The Evolution of Identity Management Dr Stefan Brands
The Evolution of Identity Management Dr. Stefan Brands February 18, 2005 © Copyright 2004, Credentica – all rights reserved
Part I The evolution of conventional I&AM © Copyright 2004, Credentica 2
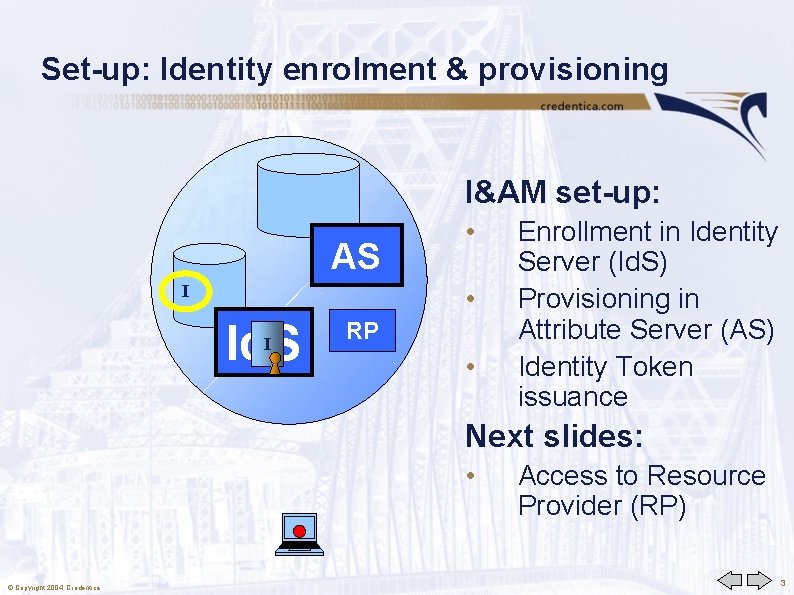
Set-up: Identity enrolment & provisioning I: a 1, a 2 , … AS I I: I&AM set-up: • • Id. S I RP • Enrollment in Identity Server (Id. S) Provisioning in Attribute Server (AS) Identity Token issuance Next slides: • © Copyright 2004, Credentica Access to Resource Provider (RP) 3
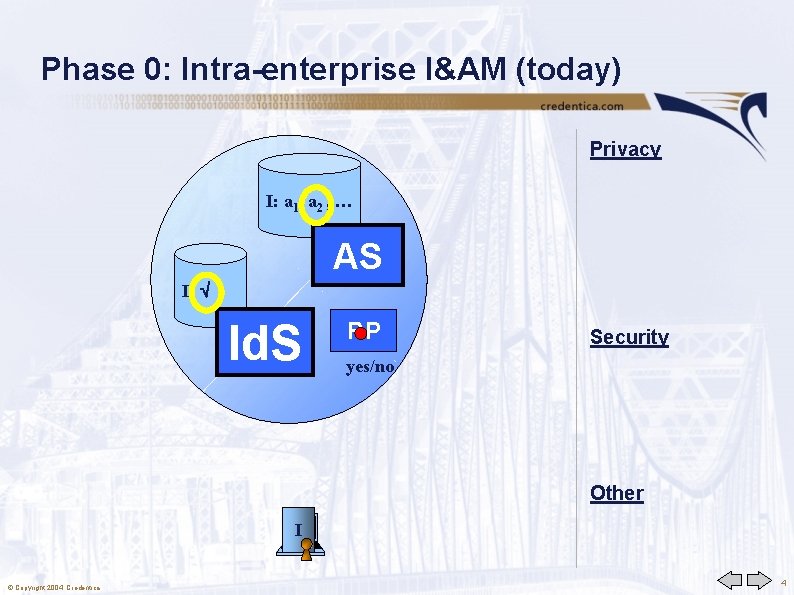
Phase 0: Intra-enterprise I&AM (today) Privacy I: a 1, a 2 , … AS I: Id. S RP Security yes/no Other I © Copyright 2004, Credentica 4
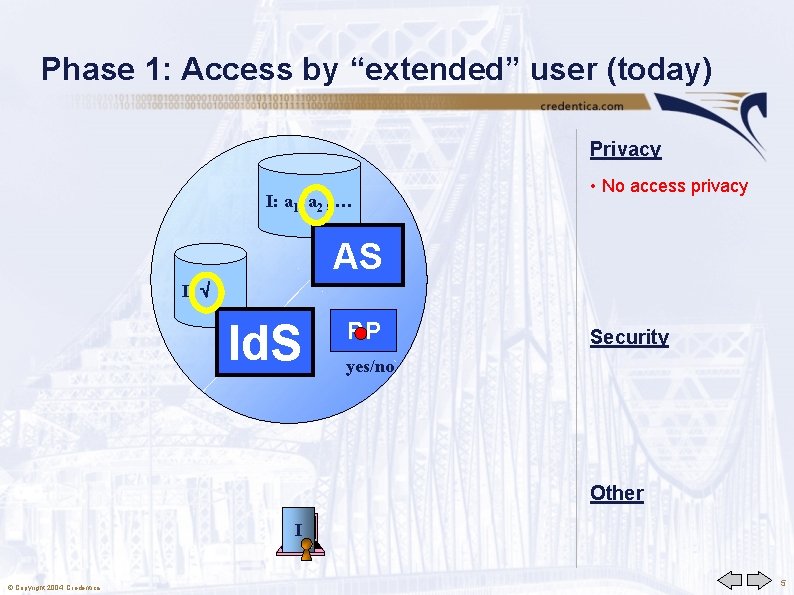
Phase 1: Access by “extended” user (today) Privacy I: a 1, a 2 , … • No access privacy AS I: Id. S RP Security yes/no Other I © Copyright 2004, Credentica 5
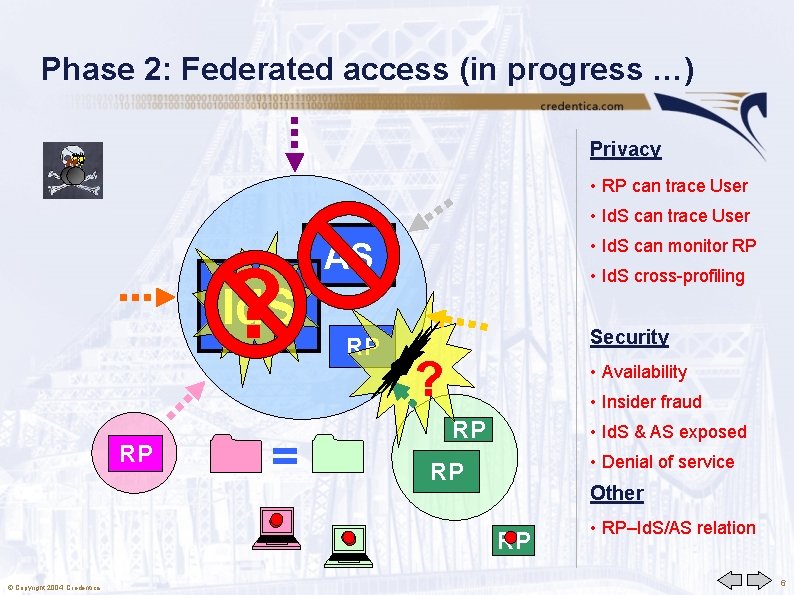
