Thesis Model Introduction Henrry C Y Chiang Thesis
- Slides: 22
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) Thesis Model Introduction Presented by: Henrry, C. Y. Chiang (江政祐) 9/11/202120071106 OPLAB, Dep. of Information Management, NTU 1 / 22
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) Today’s Agenda 1. Problem Description - A figural review 2. Problem Formulation - Given Parameters - Objective function and Constraints - Decision Variables 9/11/202120071106 OPLAB, Dep. of Information Management, NTU 2 / 22
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) Today’s Agenda 1. Problem Description 2. Problem Formulation - Given Parameters - Objective function and Constraints - Decision Variables 9/11/202120071106 OPLAB, Dep. of Information Management, NTU 3 / 22
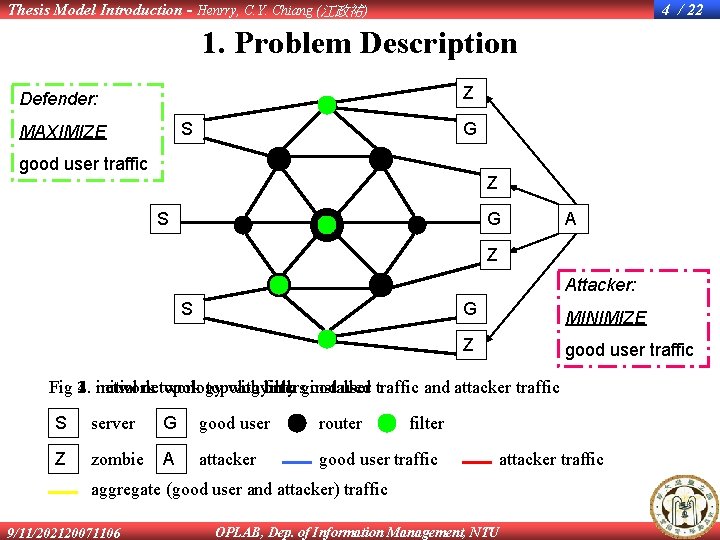
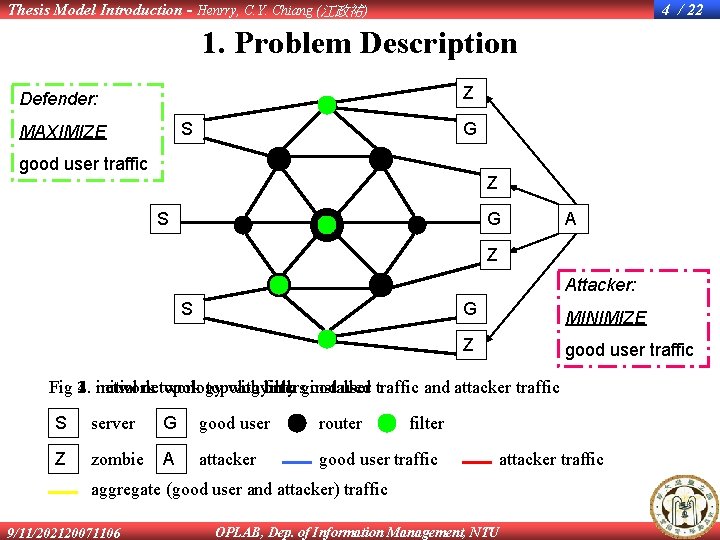
