The software model checker BLAST Dirk Beyer Thomas
The software model checker BLAST Dirk Beyer, Thomas A. Henzinger, Ranjit Jhala, Rupak Majumdar Presented by Yunho Kim
Overview n n Predicate abstraction is successfully applied to software model checking l Infinite concrete states ! finite abstract states l Tools: SLAM(MSR), BLAST(UCB), SATABS(CMU) Cost for abstraction is still too high l l n O( 2 # preds ) abstract states We need to abstract and refine locally, not globally Blast proposed l l Lazy abstraction Craig interpolation-based refinement Yunho Kim@ pswlab The software model checker BLAST 2 / 28
Contents n Part I. Software Model Checking l l l n Program behavior Predicate abstraction Counterexample-guided abstraction refinement Part II. BLAST l l Abstraction and model checking Craig interpolation-based refinement Yunho Kim@ pswlab The software model checker BLAST 3 / 28
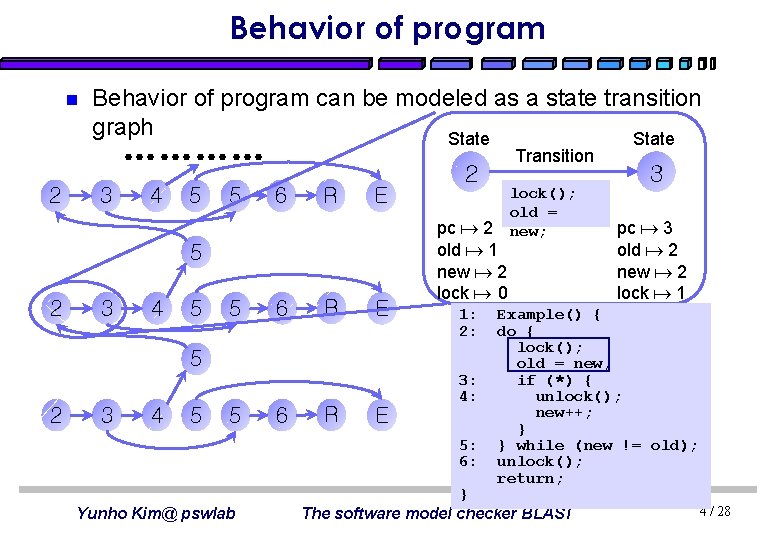
Behavior of program n Behavior of program can be modeled as a state transition graph State ………… 2 3 4 5 5 6 R E 5 2 3 4 5 5 6 R E 2 pc 2 old 1 new 2 lock 0 1: 2: 5 2 3 4 5 5 6 R E 3: 4: 5: 6: Yunho Kim@ pswlab Transition lock(); old = new; 3 pc 3 old 2 new 2 lock 1 Example() { do { lock(); old = new; if (*) { unlock(); new++; } } while (new != old); unlock(); return; } The software model checker BLAST 4 / 28
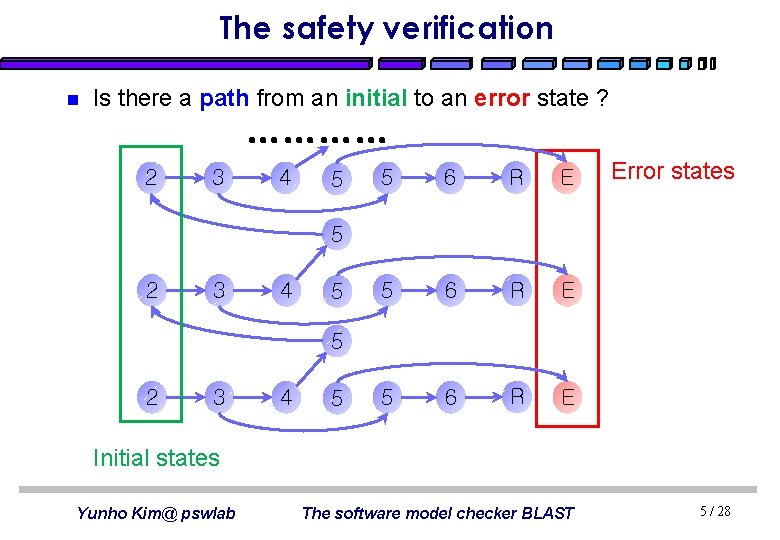
The safety verification n Is there a path from an initial to an error state ? ………… 2 3 4 5 5 6 R E Error states 5 2 3 4 5 Initial states Yunho Kim@ pswlab The software model checker BLAST 5 / 28
