The Generic Transformation from Standard Signatures to IdentityBased
The Generic Transformation from Standard Signatures to Identity-Based Aggregate Signatures Bei Liang, Hongda Li, Jinyong Chang
Identity-Based Aggregate Signatures
Identity-Based Aggregate Signatures PK MSK
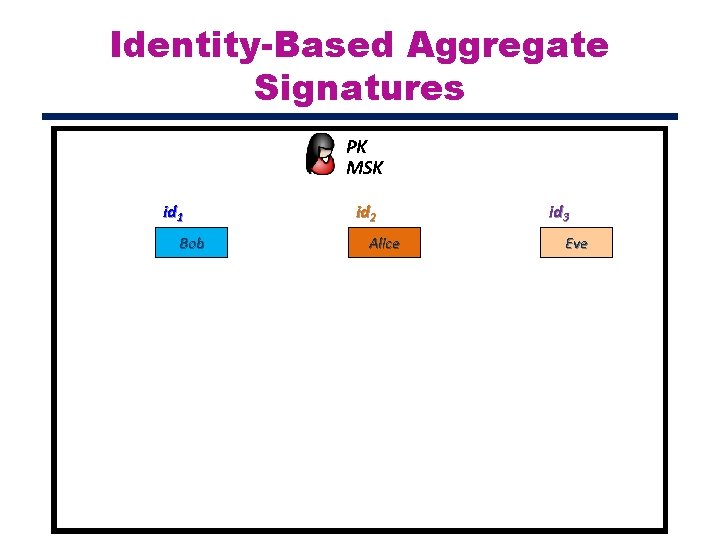
Identity-Based Aggregate Signatures PK MSK id 1 Bob id 2 Alice id 3 Eve
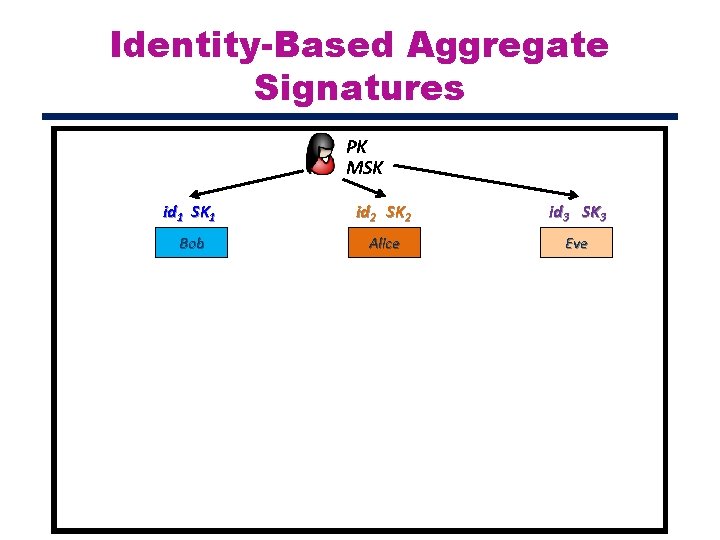
Identity-Based Aggregate Signatures PK MSK id 1 SK 1 id 2 SK 2 id 3 SK 3 Bob Alice Eve
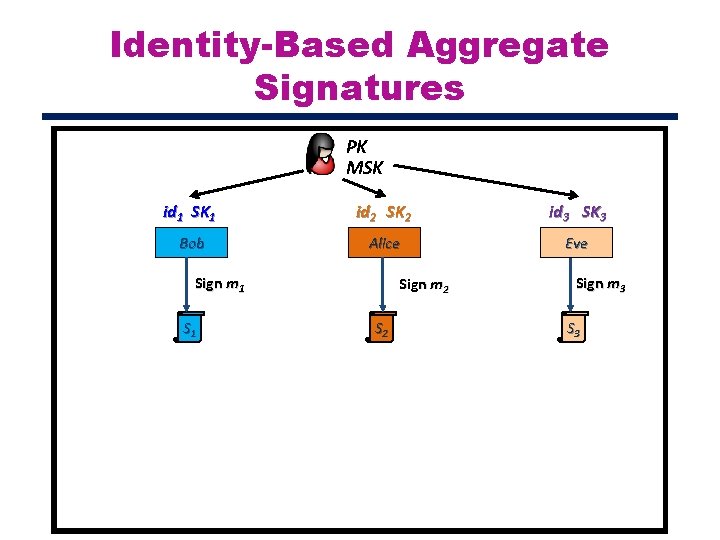
Identity-Based Aggregate Signatures PK MSK id 1 SK 1 id 2 SK 2 id 3 SK 3 Bob Alice Eve Sign m 1 Sign m 2 Sign m 3 S 3
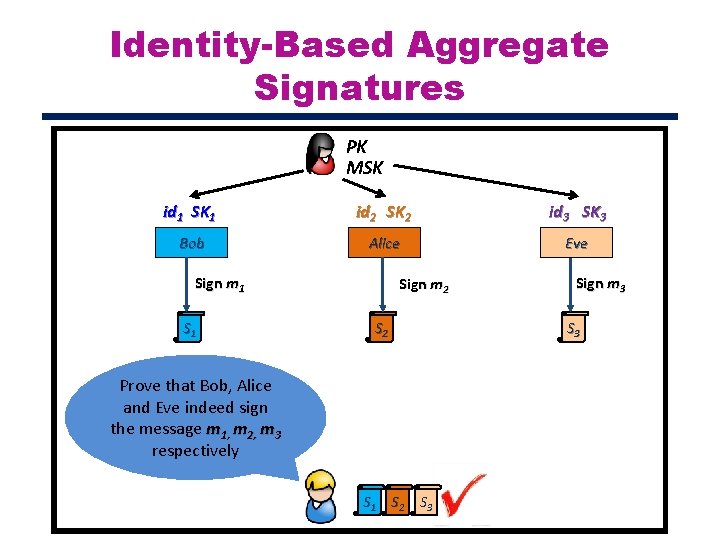
Identity-Based Aggregate Signatures PK MSK id 1 SK 1 id 2 SK 2 id 3 SK 3 Bob Alice Eve Sign m 1 Sign m 2 S 2 Prove that Bob, Alice and Eve indeed sign the message m 1, m 2, m 3 respectively S 1 S 2 S 3 Sign m 3 S 3
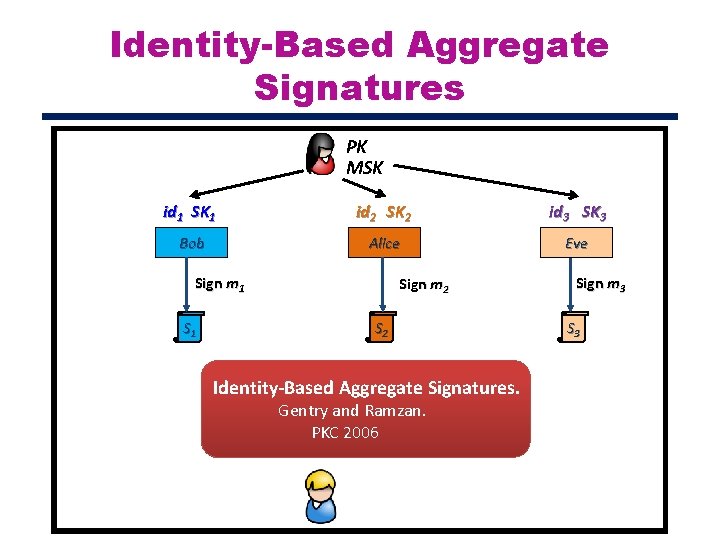
Identity-Based Aggregate Signatures PK MSK id 1 SK 1 id 2 SK 2 id 3 SK 3 Bob Alice Eve Sign m 1 Sign m 2 S 2 Identity-Based Aggregate Signatures. Gentry and Ramzan. PKC 2006 Sign m 3 S 3
