Tim La Grant Tim La GrantBecker edu Technical
Tim La. Grant Tim. La. Grant@Becker. edu Technical Director, Becker College
History of Virus & Malware Virus/malware released onto the web Ø 1990 – 200 -500 new virus Ø 2000 – 50, 000 Ø 2008 – Finally reached 1 million Ø 2013 – 100 Million Ø 2015 – 317 Million Ø 2016 – 500 -600 Million? !?

2016 Threat Landscape
Why is this important? • What does defending your data and securing your network infrastructure really mean? • Knowing your vulnerabilities & weak spots • Identifying threats and their vectors • Classifying the threat or attack • Stopping an active threat • Preventing threats or attacks • EDUCATE, EDUCATE your end-users & students

Leverage Appliances & Procesures… • Network Topology Overview • Next Generation Firewall (Stop at Perimeter) • Intrusion Prevention System (alerts if perimeter is breached) • Network Access Control System (BYOD Monitoring) • Mandated Antivirus/Anti-malware software for Students and Employees • DLP Software for Employees to find and shred PII • Monthly Scanning to find server weakness & patches • Automated tool to push Windows and non-Windows patches (SCCM, Kace) • IT Audits every 2 years to find weak areas

Know your vulnerabilities!!!! • How to identify vulnerabilities in your infrastructure • Network Scanning for Server/Network vulnerabilities, patches & updates (keep current) • Penetration testing (inside and outside) • Infrastructure and security audit performed by an outside identity • Social auditing • Current inventory of software and their versions • Current inventory of OS’s and patch levels • Connected Device inventory of LAN/Wi. Fi • What to look for… • • Weak Certificates Loose firewall policies (any/any) Unpatched/out of date servers and end points (software and firmware) Spam/malware/antivirus programs out of date/not installed/not functioning? End-users/Students port scanning Configuration errors Device hardening policies incorrectly applied or not at all Do you have a DMZ? • What ports are open to the local infrastructure • What services are needed • Are all forward facing servers in the DMZ
Identifying threats, threat vectors & attacks Threat Vectors - the method a threat uses to gain access to the target. . • Threat Vectors • LAN / WAN • VPN • Physical / local connection / wireless • Removable storage • Email / spam / malware • Social networking • Compromised website / key logging Threat Targets – data / creds / banking/ medical / credit cards • • • Unpatched servers Old firewall firmware/broad/Open FW policies Old switch Code Inadequate server hardening / Switch hardening No Antivirus or Malware Protection