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 4 / 22 1. Problem Description Z Defender: S MAXIMIZE G good user traffic Z S G A Z Attacker: S G MINIMIZE Z good user traffic Fig 2. 1. 3. network 4. initial network topology with only both good filters installed user traffic and attacker traffic S server G good user router Z zombie A attacker good user traffic filter attacker traffic aggregate (good user and attacker) traffic 9/11/202120071106 OPLAB, Dep. of Information Management, NTU
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) Today’s Agenda 1. Problem Description 2. Problem Formulation - Given Parameters - Objective function and Constraints - Decision Variables 9/11/202120071106 OPLAB, Dep. of Information Management, NTU 5 / 22
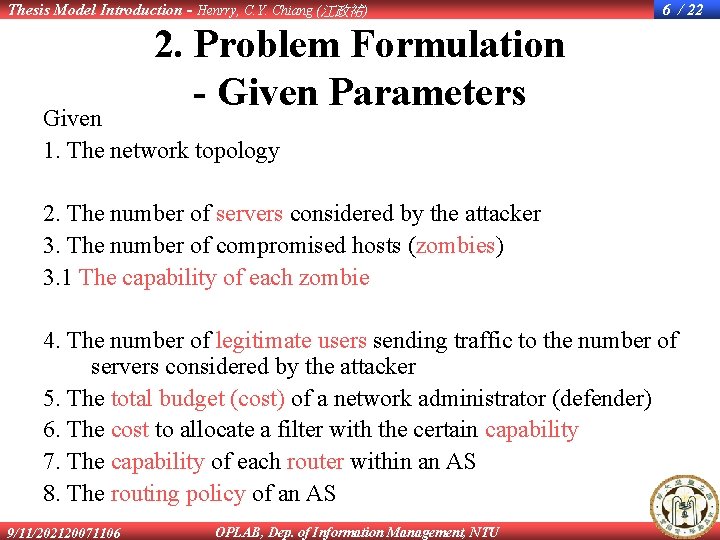
