TEMPEST Security Hidema Tanaka Security Fundamentals Group Information
![Simplification of TEMPEST Specification of FSET 22 Frequency range 100[Hz] – 22[GHz] Frequency resolution Simplification of TEMPEST Specification of FSET 22 Frequency range 100[Hz] – 22[GHz] Frequency resolution](https://slidetodoc.com/presentation_image/1488e246a7c0ef48493d83b6fdd3806c/image-11.jpg)
- Slides: 17
TEMPEST Security Hidema Tanaka Security Fundamentals Group
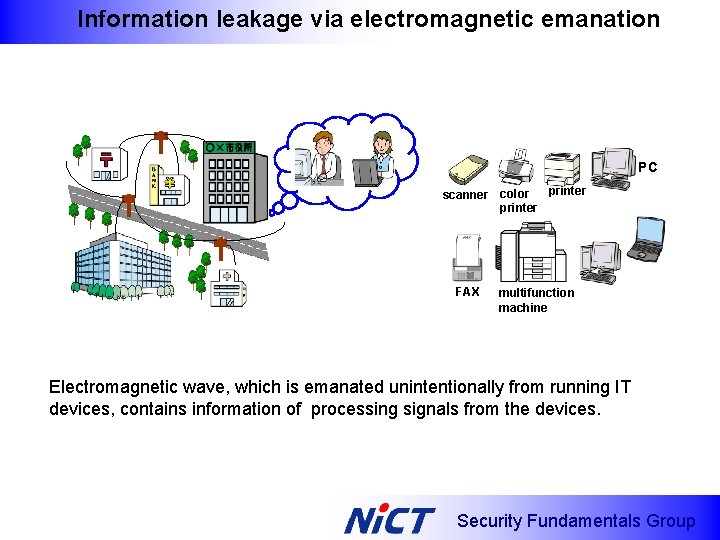
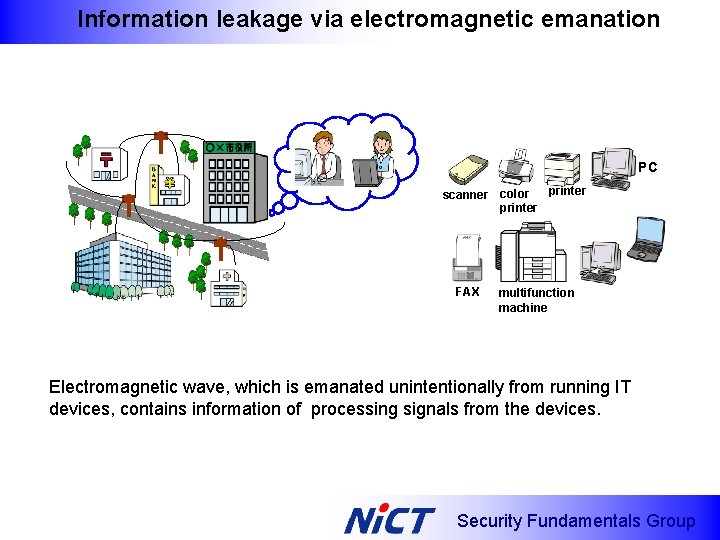
Information leakage via electromagnetic emanation PC printer scanner color printer FAX multifunction machine Electromagnetic wave, which is emanated unintentionally from running IT devices, contains information of processing signals from the devices. Security Fundamentals Group
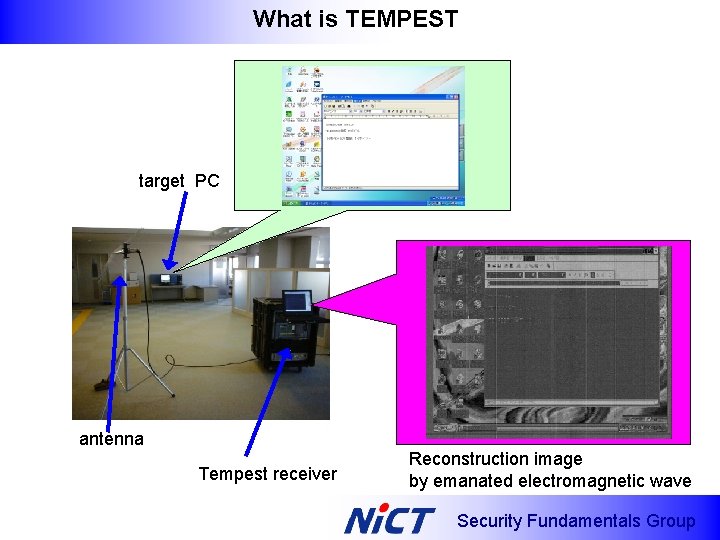