Most Common Types of Threats or Attacks Ø *** Social Engineering *** Ø DDOS Ø Malware Ø Crypto Malware Ø Viruses/Trojans/Worms Ø Hacks/breaches/data theft Ø Spam Ø Man-in-the-middle Ø Ø Ø ***Social Engineered*** Passive Active Distributed Insider Close-In Phishing Spoof Exploit Zero Day Password

Classifying the threat or attack • How do you classify a threat in general? • Each incident will be handled differently • • • Analyze the behavior Traffic patterns Try to identify the origin of the attack is it domestic or foreign Identify the targets - critical or non-critical systems What do those targets house • Data • Web site • PII • Who/What does the threat effect and assess impact to business not only downtime but monetary impact as well
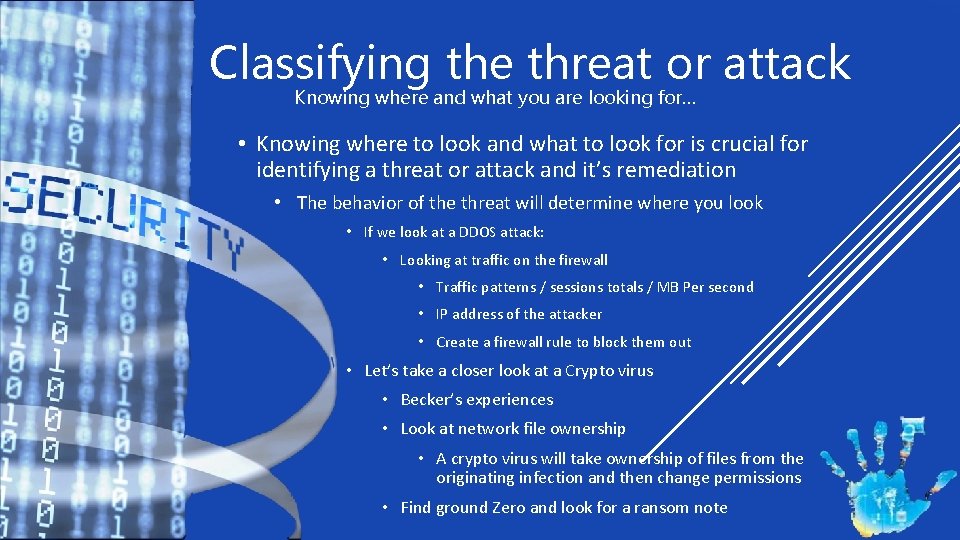
Classifying the threat or attack Knowing where and what you are looking for… • Knowing where to look and what to look for is crucial for identifying a threat or attack and it’s remediation • The behavior of the threat will determine where you look • If we look at a DDOS attack: • Looking at traffic on the firewall • Traffic patterns / sessions totals / MB Per second • IP address of the attacker • Create a firewall rule to block them out • Let’s take a closer look at a Crypto virus • Becker’s experiences • Look at network file ownership • A crypto virus will take ownership of files from the originating infection and then change permissions • Find ground Zero and look for a ransom note
Stopping an active threat or attack • The type of attack will determine the course of action • That may be any of the combination of the following • • Blocking an IP on the firewall Taking a machine off the network Disabling a port on a router or switch Locking a user account Adding tag line to your spam filtering Getting a hosting company involved Taking a forensic image using FTK Imager or another tool

Preventing threats and attacks @ 50 k Feet • Create SOP’s (Standard Operating Procedures) for the following • • Server Hardening Router/Switch hardening Firewall policies Antivirus for Faculty/Staff and Students (ENFORCE IT) • Leverage appliances: • NG firewalls (it is better to have redundancy throughout your appliances then holes) • NAC for internal network visibility and control of fact/staff/student computers • Packet Shaper – to not only shape traffic but to classify it and block or throttle certain traffic and vlans • If wireless – application aware access points • LOG EVERYTHING ON ALL APPLICIANCES
