The Definitive Coronavirus Cyber Security for Management Presentation
The Definitive ‘Coronavirus Cyber Security for Management’ Presentation Template
How We’ve Built this Template • Cynet serves a global install based of hundreds of customers across all industries, geolocations and sizes. Our constant interaction with the security decision makers among our customers provided us with unique visibility into both their security needs, as well as to the common challenges they encounter to communicate these needs to the executive management. • Cynet is the provider of Cynet 360, the world’s first Autonomous Breach Protection Platform that consolidates and automates endpoint, network and user protection across the full security lifecycle: proactive monitoring and control, attack prevention and detection, and response orchestration. Cynet 360 technology is complemented and enhanced by Cy. Ops Managed Detection and Response (MDR) service, which is included in Cynet 360 offering without additional payment. • By natively integrating all these capabilities into a single platform, Cynet 360 eliminates the need to manually deploy and integrate multiple point products. Cynet 360 enables security teams to conduct all their operations from a single console, introducing simplicity, speed and efficiency, that translate into an unprecedented level of breach protection. • Visit the Cynet 360 website to learn more on how to introduce unmatched simplicity, speed and robustness to your environment’s security The Definitive Coronavirus Cyber Security for Management 2

Template Walkthrough Guide Coronavirus Related Cyber Threats - overview on the threats that emergeintensify due to the imposed coronavirus quarantine. You can use this slide as is, or omitadd threats based on your first hand experience and your organization’s needs. Slide 5 Slide 6 