Technology in Retail Payment Innovations Mobile Payment the
Technology in Retail Payment Innovations Mobile Payment @ the POS Jack Jania SVP Gemalto Jack. Jania@gemalto. com October 2012
Agenda The changing POS payment environment Mag-Stripe, EMV, NFC…. NFC - TSM ecosystem NFC Payment examples Conclusion
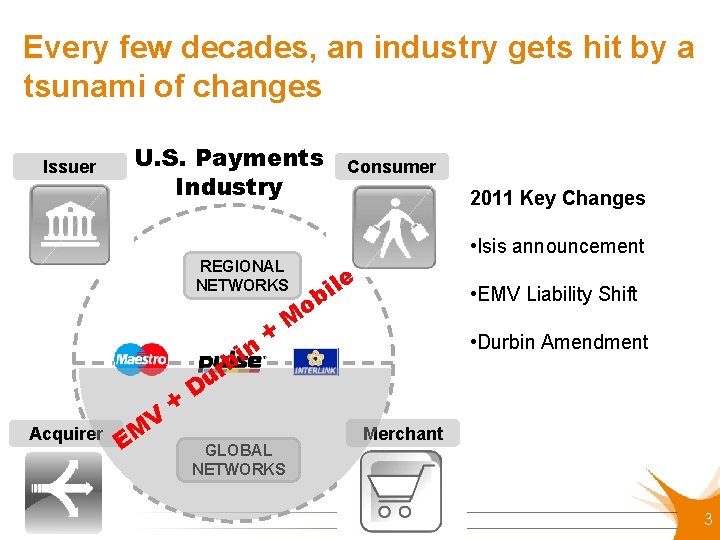
Every few decades, an industry gets hit by a tsunami of changes Issuer U. S. Payments Industry n bi Acquirer EM V + 2011 Key Changes • Isis announcement REGIONAL NETWORKS + Consumer le i b • EMV Liability Shift M o • Durbin Amendment r u D GLOBAL NETWORKS Merchant 3
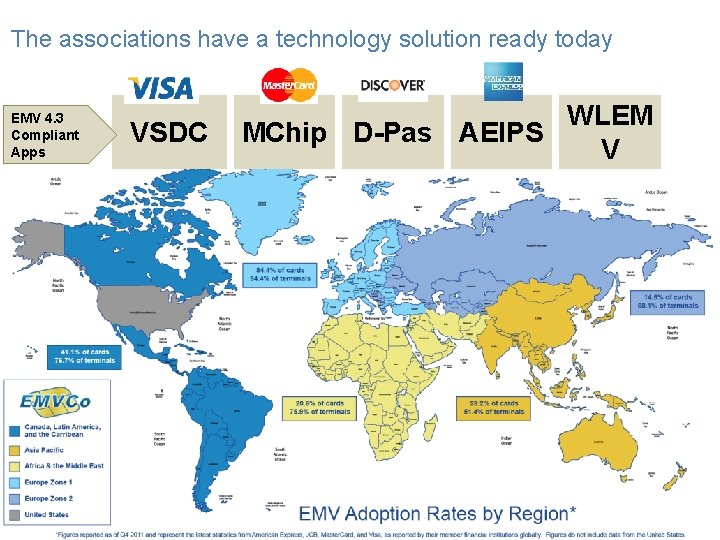
The associations have a technology solution ready today EMV 4. 3 Compliant Apps VSDC WLEM MChip D-Pas AEIPS V 44
Agenda The changing POS payment environment Mag-Stripe, EMV, NFC…. NFC - TSM ecosystem NFC Payment examples Conclusion
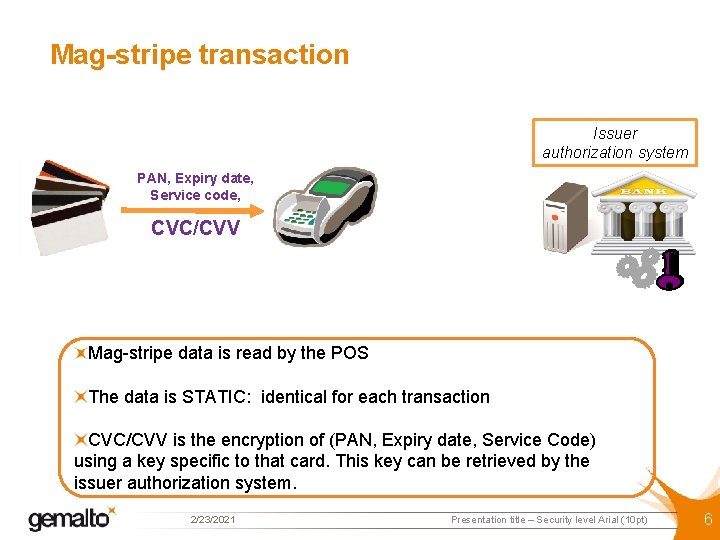
Mag-stripe transaction Issuer authorization system PAN, Expiry date, Service code, CVC/CVV Mag-stripe data is read by the POS The data is STATIC: identical for each transaction CVC/CVV is the encryption of (PAN, Expiry date, Service Code) using a key specific to that card. This key can be retrieved by the issuer authorization system. 2/23/2021 Presentation title – Security level Arial (10 pt) 6
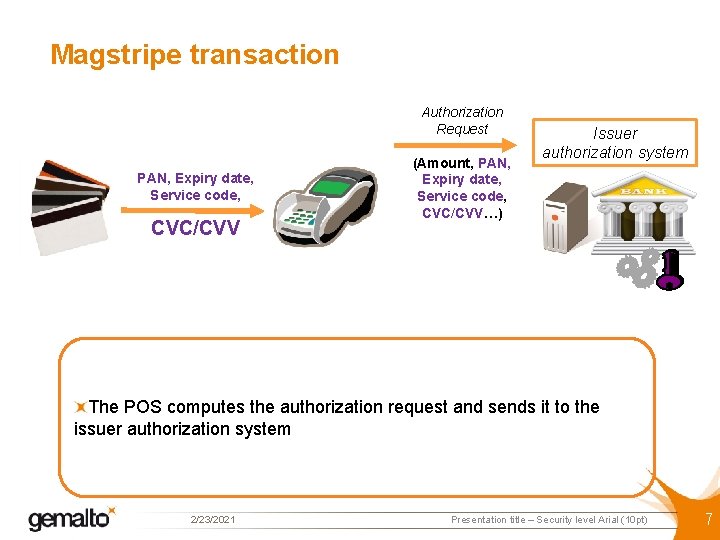
Magstripe transaction Authorization Request PAN, Expiry date, Service code, CVC/CVV (Amount, PAN, Expiry date, Service code, CVC/CVV…) Issuer authorization system The POS computes the authorization request and sends it to the issuer authorization system 2/23/2021 Presentation title – Security level Arial (10 pt) 7
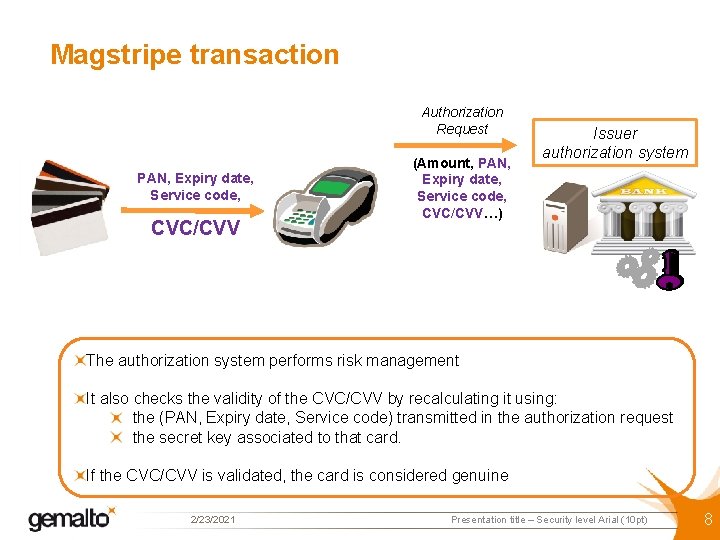
Magstripe transaction Authorization Request PAN, Expiry date, Service code, CVC/CVV (Amount, PAN, Expiry date, Service code, CVC/CVV…) Issuer authorization system The authorization system performs risk management It also checks the validity of the CVC/CVV by recalculating it using: the (PAN, Expiry date, Service code) transmitted in the authorization request the secret key associated to that card. If the CVC/CVV is validated, the card is considered genuine 2/23/2021 Presentation title – Security level Arial (10 pt) 8