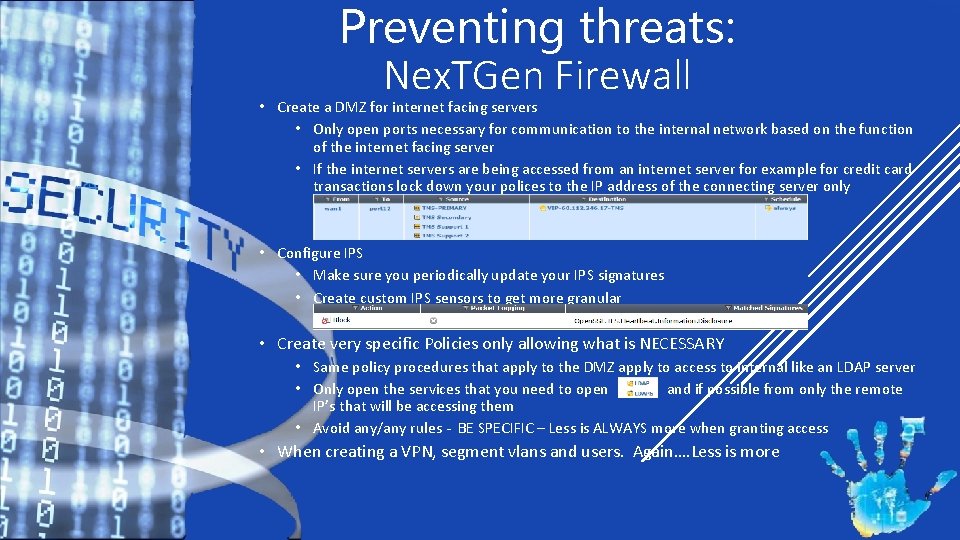
Preventing threats: Nex. TGen Firewall • Create a DMZ for internet facing servers • Only open ports necessary for communication to the internal network based on the function of the internet facing server • If the internet servers are being accessed from an internet server for example for credit card transactions lock down your polices to the IP address of the connecting server only • Configure IPS • Make sure you periodically update your IPS signatures • Create custom IPS sensors to get more granular • Create very specific Policies only allowing what is NECESSARY • Same policy procedures that apply to the DMZ apply to access to internal like an LDAP server • Only open the services that you need to open and if possible from only the remote IP’s that will be accessing them • Avoid any/any rules - BE SPECIFIC – Less is ALWAYS more when granting access • When creating a VPN, segment vlans and users. Again…. Less is more
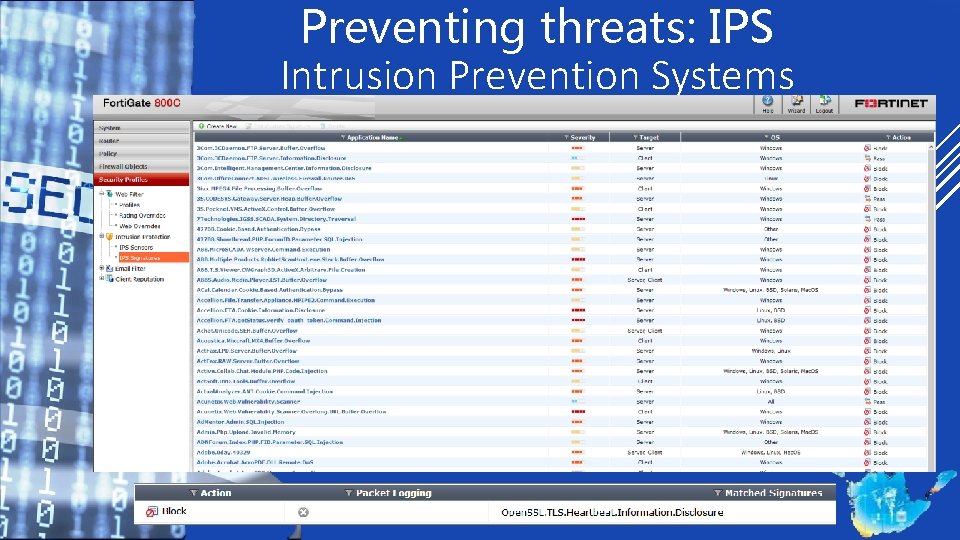
Preventing threats: IPS Intrusion Prevention Systems
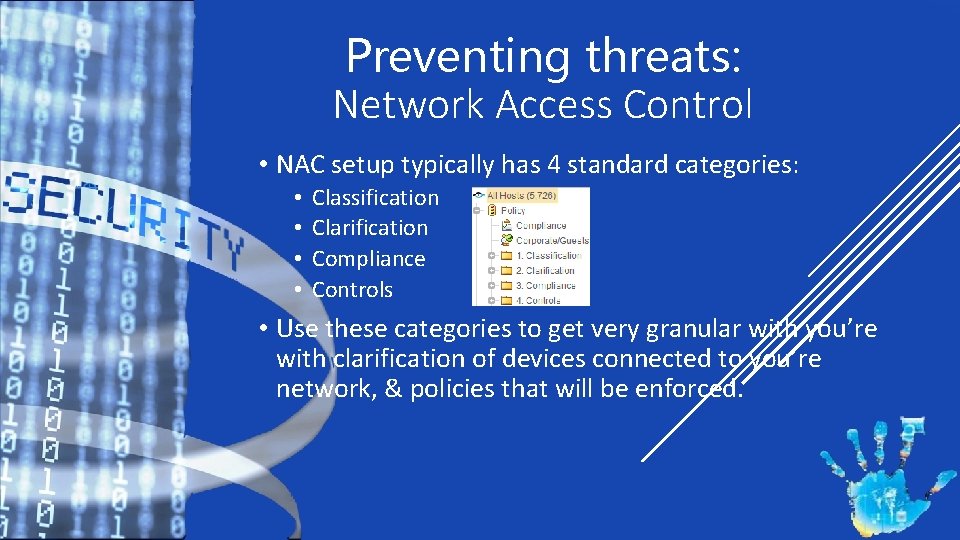
Preventing threats: Network Access Control • NAC setup typically has 4 standard categories: • • Classification Clarification Compliance Controls • Use these categories to get very granular with you’re with clarification of devices connected to you’re network, & policies that will be enforced.
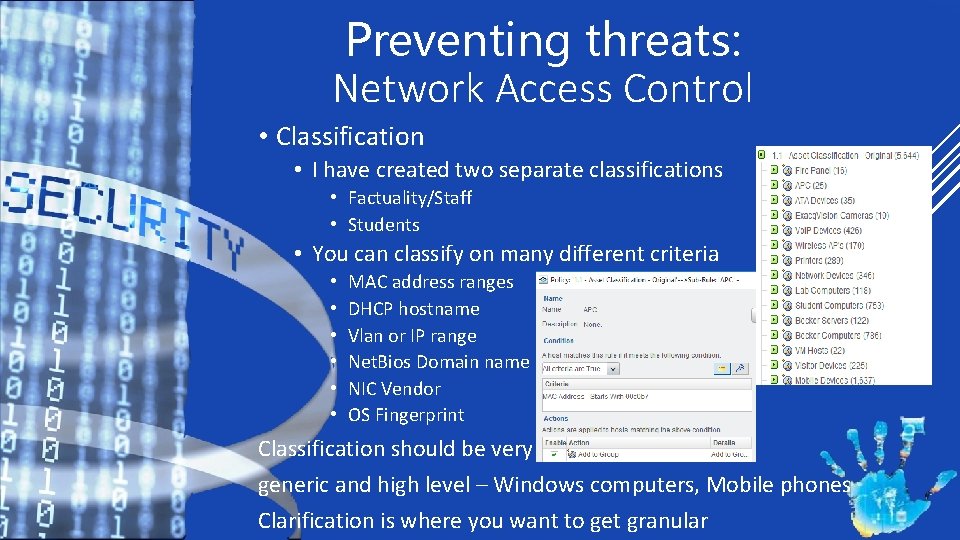
Preventing threats: Network Access Control • Classification • I have created two separate classifications • Factuality/Staff • Students • You can classify on many different criteria • • • MAC address ranges DHCP hostname Vlan or IP range Net. Bios Domain name NIC Vendor OS Fingerprint Classification should be very generic and high level – Windows computers, Mobile phones Clarification is where you want to get granular

Preventing threats: Network Access Control • Clarification • This is where you break out into more granular groups • Separate out the computer types • Windows Computers become • Faculty - Windows / Mac/ Linux • Student - Windows / Mac/ Linux • Student and faculty groups with Antivirus installed. • Who is on wireless vs wired • In this case broken out by campus location.
