THE ORANGE BOOK Ravi Sandhu 4 03 1
THE ORANGE BOOK Ravi Sandhu 4 -03 1
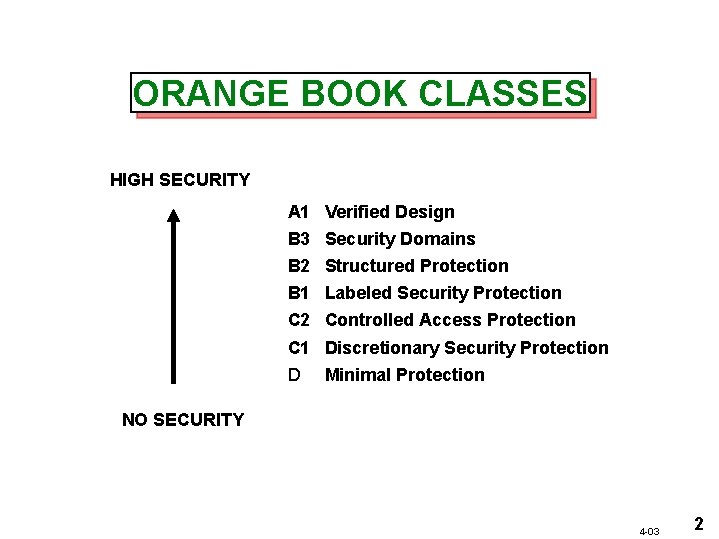
ORANGE BOOK CLASSES HIGH SECURITY A 1 Verified Design B 3 Security Domains B 2 Structured Protection B 1 Labeled Security Protection C 2 Controlled Access Protection C 1 Discretionary Security Protection D Minimal Protection NO SECURITY 4 -03 2
ORANGE BOOK CRITERIA SECURITY POLICY ACCOUNTABILITY ASSURANCE DOCUMENTATION 4 -03 3
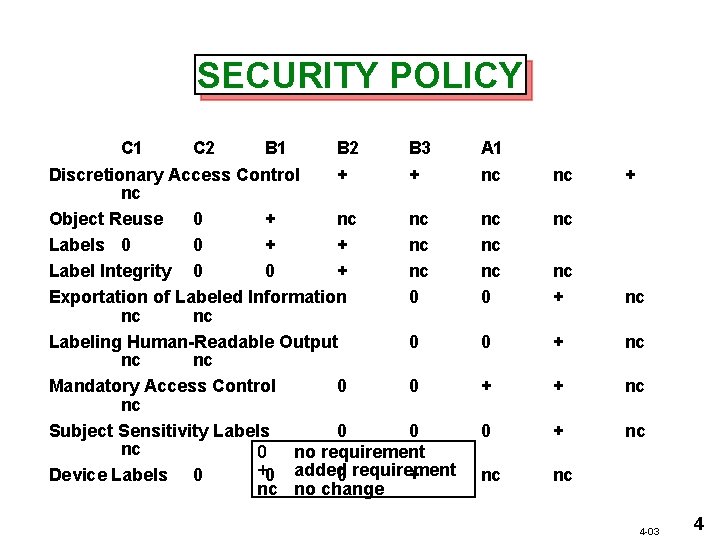
SECURITY POLICY C 1 C 2 B 1 B 2 B 3 Discretionary Access Control + + nc Object Reuse 0 + nc nc Labels 0 0 + + nc Label Integrity 0 0 + nc Exportation of Labeled Information 0 nc nc Labeling Human-Readable Output 0 nc nc Mandatory Access Control 0 0 nc Subject Sensitivity Labels 0 0 nc 0 no requirement +0 added Device Labels 0 0 requirement + nc no change A 1 nc nc + nc nc nc 0 nc nc + nc 0 + nc + + nc 0 + nc nc nc 4 -03 4
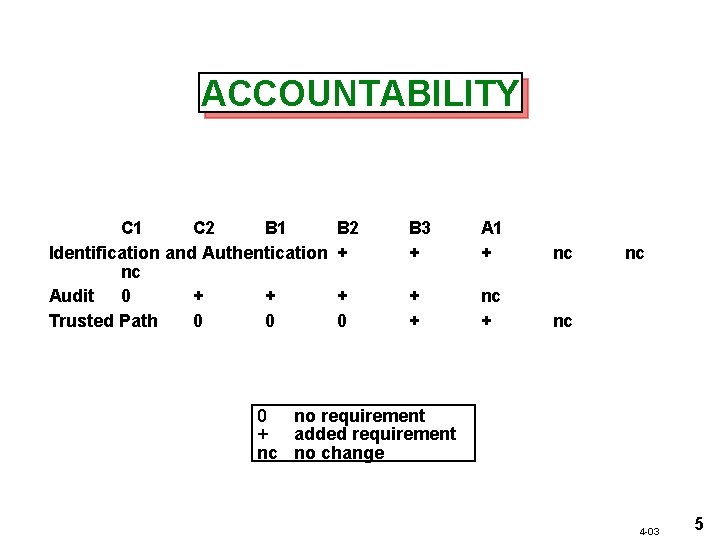