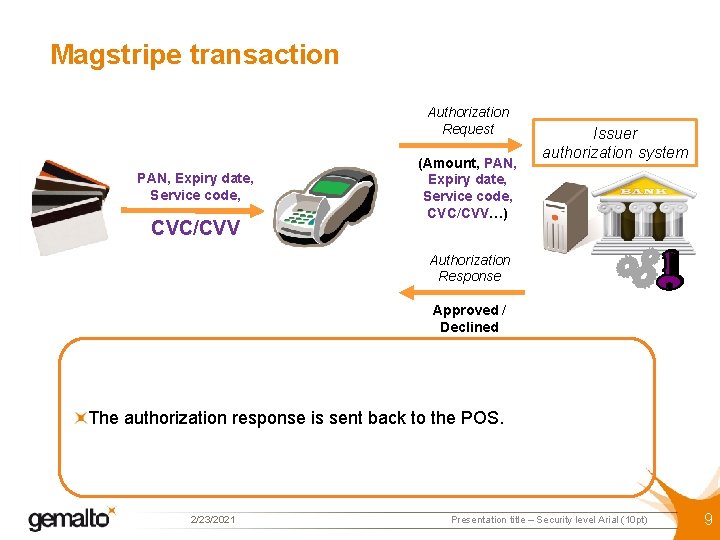
Magstripe transaction Authorization Request PAN, Expiry date, Service code, CVC/CVV (Amount, PAN, Expiry date, Service code, CVC/CVV…) Issuer authorization system Authorization Response Approved / Declined The authorization response is sent back to the POS. 2/23/2021 Presentation title – Security level Arial (10 pt) 9
Mag-stripe transactions Mag-stripe cards are easy to clone Card authentication is based on STATIC data Cloned cards will be considered authentic, since they carry the same data as real cards 2/23/2021 Presentation title – Security level Arial (10 pt) 10
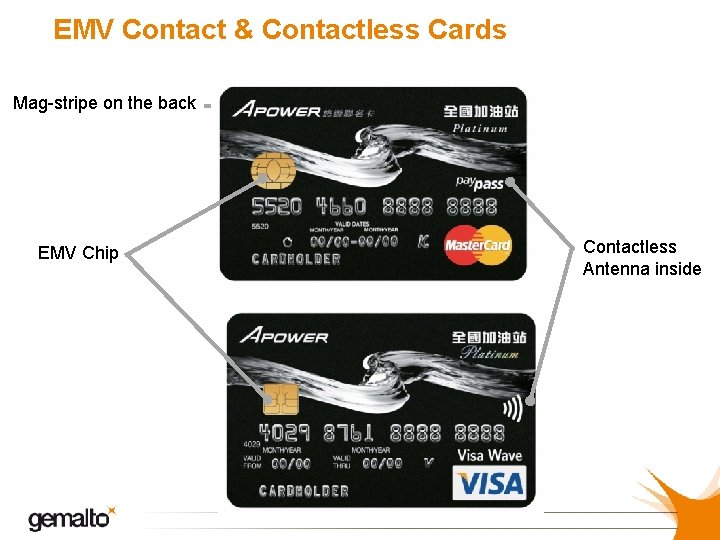
EMV Contact & Contactless Cards Mag-stripe on the back EMV Chip Contactless Antenna inside
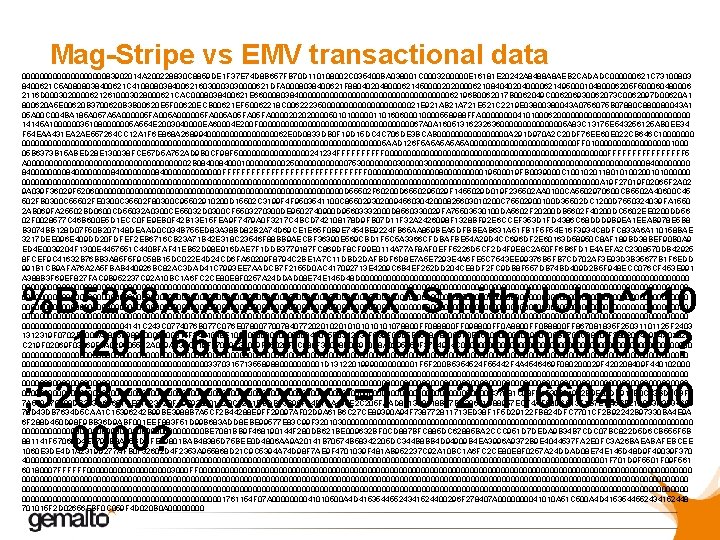
Mag-Stripe vs EMV transactional data 000000000083902014 A 200228830 C 8859 DE 1 F 37 E 74 D 8 B 657 FB 70 D 110108002 C 035400 BA 038001 C 0003200000 E 16181 E 20242 A 8488 A 8 AEB 2 CADADC 000000621 C 73100803 8400621 C 5 A 0808038400621 C 4108080384006216030003030000621 DFA 0008038400621 F 8804020480006214500002020000621084040204000062149500010480006205 F 500060480006 2116 D 00030200006212610003028000621 CAC 0008038400621 E 66000803840000000000000000062196 B 0062017 B 0062049 C 006206930062073 C 0062097 D 00620 A 1 800620 A 5 E 00620 B 3700620 B 3 B 00620 E 5 F 00620 ECB 00621 EF 50062218 C 00622235000000000021 E 921 AB 21 A 721 E 521 C 2219 E 0380043 A 0756075 B 07880 C 880080043 A 1 05 A 00 C 004 BA 185 A 057 A 5 A 000005 FA 005 A 05 FA 00002020200005010100000110160600010000558988 FFA 0000410100062000000000000000 14145 A 1000000351080000005 A 554 E 2003040000 EA 60004 E 200 F 00000000000000000067 A 0 A 1605131623263600000005 A 83 C 13175 E 543256125 AB 0 EE 34 F 54 EAA 431 EA 2 AE 557264 CC 12 A 1 F 6 E 868 A 2689940000000062 E 0 D 0833 DB 0 F 19 D 15 DC 4 C 706 DE 3 BCAB 00000000 A 291 D 970 A 2 C 20 DF 76 EE 60 E 022 CB 646 C 1000000000000000000000000000000000000000005 AAD 126 F 5 A 5 A 5 A 000000000000 FF 010000000001000 05 B 6373 B 15 ABED 28 E 130038 FCE 57 D 5 A 752 AD 9 B 0 CF 98 F 500000000241234 FFFFF 0000000000000000000000000 FFFFFFFF 5 A 0000000000000000002 B 08400010000025000000753000030000000000000000000000000008400000000840000000000000 