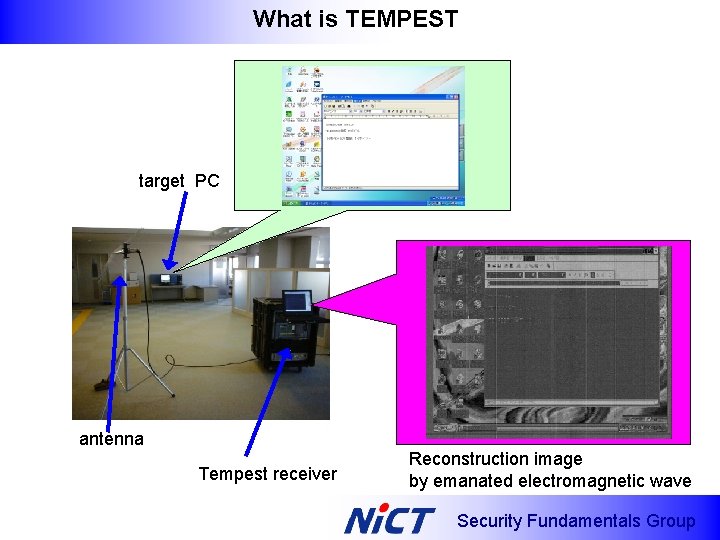
What is TEMPEST target PC antenna Tempest receiver Reconstruction image by emanated electromagnetic wave Security Fundamentals Group
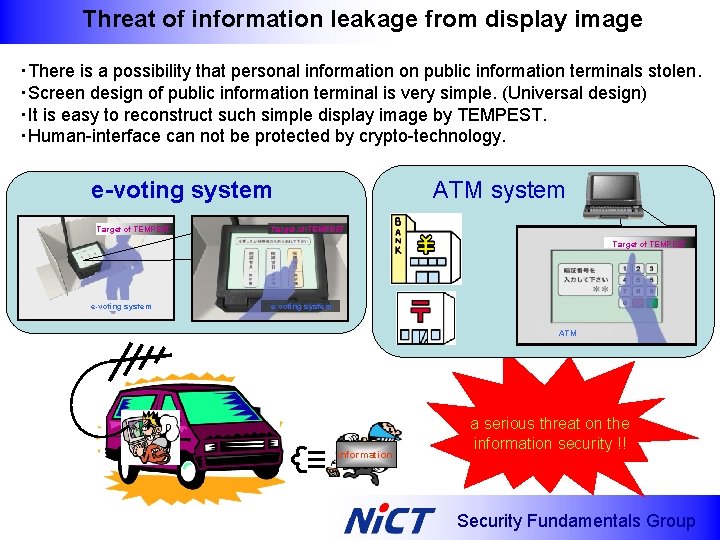
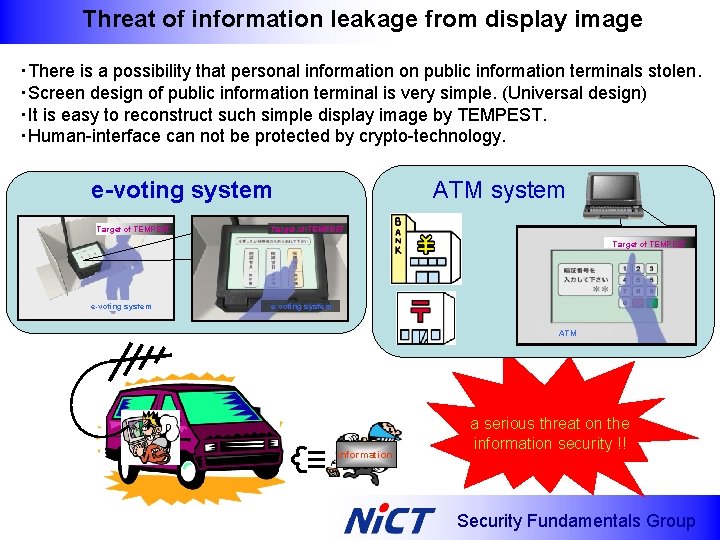
Threat of information leakage from display image ・There is a possibility that personal information on public information terminals stolen. ・Screen design of public information terminal is very simple. (Universal design) ・It is easy to reconstruct such simple display image by TEMPEST. ・Human-interface can not be protected by crypto-technology. e-voting system Target of TEMPEST ATM system Target of TEMPEST e-voting system ATM information a serious threat on the information security !! Security Fundamentals Group
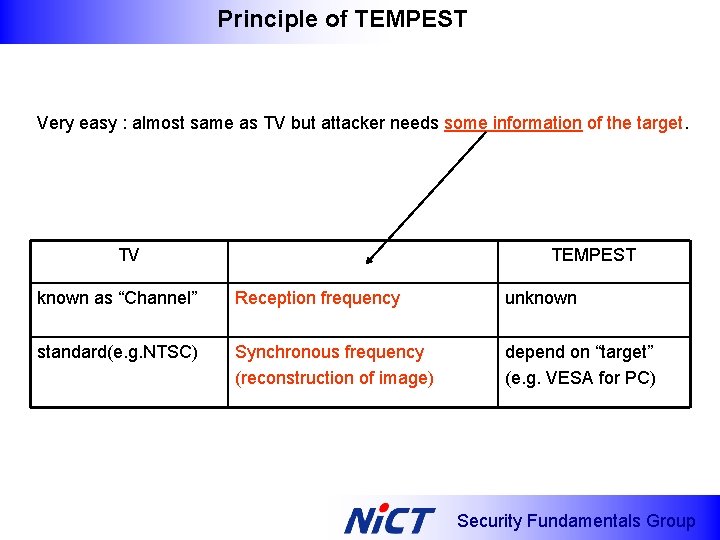
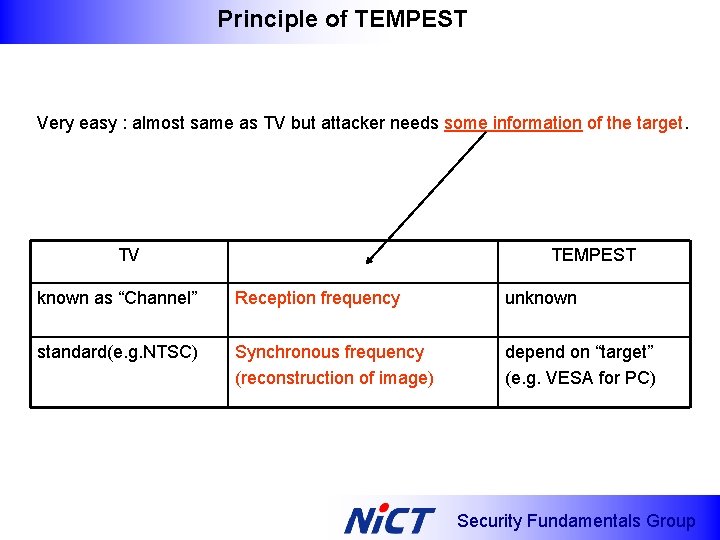
