The Network Layer 14 740 Fundamentals of Computer
- Slides: 49
The Network Layer 14 -740: Fundamentals of Computer Networks Credit: Bill Nace Material from Computer Networking: A Top Down Approach, 6 th edition. J. F. Kurose and K. W. Ross
traceroute • Network Layer • IP: Internet Protocol • IP Addressing • ICMP 14 -740: Spring 2018 2
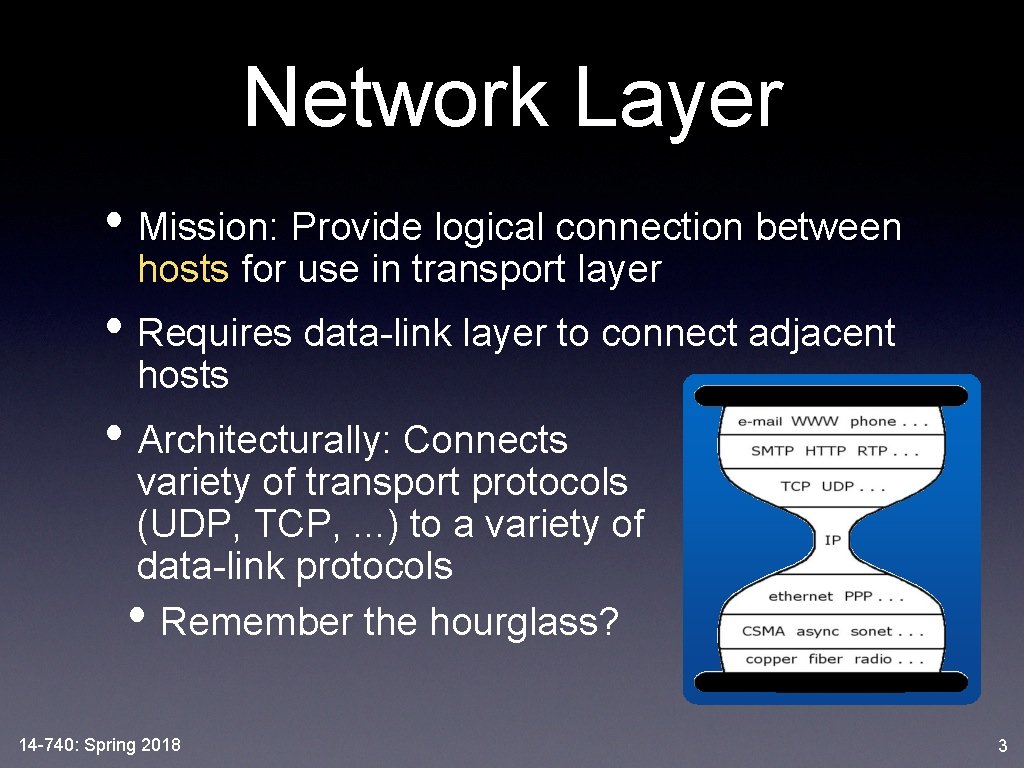
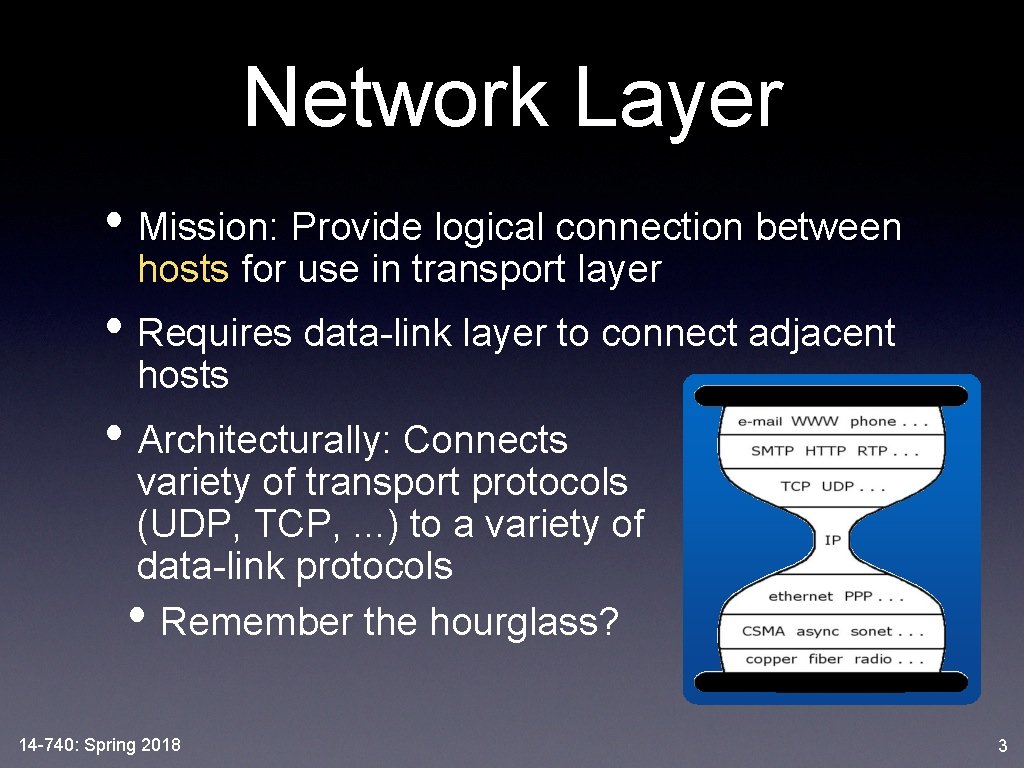
Network Layer • Mission: Provide logical connection between hosts for use in transport layer • Requires data-link layer to connect adjacent hosts • Architecturally: Connects variety of transport protocols (UDP, TCP, . . . ) to a variety of data-link protocols • Remember the hourglass? 14 -740: Spring 2018 3
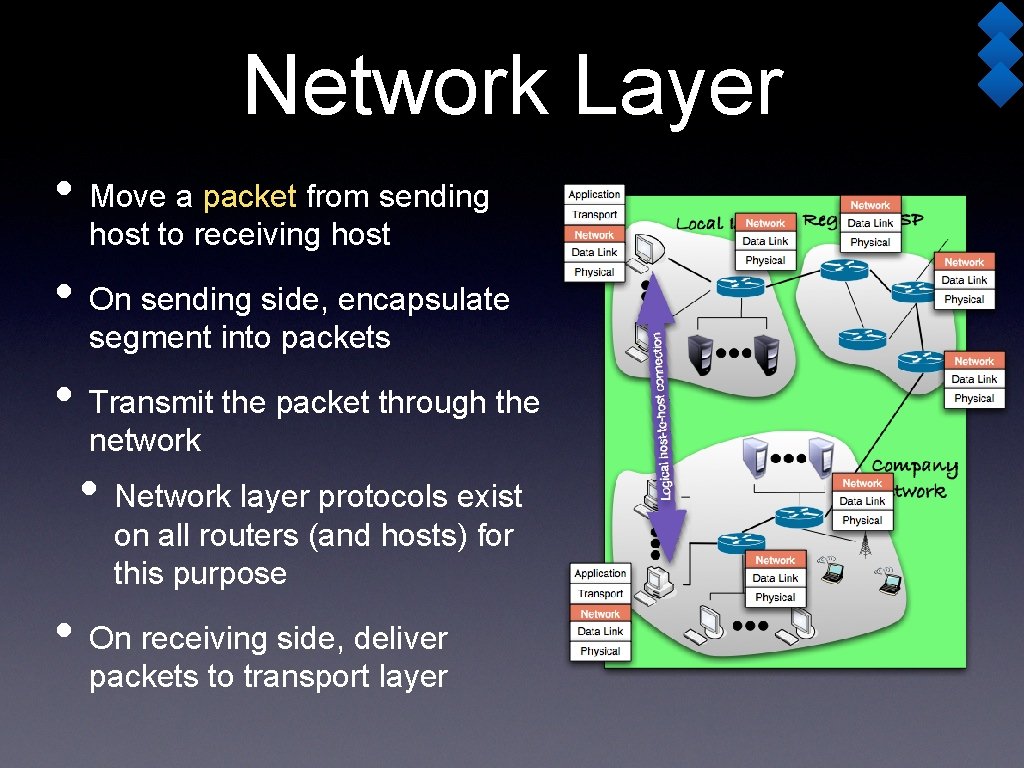
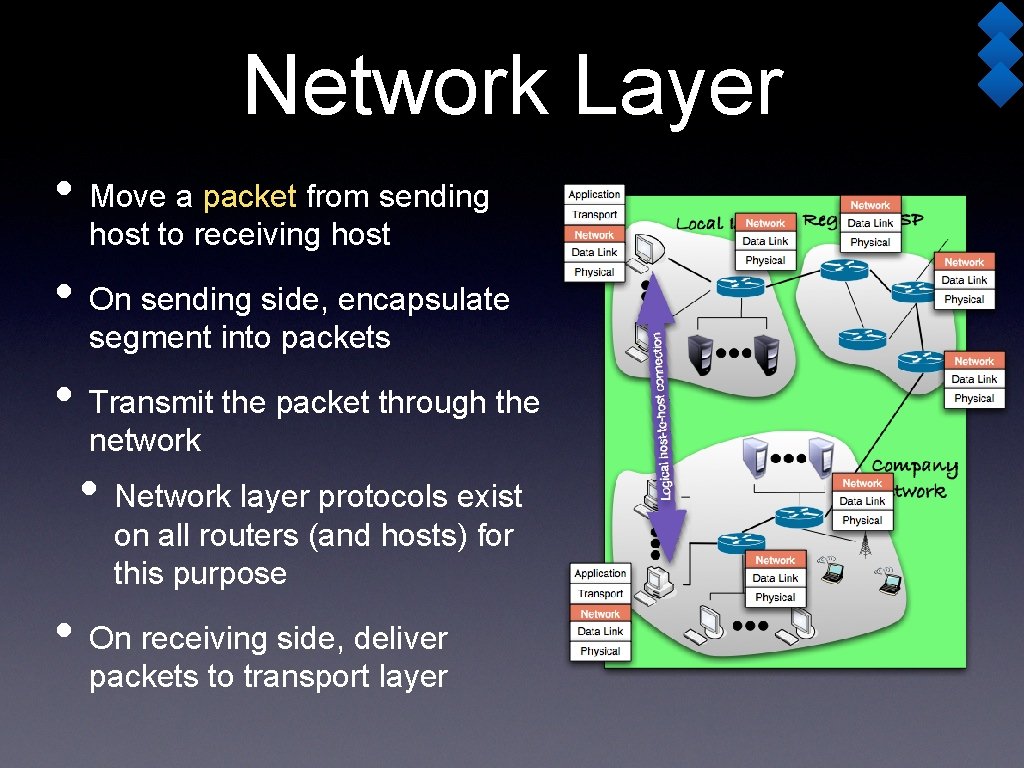
Network Layer • Move a packet from sending host to receiving host • On sending side, encapsulate segment into packets • Transmit the packet through the network • Network layer protocols exist on all routers (and hosts) for this purpose • On receiving side, deliver packets to transport layer
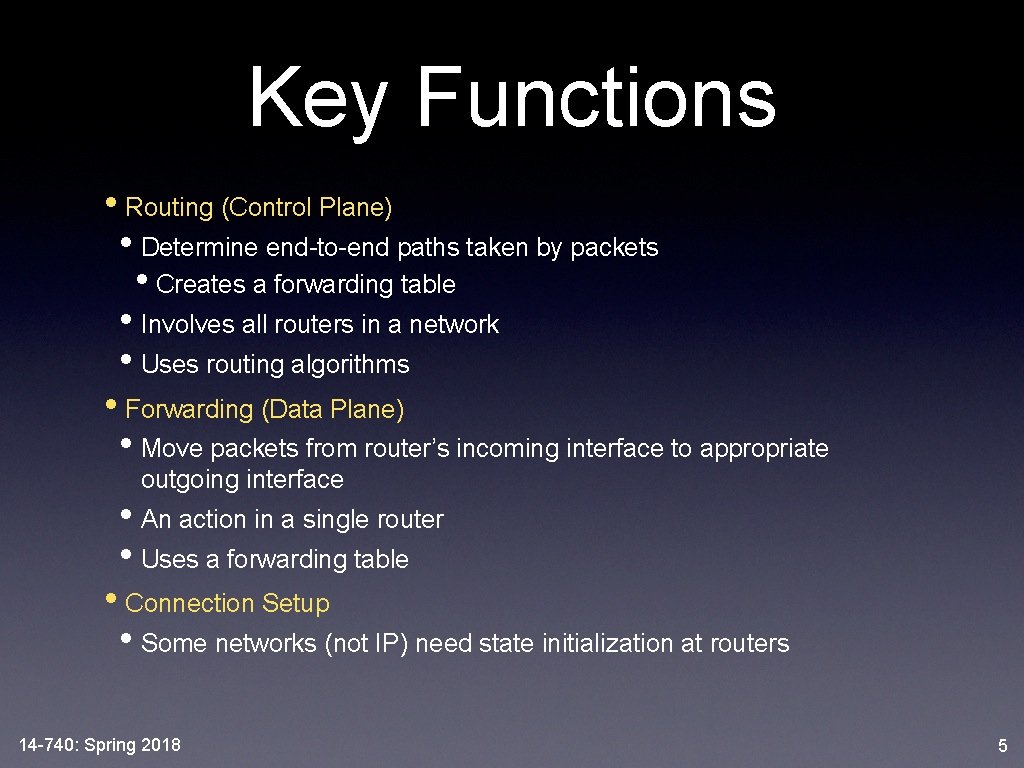
Key Functions • Routing (Control Plane) • Determine end-to-end paths taken by packets • Creates a forwarding table • Involves all routers in a network • Uses routing algorithms • Forwarding (Data Plane) • Move packets from router’s incoming interface to appropriate outgoing interface • An action in a single router • Uses a forwarding table • Connection Setup • Some networks (not IP) need state initialization at routers 14 -740: Spring 2018 5
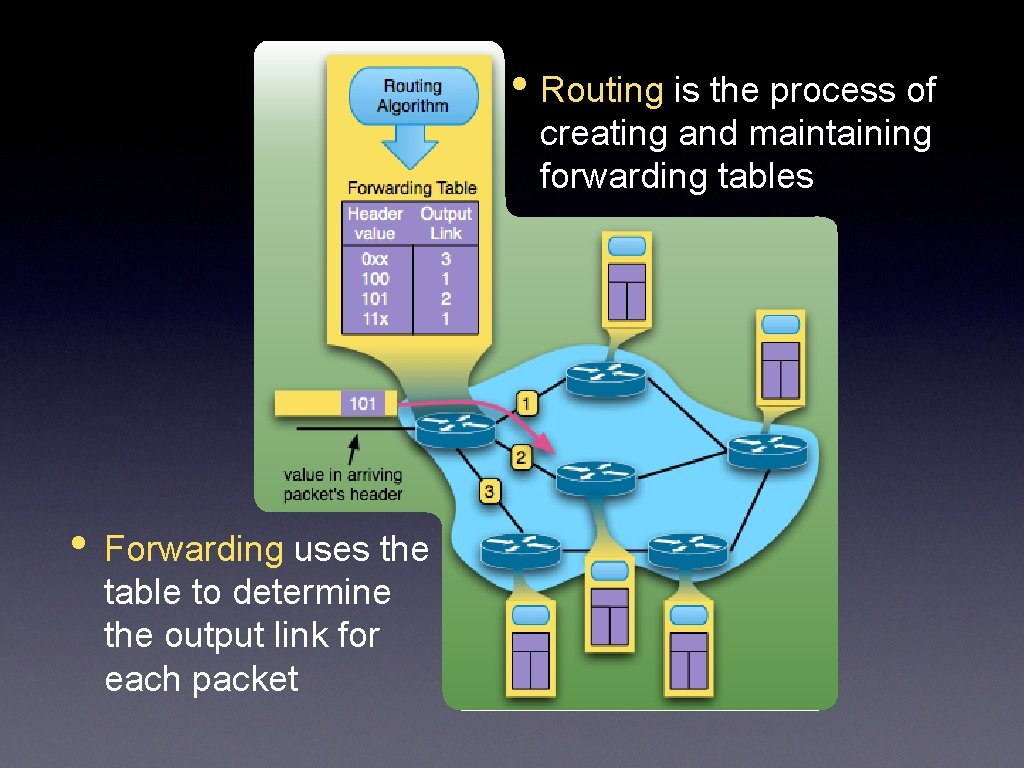
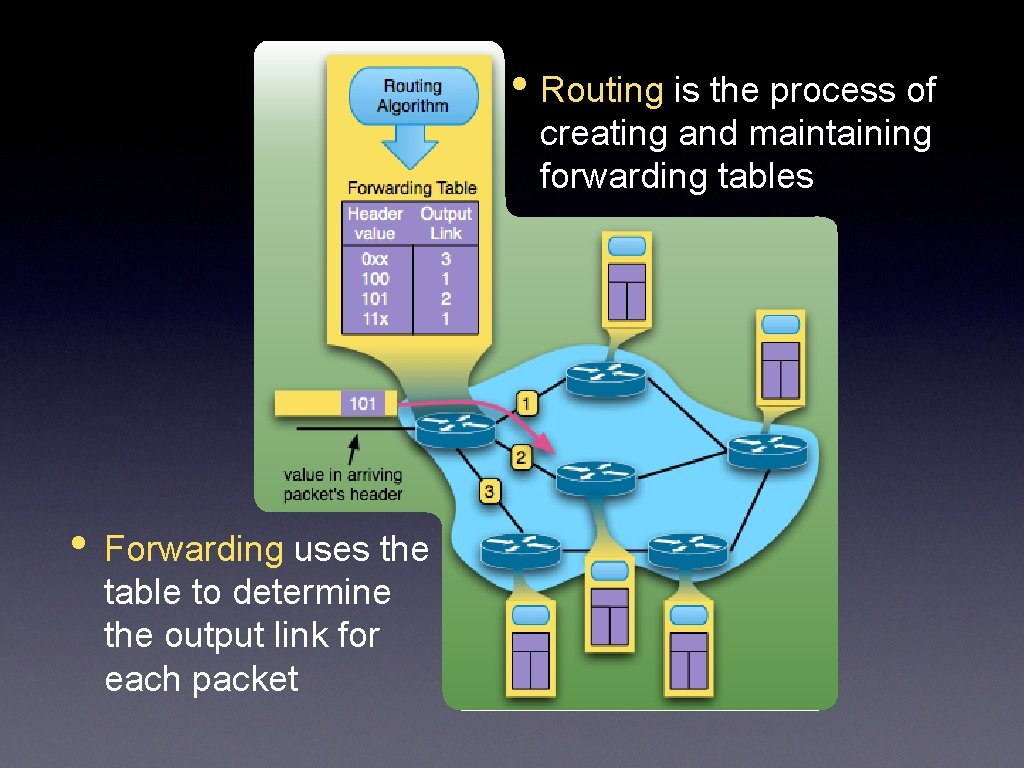
• Routing is the process of creating and maintaining forwarding tables • Forwarding uses the table to determine the output link for each packet
