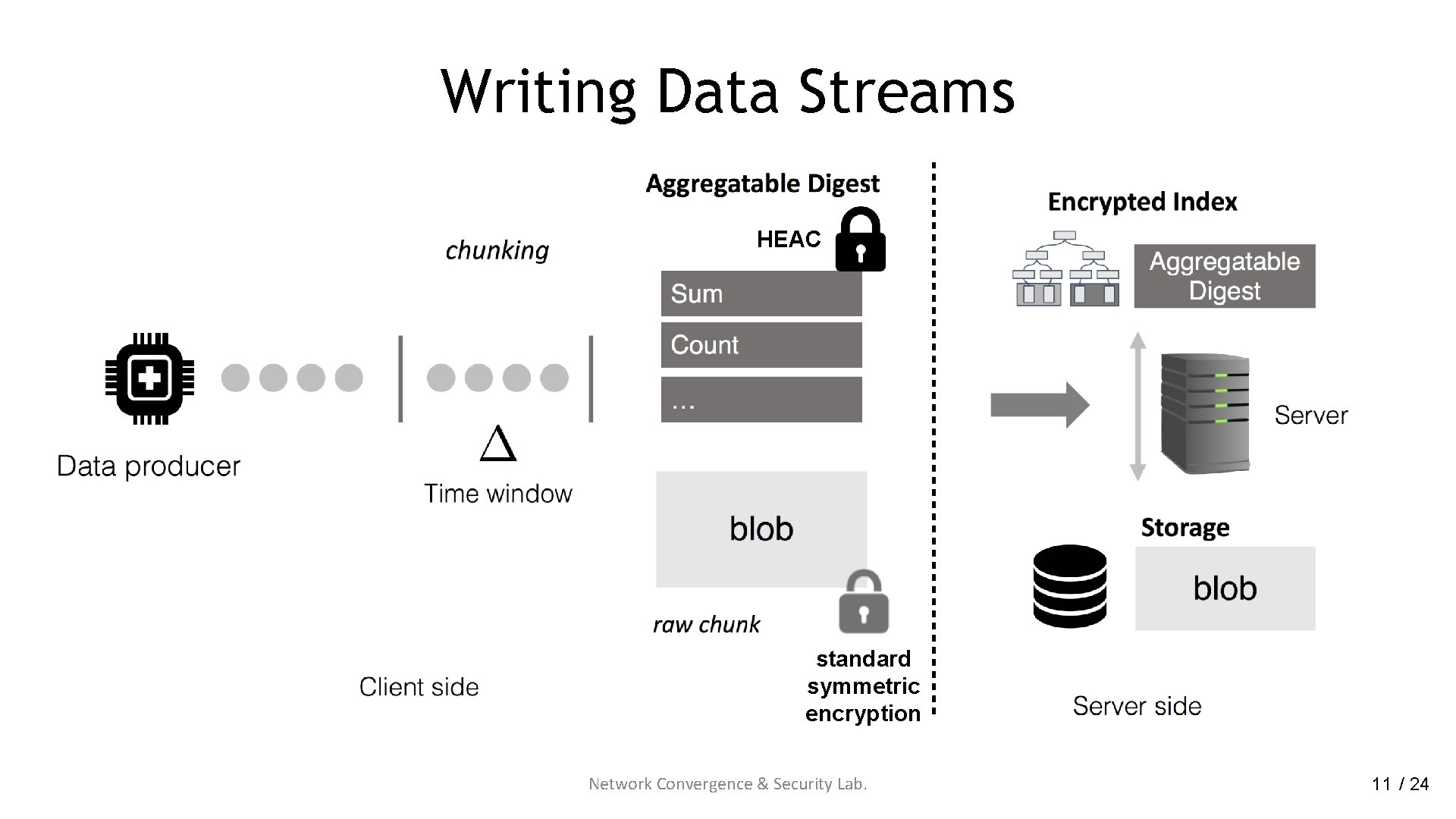
Writing Data Streams HEAC standard symmetric encryption Network Convergence & Security Lab. 11 / 24
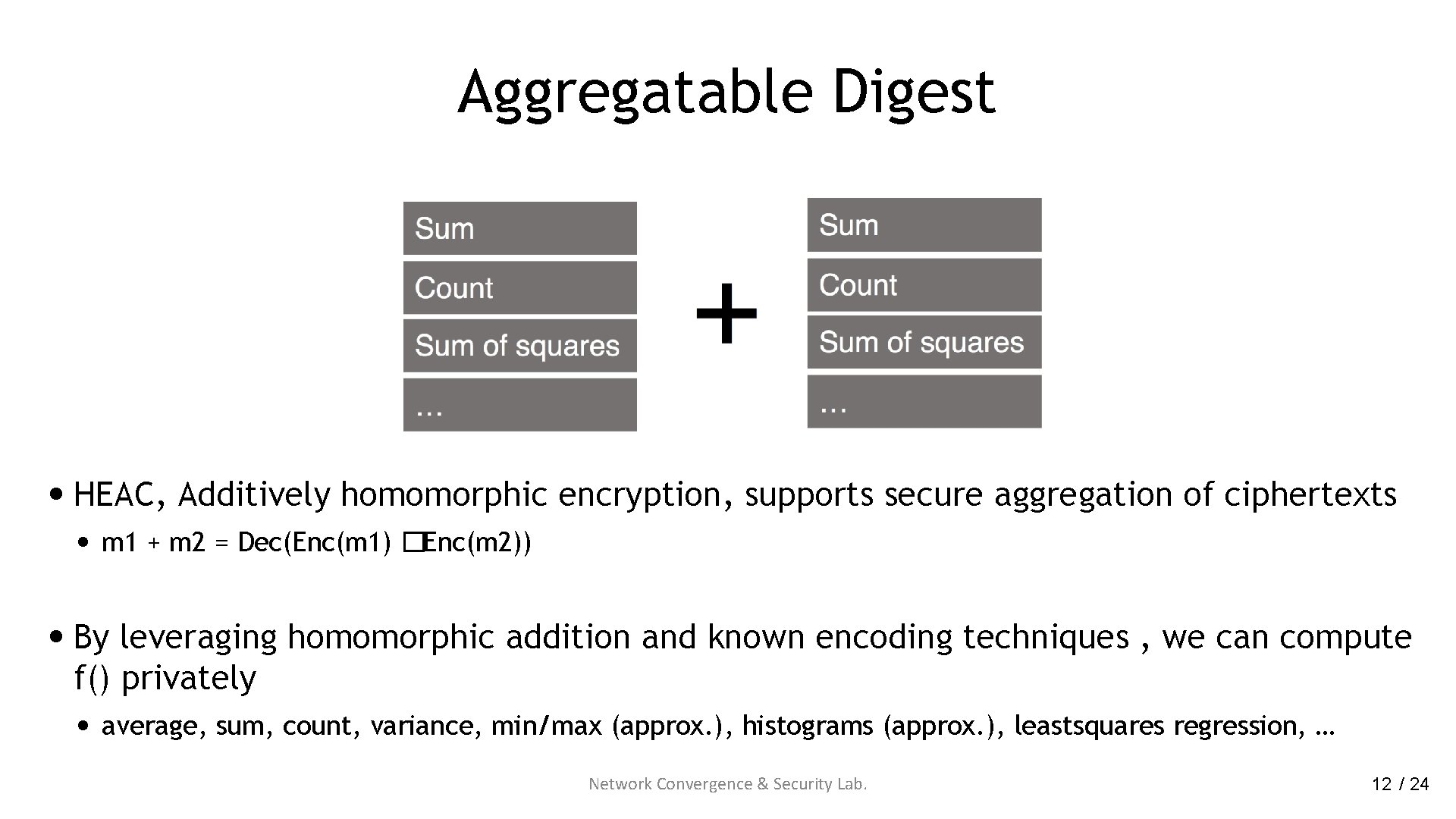
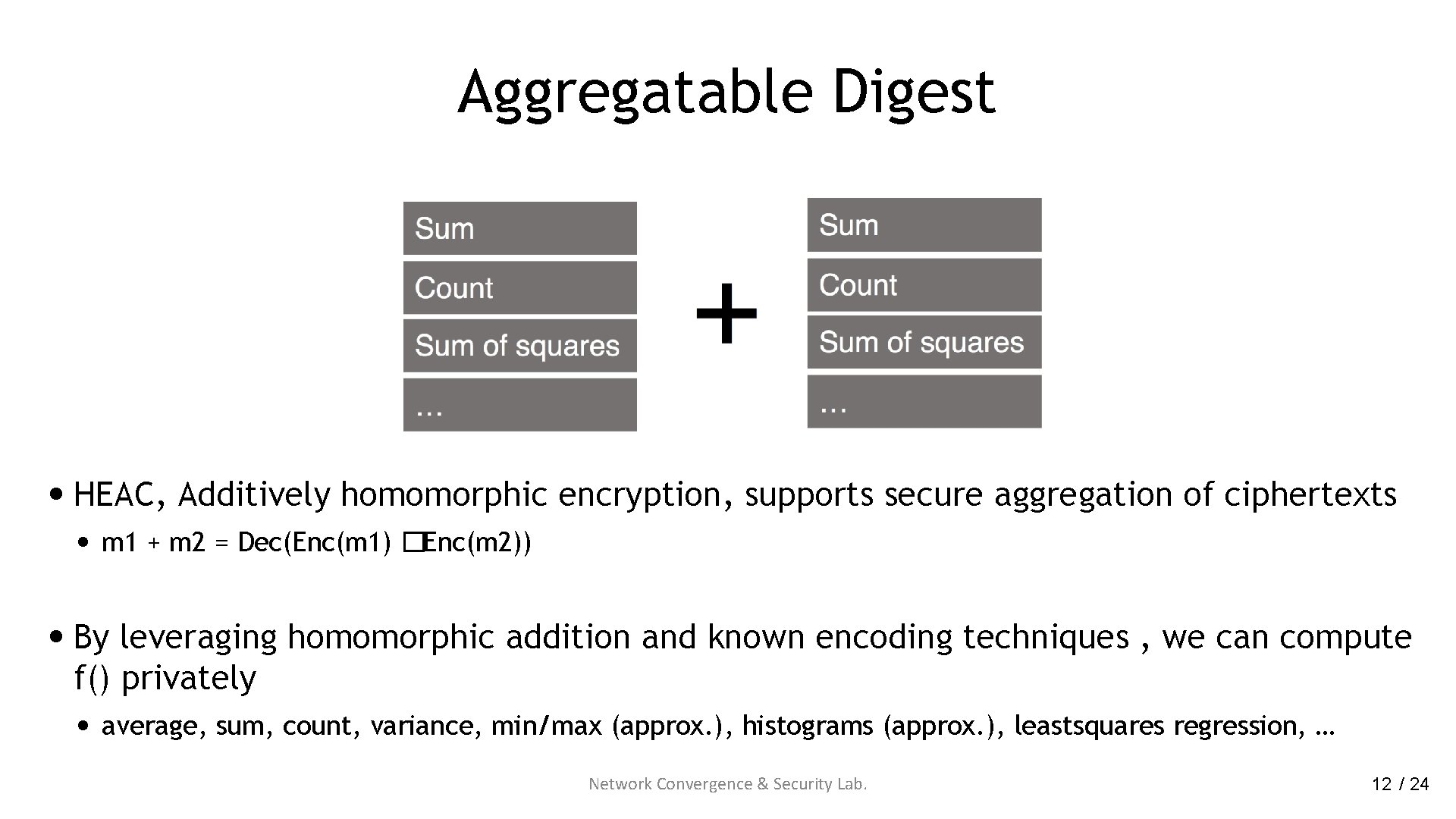
Aggregatable Digest • HEAC, Additively homomorphic encryption, supports secure aggregation of ciphertexts • m 1 + m 2 = Dec(Enc(m 1) �Enc(m 2)) • By leveraging homomorphic addition