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 6 / 22 2. Problem Formulation - Given Parameters Given 1. The network topology 2. The number of servers considered by the attacker 3. The number of compromised hosts (zombies) 3. 1 The capability of each zombie 4. The number of legitimate users sending traffic to the number of servers considered by the attacker 5. The total budget (cost) of a network administrator (defender) 6. The cost to allocate a filter with the certain capability 7. The capability of each router within an AS 8. The routing policy of an AS 9/11/202120071106 OPLAB, Dep. of Information Management, NTU
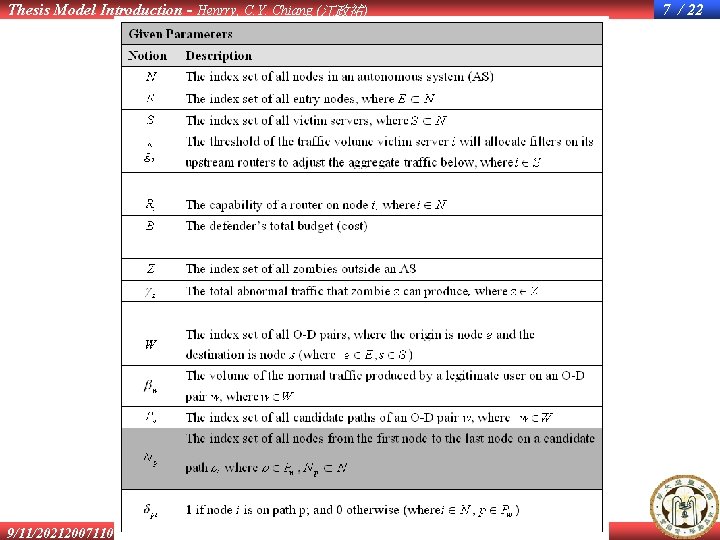
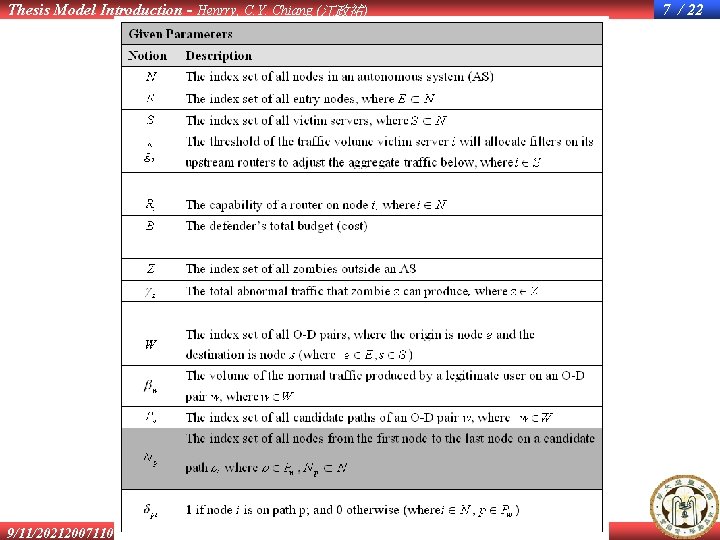
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 4. Problem Formulation - Given Parameters 9/11/202120071106 OPLAB, Dep. of Information Management, NTU 7 / 22
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) Today’s Agenda 1. Problem Description 2. Problem Formulation - Given Parameters - Objective function and Constraints - Decision Variables 9/11/202120071106 OPLAB, Dep. of Information Management, NTU 8 / 22