Principle of TEMPEST Very easy : almost same as TV but attacker needs some information of the target. TV TEMPEST known as “Channel” Reception frequency unknown standard(e. g. NTSC) Synchronous frequency (reconstruction of image) depend on “target” (e. g. VESA for PC) Security Fundamentals Group
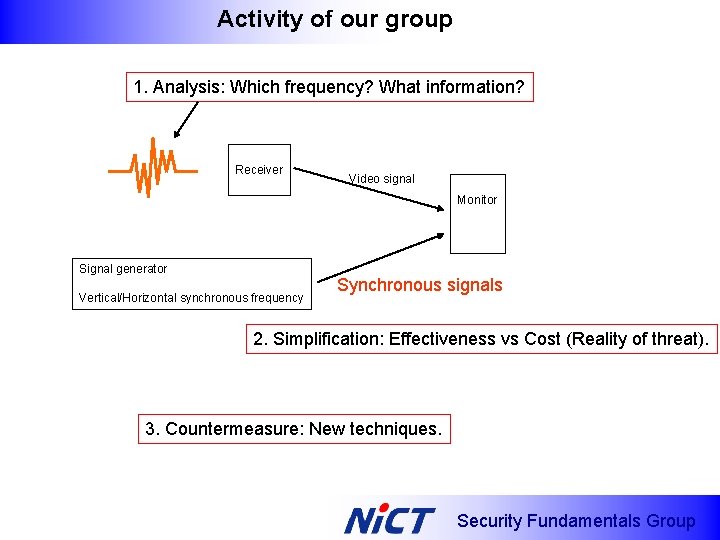
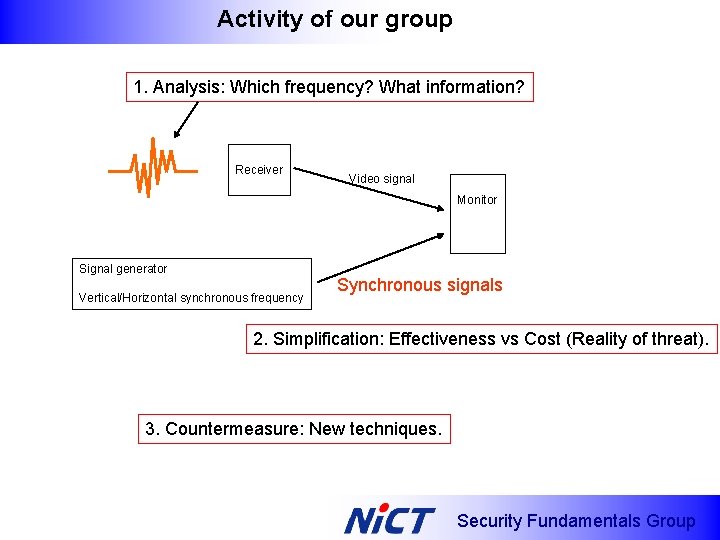
Activity of our group 1. Analysis: Which frequency? What information? Receiver Video signal Monitor Signal generator Vertical/Horizontal synchronous frequency Synchronous signals 2. Simplification: Effectiveness vs Cost (Reality of threat). 3. Countermeasure: New techniques. Security Fundamentals Group
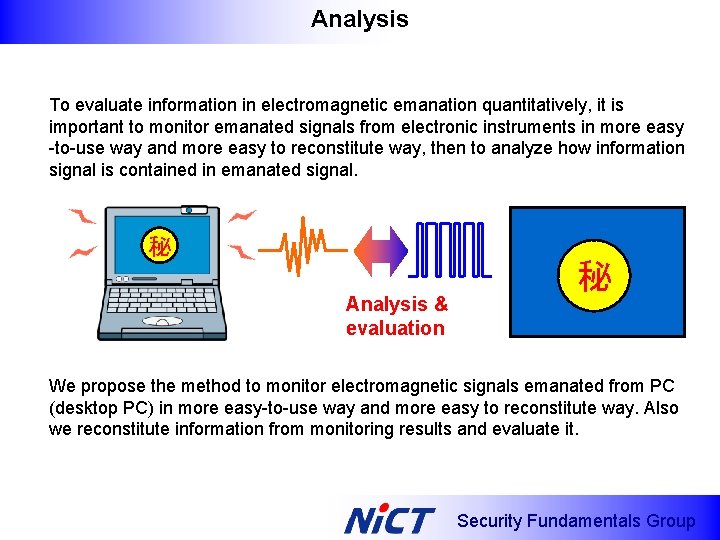
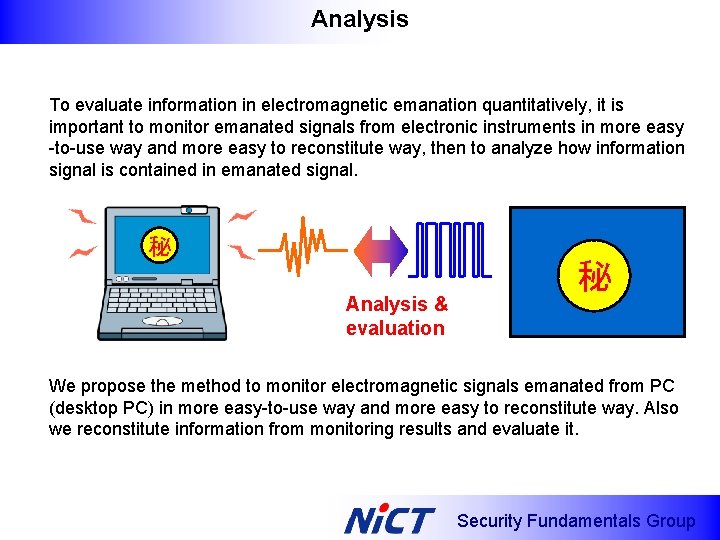