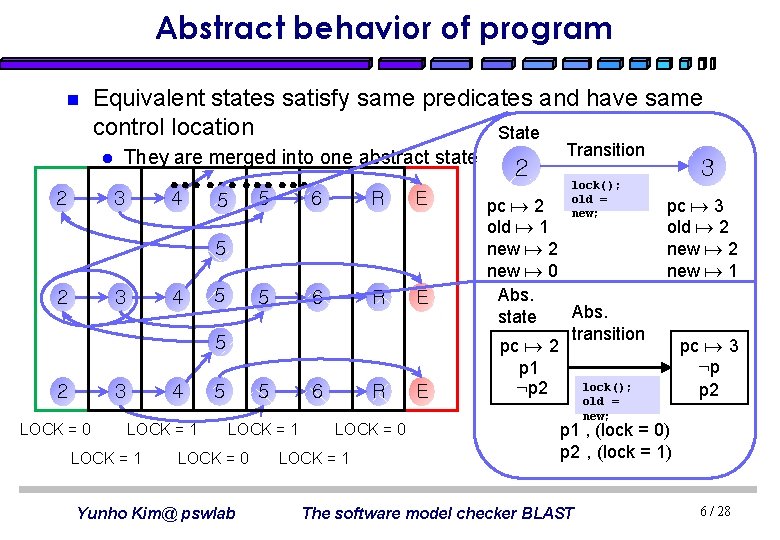
Abstract behavior of program n Equivalent states satisfy same predicates and have same control location State l 2 They are merged into one abstract state ………… 4 6 5 5 3 R E 5 2 3 4 5 5 6 5 2 3 LOCK = 0 4 LOCK = 1 5 5 LOCK = 1 LOCK = 0 Yunho Kim@ pswlab R 6 LOCK = 0 LOCK = 1 E 2 Transition lock(); old = new; pc 2 old 1 new 2 new 0 Abs. state transition pc 2 p 1 lock(); : p 2 old = new; 3 pc 3 old 2 new 1 pc 3 : p p 2 p 1 , (lock = 0) p 2 , (lock = 1) The software model checker BLAST 6 / 28
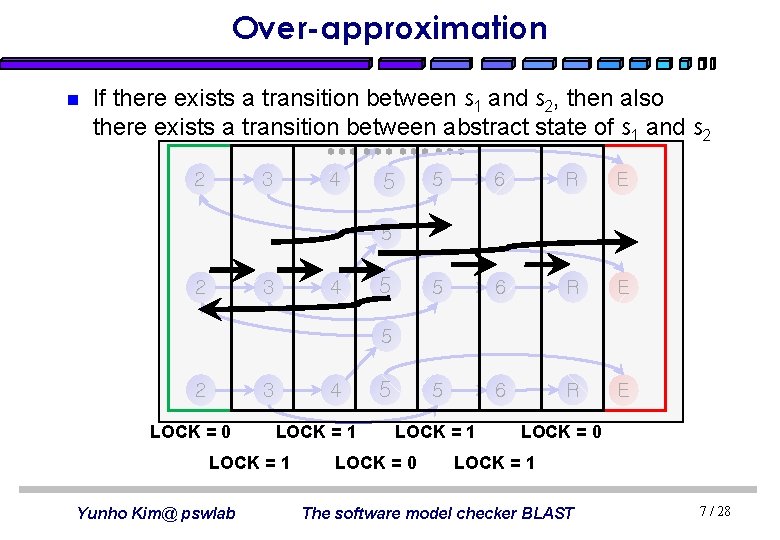
Over-approximation n If there exists a transition between s 1 and s 2, then also there exists a transition between abstract state of s 1 and s 2 2 ………… 3 4 5 5 6 R E 5 2 3 4 5 5 2 3 LOCK = 0 4 LOCK = 1 Yunho Kim@ pswlab 5 LOCK = 1 LOCK = 0 LOCK = 1 The software model checker BLAST 7 / 28
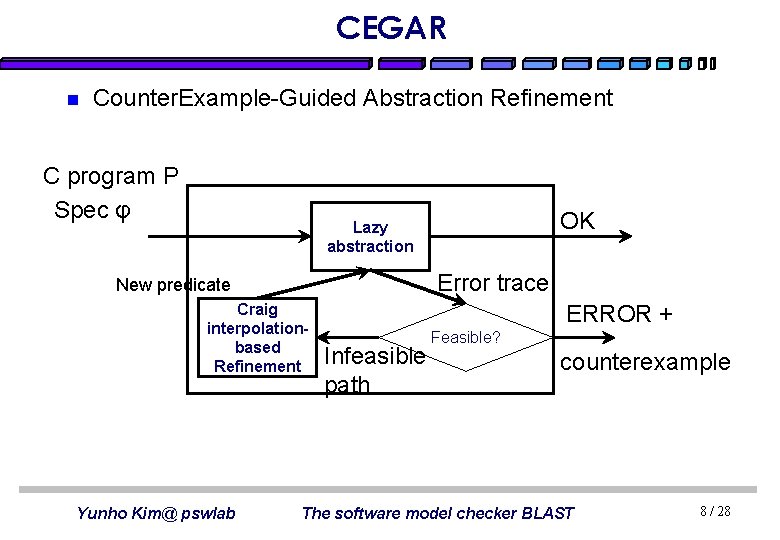
CEGAR n Counter. Example-Guided Abstraction Refinement C program P Spec φ OK Lazy abstraction Error trace New predicate Craig interpolationbased Refinement Yunho Kim@ pswlab ERROR + Infeasible path Feasible? counterexample The software model checker BLAST 8 / 28
Part II. BLAST n Abstraction and model checking n Craig interpolation-based refinement Yunho Kim@ pswlab The software model checker BLAST 9 / 28
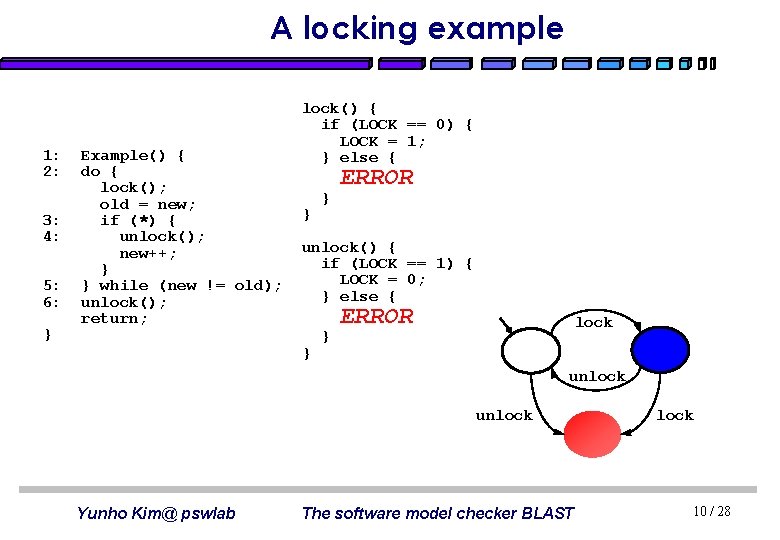
A locking example 1: 2: 3: 4: 5: 6: } Example() { do { lock(); old = new; if (*) { unlock(); new++; } } while (new != old); unlock(); return; lock() { if (LOCK == 0) { LOCK = 1; } else { } } ERROR unlock() { if (LOCK == 1) { LOCK = 0; } else { } } ERROR lock unlock Yunho Kim@ pswlab The software model checker BLAST lock 10 / 28