Slide 7 Overview on the threats that emergeintensify due to the imposed coronavirus quarantine. You can use this slide as is, or omitadd threats based on your first hand experience and your organization’s needs. Here you map the threats to tangible risks. The organization context column is left empty for you to fill based on your organization’s needs. Concrete layout of what you have now in terms of products, internal team and services along with their annual cost. Coronavirus Related Cyber Threats Translating Cyber Threats to Business Disruption Cyber Protections in Place The Definitive Coronavirus Cyber Security for Management 3
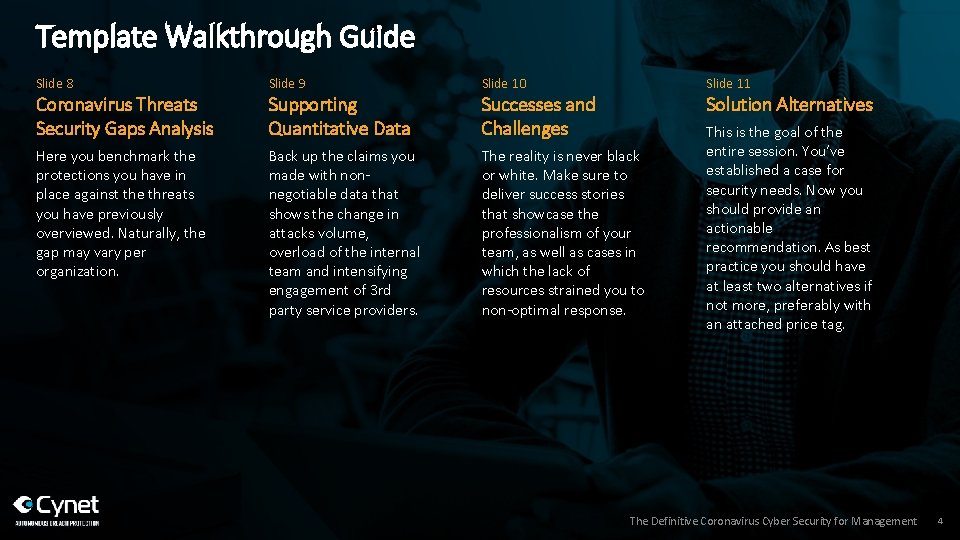
Template Walkthrough Guide Slide 8 Coronavirus Threats Security Gaps Analysis Here you benchmark the protections you have in place against the threats you have previously overviewed. Naturally, the gap may vary per organization. Slide 9 Supporting Quantitative Data Back up the claims you made with nonnegotiable data that shows the change in attacks volume, overload of the internal team and intensifying engagement of 3 rd party service providers. Slide 10 Slide 11 The reality is never black or white. Make sure to deliver success stories that showcase the professionalism of your team, as well as cases in which the lack of resources strained you to non-optimal response. This is the goal of the entire session. You’ve established a case for security needs. Now you should provide an actionable recommendation. As best practice you should have at least two alternatives if not more, preferably with an attached price tag. Successes and Challenges Solution Alternatives The Definitive Coronavirus Cyber Security for Management 4

