The Sony CD DRM Debacle A case study
The Sony CD DRM Debacle A case study of digital rights management 1
Overview: n n n DRM Goals XCP Media. Max Defeating Software Engineering Code of Ethics and the principles that were broken Lawsuit 2
Goals of DRM The primary goals of a DRM system is to protect and enable the business models of the record label and the DRM vendor. Lessons from the Sony CD DRM Episode (pg 2) 3

Record label Goals n Overall purpose is to increase profit. n Increase sales Limit disc-to-disc copying n Limit local copying n n Get software onto users computers Sell advertising n Gather and sell information about users n Lessons from the Sony CD DRM Episode (pg 2, 3) 4
DRM Vendor Goals n n Maximize price for DRM software by creating value for the record label Survive Smaller companies need to take more risk n Maximize installed base n Need to get major recording labels on board n Become THE DRM used, beat out other vendors n Lessons from the Sony CD DRM Episode (pg 3) 5
CD DRM Systems n n Must play on ordinary CD players Limited readability by computers n n n DRM software must be installed somehow n n n Must prevent copying on computer without permission DRM’s software must give access to music Autorun on windows computers Must be intentionally run by user on Mac DRM software must recognize the DRM discs Lessons from the Sony CD DRM Episode (pg 4) 6
XCP n Relies on the autorun feature of windows Commands in autorun. inf on cd executed n Auturun commonly used to display splash screens and initiate installation of programs n n n Mac. OS does not use autorun, user must manually run installer XCP protected discs contain two sessions Music session n DRM content session n Lessons from the Sony CD DRM Episode (pg 5) 7
Two Session Disc http: //www. fadden. com/cdrpics/data-surface-3. jpg 8
XCP (continued) n n Unprotected time between disc insertion and protection software installed User required to agree to End User License Agreement (EULA) Software is then installed n CD can now be played n If user declines, CD immediately ejected n Lessons from the Sony CD DRM Episode (pg 6, 7) 9
