The CYK Algorithm Implementation Wesam Fadheel Mohammed Hamdi

- Slides: 22
The CYK Algorithm Implementation Wesam Fadheel & Mohammed Hamdi CS 6800 Spring 2016, WMU
Outline • • • CYK Algorithm. The basics of CYK Algorithm. The Chomsky Normal Form CNF. CYK Algorithm steps. How does the CYK Algorithm start? Build the Triangular Table & example 1. Build the Upper Diagonal Matrix Table & example 2. Notes. References.
The CYK Algorithm • It is called CYK or CKY Algorithm according to its inventors Cocke-Kasami-Younger. • It is a membership problem to determine weather the string (w) belongs to the grammar (G) or not.
The CYK Algorithm • It is a bottom-up parser that uses the nondeterministic way in backtracking to build the table. • Trace all rules and non terminal variables that derive the string ( if w L (G) ).
The basics of the CYK Algorithm • It works only with rules in Chomsky Normal Form CNF. • Dynamic Programming Approach in constructing the table. What are the basics of CYK Algorithm ?
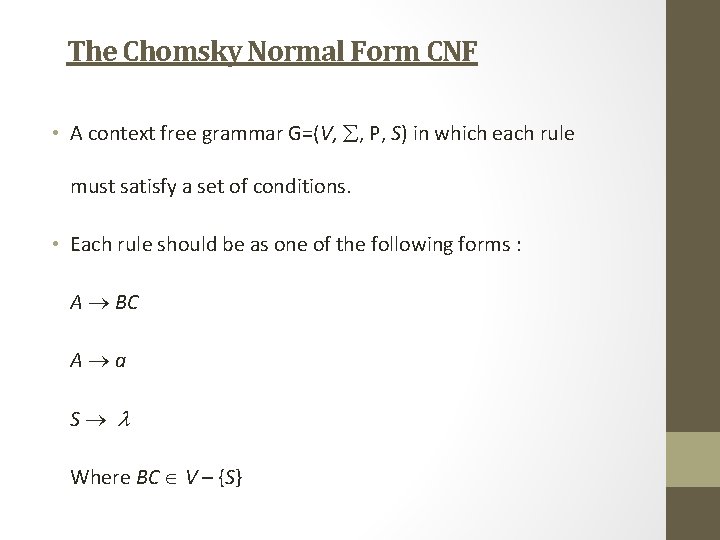
The Chomsky Normal Form CNF • A context free grammar G=(V, , P, S) in which each rule must satisfy a set of conditions. • Each rule should be as one of the following forms : A BC A a S Where BC V – {S}
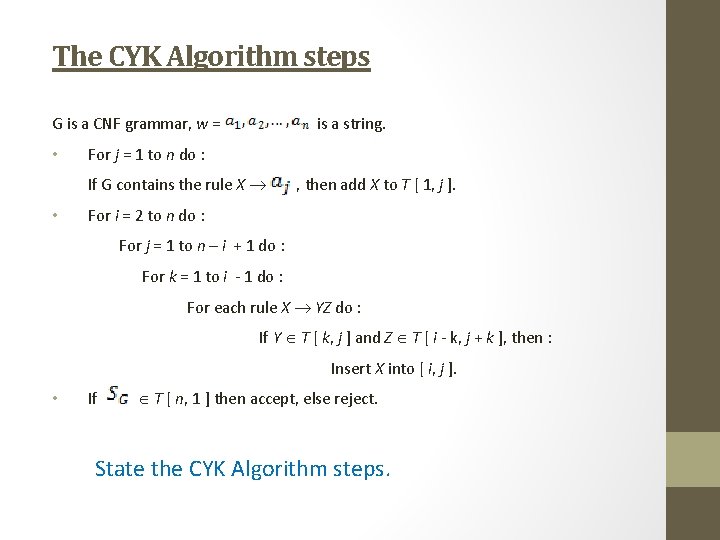
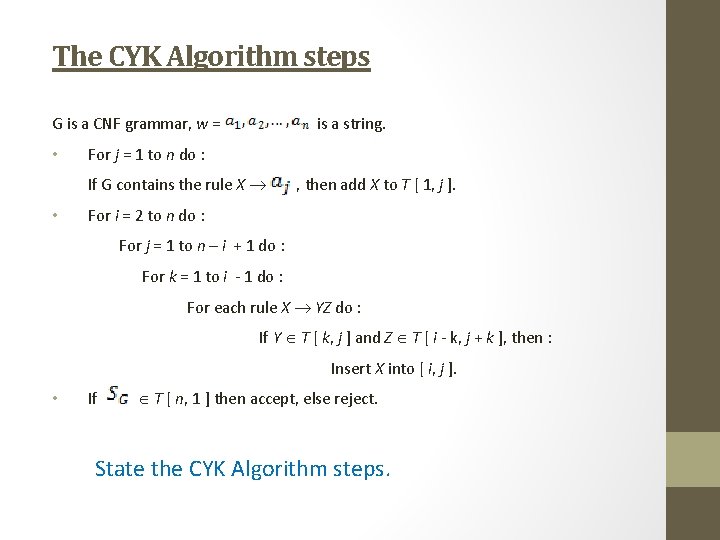
The CYK Algorithm steps G is a CNF grammar, w = • is a string. For j = 1 to n do : If G contains the rule X , then add X to T [ 1, j ]. • For i = 2 to n do : For j = 1 to n – i + 1 do : For k = 1 to i - 1 do : For each rule X YZ do : If Y T [ k, j ] and Z T [ i - k, j + k ], then : Insert X into [ i, j ]. • If T [ n, 1 ] then accept, else reject. State the CYK Algorithm steps.
