The Wave of Regulations Email Management Presented by
The Wave of Regulations --E-mail Management Presented by Lillian
Outline Motivation l Regulations Introduction l Common Concepts and Their Issues l IT Applications of Common Issues l Regulations Compliance l Conclusion l

Motivation The Importance of Regulations Compliance
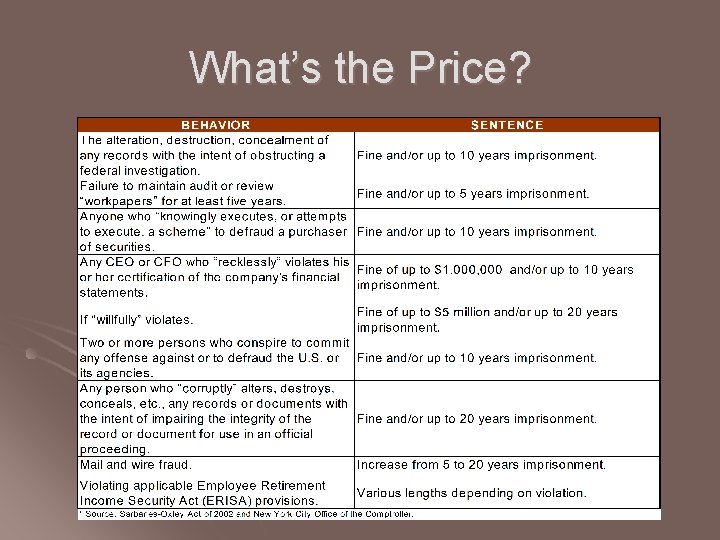
What’s the Price?
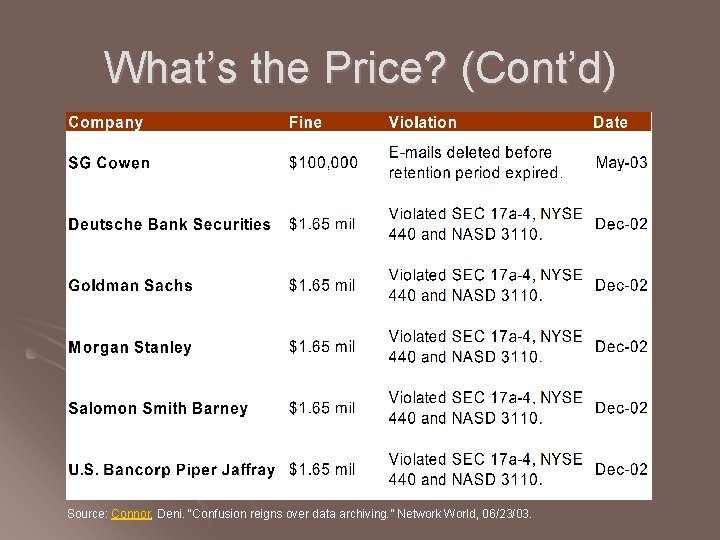
What’s the Price? (Cont’d) Source: Connor, Deni. “Confusion reigns over data archiving. ” Network World, 06/23/03.

What’s the Price? (Cont’d) Company Fine Reason Date (2004) Bank of America $ 10 million Fail to produce e March 1 st -mail Citigroup, Merrill Lynch and Morgan Stanley $750, 000 (by NASD) Fail to comply with discovery obligations in arbitrations July 19 th Philip Morris $2. 75 million E-mail destruction July 21 st Deutsche Bank $7. 7 million Fail to promptly August 27 th produce e-mails Source: Steve Gray, “Compliance and Content Management Solution”, Sun Microsystems Inc. 2004

Why Are These Regulations Important? l World wide business l In order to comply with these regulations, companies in US have to preserve documents for auditing or lawsuit cases, so as their partners. l International competency l All public companies in US must comply with the regulations. l TSMC
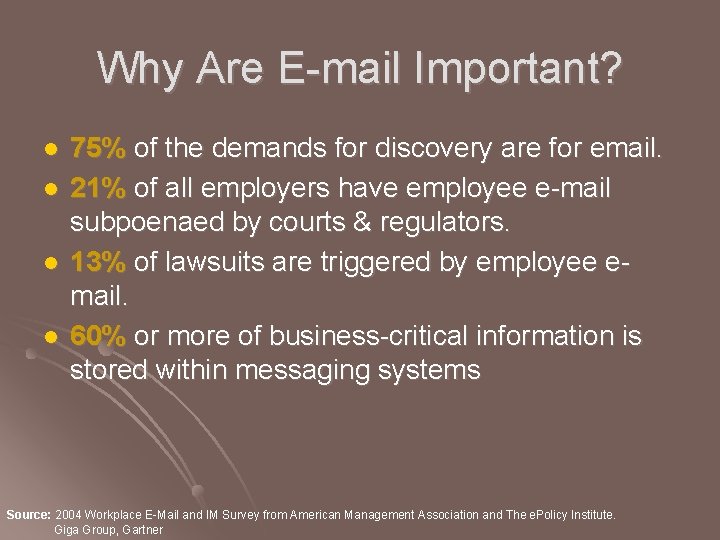
Why Are E-mail Important? l l 75% of the demands for discovery are for email. 21% of all employers have employee e-mail subpoenaed by courts & regulators. 13% of lawsuits are triggered by employee email. 60% or more of business-critical information is stored within messaging systems Source: 2004 Workplace E-Mail and IM Survey from American Management Association and The e. Policy Institute. Giga Group, Gartner

Regulations Introduction
Regulations Introduction Sarbanes-Oxley Act (SOX) l SEC regulation 17 a-3 and 17 a-4 l NASD 3010 & 3110 l Health Insurance Portability and Accountability Act (HIPAA) l
Sarbanes-Oxley Act (SOX) l Origin l signed into law July 30 2002. l A direct result of corporate scandals, such as Enron and World. Com. l Goal l Ensure accurate reporting of public companies’ finances for the benefit of investors, focusing on integrity of information and process.
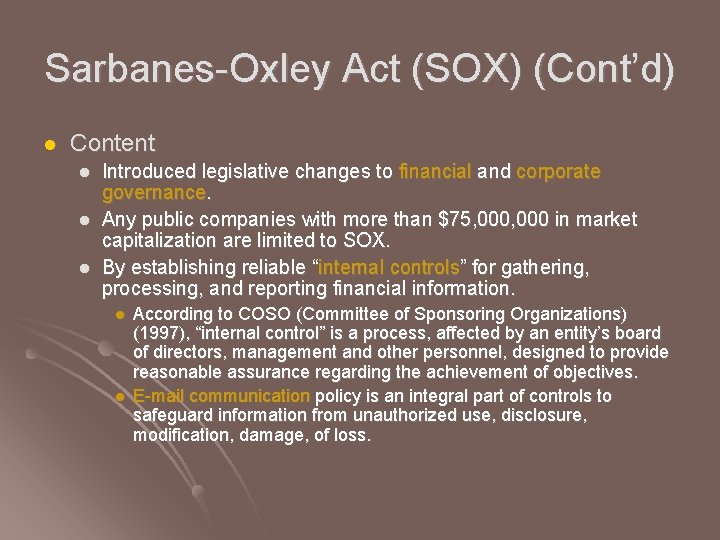
Sarbanes-Oxley Act (SOX) (Cont’d) l Content l l l Introduced legislative changes to financial and corporate governance. Any public companies with more than $75, 000 in market capitalization are limited to SOX. By establishing reliable “internal controls” for gathering, processing, and reporting financial information. l l According to COSO (Committee of Sponsoring Organizations) (1997), “internal control” is a process, affected by an entity’s board of directors, management and other personnel, designed to provide reasonable assurance regarding the achievement of objectives. E-mail communication policy is an integral part of controls to safeguard information from unauthorized use, disclosure, modification, damage, of loss.
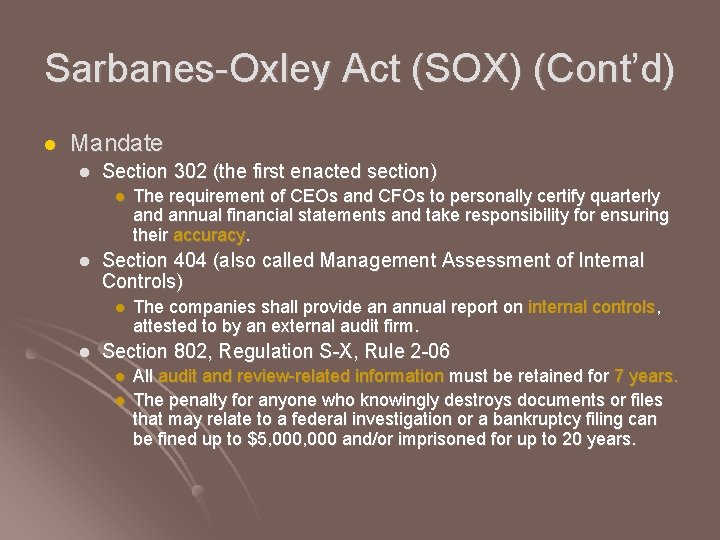
Sarbanes-Oxley Act (SOX) (Cont’d) l Mandate l Section 302 (the first enacted section) l l Section 404 (also called Management Assessment of Internal Controls) l l The requirement of CEOs and CFOs to personally certify quarterly and annual financial statements and take responsibility for ensuring their accuracy. The companies shall provide an annual report on internal controls, attested to by an external audit firm. Section 802, Regulation S-X, Rule 2 -06 l l All audit and review-related information must be retained for 7 years. The penalty for anyone who knowingly destroys documents or files that may relate to a federal investigation or a bankruptcy filing can be fined up to $5, 000 and/or imprisoned for up to 20 years.