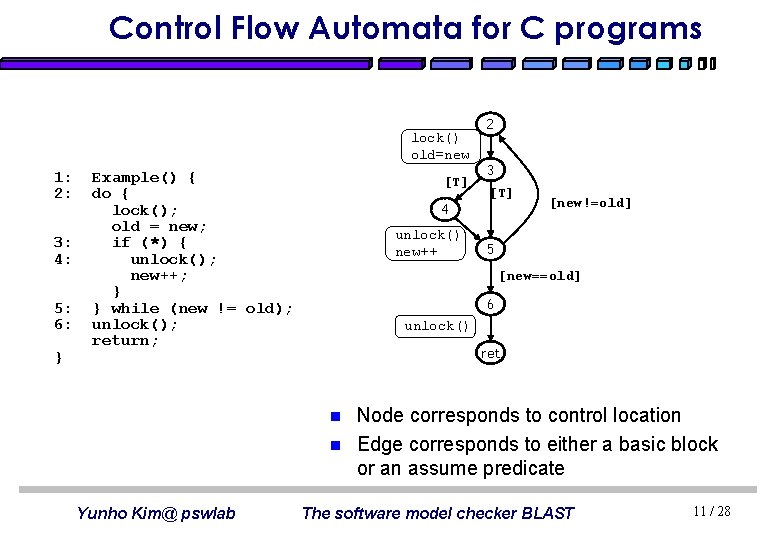
Control Flow Automata for C programs lock() old=new 1: 2: 3: 4: 5: 6: } Example() { do { lock(); old = new; if (*) { unlock(); new++; } } while (new != old); unlock(); return; [T] 3 [T] 4 unlock() new++ [new!=old] 5 [new==old] 6 unlock() ret n n Yunho Kim@ pswlab 2 Node corresponds to control location Edge corresponds to either a basic block or an assume predicate The software model checker BLAST 11 / 28
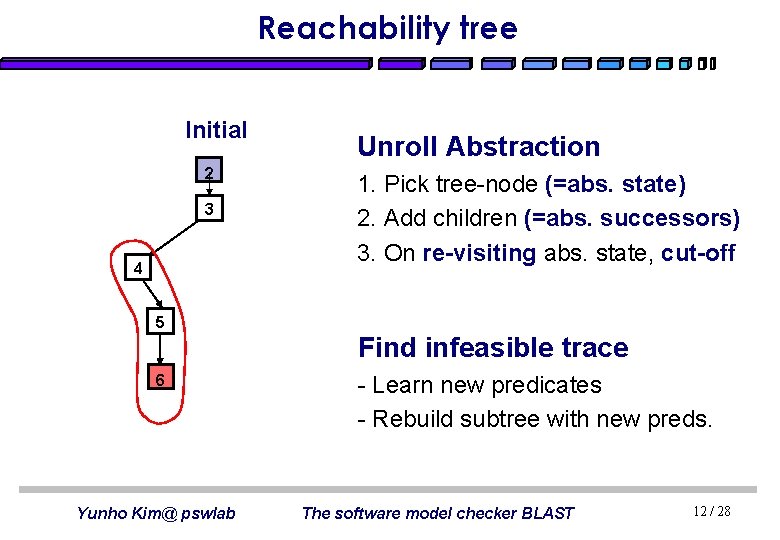
Reachability tree Initial 2 3 4 Unroll Abstraction 1. Pick tree-node (=abs. state) 2. Add children (=abs. successors) 3. On re-visiting abs. state, cut-off 5 Find infeasible trace 6 Yunho Kim@ pswlab - Learn new predicates - Rebuild subtree with new preds. The software model checker BLAST 12 / 28

Forward search(1/4) 2: 3: 4: 5: 6: do { lock(); old = new; if (*) { unlock(); new++; } } while (new != old); unlock(); return; 2 LOCK = 0 Map P from Loc to set of predicates Location Predicates 2 LOCK = 0, LOCK = 1 3 LOCK = 0, LOCK = 1 4 LOCK = 0, LOCK = 1 5 LOCK = 0, LOCK = 1 6 LOCK = 0, LOCK = 1 Yunho Kim@ pswlab n n Each tree node corresponds to control location and labeled with reachable region Edge corresponds to either a basic block or an assume predicate Reachability Tree The software model checker BLAST 13 / 28
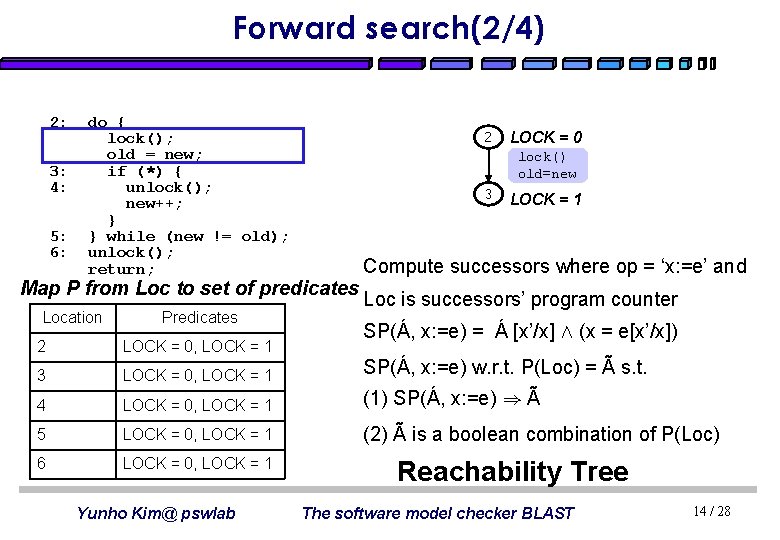