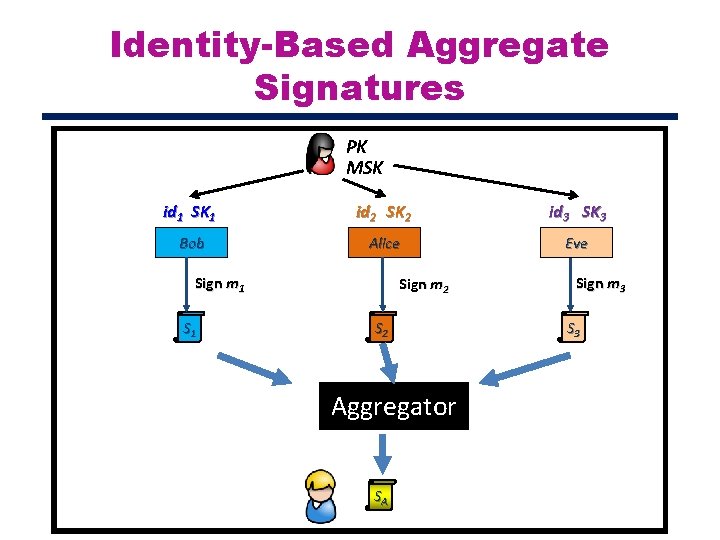
Identity-Based Aggregate Signatures PK MSK id 1 SK 1 id 2 SK 2 id 3 SK 3 Bob Alice Eve Sign m 1 Sign m 2 S 2 Aggregator SA Sign m 3 S 3
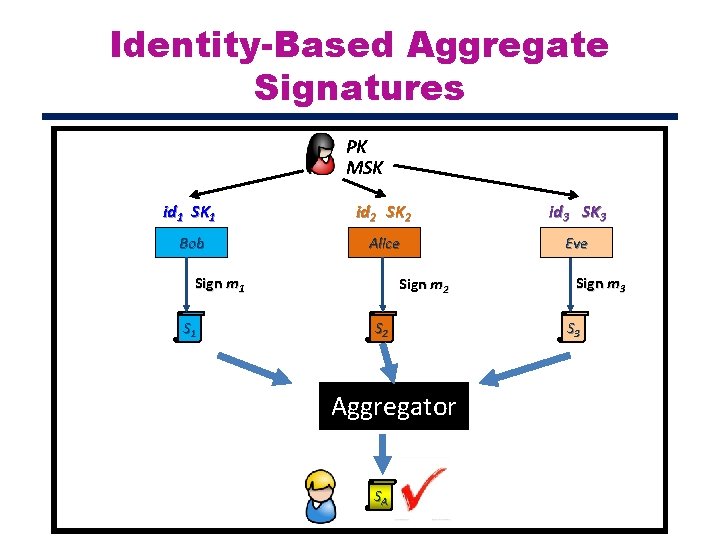
Identity-Based Aggregate Signatures PK MSK id 1 SK 1 id 2 SK 2 id 3 SK 3 Bob Alice Eve Sign m 1 Sign m 2 S 2 Aggregator SA Sign m 3 S 3
![Identity-Based Aggregate Signatures IBAS [GR 06] PKC 06 IBAS (with same common token) [BJ Identity-Based Aggregate Signatures IBAS [GR 06] PKC 06 IBAS (with same common token) [BJ](http://slidetodoc.com/presentation_image/30e4d2df1afe58732eda2daad259d3f6/image-11.jpg)
Identity-Based Aggregate Signatures IBAS [GR 06] PKC 06 IBAS (with same common token) [BJ 10] PKC 10 Sequential IBAS. [BGN+06] CCS 07 Unrestricted IBAS. [HSW 13] CRYPTO 13
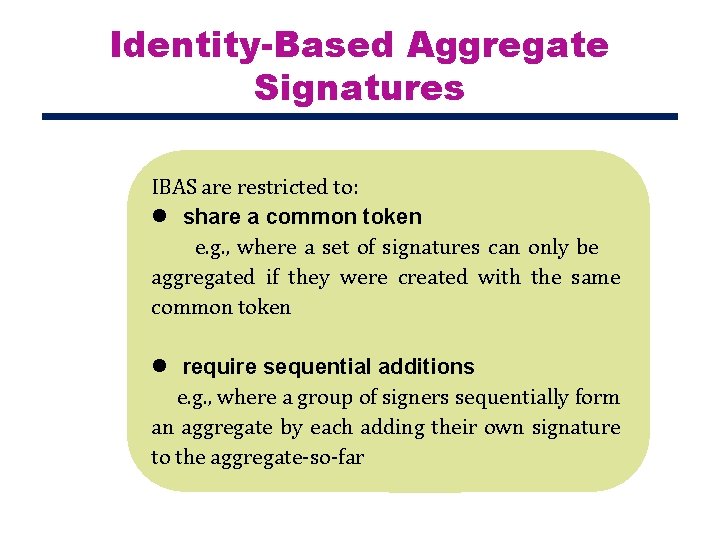