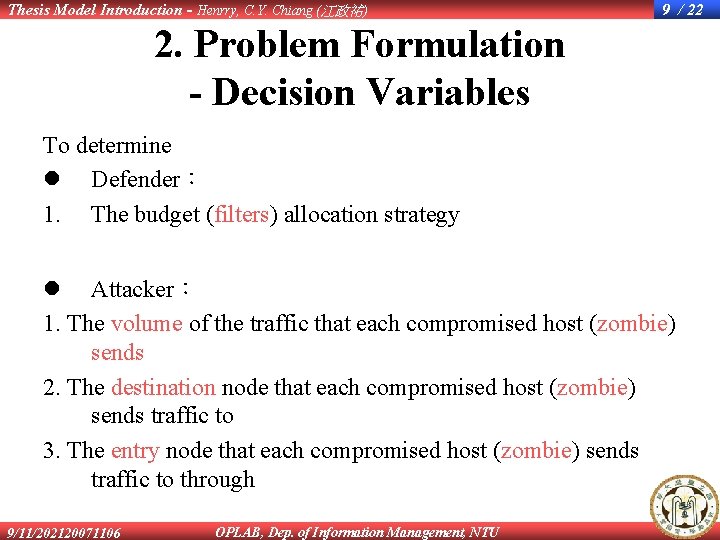
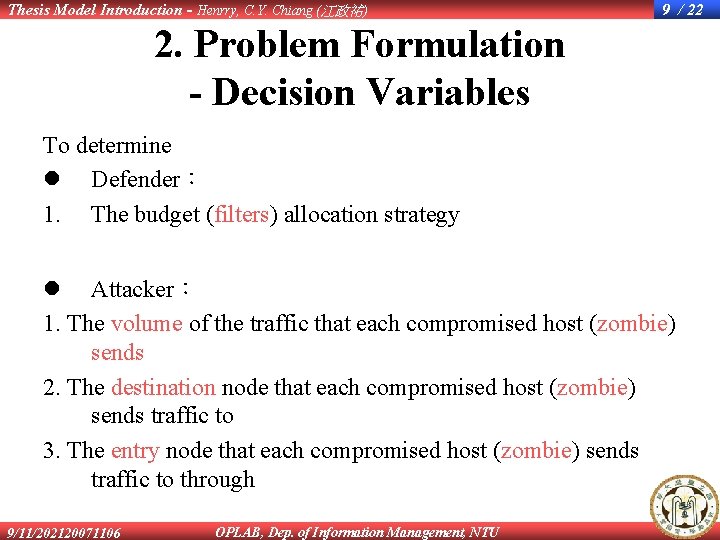
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 9 / 22 2. Problem Formulation - Decision Variables To determine l Defender: 1. The budget (filters) allocation strategy l Attacker: 1. The volume of the traffic that each compromised host (zombie) sends 2. The destination node that each compromised host (zombie) sends traffic to 3. The entry node that each compromised host (zombie) sends traffic to through 9/11/202120071106 OPLAB, Dep. of Information Management, NTU
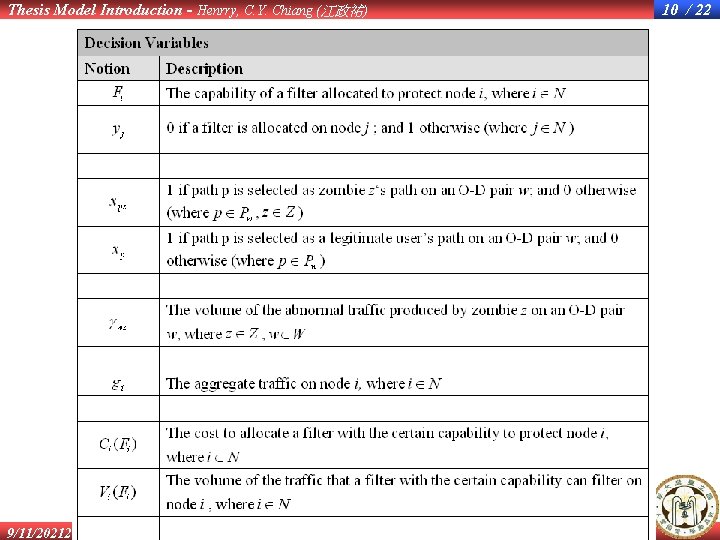
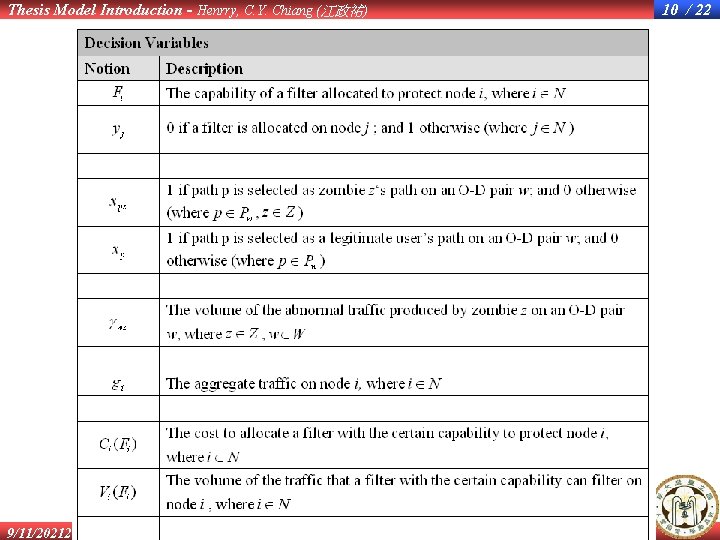
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 4. Problem Formulation - Decision Variables 9/11/202120071106 OPLAB, Dep. of Information Management, NTU 10 / 22