FFFFFFFFFFFFFFF 0000000080000019500019 FB 0039000 C 100102011801010020010100000000000000000000000000000000000000000000000000000000000000000 A 19 F 27019 F 02065 F 2 A 02 9 A 039 F 36029 F 52060000000000000000000000000000 D 55502 F 60200 D 655029 F 1455029 D 019 F 235502 AA 0100 CA 5502970600 CB 5502 A 40600 C 45 502 FB 0300 C 55502 FE 0300 C 35502 F 80300 C 95502910200 D 15502 C 3199 F 4 F 9503541100 C 85502930200945603042000825603010200 C 75502900100 D 35502 DC 1200 D 7550324039 FA 1550 2 AB 069 FA 25502 BD 0600 CD 55032 A 0300 CE 55032 D 0300 CF 5503270300 DE 9502740900 D 95603332000 D 8560330029 FA 75503530100 DA 5602 F 20200 DB 5602 F 40200 DC 5602 EE 0200 DD 56 02 F 0028577 C 46 B 600 E 5 D 1 ECC 0 FE 9 EB 0 F 42 B 13 E 15 FEA 9 F 7479 A 0 F 3217 C 4 BCD 742108178 D 9 FB 07 D 11 F 32 A 2426098 F 1328 BF 92 E 6 CCEF 353 D 1 FD 4386 C 68 DDD 9 B 9 EA 1 EEAB 978 E 5 B 8 B 3074 BB 128 D 07 F 50 B 207148 DEAAD 0 C 034 B 755 ED 83 A 38 BD 82 B 2 A 74 D 69 CE 1 E 65 F 0 B 9 E 7454 BE 9224 FB 65 AA 859 BEA 5 DFBBEAB 631 A 51 FB 1 F 5 F 54 E 16 F 3934 C 8 DFC 833 A 6 A 110158 BAE 3217 DEE 096 E 409 DD 20 FDFEF 2 EB 6716 CB 23 A 71 B 42 E 318 C 23546 F 88 BB 9 AECBF 36390 E 569 CBD 1 F 5 C 5 A 3366 CFDBAFBE 54 A 29 D 4 CC 696 DF 2 E 60163 D 58950 C 8 AF 189 BD 38 BEF 90 B 0 A 9 ED 4 E 0039204 F 1300 E 4457551 C 440 BFAF 41 EB 52 D 98 E 916 DAE 7 F 1 DDB 3779187 FC 869 DF 8 CF 99 E 0114 A 77 AF 8 AF 0 EFF 5226 D 5 CF 2 D 4 F 9 E 8 C 2 A 50 FF 6 B 6 FD 1 E 4 AEFA 2 C 2308570 DB 42925 8 FCEF 9 C 41632 B 76 BB 3 A 85 F 5 F 9 C 58 B 15 DC 022 E 4 D 24 CD 6 FA 60209 F 8794 C 2 BE 1 A 7 C 11 DBD 2 DAFBDF 6 D 8 E 7 A 5 E 7293 E 4 A 6 FE 5 C 7543 EE 99376 B 5 FB 7 CD 702 AF 3 E 93 D 3 B 35677 B 1 F 6 EDD 991 B 1 CB 9 AFA 76 A 2 A 5 FBAB 440926 BC 82 AC 3 DAD 41 C 7993 EE 7 AADCB 7 F 2155 D 0 AC 417092713 E 4209 C 6 B 4 EF 252 DD 204 CE 8 DF 2 FC 9 DB 8 F 557 DB 74 BD 409 D 2 B 5 F 948 ECC 076 CF 453 E 991 A 388 B 3 F 69 EF 827 FAC 9 B 952237 C 92 A 10 BC 1 A 6 FC 2 CE 80 E 8 F 0257 A 24 DDAD 08 E 74 E 145 D 48 D 000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 0000000000000000000000000000000000000000000000000000000000000000000000000004141 C 243 C 0774076 B 077 C 076 E 07800770078407720201010101078800 FF 088800 FF 098800 