The SPHINCS Signature Framework Andreas Hlsing Outline 1

![Stateless hash-based signatures [NY 89, Gol 87, Gol 04] OTS • OTS OTS OTS Stateless hash-based signatures [NY 89, Gol 87, Gol 04] OTS • OTS OTS OTS](https://slidetodoc.com/presentation_image_h/12df90a34701d483d42f7a91e1912375/image-27.jpg)
![SPHINCS [BHH+15] • Select index pseudorandomly • Use a few-time signature key-pair on leaves SPHINCS [BHH+15] • Select index pseudorandomly • Use a few-time signature key-pair on leaves](https://slidetodoc.com/presentation_image_h/12df90a34701d483d42f7a91e1912375/image-28.jpg)
- Slides: 53
+ The SPHINCS Signature Framework Andreas Hülsing
Outline 1. 2. 3. 4. 5. 6. Hash functions in a post-quantum world Stateful hash-based signatures SPHINCS+ Performance Applications 20. 04. 2020 https: //sphincs. org/ 2
Hash functions in a post-quantum world 20. 04. 2020 https: //sphincs. org/ 3
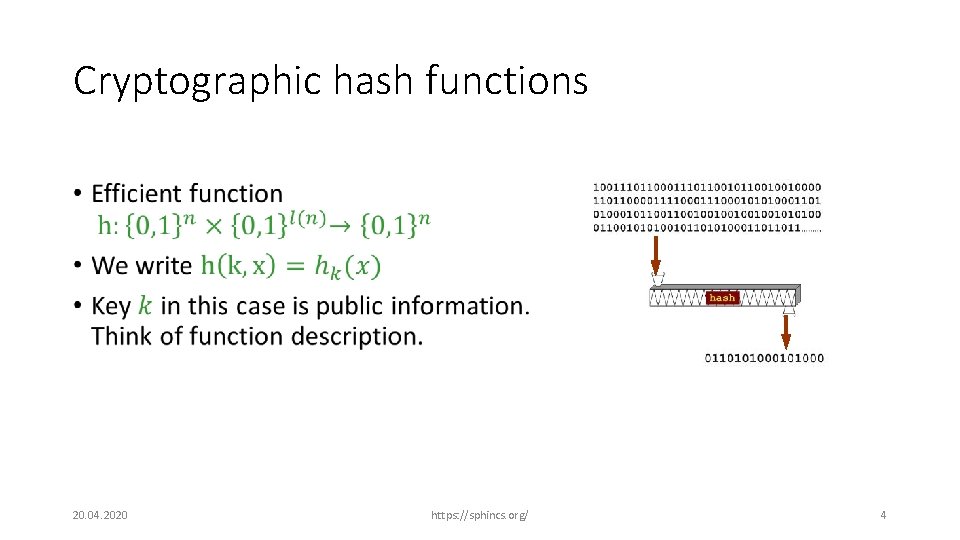
Cryptographic hash functions • 20. 04. 2020 https: //sphincs. org/ 4
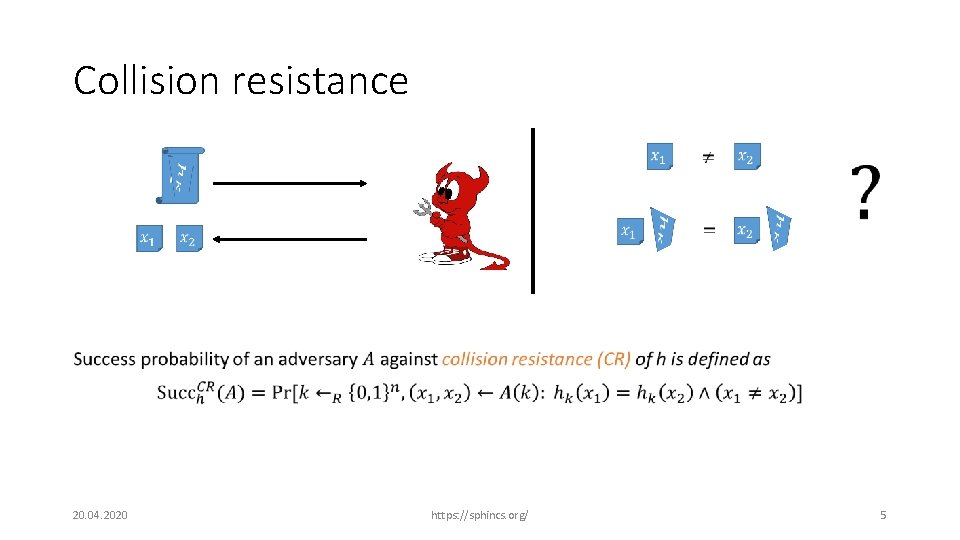
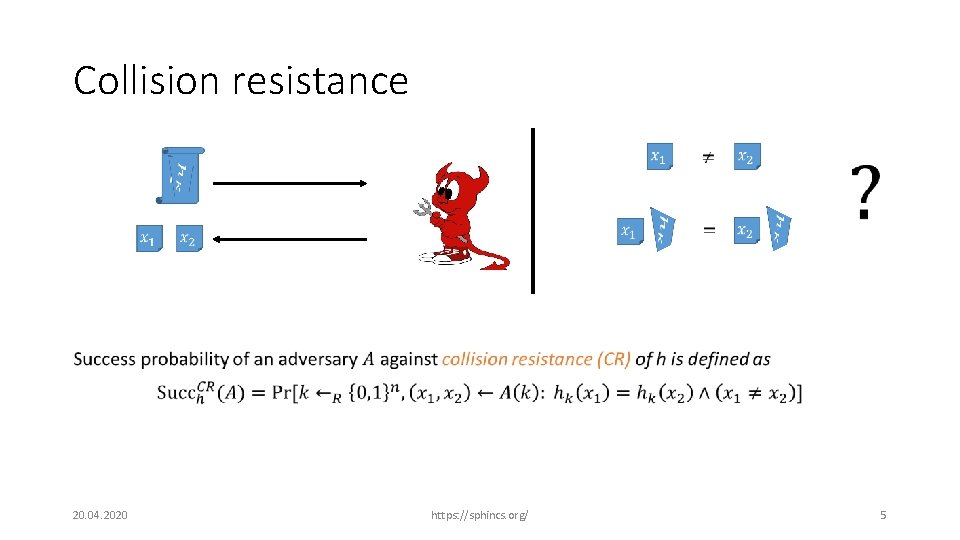
Collision resistance https: //sphincs. org/ 20. 04. 2020 • 5
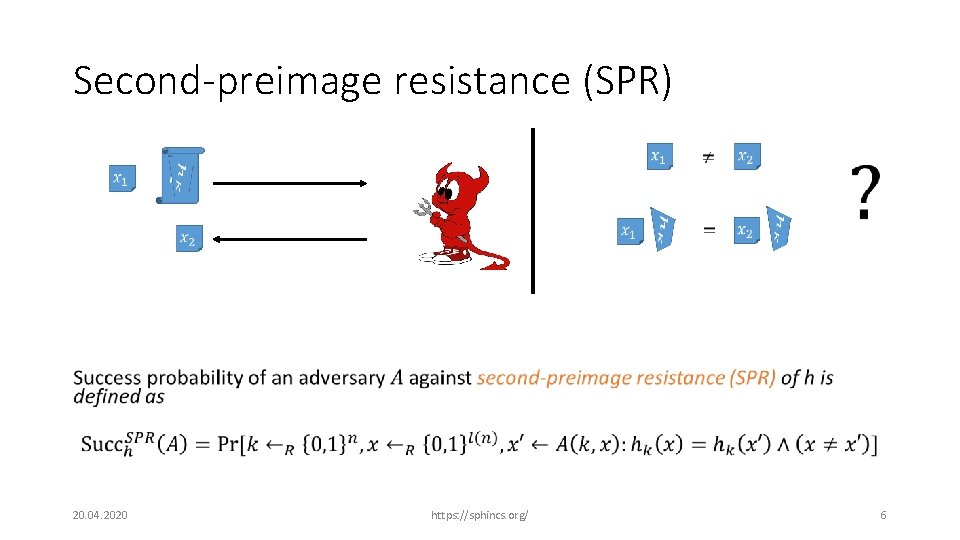
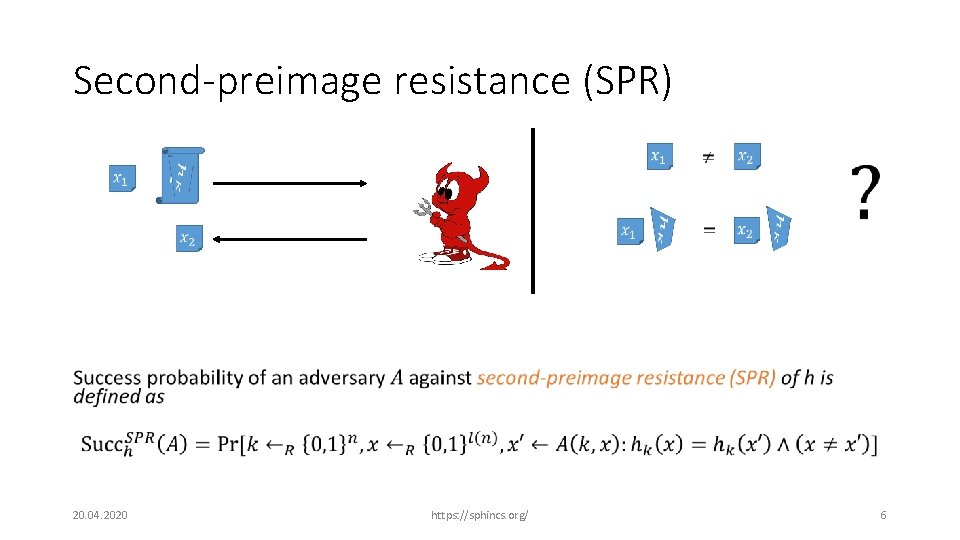
Second-preimage resistance (SPR) https: //sphincs. org/ 20. 04. 2020 • 6
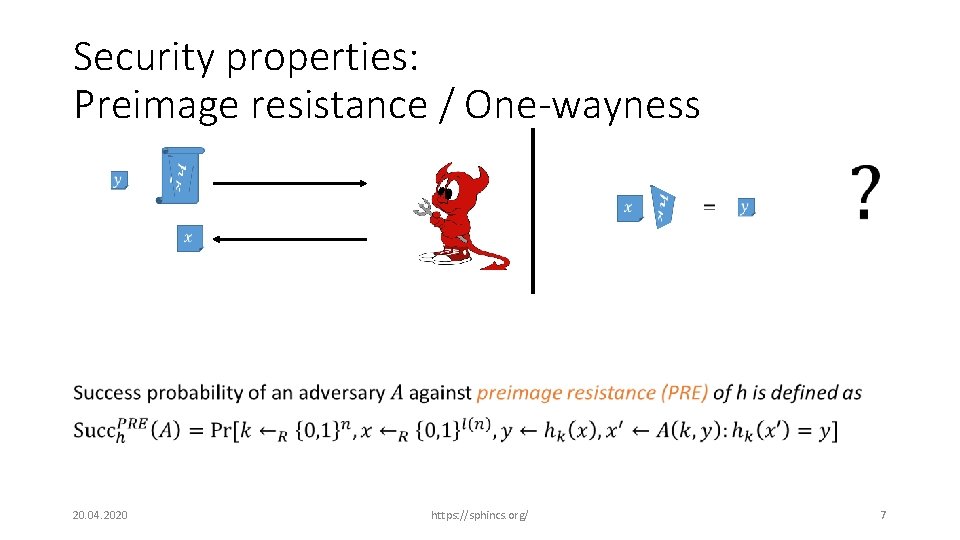
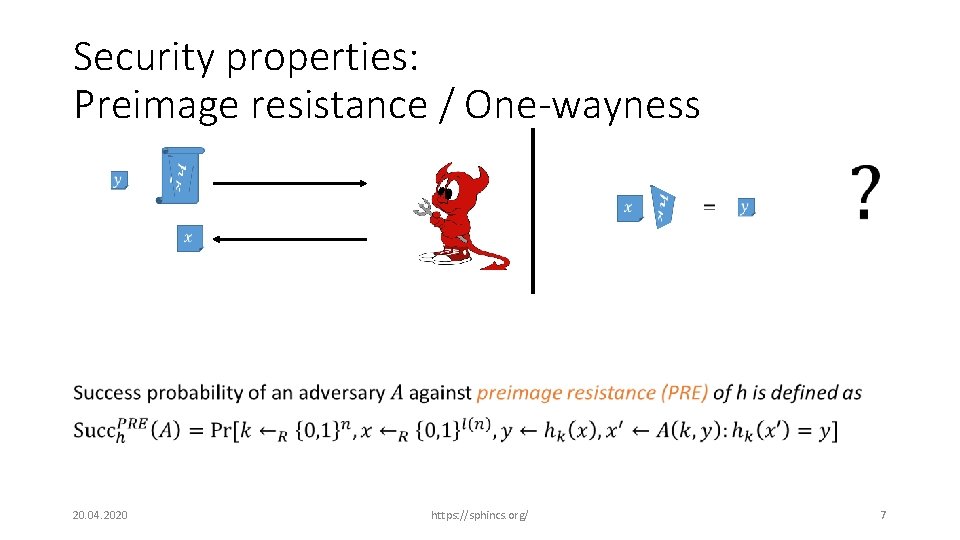
Security properties: Preimage resistance / One-wayness • 20. 04. 2020 https: //sphincs. org/ 7
What do we know about postquantum security of hash functions? 20. 04. 2020 https: //sphincs. org/ 8