and known encoding techniques , we can compute f() privately • average, sum, count, variance, min/max (approx. ), histograms (approx. ), leastsquares regression, … Network Convergence & Security Lab. 12 / 24
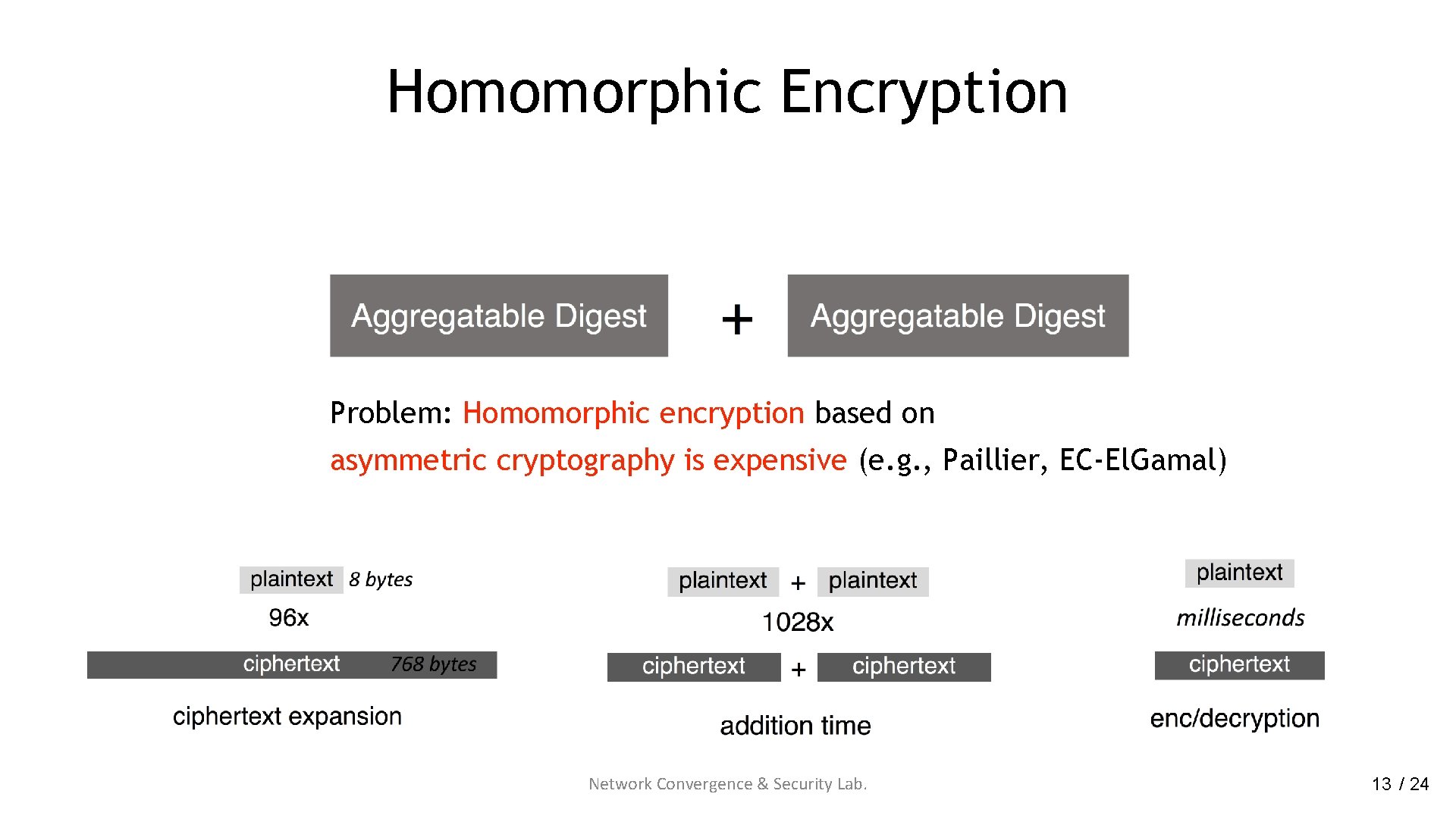
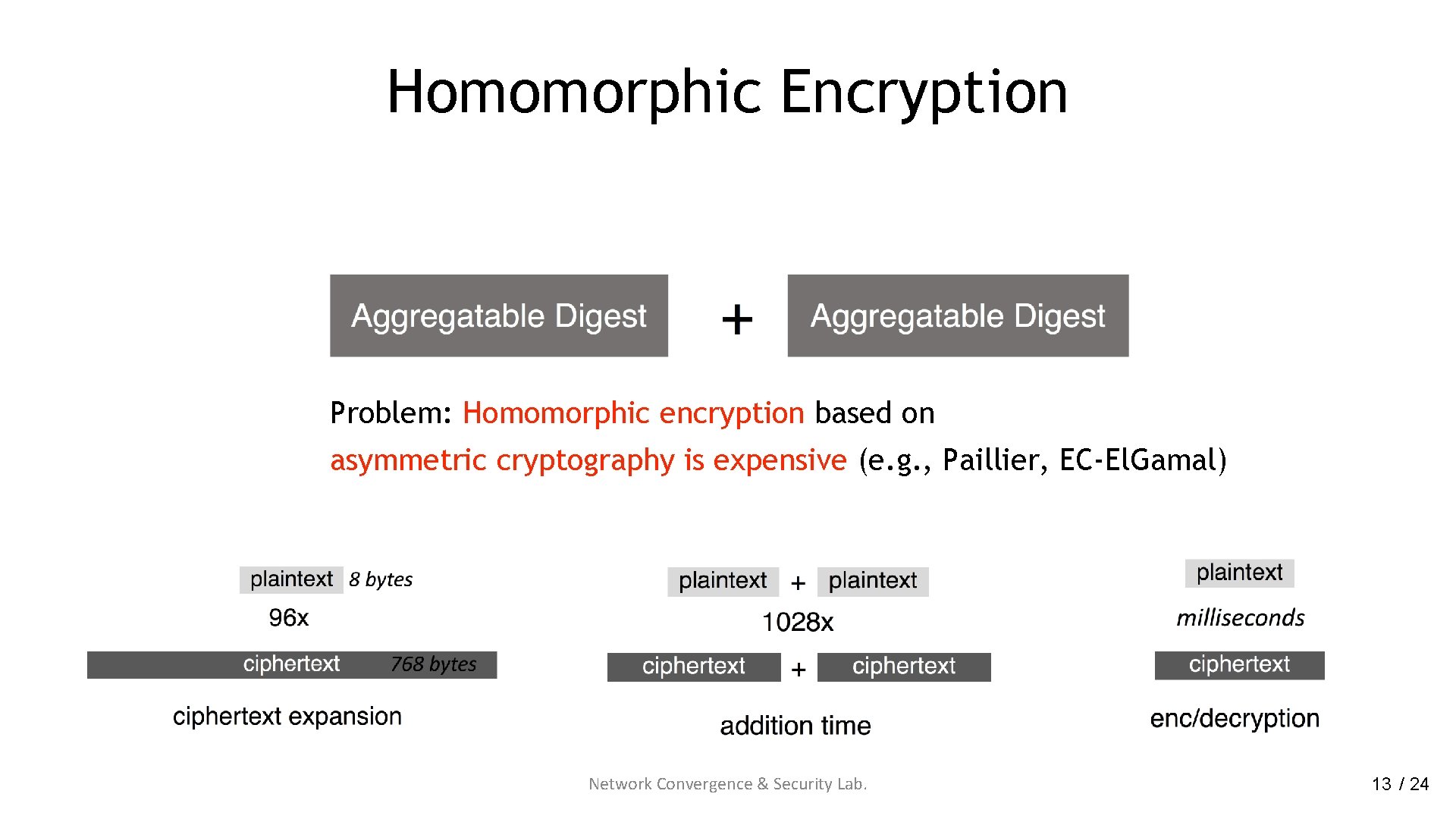
Homomorphic Encryption Problem: Homomorphic encryption based on asymmetric cryptography is expensive (e. g. , Paillier, EC-El. Gamal) Network Convergence & Security Lab. 13 / 24
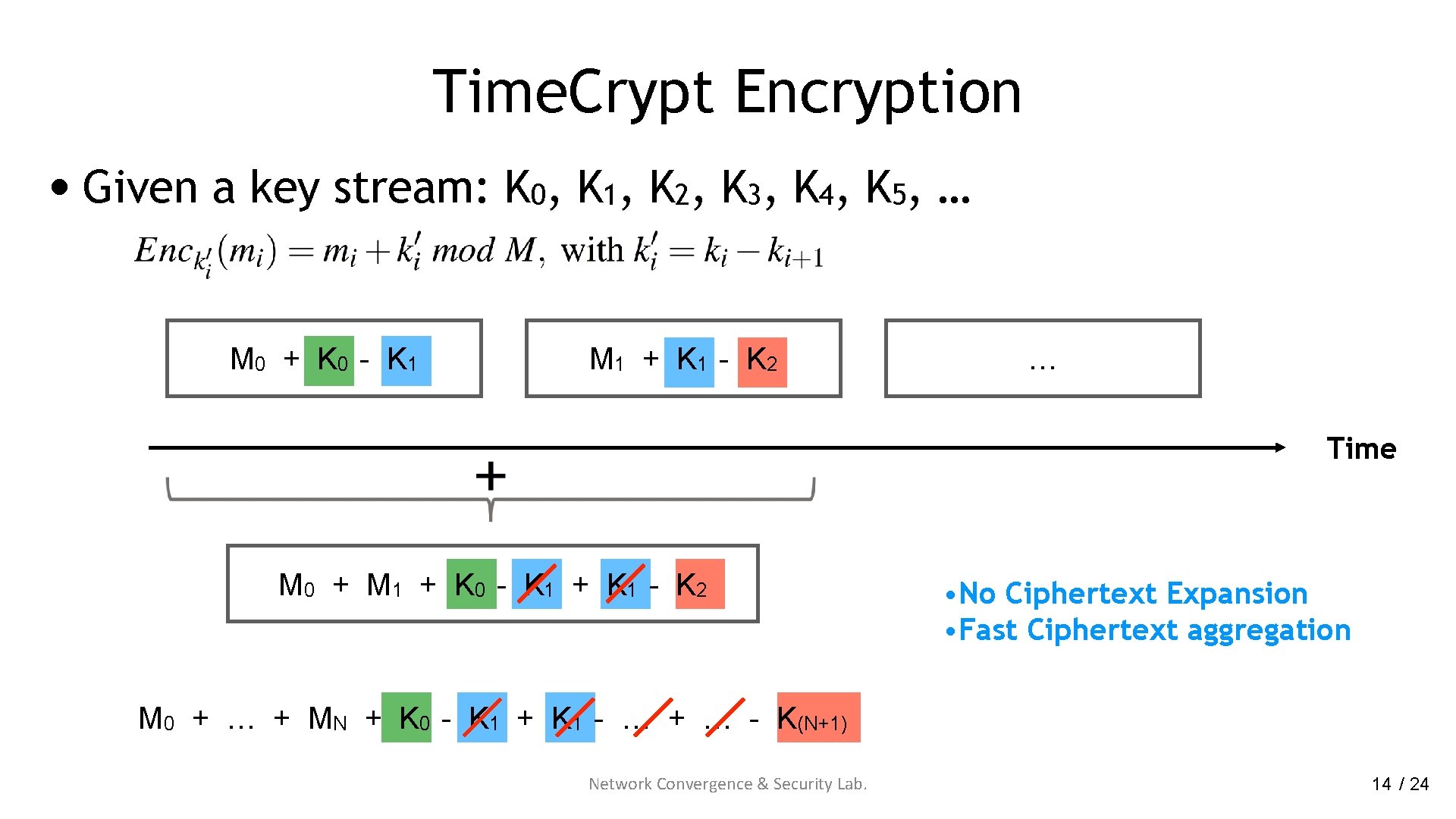
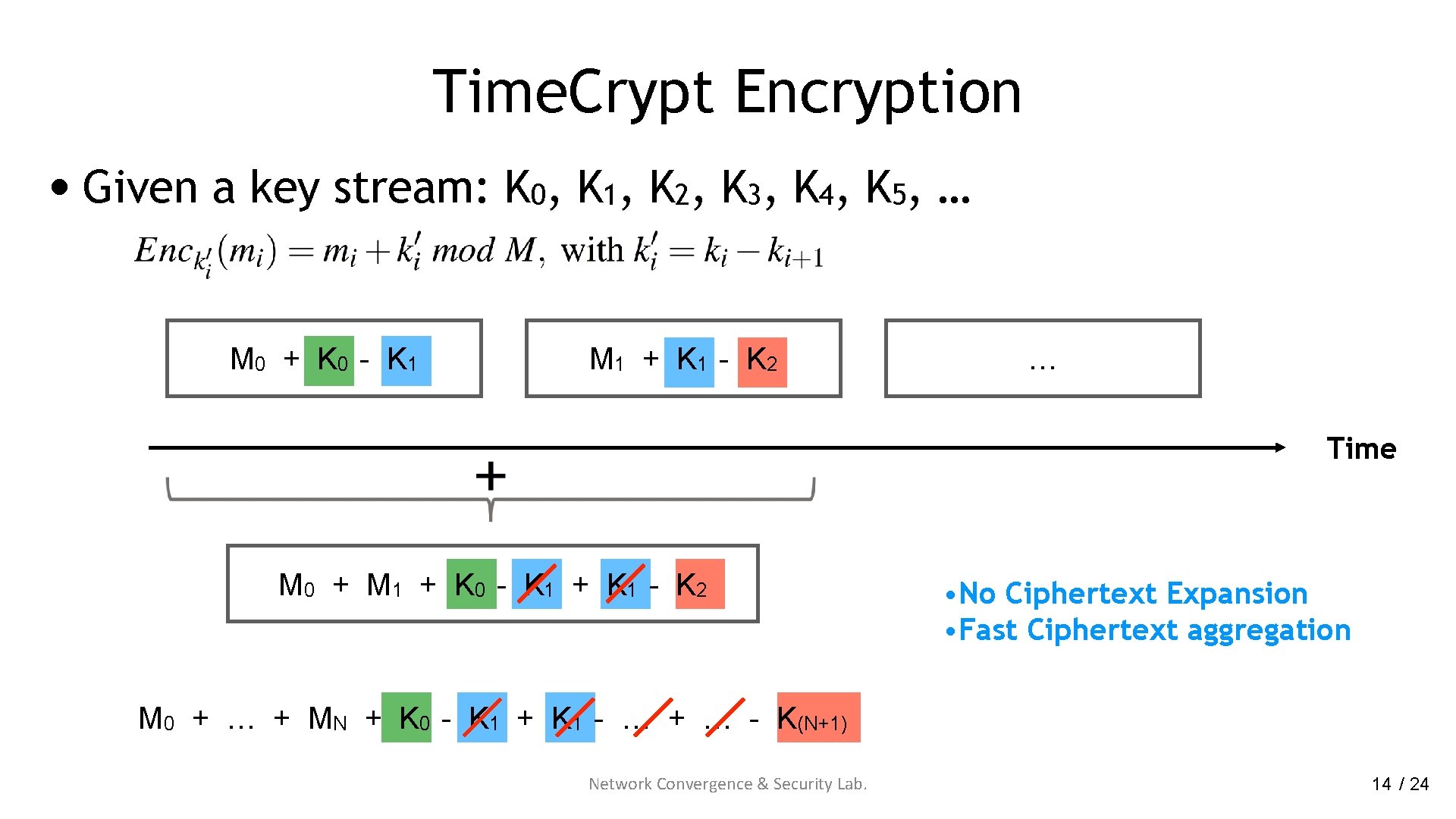
Time. Crypt Encryption • Given a key stream: K 0, K 1, K 2, K 3, K 4, K 5, … M 0 + K 0 - K 1 M 1 + K 1 - K 2 … Time M 0 + M 1 + K 0 - K 1 + K 1 - K 2 • No Ciphertext Expansion • Fast Ciphertext aggregation M 0 + … + MN + K 0 - K 1 + K 1 - … + … - K(N+1) Network Convergence & Security Lab. 14 / 24