Network Connections? • Network Layer can be: • Connectionless (Datagram, Packet Switched) • Connection-oriented (Circuit Switched) • Fundamentally different from Transport-layer • which was app-to-app, not host-to-host • which was implemented in the end hosts • not in the routers • One or the other -- not a service choice 14 -740: Spring 2018 7
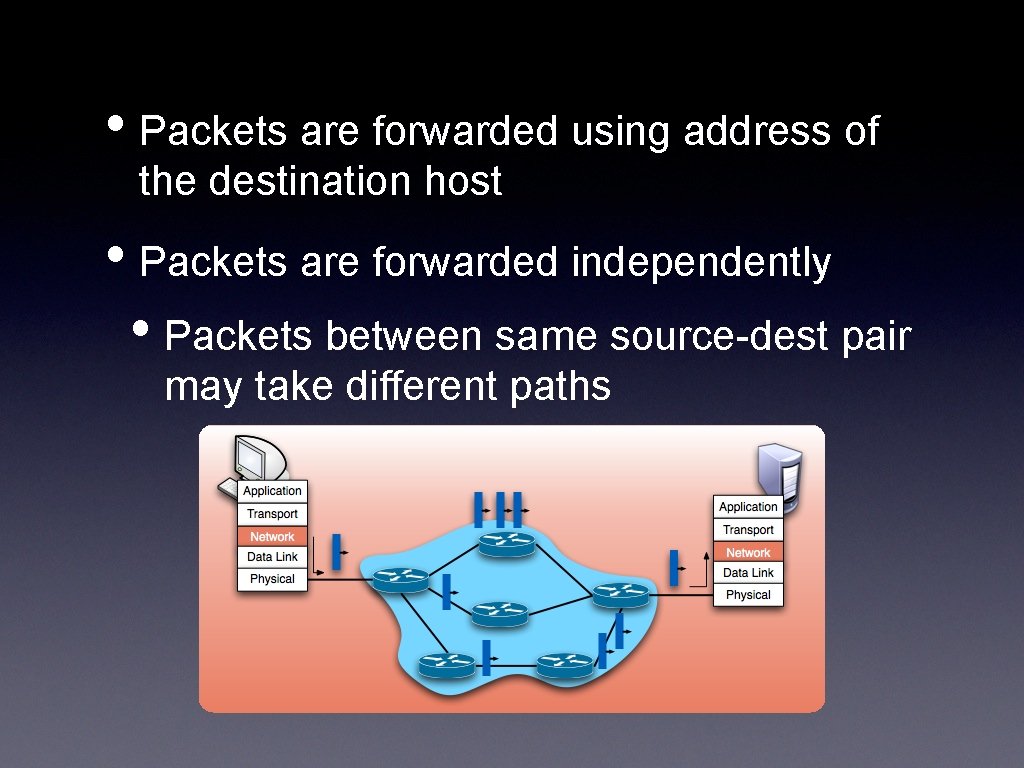
Datagram Networks • Commonly called “Packet-switched” • No call setup at network layer • routers hold no state about connections • no network-level concept of “connection” 14 -740: Spring 2018 8
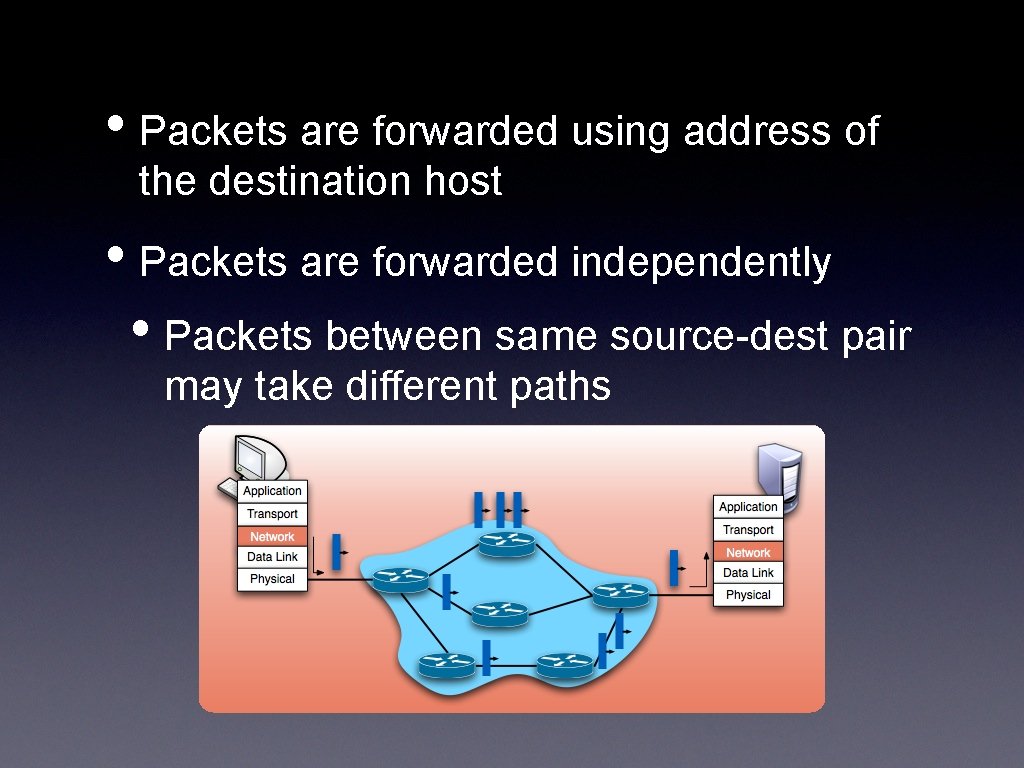
• Packets are forwarded using address of the destination host • Packets are forwarded independently • Packets between same source-dest pair may take different paths
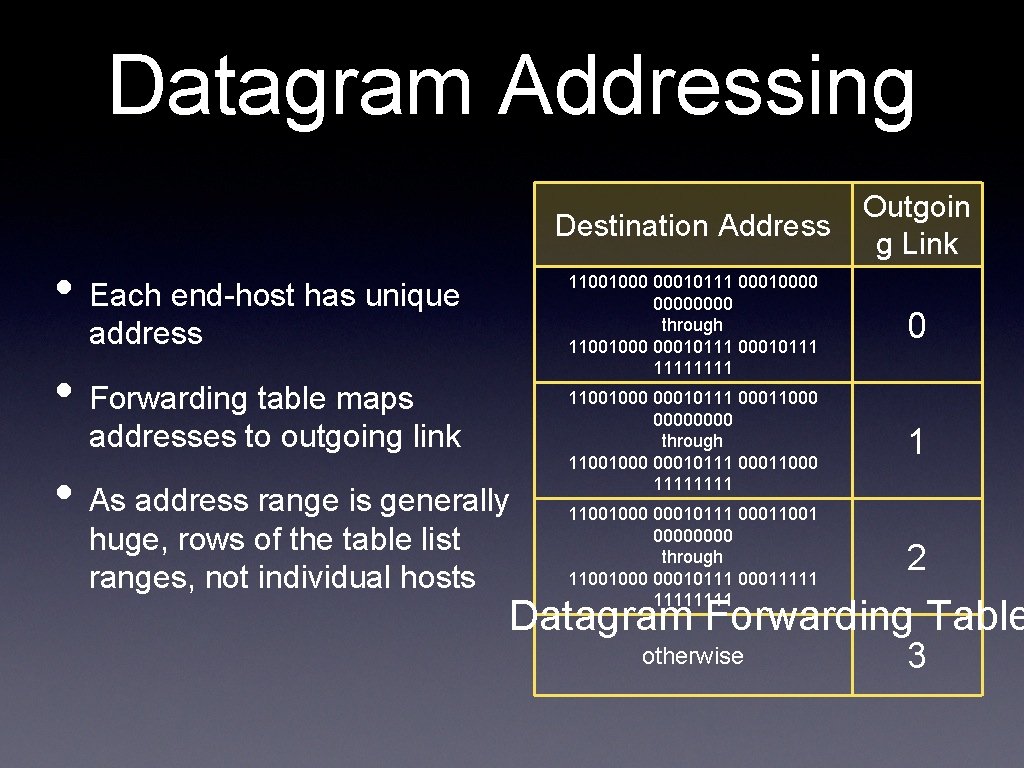
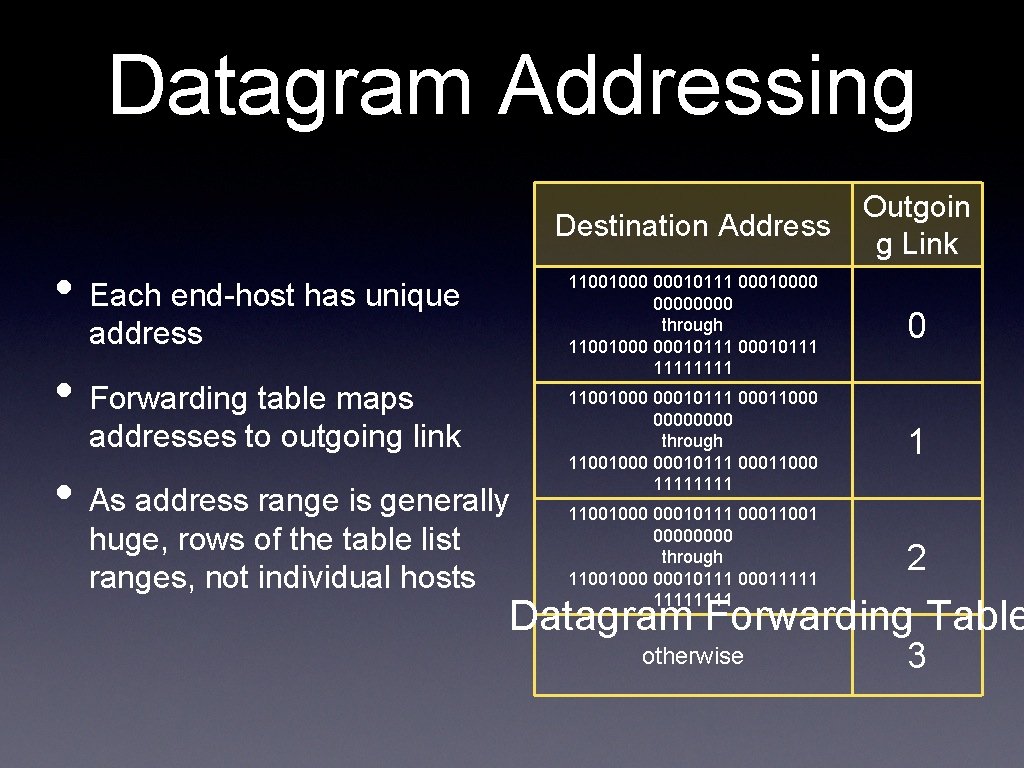
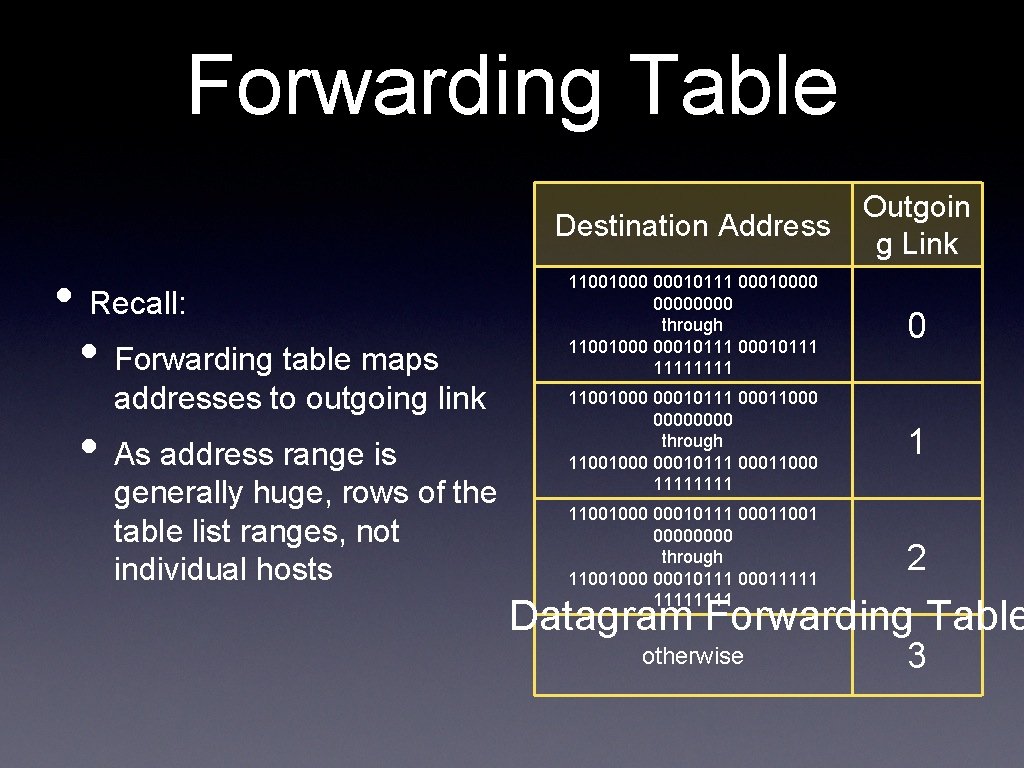
Datagram Addressing • Each end-host has unique address • Forwarding table maps addresses to outgoing link • As address range is generally huge, rows of the table list ranges, not individual hosts Destination Address Outgoin g Link 11001000 00010111 00010000 through 11001000 00010111 1111 0 11001000 00010111 00011000 0000 through 11001000 00010111 00011000 1111 1 11001000 00010111 00011001 0000 through 11001000 00010111 00011111 2 otherwise 3 Datagram Forwarding Table
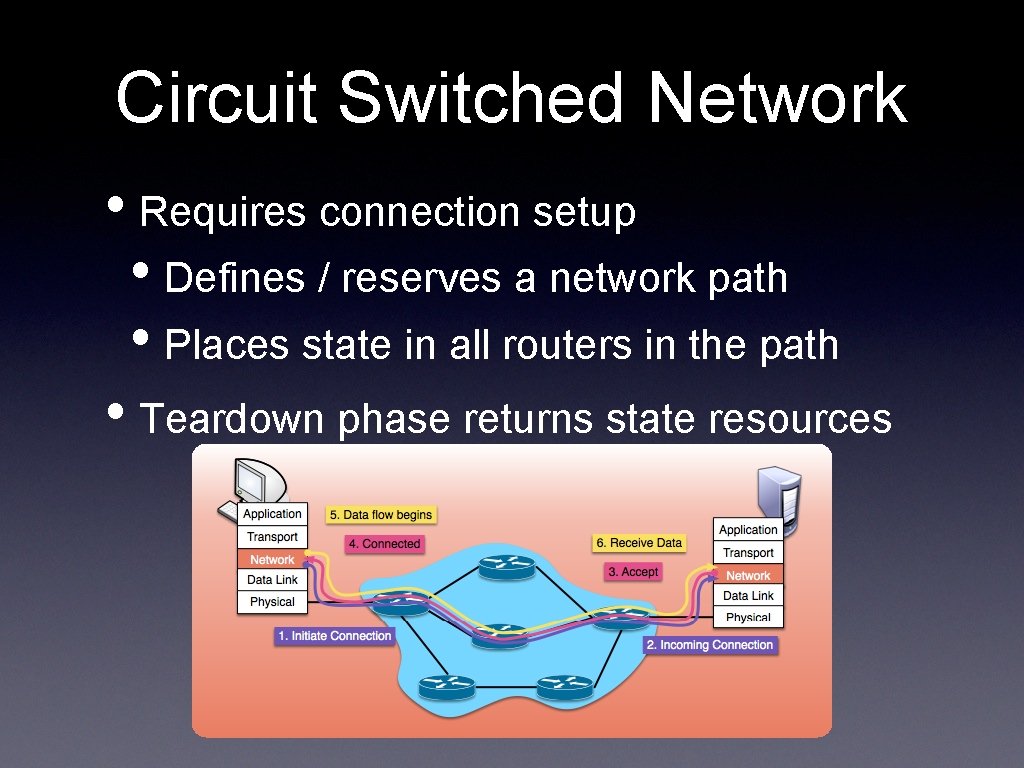
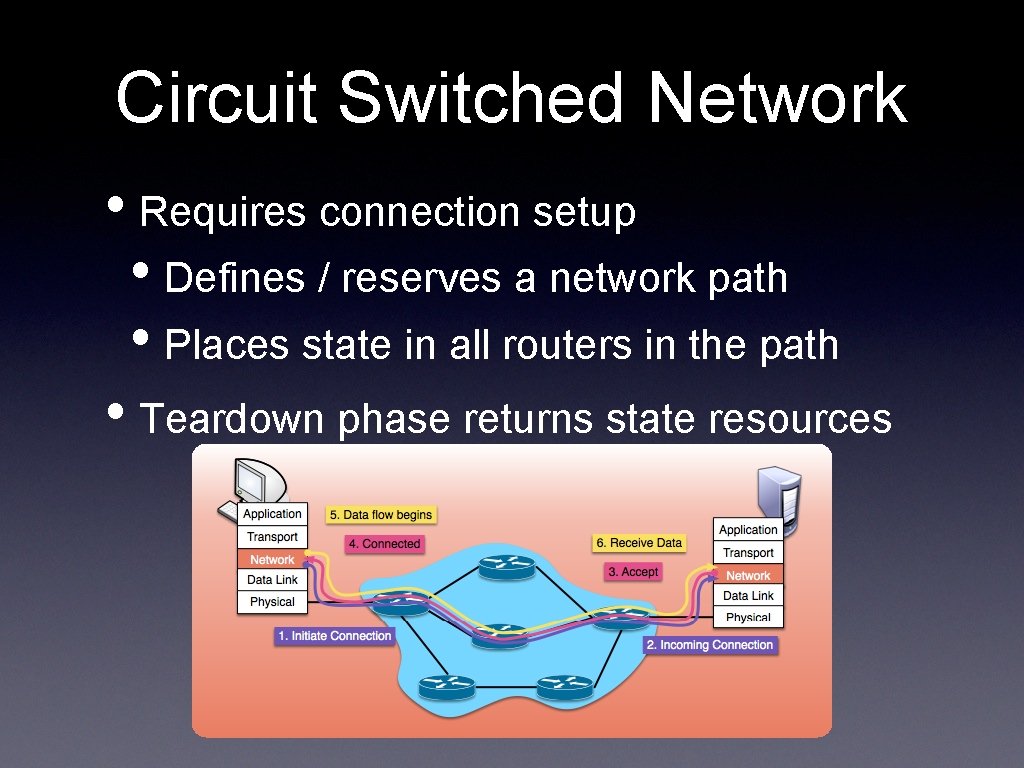
Circuit Switched Network • Requires connection setup • Defines / reserves a network path • Places state in all routers in the path • Teardown phase returns state resources
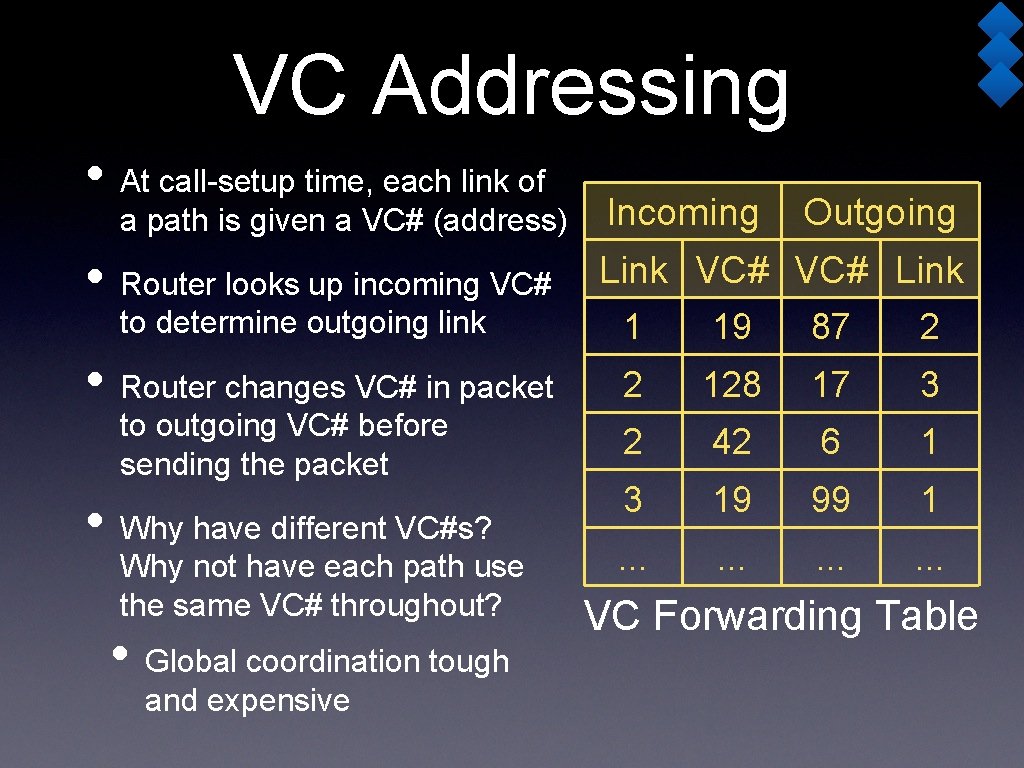
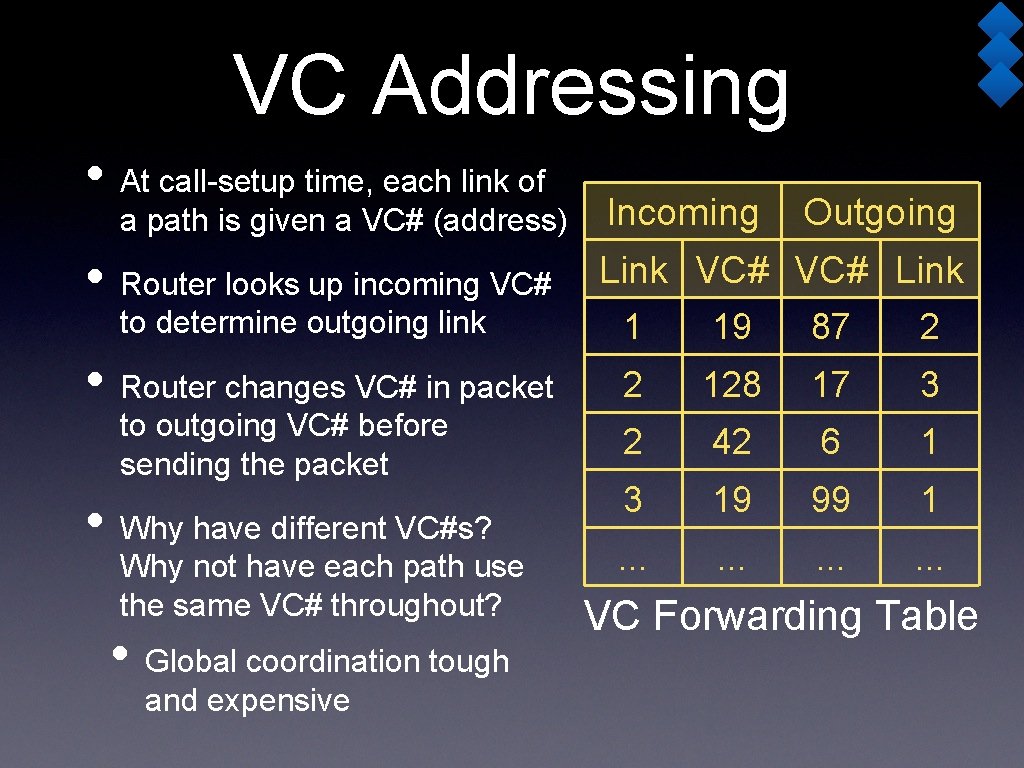
VC Addressing • At call-setup time, each link of a path is given a VC# (address) • Router looks up incoming VC# to determine outgoing link • Router changes VC# in packet to outgoing VC# before sending the packet • Why have different VC#s? Why not have each path use the same VC# throughout? • Global coordination tough and expensive Incoming Outgoing Link VC# Link 1 19 87 2 2 128 17 3 2 42 6 1 3 19 99 1 . . . VC Forwarding Table