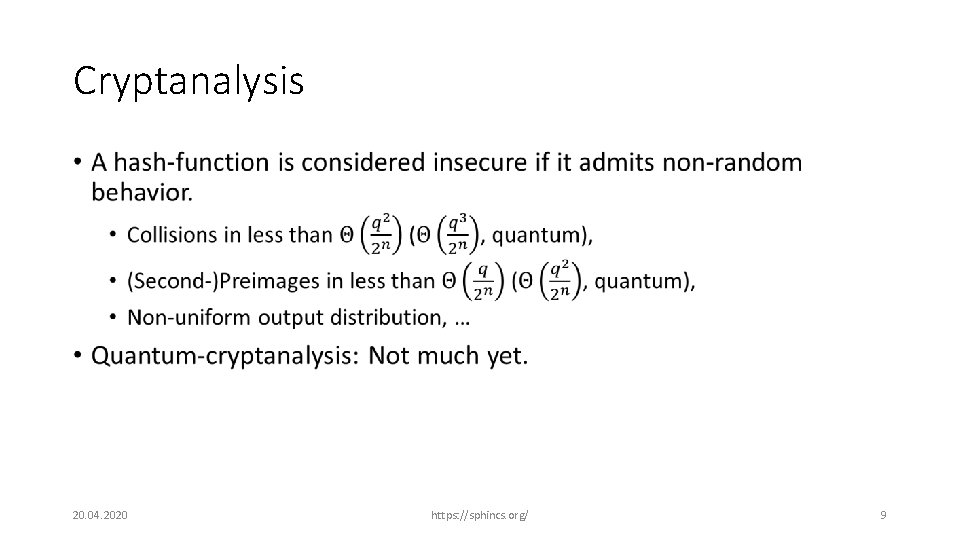
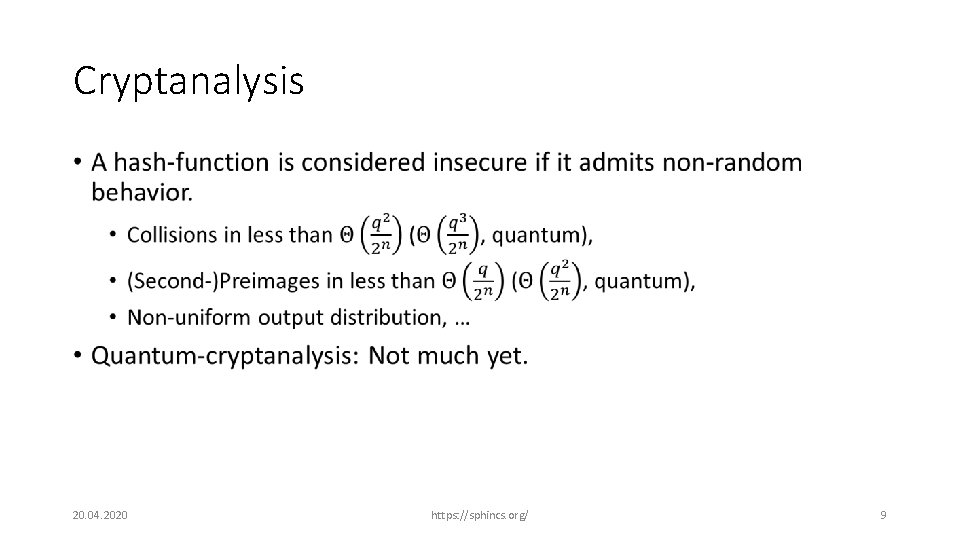
Cryptanalysis • 20. 04. 2020 https: //sphincs. org/ 9
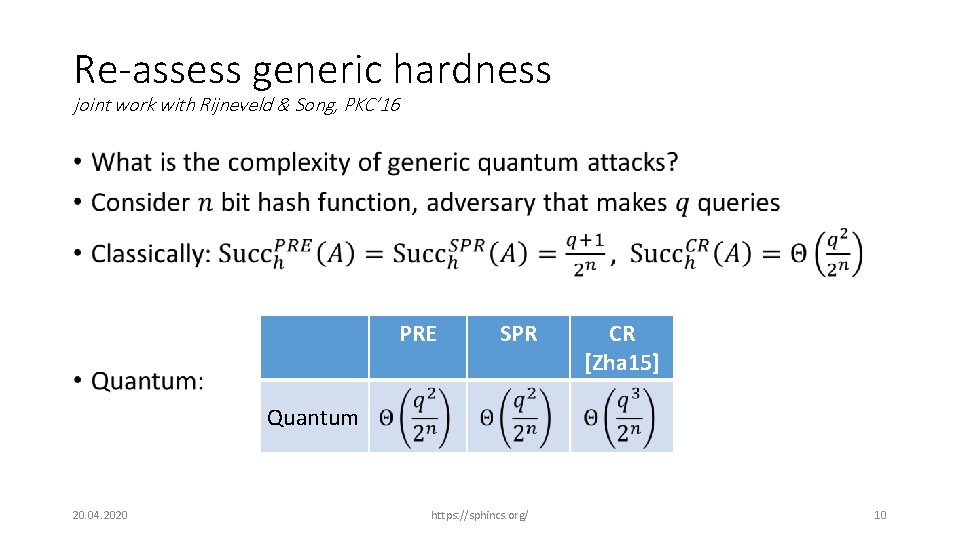
Re-assess generic hardness joint work with Rijneveld & Song, PKC’ 16 • PRE SPR CR [Zha 15] Quantum 20. 04. 2020 https: //sphincs. org/ 10
What about actual hash functions? 20. 04. 2020 https: //sphincs. org/ 11
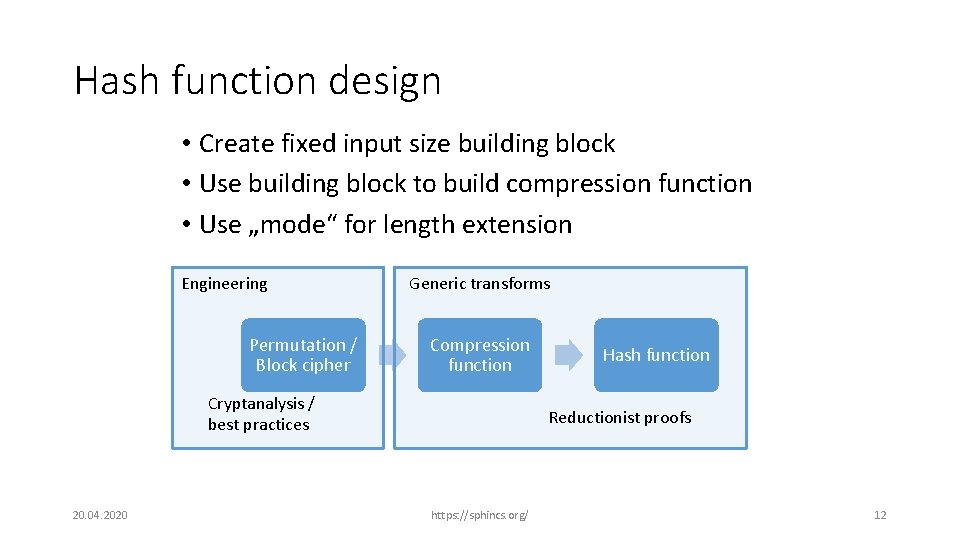
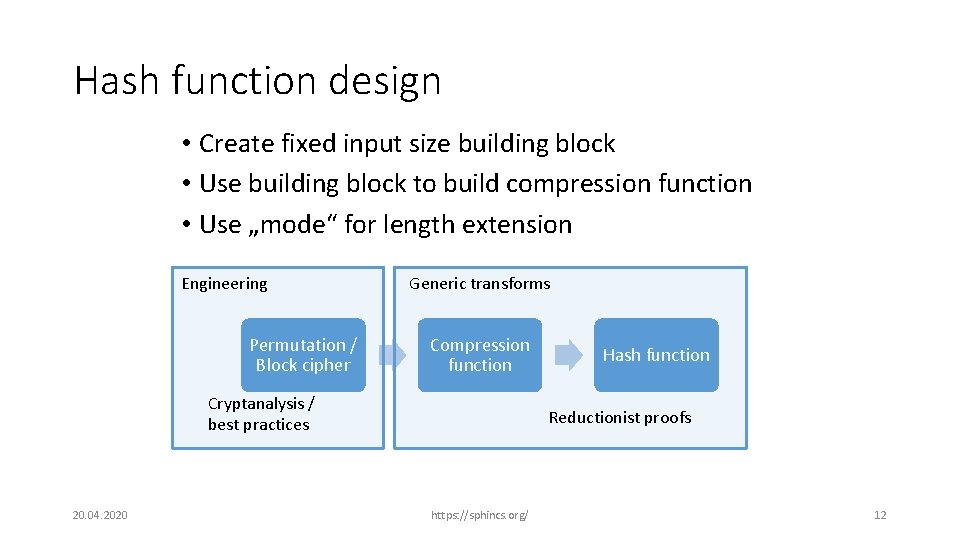
Hash function design • Create fixed input size building block • Use building block to build compression function • Use „mode“ for length extension Engineering Permutation / Block cipher Generic transforms Compression function Cryptanalysis / best practices 20. 04. 2020 Hash function Reductionist proofs https: //sphincs. org/ 12
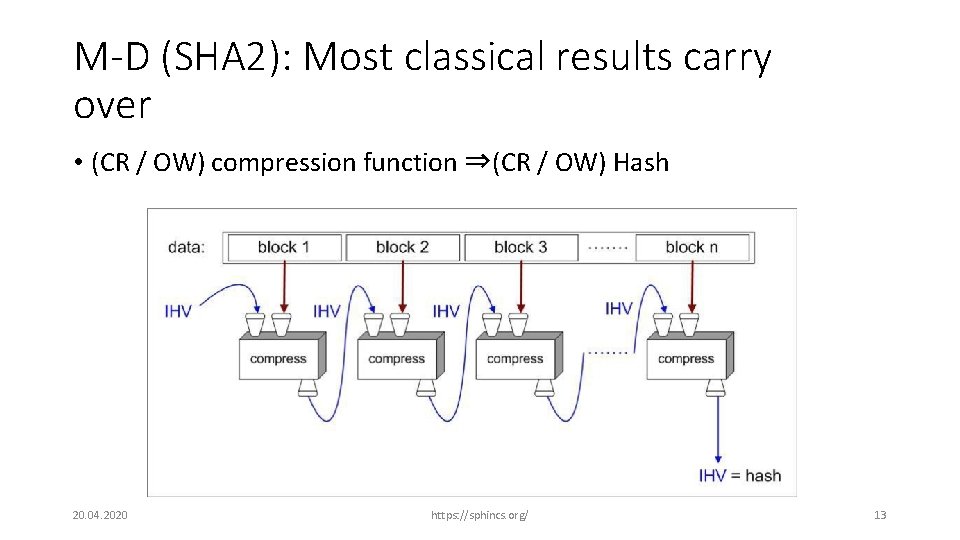
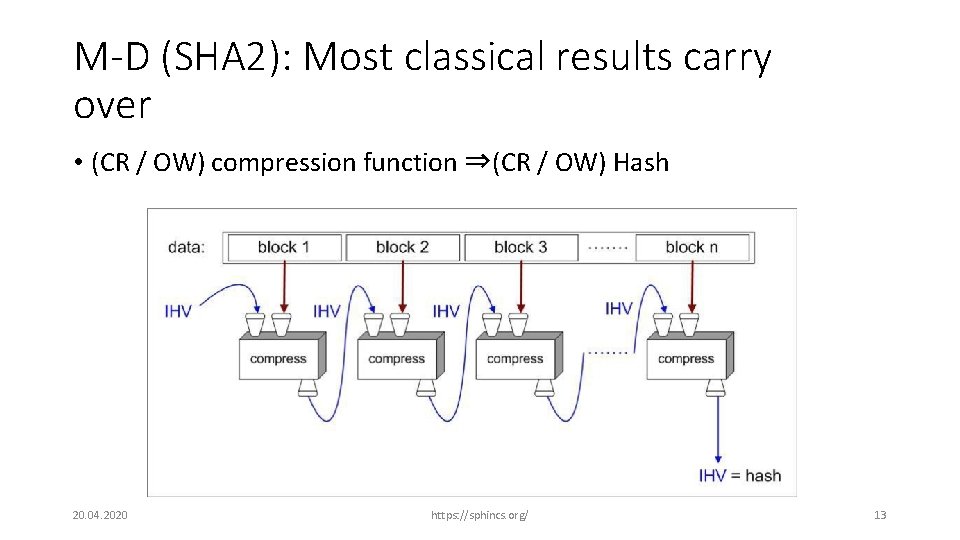
M-D (SHA 2): Most classical results carry over • (CR / OW) compression function ⇒(CR / OW) Hash 20. 04. 2020 https: //sphincs. org/ 13
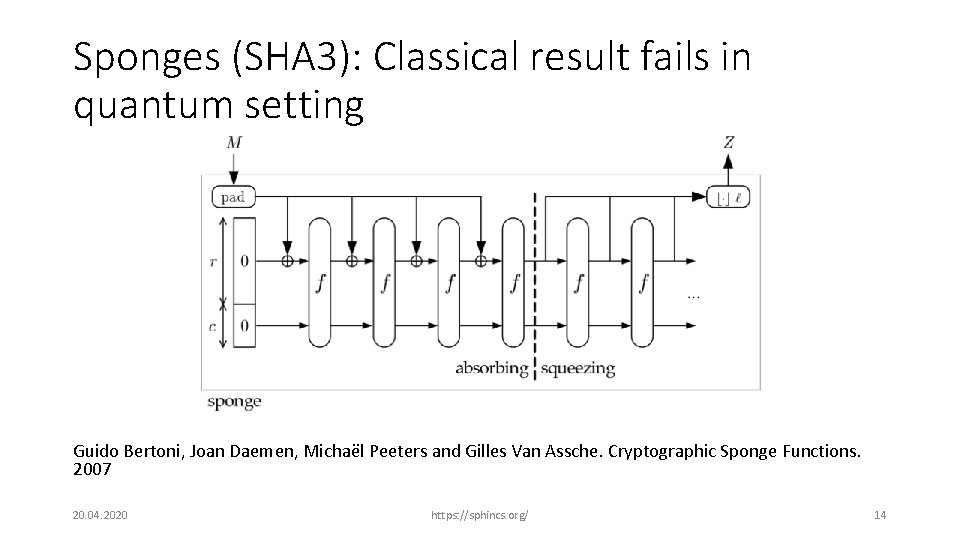
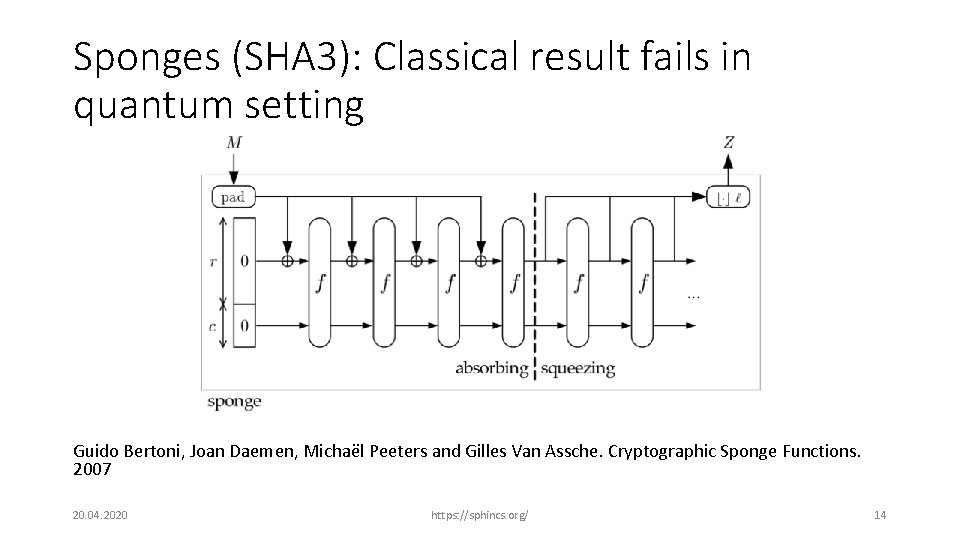
Sponges (SHA 3): Classical result fails in quantum setting Guido Bertoni, Joan Daemen, Michaël Peeters and Gilles Van Assche. Cryptographic Sponge Functions. 2007 20. 04. 2020 https: //sphincs. org/ 14
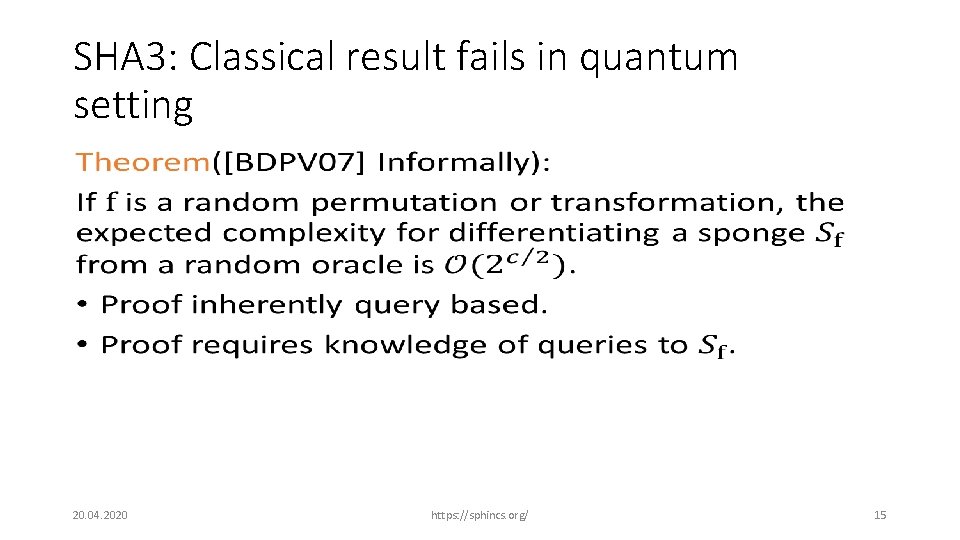
SHA 3: Classical result fails in quantum setting • 20. 04. 2020 https: //sphincs. org/ 15
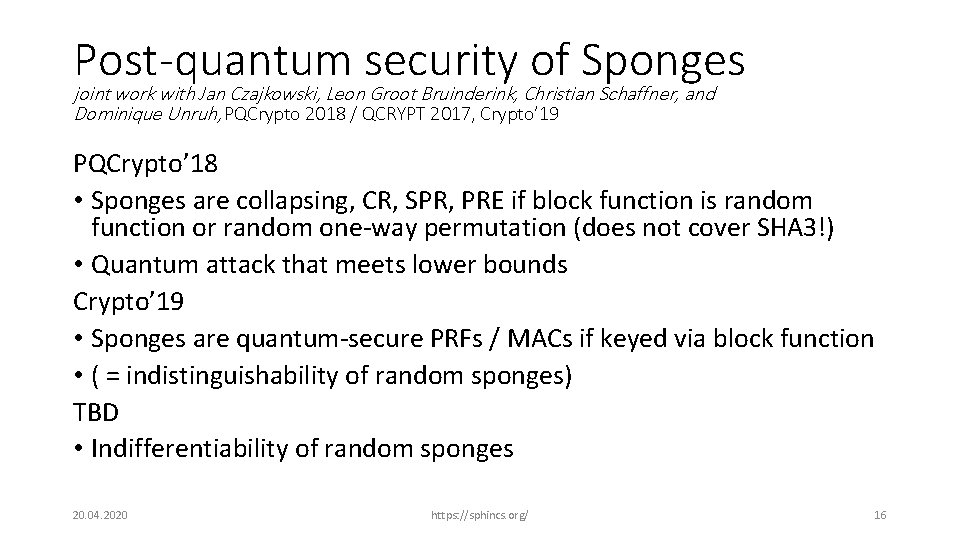