FF 0 A 8800 FF 0 B 8800 FF 867081835 F 25031101125 F 2403 1312319 F 0702 FF 005 A 085589880000015 F 3401018 E 100000000042015 E 0342031 F 039 F 0 D 05 B 8508 C 88009 F 0 E 05000009 F 0 F 05 B 8708 C 98005 F 280208409 F 4 A 01828 C 219 F 02069 F 03069 F 1 A 0295055 F 2 A 029 A 039 C 019 F 37049 F 35019 F 45029 F 4 C 089 F 34038 D 0 C 910 A 8 A 0295059 F 37049 F 4 C 080000000000000000000000000000000000000000000000000000000000000000000000000003370315713558988000001 D 1312201999000001 F 5 F 200 B 5354524 F 55442 F 4 A 4546469 F 080200029 F 420208409 F 440102000 000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 C 37081 C 08 F 01 F 39081902 E 9 E 82 DF 912 E 0 C 73 BD 3 C 3 F 7 7 A 530 A 70998 DB 353 D 61651 CE 91623 F 20 FA 97938001 E 23 C 32 A 1 BBDB 33 B 99 F 04 D 7 BA 496 E 2 C 205 FAAD 841358418 B 47 BD 39671 D 88957 ECF 4 AF 08 D 6 C 13 F 1 B 7 EBA 6 BF 21 A 893 A 3 F 34699 78 D 43 DB 7634 D 5 CAA 1 C 15396242 B 99 BE 3988 B 7 A 5 CF 2 B 44288 E 9 FF 29097 AF 02 D 9 A 61 B 6 C 27 CE 89390 A 94 F 738772811713 ED 38 F 1 F 5 D 29122 FB 824 DFC 7701 CF 2 B 92242 B 97330 BA 4 E 9 A 6 F 288 D 450 D 98 F 9 BB 36 D 9 ABF 001 EEF 883 F 51 D 99 B 683 ADD 8 EBE 99577 E 83 C 99 F 3201030000000000000000000000000000000000000000 BE 7081 BB 9 F 468190144 F 280 DB 621 BE 009632 BF 0 CD 887 BFC 885 DC 62885 BA 2 CCC 951 D 7 DEDA 9 B 34 B 7 CDC 07 BC 822 D 5 D 6 CB 555 F 5 B 881141 F 57069 D 4 E 779 FE 8 A 85 BDBFE 69801 BAB 48385 D 75 BEE 0 D 4806 AA 9 A 20141 B 70574 B 58342205 DC 344 B 8 BB 4 D 94909 B 4 EA 3996 A 9372 B 9 E 4044537 FA 2 E 0 FC 3 A 26 BAEABAFEBCEE 1060 E 3 DE 4 D 1 A 2319 D 277 AFB 0732602 D 4 F 2353 A 955868 D 21 C 9 C 5394 A 74 D 98 F 7 AE 9 F 4701039 F 481 AB 952237 C 92 A 10 BC 1 A 6 FC 2 CE 80 E 8 F 0257 A 24 DDAD 08 E 74 E 145 D 48 D 9 F 49039 F 370 4000000000000000000000000000000000000000000000000000000000000000001 F 701 D 9 F 5501 F 09 F 561 60180007 FFFFFF 00000000003000 FF 00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 000000000000000000000001761154 F 07 A 000041010500 A 4 D 41535445524341524400296 F 278407 A 000041010 A 51 C 500 A 4 D 4153544552434152448 701015 F 2 D 02656 EBF 0 C 059 F 4 D 020 B 0 A 0000 %B 5268 xxxxxx^Smith/John^110 12011660400000000000? ; 5268 xxxxxx=1101201166040000?