traceroute • Network Layer • IP: Internet Protocol • IP Addressing • ICMP 14 -740: Spring 2018 14
IP Components • IP Protocol • Datagram format • Packet handling conventions • Addressing conventions • Routing Protocols • to fill Forwarding table • ICMP Protocol • Error reporting, router signaling 14 -740: Spring 2018 15
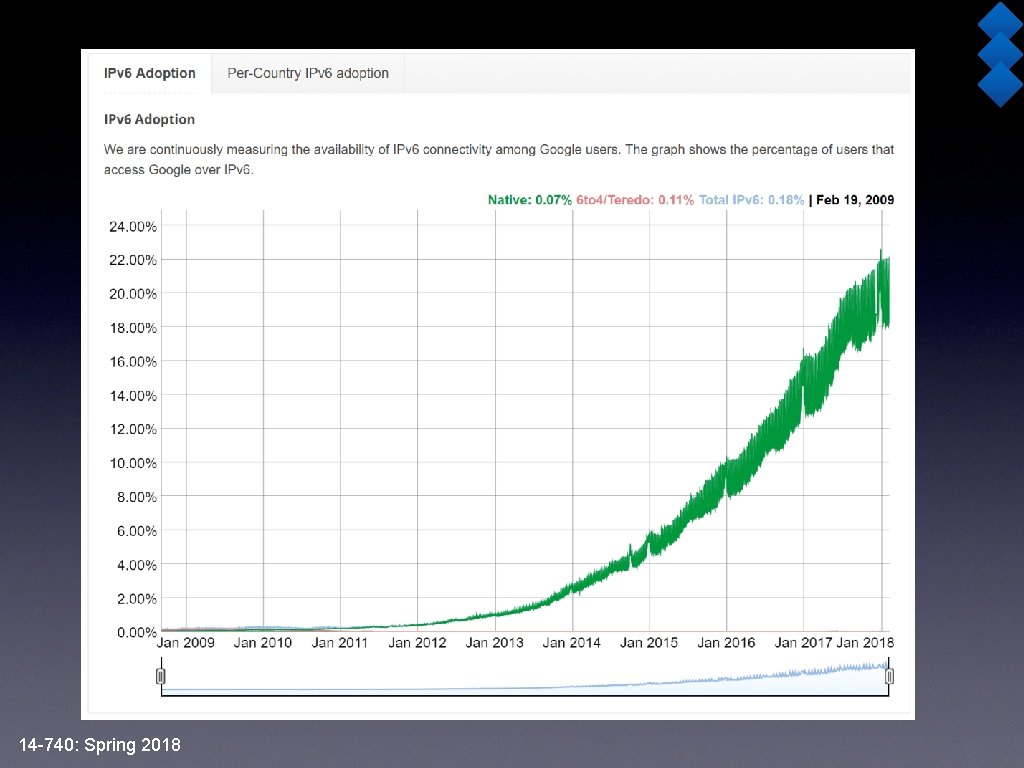
IP Standard • IPv 4 first (and only) widely deployed • Defined in RFC 791 (1981) • IPv 6 replacement • RFC 2460 (1998) • Proposed replacement • Questionable adoption rate • IPv 9: See RFC 1606 14 -740: Spring 2018 17
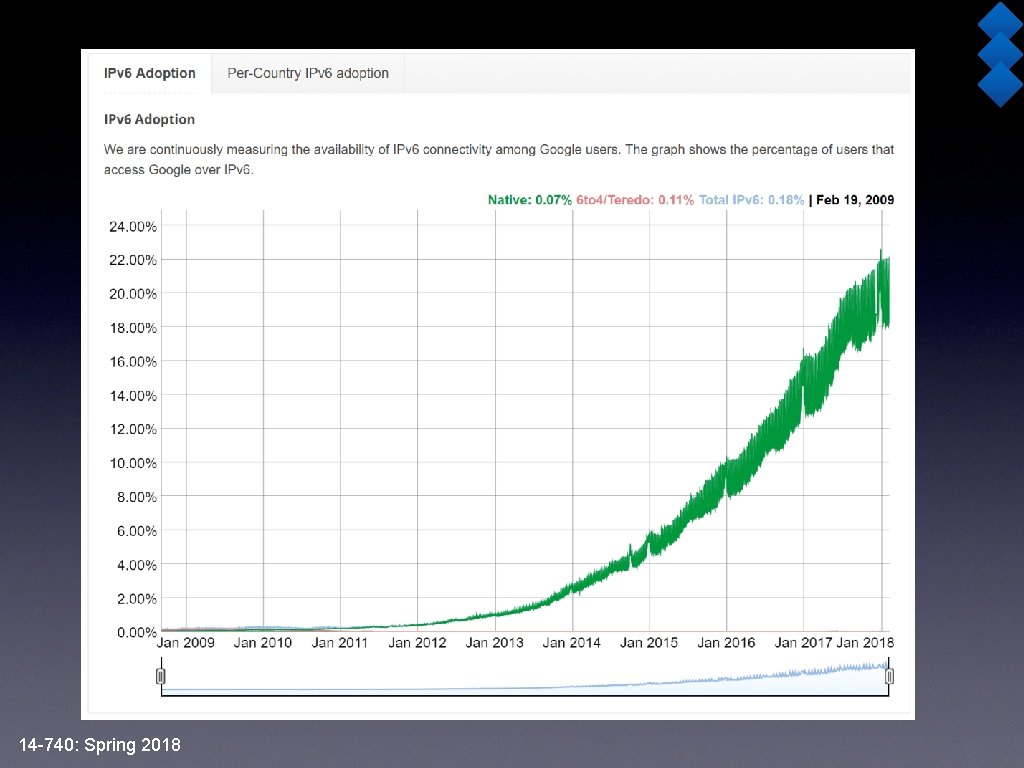
14 -740: Spring 2018
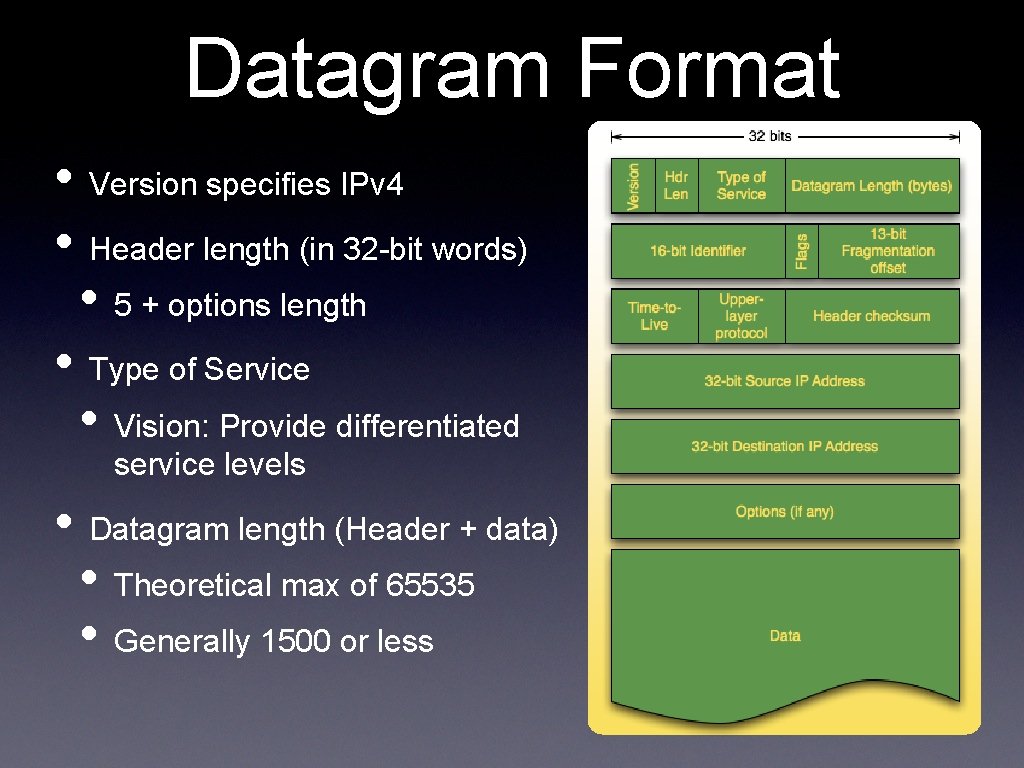
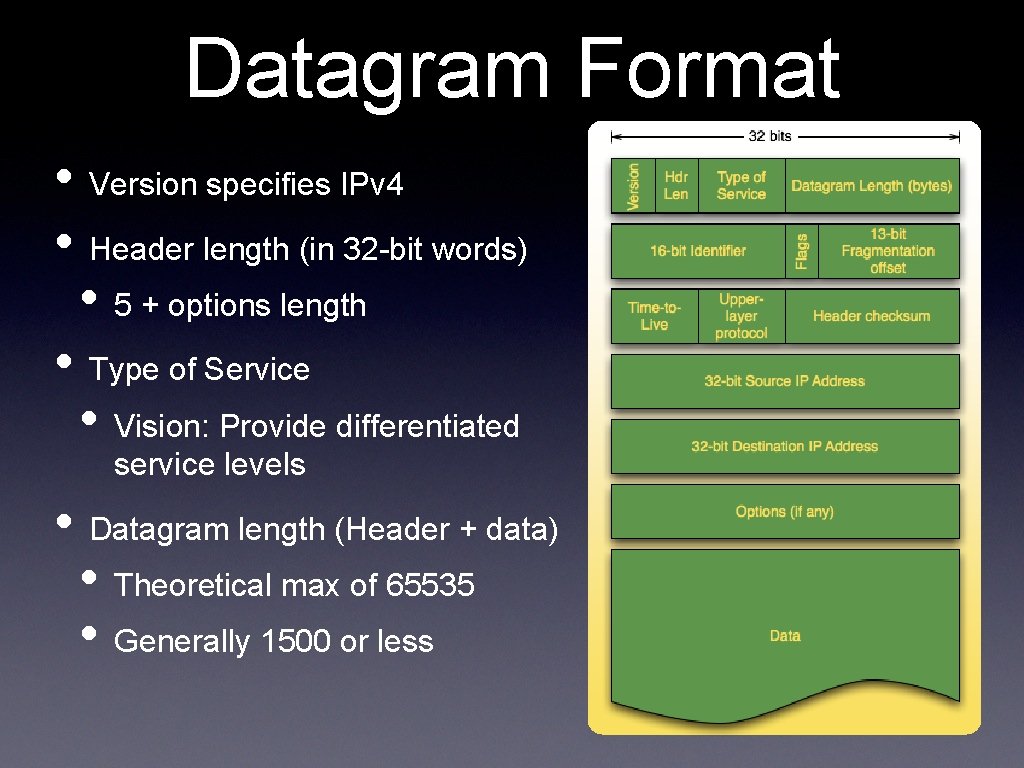
Datagram Format • Version specifies IPv 4 • Header length (in 32 -bit words) • 5 + options length • Type of Service • Vision: Provide differentiated service levels • Datagram length (Header + data) • Theoretical max of 65535 • Generally 1500 or less
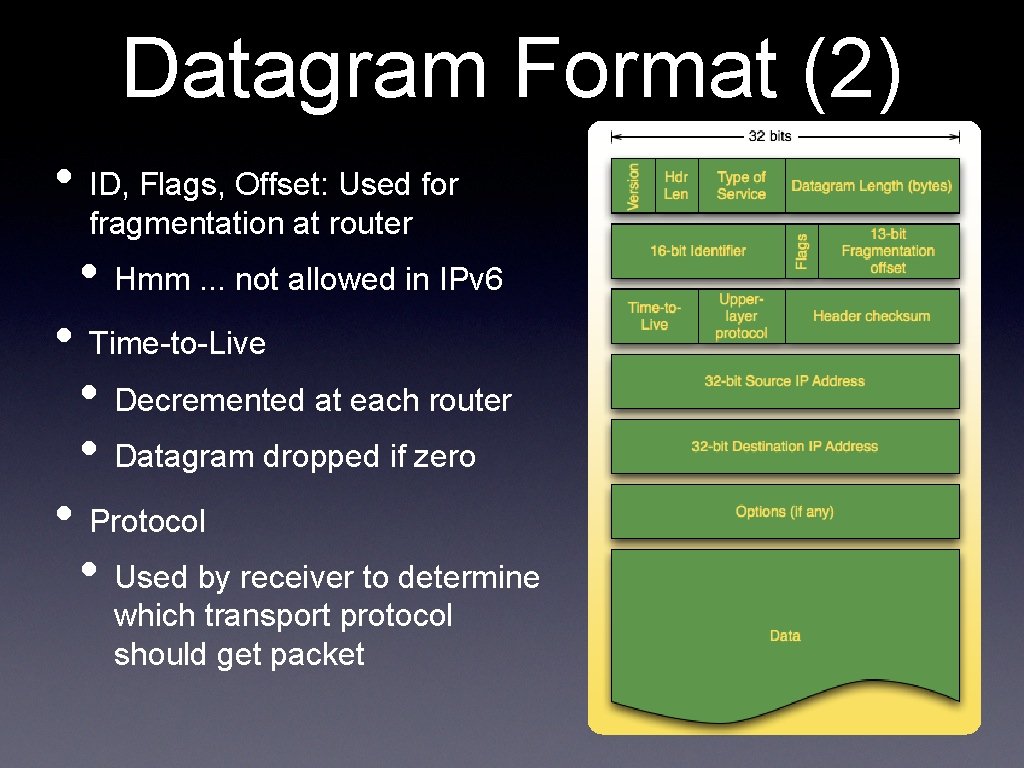
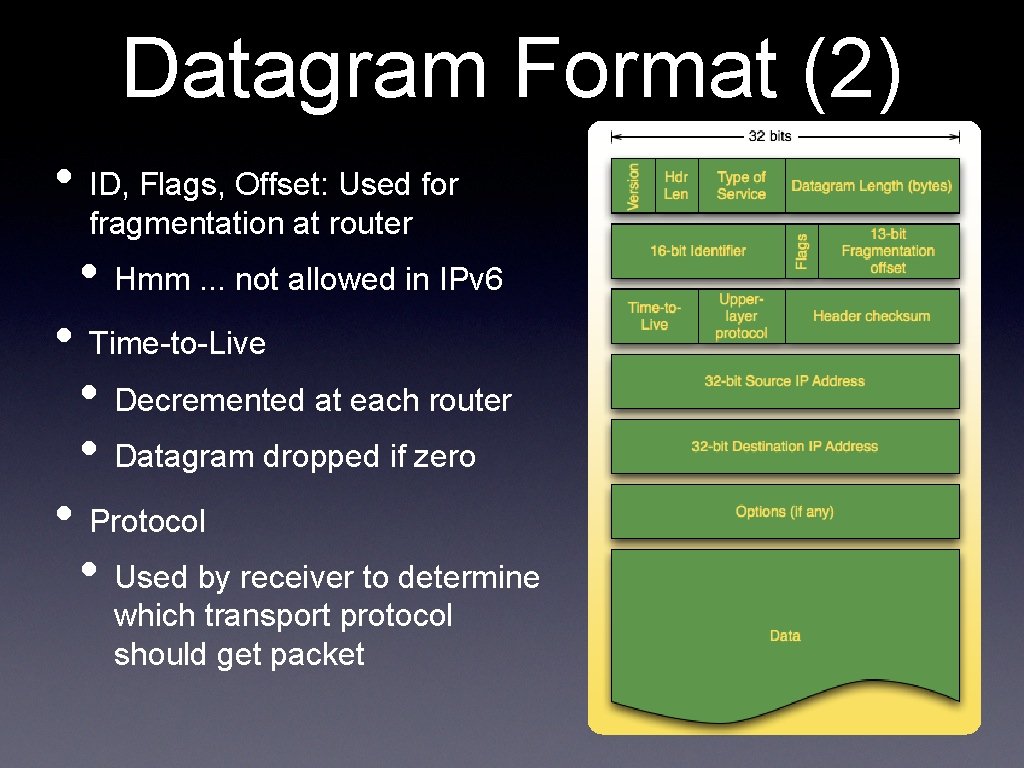
Datagram Format (2) • ID, Flags, Offset: Used for fragmentation at router • Hmm. . . not allowed in IPv 6 • Time-to-Live • Decremented at each router • Datagram dropped if zero • Protocol • Used by receiver to determine which transport protocol should get packet
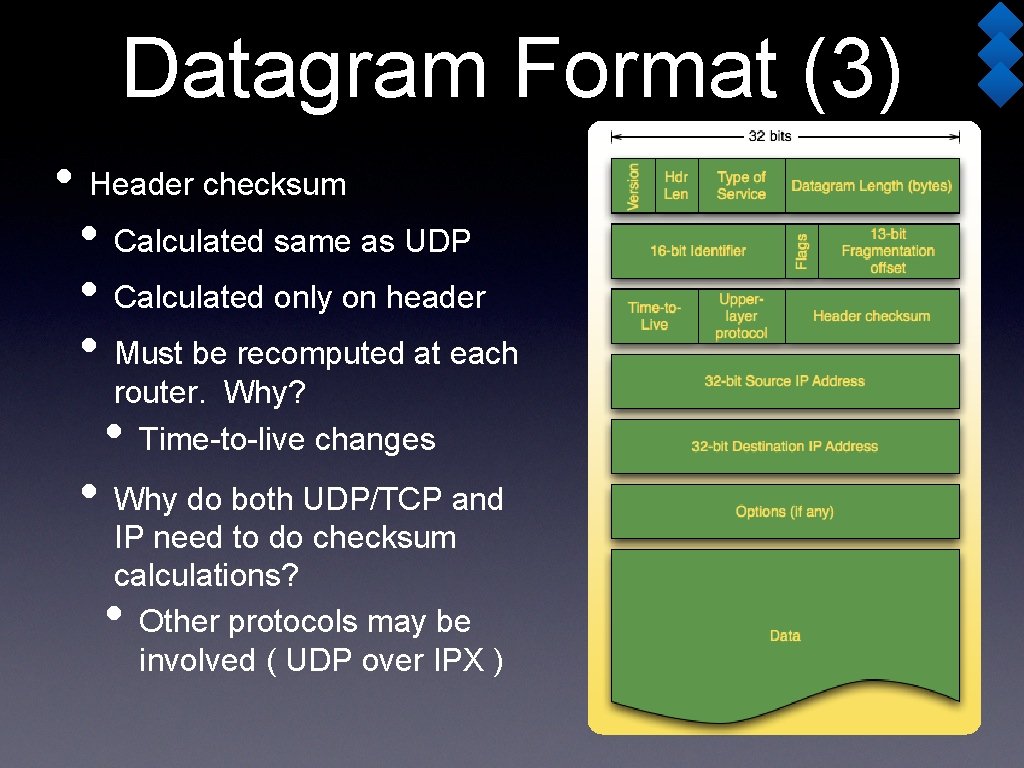
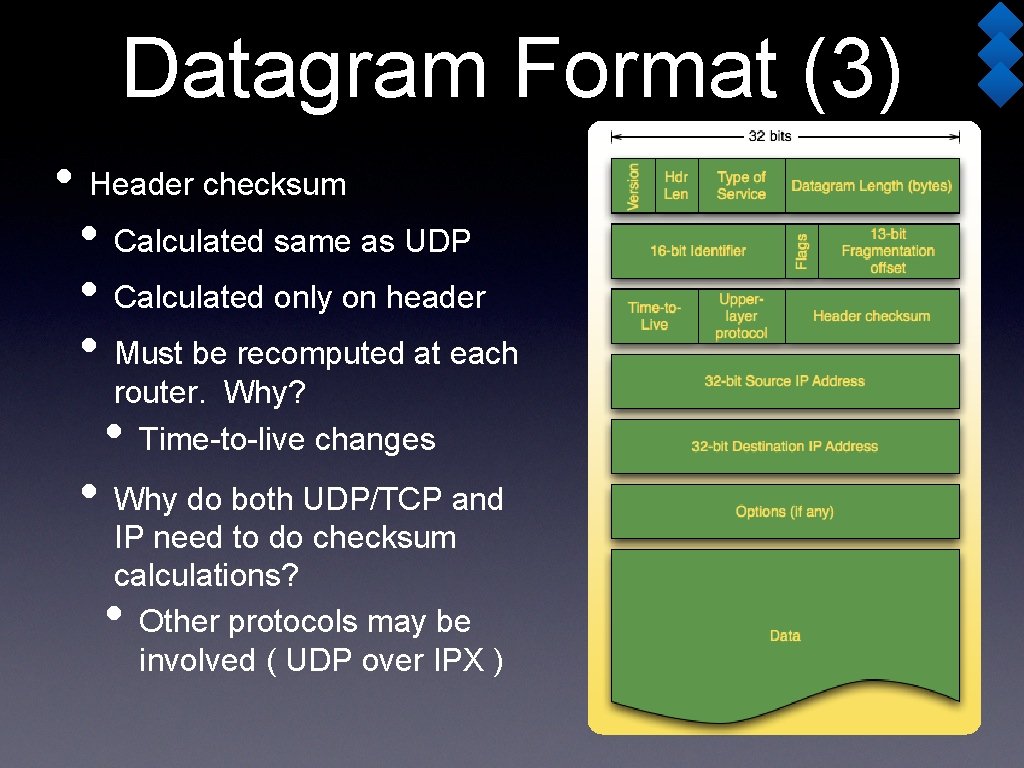
Datagram Format (3) • Header checksum • Calculated same as UDP • Calculated only on header • Must be recomputed at each router. Why? Time-to-live changes • • Why do both UDP/TCP and IP need to do checksum calculations? Other protocols may be involved ( UDP over IPX ) •