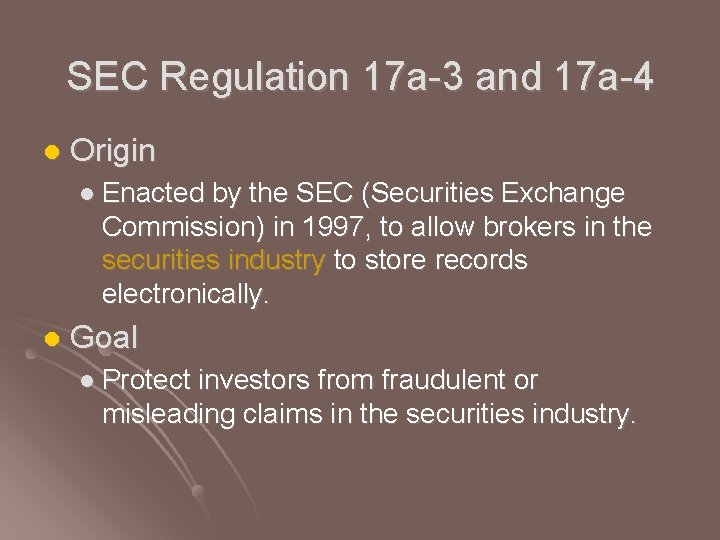
SEC Regulation 17 a-3 and 17 a-4 l Origin l Enacted by the SEC (Securities Exchange Commission) in 1997, to allow brokers in the securities industry to store records electronically. l Goal l Protect investors from fraudulent or misleading claims in the securities industry.
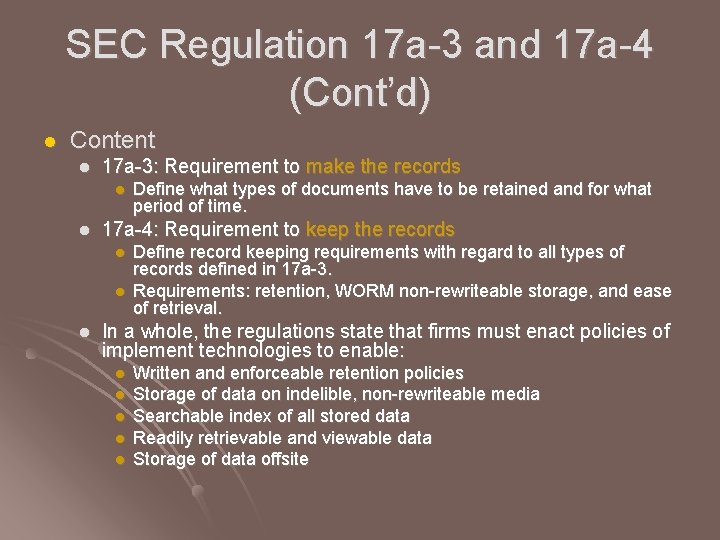
SEC Regulation 17 a-3 and 17 a-4 (Cont’d) l Content l 17 a-3: Requirement to make the records l l 17 a-4: Requirement to keep the records l l l Define what types of documents have to be retained and for what period of time. Define record keeping requirements with regard to all types of records defined in 17 a-3. Requirements: retention, WORM non-rewriteable storage, and ease of retrieval. In a whole, the regulations state that firms must enact policies of implement technologies to enable: l l l Written and enforceable retention policies Storage of data on indelible, non-rewriteable media Searchable index of all stored data Readily retrievable and viewable data Storage of data offsite
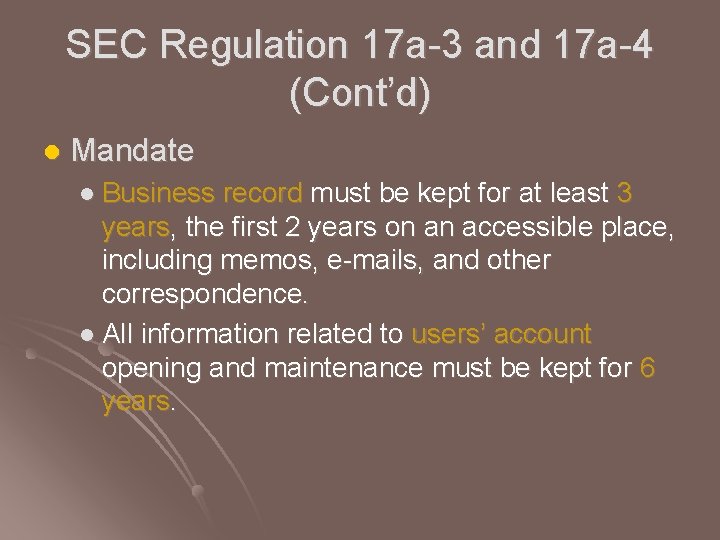
SEC Regulation 17 a-3 and 17 a-4 (Cont’d) l Mandate l Business record must be kept for at least 3 years, the first 2 years on an accessible place, including memos, e-mails, and other correspondence. l All information related to users’ account opening and maintenance must be kept for 6 years.
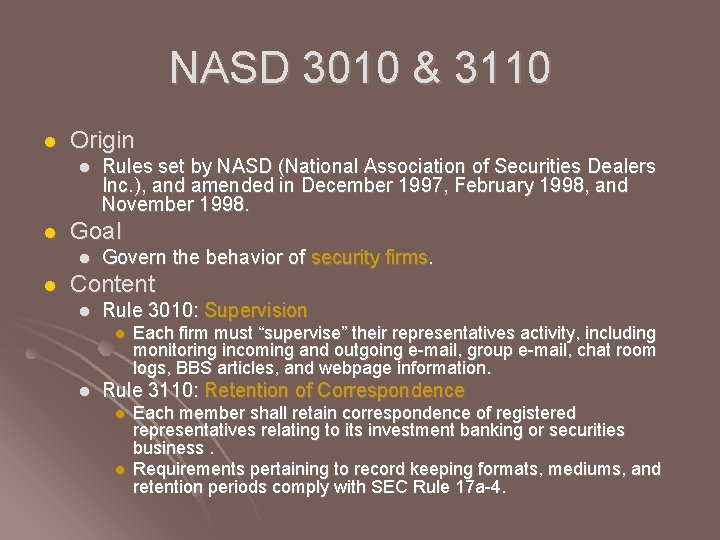
NASD 3010 & 3110 l Origin l l Goal l l Rules set by NASD (National Association of Securities Dealers Inc. ), and amended in December 1997, February 1998, and November 1998. Govern the behavior of security firms. Content l Rule 3010: Supervision l l Each firm must “supervise” their representatives activity, including monitoring incoming and outgoing e-mail, group e-mail, chat room logs, BBS articles, and webpage information. Rule 3110: Retention of Correspondence l l Each member shall retain correspondence of registered representatives relating to its investment banking or securities business. Requirements pertaining to record keeping formats, mediums, and retention periods comply with SEC Rule 17 a-4.