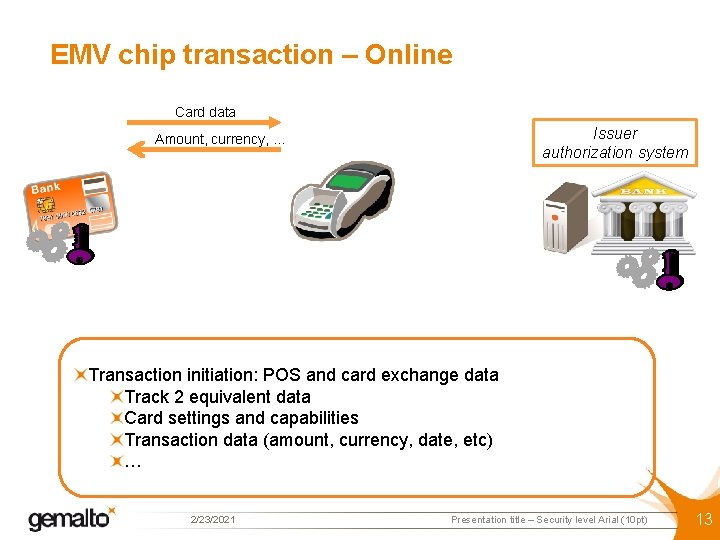
EMV chip transaction – Online Card data Issuer authorization system Amount, currency, … Transaction initiation: POS and card exchange data Track 2 equivalent data Card settings and capabilities Transaction data (amount, currency, date, etc) … 2/23/2021 Presentation title – Security level Arial (10 pt) 13
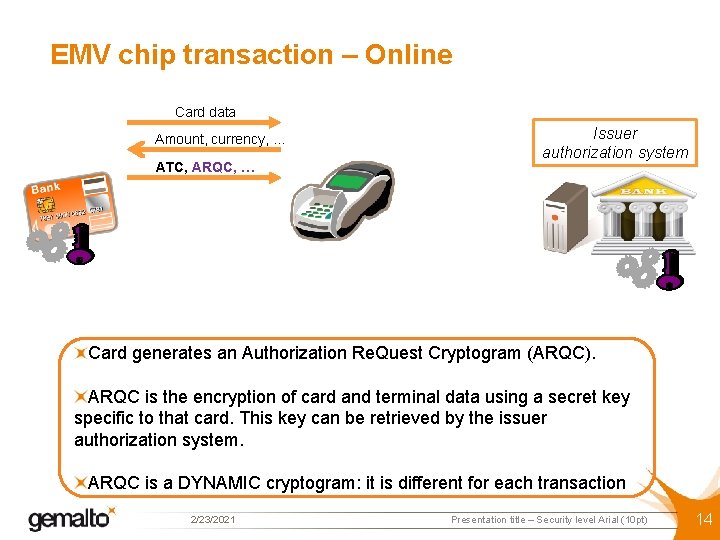
EMV chip transaction – Online Card data Amount, currency, … ATC, ARQC, … Issuer authorization system Card generates an Authorization Re. Quest Cryptogram (ARQC). ARQC is the encryption of card and terminal data using a secret key specific to that card. This key can be retrieved by the issuer authorization system. ARQC is a DYNAMIC cryptogram: it is different for each transaction 2/23/2021 Presentation title – Security level Arial (10 pt) 14
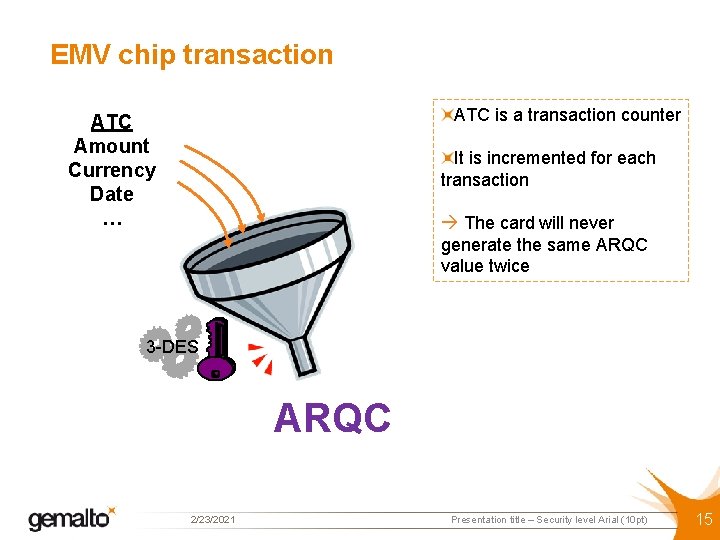
EMV chip transaction ATC is a transaction counter ATC Amount Currency Date … It is incremented for each transaction The card will never generate the same ARQC value twice 3 -DES ARQC 2/23/2021 Presentation title – Security level Arial (10 pt) 15
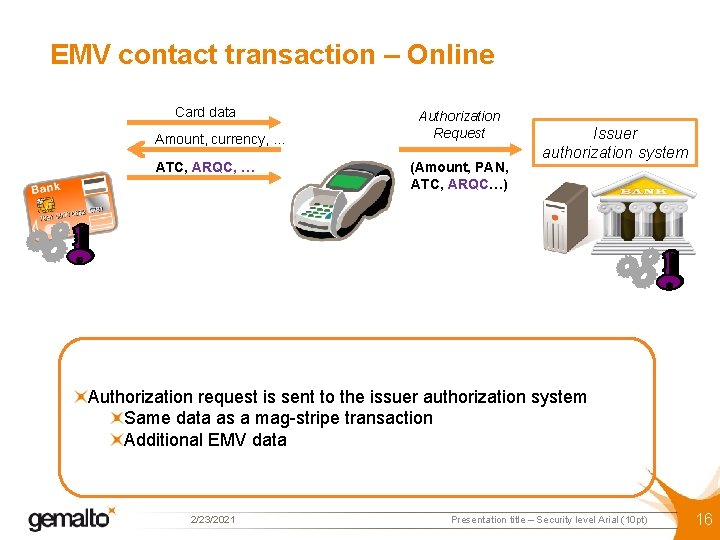
EMV contact transaction – Online Card data Amount, currency, … ATC, ARQC, … Authorization Request (Amount, PAN, ATC, ARQC…) Issuer authorization system Authorization request is sent to the issuer authorization system Same data as a mag-stripe transaction Additional EMV data 2/23/2021 Presentation title – Security level Arial (10 pt) 16
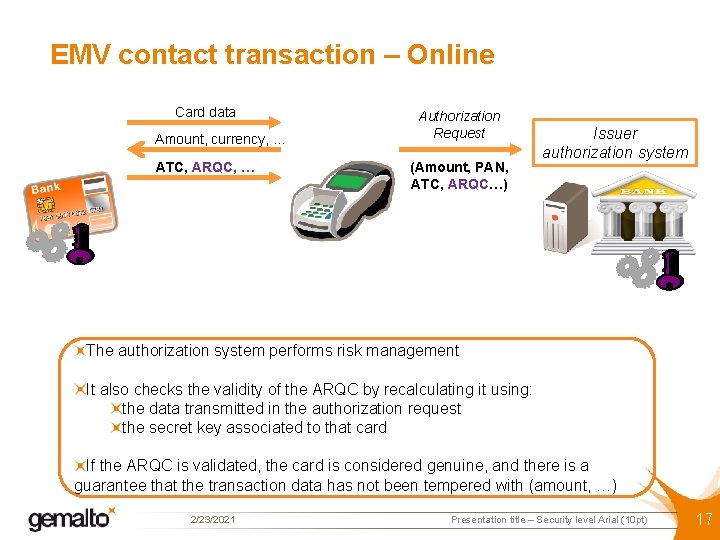