ACCOUNTABILITY C 1 C 2 B 1 Identification and Authentication nc Audit 0 + + Trusted Path 0 0 B 2 + B 3 + A 1 + nc + 0 + + nc nc 0 no requirement + added requirement nc no change 4 -03 5
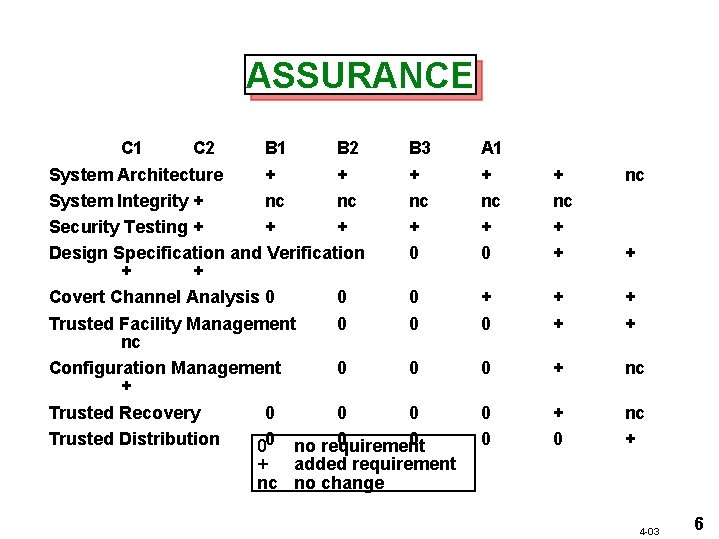
ASSURANCE C 1 C 2 B 1 B 2 B 3 System Architecture + + + System Integrity + nc nc nc Security Testing + + Design Specification and Verification 0 + + Covert Channel Analysis 0 0 0 Trusted Facility Management 0 0 nc Configuration Management 0 0 + Trusted Recovery 0 0 0 Trusted Distribution 0 0 00 no requirement + added requirement nc no change A 1 + nc + 0 + + 0 + nc 0 0 + 0 nc + + 4 -03 6
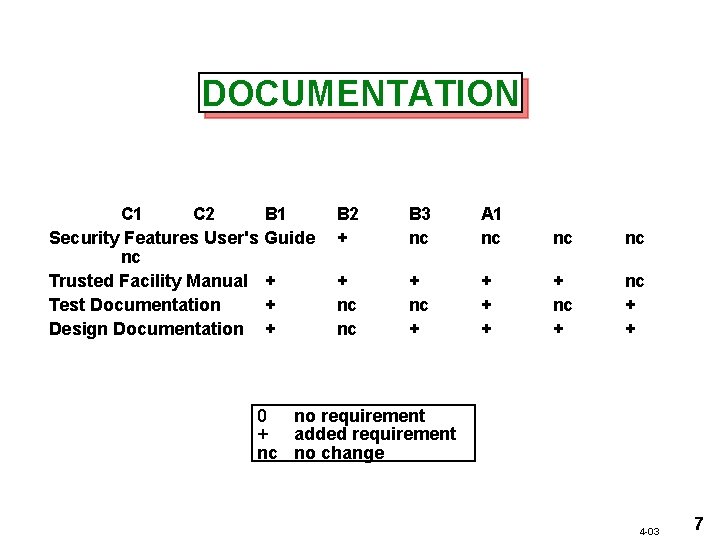
DOCUMENTATION C 1 C 2 B 1 Security Features User's Guide nc Trusted Facility Manual + Test Documentation + Design Documentation + B 2 + B 3 nc A 1 nc nc nc + + + nc + + 0 no requirement + added requirement nc no change 4 -03 7
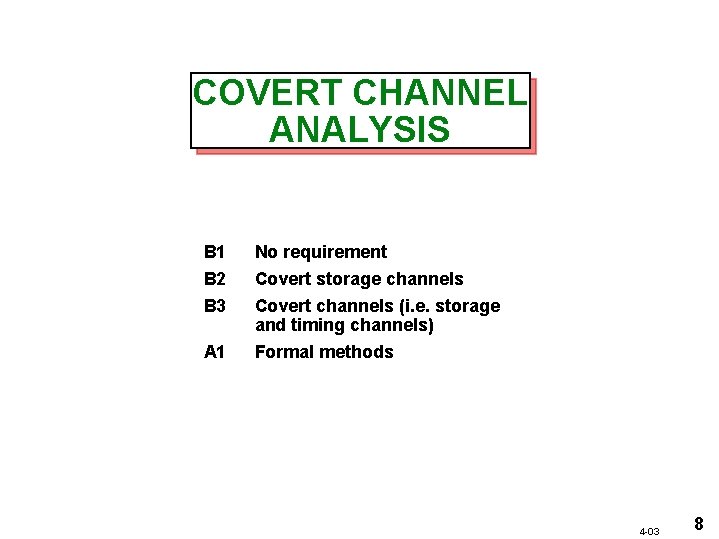
COVERT CHANNEL ANALYSIS B 1 No requirement B 2 Covert storage channels B 3 Covert channels (i. e. storage and timing channels) A 1 Formal methods 4 -03 8
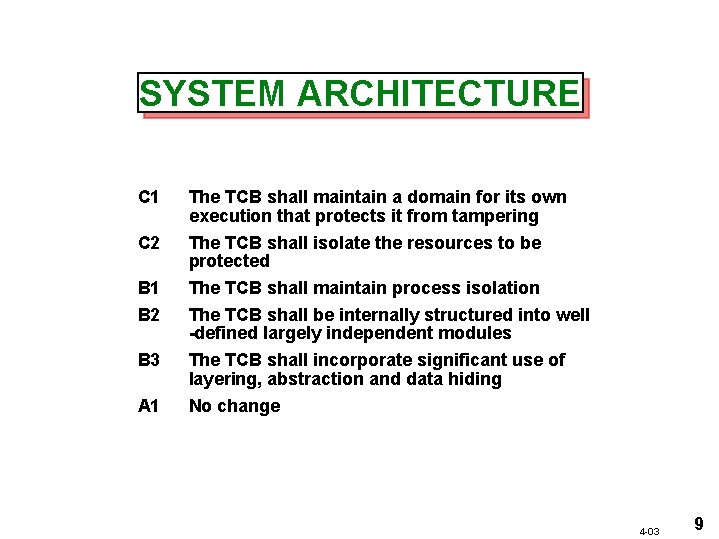