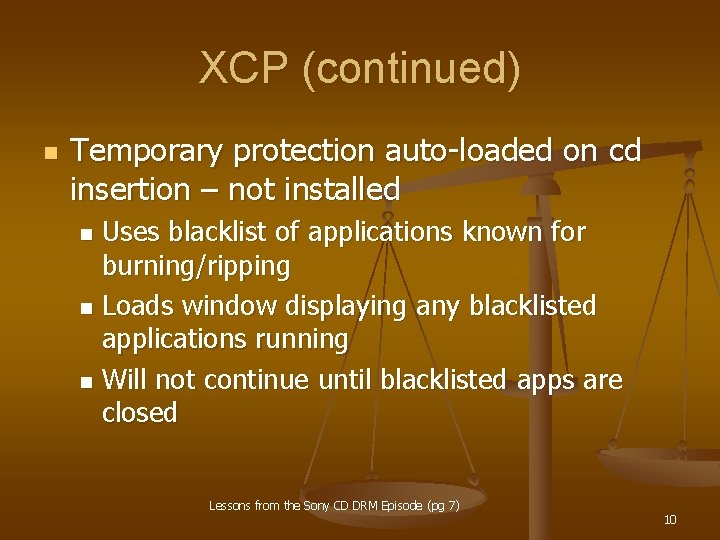
XCP (continued) n Temporary protection auto-loaded on cd insertion – not installed Uses blacklist of applications known for burning/ripping n Loads window displaying any blacklisted applications running n Will not continue until blacklisted apps are closed n Lessons from the Sony CD DRM Episode (pg 7) 10
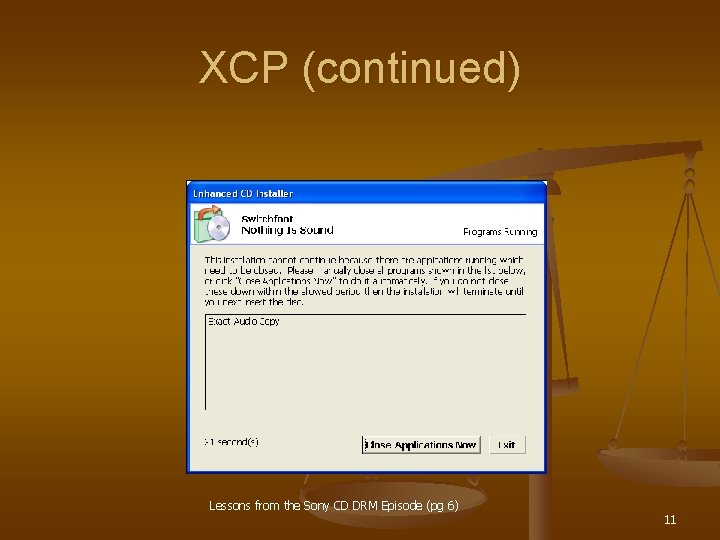
XCP (continued) Lessons from the Sony CD DRM Episode (pg 6) 11
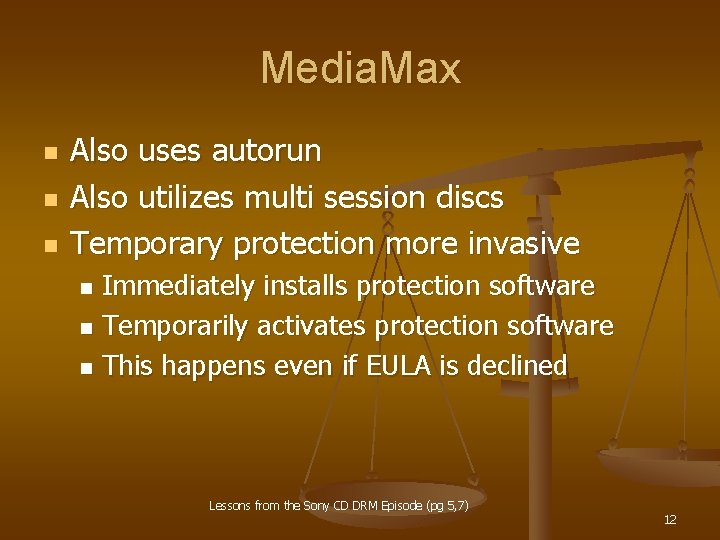
Media. Max n n n Also uses autorun Also utilizes multi session discs Temporary protection more invasive Immediately installs protection software n Temporarily activates protection software n This happens even if EULA is declined n Lessons from the Sony CD DRM Episode (pg 5, 7) 12

Defeating The Copy Protection n n Marker the Data Hold shift-key while inserting Disable auto-run Use alternative Operating System Linux n Mac n Lessons from the Sony CD DRM Episode (pg 5) 13
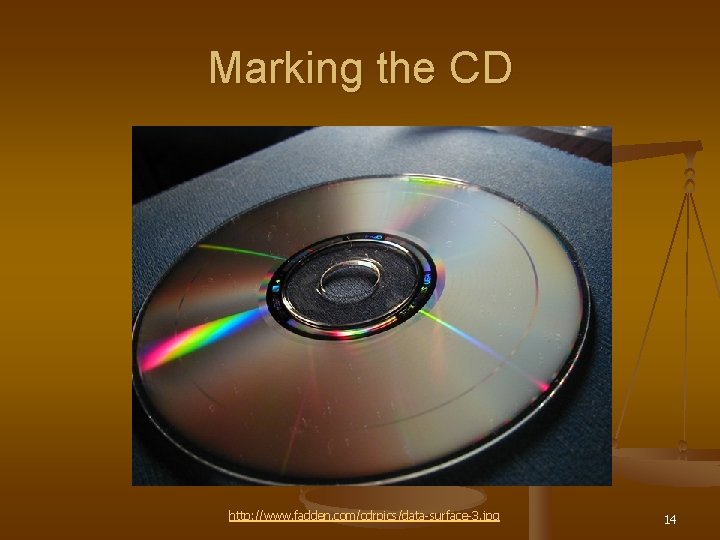
Marking the CD http: //www. fadden. com/cdrpics/data-surface-3. jpg 14
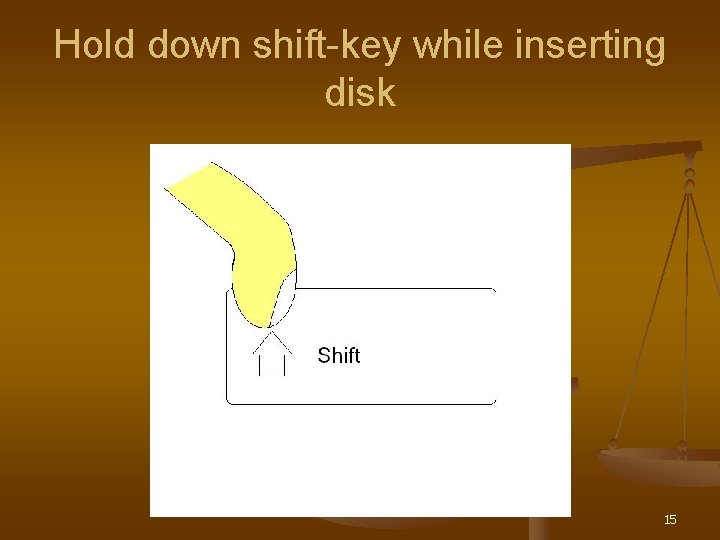
Hold down shift-key while inserting disk 15
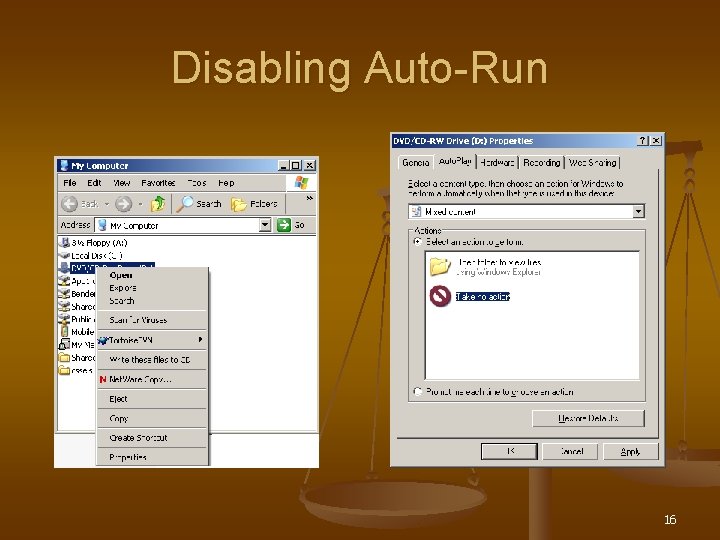
Disabling Auto-Run 16
Alternative Operating Systems Tux image from: http: //www. sjbaker. org/tux/Penguin. png Apple image from: http: //en. wikipedia. org/wiki/Image: Apple-logo. png 17
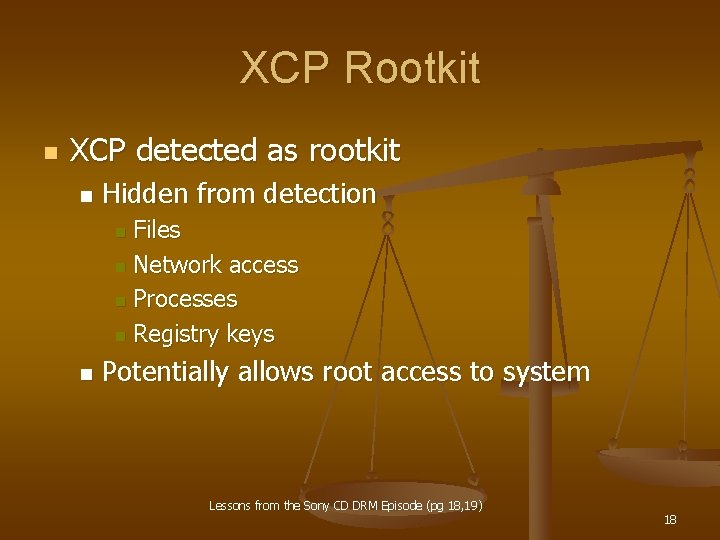
XCP Rootkit n XCP detected as rootkit n Hidden from detection Files n Network access n Processes n Registry keys n n Potentially allows root access to system Lessons from the Sony CD DRM Episode (pg 18, 19) 18
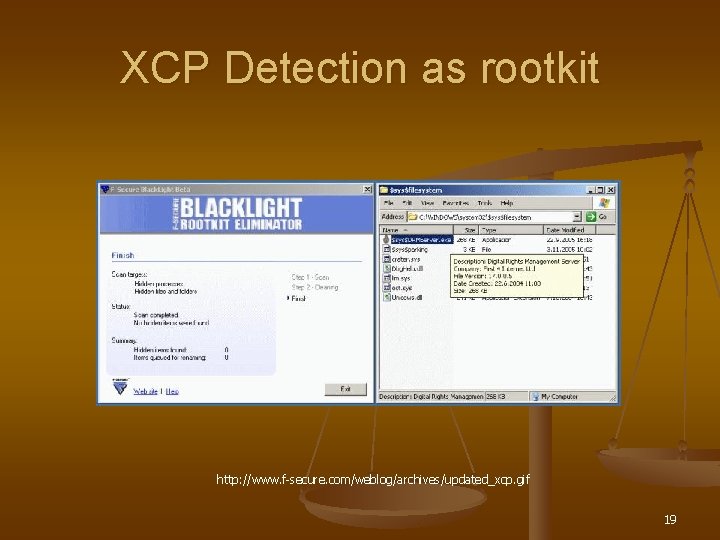
XCP Detection as rootkit http: //www. f-secure. com/weblog/archives/updated_xcp. gif 19
XCP Vulnerabilities n Installed and ran invisibly Undetectable by even virus software n Hides itself and its processes n n Hides anything starting with $sys$ Any malicious code can be hidden by $sys$ n Exploited by at least two malicious programs n n Also allows random crashing of system via updated system files Lessons from the Sony CD DRM Episode (pg 19) 20