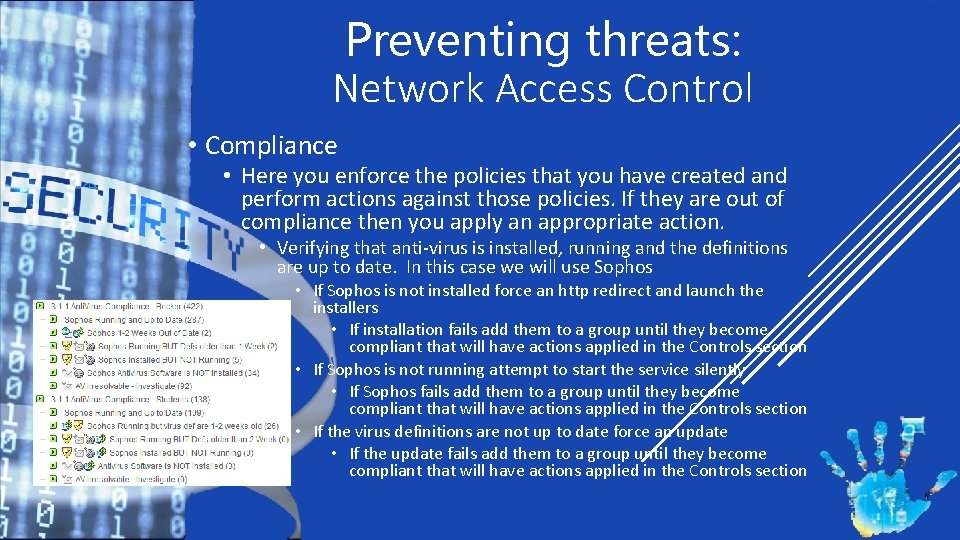
Preventing threats: Network Access Control • Compliance • Here you enforce the policies that you have created and perform actions against those policies. If they are out of compliance then you apply an appropriate action. • Verifying that anti-virus is installed, running and the definitions are up to date. In this case we will use Sophos • If Sophos is not installed force an http redirect and launch the installers • If installation fails add them to a group until they become compliant that will have actions applied in the Controls section • If Sophos is not running attempt to start the service silently • If Sophos fails add them to a group until they become compliant that will have actions applied in the Controls section • If the virus definitions are not up to date force an update • If the update fails add them to a group until they become compliant that will have actions applied in the Controls section
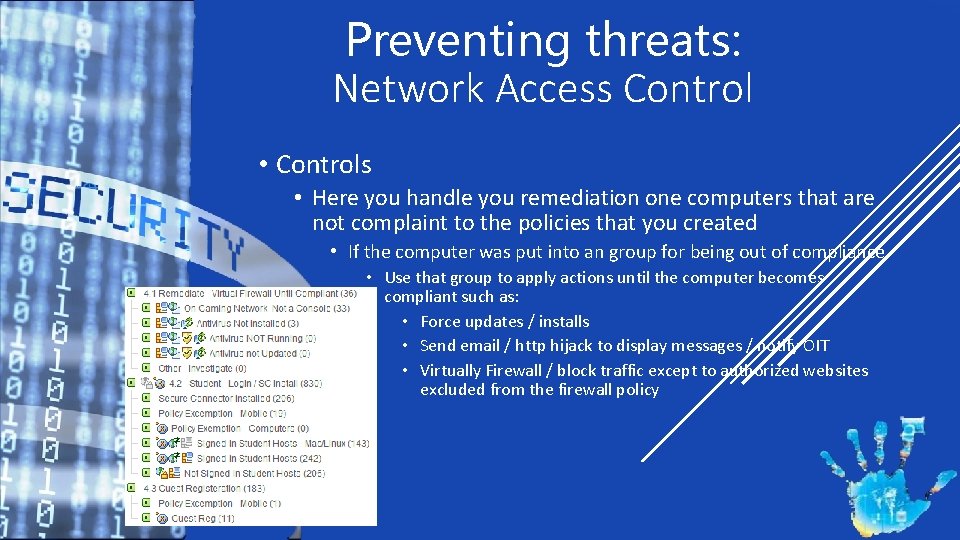
Preventing threats: Network Access Control • Controls • Here you handle you remediation one computers that are not complaint to the policies that you created • If the computer was put into an group for being out of compliance • Use that group to apply actions until the computer becomes compliant such as: • Force updates / installs • Send email / http hijack to display messages / notify OIT • Virtually Firewall / block traffic except to authorized websites excluded from the firewall policy
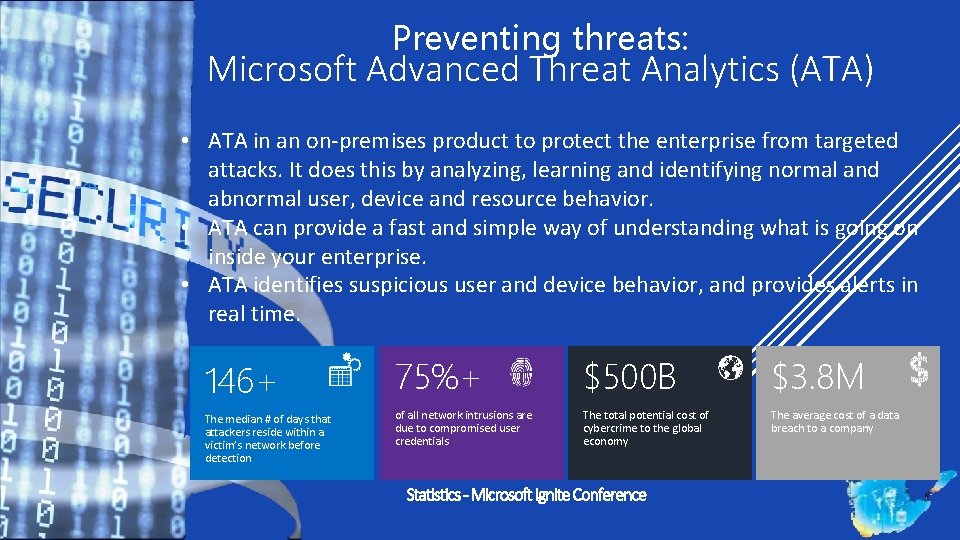