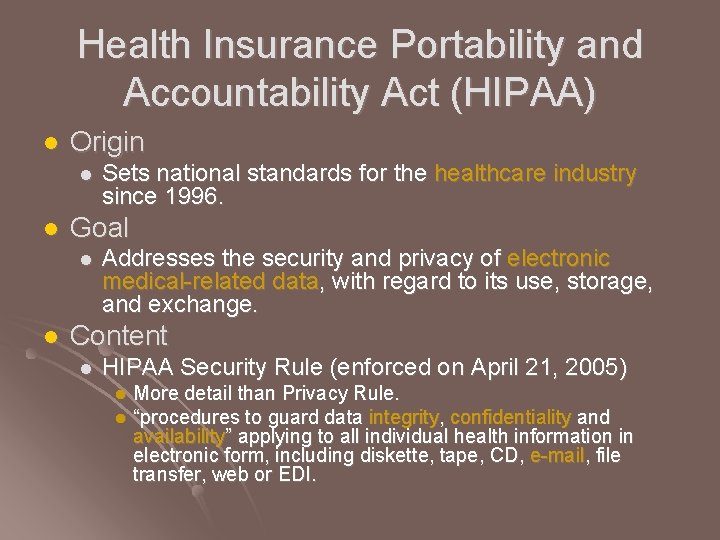
Health Insurance Portability and Accountability Act (HIPAA) l Origin l l Goal l l Sets national standards for the healthcare industry since 1996. Addresses the security and privacy of electronic medical-related data, with regard to its use, storage, and exchange. Content l HIPAA Security Rule (enforced on April 21, 2005) More detail than Privacy Rule. l “procedures to guard data integrity, confidentiality and availability” applying to all individual health information in electronic form, including diskette, tape, CD, e-mail, file transfer, web or EDI. l
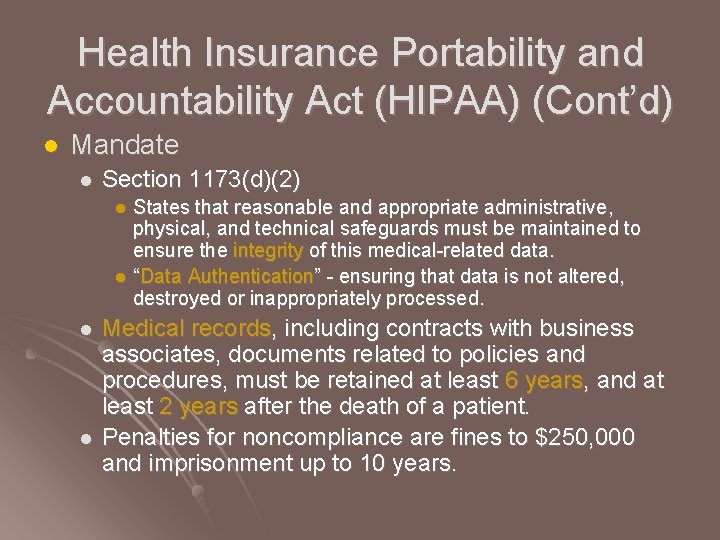
Health Insurance Portability and Accountability Act (HIPAA) (Cont’d) l Mandate l Section 1173(d)(2) States that reasonable and appropriate administrative, physical, and technical safeguards must be maintained to ensure the integrity of this medical-related data. l “Data Authentication” - ensuring that data is not altered, destroyed or inappropriately processed. l l l Medical records, including contracts with business associates, documents related to policies and procedures, must be retained at least 6 years, and at least 2 years after the death of a patient. Penalties for noncompliance are fines to $250, 000 and imprisonment up to 10 years.
Common Concepts and Issues Auditing, Retention, and Availability
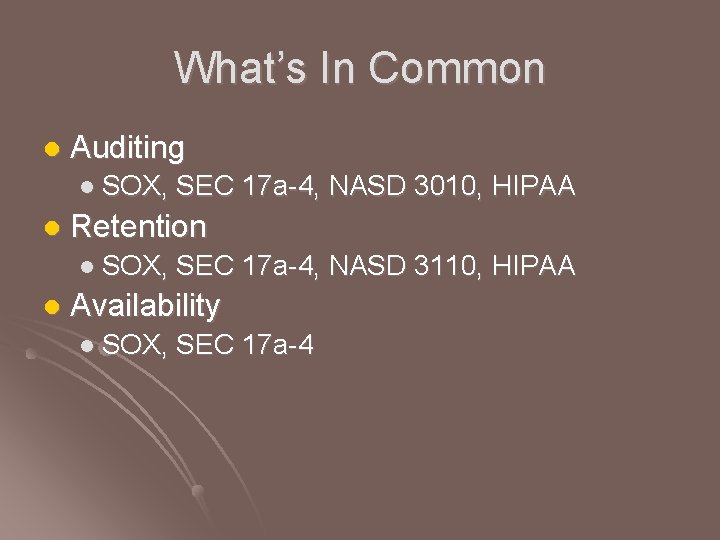
What’s In Common l Auditing l SOX, SEC 17 a-4, NASD 3010, HIPAA l Retention l SOX, SEC 17 a-4, NASD 3110, HIPAA l Availability l SOX, SEC 17 a-4
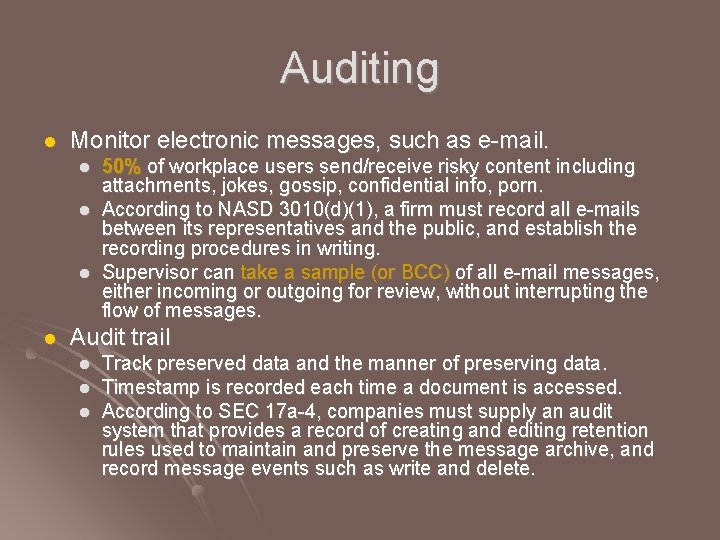
Auditing l Monitor electronic messages, such as e-mail. l l 50% of workplace users send/receive risky content including attachments, jokes, gossip, confidential info, porn. According to NASD 3010(d)(1), a firm must record all e-mails between its representatives and the public, and establish the recording procedures in writing. Supervisor can take a sample (or BCC) of all e-mail messages, either incoming or outgoing for review, without interrupting the flow of messages. Audit trail l Track preserved data and the manner of preserving data. Timestamp is recorded each time a document is accessed. According to SEC 17 a-4, companies must supply an audit system that provides a record of creating and editing retention rules used to maintain and preserve the message archive, and record message events such as write and delete.
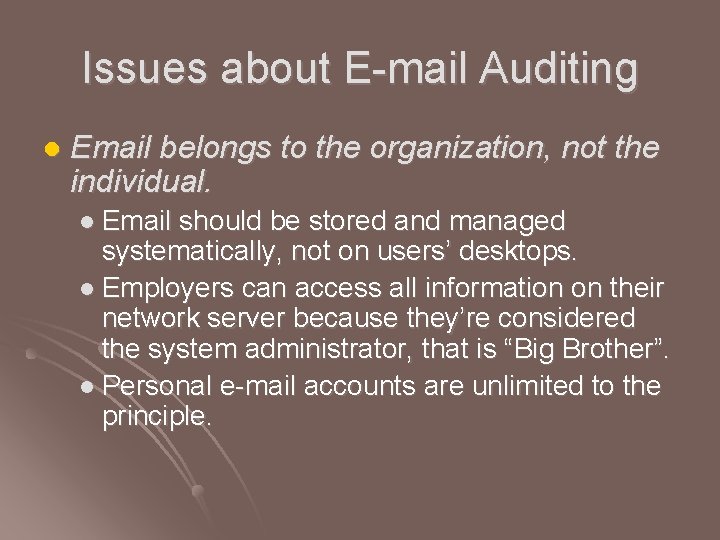
Issues about E-mail Auditing l Email belongs to the organization, not the individual. l Email should be stored and managed systematically, not on users’ desktops. l Employers can access all information on their network server because they’re considered the system administrator, that is “Big Brother”. l Personal e-mail accounts are unlimited to the principle.
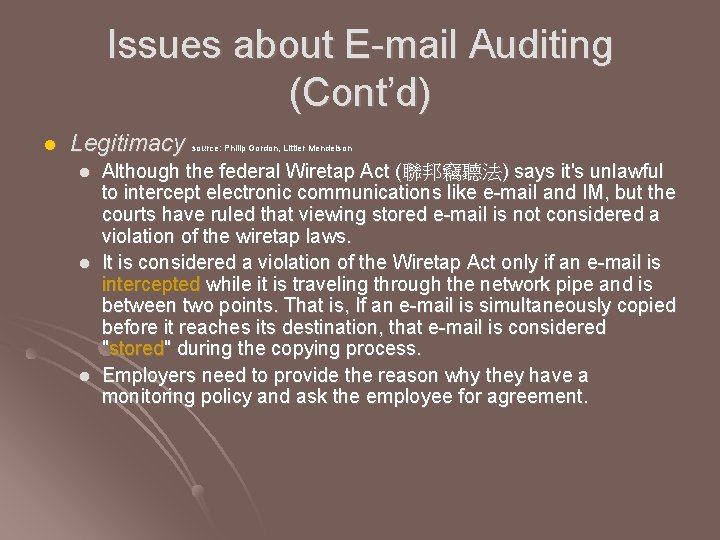
Issues about E-mail Auditing (Cont’d) l Legitimacy source: Philip Gordon, Littler Mendelson l l l Although the federal Wiretap Act (聯邦竊聽法) says it's unlawful to intercept electronic communications like e-mail and IM, but the courts have ruled that viewing stored e-mail is not considered a violation of the wiretap laws. It is considered a violation of the Wiretap Act only if an e-mail is intercepted while it is traveling through the network pipe and is between two points. That is, If an e-mail is simultaneously copied before it reaches its destination, that e-mail is considered "stored" during the copying process. Employers need to provide the reason why they have a monitoring policy and ask the employee for agreement.