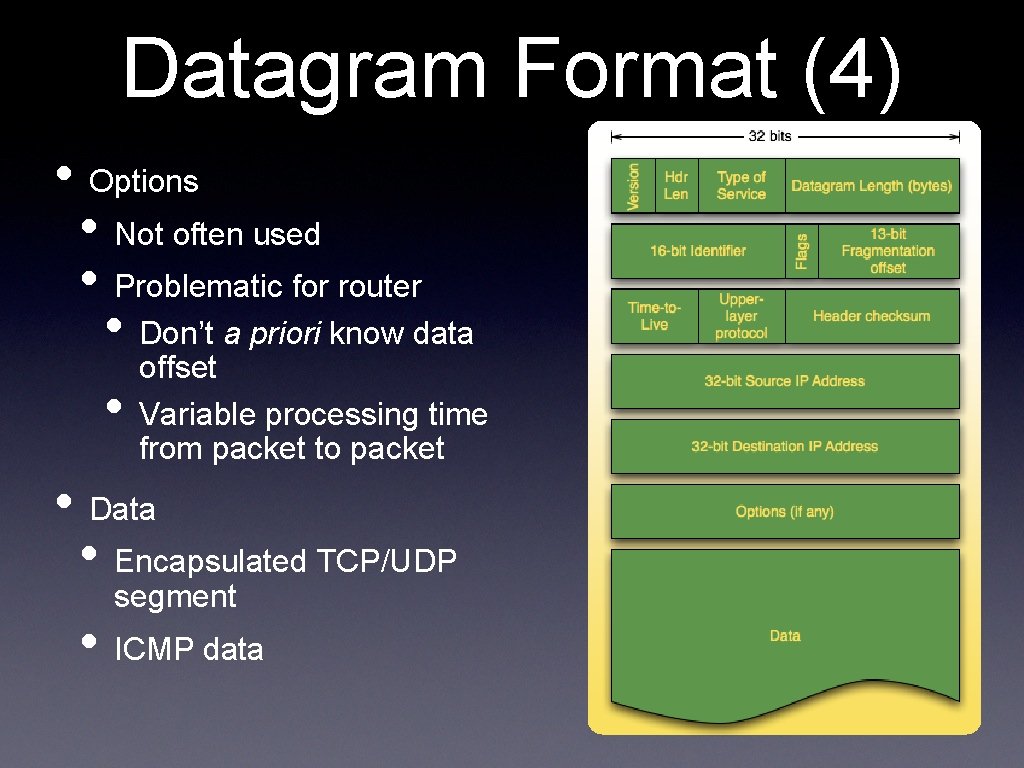
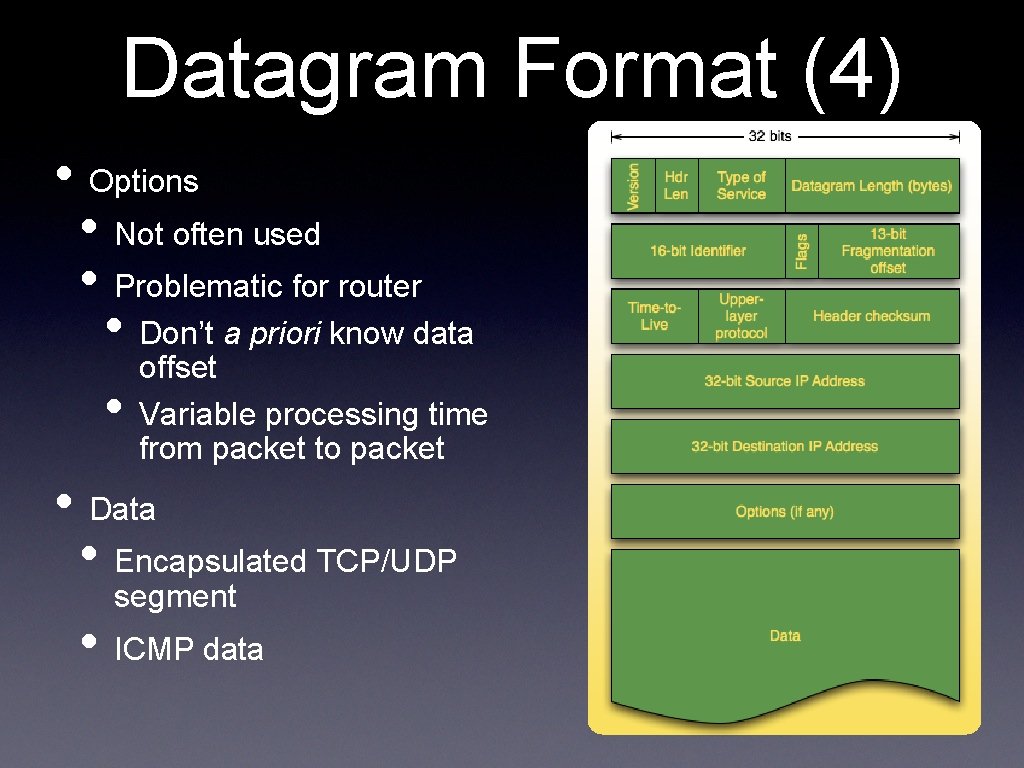
Datagram Format (4) • Options • Not often used • Problematic for router • Don’t a priori know data offset • Variable processing time from packet to packet • Data • Encapsulated TCP/UDP segment • ICMP data
IP Fragmentation • Datagram may be too big for link-layer • Remember MTU? Max Transmission Unit • Each link along the path may have different MTU • What does a router do if outbound MTU is too small for a datagram? 14 -740: Spring 2018 25
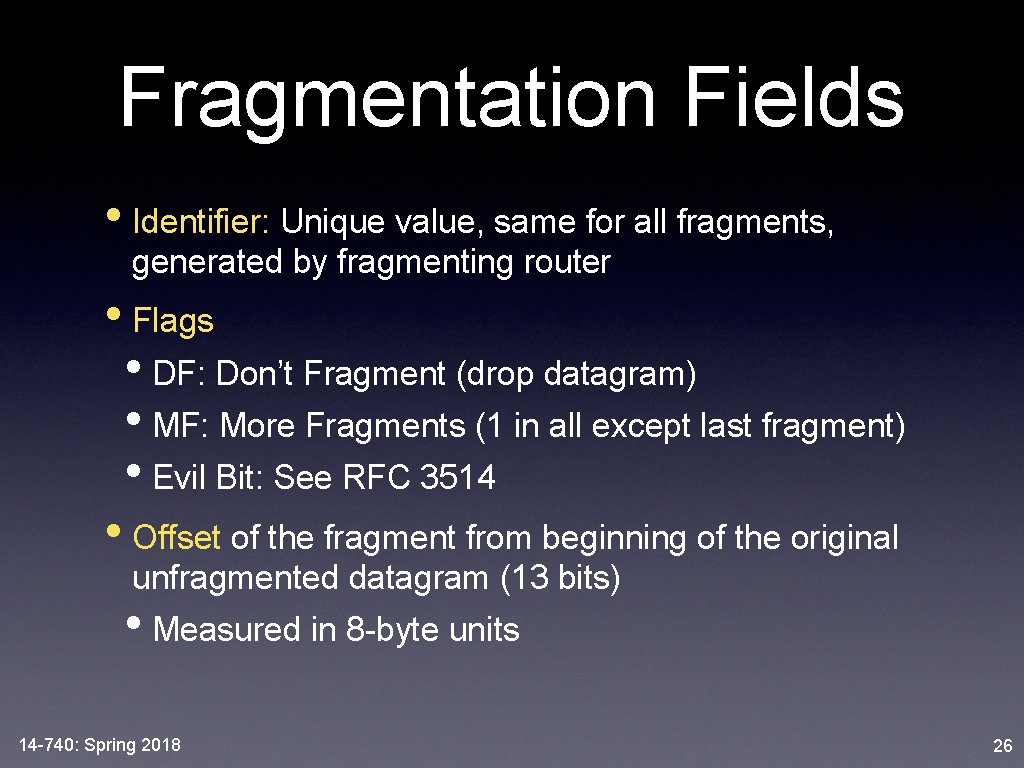
Fragmentation Fields • Identifier: Unique value, same for all fragments, generated by fragmenting router • Flags • DF: Don’t Fragment (drop datagram) • MF: More Fragments (1 in all except last fragment) • Evil Bit: See RFC 3514 • Offset of the fragment from beginning of the original unfragmented datagram (13 bits) • Measured in 8 -byte units 14 -740: Spring 2018 26
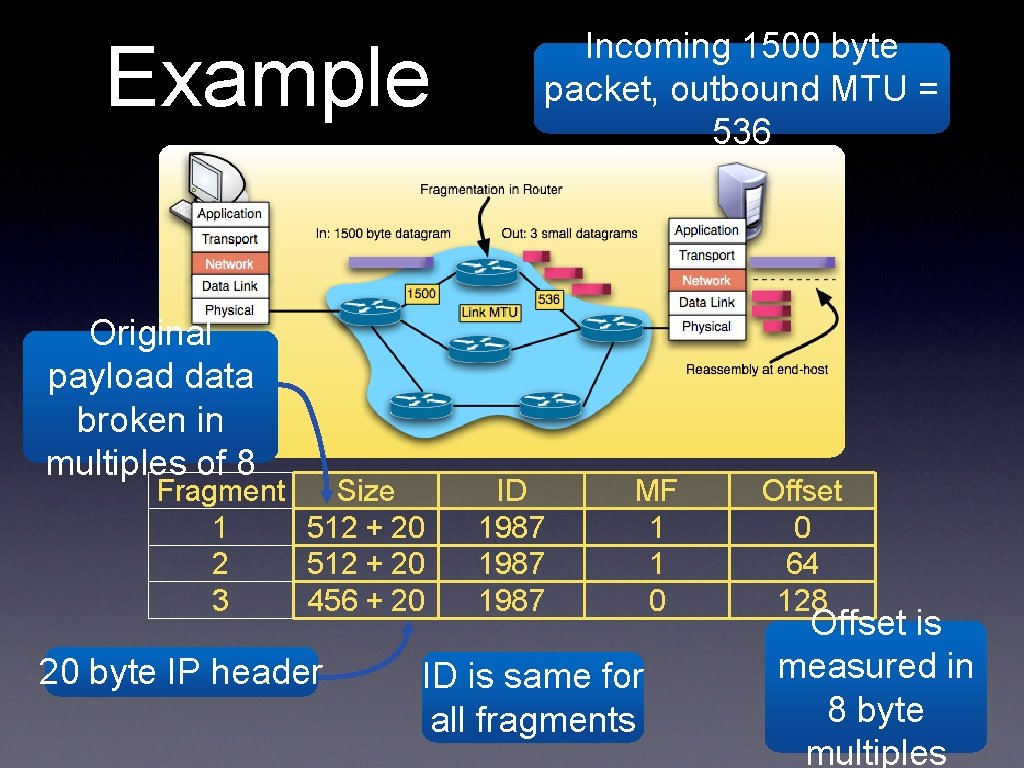
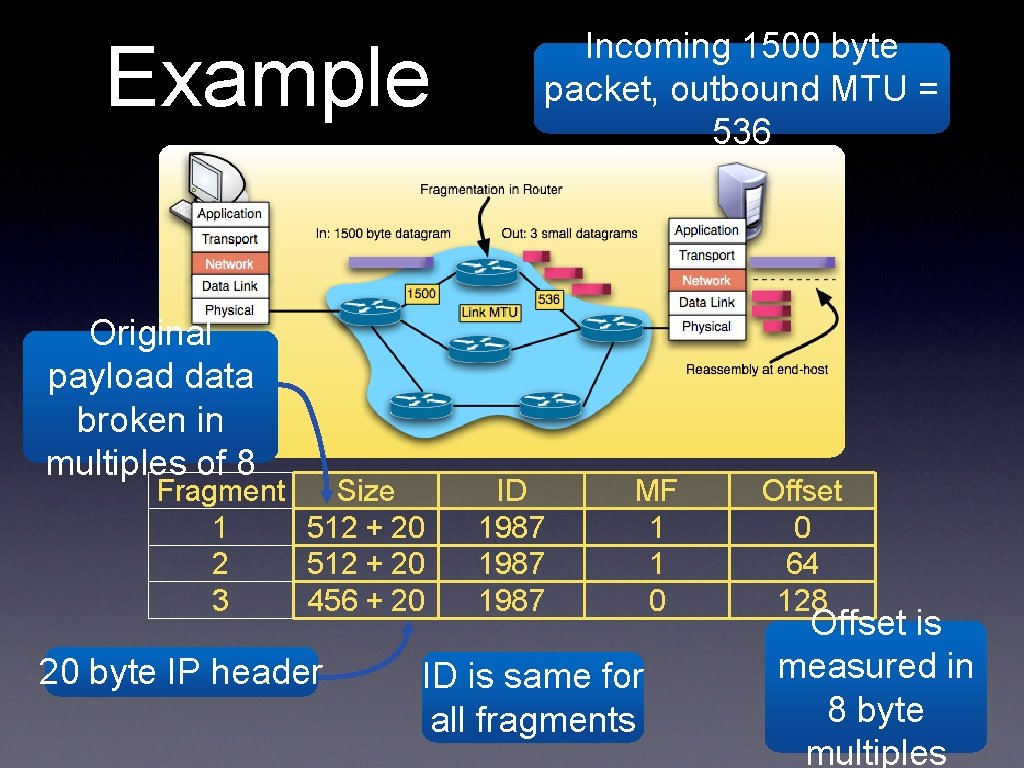
Example Original payload data broken in multiples of 8 Fragment Size 1 512 + 20 2 512 + 20 3 456 + 20 20 byte IP header Incoming 1500 byte packet, outbound MTU = 536 ID 1987 MF 1 1 0 ID is same for all fragments Offset 0 64 128 Offset is measured in 8 byte multiples
Fragmentation Issues • Reassembly done at end-host • Want to offload as much as possible from routers • If a fragment is lost, all fragments of that datagram are discarded • Fragmentation facility complicates design of routers and end-hosts • Not included in IPv 6 14 -740: Spring 2018 28
Security Issues • Fragmentation can be used to DOS • Jolt 2 Attack: send many small fragments, but no offset=0 • . . . or trigger OS crash • Send overlapping / unaligned fragments • Many OSes are vulnerable 14 -740: Spring 2018 29
traceroute • Network Layer • IP: Internet Protocol • IP Addressing • ICMP 14 -740: Spring 2018 30