Phase 2: Federated access (in progress …) Privacy • RP can trace User • Id. S can trace User ? Id. S RP = • Id. S can monitor RP AS RP • Id. S cross-profiling Security ? • Availability • Insider fraud RP • Id. S & AS exposed • Denial of service RP Other RP © Copyright 2004, Credentica • RP–Id. S/AS relation 6
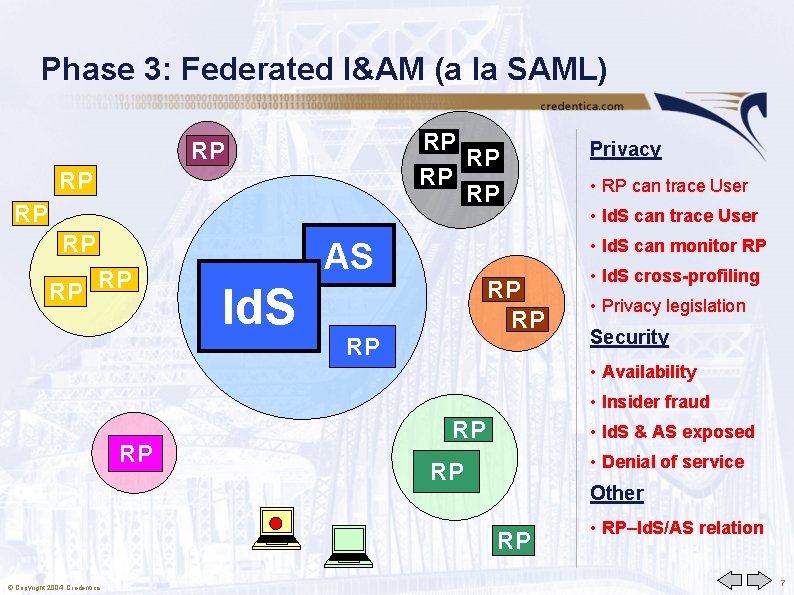
Phase 3: Federated I&AM (a la SAML) RP RP RP • RP can trace User • Id. S can monitor RP AS Id. S Privacy RP RP RP • Id. S cross-profiling • Privacy legislation Security • Availability • Insider fraud RP RP • Id. S & AS exposed • Denial of service RP Other RP © Copyright 2004, Credentica • RP–Id. S/AS relation 7
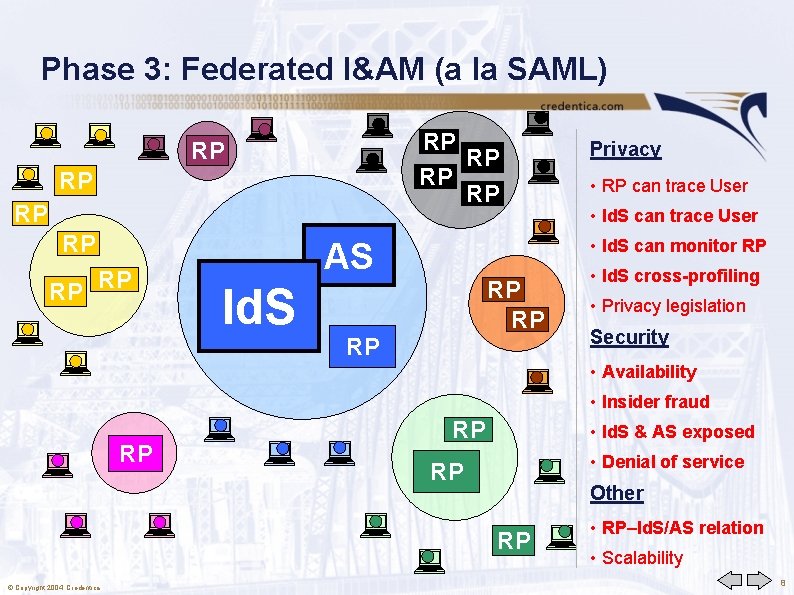
Phase 3: Federated I&AM (a la SAML) RP RP RP • RP can trace User • Id. S can monitor RP AS Id. S Privacy RP RP RP • Id. S cross-profiling • Privacy legislation Security • Availability • Insider fraud RP RP • Id. S & AS exposed • Denial of service RP Other RP © Copyright 2004, Credentica • RP–Id. S/AS relation • Scalability 8