Forward search(2/4) 2: 3: 4: 5: 6: do { lock(); old = new; if (*) { unlock(); new++; } } while (new != old); unlock(); return; 2 lock() old=new 3 Map P from Loc to set of predicates Location Predicates LOCK = 0 LOCK = 1 Compute successors where op = ‘x: =e’ and Loc is successors’ program counter SP(Á, x: =e) = Á [x’/x] Æ (x = e[x’/x]) 2 LOCK = 0, LOCK = 1 3 LOCK = 0, LOCK = 1 SP(Á, x: =e) w. r. t. P(Loc) = Ã s. t. 4 LOCK = 0, LOCK = 1 (1) SP(Á, x: =e) ) Ã 5 LOCK = 0, LOCK = 1 (2) Ã is a boolean combination of P(Loc) 6 LOCK = 0, LOCK = 1 Yunho Kim@ pswlab Reachability Tree The software model checker BLAST 14 / 28

Forward search(3/4) 2: 3: 4: 5: 6: do { lock(); old = new; if (*) { unlock(); new++; } } while (new != old); unlock(); return; 2 LOCK = 0 lock() old=new [T] 4 3 LOCK = 1 Compute successors where op = ‘[pred]’ and Map P from Loc to set of predicates Loc is successors’ program counter Location Predicates 2 LOCK = 0, LOCK = 1 SP(Á, [pred]) = Á Æ [pred] 3 LOCK = 0, LOCK = 1 SP(Á, [pred]) w. r. t. P(Loc) = Ã s. t. 4 LOCK = 0, LOCK = 1 (1) SP(Á, [pred]) ) Ã 5 LOCK = 0, LOCK = 1 (2) Ã is a boolean combination of P(Loc) 6 LOCK = 0, LOCK = 1 Yunho Kim@ pswlab Reachability Tree The software model checker BLAST 15 / 28

Forward search(4/4) 2: 3: 4: 5: 6: do { lock(); old = new; if (*) { unlock(); new++; } } while (new != old); unlock(); return; 2 lock() old=new [T] 4 Map P from Loc to set of predicates Location Predicates 2 LOCK = 0, LOCK = 1 3 LOCK = 0, LOCK = 1 4 LOCK = 0, LOCK = 1 5 LOCK = 0, LOCK = 1 6 LOCK = 0, LOCK = 1 Yunho Kim@ pswlab LOCK = 0 5 3 LOCK = 1 Counterexample trace 1: assume(true); 2: lock = 1; LOCK = 1 old = new; unlock() new++ 3: assume(true); LOCK = 0 4: lock = 0; new++; [new==old] 6 LOCK = 0 5: assume(new==old); unlock() 6: assume(LOCK!=1); err Reachability Tree The software model checker BLAST 16 / 28