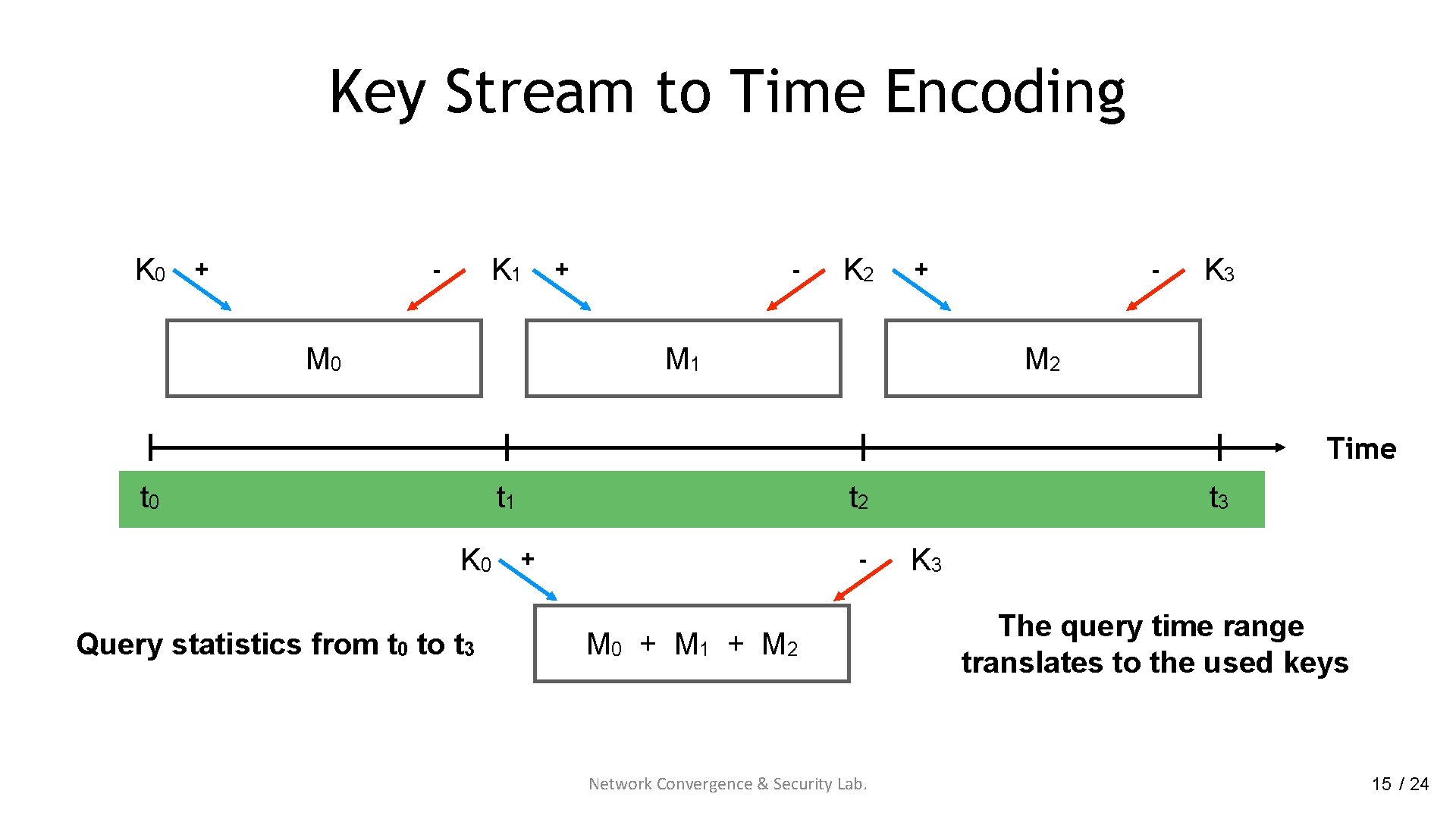
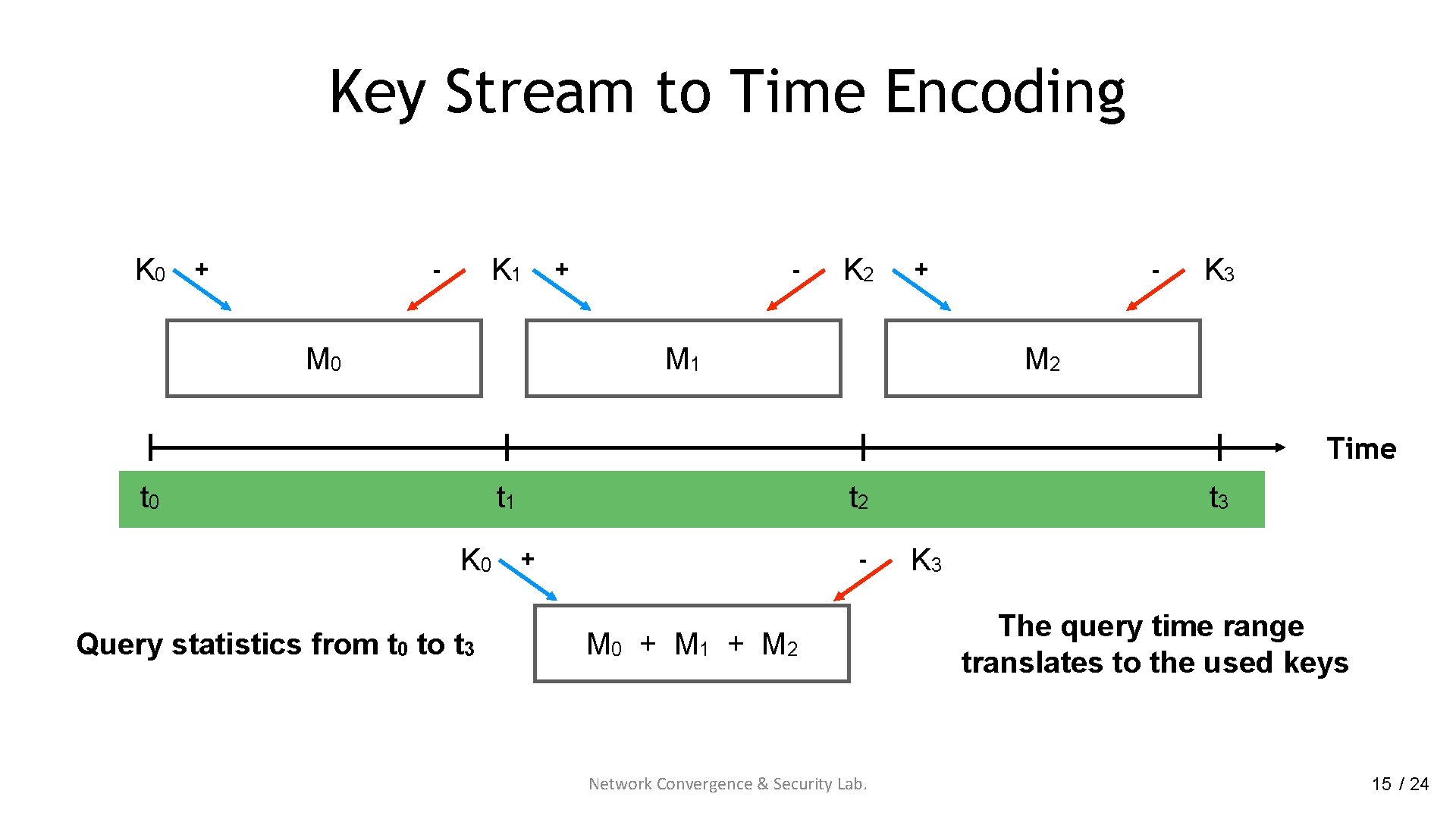
Key Stream to Time Encoding K 0 + K 1 - M 0 + - K 2 + M 1 - K 3 M 2 Time t 0 t 1 K 0 Query statistics from t 0 to t 3 t 2 + - M 0 + M 1 + M 2 Network Convergence & Security Lab. t 3 K 3 The query time range translates to the used keys 15 / 24
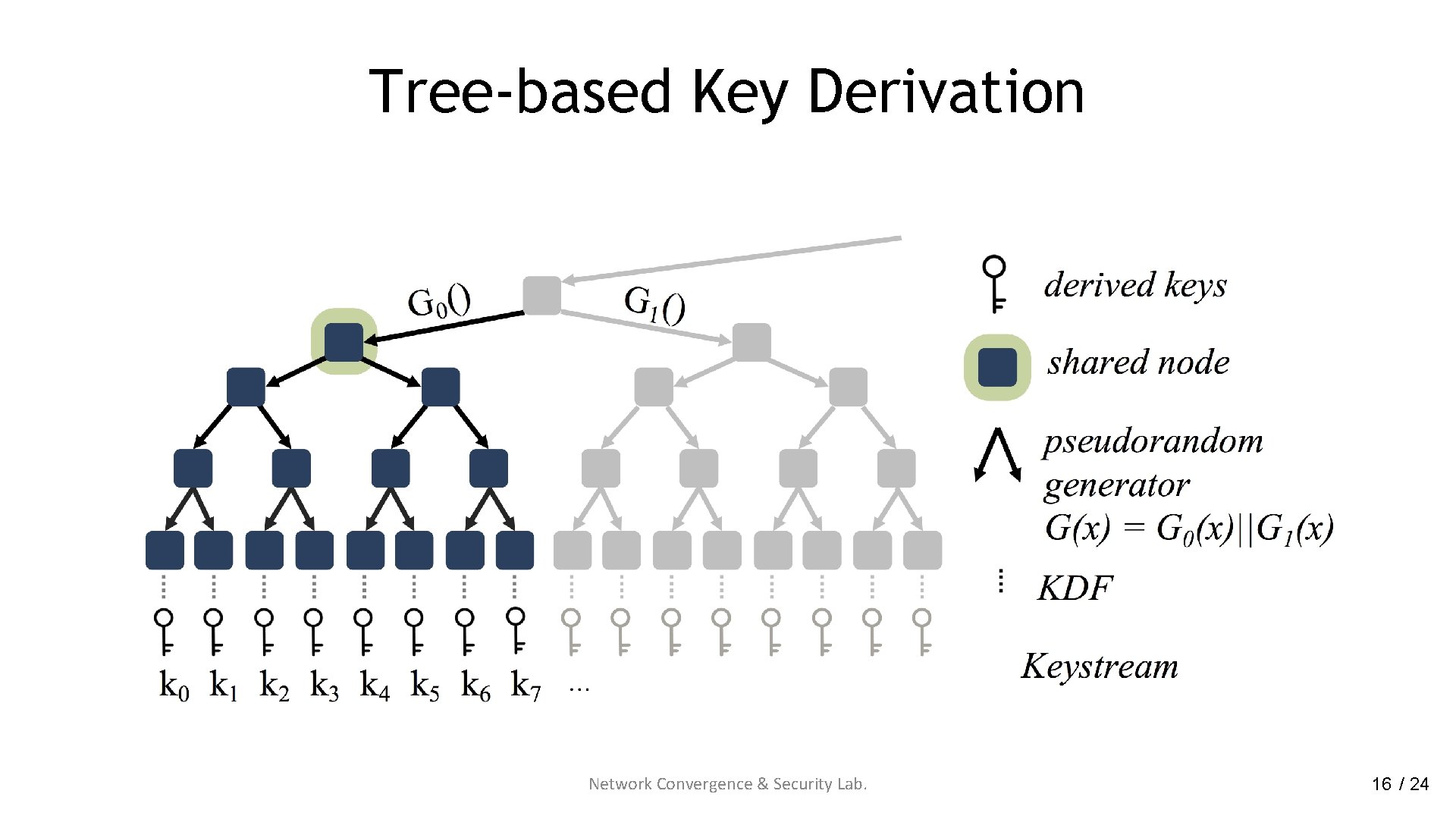