EMV contact transaction – Online Card data Amount, currency, … ATC, ARQC, … Authorization Request (Amount, PAN, ATC, ARQC…) Issuer authorization system The authorization system performs risk management It also checks the validity of the ARQC by recalculating it using: the data transmitted in the authorization request the secret key associated to that card If the ARQC is validated, the card is considered genuine, and there is a guarantee that the transaction data has not been tempered with (amount, …) 2/23/2021 Presentation title – Security level Arial (10 pt) 17
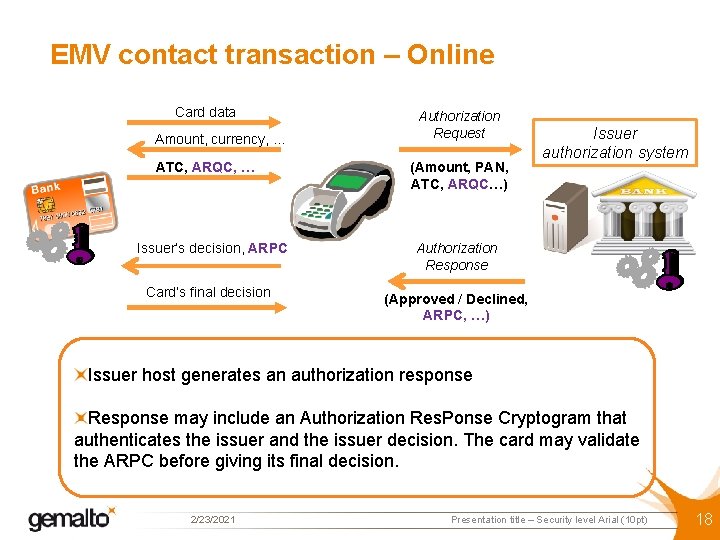
EMV contact transaction – Online Card data Amount, currency, … ATC, ARQC, … Issuer’s decision, ARPC Card’s final decision Authorization Request (Amount, PAN, ATC, ARQC…) Issuer authorization system Authorization Response (Approved / Declined, ARPC, …) Issuer host generates an authorization response Response may include an Authorization Res. Ponse Cryptogram that authenticates the issuer and the issuer decision. The card may validate the ARPC before giving its final decision. 2/23/2021 Presentation title – Security level Arial (10 pt) 18
EMV contact transaction – Online Card authentication is based on DYNAMIC data (ARQC) generated by the card secret key Card secret key cannot be retrieved from one card and duplicated onto another card 2/23/2021 Presentation title – Security level Arial (10 pt) 19
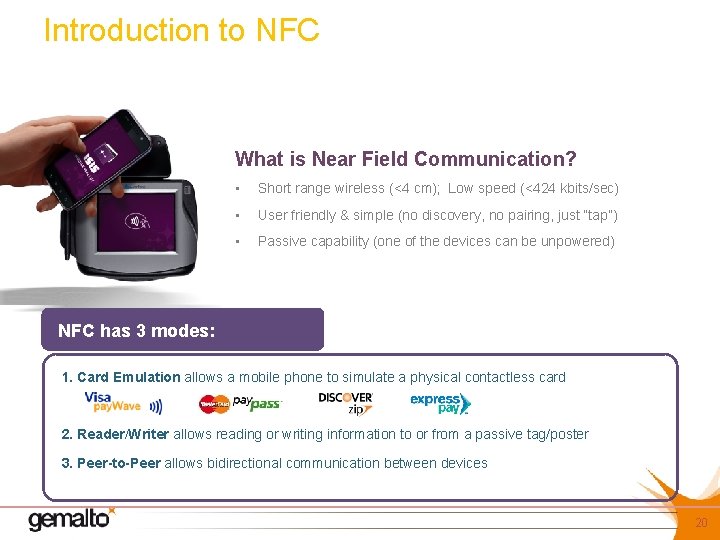
Introduction to NFC What is Near Field Communication? • Short range wireless (<4 cm); Low speed (<424 kbits/sec) • User friendly & simple (no discovery, no pairing, just “tap”) • Passive capability (one of the devices can be unpowered) NFC has 3 modes: 1. Card Emulation allows a mobile phone to simulate a physical contactless card 2. Reader/Writer allows reading or writing information to or from a passive tag/poster 3. Peer-to-Peer allows bidirectional communication between devices 20
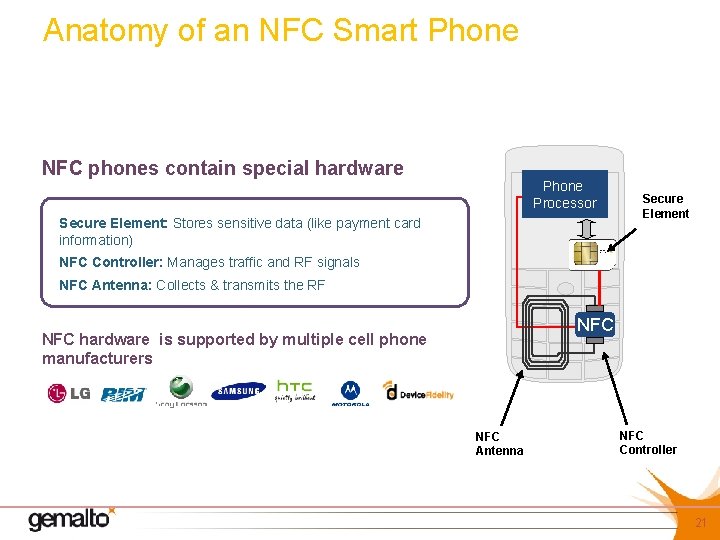