How does the CYK Algorithm start? • Count the number of terminals in the given string to determine the dimension of the table. • Look for the terminals in the right side of the given CNF rules. • Start to build the table from the lower row.
1. Build the Triangular Table • In each cell in the lower row, assign the variables in the CNF rules that derive each given terminal in the string. • Continue to construct the other rows of the table by using the computed cells in the previous row. • The no. of rows = The no. of columns = length of the given string. • The last computed cell determines the answer.
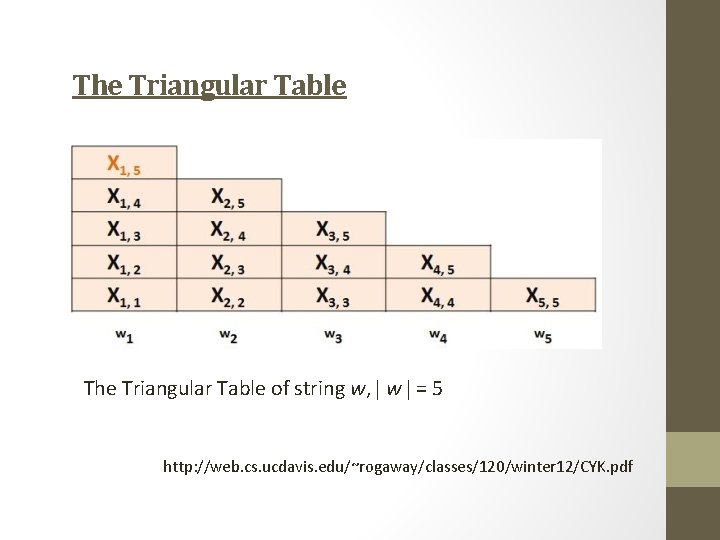
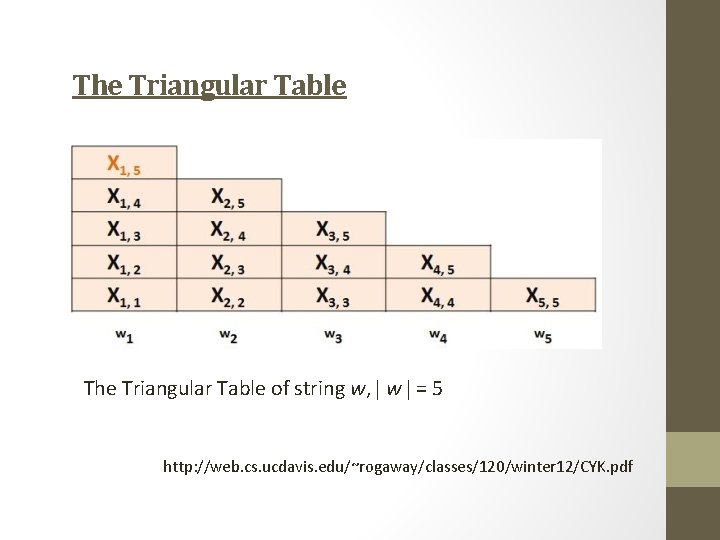
The Triangular Table of string w, w = 5 http: //web. cs. ucdavis. edu/~rogaway/classes/120/winter 12/CYK. pdf
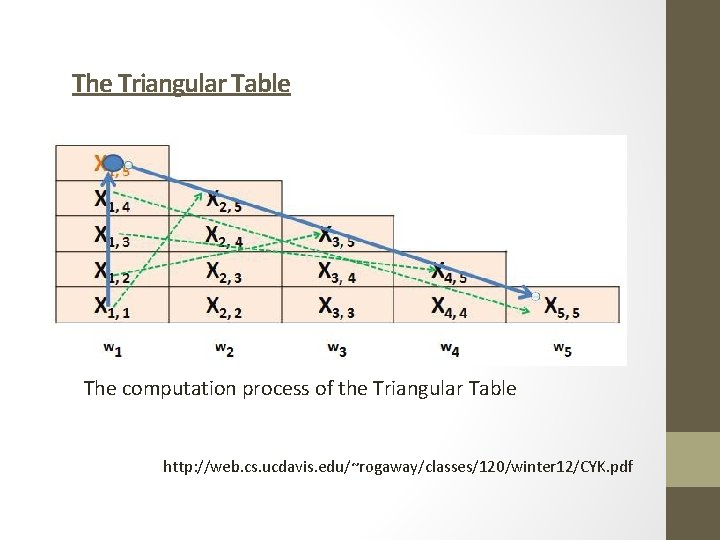
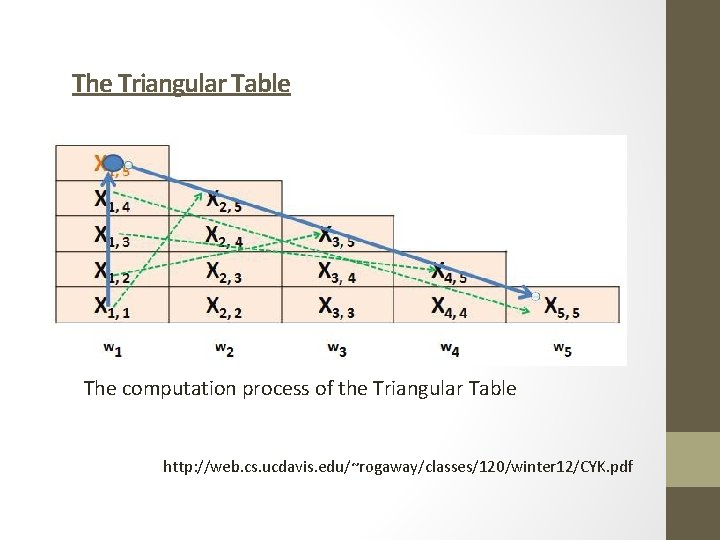
The Triangular Table The computation process of the Triangular Table http: //web. cs. ucdavis. edu/~rogaway/classes/120/winter 12/CYK. pdf