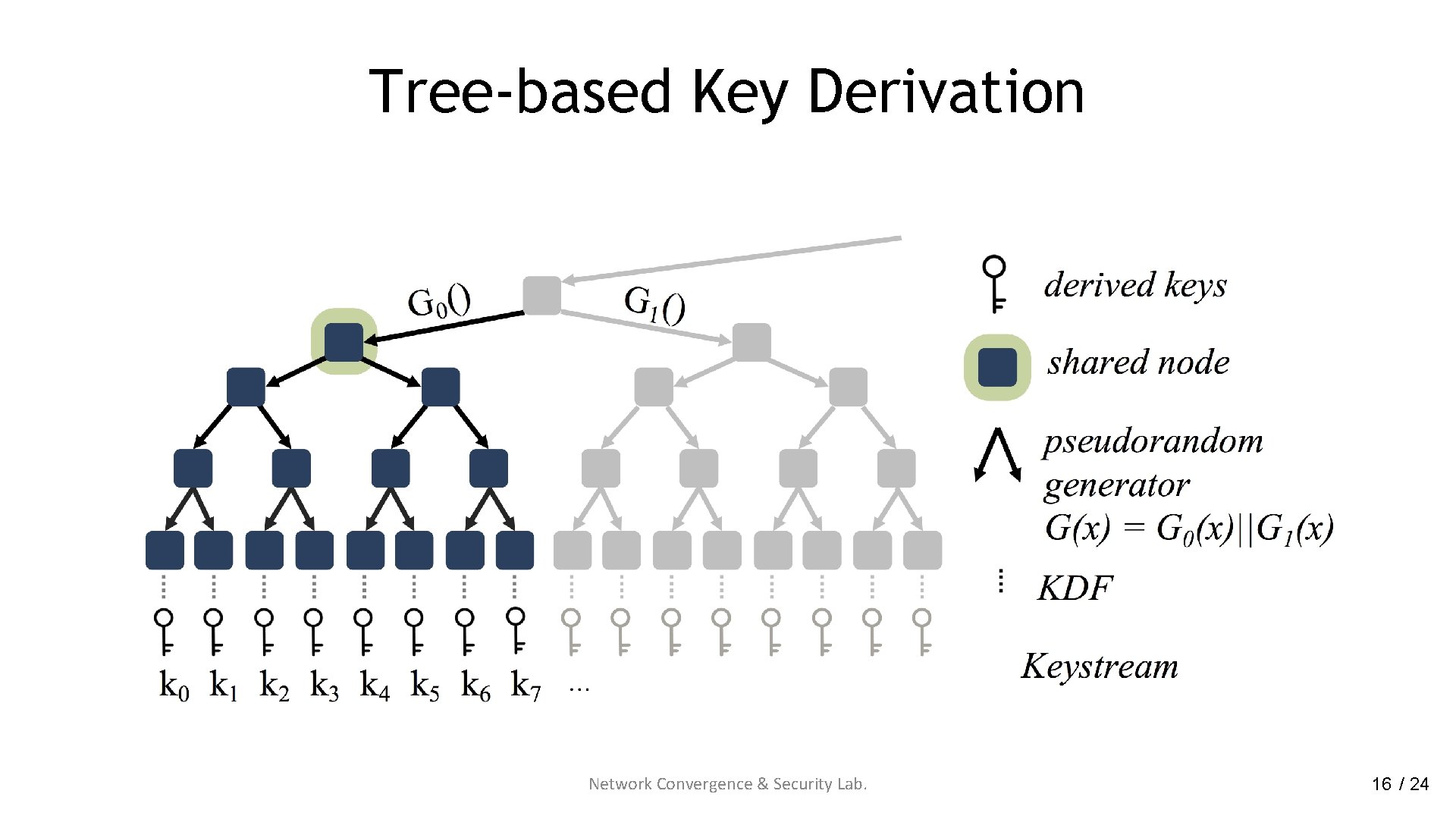
Tree-based Key Derivation Network Convergence & Security Lab. 16 / 24
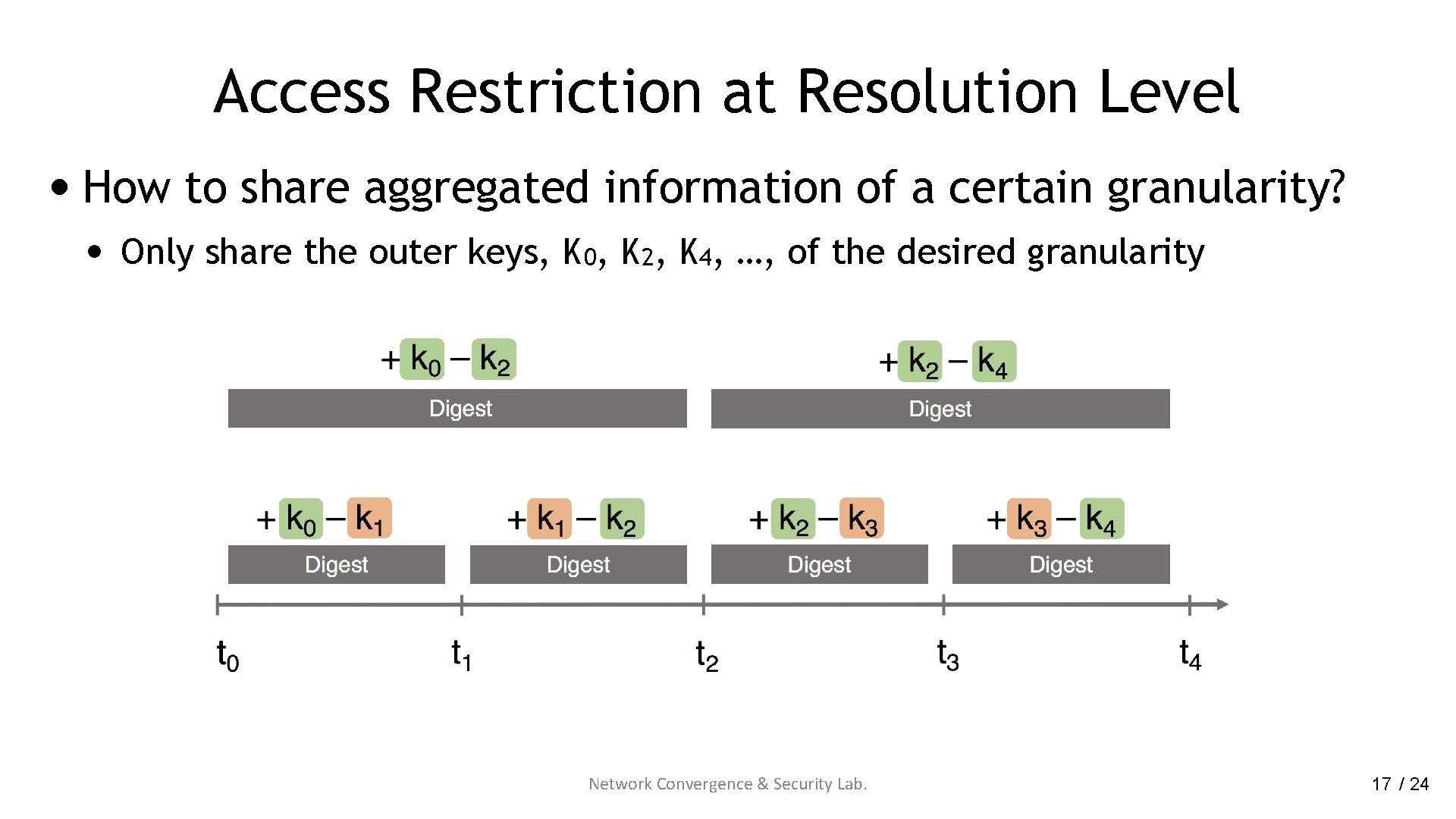
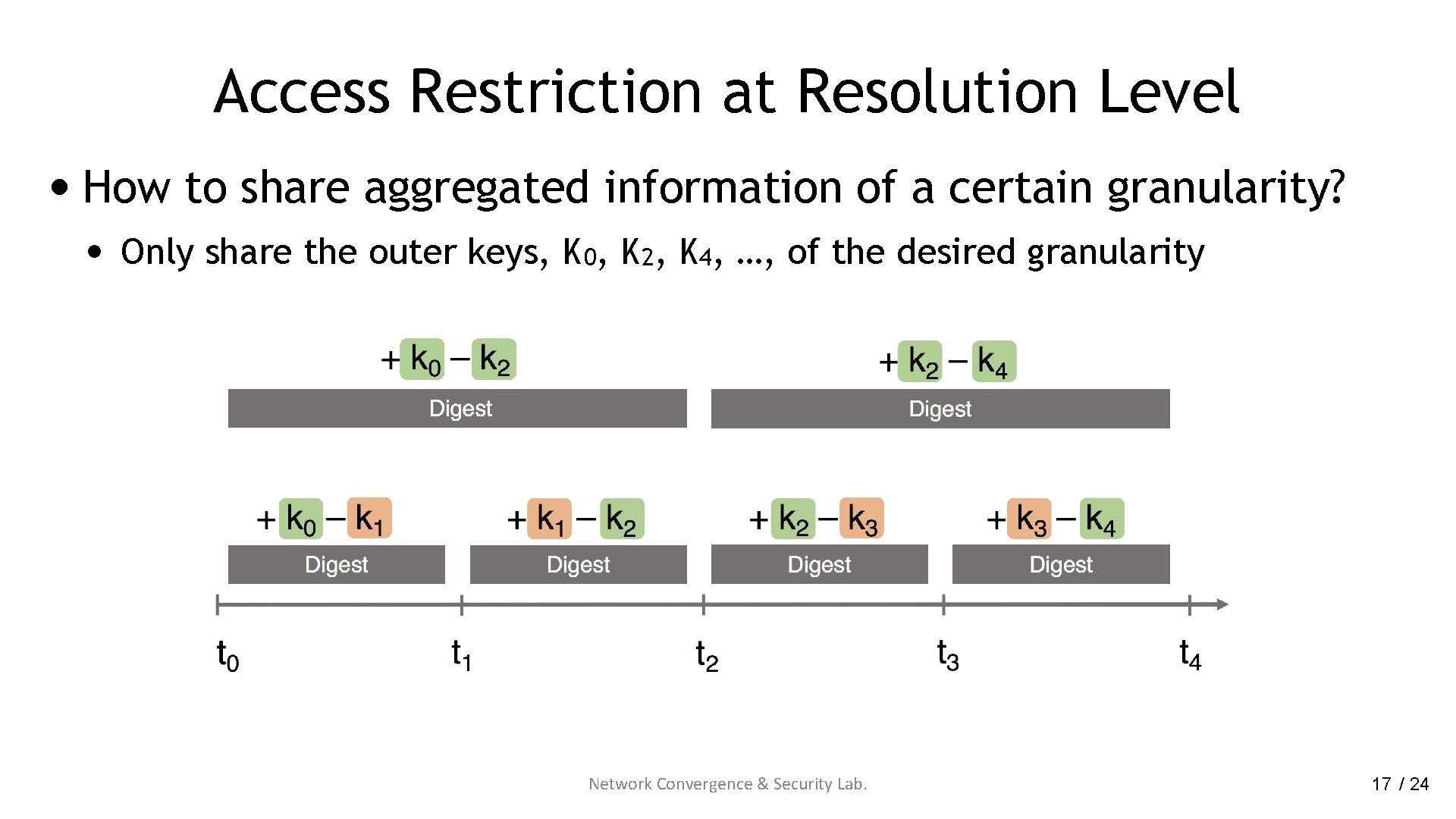
Access Restriction at Resolution Level • How to share aggregated information of a certain granularity? • Only share the outer keys, K 0, K 2, K 4, …, of the desired granularity Network Convergence & Security Lab. 17 / 24