Preventing threats: Microsoft Advanced Threat Analytics (ATA) • ATA in an on-premises product to protect the enterprise from targeted attacks. It does this by analyzing, learning and identifying normal and abnormal user, device and resource behavior. • ATA can provide a fast and simple way of understanding what is going on inside your enterprise. • ATA identifies suspicious user and device behavior, and provides alerts in real time. 146+ 75%+ $500 B $3. 8 M The median # of days that attackers reside within a victim’s network before detection of all network intrusions are due to compromised user credentials The total potential cost of cybercrime to the global economy The average cost of a data breach to a company
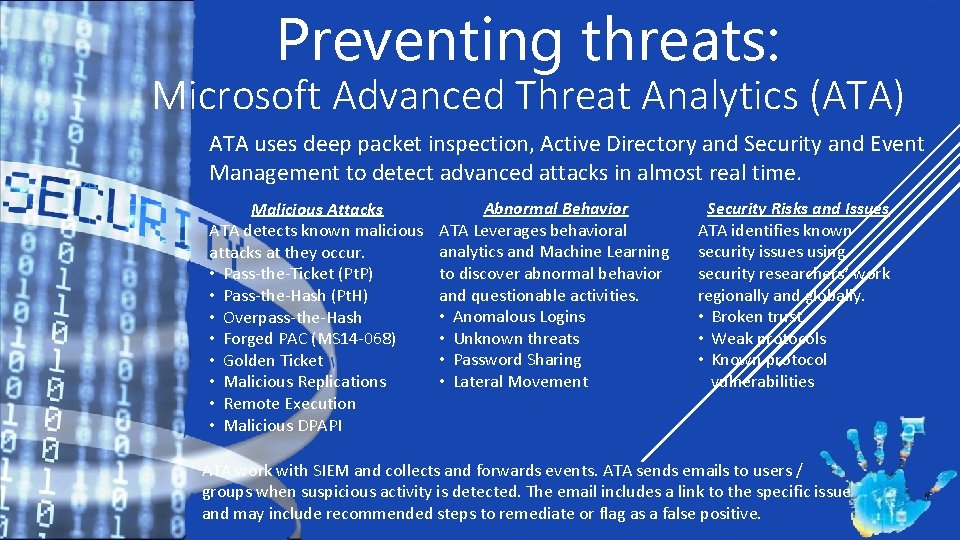
Preventing threats: Microsoft Advanced Threat Analytics (ATA) ATA uses deep packet inspection, Active Directory and Security and Event Management to detect advanced attacks in almost real time. Malicious Attacks ATA detects known malicious attacks at they occur. • Pass-the-Ticket (Pt. P) • Pass-the-Hash (Pt. H) • Overpass-the-Hash • Forged PAC (MS 14 -068) • Golden Ticket • Malicious Replications • Remote Execution • Malicious DPAPI Abnormal Behavior ATA Leverages behavioral analytics and Machine Learning to discover abnormal behavior and questionable activities. • Anomalous Logins • Unknown threats • Password Sharing • Lateral Movement Security Risks and Issues ATA identifies known security issues using security researchers’ work regionally and globally. • Broken trust • Weak protocols • Known protocol vulnerabilities ATA work with SIEM and collects and forwards events. ATA sends emails to users / groups when suspicious activity is detected. The email includes a link to the specific issue and may include recommended steps to remediate or flag as a false positive.