Post-quantum security of Sponges joint work with Jan Czajkowski, Leon Groot Bruinderink, Christian Schaffner, and Dominique Unruh, PQCrypto 2018 / QCRYPT 2017, Crypto’ 19 PQCrypto’ 18 • Sponges are collapsing, CR, SPR, PRE if block function is random function or random one-way permutation (does not cover SHA 3!) • Quantum attack that meets lower bounds Crypto’ 19 • Sponges are quantum-secure PRFs / MACs if keyed via block function • ( = indistinguishability of random sponges) TBD • Indifferentiability of random sponges 20. 04. 2020 https: //sphincs. org/ 16
(Stateful) hash-based signatures 20. 04. 2020 https: //sphincs. org/ 17
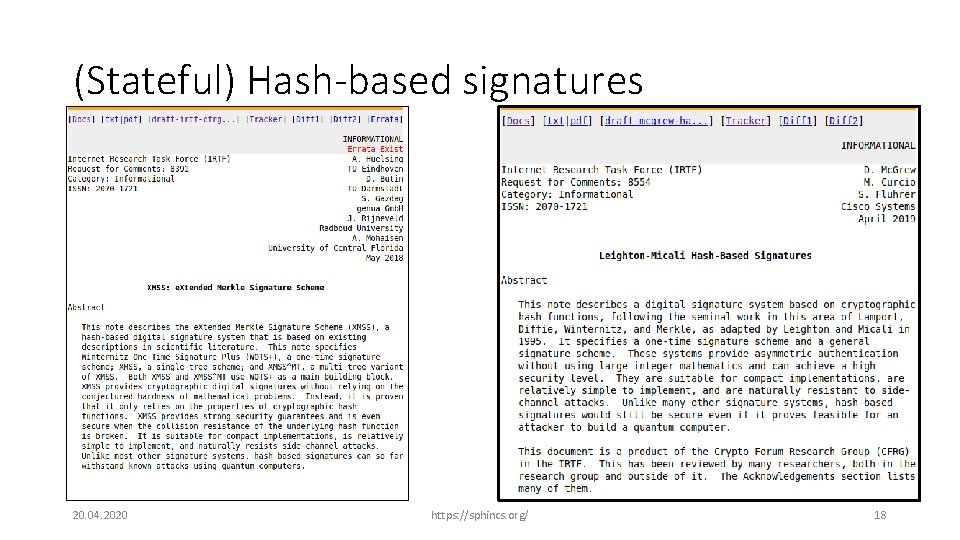
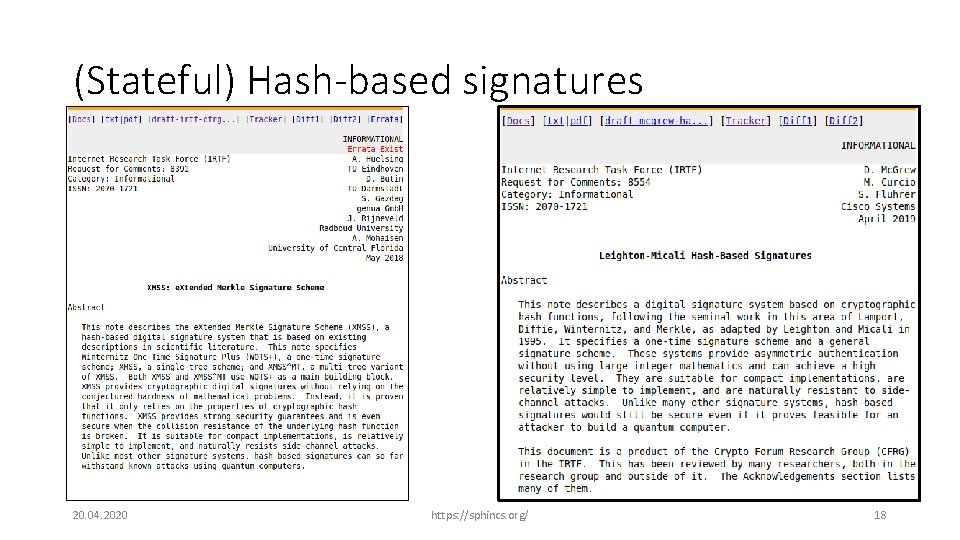
(Stateful) Hash-based signatures 20. 04. 2020 https: //sphincs. org/ 18
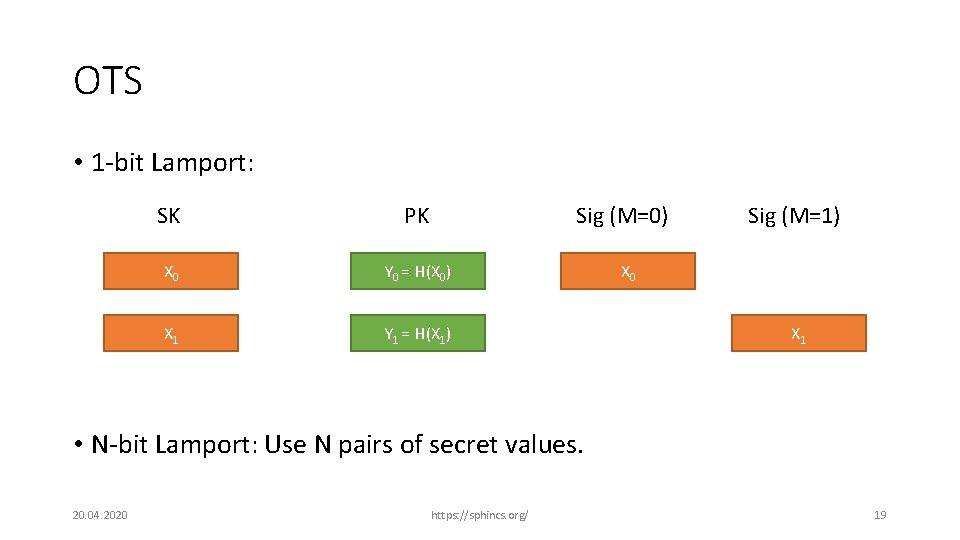
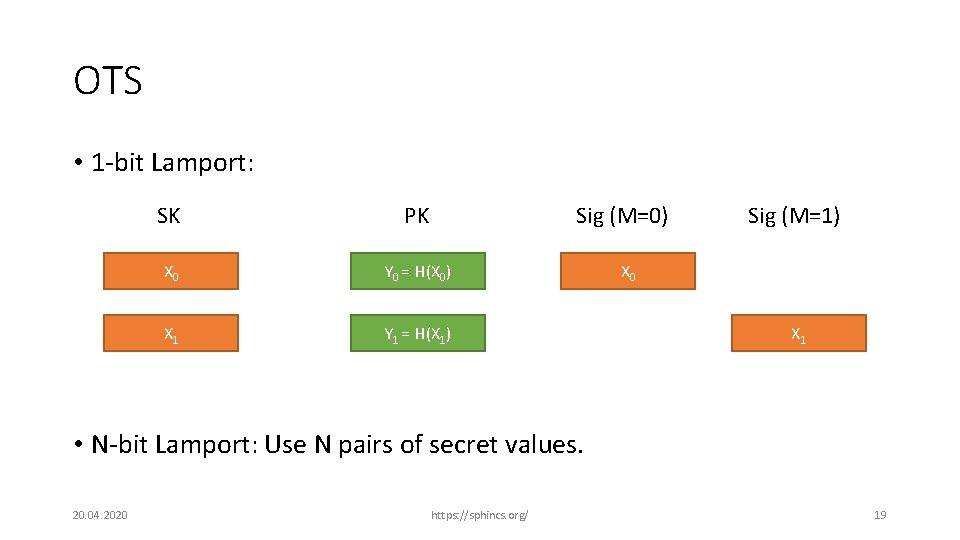
OTS • 1 -bit Lamport: Sig (M=0) SK PK X 0 Y 0 = H(X 0) X 1 Y 1 = H(X 1) Sig (M=1) X 0 X 1 • N-bit Lamport: Use N pairs of secret values. 20. 04. 2020 https: //sphincs. org/ 19
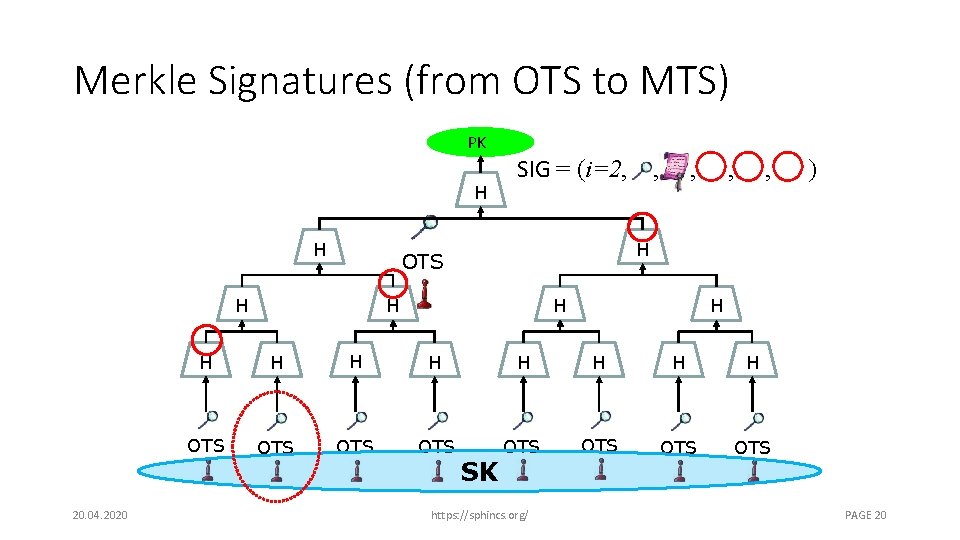
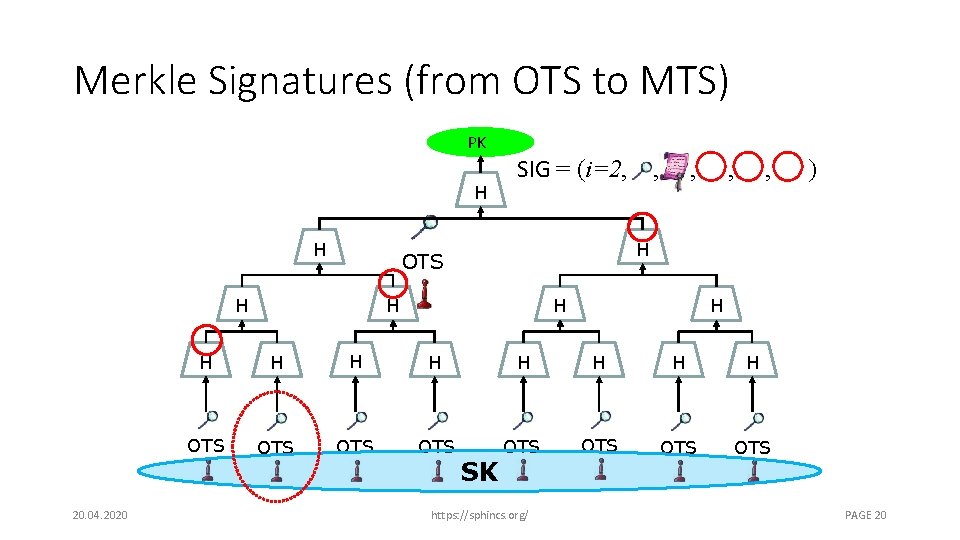
Merkle Signatures (from OTS to MTS) PK H H , , , ) H OTS H 20. 04. 2020 SIG = (i=2, , H H H OTS OTS SK https: //sphincs. org/ PAGE 20
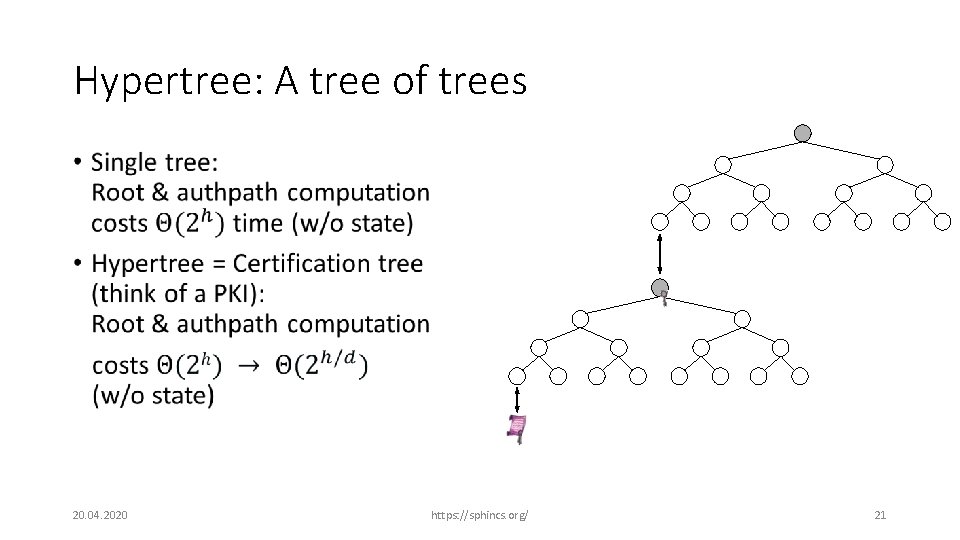
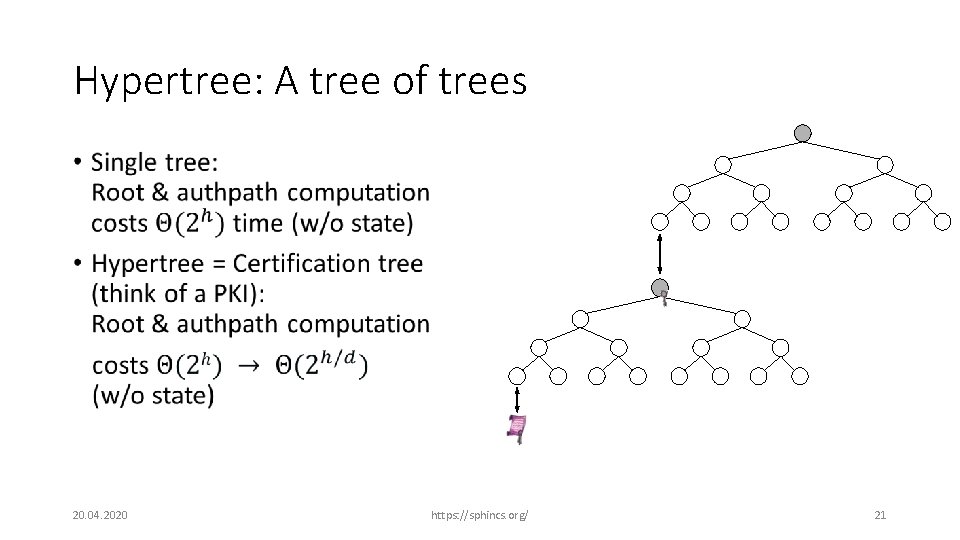
Hypertree: A tree of trees • 20. 04. 2020 https: //sphincs. org/ 21
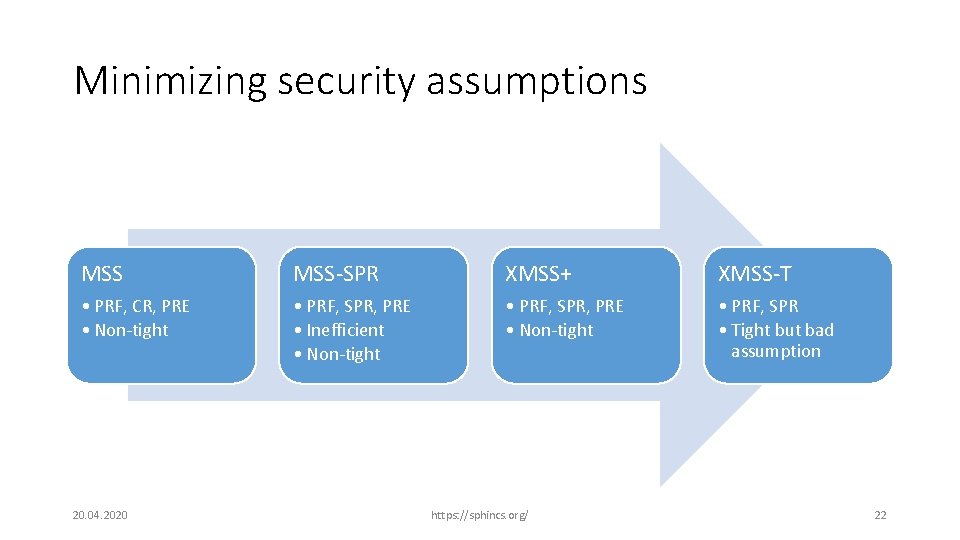
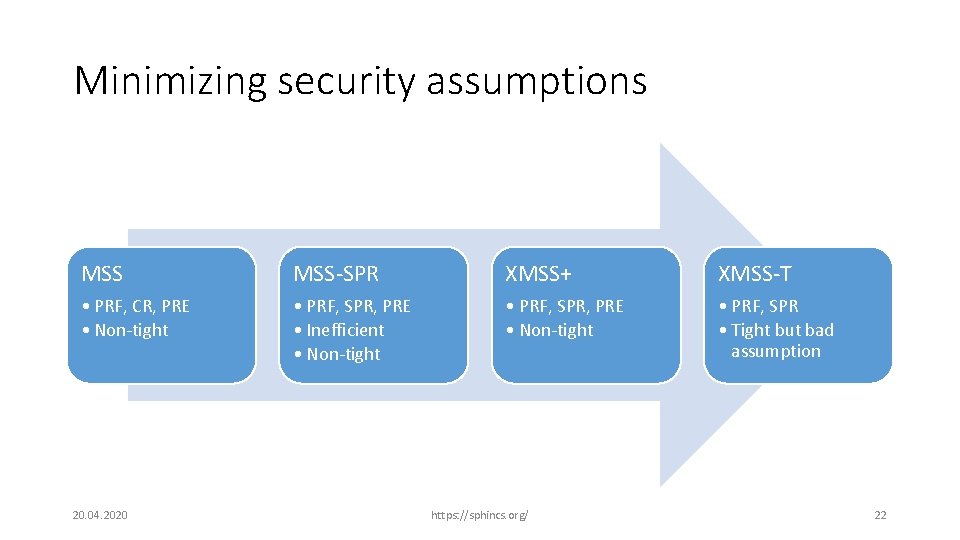
Minimizing security assumptions MSS-SPR XMSS+ XMSS-T • PRF, CR, PRE • Non-tight • PRF, SPR, PRE • Inefficient • Non-tight • PRF, SPR, PRE • Non-tight • PRF, SPR • Tight but bad assumption 20. 04. 2020 https: //sphincs. org/ 22