Media. Max Vulnerabilities n n Automatically installs on CD insertion Permissions set so any user can modify n Allows malicious code to easily be installed n Next time Media. Max protected cd inserted, malicious code executed Lessons from the Sony CD DRM Episode (pg 17, 19) 21
Vulnerabilities (continued) n Requires Power User privileges to run n Allows attacker’s code to have complete control Aggressively updates installed code with each protected CD Patch to rectify attack initiated attack code Lessons from the Sony CD DRM Episode (pg 17, 19) 22
Spyware-like Activities n Report user activities to label/vendor n n n Vendors said it did not, it infact does Retrieve images or adds to display from web Log user’s info IP address n Date and time n Identity of album n Lessons from the Sony CD DRM Episode (pg 14) 23
Software Engineering Code of Ethics (ACM/IEEE-CS Joint – shortened version) Software engineers shall commit themselves to making the analysis, specification, design, development, testing and maintenance of software a beneficial and respected profession. In accordance with their commitment to the health, safety and welfare of the public, software engineers shall adhere to the following Eight Principles: Info from: http: //www. acm. org/serving/se/code. htm 24
Software Engineering Code of Ethics (continued) n n 1. PUBLIC - Software engineers shall act consistently with the public interest. 2. CLIENT AND EMPLOYER - Software engineers shall act in a manner that is in the best interests of their client and employer and consistent with the public interest. 3. PRODUCT - Software engineers shall ensure that their products and related modifications meet the highest professional standards possible. 4. JUDGMENT - Software engineers shall maintain integrity and independence in their professional judgment. Info from: http: //www. acm. org/serving/se/code. htm 25