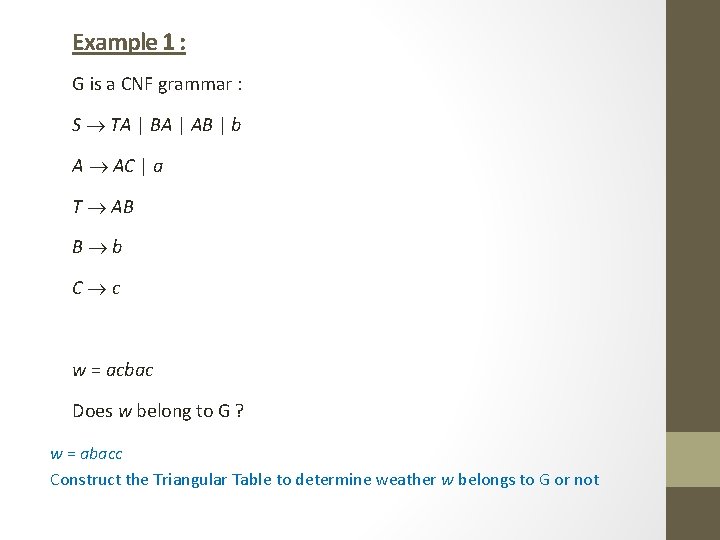
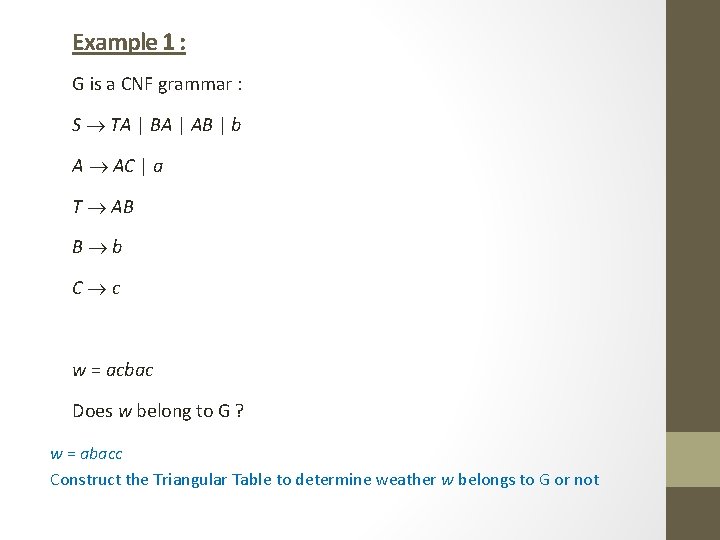
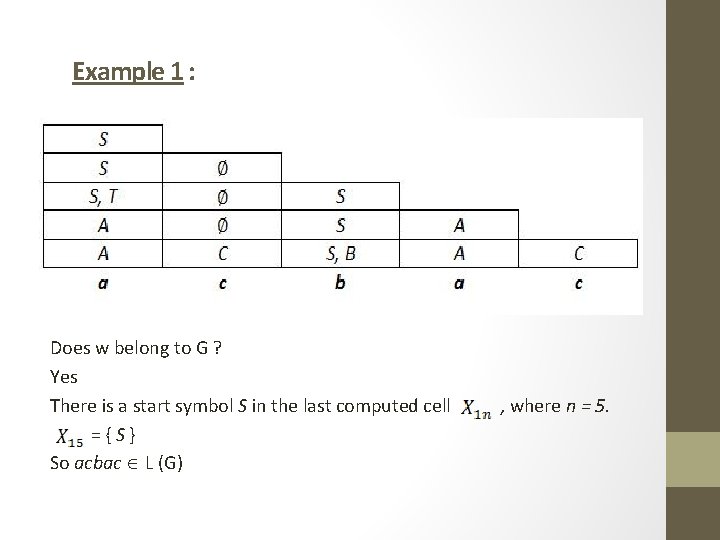
Example 1 : G is a CNF grammar : S TA | BA | AB | b A AC | a T AB B b C c w = acbac Does w belong to G ? w = abacc Construct the Triangular Table to determine weather w belongs to G or not
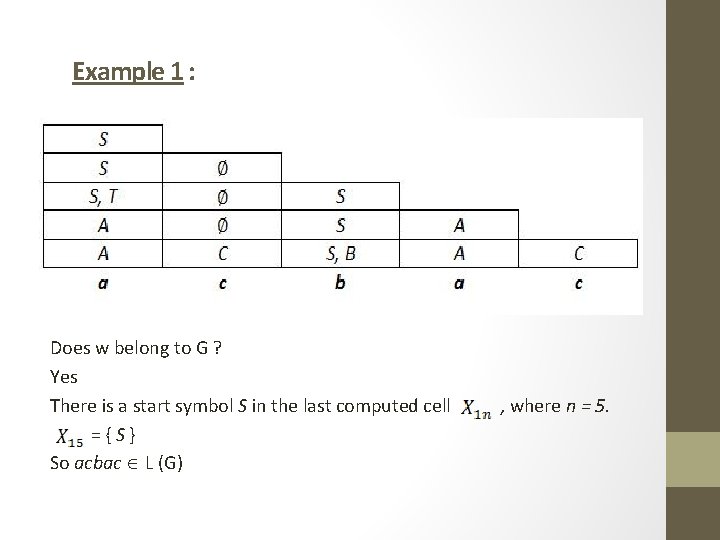
Example 1 : Does w belong to G ? Yes There is a start symbol S in the last computed cell , where n = 5. = { S } So acbac L (G)
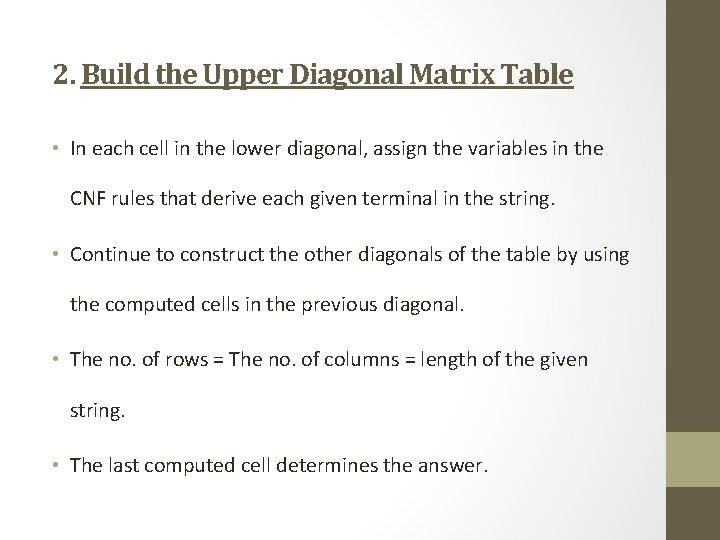