Analysis To evaluate information in electromagnetic emanation quantitatively, it is important to monitor emanated signals from electronic instruments in more easy -to-use way and more easy to reconstitute way, then to analyze how information signal is contained in emanated signal. 秘 Analysis & evaluation 秘 We propose the method to monitor electromagnetic signals emanated from PC (desktop PC) in more easy-to-use way and more easy to reconstitute way. Also we reconstitute information from monitoring results and evaluate it. Security Fundamentals Group
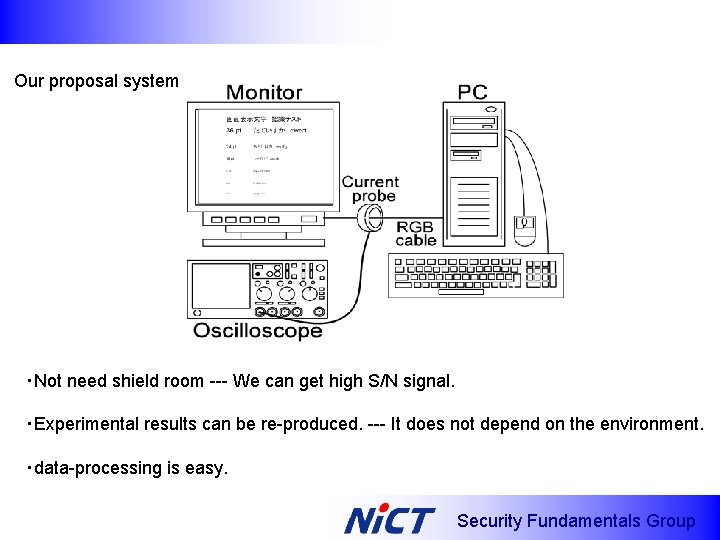
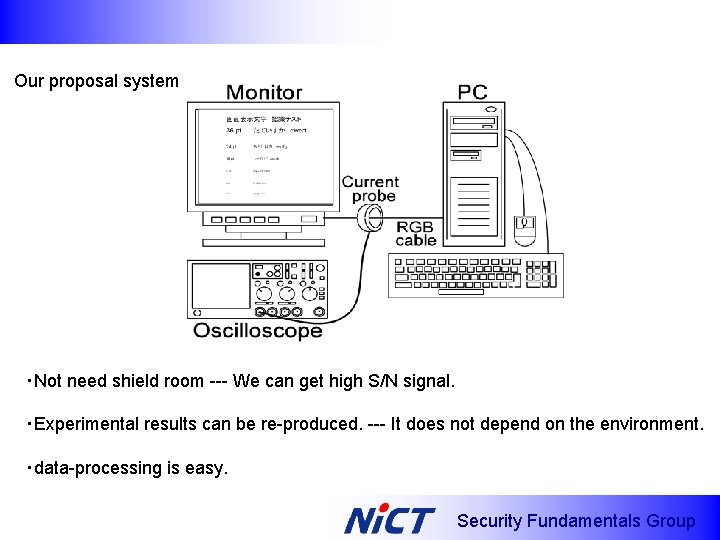
Our proposal system ・Not need shield room --- We can get high S/N signal. ・Experimental results can be re-produced. --- It does not depend on the environment. ・data-processing is easy. Security Fundamentals Group
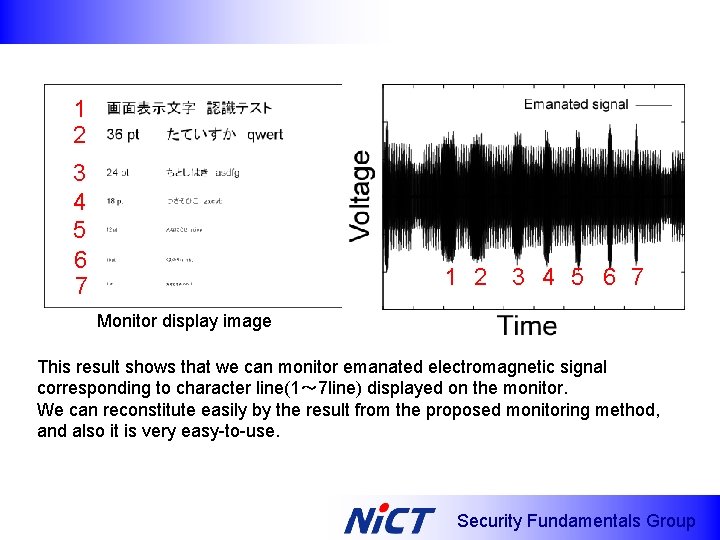
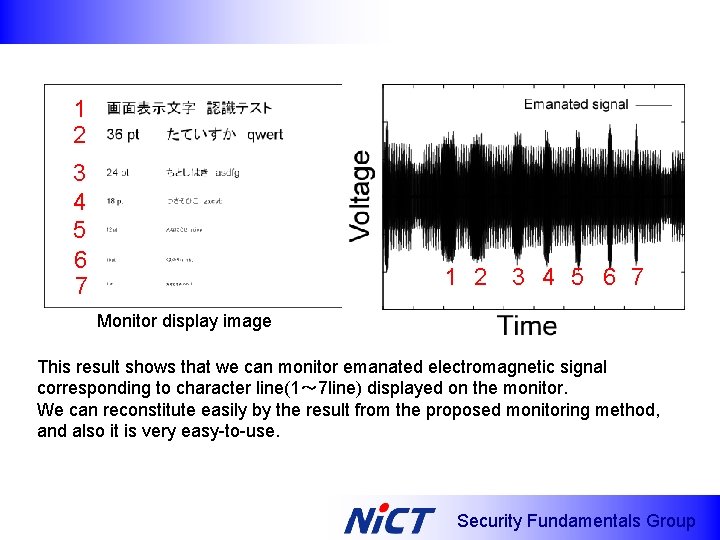