New security requirements for hash functions Decisional second preimage resistance (DSPR) Joint work with Daniel J. Bernstein 20. 04. 2020 https: //sphincs. org/ 23
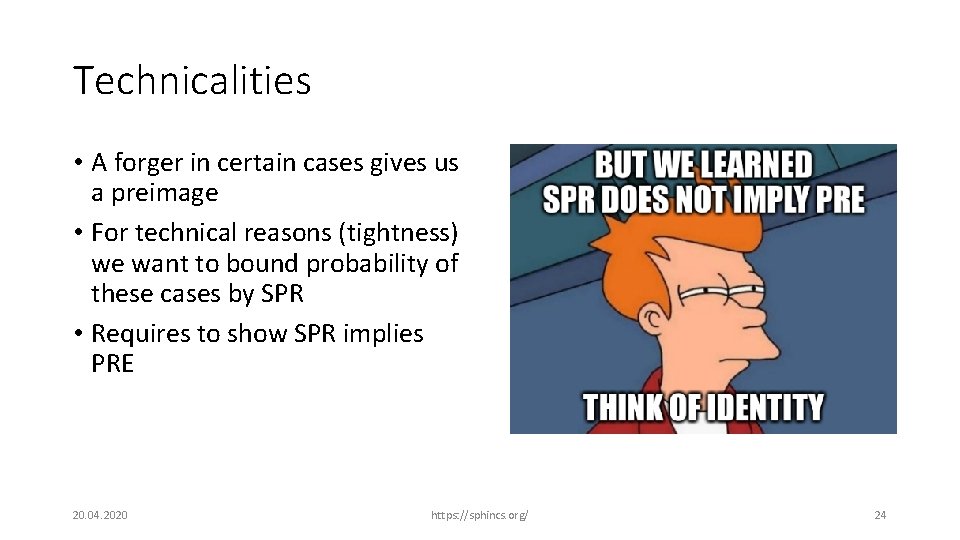
Technicalities • A forger in certain cases gives us a preimage • For technical reasons (tightness) we want to bound probability of these cases by SPR • Requires to show SPR implies PRE 20. 04. 2020 https: //sphincs. org/ 24
Decisional Second-Preimage Resistance joint work with Daniel J. Bernstein, Asiacrypt 2019 • 20. 04. 2020 https: //sphincs. org/ 25

Stateless hash-based signatures SPHINCS Joint work with Daniel J. Bernstein, Daira Hopwood, Tanja Lange, Ruben Niederhagen, Louiza Papachristodoulou, Michael Schneider, Peter Schwabe, and Zooko Wilcox-O’Hearn 20. 04. 2020 https: //sphincs. org/ 26
![Stateless hashbased signatures NY 89 Gol 87 Gol 04 OTS OTS OTS OTS Stateless hash-based signatures [NY 89, Gol 87, Gol 04] OTS • OTS OTS OTS](https://slidetodoc.com/presentation_image_h/12df90a34701d483d42f7a91e1912375/image-27.jpg)
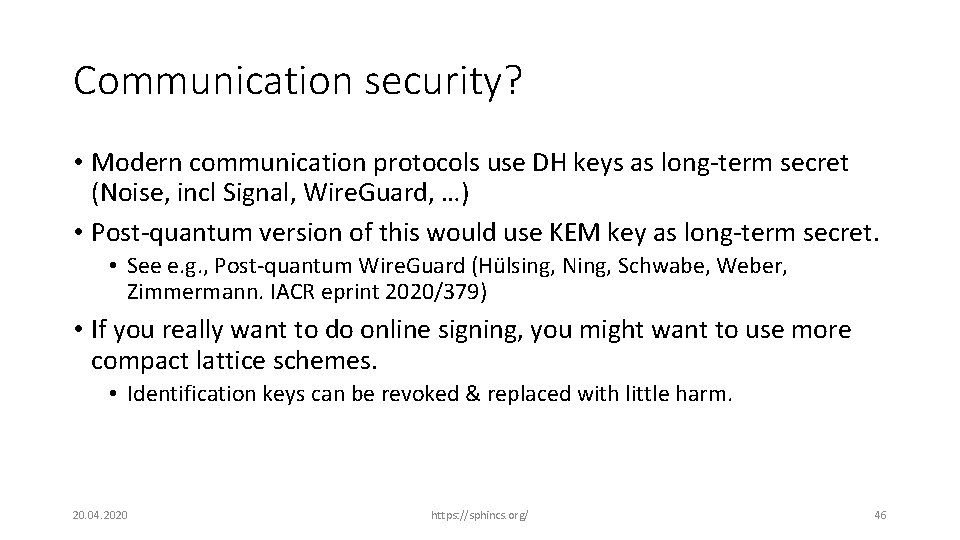
Stateless hash-based signatures [NY 89, Gol 87, Gol 04] OTS • OTS OTS OTS 20. 04. 2020 https: //sphincs. org/ OTS 27
![SPHINCS BHH15 Select index pseudorandomly Use a fewtime signature keypair on leaves SPHINCS [BHH+15] • Select index pseudorandomly • Use a few-time signature key-pair on leaves](https://slidetodoc.com/presentation_image_h/12df90a34701d483d42f7a91e1912375/image-28.jpg)
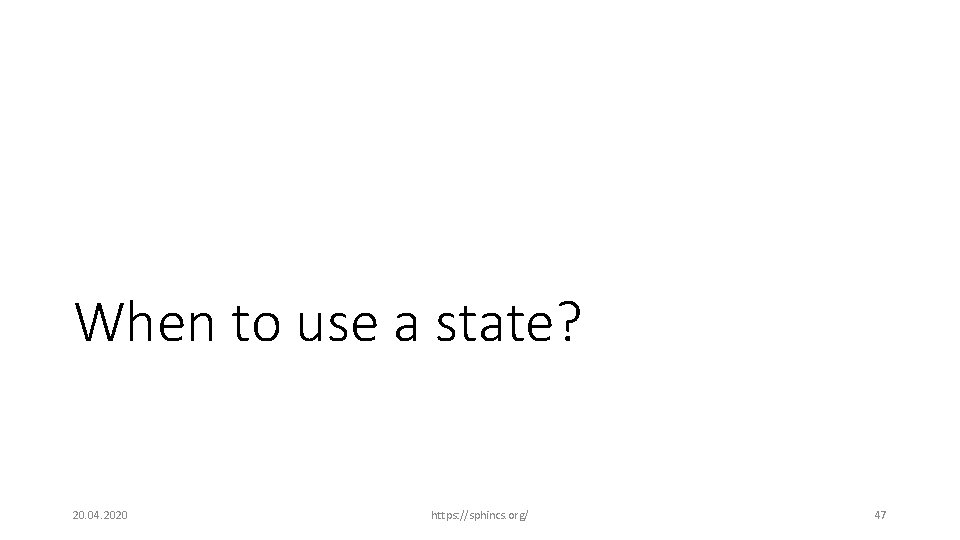