Session Agenda › Coronavirus Related Cyber Threats › Translating Cyber Threats to Business Disruption › Cyber Protections in Place › Coronavirus Threats Security Gaps Analysis › Supporting Quantitative Data › Successes and Challenges › Solution Alternatives 2020 Security Plan Template 5
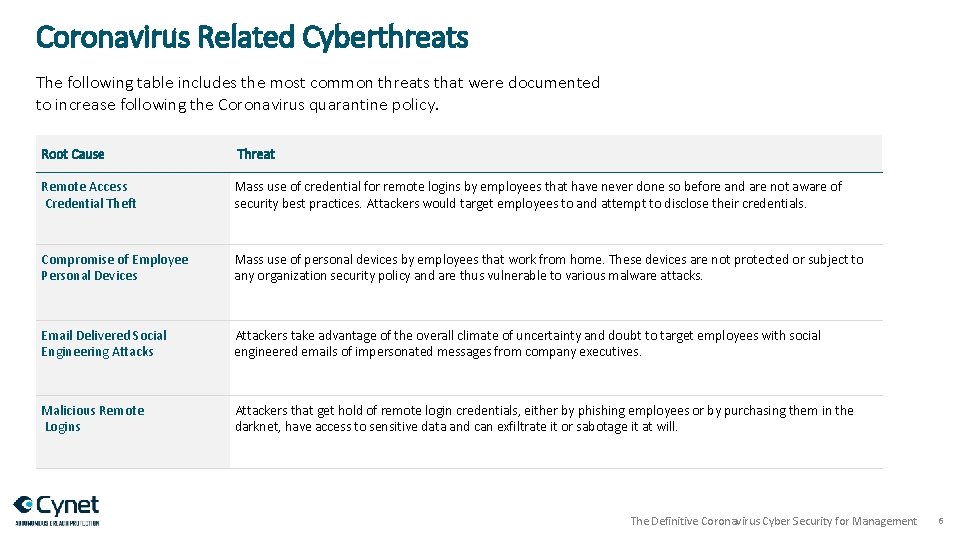
Coronavirus Related Cyberthreats The following table includes the most common threats that were documented to increase following the Coronavirus quarantine policy. Root Cause Threat Remote Access Credential Theft Mass use of credential for remote logins by employees that have never done so before and are not aware of security best practices. Attackers would target employees to and attempt to disclose their credentials. Compromise of Employee Personal Devices Mass use of personal devices by employees that work from home. These devices are not protected or subject to any organization security policy and are thus vulnerable to various malware attacks. Email Delivered Social Engineering Attacks Attackers take advantage of the overall climate of uncertainty and doubt to target employees with social engineered emails of impersonated messages from company executives. Malicious Remote Logins Attackers that get hold of remote login credentials, either by phishing employees or by purchasing them in the darknet, have access to sensitive data and can exfiltrate it or sabotage it at will. The Definitive Coronavirus Cyber Security for Management 6
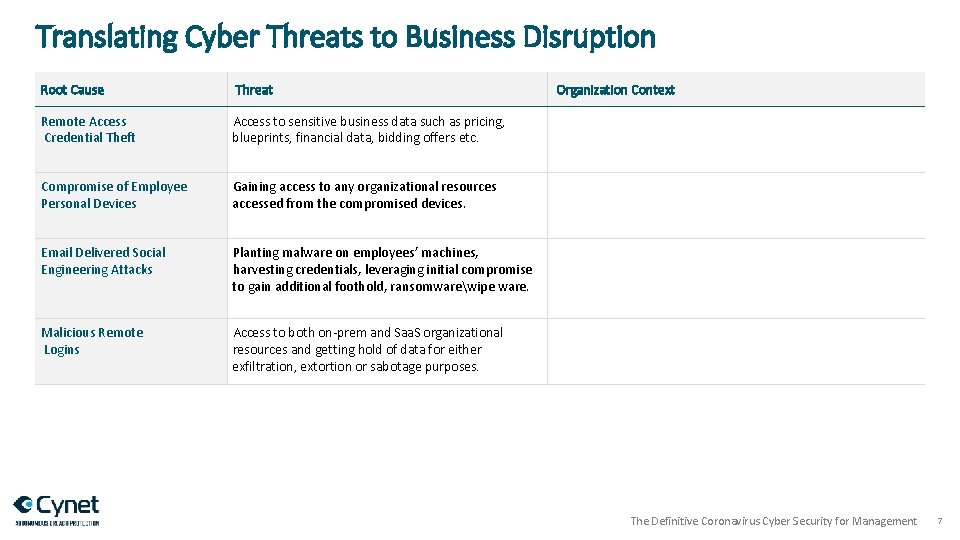
Translating Cyber Threats to Business Disruption Root Cause Threat Remote Access Credential Theft Access to sensitive business data such as pricing, blueprints, financial data, bidding offers etc. Compromise of Employee Personal Devices Gaining access to any organizational resources accessed from the compromised devices. Email Delivered Social Engineering Attacks Planting malware on employees’ machines, harvesting credentials, leveraging initial compromise to gain additional