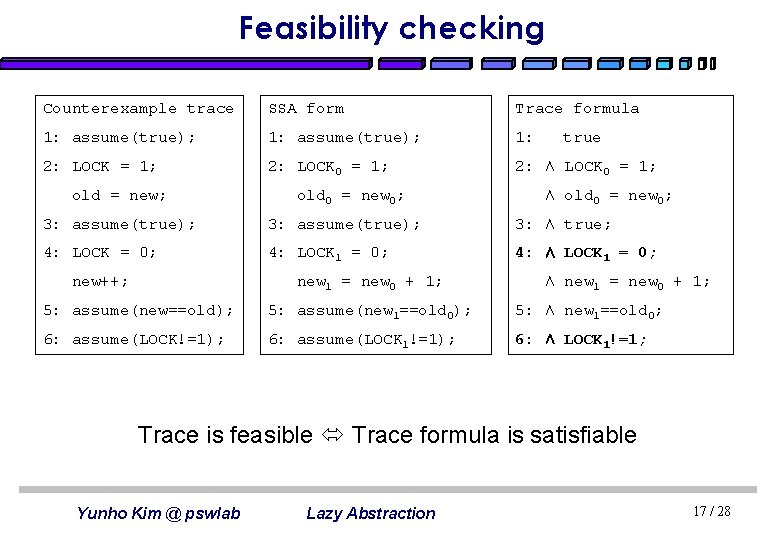
Feasibility checking Counterexample trace SSA form Trace formula 1: assume(true); 1: 2: LOCK = 1; 2: LOCK 0 = 1; 2: Æ LOCK 0 = 1; old = new; old 0 = new 0; true Æ old 0 = new 0; 3: assume(true); 3: Æ true; 4: LOCK = 0; 4: LOCK 1 = 0; 4: Æ LOCK 1 = 0; new++; new 1 = new 0 + 1; Æ new 1 = new 0 + 1; 5: assume(new==old); 5: assume(new 1==old 0); 5: Æ new 1==old 0; 6: assume(LOCK!=1); 6: assume(LOCK 1!=1); 6: Æ LOCK 1!=1; Trace is feasible Trace formula is satisfiable Yunho Kim @ pswlab Lazy Abstraction 17 / 28
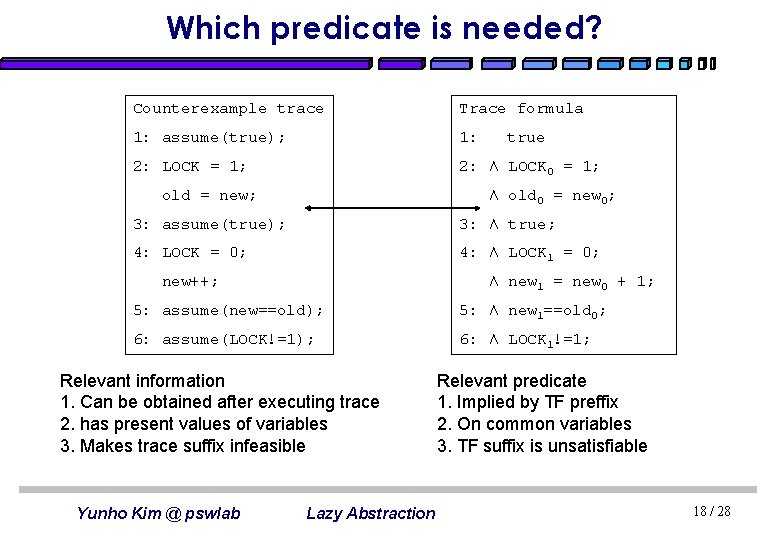
Which predicate is needed? Counterexample trace Trace formula 1: assume(true); 1: 2: LOCK = 1; 2: Æ LOCK 0 = 1; old = new; true Æ old 0 = new 0; 3: assume(true); 3: Æ true; 4: LOCK = 0; 4: Æ LOCK 1 = 0; new++; Æ new 1 = new 0 + 1; 5: assume(new==old); 5: Æ new 1==old 0; 6: assume(LOCK!=1); 6: Æ LOCK 1!=1; Relevant information 1. Can be obtained after executing trace 2. has present values of variables 3. Makes trace suffix infeasible Yunho Kim @ pswlab Lazy Abstraction Relevant predicate 1. Implied by TF preffix 2. On common variables 3. TF suffix is unsatisfiable 18 / 28
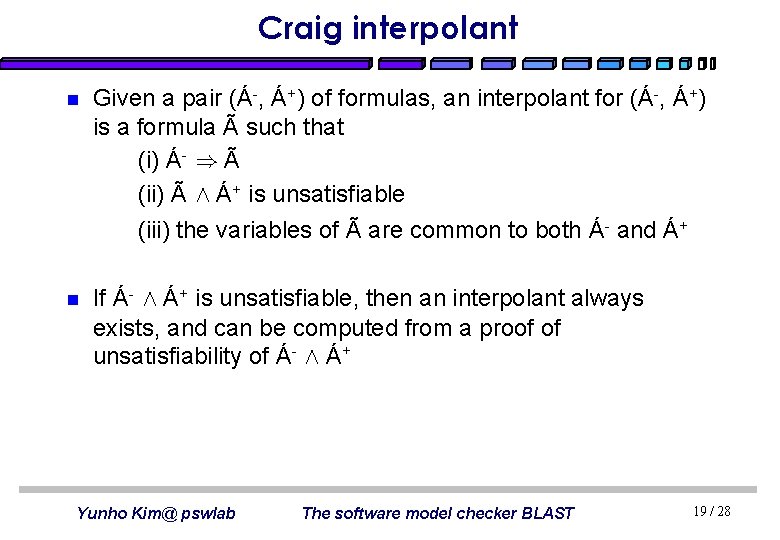
Craig interpolant n Given a pair (Á-, Á+) of formulas, an interpolant for (Á-, Á+) is a formula à such that (i) Á- ) à (ii) Ã Æ Á+ is unsatisfiable (iii) the variables of à are common to both Á- and Á+ n If Á- Æ Á+ is unsatisfiable, then an interpolant always exists, and can be computed from a proof of unsatisfiability of Á- Æ Á+ Yunho Kim@ pswlab The software model checker BLAST 19 / 28