Identity-Based Aggregate Signatures IBAS are restricted to: l share a common token e. g. , where a set of signatures can only be aggregated if they were created with the same common token l require sequential additions e. g. , where a group of signers sequentially form an aggregate by each adding their own signature to the aggregate-so-far
Identity-Based Aggregate Signatures How to achieve identity-based aggregate signatures from standard signatures?
![Overview of our Approach Standard signature scheme Universal samplers [HJK+14] Identity-based signature Indistinguishability obfuscation Overview of our Approach Standard signature scheme Universal samplers [HJK+14] Identity-based signature Indistinguishability obfuscation](http://slidetodoc.com/presentation_image/30e4d2df1afe58732eda2daad259d3f6/image-14.jpg)
Overview of our Approach Standard signature scheme Universal samplers [HJK+14] Identity-based signature Indistinguishability obfuscation [HKW 14] Identity-based aggregate signature
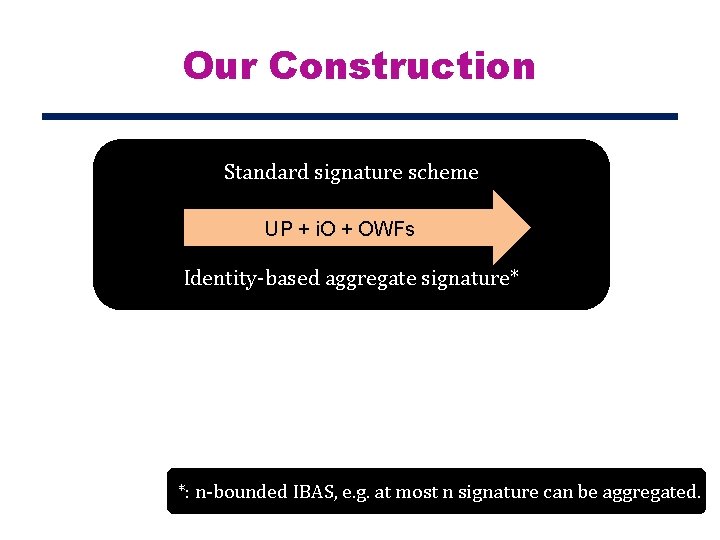
Our Construction Standard signature scheme UP + i. O + OWFs Identity-based aggregate signature* *: n-bounded IBAS, e. g. at most n signature can be aggregated.