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) Today’s Agenda 1. Problem Description 2. Problem Formulation - Given Parameters - Objective function and Constraints - Decision Variables 9/11/202120071106 OPLAB, Dep. of Information Management, NTU 11 / 22
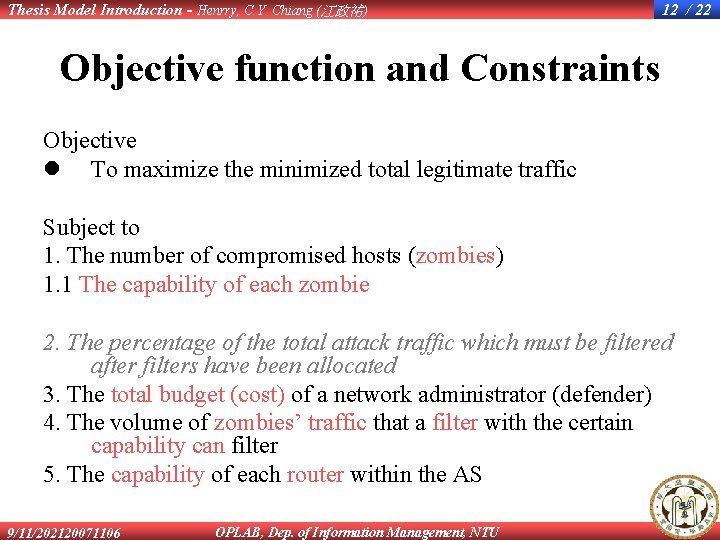
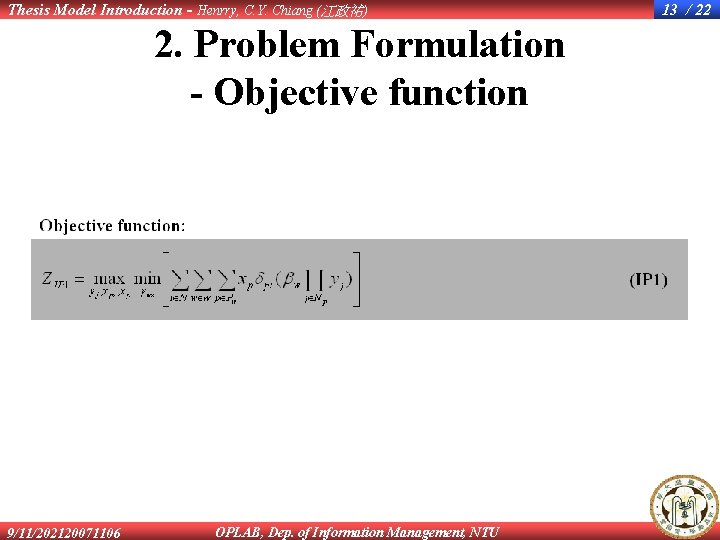
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 12 / 22 Objective function and Constraints Objective l To maximize the minimized total legitimate traffic Subject to 1. The number of compromised hosts (zombies) 1. 1 The capability of each zombie 2. The percentage of the total attack traffic which must be filtered after filters have been allocated 3. The total budget (cost) of a network administrator (defender) 4. The volume of zombies’ traffic that a filter with the certain capability can filter 5. The capability of each router within the AS 9/11/202120071106 OPLAB, Dep. of Information Management, NTU