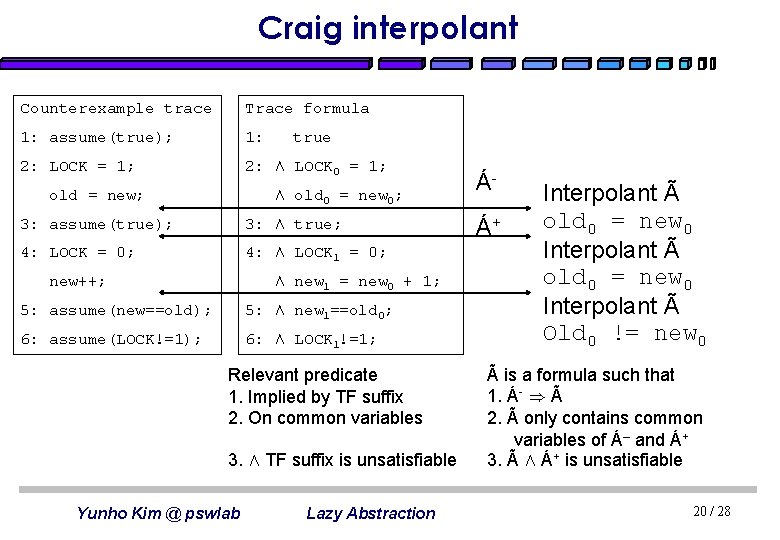
Craig interpolant Counterexample trace Trace formula 1: assume(true); 1: 2: LOCK = 1; 2: Æ LOCK 0 = 1; old = new; true Æ old 0 = new 0; 3: assume(true); 3: Æ true; 4: LOCK = 0; 4: Æ LOCK 1 = 0; new++; Æ new 1 = new 0 + 1; 5: assume(new==old); 5: Æ new 1==old 0; 6: assume(LOCK!=1); 6: Æ LOCK 1!=1; Relevant predicate 1. Implied by TF suffix 2. On common variables 3. Æ TF suffix is unsatisfiable Yunho Kim @ pswlab Lazy Abstraction ÁÁ+ Interpolant à old 0 = new 0 Interpolant à Old 0 != new 0 à is a formula such that 1. Á- ) à 2. à only contains common variables of Á– and Á+ 3. Ã Æ Á+ is unsatisfiable 20 / 28
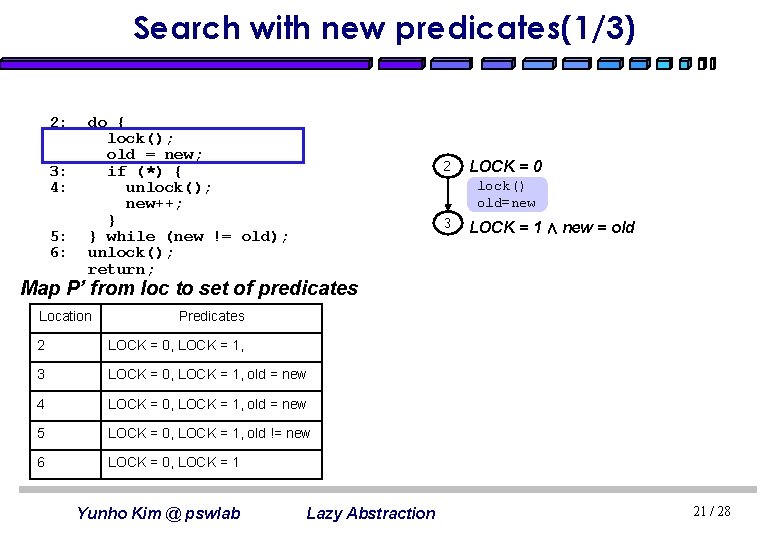
Search with new predicates(1/3) 2: 3: 4: 5: 6: do { lock(); old = new; if (*) { unlock(); new++; } } while (new != old); unlock(); return; 2 LOCK = 0 lock() old=new 3 LOCK = 1 Æ new = old Map P’ from loc to set of predicates Location Predicates 2 LOCK = 0, LOCK = 1, 3 LOCK = 0, LOCK = 1, old = new 4 LOCK = 0, LOCK = 1, old = new 5 LOCK = 0, LOCK = 1, old != new 6 LOCK = 0, LOCK = 1 Yunho Kim @ pswlab Lazy Abstraction 21 / 28
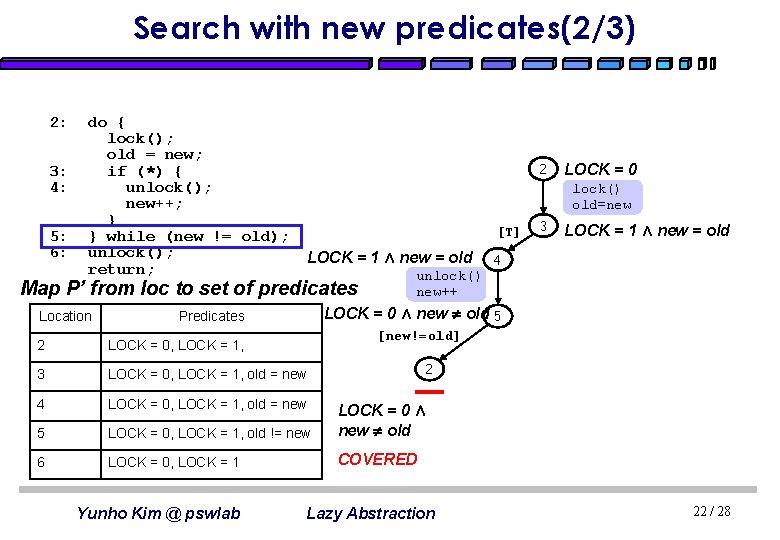
Search with new predicates(2/3) 2: 3: 4: 5: 6: do { lock(); old = new; if (*) { unlock(); new++; } } while (new != old); unlock(); return; 2 lock() old=new [T] LOCK = 1 Æ new = old Map P’ from loc to set of predicates Location 3 LOCK = 1 Æ new = old 4 unlock() new++ LOCK = 0 Æ new old 5 Predicates [new!