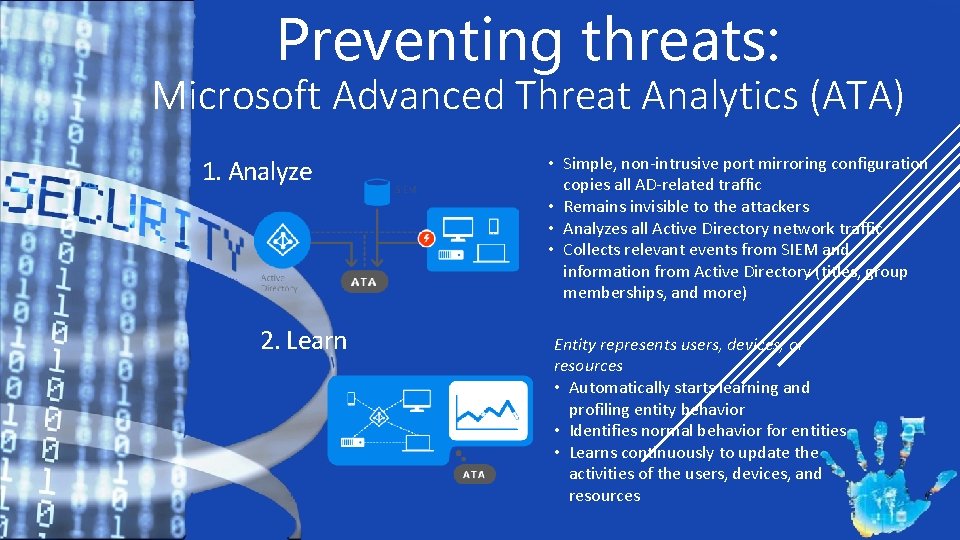
Preventing threats: Microsoft Advanced Threat Analytics (ATA) 1. Analyze 2. Learn • Simple, non-intrusive port mirroring configuration copies all AD-related traffic • Remains invisible to the attackers • Analyzes all Active Directory network traffic • Collects relevant events from SIEM and information from Active Directory (titles, group memberships, and more) Entity represents users, devices, or resources • Automatically starts learning and profiling entity behavior • Identifies normal behavior for entities • Learns continuously to update the activities of the users, devices, and resources
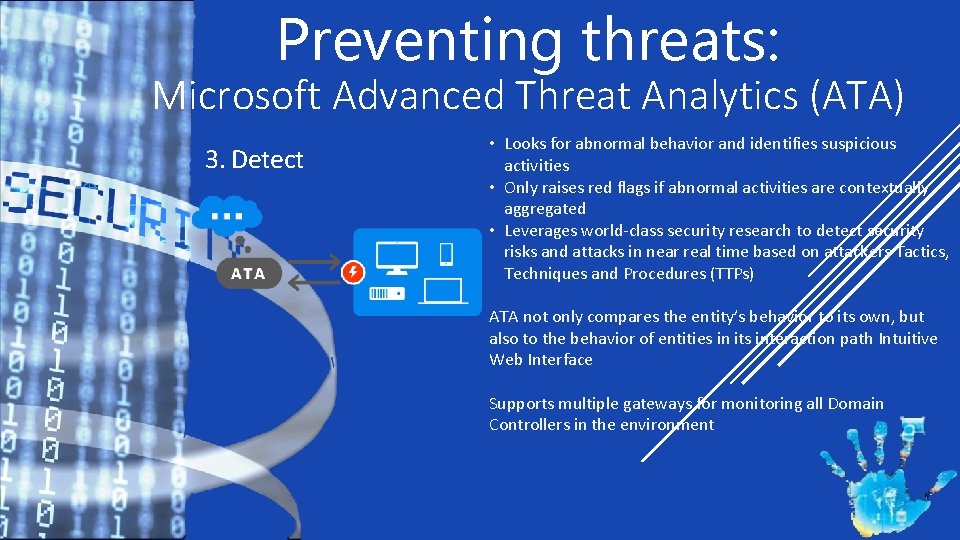
Preventing threats: Microsoft Advanced Threat Analytics (ATA) 3. Detect • Looks for abnormal behavior and identifies suspicious activities • Only raises red flags if abnormal activities are contextually aggregated • Leverages world-class security research to detect security risks and attacks in near real time based on attackers Tactics, Techniques and Procedures (TTPs) ATA not only compares the entity’s behavior to its own, but also to the behavior of entities in its interaction path Intuitive Web Interface Supports multiple gateways for monitoring all Domain Controllers in the environment

Preventing threats: Data Loss Prevention (DLP) • Use a DLP to find PII on endpoints and your network • Require weekly scans of employee computers • Require an security administrator to review results and follow-up with users not in compliance. • Scan your network for PII • Create encrypted shares on network to house PII that can’t be stored in databases. • Ensure that Senior Management will enforce compliance with employees who resist.
