Theories of cyberspace regulation z The problem Cyberspace
Theories of cyberspace regulation z. The problem: Cyberspace is a different context from the physical world. y. We may need to rethink how regulation of behaviour works. z. The question: What regulates? y. What different forms of regulation are there?
Forms of regulation z Lawrence Lessig's answers: y 4 things regulate - Norms; Markets, Law and 'Code' (environment) y. Law also regulates the other 3 - indirect regulation by law y. Effectiveness is very different in cyberspace z Lessig's main lesson: Consider all 4 and how they interact z Criticism: Surveillance is a 5 th form of regulation
1 Norms, morality and selfregulation z. Real space norms cause disapproval and guilt z. Cyberspace has its own 'netiquette' y. Examples: using CAPITALS; attachments sent to lists z. Effectiveness in cyberspace increased by surveillance y. The morality of the goldfish bowl
2 Markets z. Market constrains work in cyberspace z. Unpopular 'code' can perish y. Selling region-blocked DVD players in HK? y. Surveillance damaged Double. Click's share price z. Prices can affect norms y. Are CD / DVD prices considered fair? y. Is DVD region blocking fair?
3 'Code’ (environment) z In real space - Natural and built environment y. Bank robberies - Laws and morality help; but walls, locks, glass & guns are better y. Immigration - Distance and lack of borders y. Easy to ignore, often because unchangeable z In cyberspace - ‘Code’ is the equivalent y. Can control access, and monitor it y. Determines what actions are possible and impossible y‘A set of constraints on how one can behave’ -Lessig y. The walls, bridges, locks and cameras of cyberspace
‘Code' or 'architecture'? z 'Code' is cute but confusing y. East code (Washington) vs West coast code (Redmond) y. The US Code vs hackers' code z 'Architecture' is more accurate y. Cyberspace is more than software x. Protocols (non-material artefacts) x. Hardware (material artefacts) x. Biology and geography (natural environment) z 'Code' is part of cyberspace architecture
4 Law - direct and indirect z. Law increasingly directly regulates cyberspace behaviour z. But it indirectly regulates the other 3 constraints z. Legal regulation of architecture is the key y. It is the most effective strategy for governments y. It is also vital for limiting private power
Effective regulation z. Finding the best mix of constraints y. How to prevent discrimination? x. Prohibition; education; building codes y. How to stop people smoking? x. Age limits; prohibited places; education; warnings; taxes
Surveillance: 5 th constraint z. A relationship of knowledge y. Knowledge by the watcher of those watched y. Foucault's 'discipline'; Bentham's Panopticon y. Facilitated by architecture, but not part of it y. Facilitates observance of norms and laws, but independent z. More important in cyberspace regulation y. The normal context of identification is removed y. Identification, not anonymity, is the default
Law modifying surveillance z. Law acts indirectly to modify surveillance y. Data protection laws protect privacy x. Eg Personal Data (Privacy) Ordinance y. Laws mandate compliance xeg smart ID card y. Laws prevent circumvention xeg DRMS anti-circumvention
Cyber-regulation is different z. Cyberspace architecture is mainly artefact z. Greater immediacy of application y. Cyberspace architecture is often selfexecuting z. Most architecture has high plasticity y. Its easier to change cyberspace z. Architecture's legitimacy is questionable y. We should ask the pedigree of any regulation y. What should private companies control?