Address Properties • Global uniqueness to identify hosts • Ethernet addresses are globally unique, why not use it in the Internet? • They are flat, no structure to aid routing • First 24 bits identify the manufacturer, but do not relate with network topology • Hierarchical Addresses • Network / Subnet part, Host part • Necessary for Internet to scale to large number of hosts 14 -740: Spring 2018 31
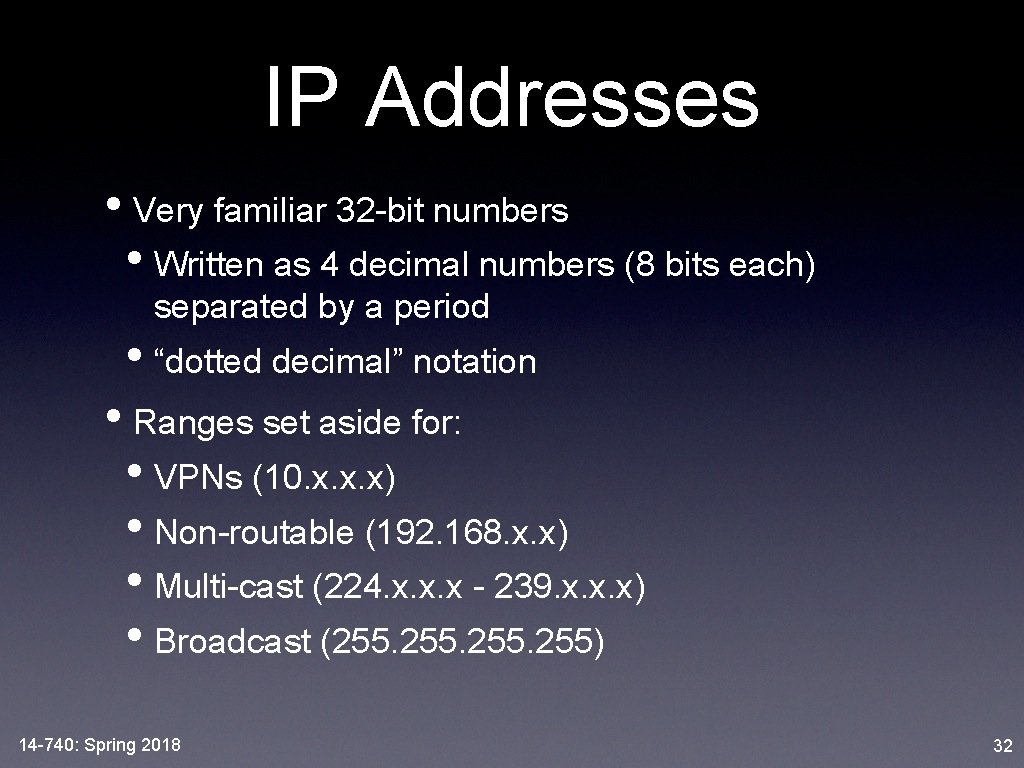
IP Addresses • Very familiar 32 -bit numbers • Written as 4 decimal numbers (8 bits each) separated by a period • “dotted decimal” notation • Ranges set aside for: • VPNs (10. x. x. x) • Non-routable (192. 168. x. x) • Multi-cast (224. x. x. x - 239. x. x. x) • Broadcast (255. 255) 14 -740: Spring 2018 32
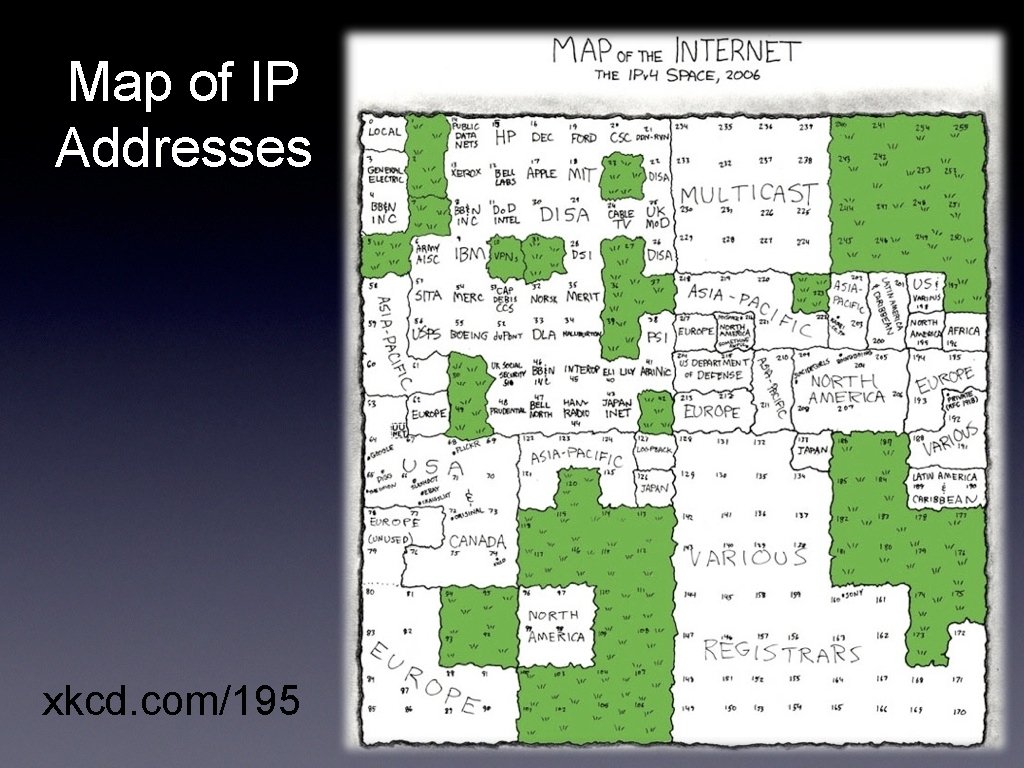
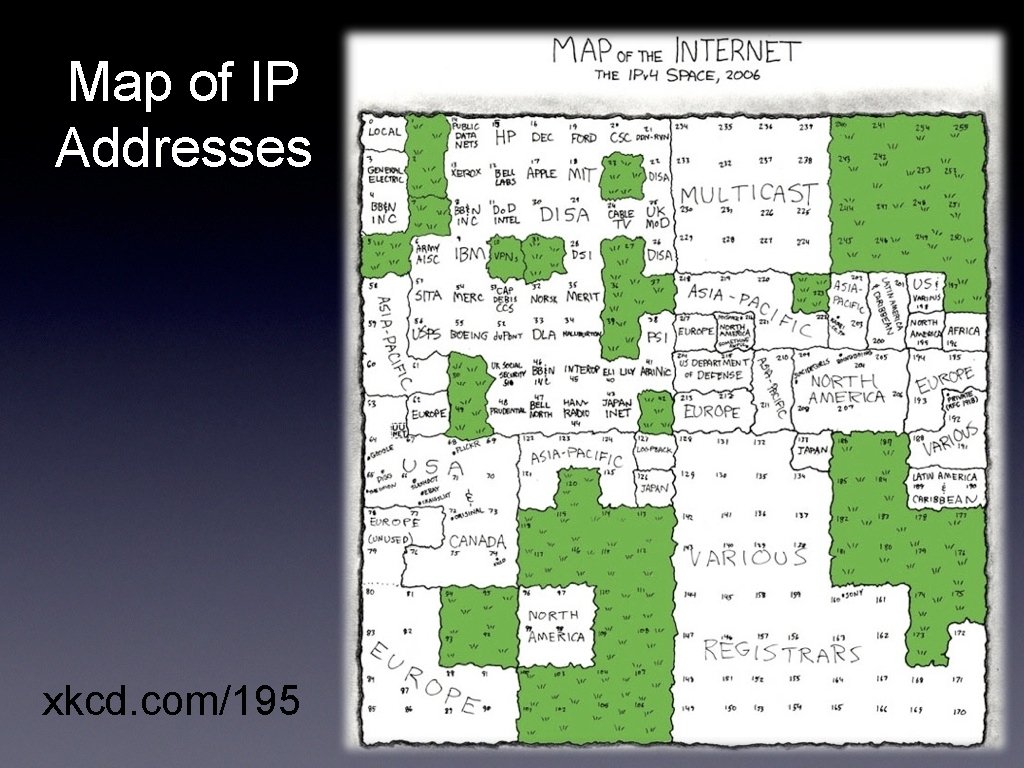
Map of IP Addresses xkcd. com/195
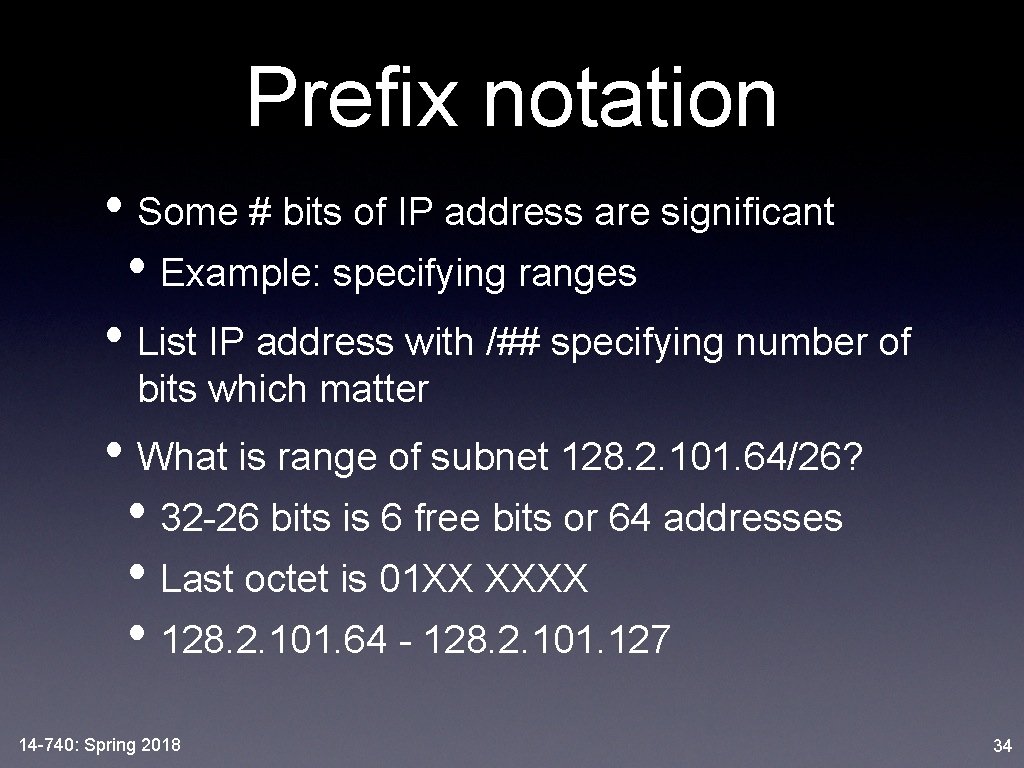
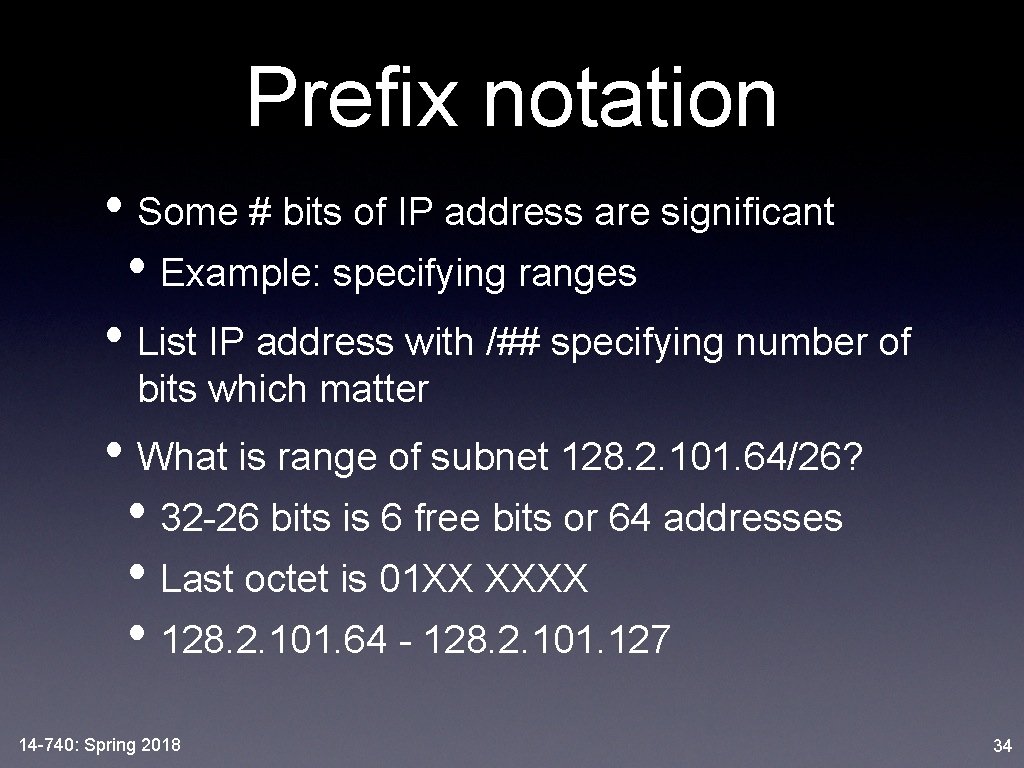
Prefix notation • Some # bits of IP address are significant • Example: specifying ranges • List IP address with /## specifying number of bits which matter • What is range of subnet 128. 2. 101. 64/26? • 32 -26 bits is 6 free bits or 64 addresses • Last octet is 01 XX XXXX • 128. 2. 101. 64 - 128. 2. 101. 127 14 -740: Spring 2018 34
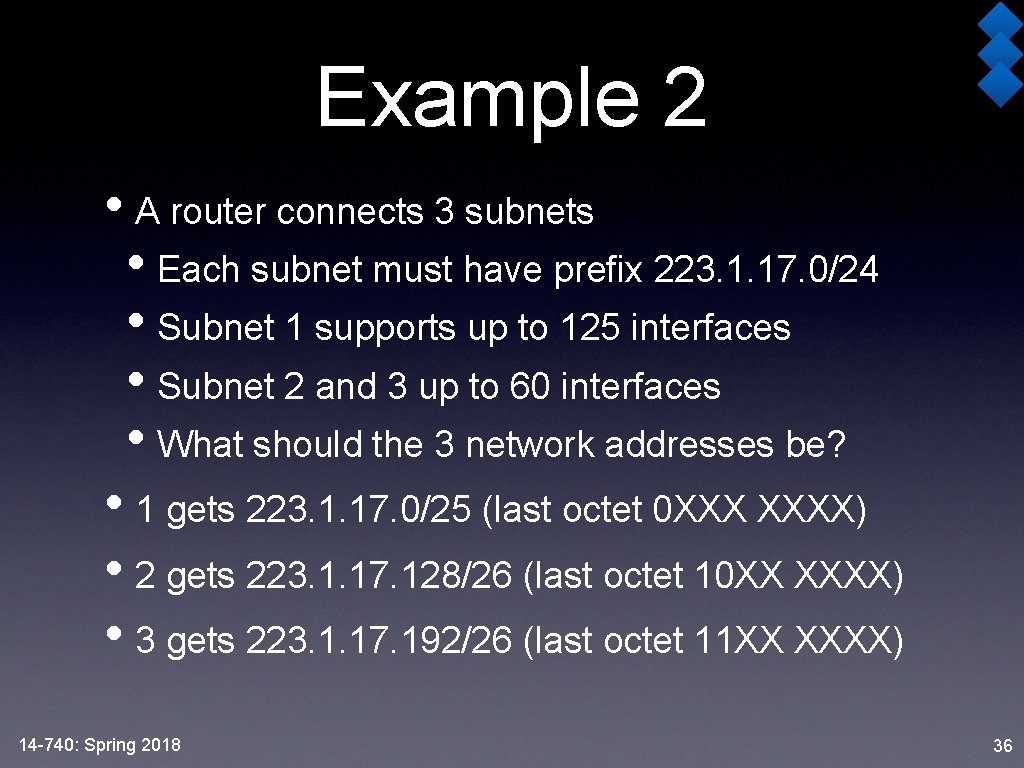
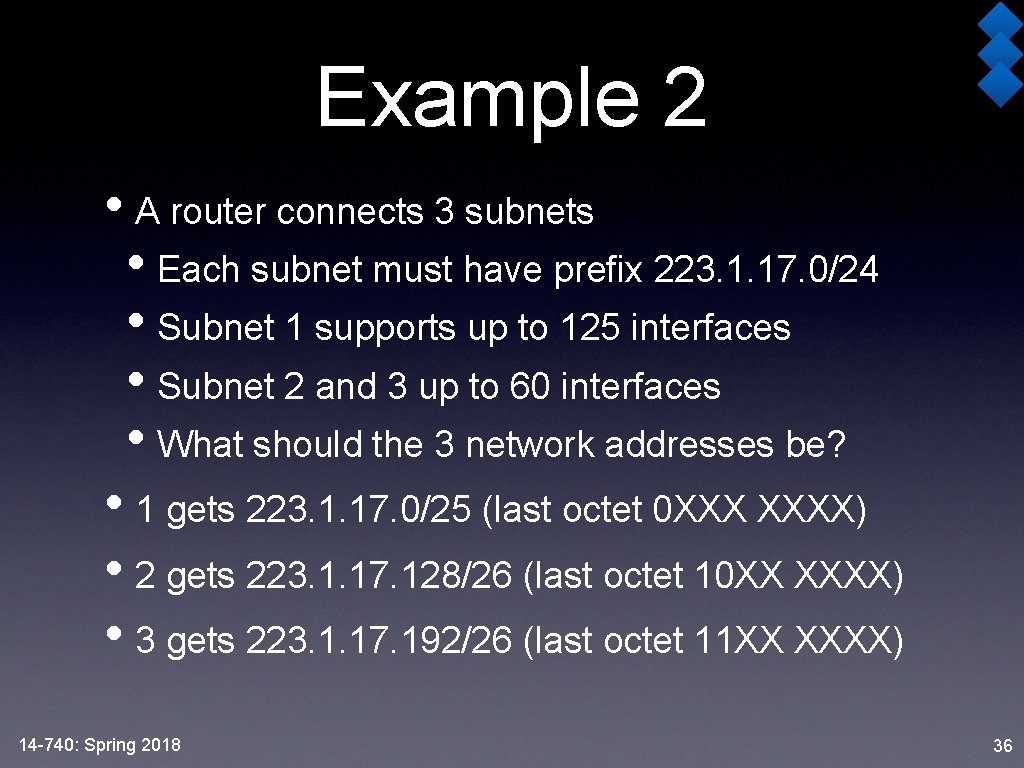
Example 2 • A router connects 3 subnets • Each subnet must have prefix 223. 1. 17. 0/24 • Subnet 1 supports up to 125 interfaces • Subnet 2 and 3 up to 60 interfaces • What should the 3 network addresses be? • 1 gets 223. 1. 17. 0/25 (last octet 0 XXX XXXX) • 2 gets 223. 1. 17. 128/26 (last octet 10 XX XXXX) • 3 gets 223. 1. 17. 192/26 (last octet 11 XX XXXX) 14 -740: Spring 2018 36
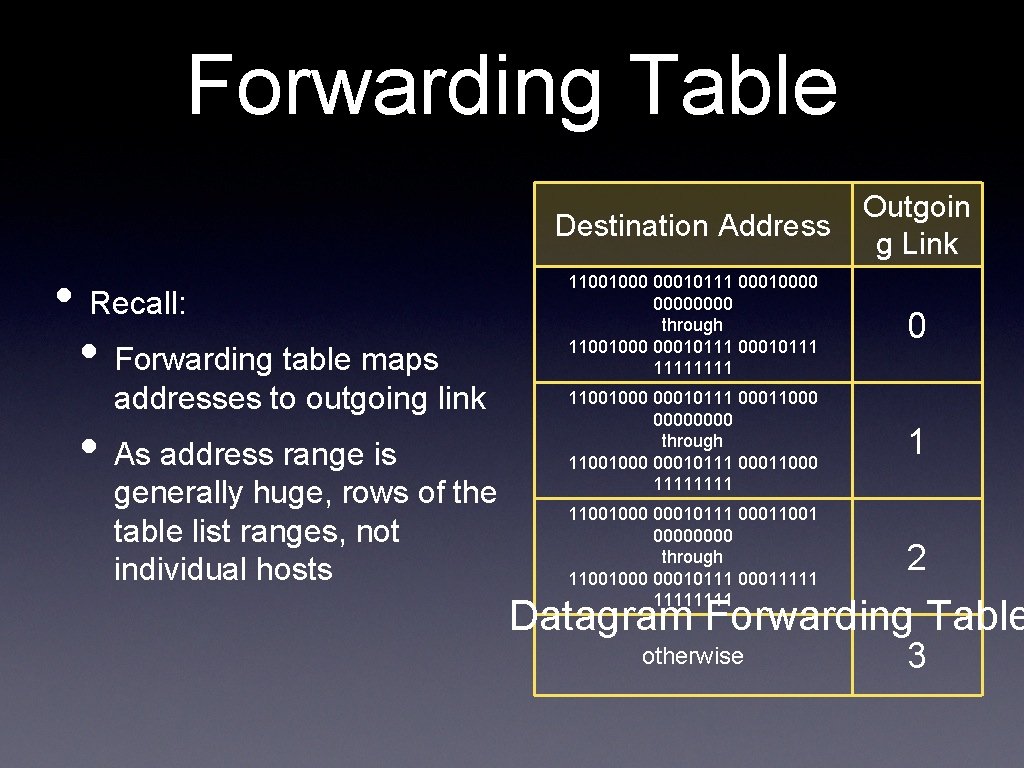