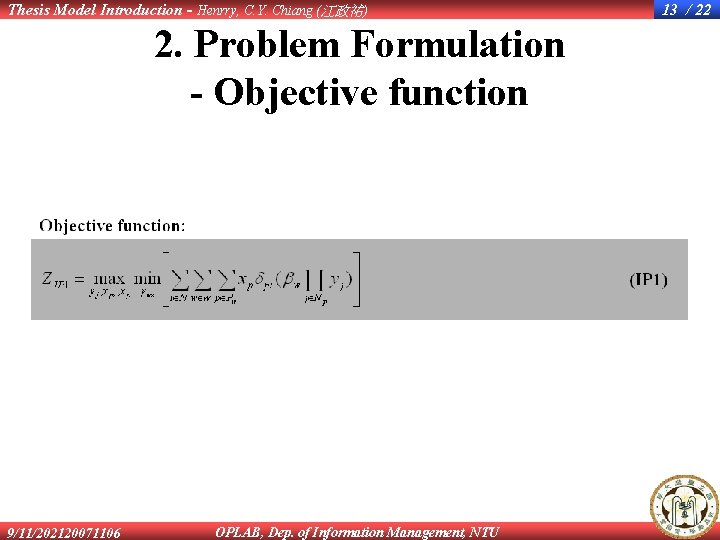
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 2. Problem Formulation - Objective function 9/11/202120071106 OPLAB, Dep. of Information Management, NTU 13 / 22
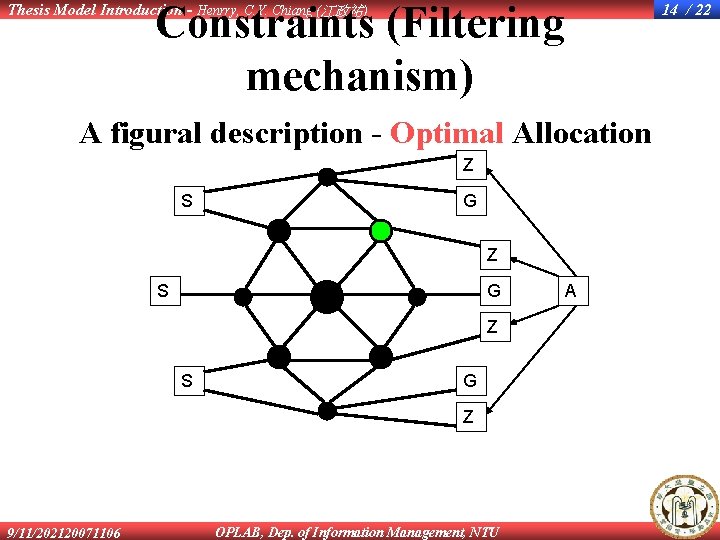
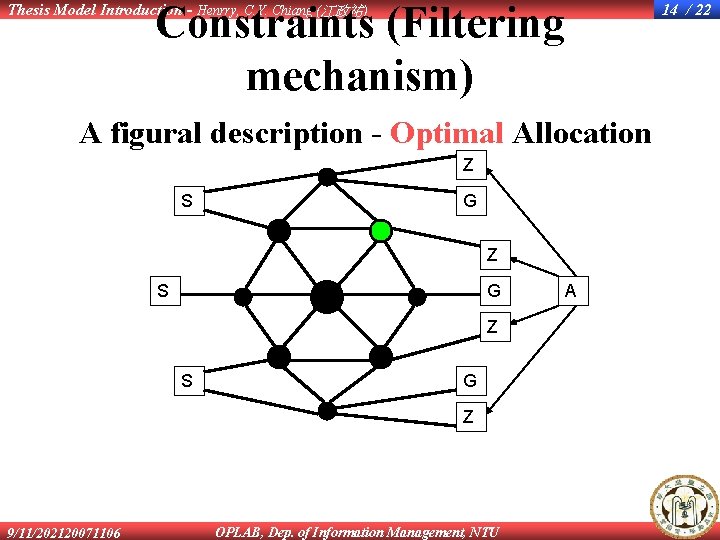
Constraints (Filtering mechanism) Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 14 / 22 A figural description - Optimal Allocation Z S G Z 9/11/202120071106 OPLAB, Dep. of Information Management, NTU A
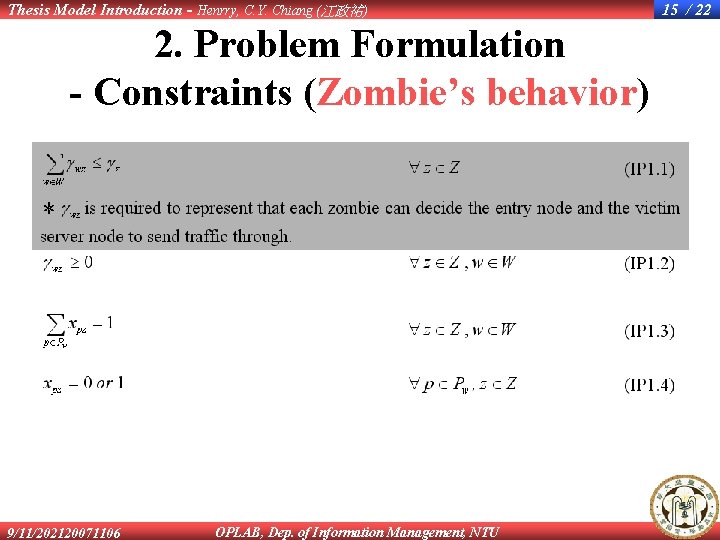
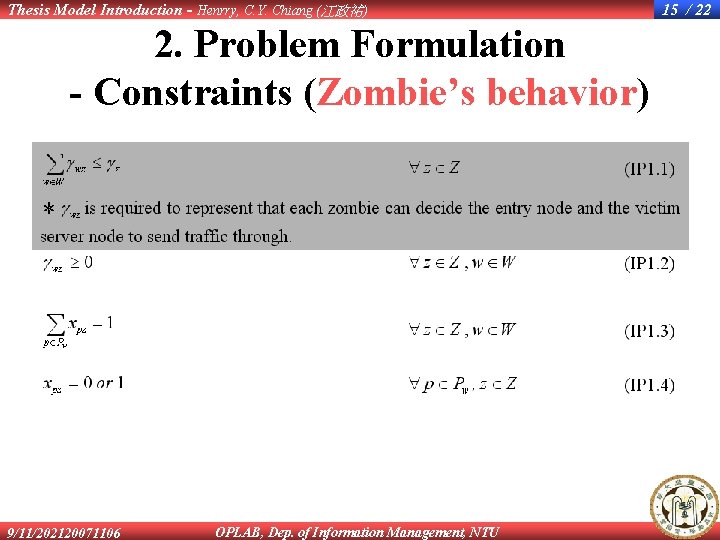
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 2. Problem Formulation - Constraints (Zombie’s behavior) 9/11/202120071106 OPLAB, Dep. of Information Management, NTU 15 / 22
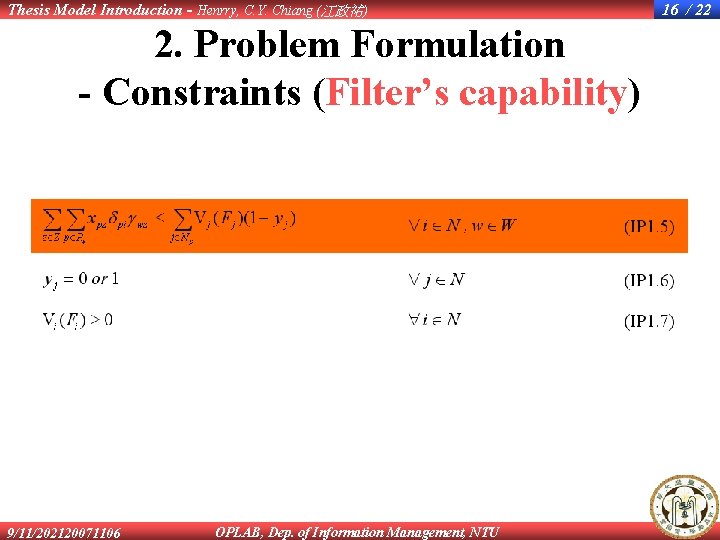