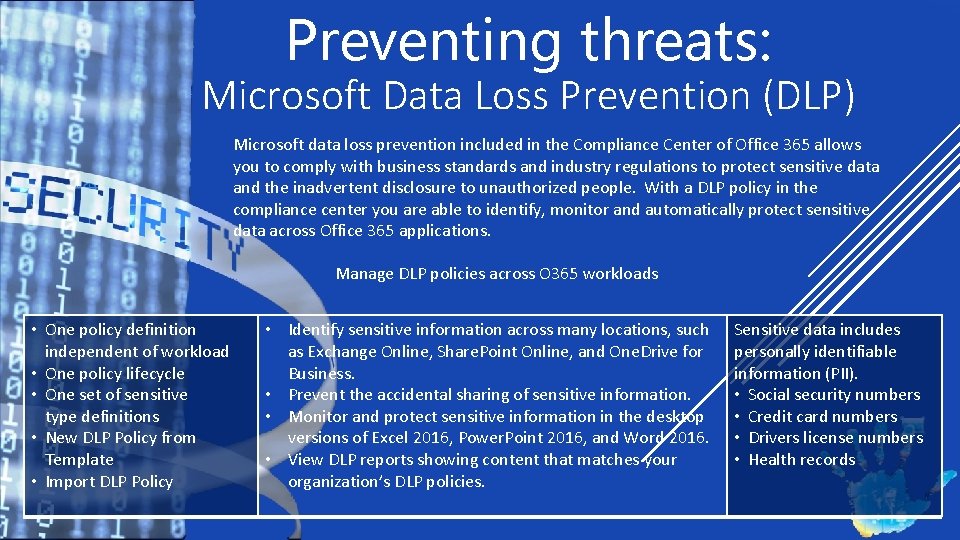
Preventing threats: Microsoft Data Loss Prevention (DLP) Microsoft data loss prevention included in the Compliance Center of Office 365 allows you to comply with business standards and industry regulations to protect sensitive data and the inadvertent disclosure to unauthorized people. With a DLP policy in the compliance center you are able to identify, monitor and automatically protect sensitive data across Office 365 applications. Manage DLP policies across O 365 workloads • One policy definition independent of workload • One policy lifecycle • One set of sensitive type definitions • New DLP Policy from Template • Import DLP Policy • Identify sensitive information across many locations, such as Exchange Online, Share. Point Online, and One. Drive for Business. • Prevent the accidental sharing of sensitive information. • Monitor and protect sensitive information in the desktop versions of Excel 2016, Power. Point 2016, and Word 2016. • View DLP reports showing content that matches your organization’s DLP policies. Sensitive data includes personally identifiable information (PII). • Social security numbers • Credit card numbers • Drivers license numbers • Health records

Preventing threats: Microsoft Data Loss Prevention (DLP) A DLP policy contains a few basic things: Where to protect the content – Exchange & Share. Point Online, and One. Drive When and how to protect the content by enforcing rules comprised of: • Conditions: determine what types of information you’re looking for, and when to take an action. • Actions: occur when content matches a condition in a rule, you can apply actions to automatically protect the document or content. With these actions, you can: Block the content For site content, this means that permissions for the document are restricted for everyone except the primary site collection administrator, document owner, and person who last modified the document. Send a notification / Policy Tip The email notification and policy tip explain why content conflicts with a DLP policy. If you choose, the email notification and policy tip can allow users to override a rule by reporting a false positive or providing a business justification. Information about overrides and false positives is also logged for reporting and included in the incident reports so it can be reviewed.
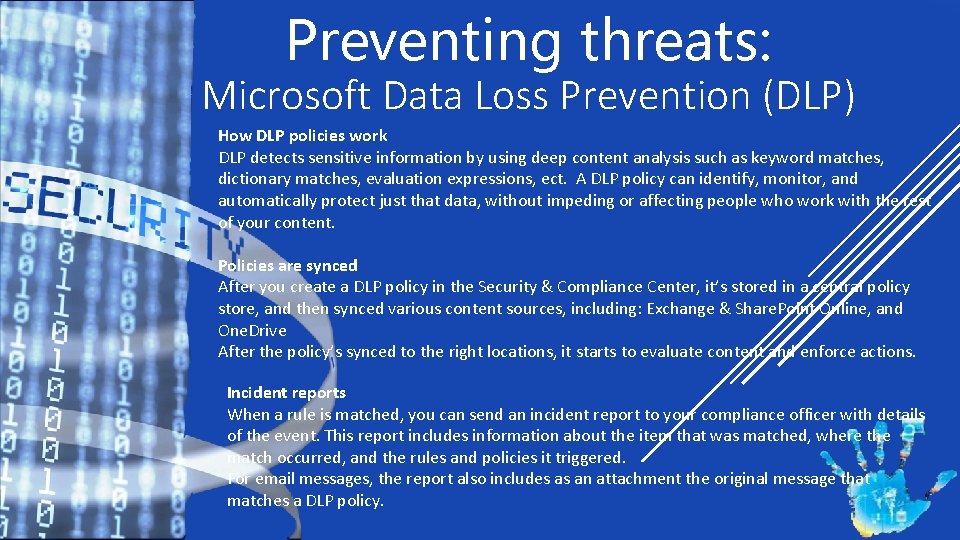
Preventing threats: Microsoft Data Loss Prevention (DLP) How DLP policies work DLP detects sensitive information by using deep content analysis such as keyword matches, dictionary matches, evaluation expressions, ect. A DLP policy can identify, monitor, and automatically protect just that data, without impeding or affecting people who work with the rest of your content. Policies are synced After you create a DLP policy in the Security & Compliance Center, it’s stored in a central policy store, and then synced various content sources, including: Exchange & Share. Point Online, and One. Drive After the policy’s synced to the right locations, it starts to evaluate content and enforce actions. Incident reports When a rule is matched, you can send an incident report to your compliance officer with details of the event. This report includes information about the item that was matched, where the match occurred, and the rules and policies it triggered. For email messages, the report also includes as an attachment the original message that matches a DLP policy.