Phase 4: Data sharing a la Liberty Alliance RP RP RP • RP can trace User • Id. S can monitor RP AS Id. S Privacy RP RP RP • Id. S cross-profiling • Privacy legislation Security • Availability • Insider fraud RP RP • Id. S & AS exposed • Denial of service RP Other RP © Copyright 2004, Credentica • RP–Id. S/AS relation • Scalability 9
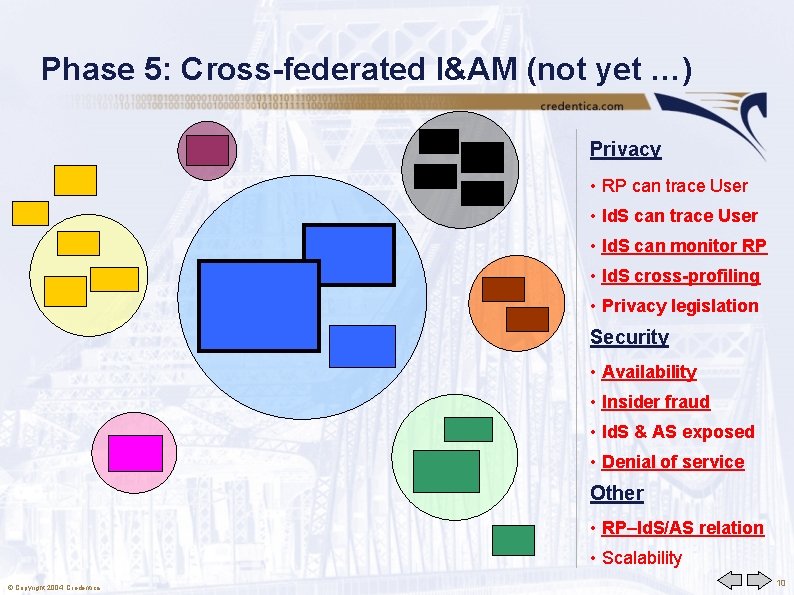
Phase 5: Cross-federated I&AM (not yet …) Privacy • RP can trace User • Id. S can monitor RP • Id. S cross-profiling • Privacy legislation Security • Availability • Insider fraud • Id. S & AS exposed • Denial of service Other • RP–Id. S/AS relation • Scalability © Copyright 2004, Credentica 10

Phase 5: Cross-federated I&AM (not yet …) Privacy • RP can trace User • Id. S can monitor RP Id. P • Id. S cross-profiling • Privacy legislation Security • Availability • Insider fraud • Id. S & AS exposed • Denial of service Other • RP–Id. S/AS relation • Scalability © Copyright 2004, Credentica 11