Example: Copyright, DRMS and anti-circumvention z. DRMS - The new paradigm for content protection y. Copyright law was the old paradigm z. Content owners want to control 3 parties y. Content consumers y. Consumer hardware manufacturers y. Content intermediaries z(DRMS diagram modified from Bechtold)
Importance of 'commons' z. Lessig's argument in ’The Future of Ideas' y. The Internet is an 'innovation commons’ y. It is in danger of losing that character z'Commons' - Resources from which noone may be excluded - the 'free' z. Commons are not necessarily 'tragic': y. Not if they are non-rivalrous (eg protocols) y. Not if you control over-consumption y. Both require sufficient incentives to create
Internet as an 'innovation commons' z. Benefits of the Internet as a commons y. Benefits to freedom (first book) y. Benefits to innovation (second book) z. Must consider each Internet 'layer' y. Physical layer, 'code' layer (protocols and applications) and content layer y. Each could be a commons or controlled y. Currently, each layer is partly controlled y. Changes imperil the mix providing innovation
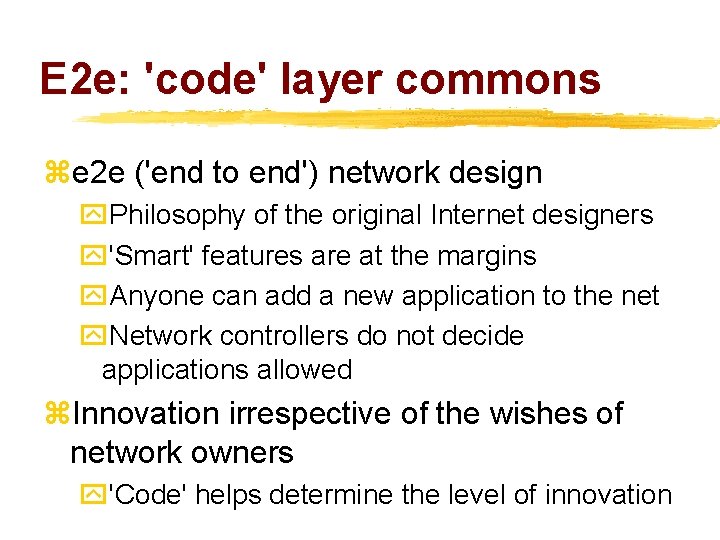
E 2 e: 'code' layer commons ze 2 e ('end to end') network design y. Philosophy of the original Internet designers y'Smart' features are at the margins y. Anyone can add a new application to the net y. Network controllers do not decide applications allowed z. Innovation irrespective of the wishes of network owners y'Code' helps determine the level of innovation
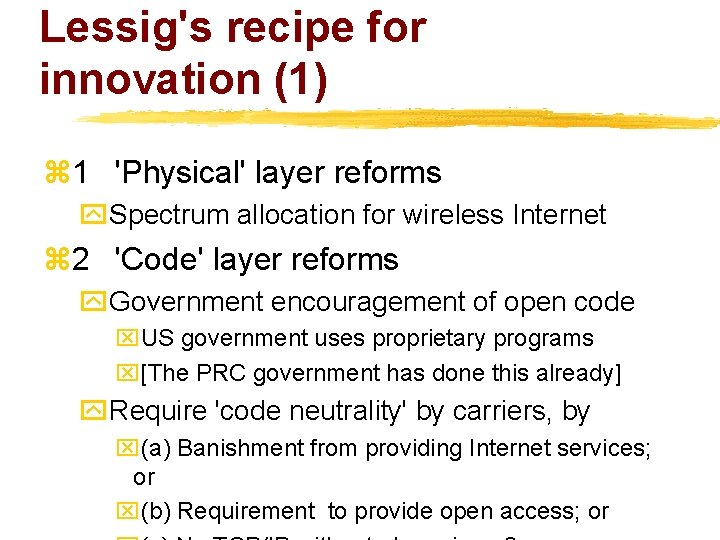
Lessig's recipe for innovation (1) z 1 'Physical' layer reforms y. Spectrum allocation for wireless Internet z 2 'Code' layer reforms y. Government encouragement of open code x. US government uses proprietary programs x[The PRC government has done this already] y. Require 'code neutrality' by carriers, by x(a) Banishment from providing Internet services; or x(b) Requirement to provide open access; or