1 2 3 4 5 6 7 Monitor display image This result shows that we can monitor emanated electromagnetic signal corresponding to character line(1~ 7 line) displayed on the monitor. We can reconstitute easily by the result from the proposed monitoring method, and also it is very easy-to-use. Security Fundamentals Group
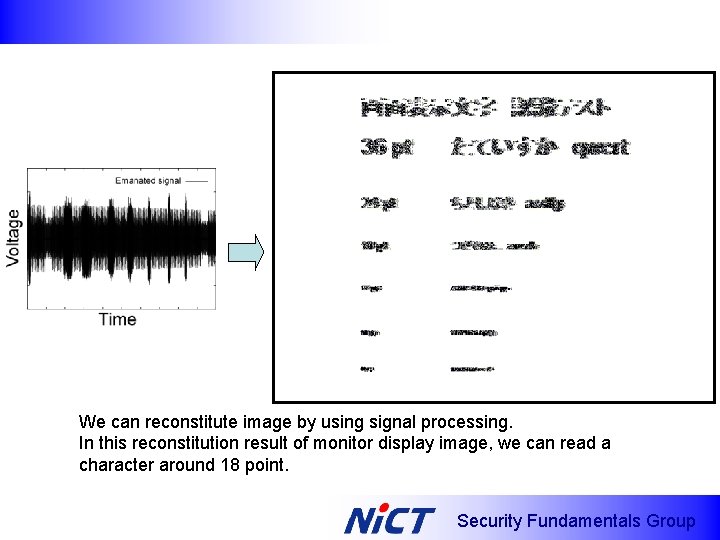
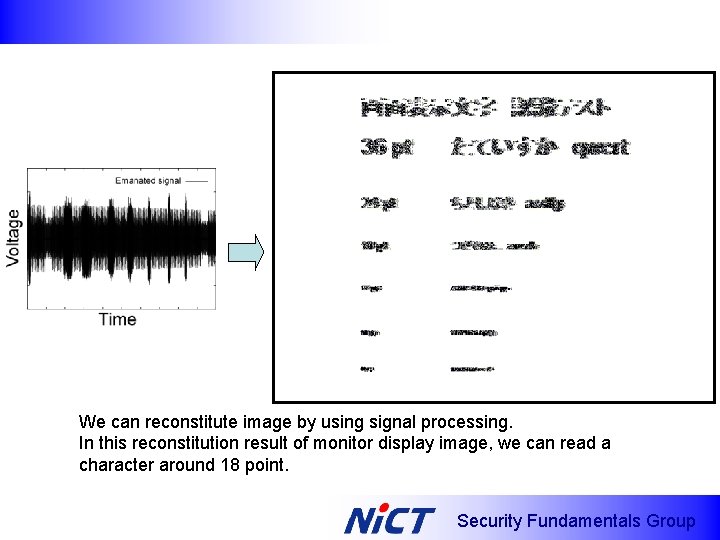
We can reconstitute image by using signal processing. In this reconstitution result of monitor display image, we can read a character around 18 point. Security Fundamentals Group
![Simplification of TEMPEST Specification of FSET 22 Frequency range 100Hz 22GHz Frequency resolution Simplification of TEMPEST Specification of FSET 22 Frequency range 100[Hz] – 22[GHz] Frequency resolution](https://slidetodoc.com/presentation_image/1488e246a7c0ef48493d83b6fdd3806c/image-11.jpg)