Part II Solution with Digital Credentials © Copyright 2004, Credentica 12

Digital Credentials • The digital equivalent of real-world objects issued by “trusted” issuers: Driver licenses, passports, stamps, coupons, entitlements, cash, ballots, credit report data, health record entries, …. New “credentials” that have no real-world equivalent • • • Unique security, privacy, and efficiency features Independent “sliders” – pick according to application needs Traditional digital certificate techniques do not work • • – – • Inescapable systemic identification, security problems, inefficient Note: Encryption only protects against content wiretapping Security is tied to the “attribute” data itself, so that the credential information can flow anywhere • © Copyright 2004, Credentica Accomplished through modern cryptographic techniques 13
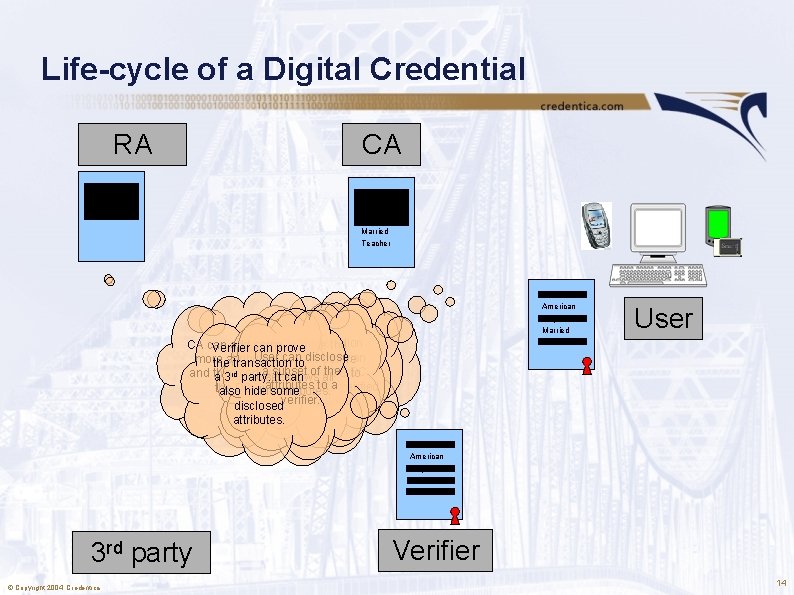