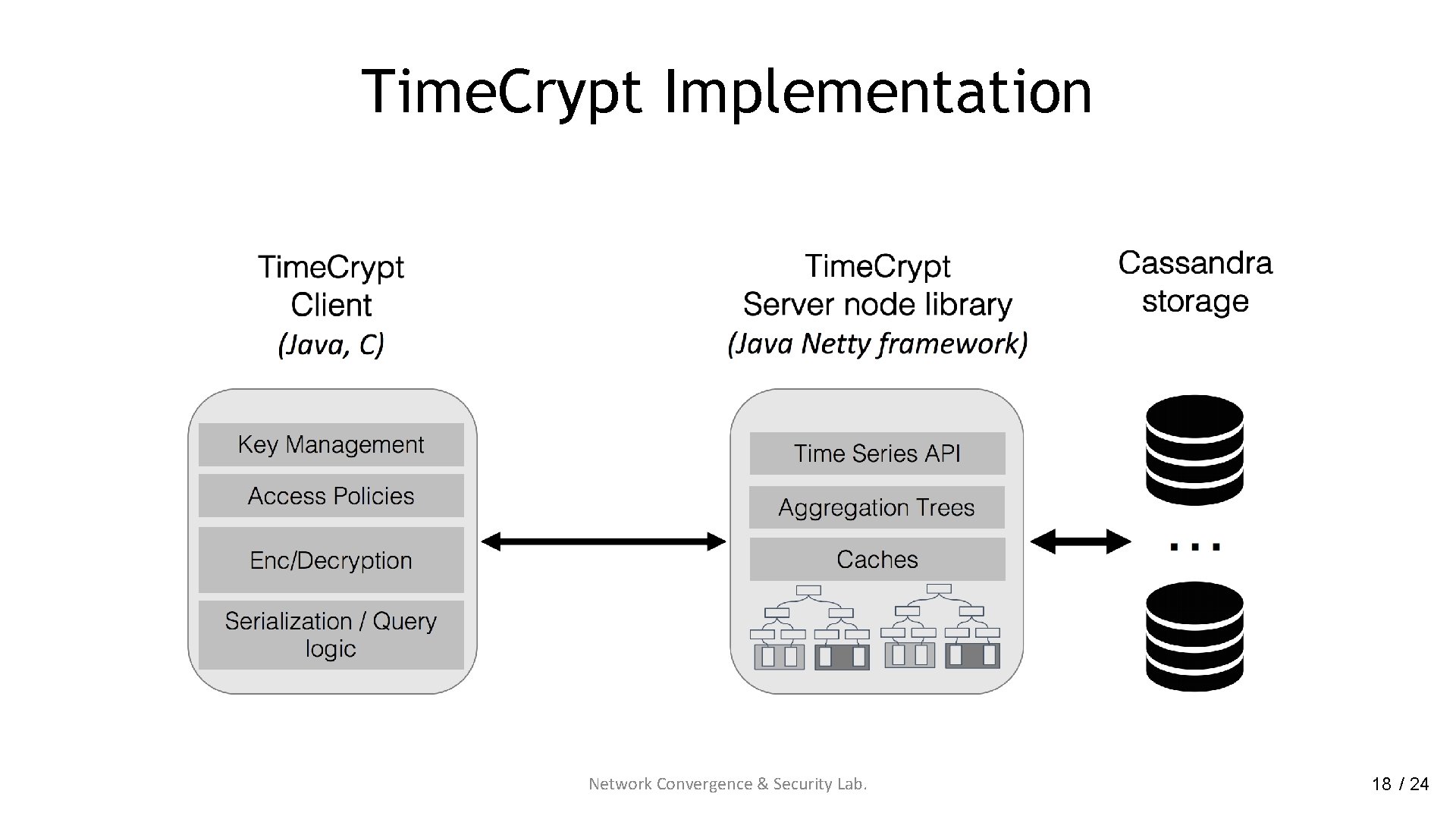
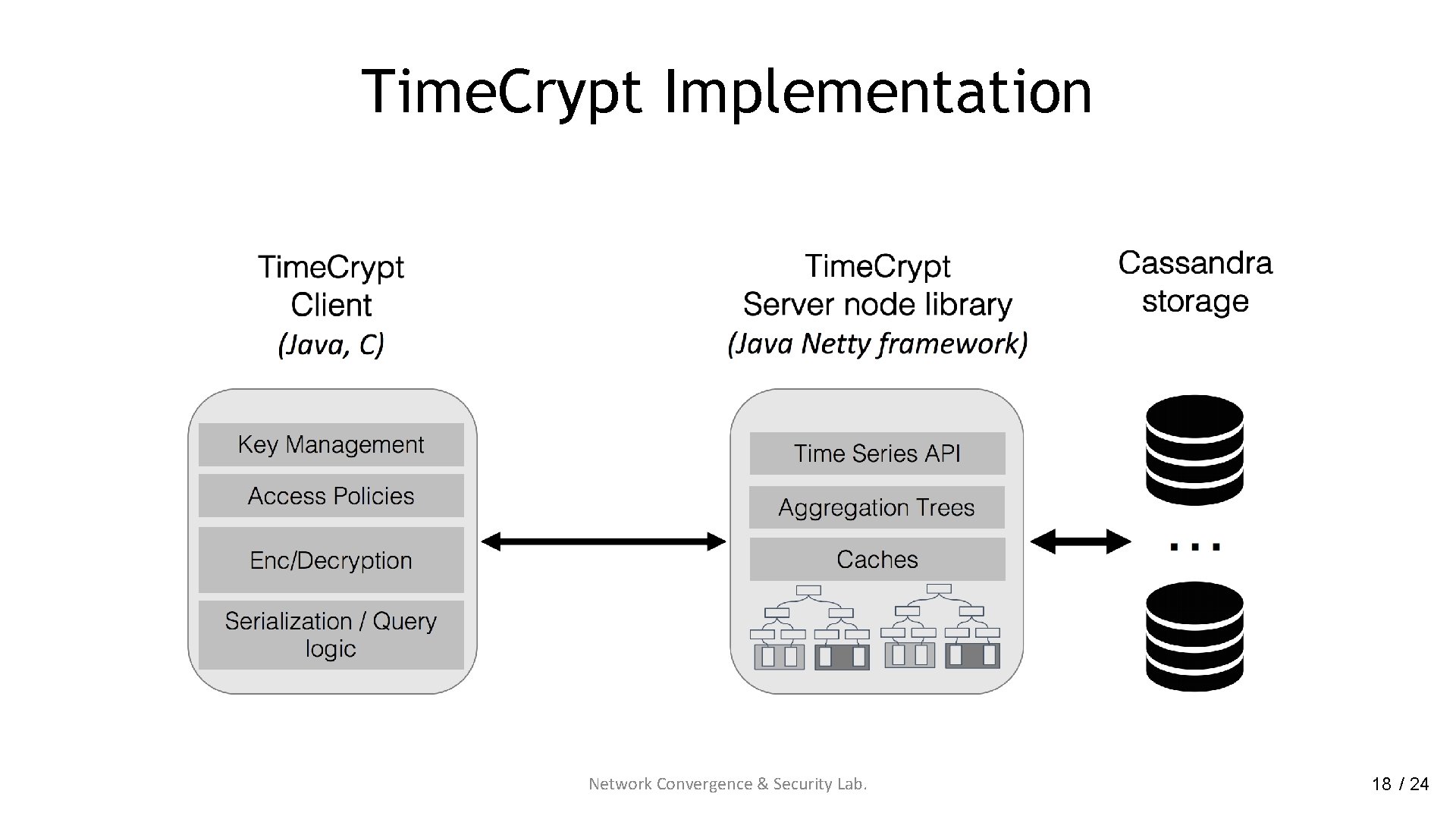
Time. Crypt Implementation Network Convergence & Security Lab. 18 / 24
Evaluation
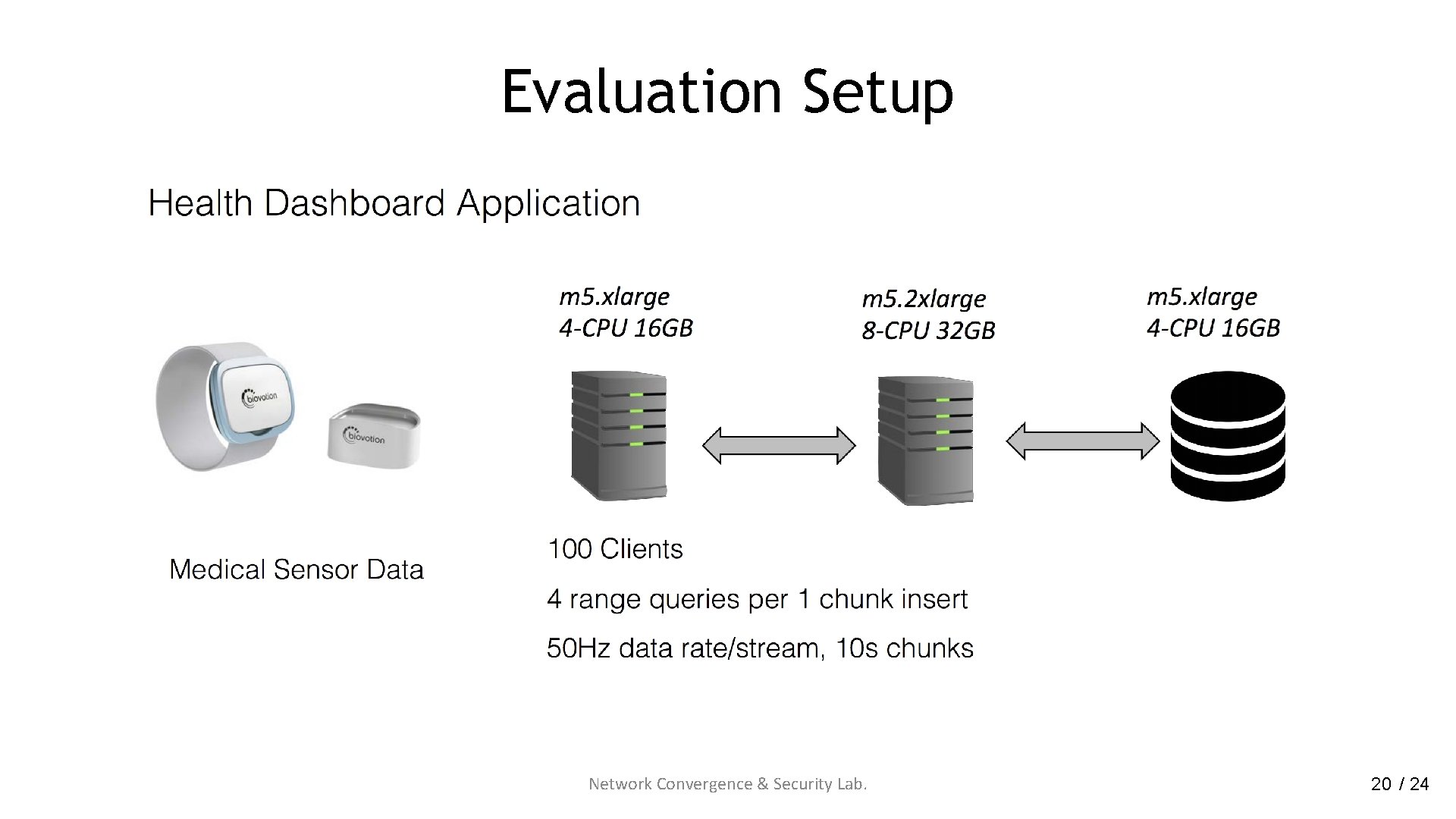
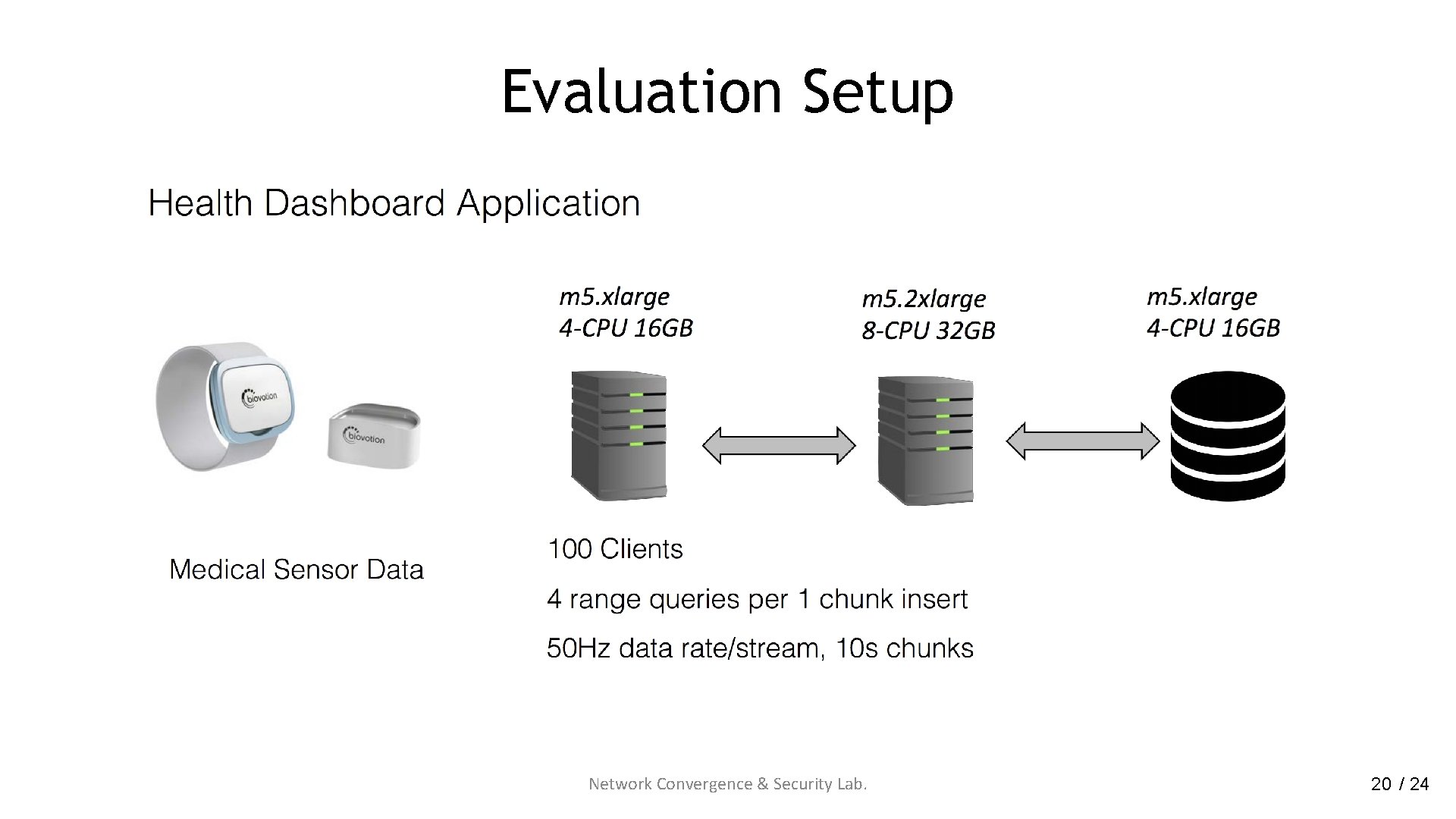
Evaluation Setup Network Convergence & Security Lab. 20 / 24
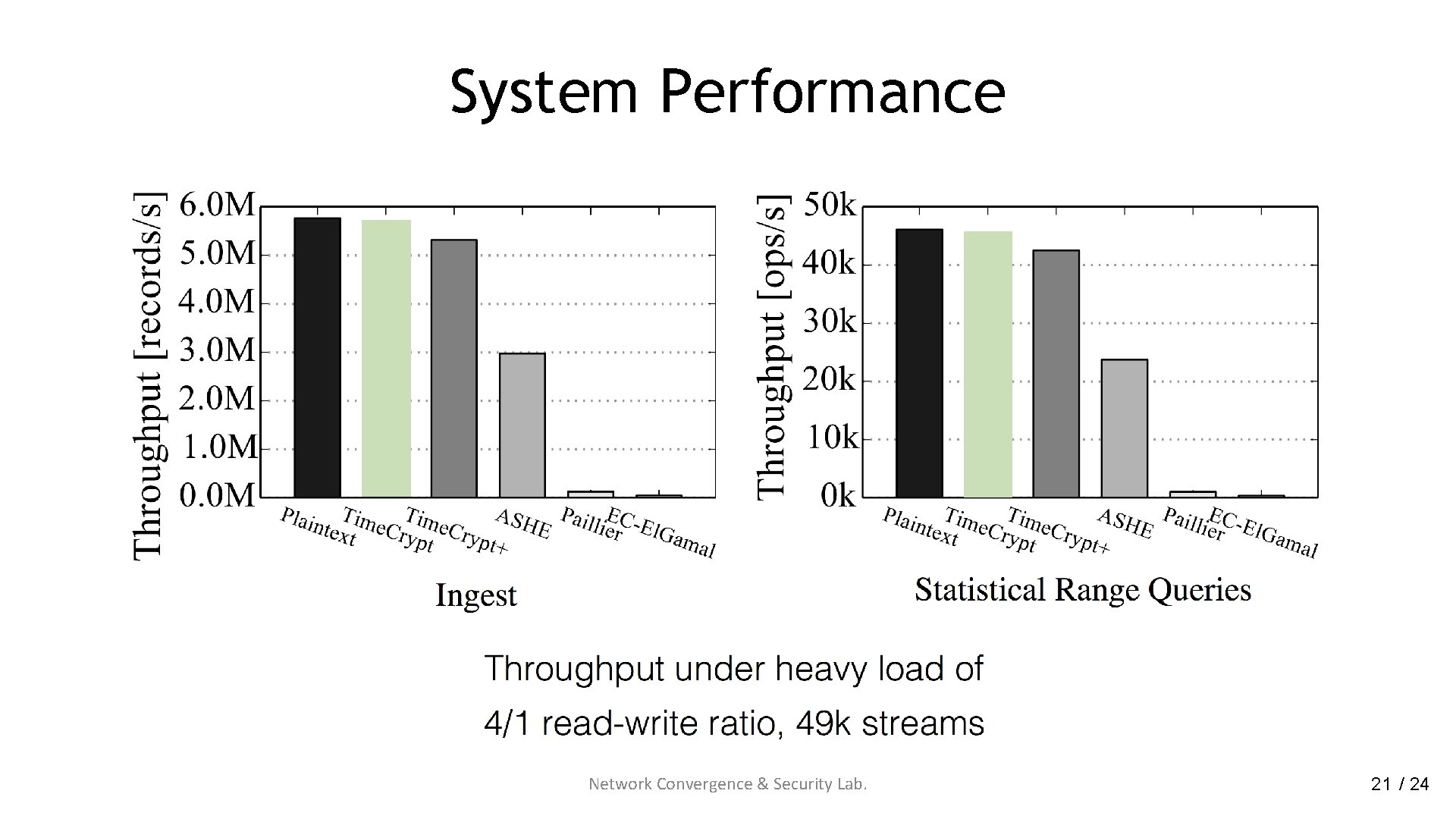
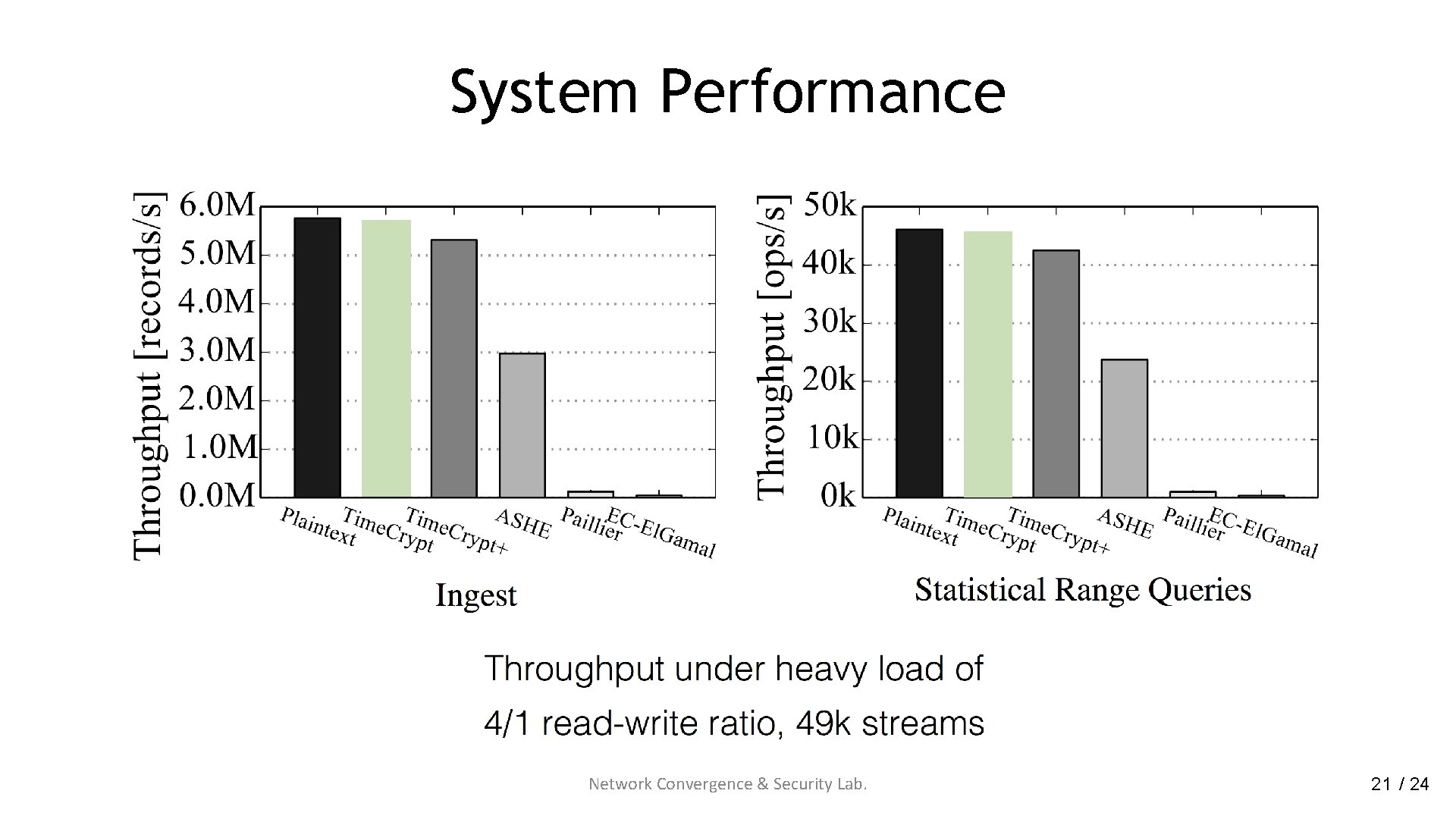