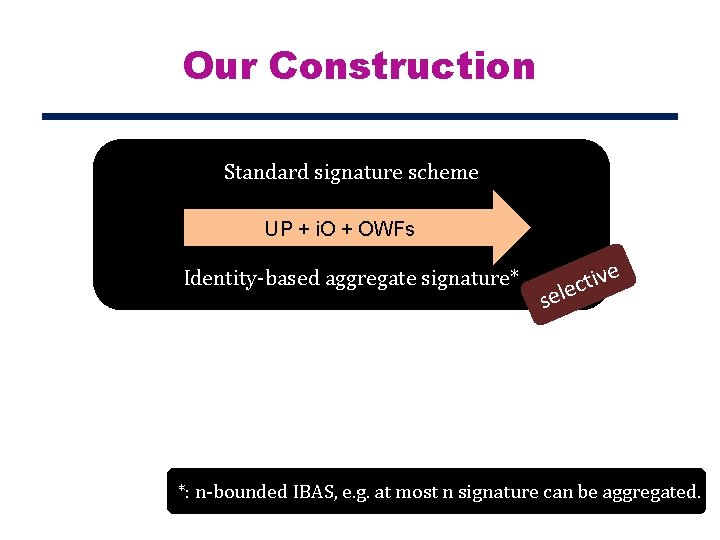
Our Construction Standard signature scheme UP + i. O + OWFs Identity-based aggregate signature* e v i t lec se *: n-bounded IBAS, e. g. at most n signature can be aggregated.
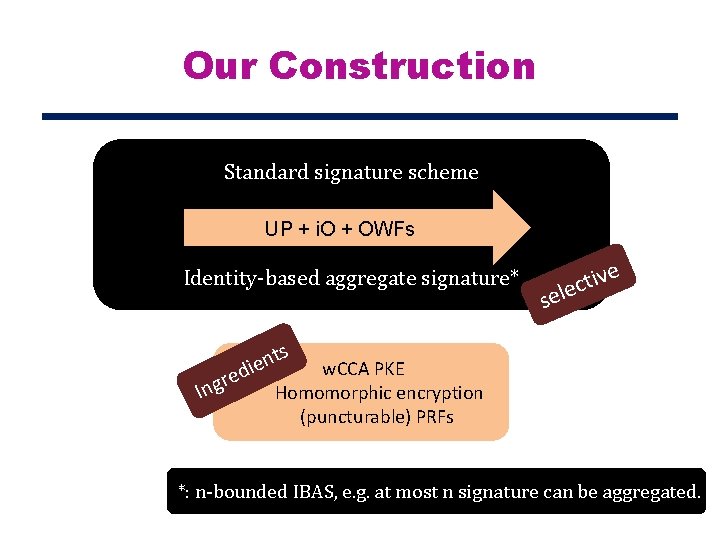
Our Construction Standard signature scheme UP + i. O + OWFs Identity-based aggregate signature* ngr I e v i t lec se s t n e edi w. CCA PKE Homomorphic encryption (puncturable) PRFs *: n-bounded IBAS, e. g. at most n signature can be aggregated.