Life-cycle of a Digital Credential RA CA Alice American 23 y. o. Married Teacher Alice American 23 y. o. Married CA can add some Can. Registration hide the Verifier can prove User can Authority can more attributes before the transaction todisclose a subset of the prepare a DC and then passing theall. DC to a 3 rd certifies party. It can User knows attributes to a with some verified the DC. the CA. also hide thesome attributes. verifier. user attributes. disclosed attributes. User Teacher Alice American 23 y. o. Married Teacher 3 rd party © Copyright 2004, Credentica Verifier 14
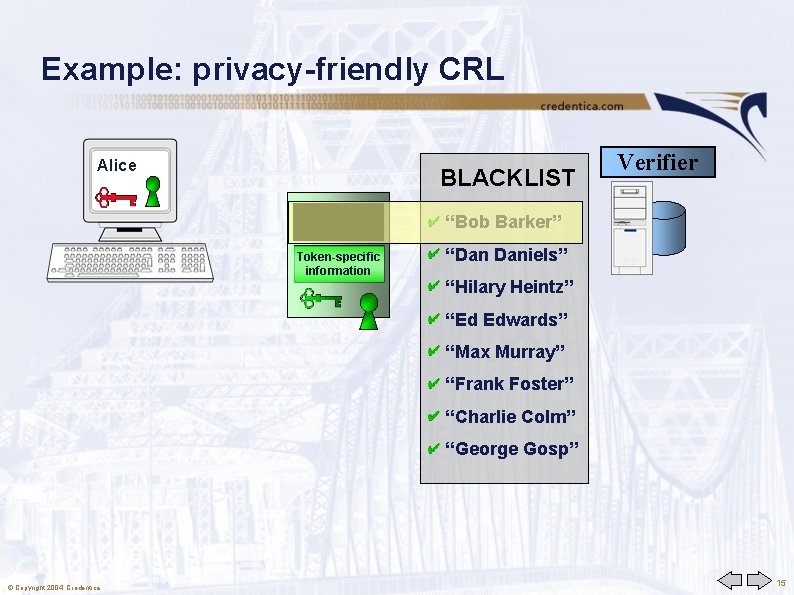
Example: privacy-friendly CRL Alice BLACKLIST Alice Smith “Bob Barker” Token-specific information “Dan Daniels” Verifier “Hilary Heintz” “Ed Edwards” “Max Murray” “Frank Foster” “Charlie Colm” “George Gosp” © Copyright 2004, Credentica 15

Example: privacy-friendly blacklist Alice BLACKLIST Verifier “Bob Barker” Token-specific information “Dan Daniels” “Hilary Heintz” “Ed Edwards” Alice Smith “Alice Smith” “Frank Foster” “Charlie Colm” “George Gosp” © Copyright 2004, Credentica 16