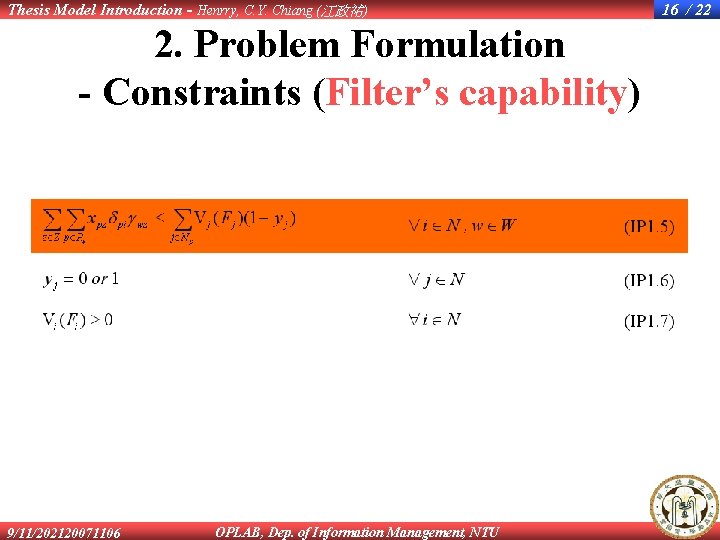
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 2. Problem Formulation - Constraints (Filter’s capability) 9/11/202120071106 OPLAB, Dep. of Information Management, NTU 16 / 22
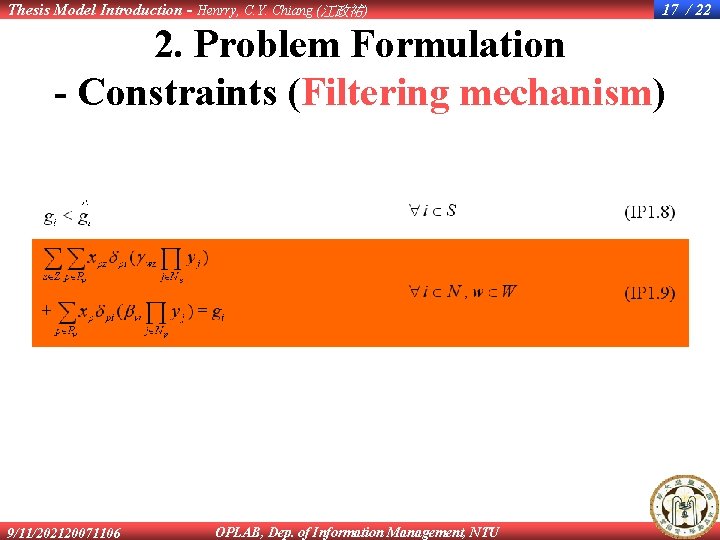
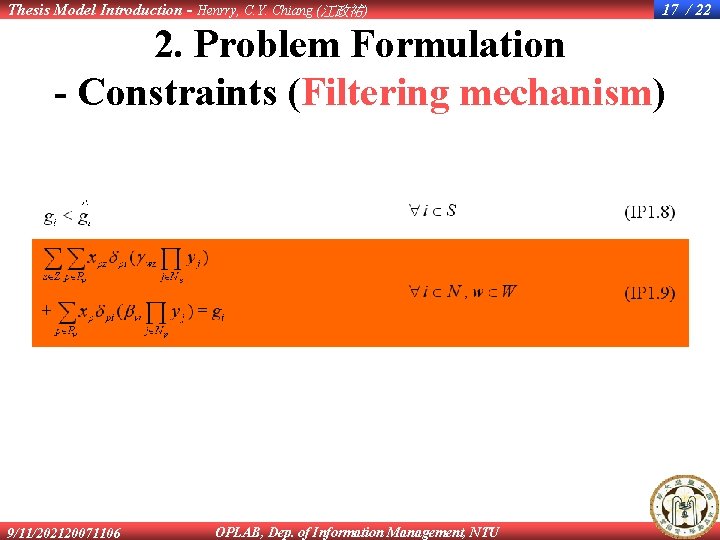
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 17 / 22 2. Problem Formulation - Constraints (Filtering mechanism) 9/11/202120071106 OPLAB, Dep. of Information Management, NTU
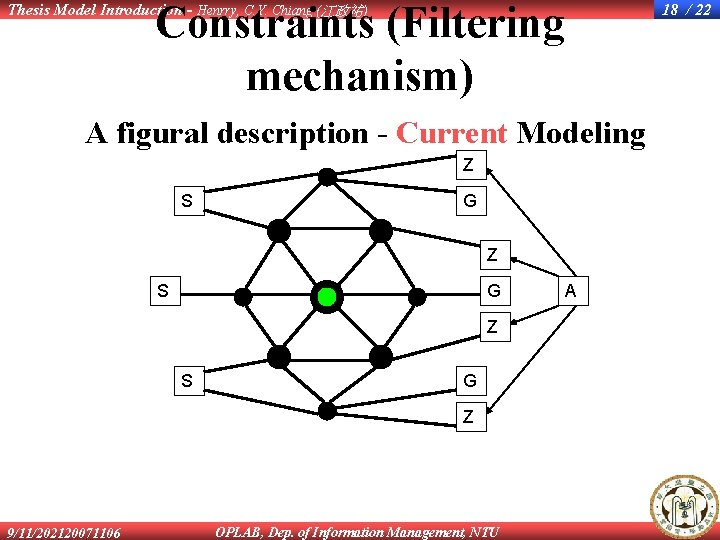
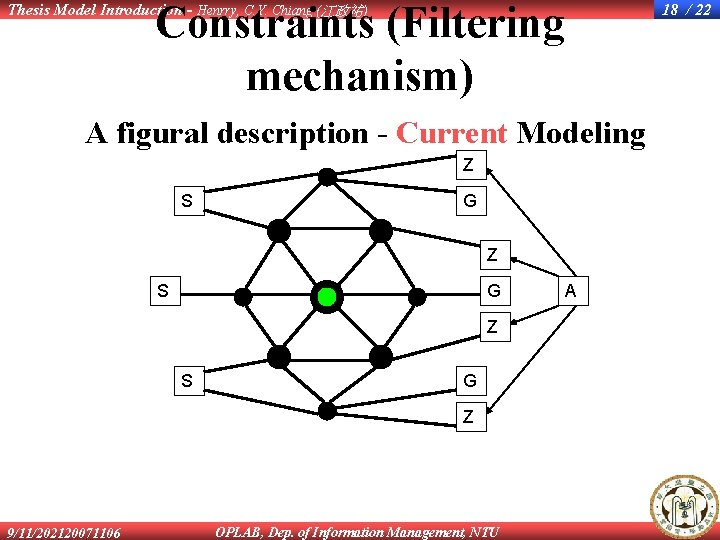
Constraints (Filtering mechanism) Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 18 / 22 A figural description - Current Modeling Z S G Z 9/11/202120071106 OPLAB, Dep. of Information Management, NTU A
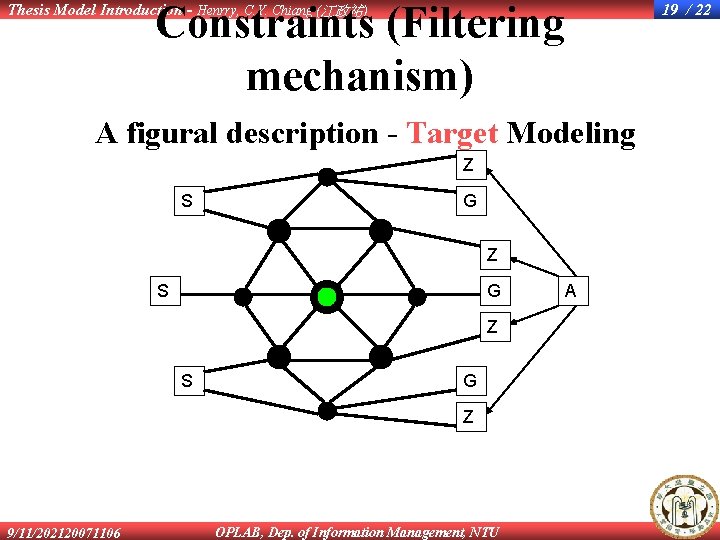
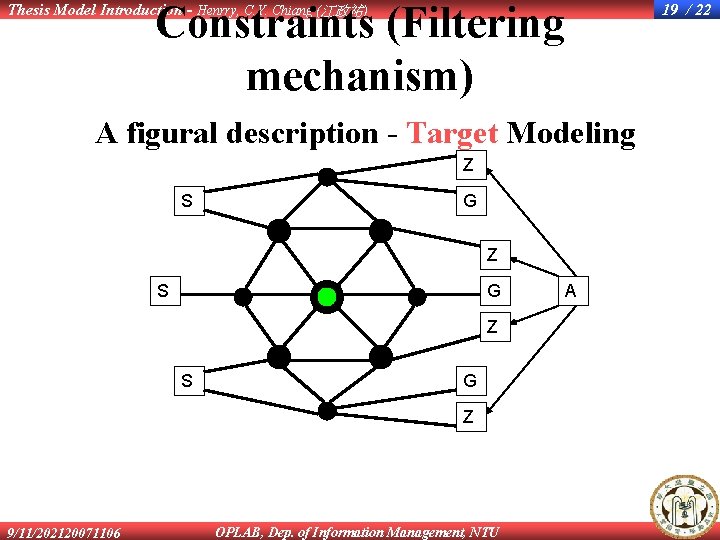