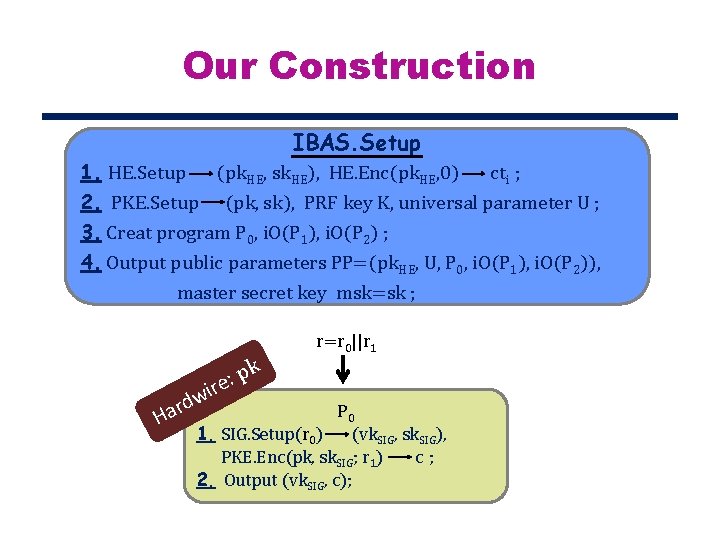
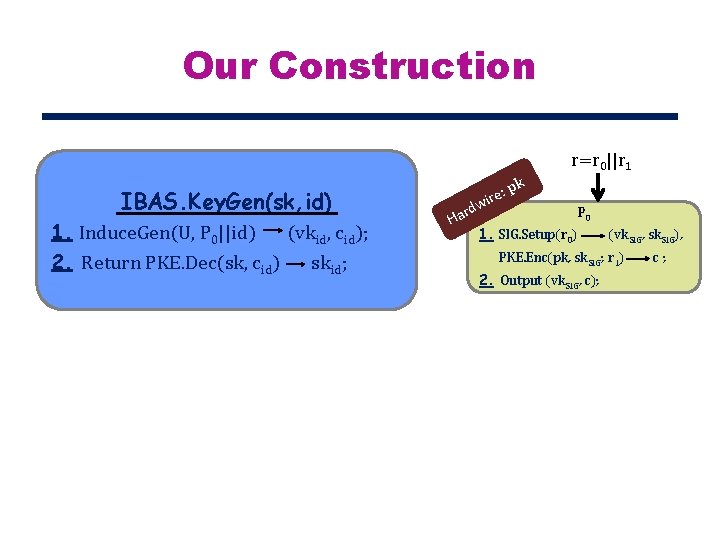
Our Construction IBAS. Setup 1. HE. Setup (pk. HE, sk. HE), HE. Enc(pk. HE, 0) cti ; 2. PKE. Setup (pk, sk), PRF key K, universal parameter U ; 3. Creat program P 0, i. O(P 1), i. O(P 2) ; 4. Output public parameters PP=(pk. HE, U, P 0, i. O(P 1), i. O(P 2)), master secret key msk=sk ; r=r 0||r 1 k p : re i H w ard P 0 1. SIG. Setup(r 0) (vk. SIG, sk. SIG), PKE. Enc(pk, sk. SIG; r 1) c; 2. Output (vk. SIG, c);
Our Construction r=r 0||r 1 IBAS. Key. Gen(sk, id) 1. Induce. Gen(U, P 0||id) (vkid, cid); 2. Return PKE. Dec(sk, cid) skid; rd Ha e: wir pk P 0 1. SIG. Setup(r 0) (vk. SIG, sk. SIG), PKE. Enc(pk, sk. SIG; r 1) 2. Output (vk. SIG, c); c;
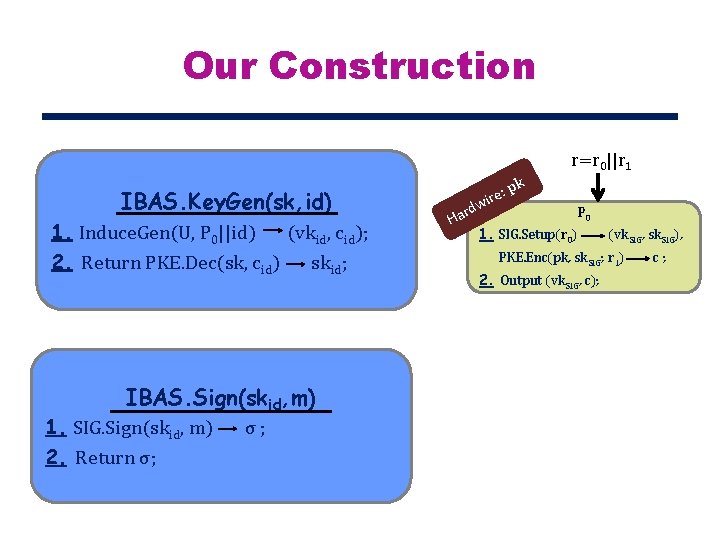
Our Construction r=r 0||r 1 IBAS. Key. Gen(sk, id) 1. Induce. Gen(U, P 0||id) (vkid, cid); 2. Return PKE. Dec(sk, cid) skid; IBAS. Sign(skid, m) 1. SIG. Sign(skid, m) 2. Return σ; rd Ha e: wir pk P 0 1. SIG. Setup(r 0) (vk. SIG, sk. SIG), PKE. Enc(pk, sk. SIG; r 1) 2. Output (vk. SIG, c); c;