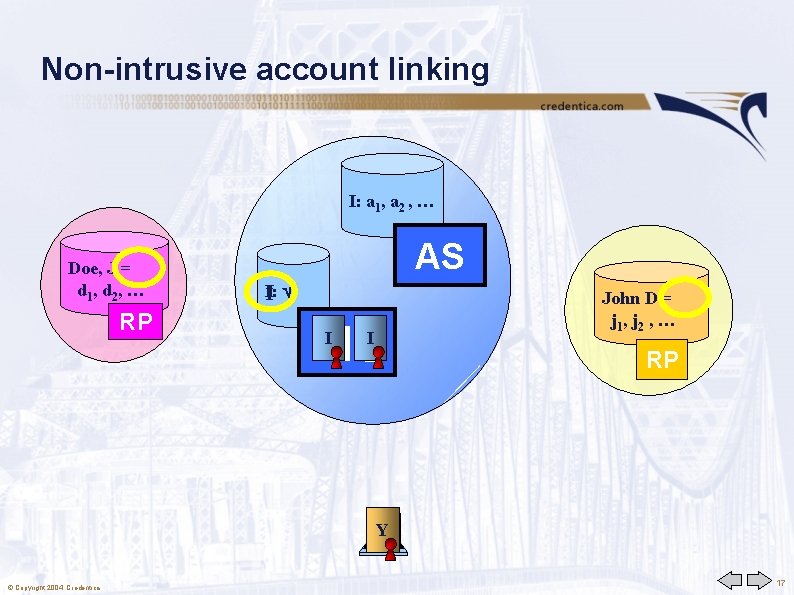
Non-intrusive account linking I: a 1, a 2 , … Doe, J = X d 1 , d 2 , … RP AS I I: Id. S I I John D = Y j 1 , j 2 , … RP Y X I © Copyright 2004, Credentica 17
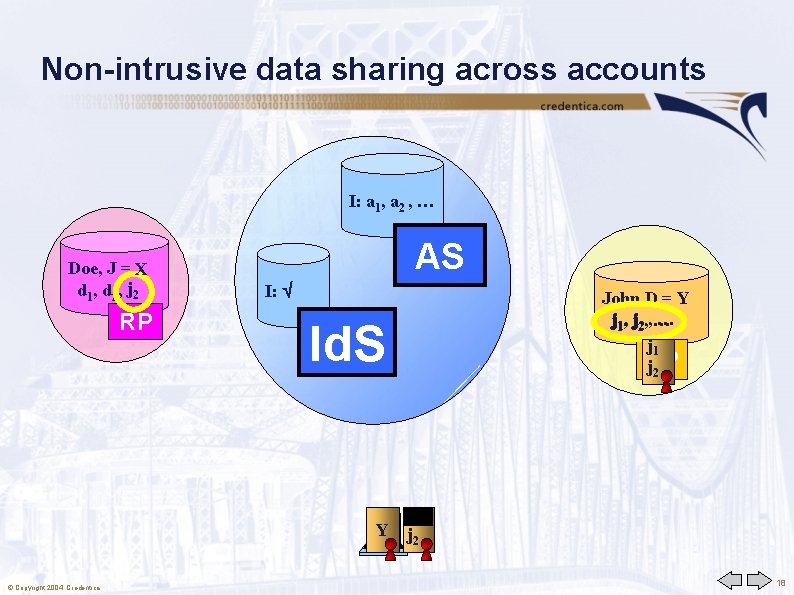
Non-intrusive data sharing across accounts I: a 1, a 2 , … Doe, J = X d 1, d 2, j… 2 RP AS I: Id. S John D = Y … j 1, j 2, , … j 1 RP j 2 j 1 Y j 2 X © Copyright 2004, Credentica 18
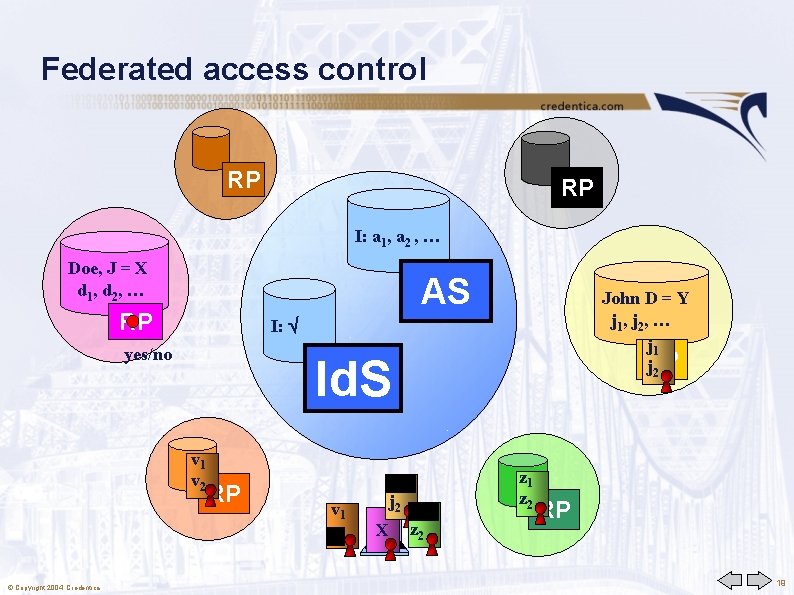
Federated access control RP RP I: a 1, a 2 , … Doe, J = X d 1 , d 2 , … AS RP I: yes/no Id. S v 1 v 2 © Copyright 2004, Credentica John D = Y j 1 , j 2 , … j 1 RP j 2 RP v 1 v 2 j 1 j 2 z 1 X z 2 z 1 z 2 RP 19

Federated security services RP RP I: a 1, a 2 , … Doe, J = X d 1 , d 2 , … AS RP CRL John D = Y Y j 1 , j 2 , … I I: RP Id. S I I CRL I I X=Y RP Y X © Copyright 2004, Credentica ABUSE RP 20
- Slides: 20