Simplification of TEMPEST Specification of FSET 22 Frequency range 100[Hz] – 22[GHz] Frequency resolution 0. 1[Hz] Bandwidth 10[Hz] – 500[MHz] Average noise level < 142 d. Bm ・High performance receiver (10~ 20 years ago, FSET 22 was a military model) ・Real time image processing (such as Adobe Photoshop) ・Hardware Amplification and noise canceller ・Setting of synchronous frequency in 0. 001[Hz] step ・Very expensive ($100 M or higher? I do not know. ) Does attacker (such a pedestrian hacker) need such expensive machines ? Security Fundamentals Group
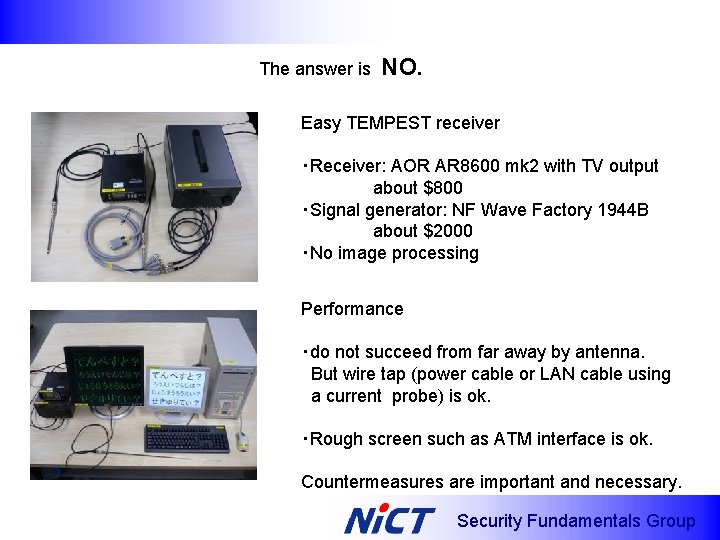
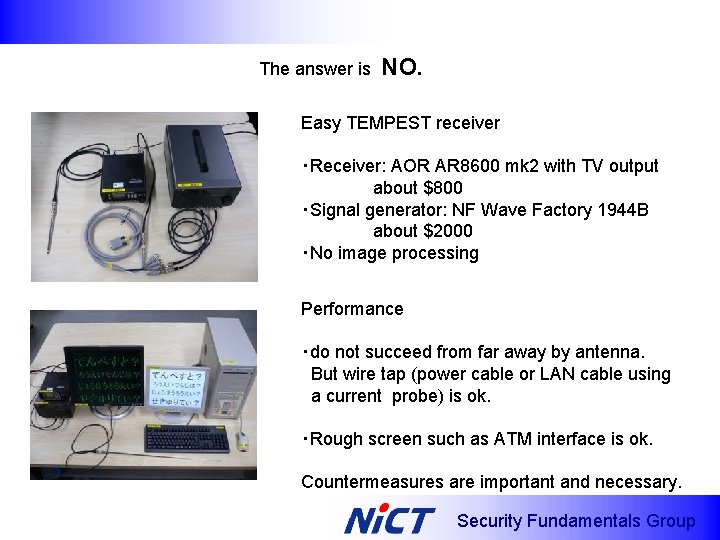
The answer is NO. Easy TEMPEST receiver ・Receiver: AOR AR 8600 mk 2 with TV output about $800 ・Signal generator: NF Wave Factory 1944 B about $2000 ・No image processing Performance ・do not succeed from far