Forwarding Table • Recall: • Forwarding table maps addresses to outgoing link • As address range is generally huge, rows of the table list ranges, not individual hosts Destination Address Outgoin g Link 11001000 00010111 00010000 through 11001000 00010111 1111 0 11001000 00010111 00011000 0000 through 11001000 00010111 00011000 1111 1 11001000 00010111 00011001 0000 through 11001000 00010111 00011111 2 otherwise 3 Datagram Forwarding Table
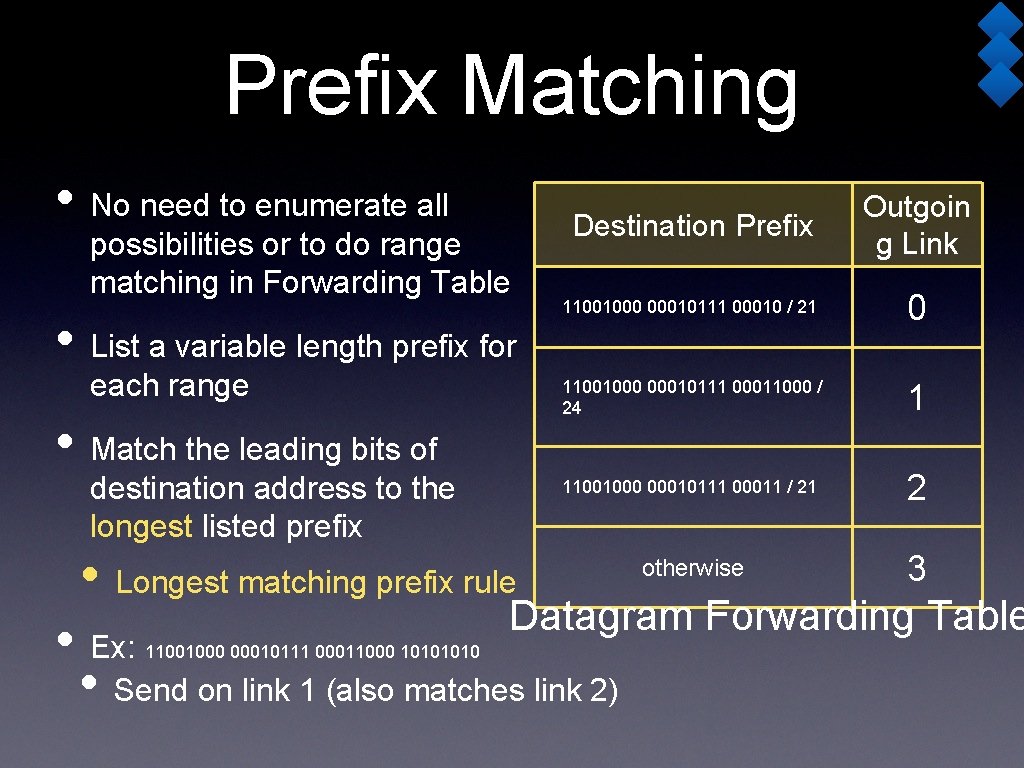
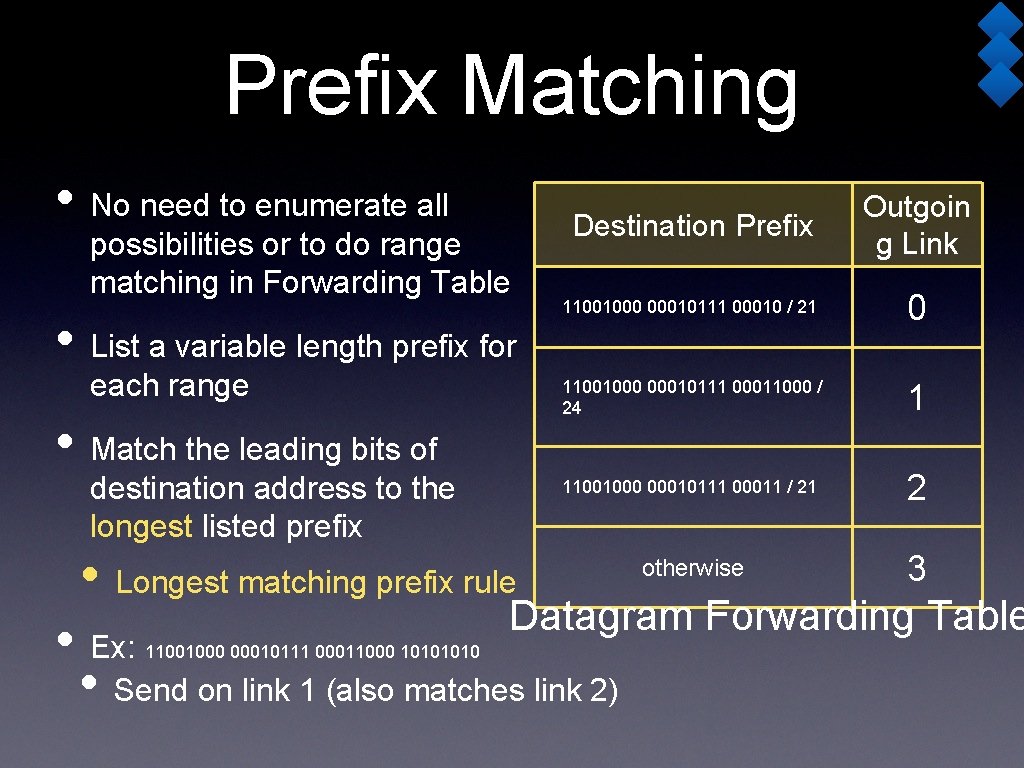
Prefix Matching • No need to enumerate all possibilities or to do range matching in Forwarding Table • List a variable length prefix for each range • Match the leading bits of destination address to the longest listed prefix Destination Prefix Outgoin g Link 11001000 00010111 00010 / 21 0 11001000 00010111 00011000 / 24 1 11001000 00010111 00011 / 21 2 otherwise 3 • Longest matching prefix rule Datagram Forwarding Table • Ex: • Send on link 1 (also matches link 2) 11001000 00010111 00011000 1010
Classless Interdomain Routing • Subnet portion of address can be of arbitrary length • Address format a. b. c. d/x, where x is any value 0 -32 • Reaction to Classful addressing from the “early days” • Subnets could only have x=8, 16, 24 14 -740: Spring 2018 40
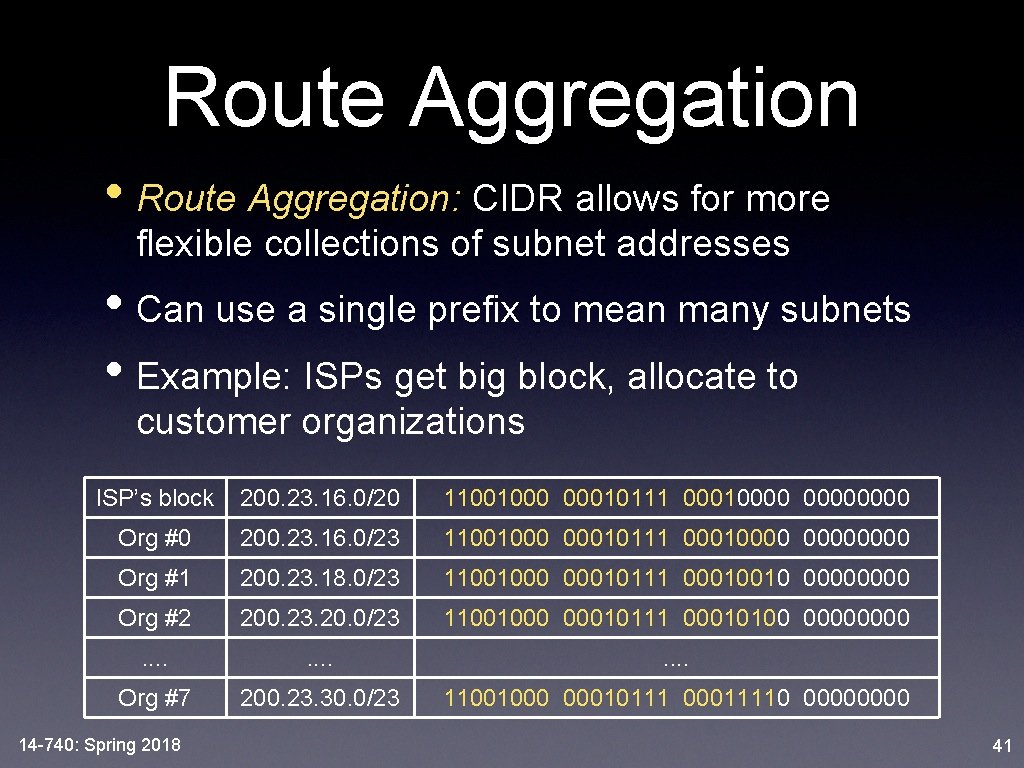
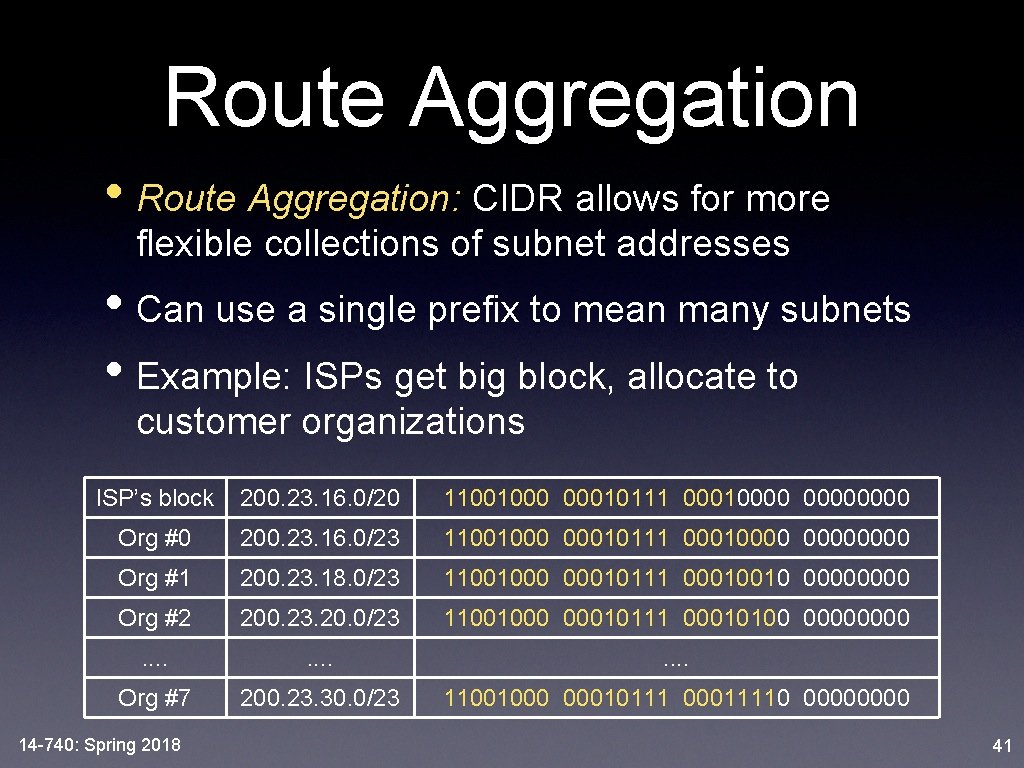
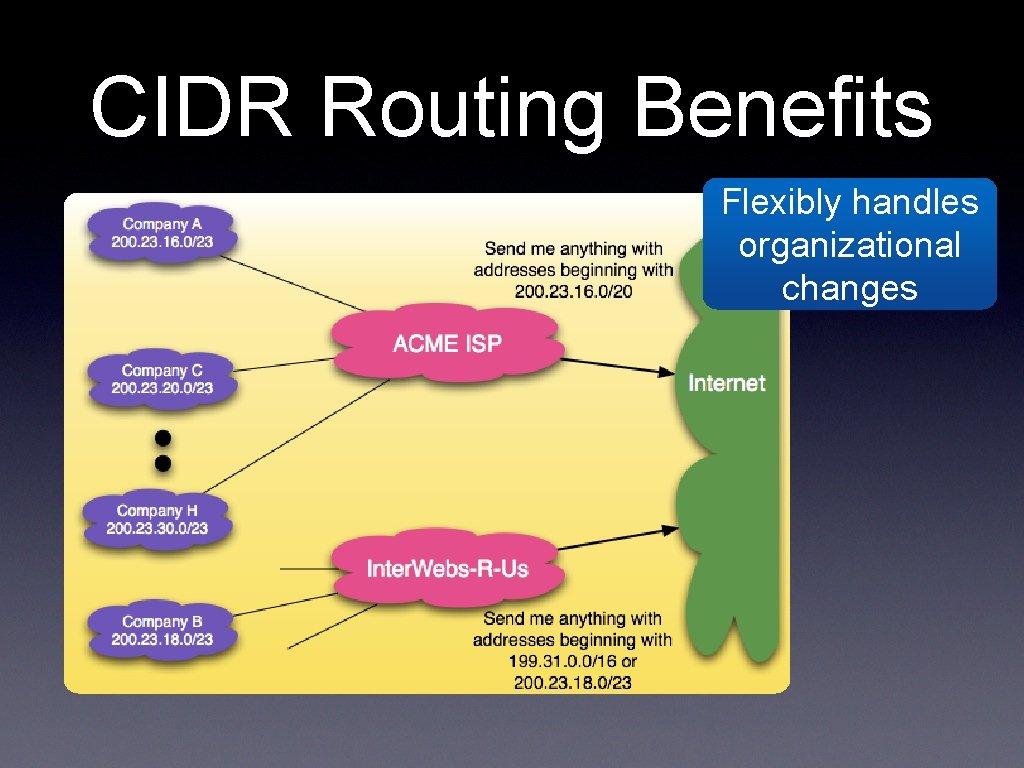
Route Aggregation • Route Aggregation: CIDR allows for more flexible collections of subnet addresses • Can use a single prefix to mean many subnets • Example: ISPs get big block, allocate to customer organizations ISP’s block 200. 23. 16. 0/20 11001000 00010111 00010000 Org #0 200. 23. 16. 0/23 11001000 00010111 00010000 Org #1 200. 23. 18. 0/23 11001000 00010111 00010010 0000 Org #2 200. 23. 20. 0/23 11001000 00010111 00010100 0000 . . . Org #7 200. 23. 30. 0/23 11001000 00010111 00011110 0000 14 -740: Spring 2018 41