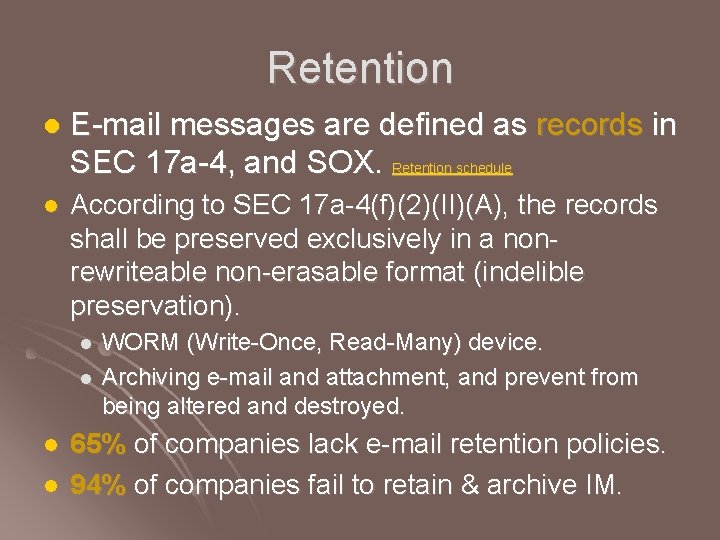
Retention l E-mail messages are defined as records in SEC 17 a-4, and SOX. Retention schedule l According to SEC 17 a-4(f)(2)(II)(A), the records shall be preserved exclusively in a nonrewriteable non-erasable format (indelible preservation). l l WORM (Write-Once, Read-Many) device. Archiving e-mail and attachment, and prevent from being altered and destroyed. 65% of companies lack e-mail retention policies. 94% of companies fail to retain & archive IM.
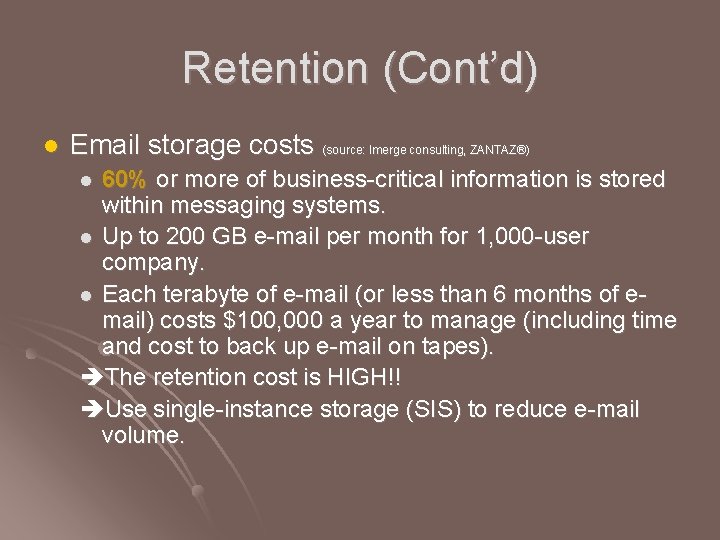
Retention (Cont’d) l Email storage costs (source: Imerge consulting, ZANTAZ®) 60% or more of business-critical information is stored within messaging systems. l Up to 200 GB e-mail per month for 1, 000 -user company. l Each terabyte of e-mail (or less than 6 months of email) costs $100, 000 a year to manage (including time and cost to back up e-mail on tapes). The retention cost is HIGH!! Use single-instance storage (SIS) to reduce e-mail volume. l
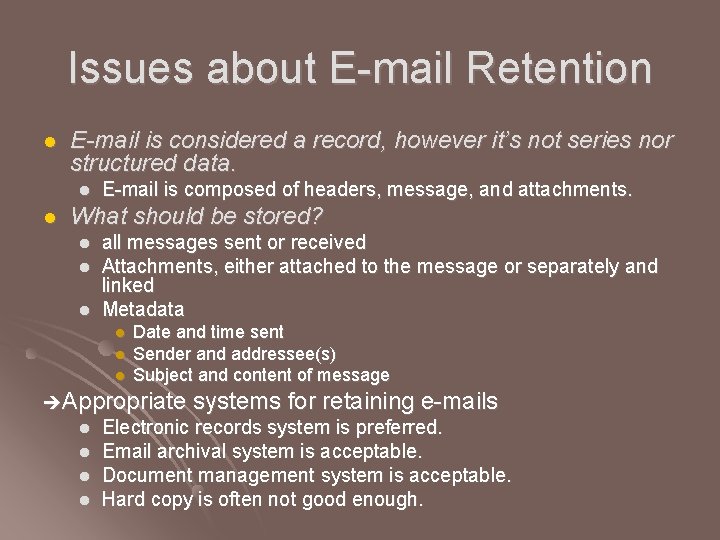
Issues about E-mail Retention l E-mail is considered a record, however it’s not series nor structured data. l l E-mail is composed of headers, message, and attachments. What should be stored? l l l all messages sent or received Attachments, either attached to the message or separately and linked Metadata l l l Date and time sent Sender and addressee(s) Subject and content of message Appropriate systems for retaining e-mails l l Electronic records system is preferred. Email archival system is acceptable. Document management system is acceptable. Hard copy is often not good enough.
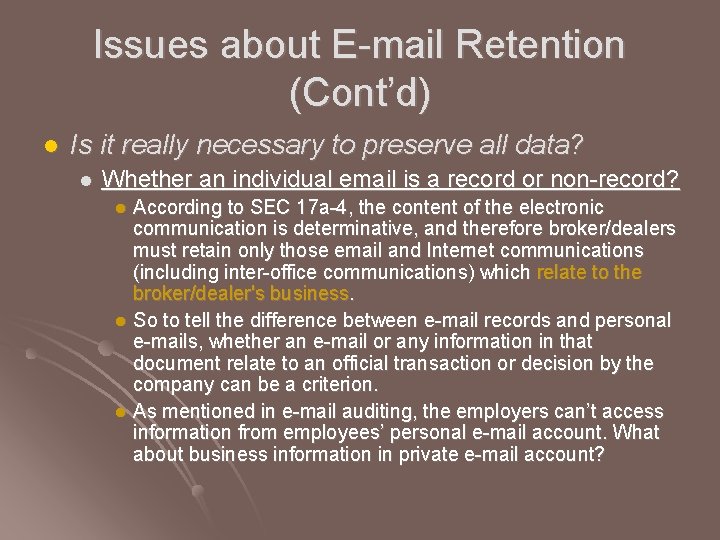
Issues about E-mail Retention (Cont’d) l Is it really necessary to preserve all data? l Whether an individual email is a record or non-record? According to SEC 17 a-4, the content of the electronic communication is determinative, and therefore broker/dealers must retain only those email and Internet communications (including inter-office communications) which relate to the broker/dealer's business. l So to tell the difference between e-mail records and personal e-mails, whether an e-mail or any information in that document relate to an official transaction or decision by the company can be a criterion. l As mentioned in e-mail auditing, the employers can’t access information from employees’ personal e-mail account. What about business information in private e-mail account? l
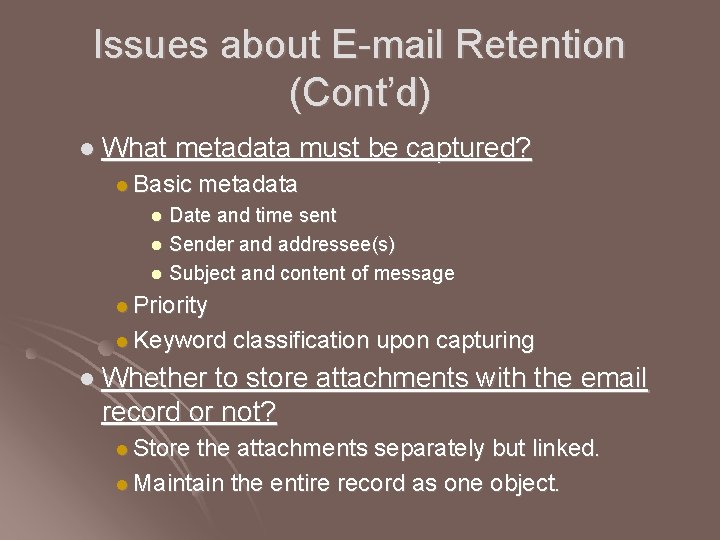
Issues about E-mail Retention (Cont’d) l What metadata must be captured? l Basic metadata Date and time sent l Sender and addressee(s) l Subject and content of message l l Priority l Keyword classification upon capturing l Whether to store attachments with the email record or not? l Store the attachments separately but linked. l Maintain the entire record as one object.