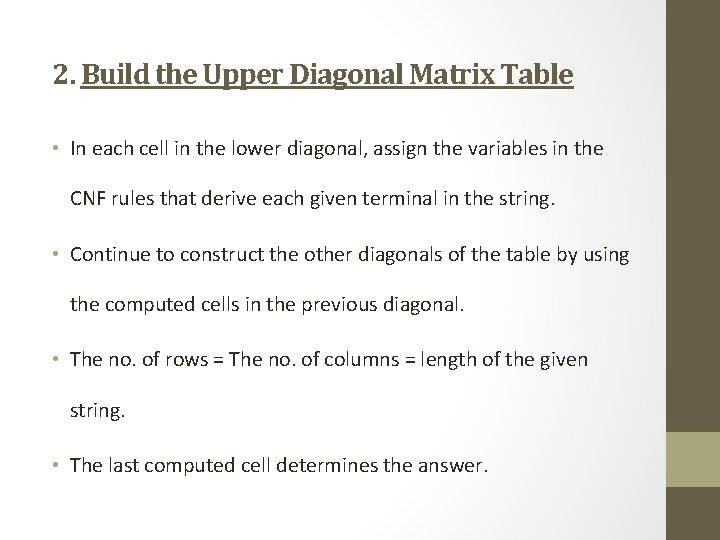
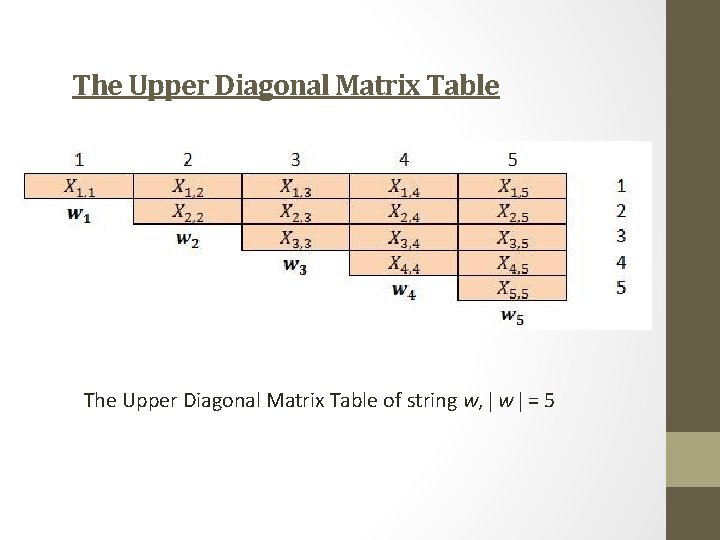
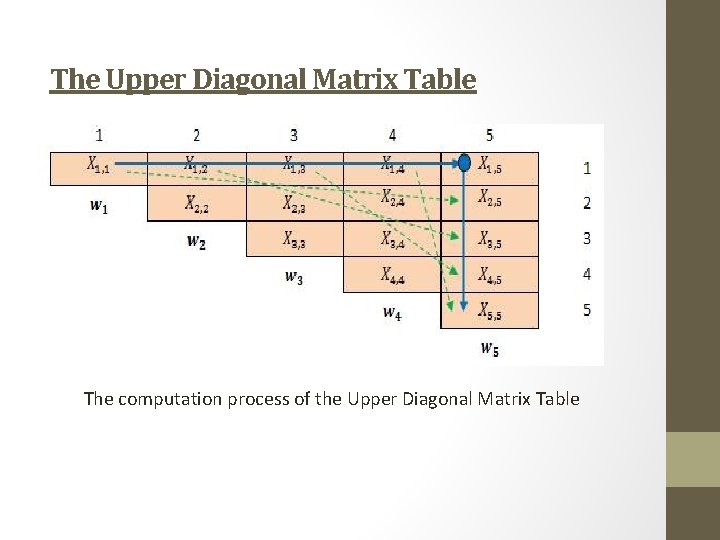
2. Build the Upper Diagonal Matrix Table • In each cell in the lower diagonal, assign the variables in the CNF rules that derive each given terminal in the string. • Continue to construct the other diagonals of the table by using the computed cells in the previous diagonal. • The no. of rows = The no. of columns = length of the given string. • The last computed cell determines the answer.