=old] 2 LOCK = 0, LOCK = 1, 3 LOCK = 0, LOCK = 1, old = new 4 LOCK = 0, LOCK = 1, old = new 5 LOCK = 0, LOCK = 1, old != new LOCK = 0 Æ new old 6 LOCK = 0, LOCK = 1 COVERED Yunho Kim @ pswlab LOCK = 0 2 Lazy Abstraction 22 / 28
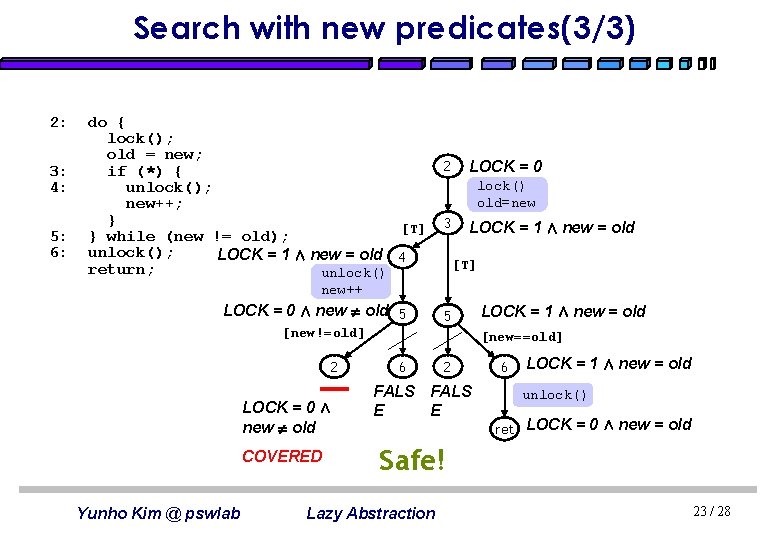
Search with new predicates(3/3) 2: 3: 4: 5: 6: do { lock(); old = new; if (*) { unlock(); new++; } [T] } while (new != old); unlock(); LOCK = 1 Æ new = old 4 return; unlock() 2 LOCK = 0 lock() old=new 3 LOCK = 1 Æ new = old [T] new++ LOCK = 0 Æ new old 5 5 [new!=old] 2 LOCK = 0 Æ new old COVERED Yunho Kim @ pswlab LOCK = 1 Æ new = old [new==old] 6 2 FALS E E 6 LOCK = 1 Æ new = old unlock() ret LOCK = 0 Æ new = old Safe! Lazy Abstraction 23 / 28
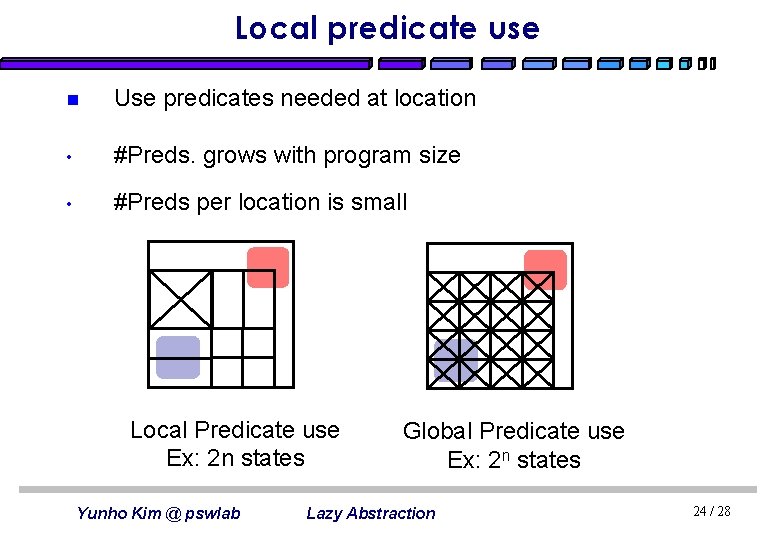
Local predicate use n Use predicates needed at location • #Preds. grows with program size • #Preds per location is small Local Predicate use Ex: 2 n states Yunho Kim @ pswlab Global Predicate use Ex: 2 n states Lazy Abstraction 24 / 28

Experiments n n n funlock. c is an example we covered driver. c is a Windows driver for verifying locking discipline read. c, floppy. c are drivers from Windows DDK qpmouse. c and llrw_block. c are drivers from Linux Experiments ran on 800 MHz PIII with 256 M RAM Yunho Kim @ pswlab Lazy Abstraction 25 / 28

Conclusions n BLAST is a software model checker for verifying program written in C language n BLAST improves the scheme of CEGAR by implementing lazy abstraction l l avoids redundant abstraction and checking Predicates are locally applied and states are locally abstracted Yunho Kim @ pswlab Lazy Abstraction 26 / 28