SYSTEM ARCHITECTURE C 1 C 2 B 1 B 2 B 3 A 1 The TCB shall maintain a domain for its own execution that protects it from tampering The TCB shall isolate the resources to be protected The TCB shall maintain process isolation The TCB shall be internally structured into well -defined largely independent modules The TCB shall incorporate significant use of layering, abstraction and data hiding No change 4 -03 9
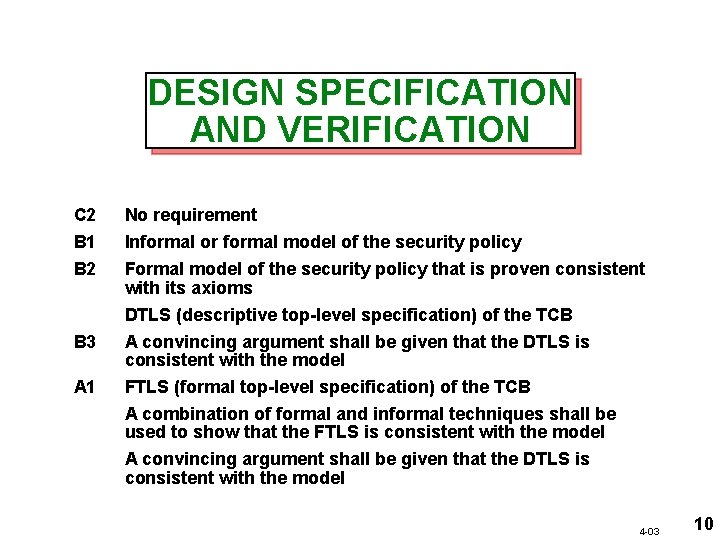
DESIGN SPECIFICATION AND VERIFICATION C 2 No requirement B 1 B 2 Informal or formal model of the security policy Formal model of the security policy that is proven consistent with its axioms DTLS (descriptive top-level specification) of the TCB A convincing argument shall be given that the DTLS is consistent with the model FTLS (formal top-level specification) of the TCB A combination of formal and informal techniques shall be used to show that the FTLS is consistent with the model B 3 A 1 A convincing argument shall be given that the DTLS is consistent with the model 4 -03 10