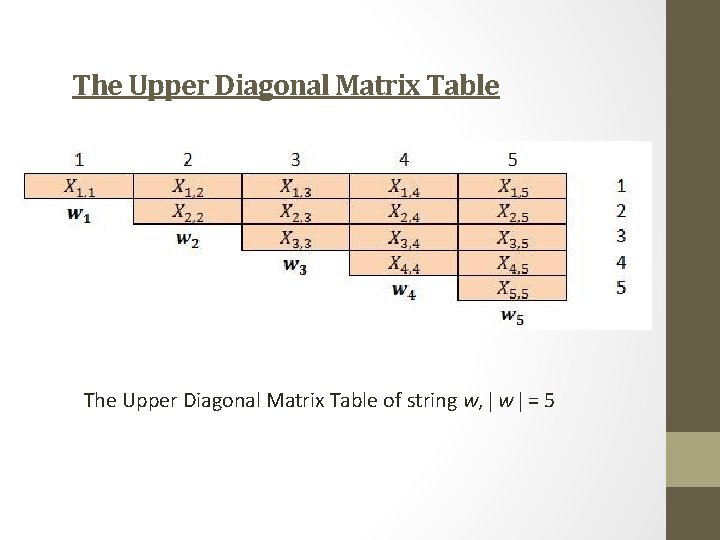
The Upper Diagonal Matrix Table of string w, w = 5
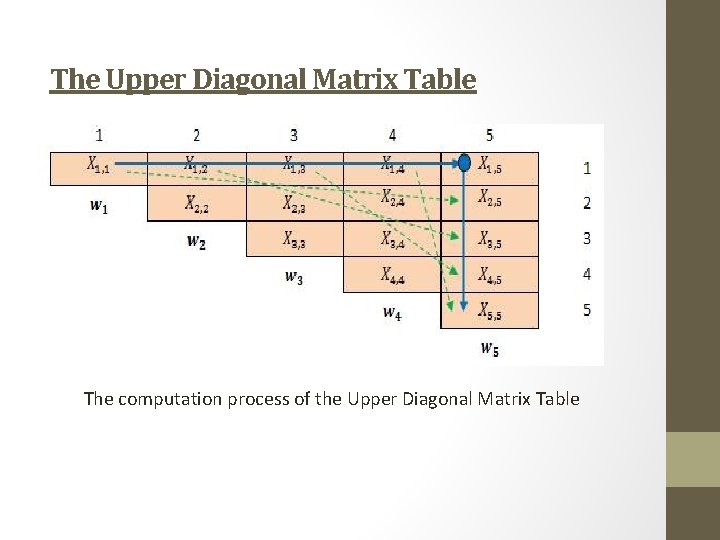
The Upper Diagonal Matrix Table The computation process of the Upper Diagonal Matrix Table
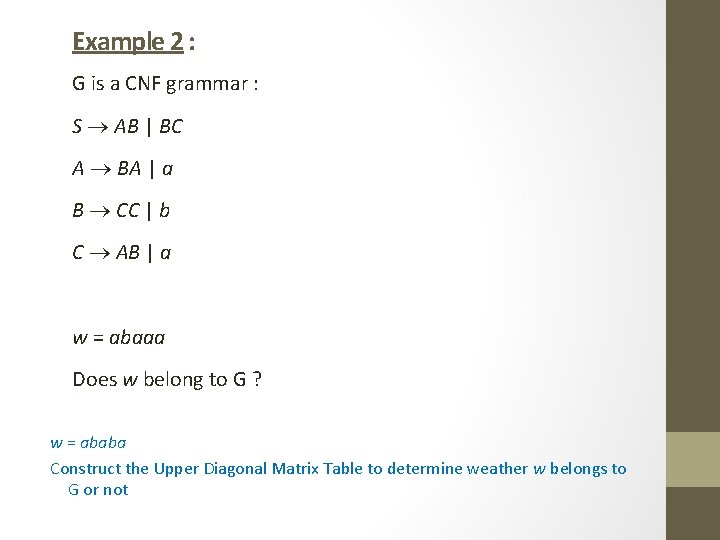
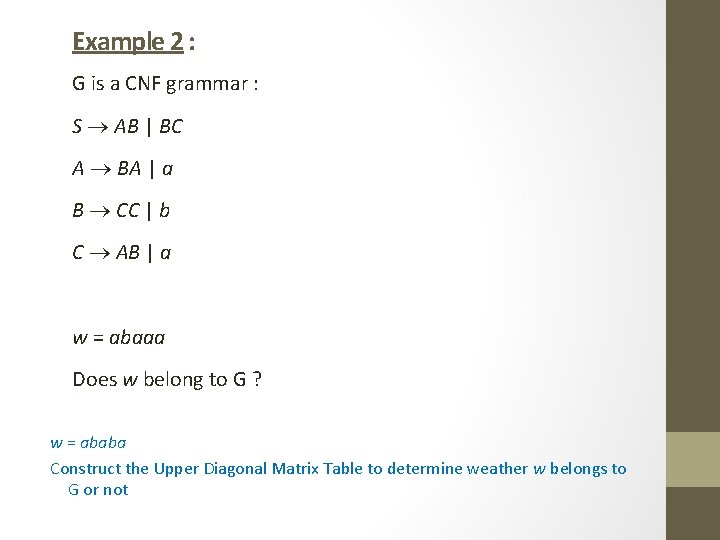
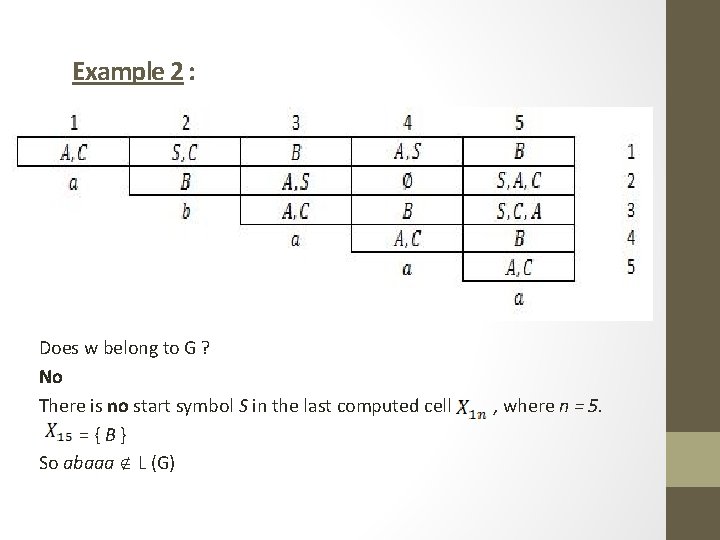
Example 2 : G is a CNF grammar : S AB | BC A BA | a B CC | b C AB | a w = abaaa Does w belong to G ? w = ababa