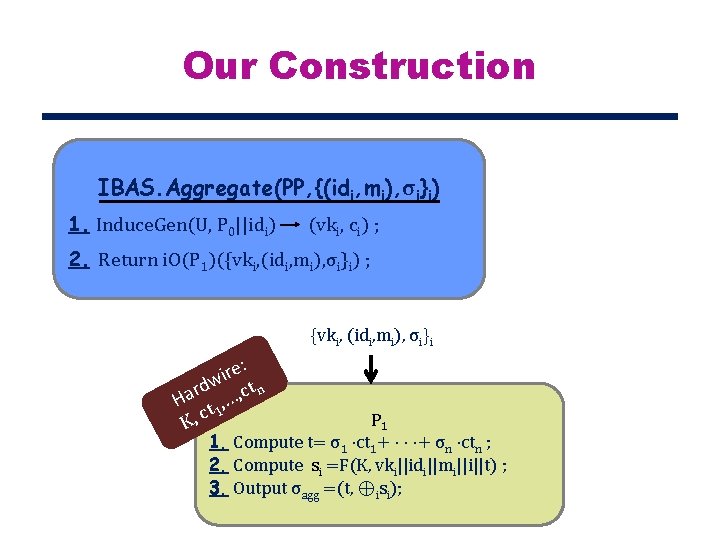
Our Construction IBAS. Aggregate(PP, {(idi, mi), σi}i) 1. Induce. Gen(U, P 0||idi) (vki, ci) ; 2. Return i. O(P 1)({vki, (idi, mi), σi}i) ; {vki, (idi, mi), σi}i e: r i rdw , ct n a H t , … 1 K, c P 1 1. Compute t= σ1 ·ct 1+ · · ·+ σn ·ctn ; 2. Compute si =F(K, vki||idi||mi||i||t) ; 3. Output σagg =(t, ⊕isi);
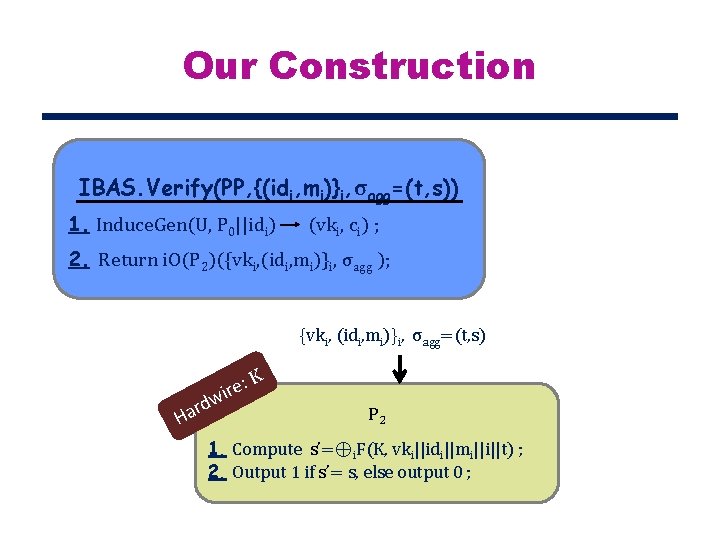
Our Construction IBAS. Verify(PP, {(idi, mi)}i, σagg=(t, s)) 1. Induce. Gen(U, P 0||idi) (vki, ci) ; 2. Return i. O(P 2)({vki, (idi, mi)}i, σagg ); {vki, (idi, mi)}i, σagg=(t, s) : K e wir rd a H P 2 1. Compute s’=⊕i. F(K, vki||idi||mi||i||t) ; 2. Output 1 if s’= s, else output 0 ;
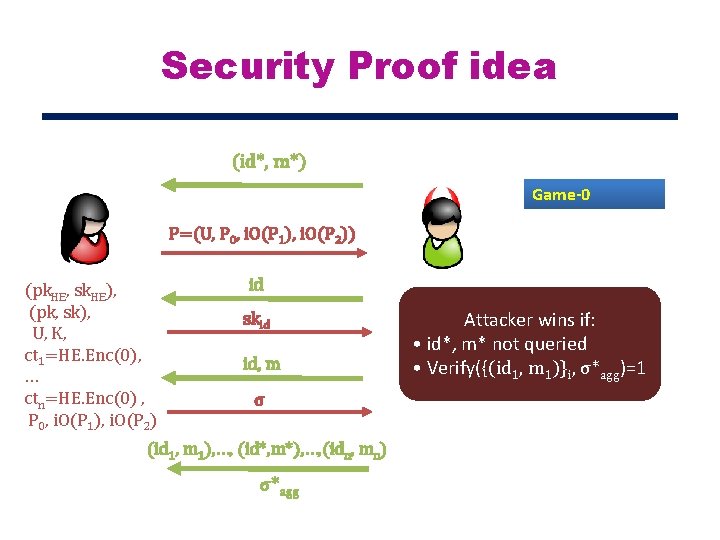
Security Proof idea (id*, m*) Game-0 P=(U, P 0, i. O(P 1), i. O(P 2)) (pk. HE, sk. HE), (pk, sk), U, K, ct 1=HE. Enc(0), … ctn=HE. Enc(0) , P 0, i. O(P 1), i. O(P 2) id skid id, m σ (id 1, m 1), …, (id*, m*), …, (idn, mn) σ*agg Attacker wins if: • id*, m* not queried • Verify({(id 1, m 1)}i, σ*agg)=1