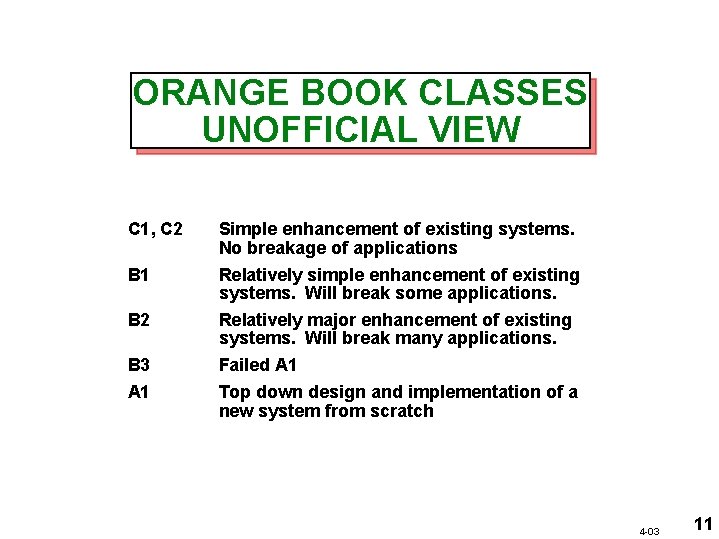
ORANGE BOOK CLASSES UNOFFICIAL VIEW C 1, C 2 B 1 B 2 B 3 A 1 Simple enhancement of existing systems. No breakage of applications Relatively simple enhancement of existing systems. Will break some applications. Relatively major enhancement of existing systems. Will break many applications. Failed A 1 Top down design and implementation of a new system from scratch 4 -03 11
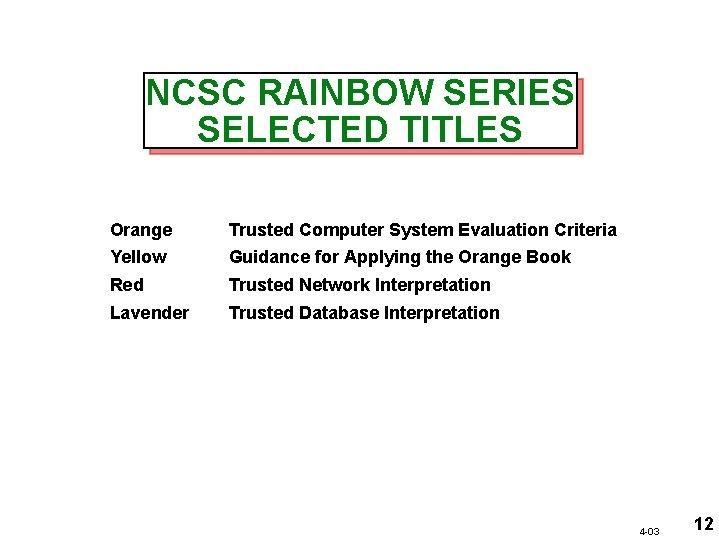
NCSC RAINBOW SERIES SELECTED TITLES Orange Trusted Computer System Evaluation Criteria Yellow Guidance for Applying the Orange Book Red Trusted Network Interpretation Lavender Trusted Database Interpretation 4 -03 12
ORANGE BOOK CRITICISMS • Mixes various levels of abstraction in a single document • • Does not address integrity of data Combines functionality and assurance in a single linear rating scale 4 -03 13
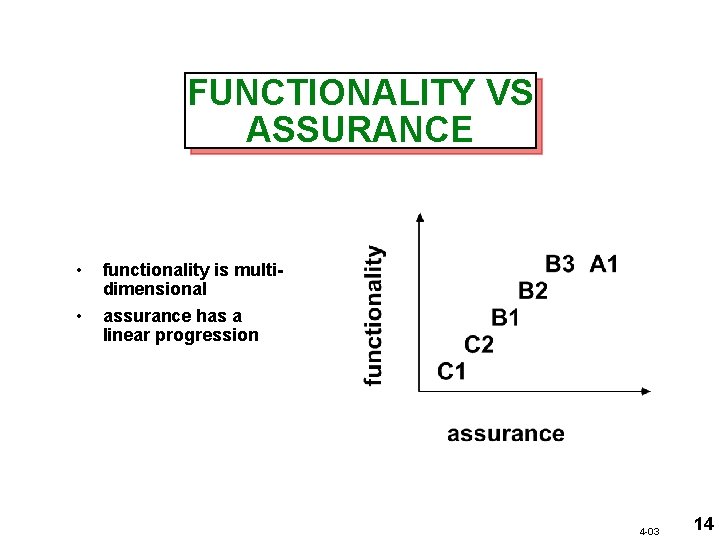
FUNCTIONALITY VS ASSURANCE • functionality is multidimensional • assurance has a linear progression 4 -03 14
- Slides: 14