Construct the Upper Diagonal Matrix Table to determine weather w belongs to G or not
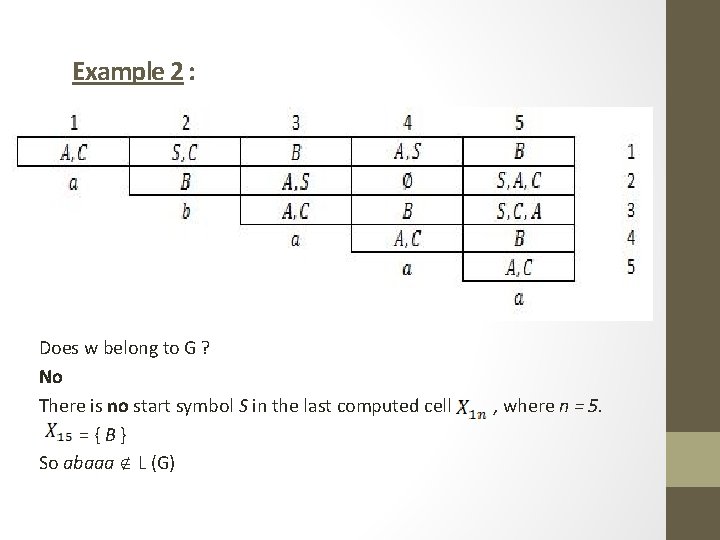
Example 2 : Does w belong to G ? No There is no start symbol S in the last computed cell , where n = 5. = { B } So abaaa L (G)
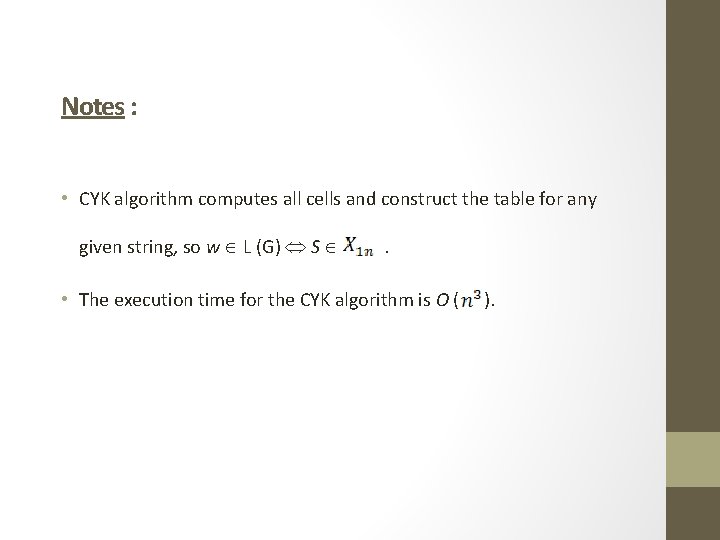
Notes : • CYK algorithm computes all cells and construct the table for any given string, so w L (G) S . • The execution time for the CYK algorithm is O ( ).