SPHINCS [BHH+15] • Select index pseudorandomly • Use a few-time signature key-pair on leaves to sign messages • Few index collisions allowed • Allows to reduce tree height • Use hypertree: Use d < h. (SPHINCS-256: h=60, d=12) FTS 20. 04. 2020 https: //sphincs. org/ 28
+ The SPHINCS Signature Framework Joint work with Daniel J. Bernstein, Stefan Kölbl, Ruben Niederhagen, Joost Rijneveld, Peter Schwabe 20. 04. 2020 https: //sphincs. org/ 29
The SPHINCS + team Jean-Philippe Aumasson, Daniel J. Bernstein, Christoph Dobraunig, Maria Eichlseder, Scott Fluhrer, Stefan-Lukas Gazdag, Andreas Hülsing, Panos Kampanakis, Stefan Kölbl, Tanja Lange, Martin M. Lauridsen, Florian Mendel, Ruben Niederhagen, Christian Rechberger, Joost Rijneveld, Peter Schwabe 20. 04. 2020 https: //sphincs. org/ 30
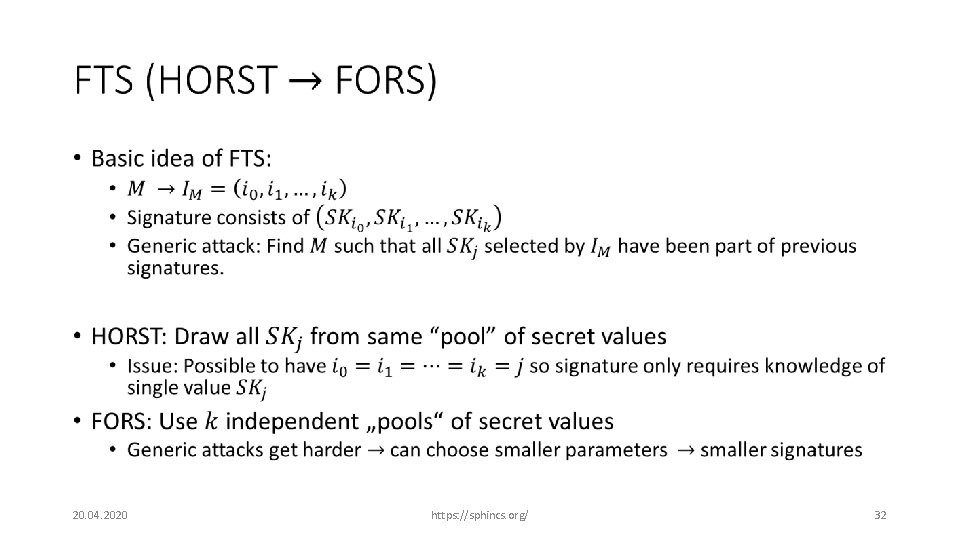
From SPHINCS to SPHINCS+ • 20. 04. 2020 https: //sphincs. org/ 31
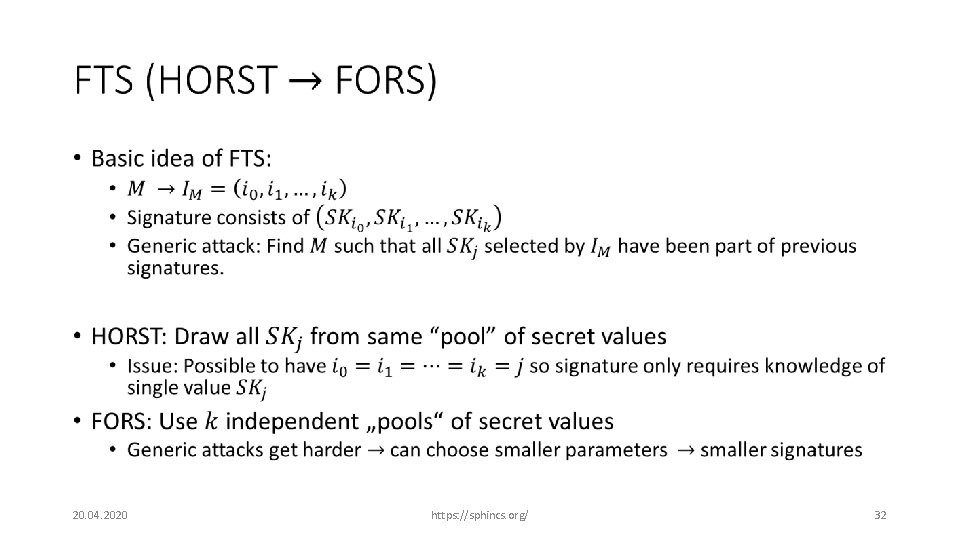
• 20. 04. 2020 https: //sphincs. org/ 32
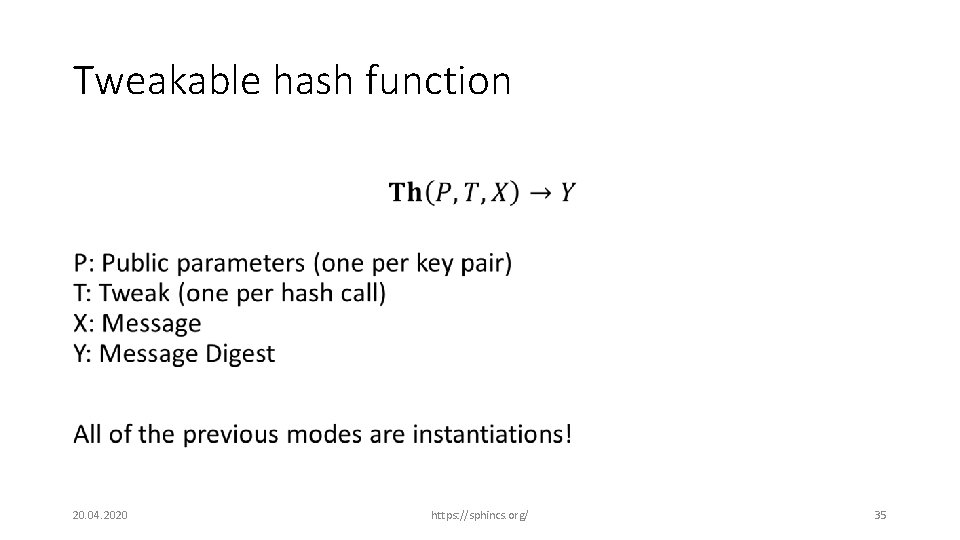
Tweakable hash functions A tool for modular proofs for hash-based signatures 20. 04. 2020 https: //sphincs. org/ 33
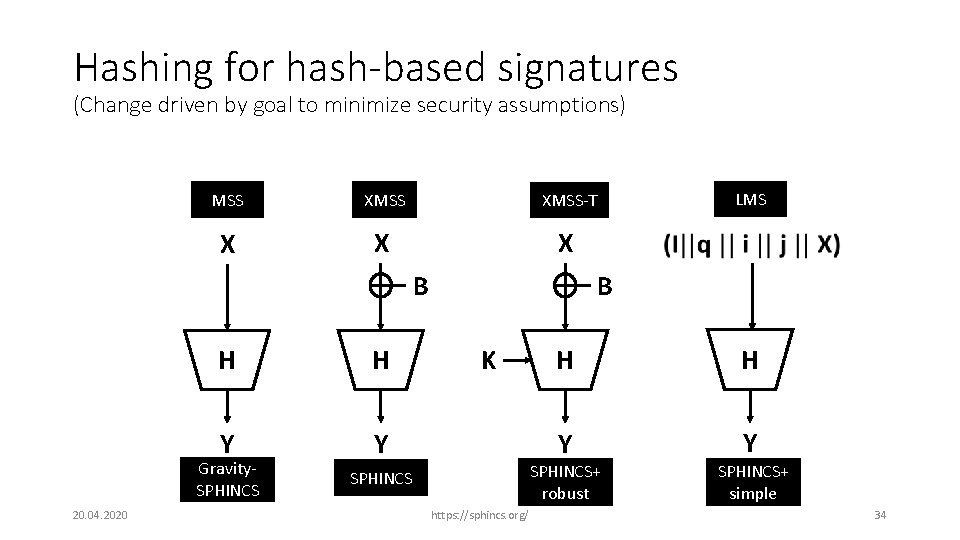
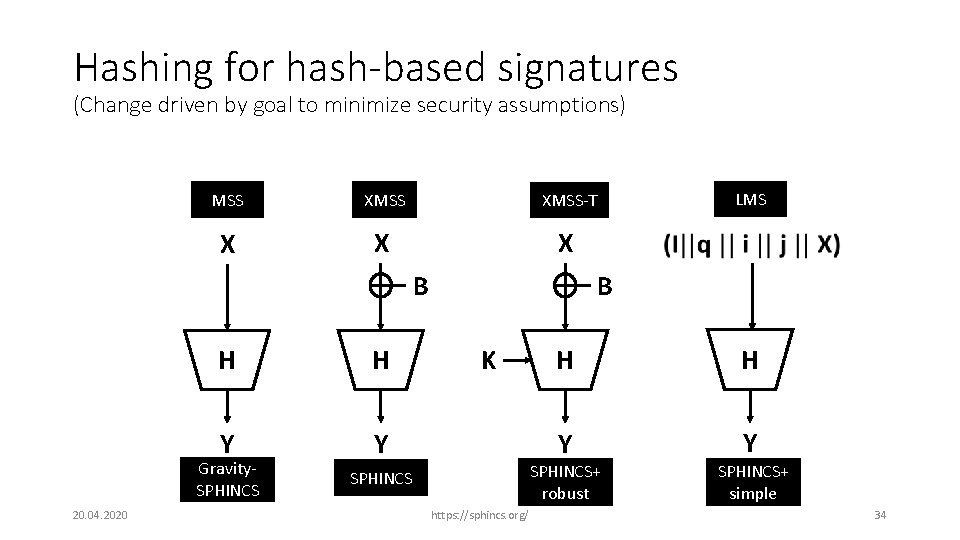
Hashing for hash-based signatures (Change driven by goal to minimize security assumptions) MSS XMSS-T X X X B H H Y Y Gravity. SPHINCS 20. 04. 2020 LMS B K H H Y Y SPHINCS+ robust SPHINCS https: //sphincs. org/ SPHINCS+ simple 34
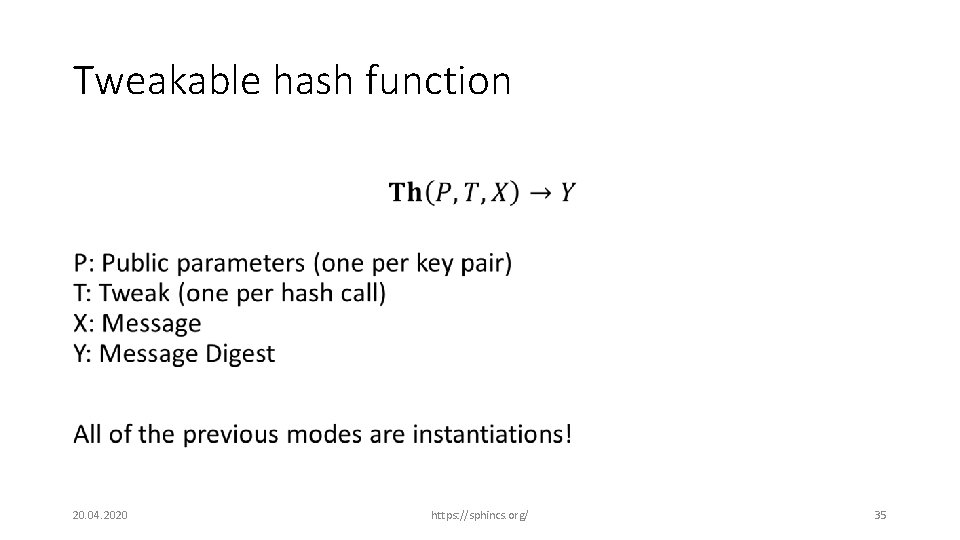
Tweakable hash function • 20. 04. 2020 https: //sphincs. org/ 35
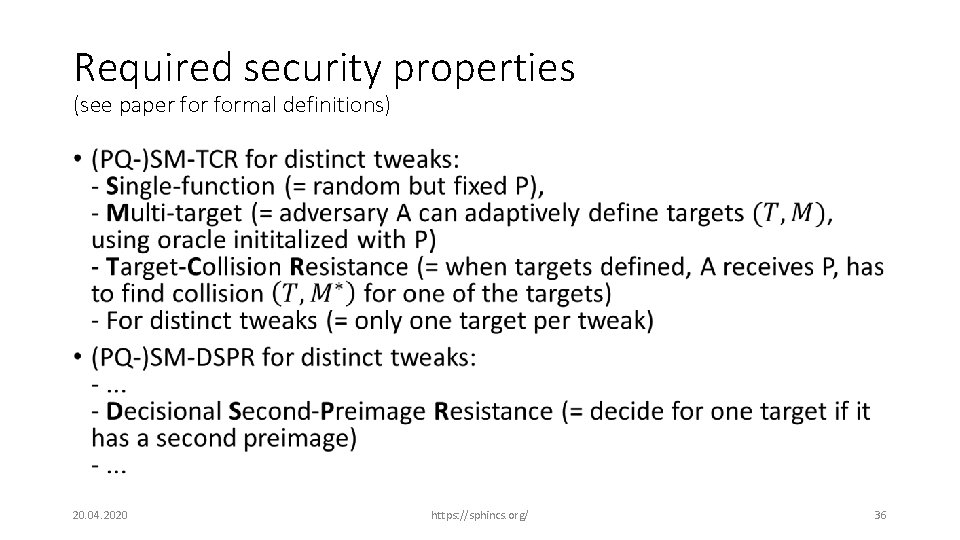
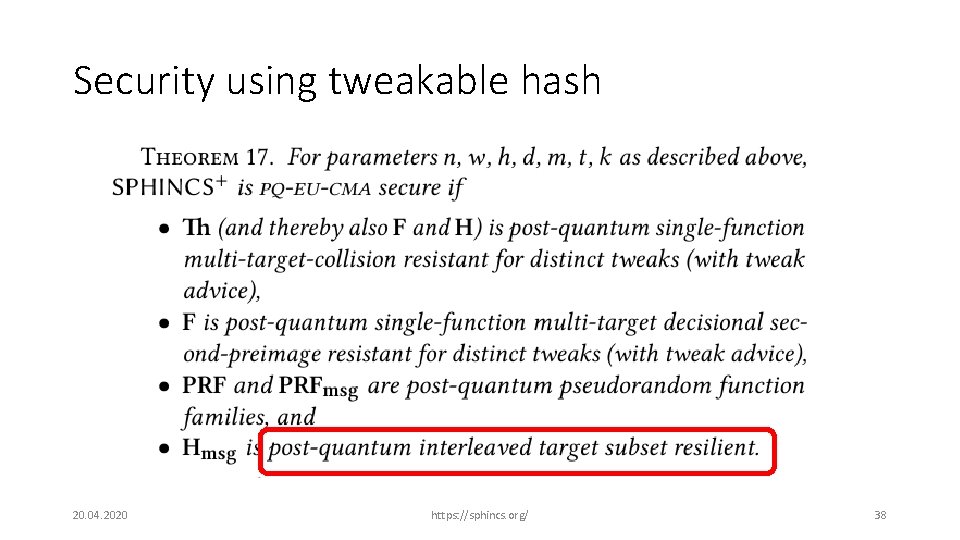