Reference n n n The Software Model Checker Blast: Applications to Software Engineering. by Dirk Beyer, Thomas A. Henzinger, Ranjit Jhala, and Rupak Majumdar in Int. Journal on Software Tools for Technology Transfer, 2007 Lazy abstraction by Thomas A. Henzinger, Ranjit Jhala, Rupak Majumdar, and Grégoire Sutre in ACM SIGPLAN – SIGACT Conference on Principle Of Programming Language 2000 Abstractions from Proofs by Thomas A. Henzinger, Ranjit Jhala, Rupak Majumdar and Kenneth L. Mc. Millan in ACM SIGPLAN-SIGACT Conference on Principles of Programming Languages, 2004 Yunho Kim @ pswlab Lazy Abstraction 27 / 28
Reference n n Lazy Abstraction slides by Jinseong Jeon in CS 750 class, Fall, 2006 Software Verification with BLAST slides by Tom Henzinger, Ranjit , Rupak Majumdar in SPIN workshop 2005 tutoria Á Ã Yunho Kim @ pswlab Lazy Abstraction 28 / 28

Control Flow Automata for C programs 1 Example(){ 2 do{ 3 if (LOCK == 0) 4 LOCK=1; 5 else 6 ERROR: 7 old = new; 8 if (*){ 9 if (LOCK == 1) 10 LOCK = 0; 11 else 12 ERROR: 13 new++; 14 } 15 }while (new != old); 16 if (LOCK == 1) 17 LOCK = 0; 18 else 19 ERROR: 20 return; 21 } Yunho Kim@ pswlab [LOCK == 0] 3 [LOCK != 0] 4 6 LOCK=1 Skip 7 old = new 8 [TRUE] [LOCK == 1] 9 10 LOCK=0 [new != old] [TRUE] [LOCK != 1] 12 13 [LOCK == 1] Skip 16[LOCK != 1] 17 19 LOCK=0 20 15 Skip return ret [new == old] n n Node corresponds to control location Edge corresponds to either a basic block or an assume predicate The software model checker BLAST 29 / 28
- Slides: 29