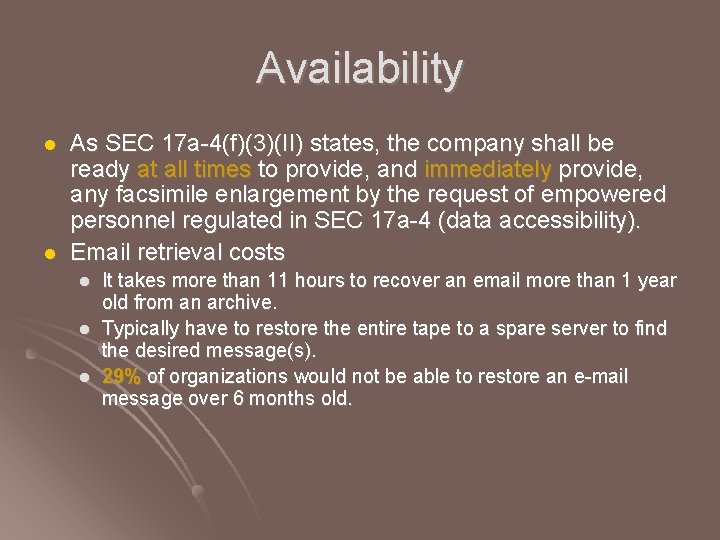
Availability l l As SEC 17 a-4(f)(3)(II) states, the company shall be ready at all times to provide, and immediately provide, any facsimile enlargement by the request of empowered personnel regulated in SEC 17 a-4 (data accessibility). Email retrieval costs l l l It takes more than 11 hours to recover an email more than 1 year old from an archive. Typically have to restore the entire tape to a spare server to find the desired message(s). 29% of organizations would not be able to restore an e-mail message over 6 months old.
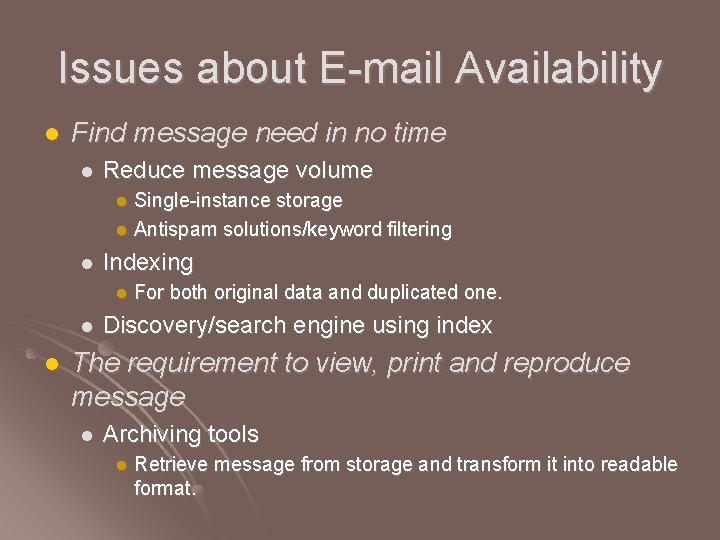
Issues about E-mail Availability l Find message need in no time l Reduce message volume Single-instance storage l Antispam solutions/keyword filtering l l Indexing l l l For both original data and duplicated one. Discovery/search engine using index The requirement to view, print and reproduce message l Archiving tools l Retrieve message from storage and transform it into readable format.
IT Applications of Common Issues Auditing, Retention, and Availability
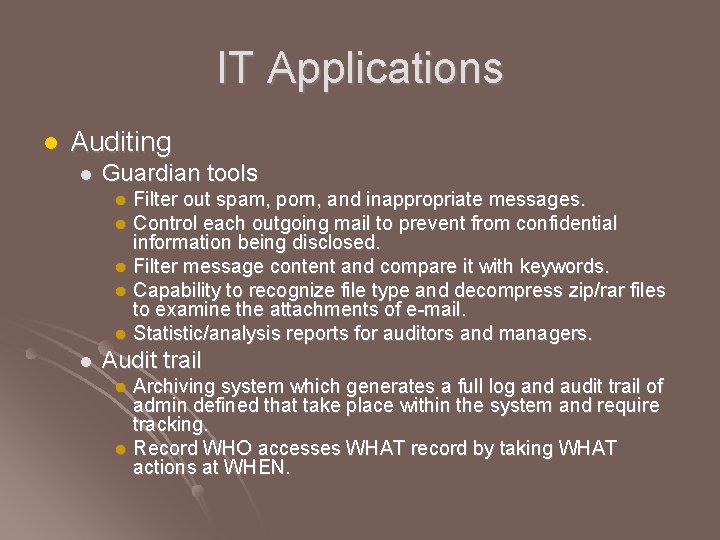
IT Applications l Auditing l Guardian tools Filter out spam, porn, and inappropriate messages. l Control each outgoing mail to prevent from confidential information being disclosed. l Filter message content and compare it with keywords. l Capability to recognize file type and decompress zip/rar files to examine the attachments of e-mail. l Statistic/analysis reports for auditors and managers. l l Audit trail Archiving system which generates a full log and audit trail of admin defined that take place within the system and require tracking. l Record WHO accesses WHAT record by taking WHAT actions at WHEN. l
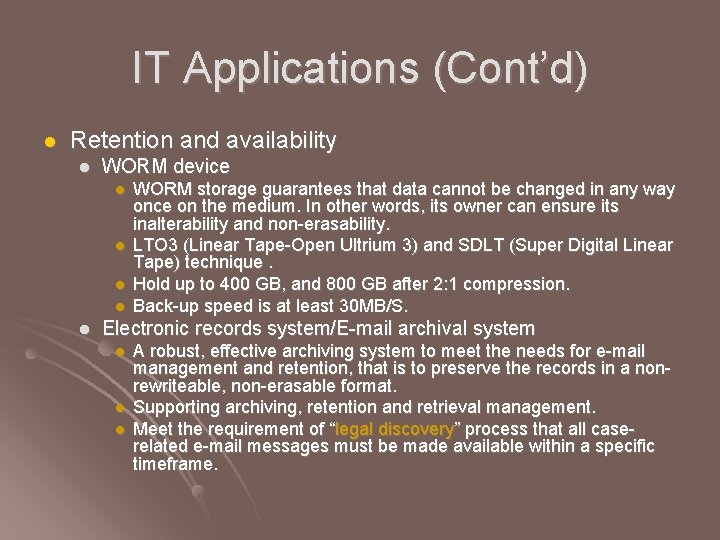
IT Applications (Cont’d) l Retention and availability l WORM device l l l WORM storage guarantees that data cannot be changed in any way once on the medium. In other words, its owner can ensure its inalterability and non-erasability. LTO 3 (Linear Tape-Open Ultrium 3) and SDLT (Super Digital Linear Tape) technique. Hold up to 400 GB, and 800 GB after 2: 1 compression. Back-up speed is at least 30 MB/S. Electronic records system/E-mail archival system l l l A robust, effective archiving system to meet the needs for e-mail management and retention, that is to preserve the records in a nonrewriteable, non-erasable format. Supporting archiving, retention and retrieval management. Meet the requirement of “legal discovery” process that all caserelated e-mail messages must be made available within a specific timeframe.