Required security properties (see paper formal definitions) • 20. 04. 2020 https: //sphincs. org/ 36
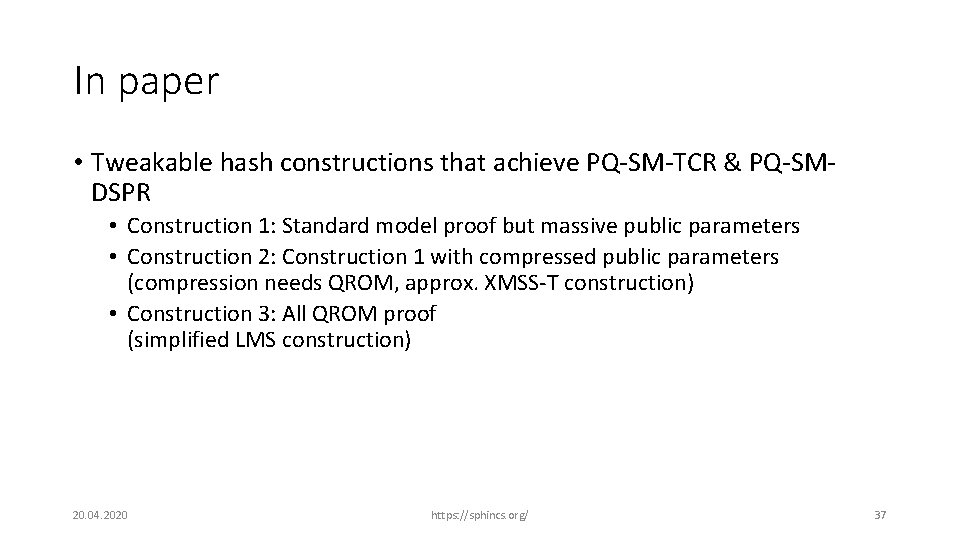
In paper • Tweakable hash constructions that achieve PQ-SM-TCR & PQ-SMDSPR • Construction 1: Standard model proof but massive public parameters • Construction 2: Construction 1 with compressed public parameters (compression needs QROM, approx. XMSS-T construction) • Construction 3: All QROM proof (simplified LMS construction) 20. 04. 2020 https: //sphincs. org/ 37
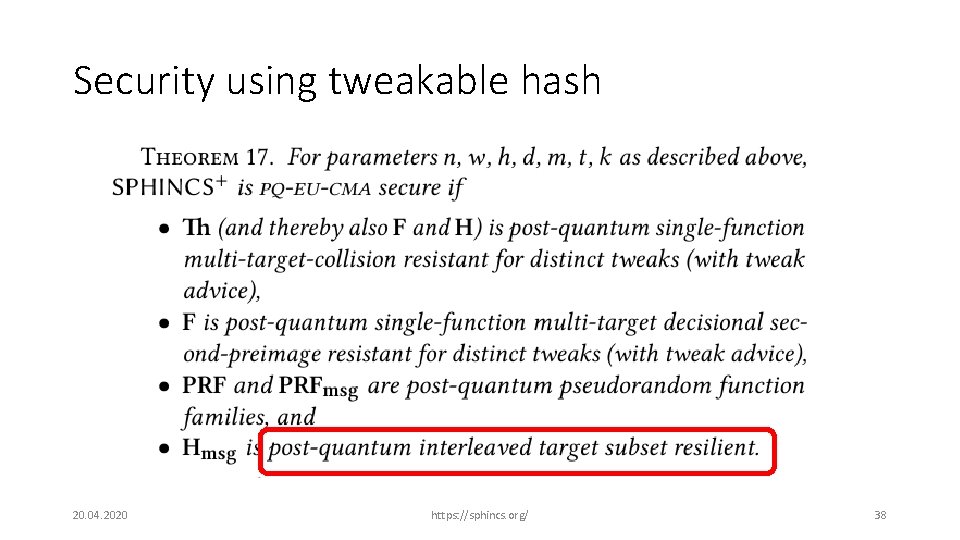
Security using tweakable hash 20. 04. 2020 https: //sphincs. org/ 38
Performance 20. 04. 2020 https: //sphincs. org/ 39
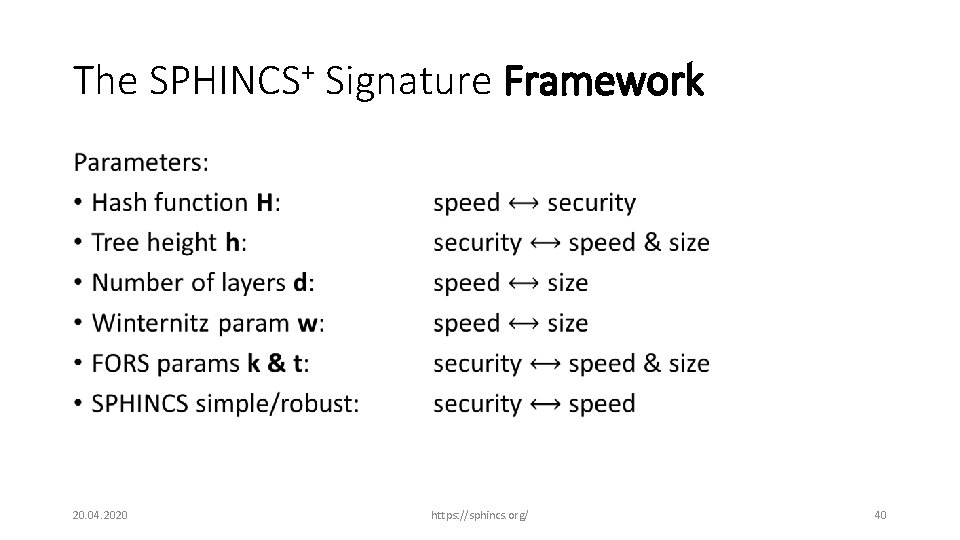
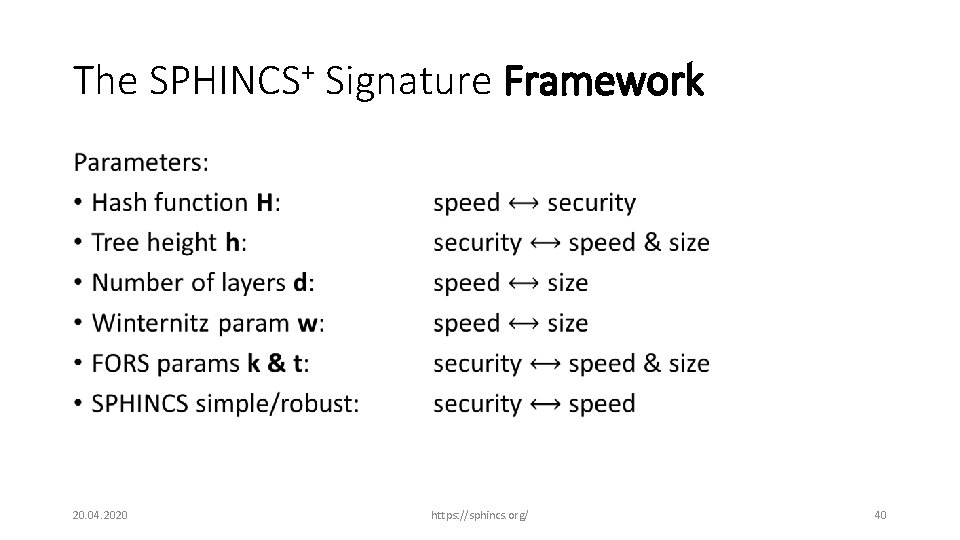
The SPHINCS+ Signature Framework • 20. 04. 2020 https: //sphincs. org/ 40
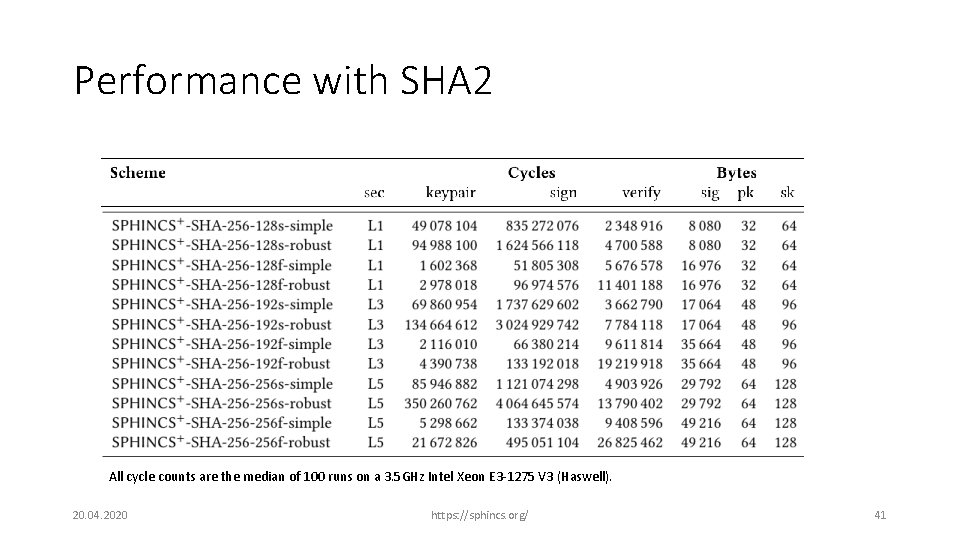
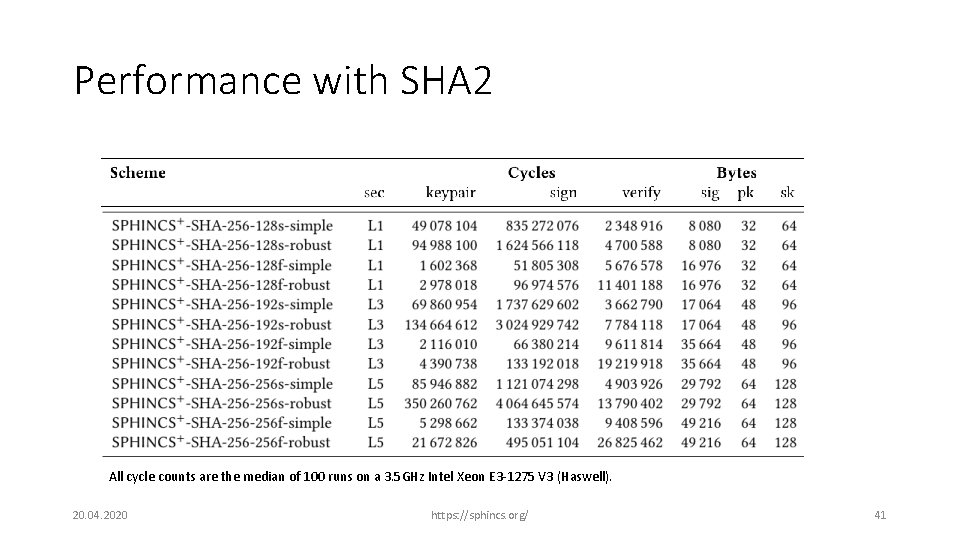
Performance with SHA 2 All cycle counts are the median of 100 runs on a 3. 5 GHz Intel Xeon E 3 -1275 V 3 (Haswell). 20. 04. 2020 https: //sphincs. org/ 41
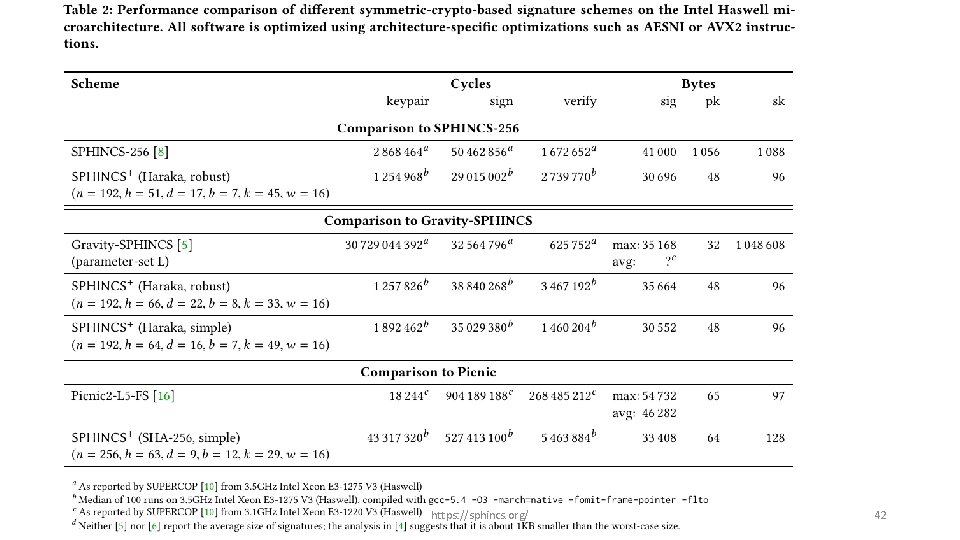
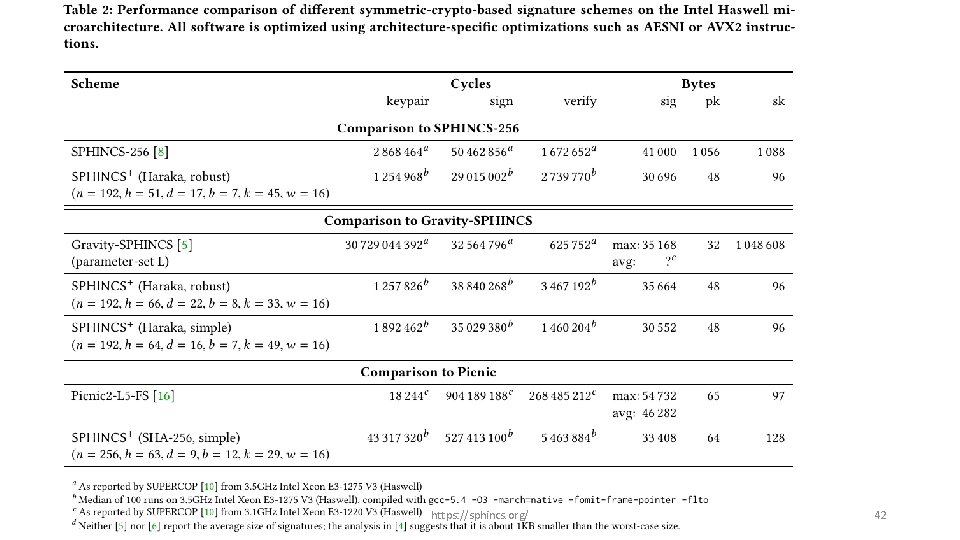
20. 04. 2020 https: //sphincs. org/ 42
Applications 20. 04. 2020 https: //sphincs. org/ 43
When to use hash-based signatures? When… • …you need reliable security • …you only have a hash-function available • …verification speed is critical • …you can handle its issues (performance or state) Generally, all sign once, verify often applications 20. 04. 2020 https: //sphincs. org/ 44