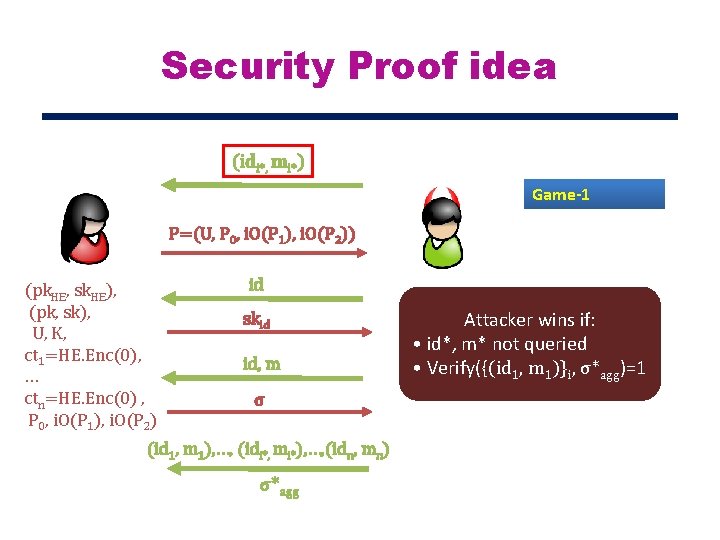
Security Proof idea (idi*, mi*) Game-1 P=(U, P 0, i. O(P 1), i. O(P 2)) (pk. HE, sk. HE), (pk, sk), U, K, ct 1=HE. Enc(0), … ctn=HE. Enc(0) , P 0, i. O(P 1), i. O(P 2) id skid id, m σ (id 1, m 1), …, (idi*, mi*), …, (idn, mn) σ*agg Attacker wins if: • id*, m* not queried • Verify({(id 1, m 1)}i, σ*agg)=1
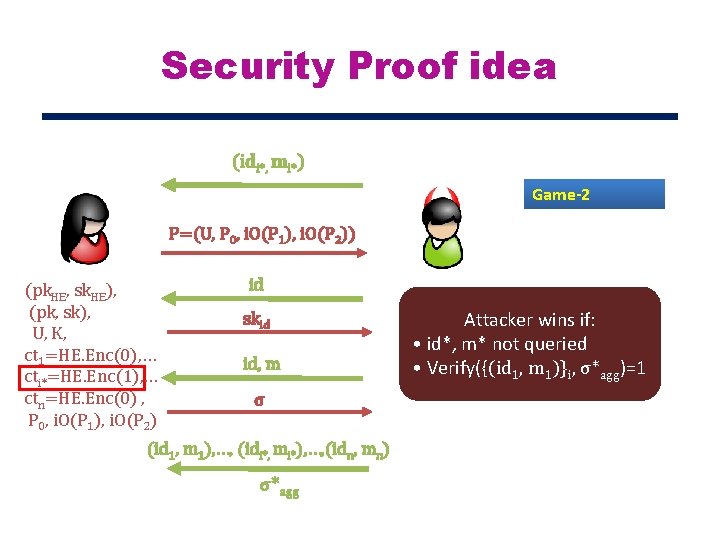
Security Proof idea (idi*, mi*) Game-2 P=(U, P 0, i. O(P 1), i. O(P 2)) (pk. HE, sk. HE), (pk, sk), U, K, ct 1=HE. Enc(0), … cti*=HE. Enc(1), … ctn=HE. Enc(0) , P 0, i. O(P 1), i. O(P 2) id skid id, m σ (id 1, m 1), …, (idi*, mi*), …, (idn, mn) σ*agg Attacker wins if: • id*, m* not queried • Verify({(id 1, m 1)}i, σ*agg)=1
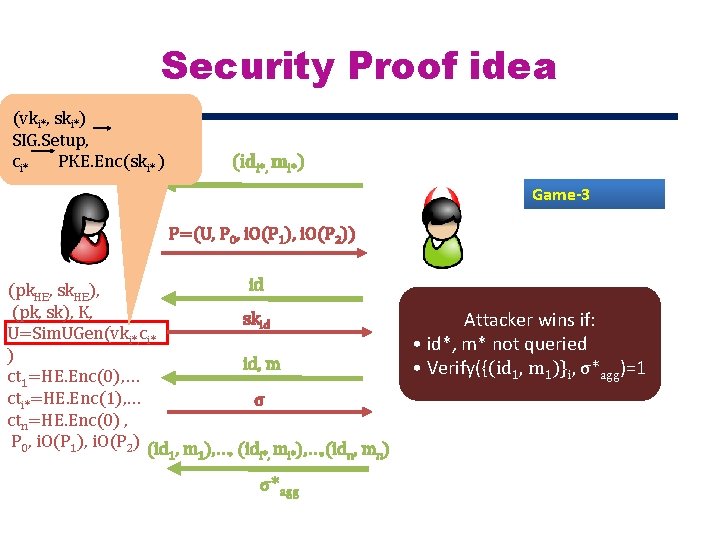
Security Proof idea (vki*, ski*) SIG. Setup, ci* PKE. Enc(ski* ) (idi*, mi*) Game-3 P=(U, P 0, i. O(P 1), i. O(P 2)) id (pk. HE, sk. HE), (pk, sk), K, skid U=Sim. UGen(vki*, ci* ) id, m ct 1=HE. Enc(0), … cti*=HE. Enc(1), … σ ctn=HE. Enc(0) , P 0, i. O(P 1), i. O(P 2) (id , m ), …, (id , m ) 1 1 i*, i* n n σ*agg Attacker wins if: • id*, m* not queried • Verify({(id 1, m 1)}i, σ*agg)=1