Regulations Compliance l. SOX, SEC 17 a-4 Compliance l. Archiving Software Features
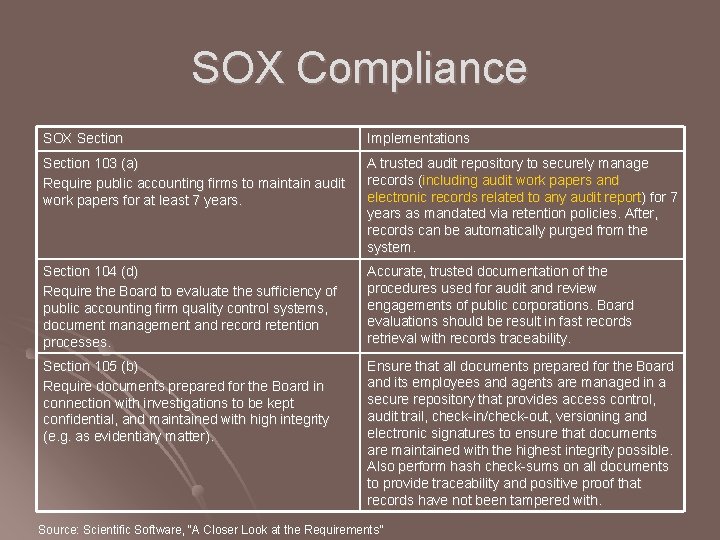
SOX Compliance SOX Section Implementations Section 103 (a) Require public accounting firms to maintain audit work papers for at least 7 years. A trusted audit repository to securely manage records (including audit work papers and electronic records related to any audit report) for 7 years as mandated via retention policies. After, records can be automatically purged from the system. Section 104 (d) Require the Board to evaluate the sufficiency of public accounting firm quality control systems, document management and record retention processes. Accurate, trusted documentation of the procedures used for audit and review engagements of public corporations. Board evaluations should be result in fast records retrieval with records traceability. Section 105 (b) Require documents prepared for the Board in connection with investigations to be kept confidential, and maintained with high integrity (e. g. as evidentiary matter). Ensure that all documents prepared for the Board and its employees and agents are managed in a secure repository that provides access control, audit trail, check-in/check-out, versioning and electronic signatures to ensure that documents are maintained with the highest integrity possible. Also perform hash check-sums on all documents to provide traceability and positive proof that records have not been tampered with. Source: Scientific Software, “A Closer Look at the Requirements”
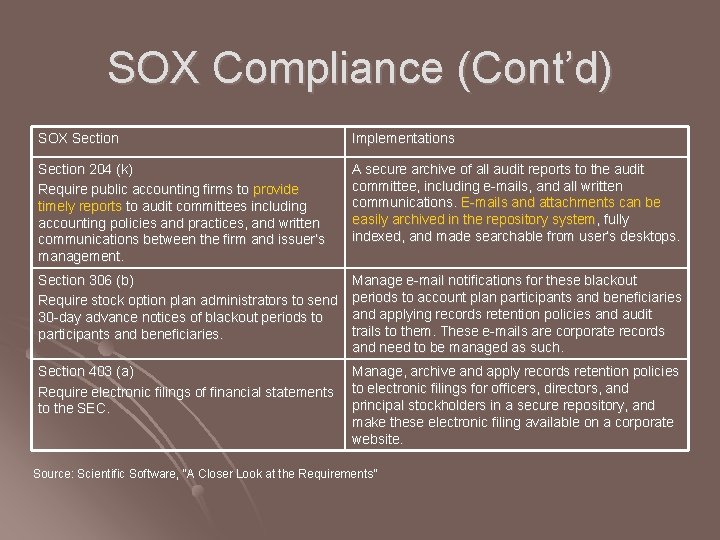
SOX Compliance (Cont’d) SOX Section Implementations Section 204 (k) Require public accounting firms to provide timely reports to audit committees including accounting policies and practices, and written communications between the firm and issuer’s management. A secure archive of all audit reports to the audit committee, including e-mails, and all written communications. E-mails and attachments can be easily archived in the repository system, fully indexed, and made searchable from user’s desktops. Section 306 (b) Require stock option plan administrators to send 30 -day advance notices of blackout periods to participants and beneficiaries. Manage e-mail notifications for these blackout periods to account plan participants and beneficiaries and applying records retention policies and audit trails to them. These e-mails are corporate records and need to be managed as such. Section 403 (a) Manage, archive and apply records retention policies Require electronic filings of financial statements to electronic filings for officers, directors, and principal stockholders in a secure repository, and to the SEC. make these electronic filing available on a corporate website. Source: Scientific Software, “A Closer Look at the Requirements”
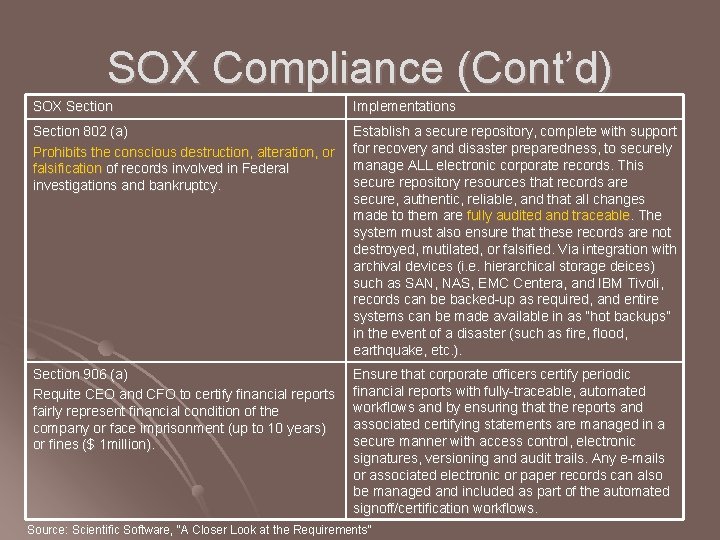
SOX Compliance (Cont’d) SOX Section Implementations Section 802 (a) Prohibits the conscious destruction, alteration, or falsification of records involved in Federal investigations and bankruptcy. Establish a secure repository, complete with support for recovery and disaster preparedness, to securely manage ALL electronic corporate records. This secure repository resources that records are secure, authentic, reliable, and that all changes made to them are fully audited and traceable. The system must also ensure that these records are not destroyed, mutilated, or falsified. Via integration with archival devices (i. e. hierarchical storage deices) such as SAN, NAS, EMC Centera, and IBM Tivoli, records can be backed-up as required, and entire systems can be made available in as “hot backups” in the event of a disaster (such as fire, flood, earthquake, etc. ). Section 906 (a) Requite CEO and CFO to certify financial reports fairly represent financial condition of the company or face imprisonment (up to 10 years) or fines ($ 1 million). Ensure that corporate officers certify periodic financial reports with fully-traceable, automated workflows and by ensuring that the reports and associated certifying statements are managed in a secure manner with access control, electronic signatures, versioning and audit trails. Any e-mails or associated electronic or paper records can also be managed and included as part of the automated signoff/certification workflows. Source: Scientific Software, “A Closer Look at the Requirements”
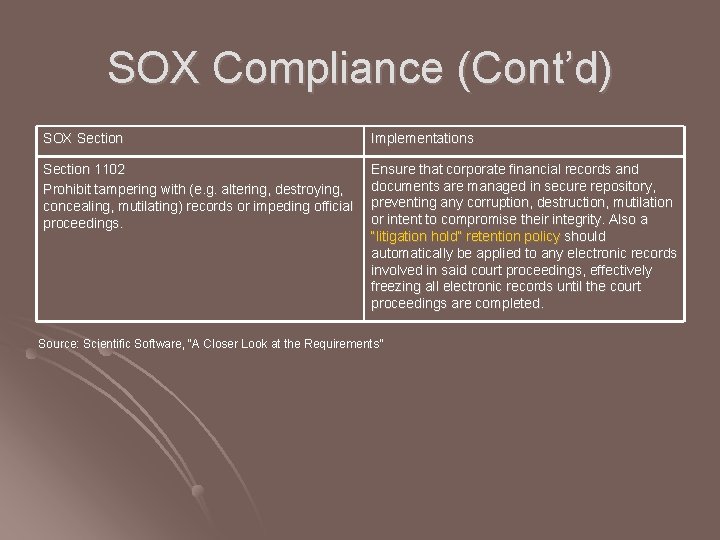
SOX Compliance (Cont’d) SOX Section Implementations Section 1102 Prohibit tampering with (e. g. altering, destroying, concealing, mutilating) records or impeding official proceedings. Ensure that corporate financial records and documents are managed in secure repository, preventing any corruption, destruction, mutilation or intent to compromise their integrity. Also a “litigation hold” retention policy should automatically be applied to any electronic records involved in said court proceedings, effectively freezing all electronic records until the court proceedings are completed. Source: Scientific Software, “A Closer Look at the Requirements”
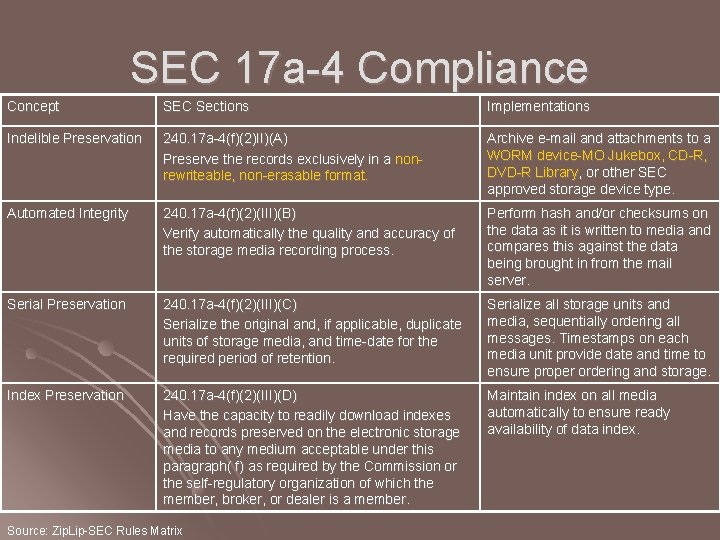
SEC 17 a-4 Compliance Concept SEC Sections Implementations Indelible Preservation 240. 17 a-4(f)(2)II)(A) Preserve the records exclusively in a nonrewriteable, non-erasable format. Archive e-mail and attachments to a WORM device-MO Jukebox, CD-R, DVD-R Library, or other SEC approved storage device type. Automated Integrity 240. 17 a-4(f)(2)(III)(B) Verify automatically the quality and accuracy of the storage media recording process. Perform hash and/or checksums on the data as it is written to media and compares this against the data being brought in from the mail server. Serial Preservation 240. 17 a-4(f)(2)(III)(C) Serialize the original and, if applicable, duplicate units of storage media, and time-date for the required period of retention. Serialize all storage units and media, sequentially ordering all messages. Timestamps on each media unit provide date and time to ensure proper ordering and storage. Index Preservation 240. 17 a-4(f)(2)(III)(D) Have the capacity to readily download indexes and records preserved on the electronic storage media to any medium acceptable under this paragraph( f) as required by the Commission or the self-regulatory organization of which the member, broker, or dealer is a member. Maintain index on all media automatically to ensure ready availability of data index. Source: Zip. Lip-SEC Rules Matrix