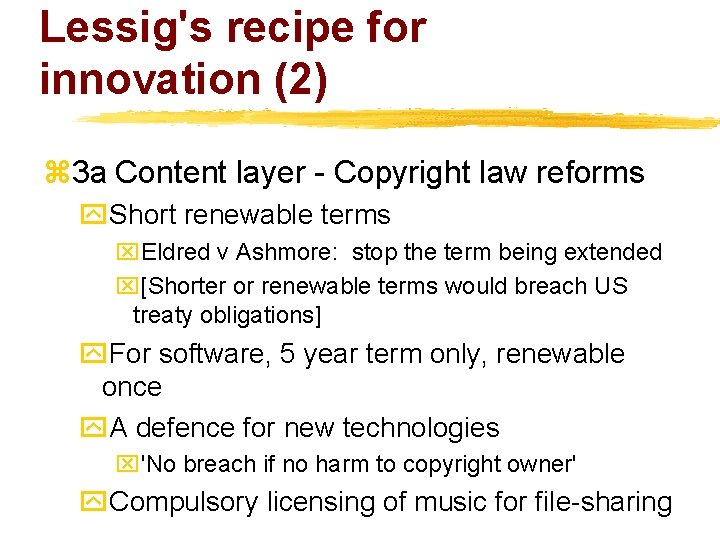
Lessig's recipe for innovation (2) z 3 a Content layer - Copyright law reforms y. Short renewable terms x. Eldred v Ashmore: stop the term being extended x[Shorter or renewable terms would breach US treaty obligations] y. For software, 5 year term only, renewable once y. A defence for new technologies x'No breach if no harm to copyright owner' y. Compulsory licensing of music for file-sharing
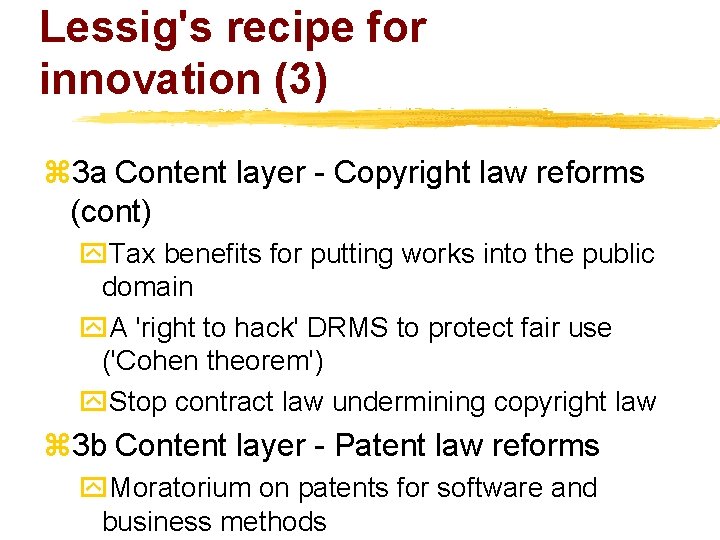
Lessig's recipe for innovation (3) z 3 a Content layer - Copyright law reforms (cont) y. Tax benefits for putting works into the public domain y. A 'right to hack' DRMS to protect fair use ('Cohen theorem') y. Stop contract law undermining copyright law z 3 b Content layer - Patent law reforms y. Moratorium on patents for software and business methods
References(1) z. Works by Lawrence Lessig • Lawrence Lessig 'The Law of the Horse: What Cyberlaw Might Teach' (PDF only) (1999) 113 Harvard Law Review 501 (drafts were available from 1997) • Lawrence Lessig Code and Other Laws of Cyberspace Basic Books 1999 • Lawrence Lessig 'Cyberspace's Architectural Constitution' (June 2000, Text of lecture at www 9, Amsterdam) • Lawrence Lessig The Future of Ideas: The Fate of the Commons in a Connected World Random House, 2001 • See his home page for links to these and others
References(2) z. Works by others • James Boyle 'Surveillance, Sovereignty, and Hard-Wired Censors' (1997) • Graham Greenleaf 'An Endnote on Regulating Cyberspace: Architecture vs Law? (1998) University of New South Wales Law Journal Volume 21, Number 2 • Stefan Bechtold 'From Copyright to Information Law Implications of Digital Rights Management'. Workshop on Security and Privacy in Digital Rights Management 2001. 5. November 2001, Philadelphia, USA. • See the Timetable for further reading
- Slides: 22