System Performance Network Convergence & Security Lab. 21 / 24
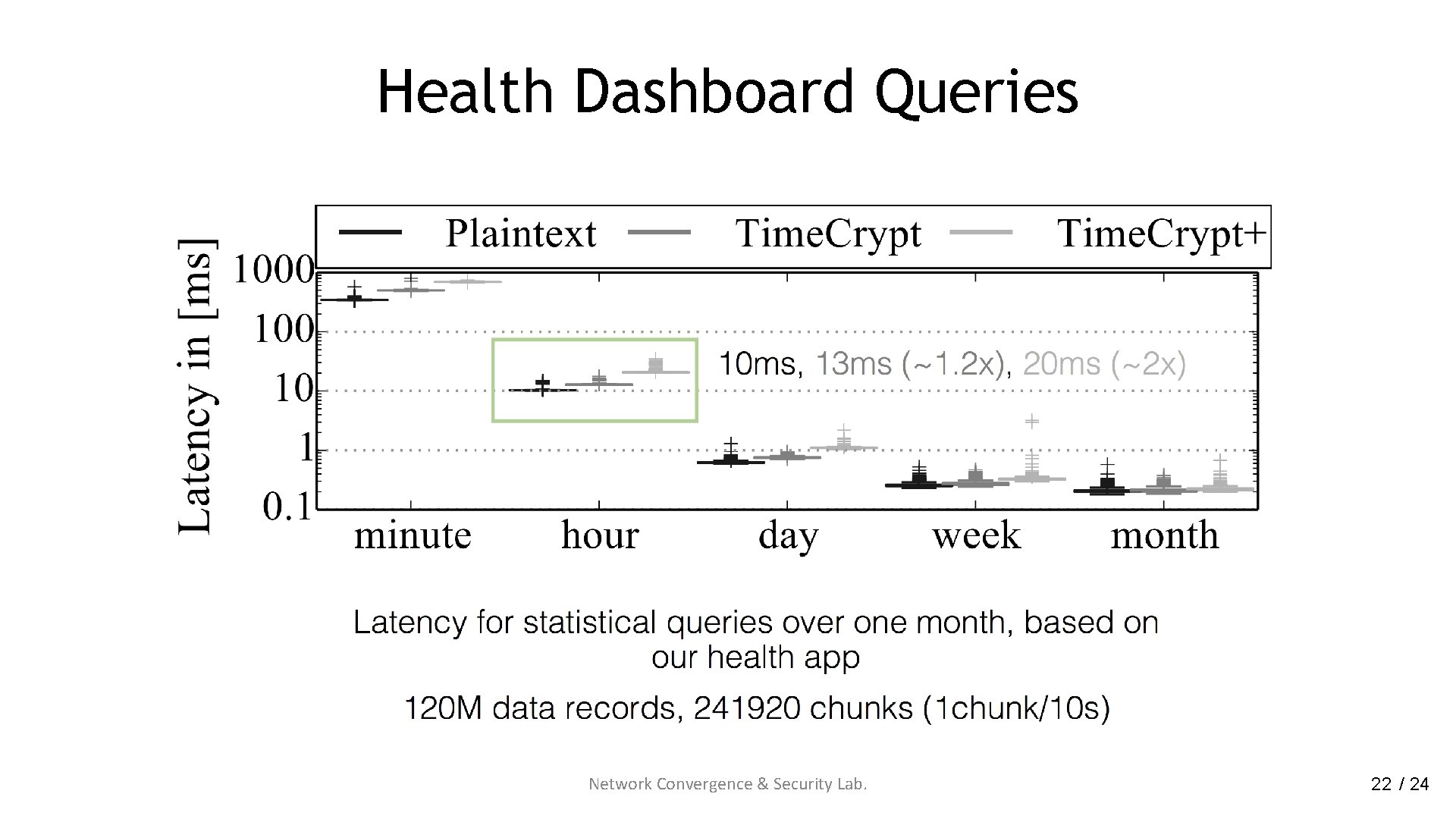
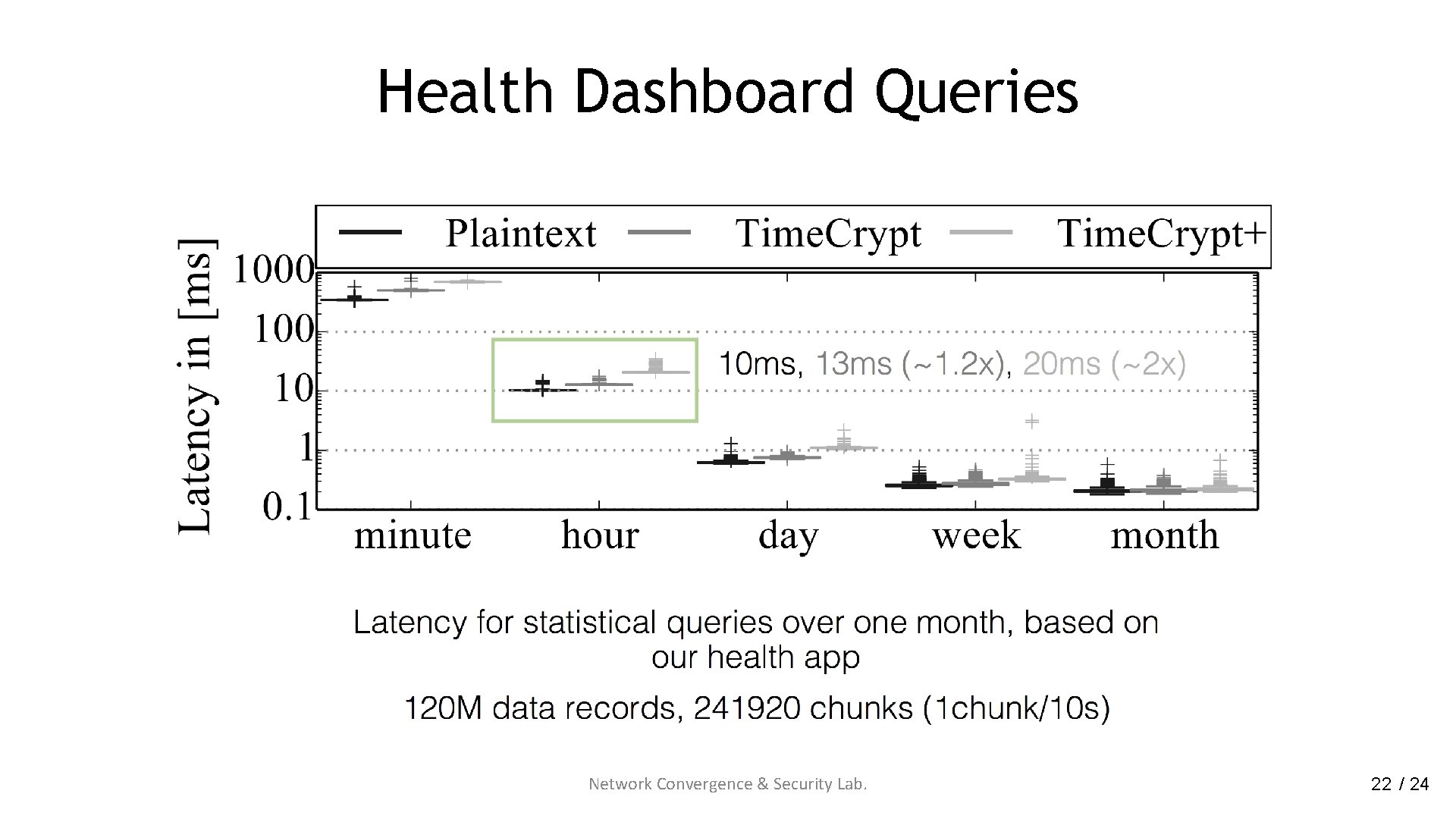
Health Dashboard Queries Network Convergence & Security Lab. 22 / 24
Summary
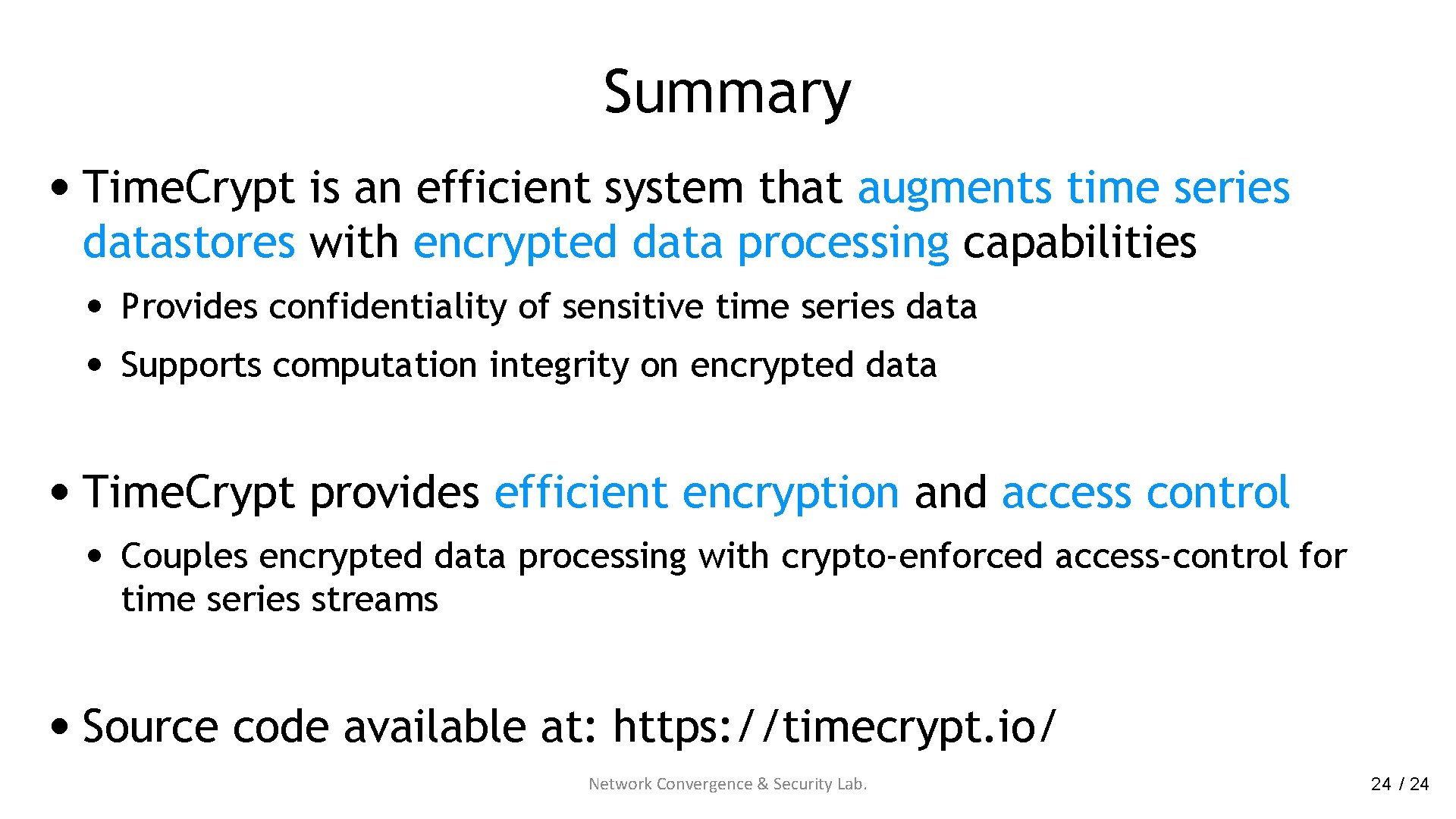
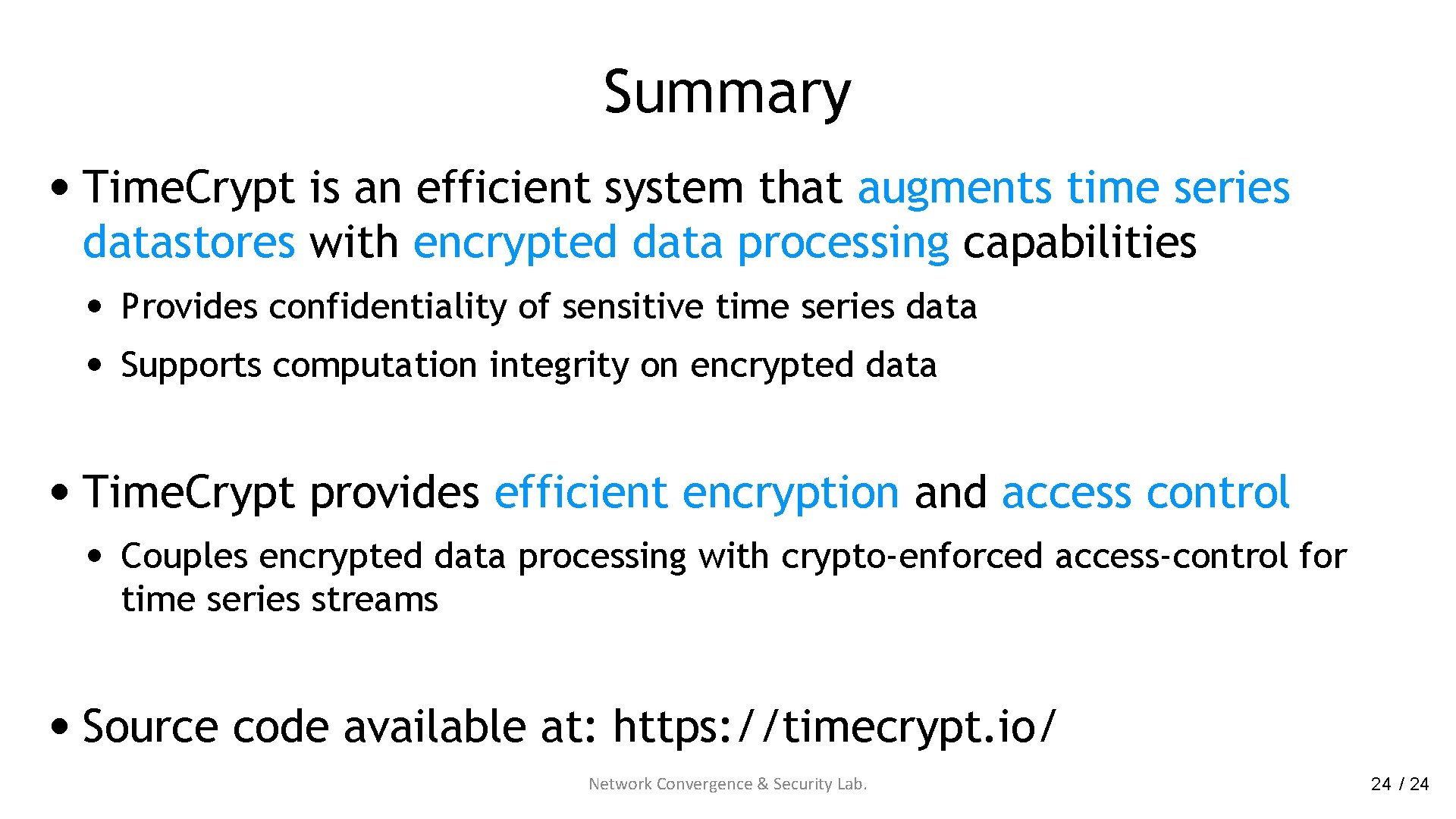
Summary • Time. Crypt is an efficient system that augments time series datastores with encrypted data processing capabilities • Provides confidentiality of sensitive time series data • Supports computation integrity on encrypted data • Time. Crypt provides efficient encryption and access control • Couples encrypted data processing with crypto-enforced access-control for time series streams • Source code available at: https: //timecrypt. io/ Network Convergence & Security Lab. 24 / 24