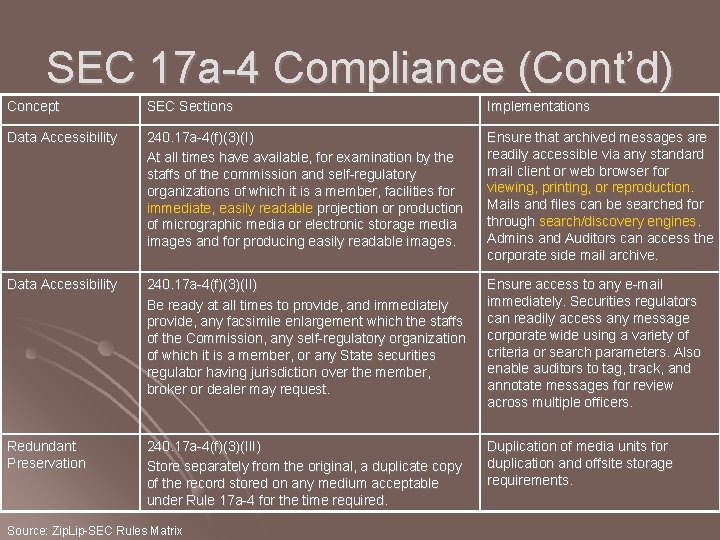
SEC 17 a-4 Compliance (Cont’d) Concept SEC Sections Implementations Data Accessibility 240. 17 a-4(f)(3)(I) At all times have available, for examination by the staffs of the commission and self-regulatory organizations of which it is a member, facilities for immediate, easily readable projection or production of micrographic media or electronic storage media images and for producing easily readable images. Ensure that archived messages are readily accessible via any standard mail client or web browser for viewing, printing, or reproduction. Mails and files can be searched for through search/discovery engines. Admins and Auditors can access the corporate side mail archive. Data Accessibility 240. 17 a-4(f)(3)(II) Be ready at all times to provide, and immediately provide, any facsimile enlargement which the staffs of the Commission, any self-regulatory organization of which it is a member, or any State securities regulator having jurisdiction over the member, broker or dealer may request. Ensure access to any e-mail immediately. Securities regulators can readily access any message corporate wide using a variety of criteria or search parameters. Also enable auditors to tag, track, and annotate messages for review across multiple officers. Redundant Preservation 240. 17 a-4(f)(3)(III) Store separately from the original, a duplicate copy of the record stored on any medium acceptable under Rule 17 a-4 for the time required. Duplication of media units for duplication and offsite storage requirements. Source: Zip. Lip-SEC Rules Matrix
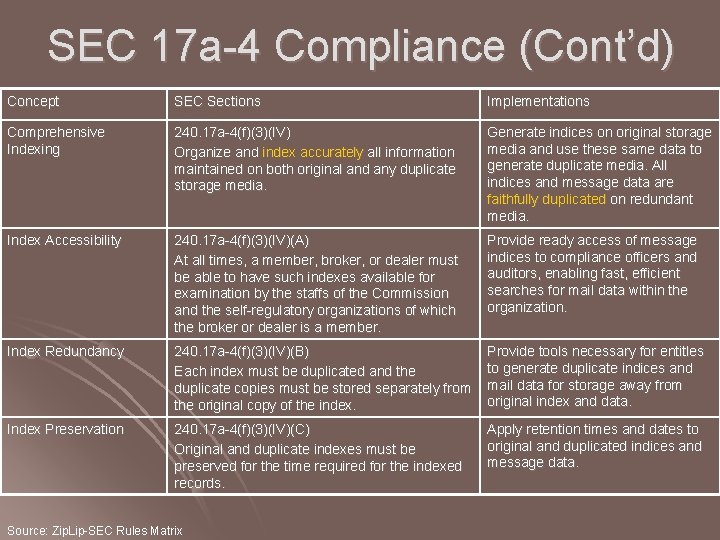
SEC 17 a-4 Compliance (Cont’d) Concept SEC Sections Implementations Comprehensive Indexing 240. 17 a-4(f)(3)(IV) Organize and index accurately all information maintained on both original and any duplicate storage media. Generate indices on original storage media and use these same data to generate duplicate media. All indices and message data are faithfully duplicated on redundant media. Index Accessibility 240. 17 a-4(f)(3)(IV)(A) At all times, a member, broker, or dealer must be able to have such indexes available for examination by the staffs of the Commission and the self-regulatory organizations of which the broker or dealer is a member. Provide ready access of message indices to compliance officers and auditors, enabling fast, efficient searches for mail data within the organization. Index Redundancy 240. 17 a-4(f)(3)(IV)(B) Each index must be duplicated and the duplicate copies must be stored separately from the original copy of the index. Provide tools necessary for entitles to generate duplicate indices and mail data for storage away from original index and data. Index Preservation 240. 17 a-4(f)(3)(IV)(C) Original and duplicate indexes must be preserved for the time required for the indexed records. Apply retention times and dates to original and duplicated indices and message data. Source: Zip. Lip-SEC Rules Matrix
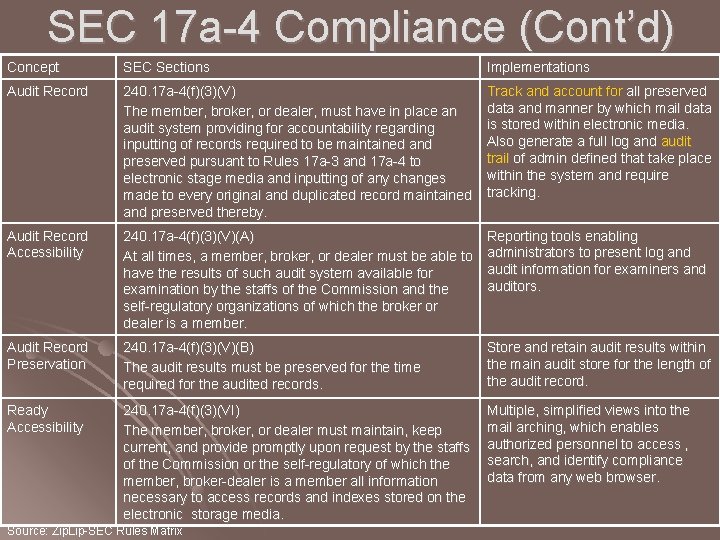
SEC 17 a-4 Compliance (Cont’d) Concept SEC Sections Implementations Audit Record 240. 17 a-4(f)(3)(V) The member, broker, or dealer, must have in place an audit system providing for accountability regarding inputting of records required to be maintained and preserved pursuant to Rules 17 a-3 and 17 a-4 to electronic stage media and inputting of any changes made to every original and duplicated record maintained and preserved thereby. Track and account for all preserved data and manner by which mail data is stored within electronic media. Also generate a full log and audit trail of admin defined that take place within the system and require tracking. Audit Record Accessibility 240. 17 a-4(f)(3)(V)(A) At all times, a member, broker, or dealer must be able to have the results of such audit system available for examination by the staffs of the Commission and the self-regulatory organizations of which the broker or dealer is a member. Reporting tools enabling administrators to present log and audit information for examiners and auditors. Audit Record Preservation 240. 17 a-4(f)(3)(V)(B) The audit results must be preserved for the time required for the audited records. Store and retain audit results within the main audit store for the length of the audit record. Ready Accessibility 240. 17 a-4(f)(3)(VI) The member, broker, or dealer must maintain, keep current, and provide promptly upon request by the staffs of the Commission or the self-regulatory of which the member, broker-dealer is a member all information necessary to access records and indexes stored on the electronic storage media. Multiple, simplified views into the mail arching, which enables authorized personnel to access , search, and identify compliance data from any web browser. Source: Zip. Lip-SEC Rules Matrix
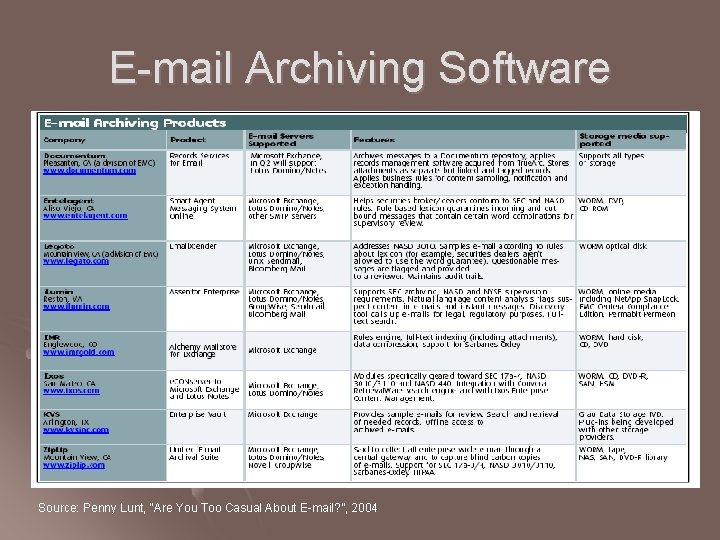
E-mail Archiving Software Source: Penny Lunt, “Are You Too Casual About E-mail? ”, 2004
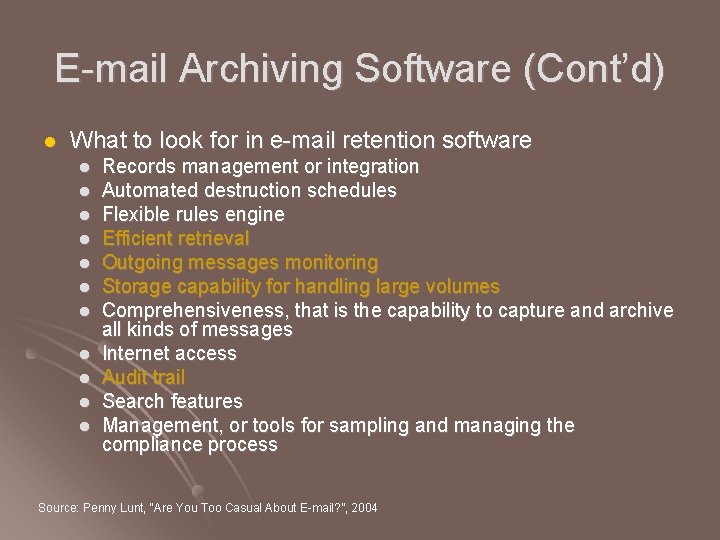
E-mail Archiving Software (Cont’d) l What to look for in e-mail retention software l l l Records management or integration Automated destruction schedules Flexible rules engine Efficient retrieval Outgoing messages monitoring Storage capability for handling large volumes Comprehensiveness, that is the capability to capture and archive all kinds of messages Internet access Audit trail Search features Management, or tools for sampling and managing the compliance process Source: Penny Lunt, “Are You Too Casual About E-mail? ”, 2004
Conclusion
Conclusion l Auditing l Guardian tools l l Audit trail l l Done by recording information of access to all preserved data. Retention & availability l Only 60% of U. S. companies now use software to monitor incoming and outgoing external e-mail, and only 27% track internal e-mail between employees according to the e. Policy. AMA survey in 2004. Done by record archiving system with security assurance and regulations compliance function.