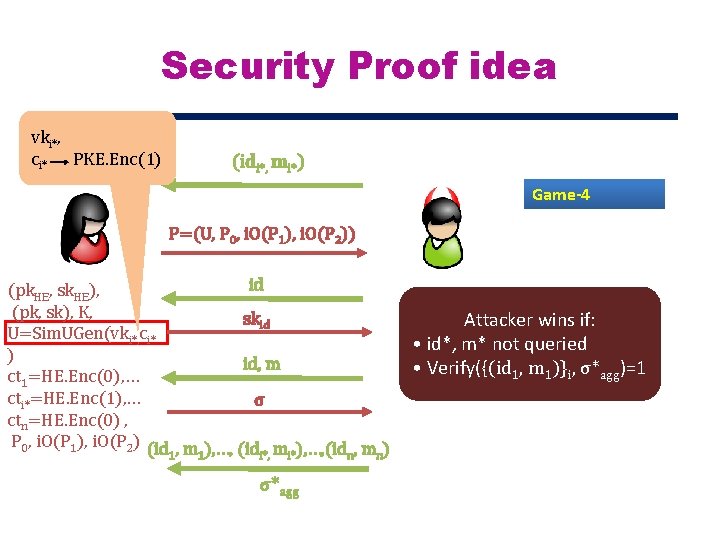
Security Proof idea vki*, ci* PKE. Enc(1) (idi*, mi*) Game-4 P=(U, P 0, i. O(P 1), i. O(P 2)) id (pk. HE, sk. HE), (pk, sk), K, skid U=Sim. UGen(vki*, ci* ) id, m ct 1=HE. Enc(0), … cti*=HE. Enc(1), … σ ctn=HE. Enc(0) , P 0, i. O(P 1), i. O(P 2) (id , m ), …, (id , m ) 1 1 i*, i* n n σ*agg Attacker wins if: • id*, m* not queried • Verify({(id 1, m 1)}i, σ*agg)=1
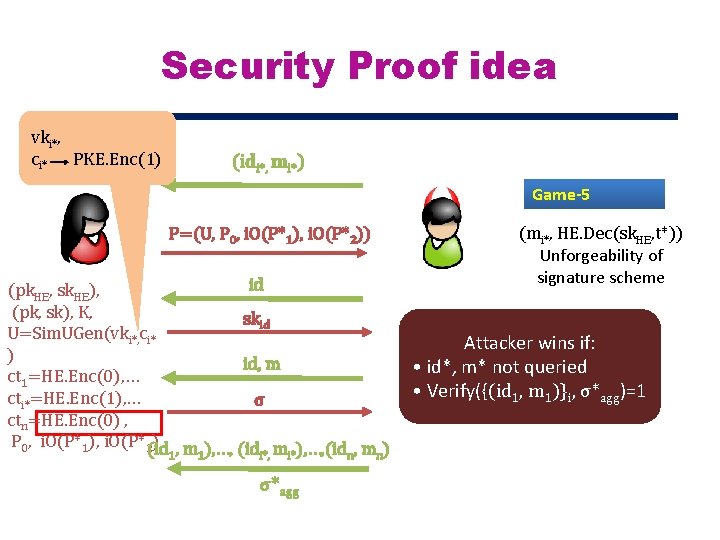
Security Proof idea vki*, ci* PKE. Enc(1) (idi*, mi*) Game-5 P=(U, P 0, i. O(P*1), i. O(P*2)) id (pk. HE, sk. HE), (pk, sk), K, skid U=Sim. UGen(vki*, ci* ) id, m ct 1=HE. Enc(0), … cti*=HE. Enc(1), … σ ctn=HE. Enc(0) , P 0, i. O(P*1), i. O(P*2(id ) , m ), …, (id , m ) 1 1 i*, i* n n σ*agg (mi*, HE. Dec(sk. HE, t*)) Unforgeability of signature scheme Attacker wins if: • id*, m* not queried • Verify({(id 1, m 1)}i, σ*agg)=1

THANK YOU!
- Slides: 29