away by antenna. But wire tap (power cable or LAN cable using a current probe) is ok. ・Rough screen such as ATM interface is ok. Countermeasures are important and necessary. Security Fundamentals Group
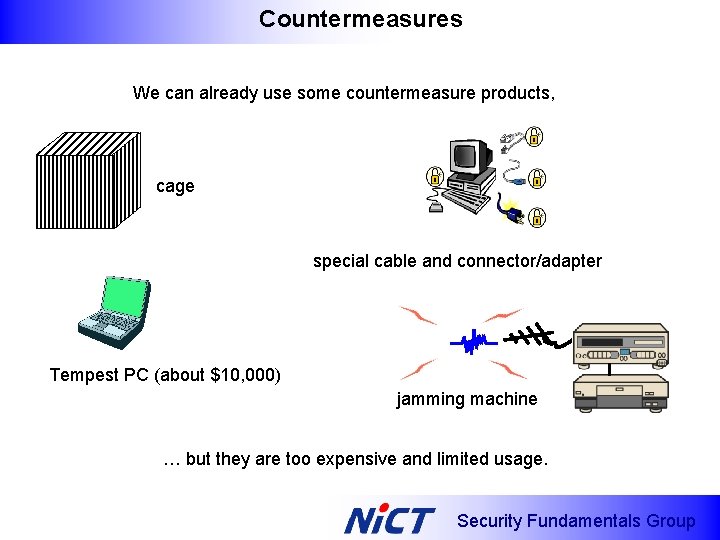
Countermeasures We can already use some countermeasure products, cage special cable and connector/adapter Tempest PC (about $10, 000) jamming machine … but they are too expensive and limited usage. Security Fundamentals Group
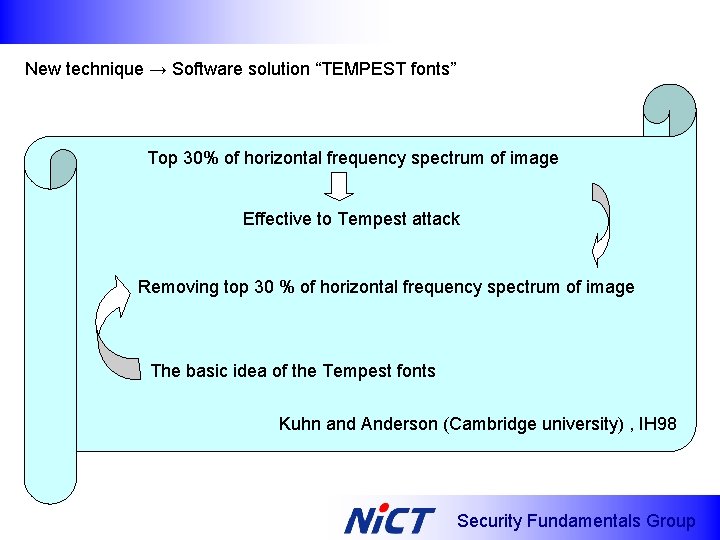
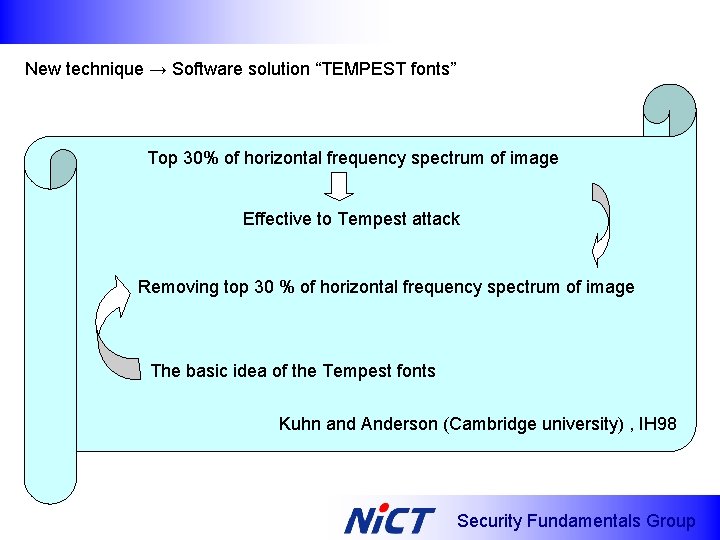
New technique → Software solution “TEMPEST fonts” Top 30% of horizontal frequency spectrum of image Effective to Tempest attack Removing top 30 % of horizontal frequency spectrum of image The basic idea of the Tempest fonts Kuhn and Anderson (Cambridge university) , IH 98 Security Fundamentals Group