foothold, ransomwarewipe ware. Malicious Remote Logins Access to both on-prem and Saa. S organizational resources and getting hold of data for either exfiltration, extortion or sabotage purposes. Organization Context The Definitive Coronavirus Cyber Security for Management 7
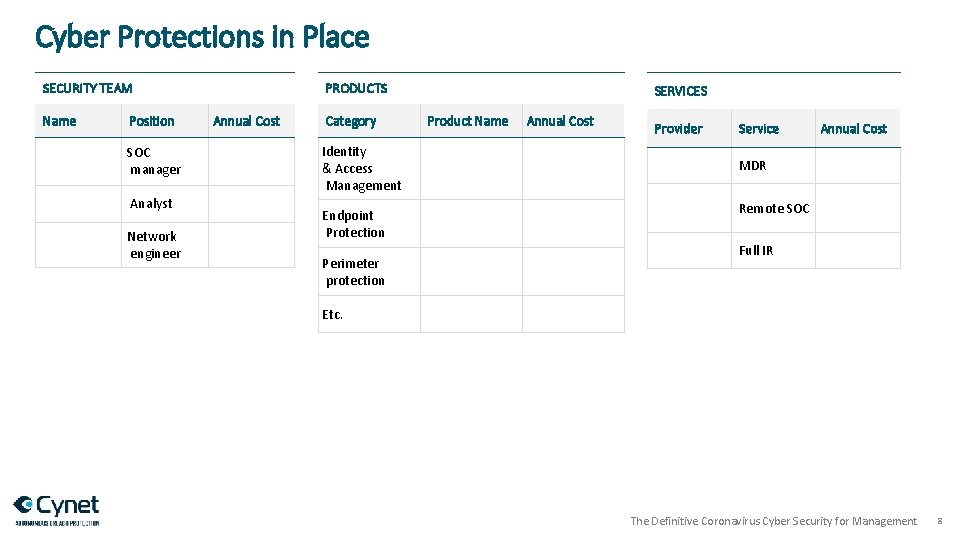
Cyber Protections in Place PRODUCTS SECURITY TEAM Name Position SOC manager Analyst Network engineer Annual Cost Category Identity & Access Management Endpoint Protection Perimeter protection SERVICES Product Name Annual Cost Provider Service Annual Cost MDR Remote SOC Full IR Etc. The Definitive Coronavirus Cyber Security for Management 8
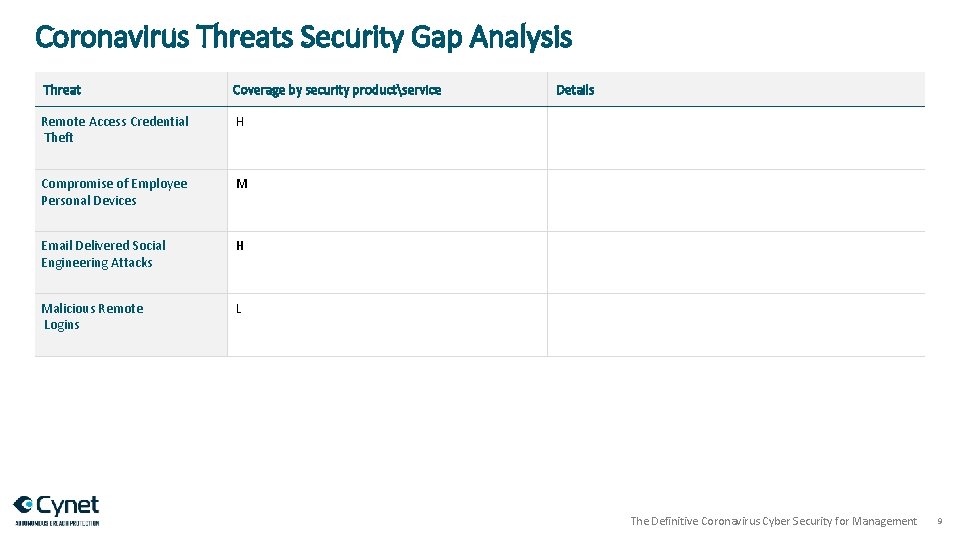
Coronavirus Threats Security Gap Analysis Threat Coverage by security productservice Remote Access Credential Theft H Compromise of Employee Personal Devices M Email Delivered Social Engineering Attacks H Malicious Remote Logins L Details The Definitive Coronavirus Cyber Security for Management 9
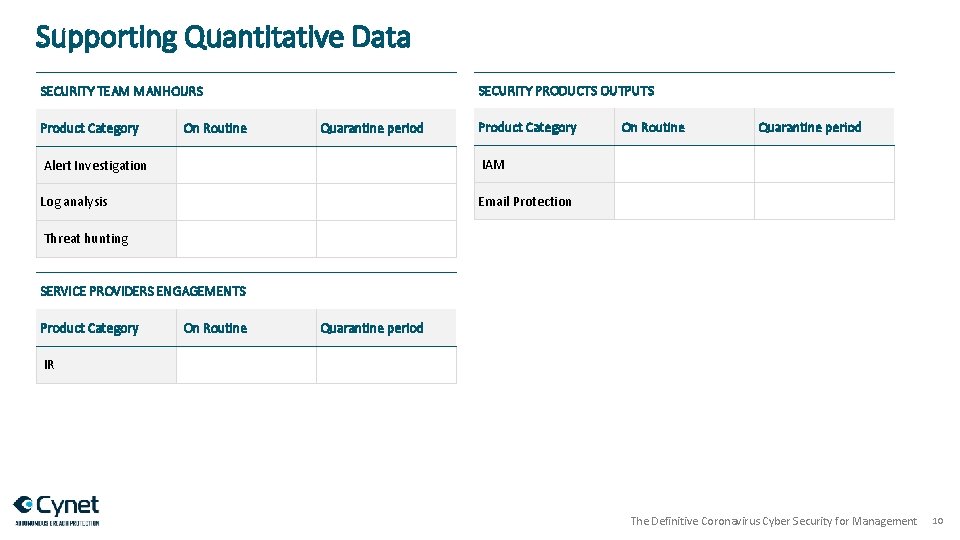
Supporting Quantitative Data SECURITY PRODUCTS OUTPUTS SECURITY TEAM MANHOURS Product Category On Routine Quarantine period Product Category Alert Investigation IAM Log analysis Email Protection On Routine Quarantine period Threat hunting SERVICE PROVIDERS ENGAGEMENTS Product Category On Routine Quarantine period IR The Definitive Coronavirus Cyber Security for Management 10
Successes and Challenges SUCCESS Case Study Title Description ProductTeam MemberService Provider CHALLENGE Case Study Title The Definitive Coronavirus Cyber Security for Management 11
Solutions Alternatives Root Cause Addressed Risk AdvantagesDrawbacks Overall Cost Security Technology Security Staff Security Services The Definitive Coronavirus Cyber Security for Management 12

THANK YOU! info@cynet. com www. cynet. com
- Slides: 13