The Socialbot Network When Bots Socialize for Fame
The Socialbot Network: When Bots Socialize for Fame and Money Authors: Yazan Boshmaf, Lldar Muslukhov, Konstantin Beznosov, Matei Ripeanu University of British Columbia Annual Computer Security Applications Conference (ACSAC) 2011 Presented By: Gavin Grant
Acknowledgement �http: //en. wikipedia. org/wiki/CAPTCHA �http: //developers. facebook. com/docs/reference/api/
Overview �Abstract �OSN Vulnerabilities �Socialbot Network �The Attack �Findings �FIS effectiveness
Abstract �Social Networks have millions of users �Illustrate that Online Social Networks (OSN) are vulnerable to infiltrations by socialbots � In particular Facebook � 80% success rate �Socialbots – computer programs that control OSN accounts and mimic real users

OSN Vulnerabilities �Ineffective CAPTCHAs �Hiring cheap labor ($1 per 1, 000 broken) �Reusing session IDs of known CAPTCHAs �Fake User Accounts and Profiles �Email and profile �Crawlable Social Graphs �Traversing linked profiles �Exploitable Platforms and APIs �Use APIs to automate the execution of activities
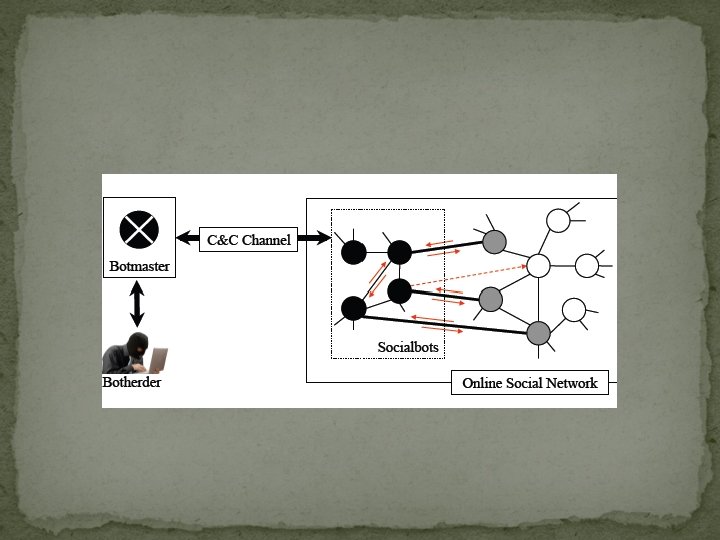
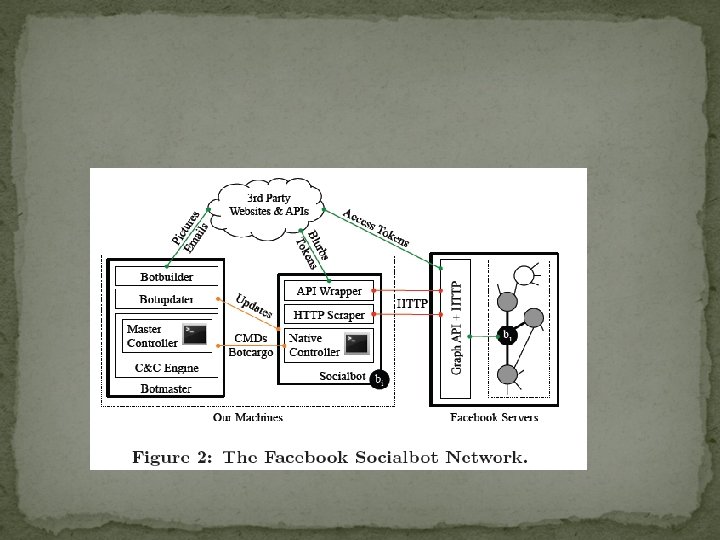
Socialbot Network �Set of socialbots owned and maintained by human controller called the botherder �Made up of socialbots, botmaster, and command control channel �Socialbot controls a profile �Data collected called botcargo �Capable of executing commands �Botmaster is software botherder uses to send commands through C & C channel �C & C facilitates transfer of botcargo and commands
Socialbots �Read, write, connect, disconnect �Set of commands used to mimic a real user �Native commands �Master commands
Botmaster �Botworker builds and maintains profiles �Botupdater pushes new software updates �C & C engine maintains a repository of master commands �Master commands needed �Cluster �Rand_connect(k) �Decluster �Crawl_extneighborhood �Mutual_connect �Harvest-data
C & C Channel �Communication model �Works with socialbot-OSN Channel �Only OSN-specific API calls and HTTP traffic �Helps in non detection
Effective Sb. N �Socialbot has to hide its real identity �Botmaster should be able to perform large-scale infiltration �C & C channel traffic has to look benign
The Attack �Facebook Immune System (FIS) � 8 week process �Exploited Facebook’s Graph API to carry out social- interaction operations �Used HTTP request to send friendship request �Iheartquotes. com, decaptcher. com, hotornot. com, mail. ru
Facebook Sb. N � 102 socialbots created and 1 botmaster �Users were created manually � 49 males � 53 females � 5053 valid profile IDs � 25 request per day per socialbot �Harvested data
Findings �First 2 weeks � 2 days t send 5043 request (2, 391 male , 2. 662 female) � 976 accepted (381 M, 595 F) �Next 6 weeks � 3, 517 more users added � 2, 079 infiltrated successfully �Generated 250 GB inbound and 3 GB outbound traffic �Acceptance rate increase to 80% as mutual friends increased
Data Harvested �News feeds �Profile info �Wall messages � 3, 055 direct neighborhoods � 1, 085, 785 extended neighborhoods
Facebook Immune System �Real time learning system used to protect its users �Only 20 bots were flagged by system �Doesn’t consider fake accounts a real threat
Contribution �OSN vulnerability to a large-scale socialbot network infiltration �Defense social networks have against social bots that mimic human behavior �Prayed on common user behavior
Weaknesses �Only Facebook was attacked �Didn’t provide any prevention techniques
Improvement �Try on other social networking sites �Not create socialbots manually
Questions
- Slides: 21