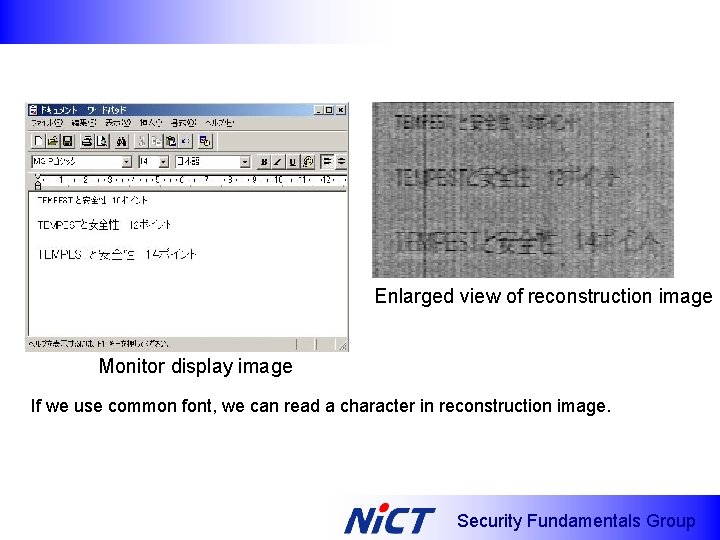
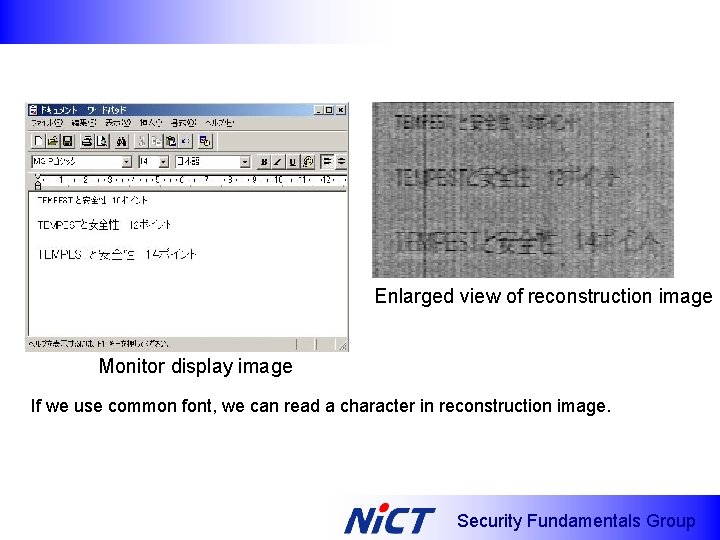
Enlarged view of reconstruction image Monitor display image If we use common font, we can read a character in reconstruction image. Security Fundamentals Group
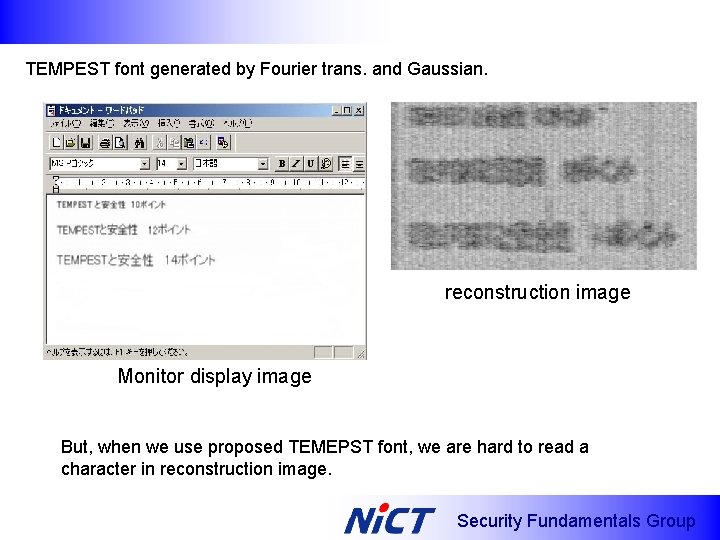
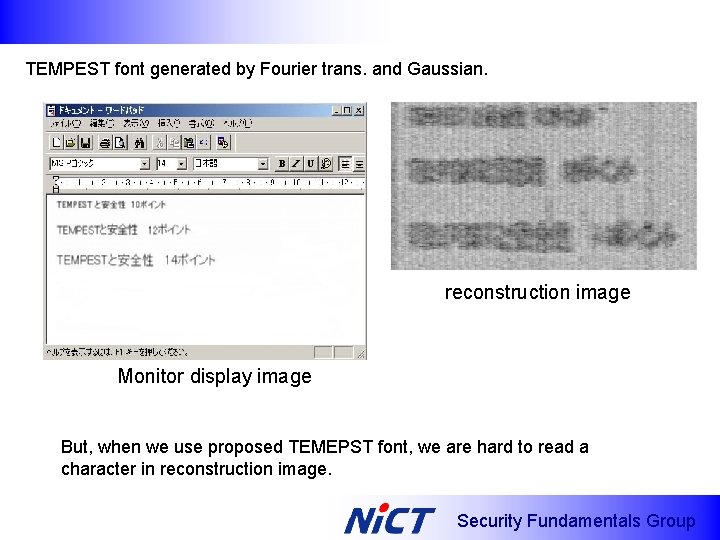
TEMPEST font generated by Fourier trans. and Gaussian. reconstruction image Monitor display image But, when we use proposed TEMEPST font, we are hard to read a character in reconstruction image. Security Fundamentals Group
Future works ・Reconstruction of keyboard typing information via EM ⇔ “Keyboard acoustic emanation” (L. Lhuag et. al , CSS 05) ・EM side-channel cryptanalysis (IC card, RFID etc) ・EM attack (small scale of E-Bomb) on IT devices e. g. Attack to LAN cable → packet error → Do. S attack Security Fundamentals Group