Software Engineering Code of Ethics (Continued) n 5. MANAGEMENT - Software engineering managers and leaders shall subscribe to and promote an ethical approach to the management of software development and maintenance. n 6. PROFESSION - Software engineers shall advance the integrity and reputation of the profession consistent with the public interest. n 7. COLLEAGUES - Software engineers shall be fair to and supportive of their colleagues. n 8. SELF - Software engineers shall participate in lifelong learning regarding the practice of their profession and shall promote an ethical approach to the practice of the profession. Info from: http: //www. acm. org/serving/se/code. htm 26
Ethical Issues n n n n Install without user permission Users left vulnerable to malware After uninstall, user still vulnerable Spyware tactics used Prevents fair use Damages the reputation of software manufacturers Sony refused to deny wrong-doing 27
Class Action against Sony n Requests from Electronic Frontier Foundation (EFF) n n n Stop production of CDs with bad DRM Get people non-DRM’d versions of music Do this quickly Get people free music or money in case of XCP Ensure independent security testing pre-launch of any new DRM Agree to quick response by Sony BMG in future security flaws of DRM http: //www. eff. org/IP/DRM/Sony-BMG/settlement_faq. php 28
Settlement n n Sony agreed to EFF’s requests Never admitted to wrong doing No reparations for crashed systems At present no criminal cases n Sony still left open to future law suits, but EFF’s case over http: //www. eff. org/IP/DRM/Sony-BMG/settlement_faq. php 29
Sources: n n n n 1. http: //www. acm. org/serving/se/code. htm 2. Lessons from the Sony CD DRM Episode, Authors: J. Alex Halderman and Edward W. Felten Center for Information Technology Policy, Department of Computer Science, Princeton University, Extended Version. February 14, 2006 3. http: //www. eff. org/IP/DRM/Sony-BMG/mediamaxfaq. php 4. http: //www. eff. org/IP/DRM/Sony-BMG/ 5. http: //www. f-secure. com/weblog/archives/updated_xcp. gif 6. http: //www. sjbaker. org/tux/Penguin. png 7. http: //en. wikipedia. org/wiki/Image: Apple-logo. png 8. http: //www. fadden. com/cdrpics/data-surface-3. jpg 30
- Slides: 30