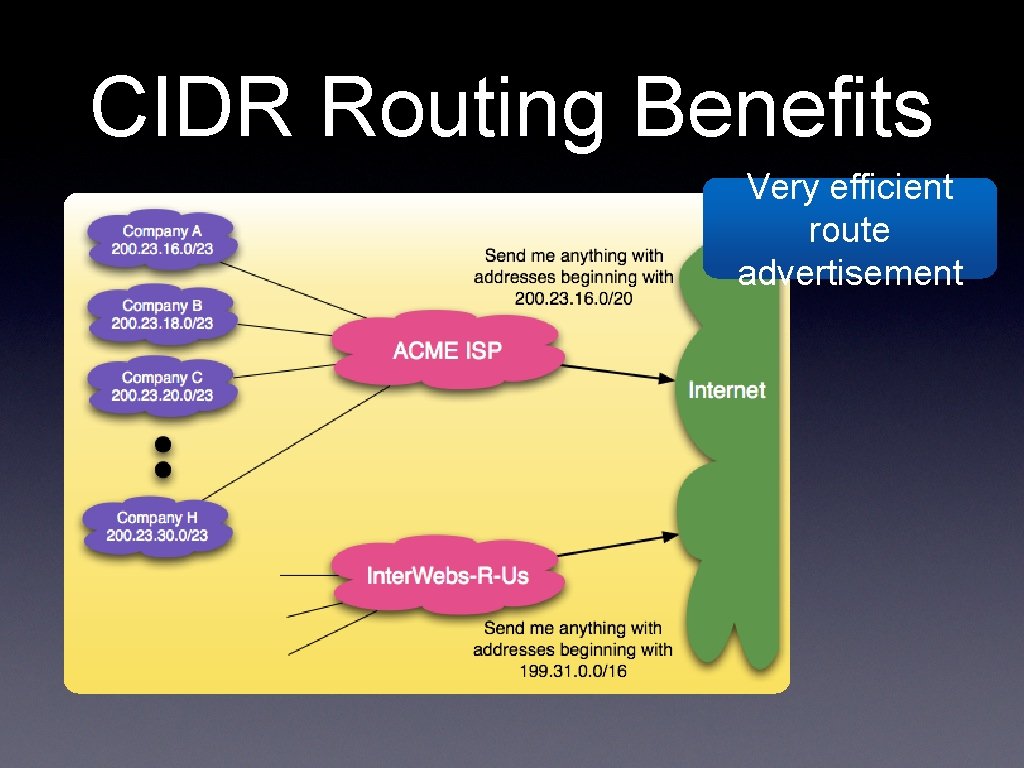
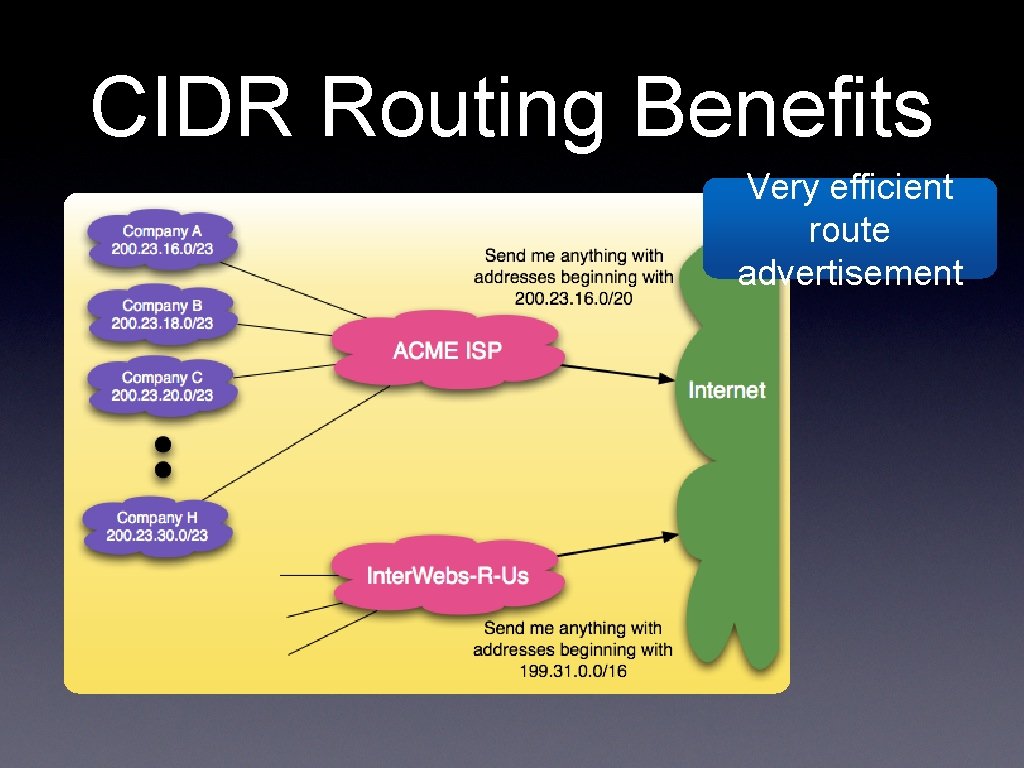
CIDR Routing Benefits Very efficient route advertisement
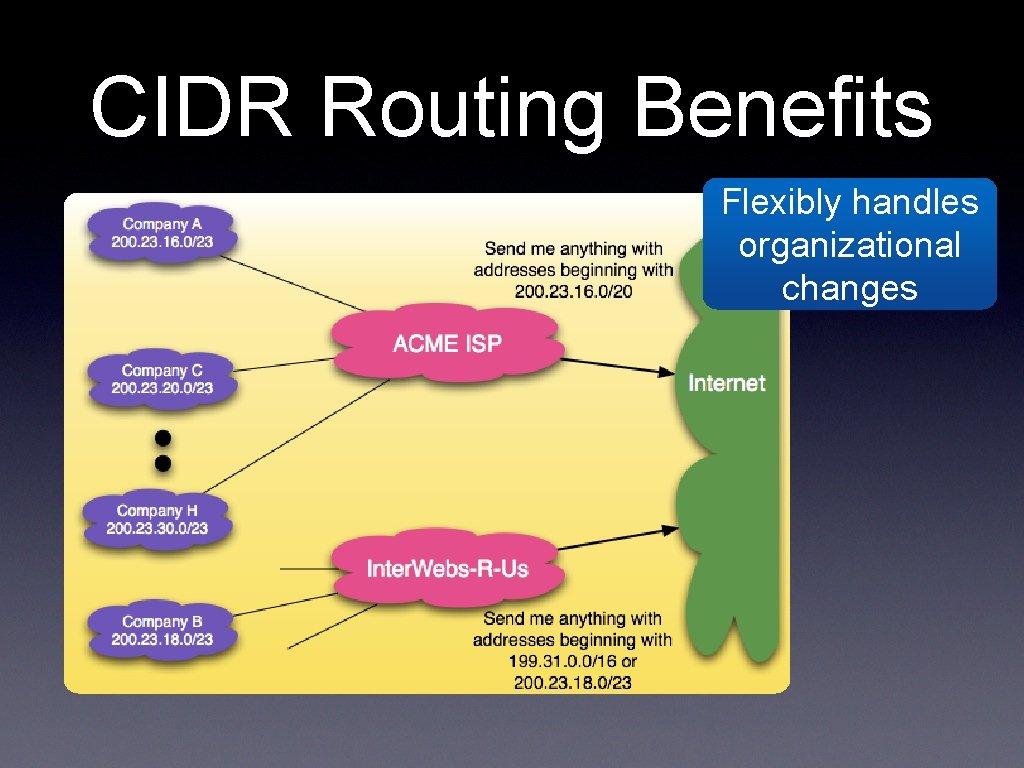
CIDR Routing Benefits Flexibly handles organizational changes
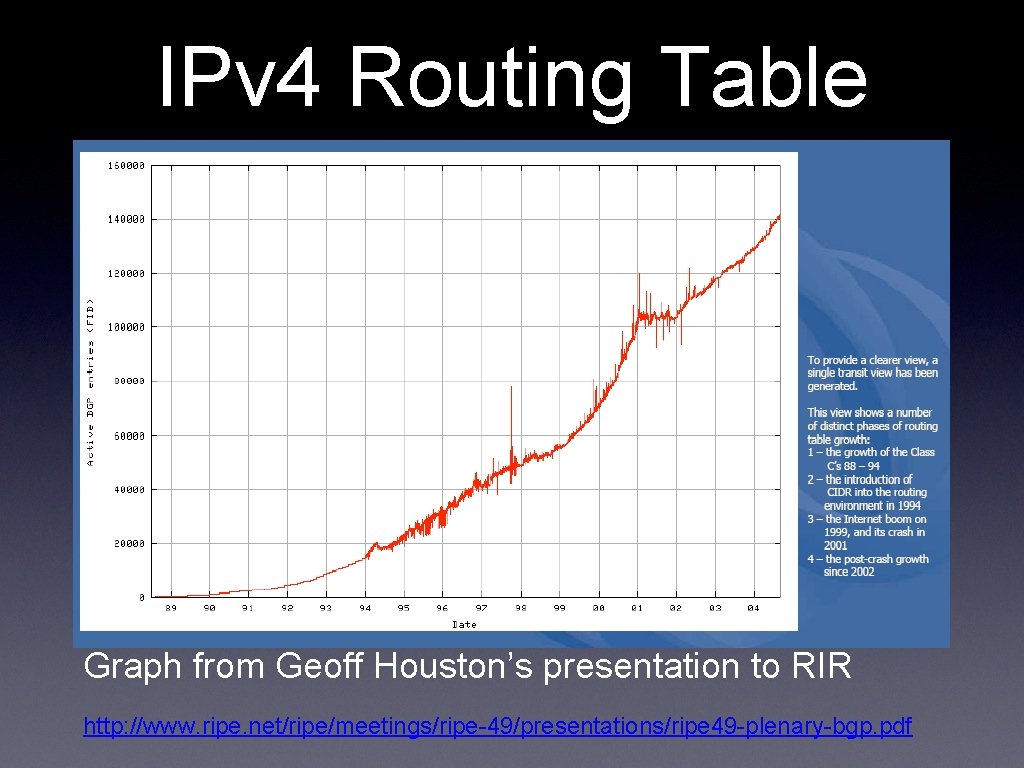
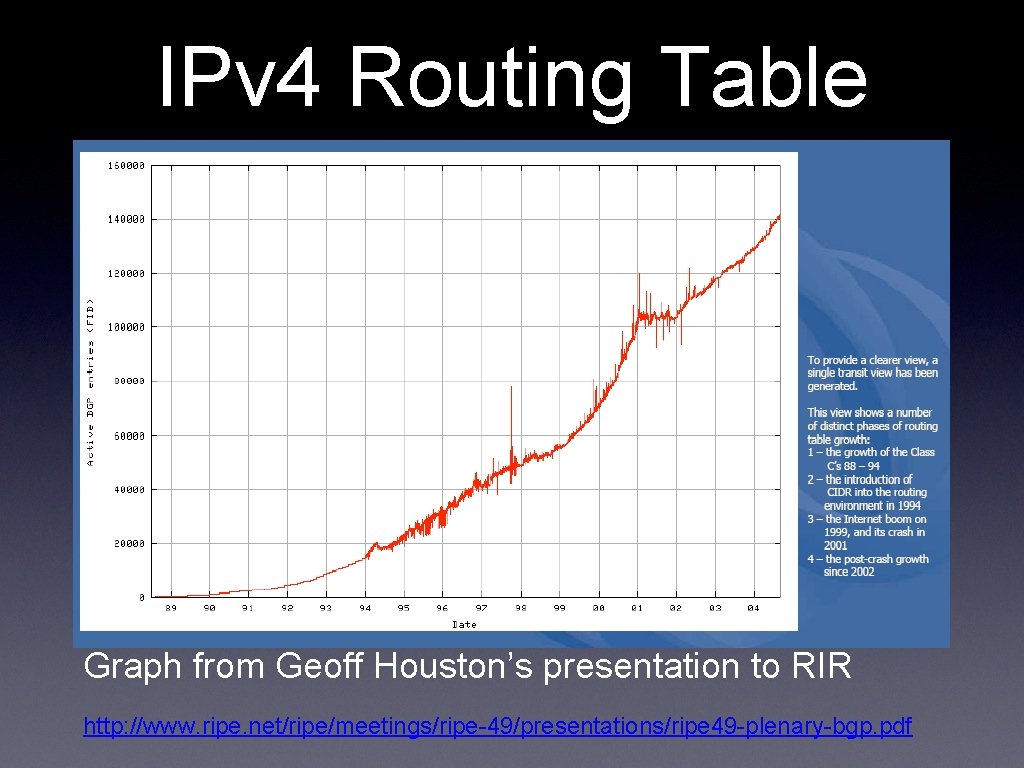
IPv 4 Routing Table Size Graph from Geoff Houston’s presentation to RIR http: //www. ripe. net/ripe/meetings/ripe-49/presentations/ripe 49 -plenary-bgp. pdf
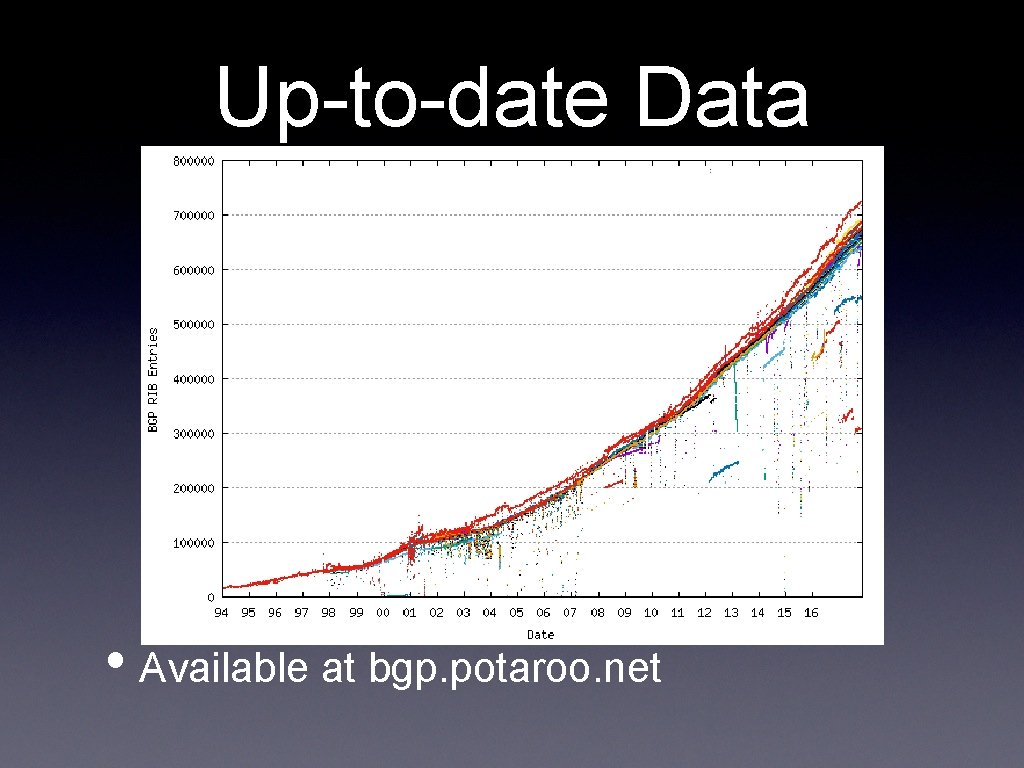
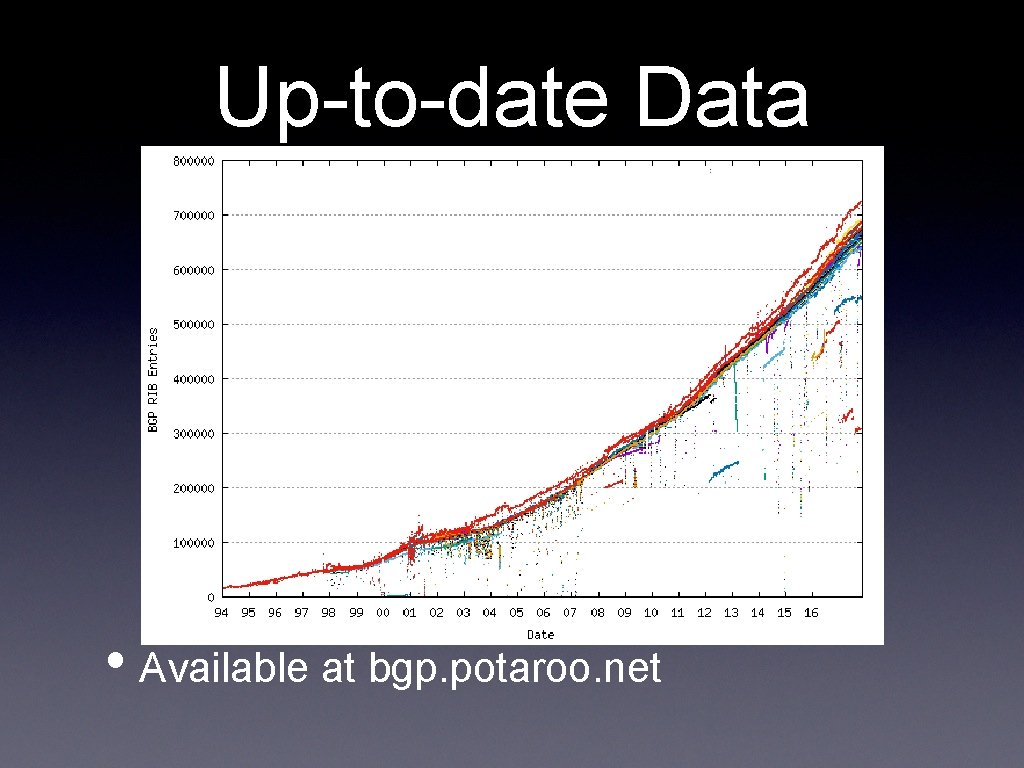
Up-to-date Data • Available at bgp. potaroo. net
traceroute • Network Layer • IP: Internet Protocol • IP Addressing • ICMP 14 -740: Spring 2018 46
ICMP • Internet Control Message Protocol • RFC 792 (1981) • Used for error messages and some routing information • Basis of ping and traceroute 14 -740: Spring 2018 47
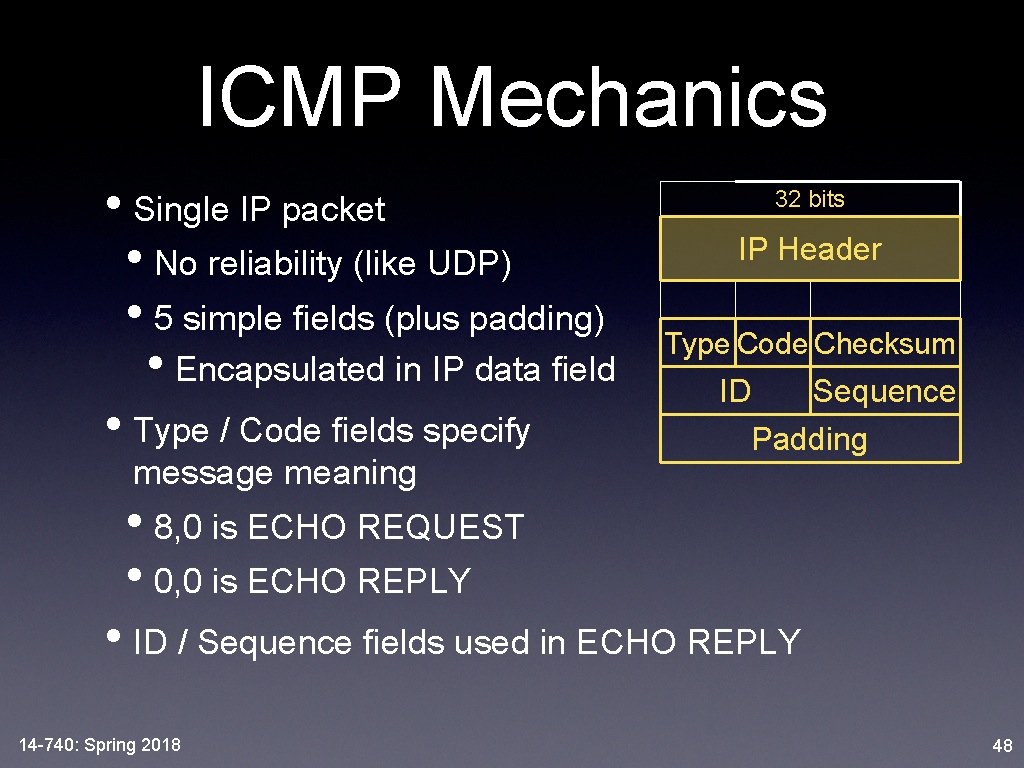
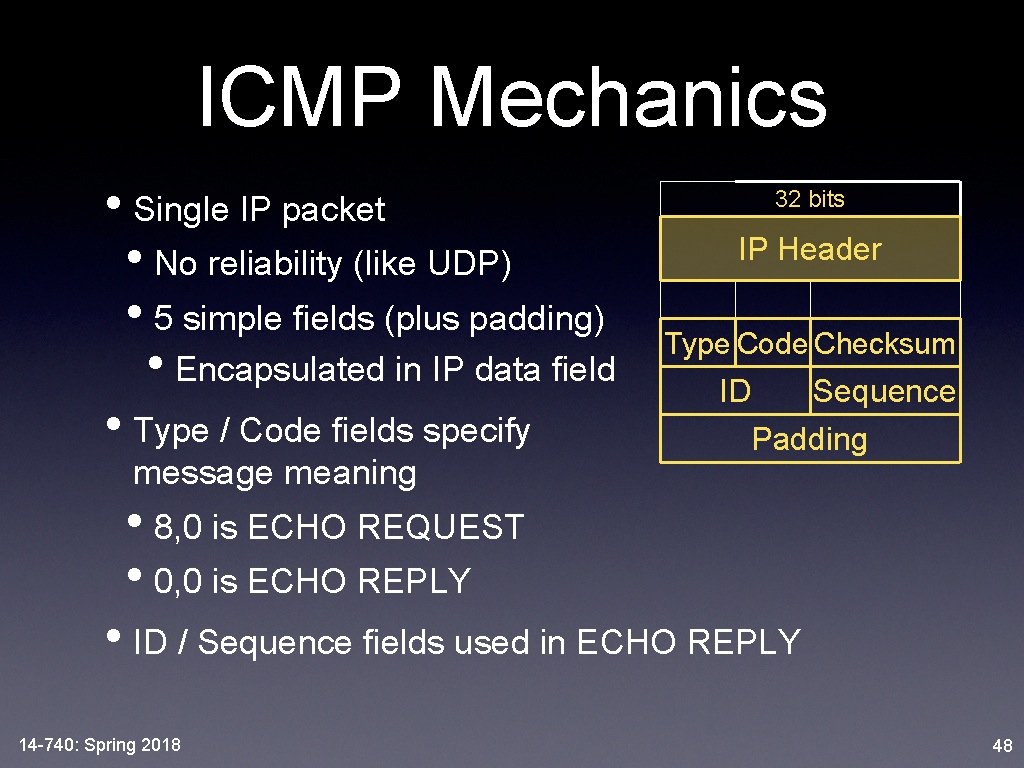
ICMP Mechanics • Single IP packet • No reliability (like UDP) • 5 simple fields (plus padding) • Encapsulated in IP data field • Type / Code fields specify message meaning 32 bits IP Header Type Code Checksum ID Sequence Padding • 8, 0 is ECHO REQUEST • 0, 0 is ECHO REPLY • ID / Sequence fields used in ECHO REPLY 14 -740: Spring 2018 48
Error Messages • Type 3 is Destination Unreachable • Further codes for • Network unreachable • Host unreachable • Fragmentation required, but can’t • + 13 others • Type 4 is Source Quench • Designed for Congestion Control messages from network to host ➙ rarely used today 14 -740: Spring 2018 49
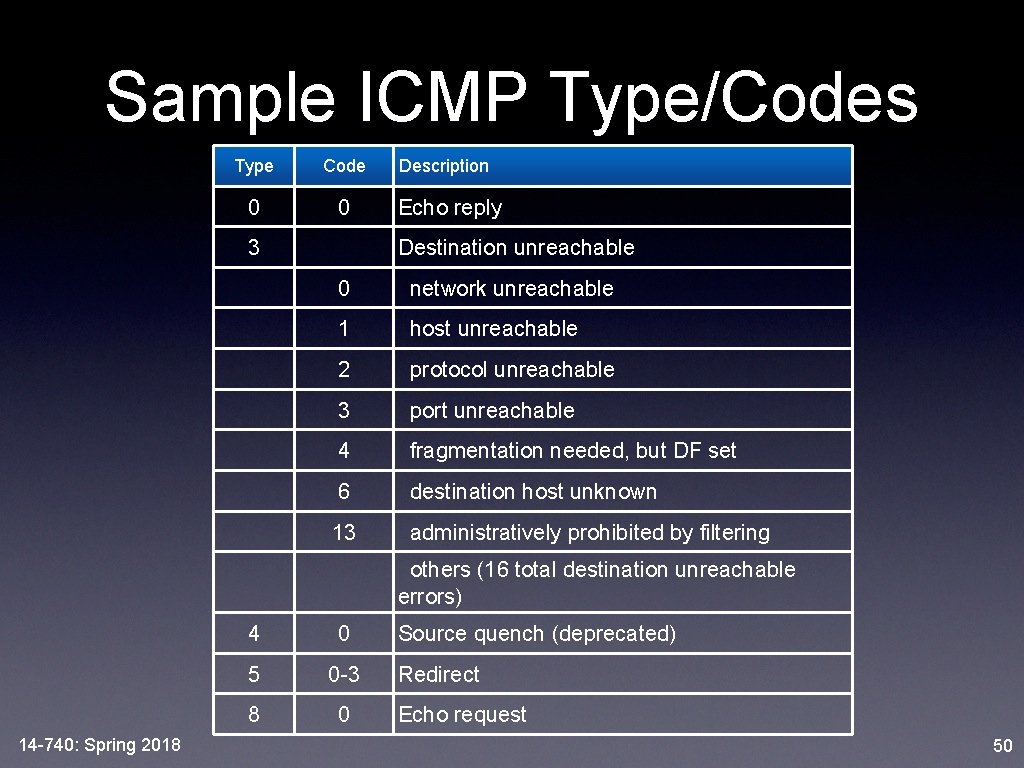
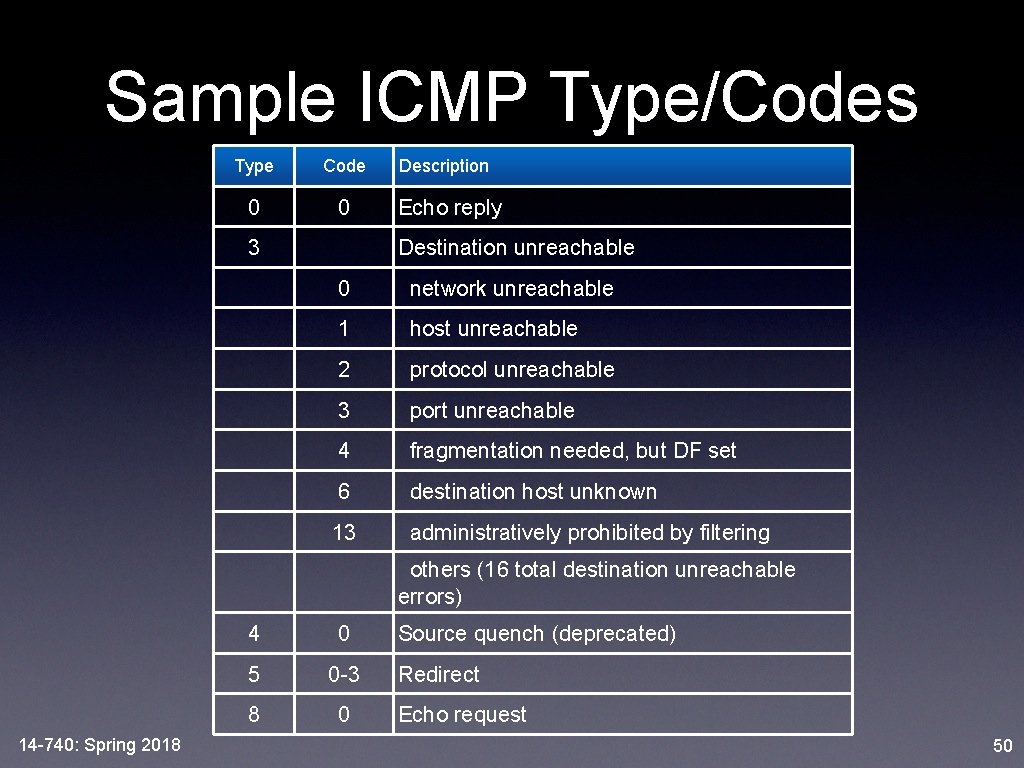