Conclusion (Cont’d) l l Current IT is capable for complying with enacted regulations. The question is how to choose appropriate tools. Set up a good e-mail auditing and management policy is key to success. Employee education is also important. l l 46% of companies offer employees NO e-mail policy training. Retention of voice, video and other unstructured data may be required in the future.
Reference l l l l “Zip. Lip: SEC Rules Overview” “Zip. Lip-SEC Rules Matrix” “Zip. Lip-NASD 3010 Rules” “Email Management in the Workplace-a Simple Guide For Employers”, Waterford Technologies. November 2003. , “A Guide to the Sarbanes-Oxley Act and Email Security”, Voltage Security, Inc. and Cipher. Trust. November 2004. Jesse Wilkins, “Email: the Case for Active Management”, Imerge Consulting. Semptember 2004. Steve Gray, “Compliance and Content Management Solution”, Sun Microsystems Inc. 2004. “Data Integrity and Data Retention Regulations”, Advanced Intelligent Tape. “Email Archiving, Retrieval and Analysis for the Risk Manager”, aftermail. 2004. Penny Lunt, “Are You Too Casual About E-mail? ”, Feb. 2004. “Digital Archiving Strategies for Regulatory Compliance in Financial Service”, Archivas, Inc. “Email Archiving – Analyzing the Return on Investment”, ZANTAZ®. Jon Busby, “Sarbanes-Oxley: Compliance with Corporate Governance and Industry Legislation with Protocom Seure. Login®”, Protocom Development Systems. 2005.
Reference (Cont’d) l l l “Sarbanes-Oxley Solutions”, IBM Global Services. http: //www. ibm. com/services/sox (EN); http: //www-8. ibm. com/services/bcs/tw/sox. html (CH) Dawn Kawamoto, “Mind those IMs--your cubicle's walls have eyes”, CNET News. com. October 2004. http: //news. zdnet. com/2100 -1040_22 -5423220. html Dawn Kawamoto撰.唐慧文譯,辦公室長眼 傳簡訊全都露 。2004/11/03。 http: //taiwan. cnet. com/enterprise/technology/0, 2000062852, 20093794, 00. htm Data Protection Services, LLC. http: //www. dataprotection. com/regulatory-compliance/ “Non-Compliant Impact“, Security Forensics, Inc. 2004. http: //www. securityforensics. com/knowledgebase. htm 潘景華,”美國證券市場稽核制度之探討(上)”。 http: //w 3. tse. com. tw/plan/essay/474/Pan. htm 張智鴻,“ 184 -專題報導-LTO-3“,i. Thome採購情報。2005 -04 -04。 http: //shoppingguide. ithome. com. tw/special 2005 -04 -04 -001. html Ron Anderson, “Message Archiving is a Must”, Compliance Pipeline. 2005. http: //www. compliancepipeline. com/show. Article. jhtml? article. Id=162800283&pgno=5 “A Closer Look at the Requirements”, Scientific Software. http: //www. scisw. com/solutions_new/sox/index 2. htm ZIPLip, Inc. http: //www. ziplip. com/solutions/compliance. html Tony Redmond, “Does Single-Instance Storage matter Anymore? ”, Windows IT Pro. September 2001. http: //www. windowsitpro. com/Article. ID/21564. html? Ad=1, http: //www. windowsitpro. com/Windows/Article. ID/21564/pg/2/2. html
Thanks for your listening
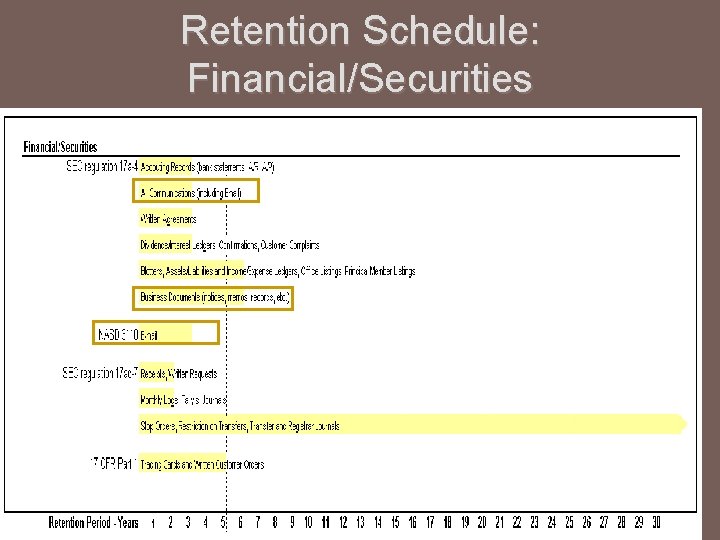
Retention Schedule: Financial/Securities
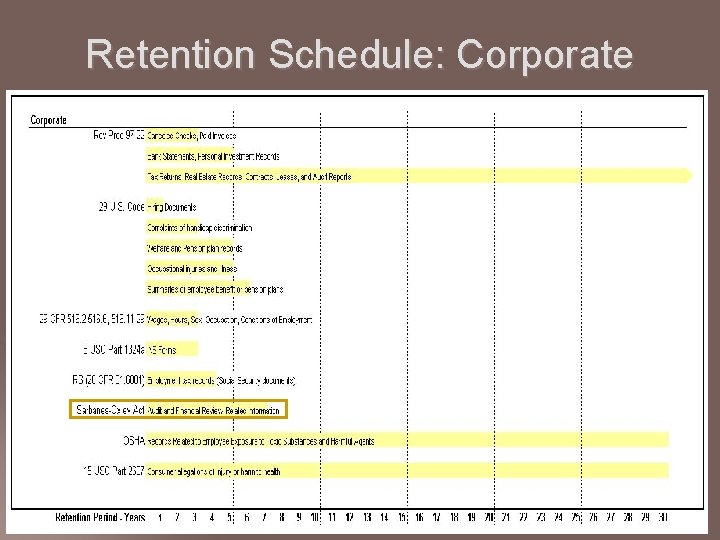
Retention Schedule: Corporate
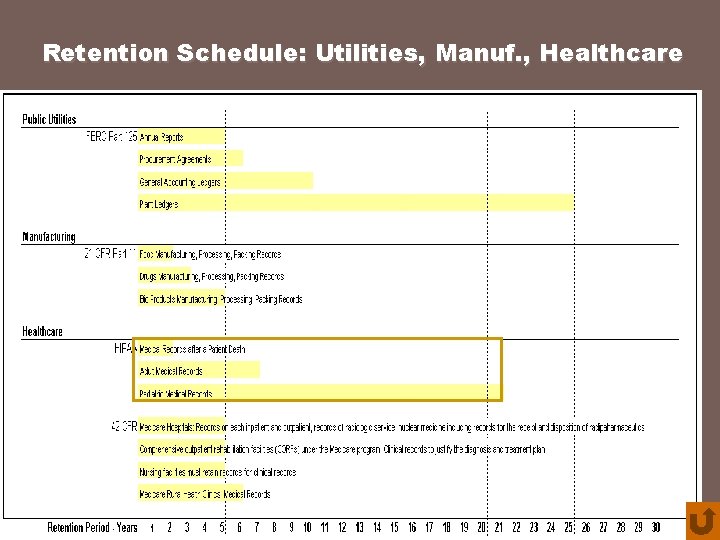
Retention Schedule: Utilities, Manuf. , Healthcare
- Slides: 54