Examples • Certificates: • Security issues have great impact • Verification speed far more critical than signing speed (If signing throughput important use batch-signing) • Pk + sig size pretty small • Secure mail • Security first • Size & latency not too important • Software & document signing • Security first • Size & latency not too important • Verification speed far more critical than signing speed 20. 04. 2020 https: //sphincs. org/ 45
Communication security? • Modern communication protocols use DH keys as long-term secret (Noise, incl Signal, Wire. Guard, …) • Post-quantum version of this would use KEM key as long-term secret. • See e. g. , Post-quantum Wire. Guard (Hülsing, Ning, Schwabe, Weber, Zimmermann. IACR eprint 2020/379) • If you really want to do online signing, you might want to use more compact lattice schemes. • Identification keys can be revoked & replaced with little harm. 20. 04. 2020 https: //sphincs. org/ 46
When to use a state? 20. 04. 2020 https: //sphincs. org/ 47
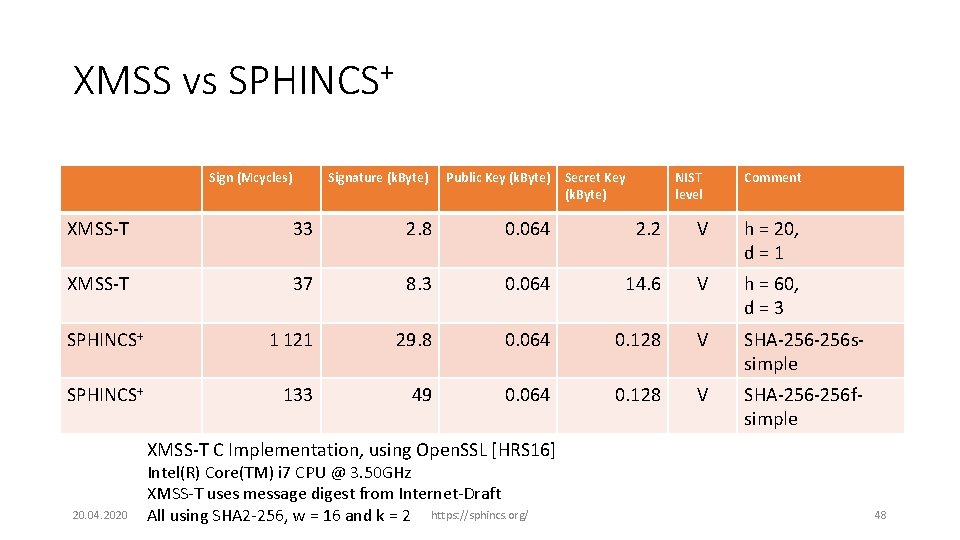
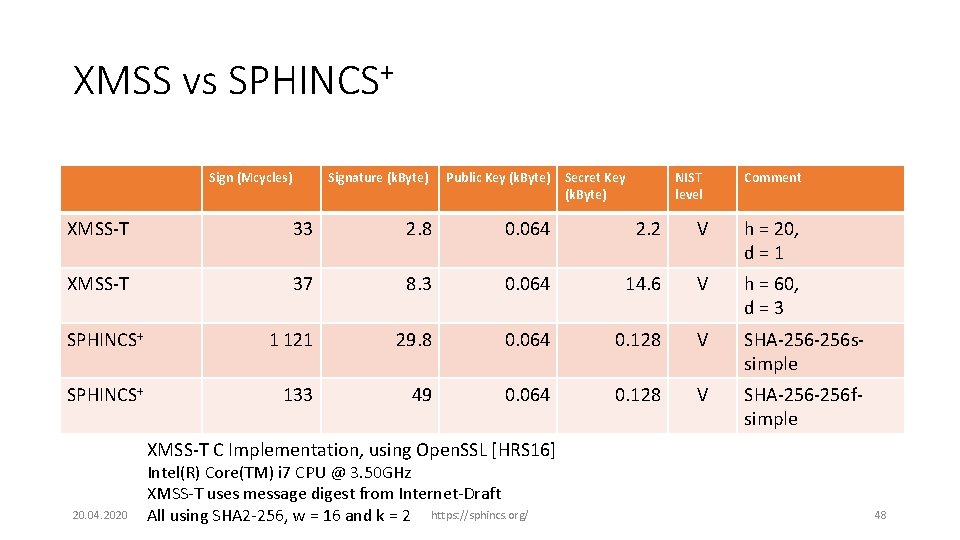
XMSS vs SPHINCS+ Sign (Mcycles) Signature (k. Byte) Public Key (k. Byte) Secret Key (k. Byte) NIST level Comment XMSS-T 33 2. 8 0. 064 2. 2 V h = 20, d = 1 XMSS-T 37 8. 3 0. 064 14. 6 V h = 60, d = 3 SPHINCS+ 1 121 29. 8 0. 064 0. 128 V SHA-256 ssimple SPHINCS+ 133 49 0. 064 0. 128 V SHA-256 fsimple XMSS-T C Implementation, using Open. SSL [HRS 16] 20. 04. 2020 Intel(R) Core(TM) i 7 CPU @ 3. 50 GHz XMSS-T uses message digest from Internet-Draft All using SHA 2 -256, w = 16 and k = 2 https: //sphincs. org/ 48
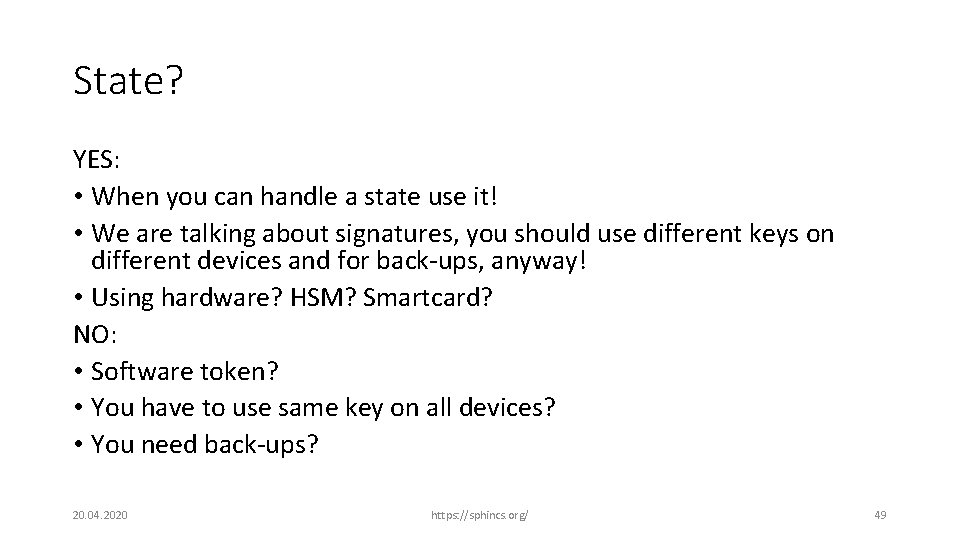