Sample ICMP Type/Codes Type Code 0 0 3 Description Echo reply Destination unreachable 0 network unreachable 1 host unreachable 2 protocol unreachable 3 port unreachable 4 fragmentation needed, but DF set 6 destination host unknown 13 administratively prohibited by filtering others (16 total destination unreachable errors) 14 -740: Spring 2018 4 0 5 0 -3 8 0 Source quench (deprecated) Redirect Echo request 50
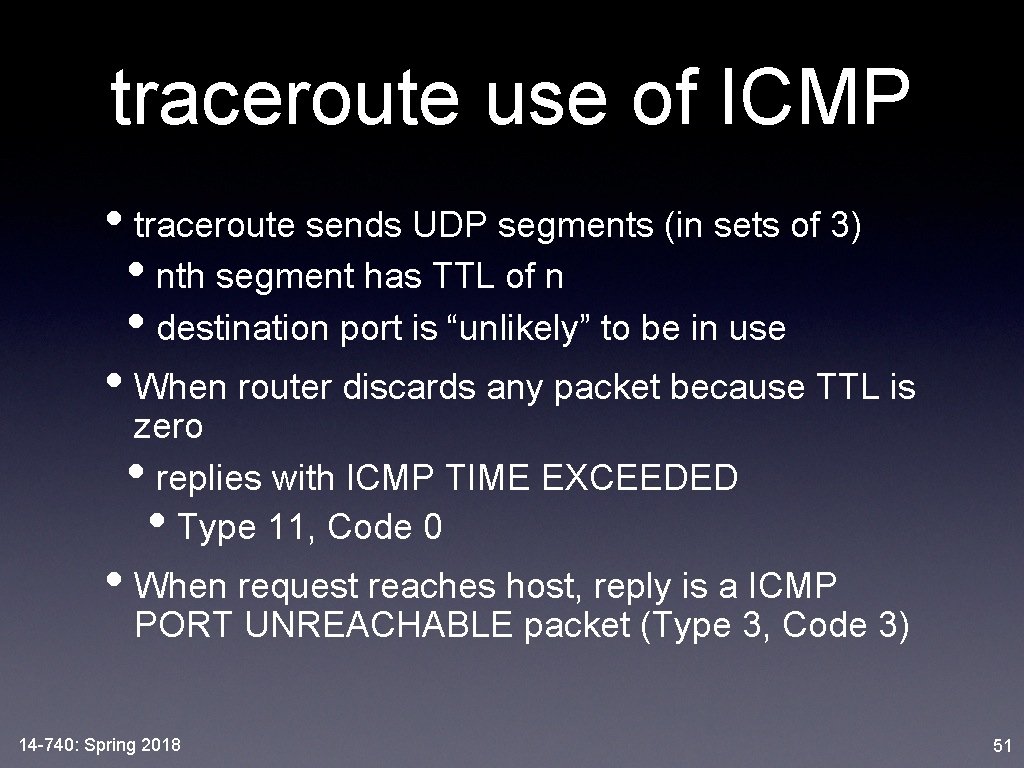
traceroute use of ICMP • traceroute sends UDP segments (in sets of 3) • nth segment has TTL of n • destination port is “unlikely” to be in use • When router discards any packet because TTL is zero • replies with ICMP TIME EXCEEDED • Type 11, Code 0 • When request reaches host, reply is a ICMP PORT UNREACHABLE packet (Type 3, Code 3) 14 -740: Spring 2018 51
What Layer? Is ICMP a Network-layer Protocol? • Messages used for communication between routers and end-hosts • Messages sent in an IP packet • Just like a UDP segment • Messages require special processing by the IP layer software on each router 14 -740: Spring 2018 52
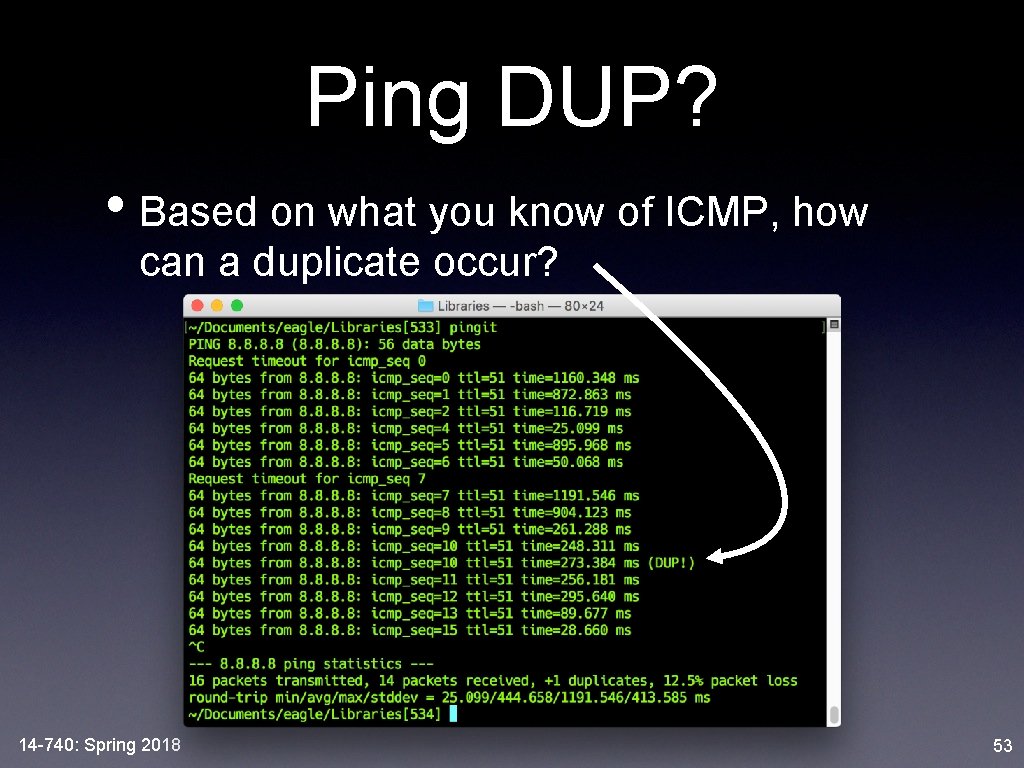
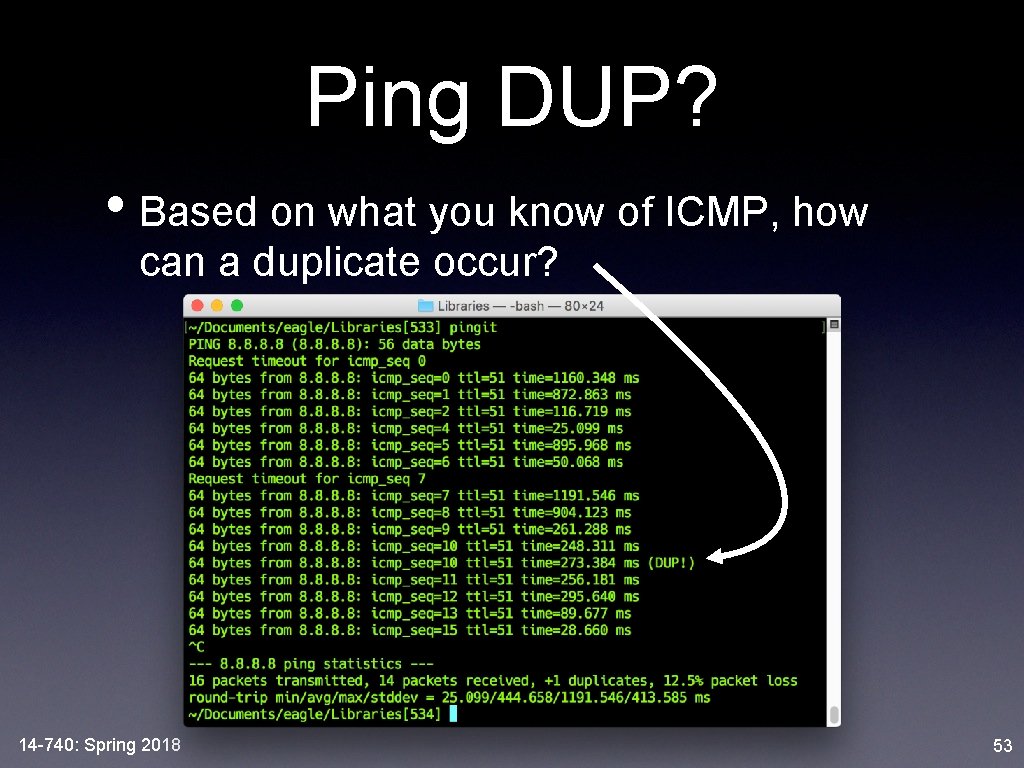
Ping DUP? • Based on what you know of ICMP, how can a duplicate occur? 14 -740: Spring 2018 53
Lesson Objectives • Now, you should be able to: • describe the mission, scope, addressing mechanism, data types and responsibilities of the Network Layer • describe the differences that would result from a connectionless or connection-oriented network • explain IPv 4, including advantages/disadvantages, datagram format, and packet-handling operations at each router 14 -740: Spring 2018 55
• You should be able to: • calculate the packets that result from an IPv 4 fragmentation scenario, including size, id, flags and offset fields • calculate IPv 4 address ranges from prefix notation and be able to apply the longest matching prefix rule to forwarding decisions • apply route aggregation to prefix scenarios • describe ICMP, including packet format, use of type/code fields for ping, traceroute, and error situations