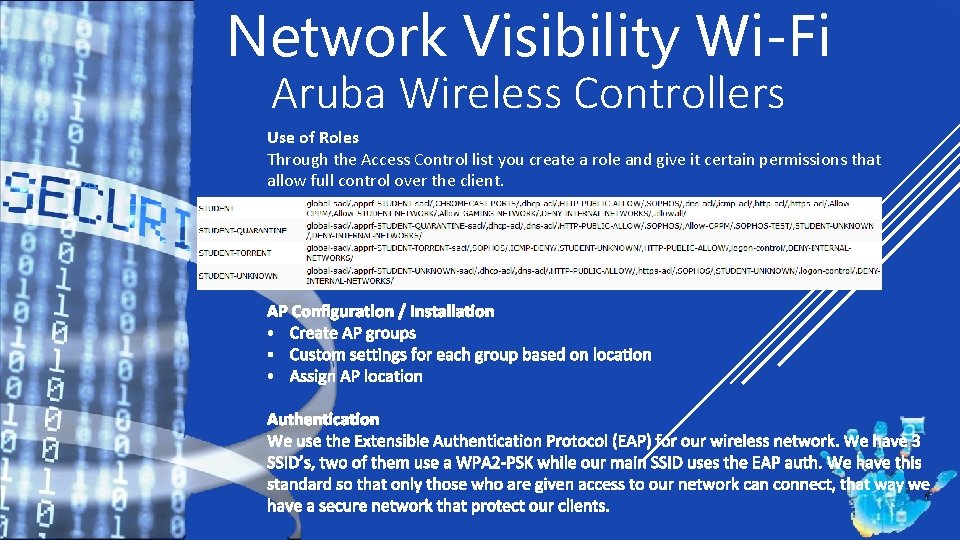
Network Visibility Wi-Fi Aruba Wireless Controllers Use of Roles Through the Access Control list you create a role and give it certain permissions that allow full control over the client.
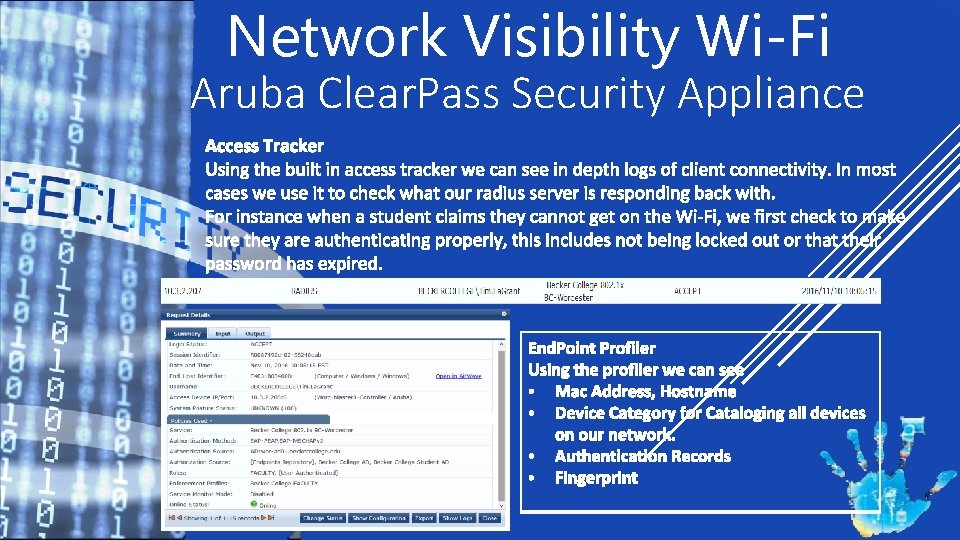
Network Visibility Wi-Fi Aruba Clear. Pass Security Appliance
Network Visibility Wi-Fi Aruba Clear. Pass Security Appliance
Network Visibility Wi-Fi Aruba Airwave Reporting Platform
Technology is critical, but…… EDUCATION is KEY • Topics to talk about • Phishing/malware/emails • Viruses • When to call IT • Approaches to Education • Surveys/online training • MAKE IT ENGAGING!!! “Don’t just stand there” • Give Prizes “Tell me and I forget. Teach me and I will remember Involve me and I learn”~Benjamin Franklin
- Slides: 32