Constraints (Filtering mechanism) Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 19 / 22 A figural description - Target Modeling Z S G Z 9/11/202120071106 OPLAB, Dep. of Information Management, NTU A
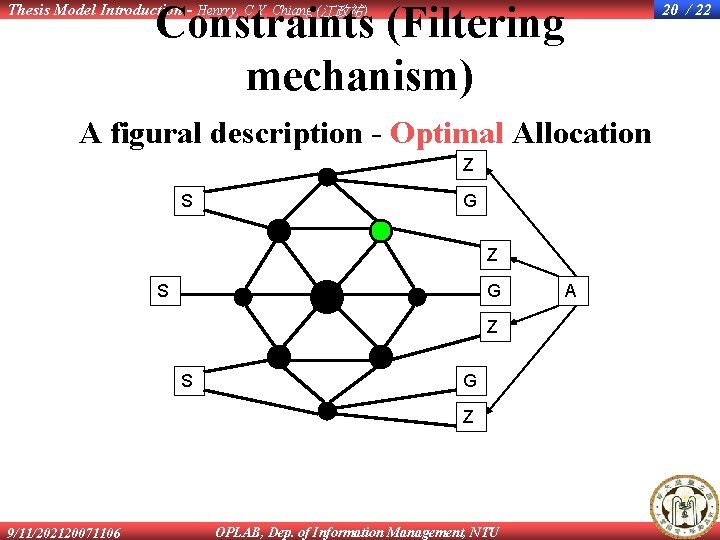
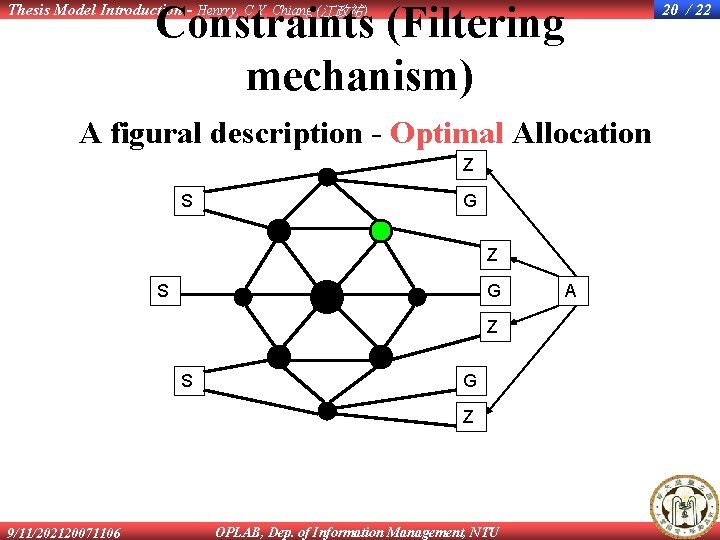
Constraints (Filtering mechanism) Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 20 / 22 A figural description - Optimal Allocation Z S G Z 9/11/202120071106 OPLAB, Dep. of Information Management, NTU A
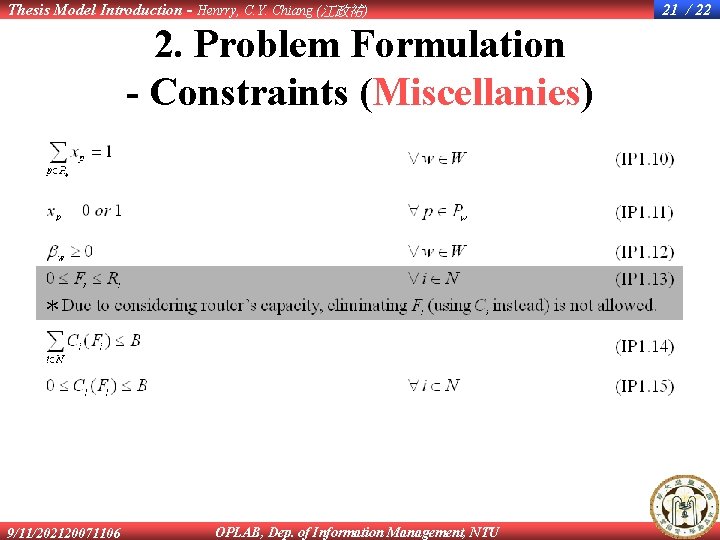
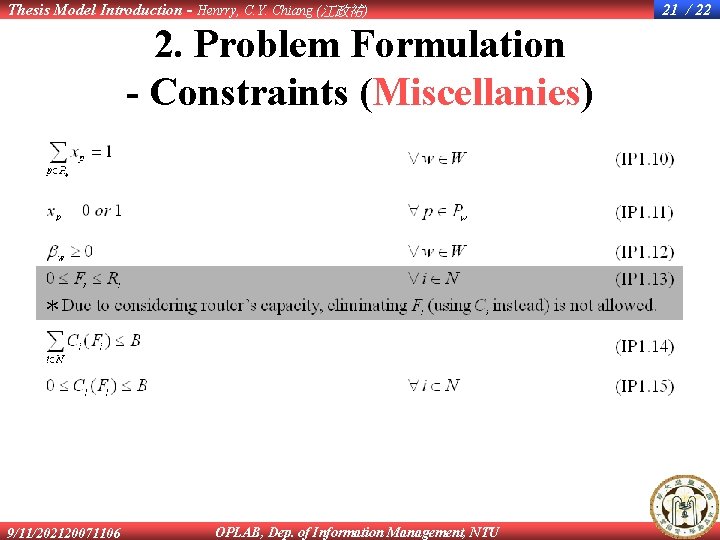
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 2. Problem Formulation - Constraints (Miscellanies) 9/11/202120071106 OPLAB, Dep. of Information Management, NTU 21 / 22
Thesis Model Introduction - Henrry, C. Y. Chiang (江政祐) 22 / 22 The End - It’s my greatest honor to have your attention. 9/11/202120071106 OPLAB, Dep. of Information Management, NTU