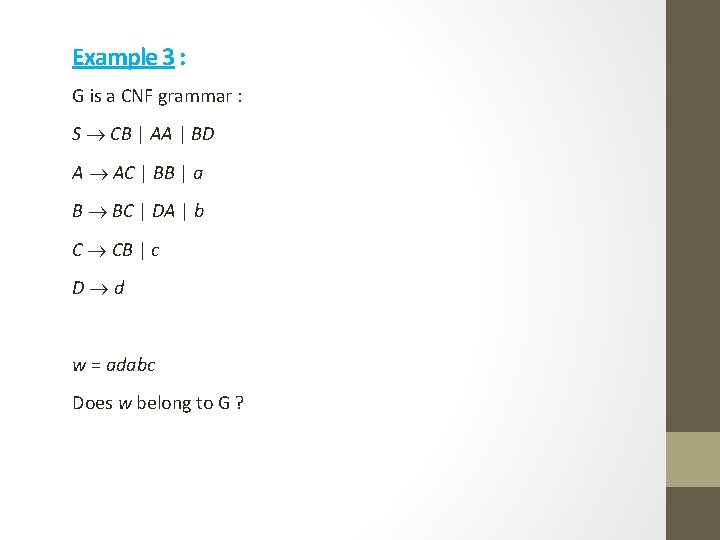
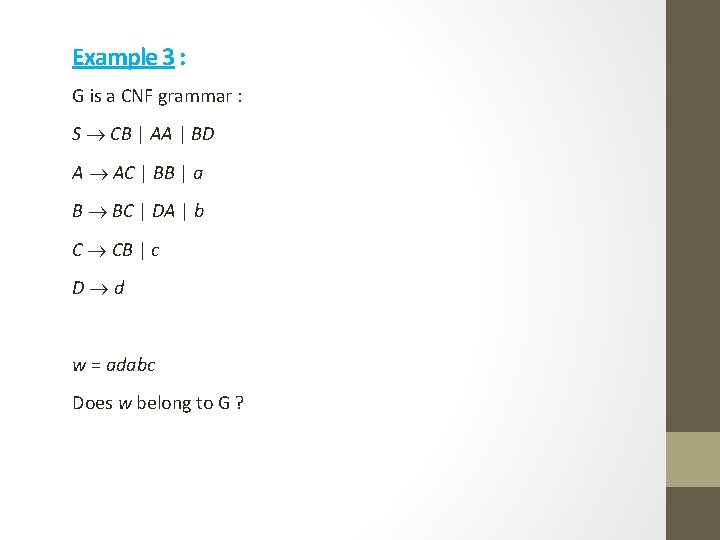
Example 3 : G is a CNF grammar : S CB | AA | BD A AC | BB | a B BC | DA | b C CB | c D d w = adabc Does w belong to G ?
The References : 1. Rich E. . (2008). Automata, Computability & Complexity: Theory and Application. 2. Rodriguez D. , Velazquez. (2009). The CYK Algorithm. Retrieved from : http: //web. cs. ucdavis. edu/~rogaway/classes/120/winter 12/CYK. pdf 3. Sudkamp T. . (1997). Languages and Machines: An Introduction to Theory of Computer Science. 2 nd Edition.

Thank you