State? YES: • When you can handle a state use it! • We are talking about signatures, you should use different keys on different devices and for back-ups, anyway! • Using hardware? HSM? Smartcard? NO: • Software token? • You have to use same key on all devices? • You need back-ups? 20. 04. 2020 https: //sphincs. org/ 49
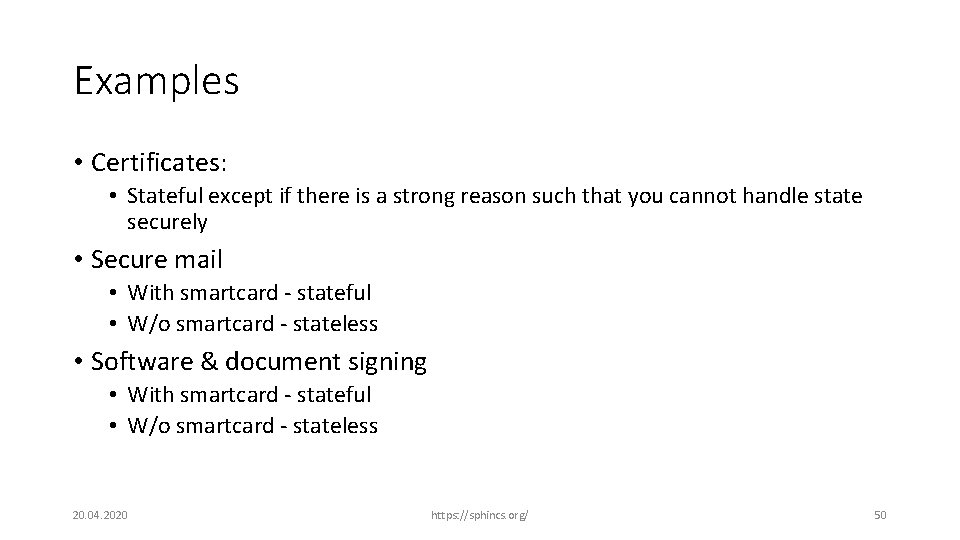
Examples • Certificates: • Stateful except if there is a strong reason such that you cannot handle state securely • Secure mail • With smartcard - stateful • W/o smartcard - stateless • Software & document signing • With smartcard - stateful • W/o smartcard - stateless 20. 04. 2020 https: //sphincs. org/ 50
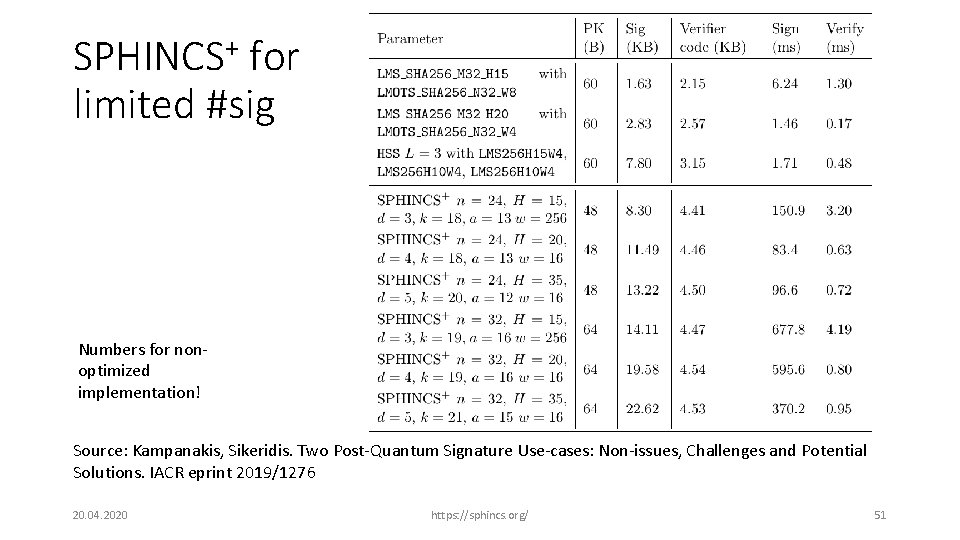
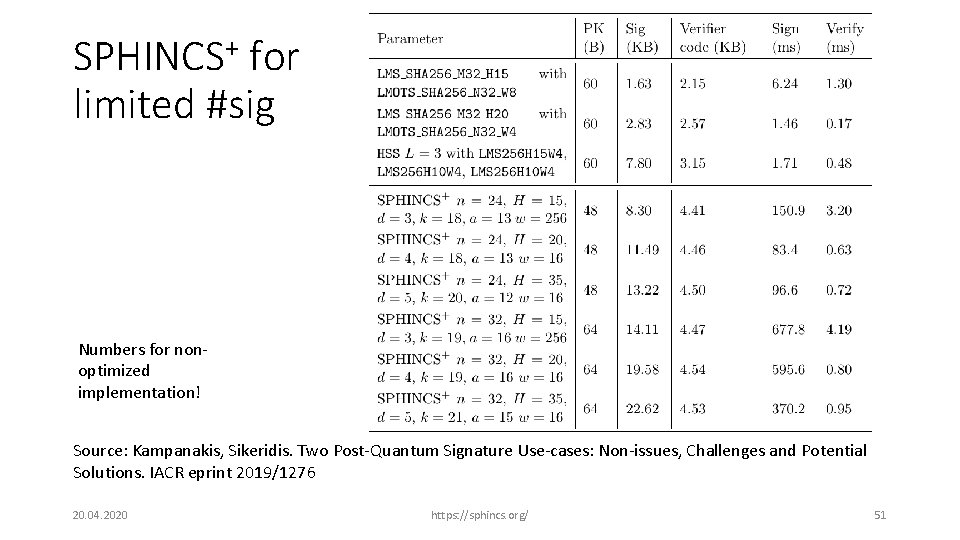
SPHINCS+ for limited #sig Numbers for nonoptimized implementation! Source: Kampanakis, Sikeridis. Two Post-Quantum Signature Use-cases: Non-issues, Challenges and Potential Solutions. IACR eprint 2019/1276 20. 04. 2020 https: //sphincs. org/ 51
Conclusion • SPHINCS+ with SHA 2 is probably the scheme with the weakest security assumptions in the competition (no new mathematics, no new block cipher). • Hash-based signatures fit well with sign-once, verify-often applications • If you can handle state, stateful schemes are better but • We might be able to get better performance if NIST reduces the number of signatures per key pair 20. 04. 2020 https: //sphincs. org/ 52
“If you’re signing something for the long-term 30 future, and 40 KB sigs is not a problem, use (stateless) hash-based sigs e. g. SPHINCS” Vadim Lyubashevsky, 2017 20. 04. 2020 https: //sphincs. org/ 53