Anatomy of an NFC Smart Phone NFC phones contain special hardware Phone Processor Secure Element: Stores sensitive data (like payment card information) Secure Element NFC Controller: Manages traffic and RF signals NFC Antenna: Collects & transmits the RF NFC hardware is supported by multiple cell phone manufacturers NFC Antenna NFC Controller 21
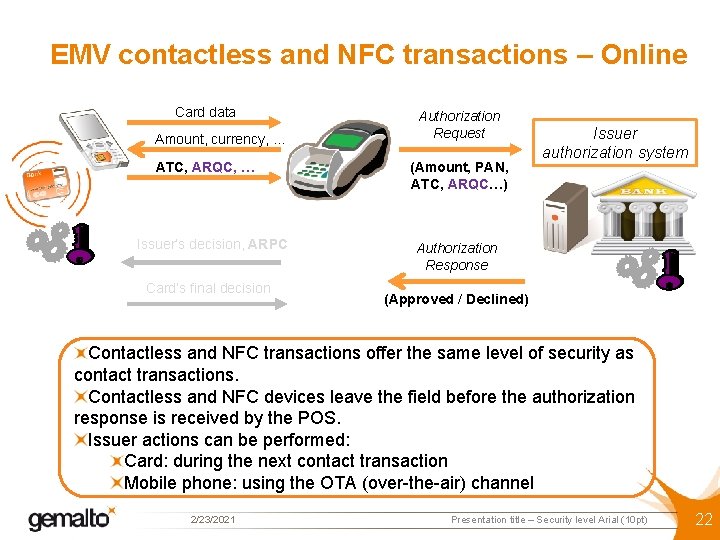
EMV contactless and NFC transactions – Online Card data Amount, currency, … ATC, ARQC, … Issuer’s decision, ARPC Card’s final decision Authorization Request (Amount, PAN, ATC, ARQC…) Issuer authorization system Authorization Response (Approved / Declined) Contactless and NFC transactions offer the same level of security as contact transactions. Contactless and NFC devices leave the field before the authorization response is received by the POS. Issuer actions can be performed: Card: during the next contact transaction Mobile phone: using the OTA (over-the-air) channel 2/23/2021 Presentation title – Security level Arial (10 pt) 22
Agenda The changing POS payment environment Mag-Stripe, EMV, NFC…. NFC - TSM ecosystem NFC Payment examples Conclusion
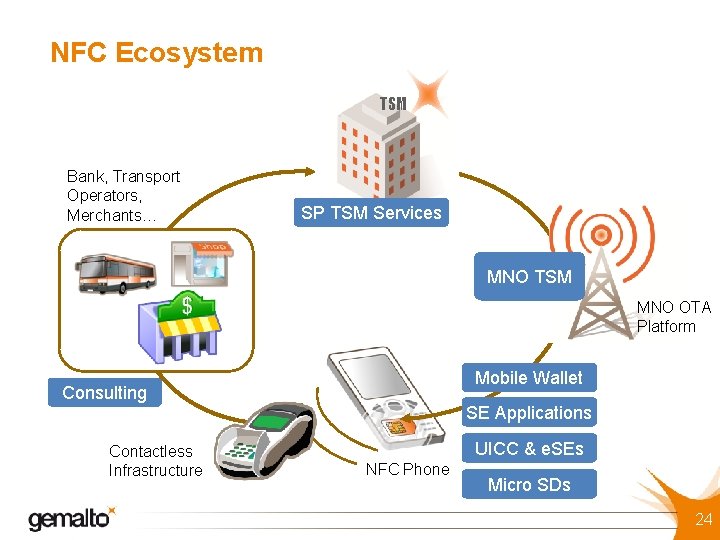
NFC Ecosystem TSM Bank, Transport Operators, Merchants… SP TSM Services MNO TSM MNO OTA Platform Mobile Wallet Consulting Contactless Infrastructure SE Applications UICC & e. SEs NFC Phone Micro SDs 24
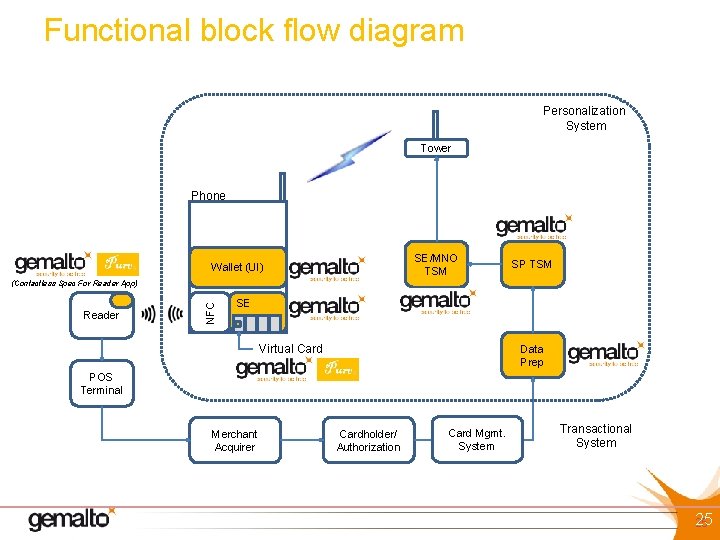
Functional block flow diagram Personalization System Tower Phone SE/MNO TSM Wallet (UI) SP TSM Reader NFC (Contactless Spec For Reader App) SE Virtual Card Data Prep POS Terminal Merchant Acquirer Cardholder/ Authorization Card Mgmt. System Transactional System 25 25
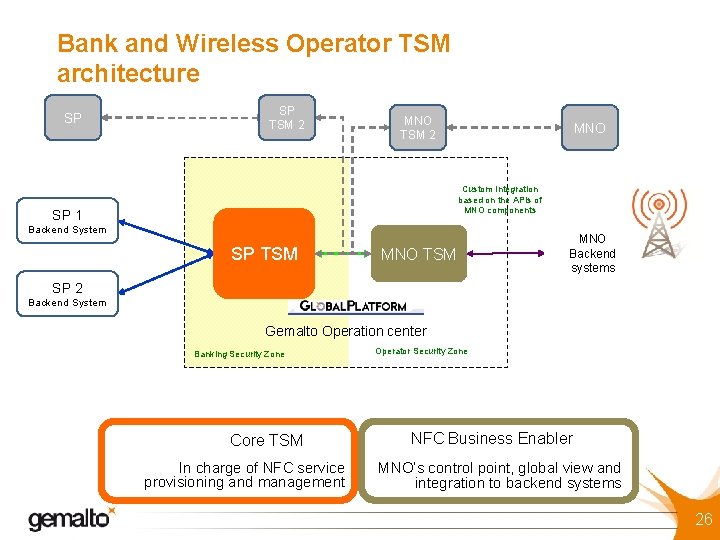
Bank and Wireless Operator TSM architecture SP SP TSM 2 MNO Custom Integration based on the APIs of MNO components SP 1 Backend System SP TSM MNO Backend systems SP 2 Backend System Gemalto Operation center Banking Security Zone Core TSM In charge of NFC service provisioning and management Operator Security Zone NFC Business Enabler MNO’s control point, global view and integration to backend systems 26
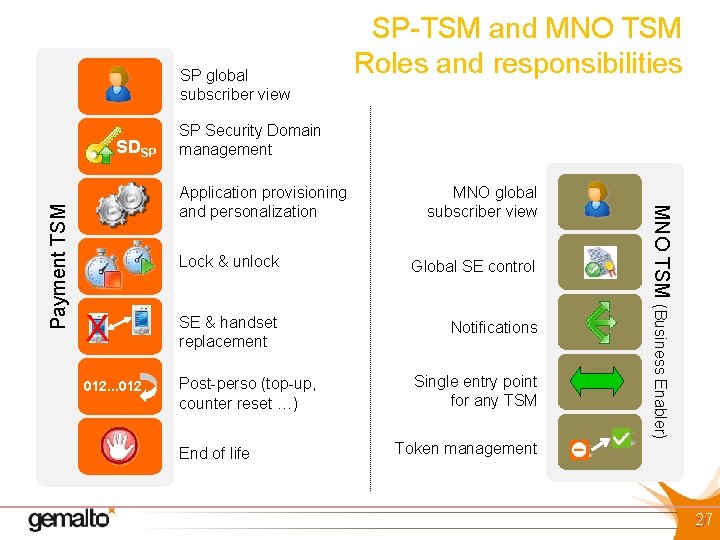
SP global subscriber view SP Security Domain management Application provisioning and personalization MNO global subscriber view Lock & unlock Global SE control X SE & handset replacement Notifications 012. . . 012 Post-perso (top-up, counter reset …) End of life Single entry point for any TSM Token management MNO TSM (Business Enabler) Payment TSM SDSP SP-TSM and MNO TSM Roles and responsibilities 27 27
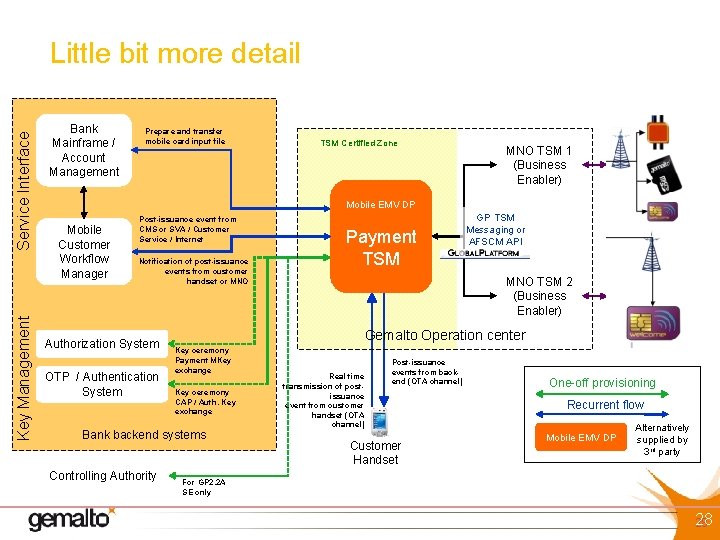
Key Management Service Interface Little bit more detail Bank Mainframe / Account Management Prepare and transfer mobile card input file TSM Certified Zone NBE MNO TSM 1 (Business Enabler) MNO 1 Backend System Mobile EMV DP Mobile Customer Workflow Manager Post-issuance event from CMS or SVA / Customer Service / Internet Notification of post-issuance events from customer handset or MNO Authorization System OTP / Authentication System MNO TSM 2 (Business Enabler) MNO 2 Backend System Gemalto Operation center Key ceremony Payment MKey exchange Key ceremony CAP / Auth. Key exchange Bank backend systems Controlling Authority Payment TSM GP TSM Messaging or AFSCM API Real time transmission of postissuance event from customer handset (OTA channel) Post-issuance events from backend (OTA channel) Customer Handset One-off provisioning Recurrent flow Mobile EMV DP Alternatively supplied by 3 rd party For GP 2. 2 A SE only 28 28
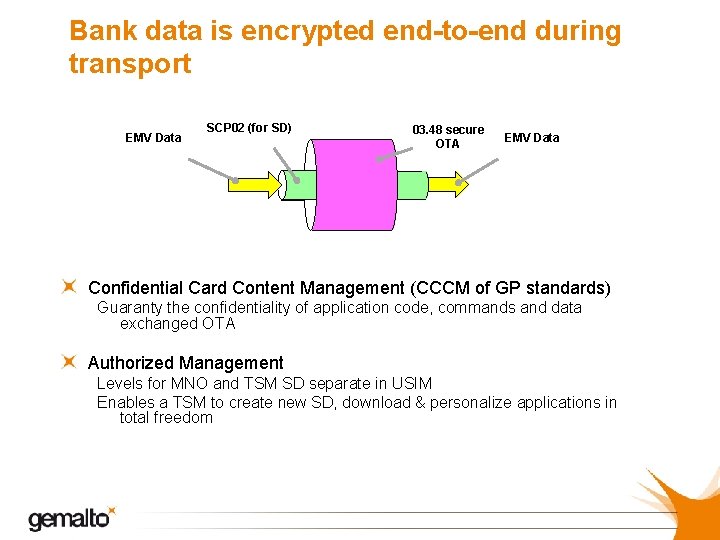
Bank data is encrypted end-to-end during transport EMV Data SCP 02 (for SD) 03. 48 secure OTA EMV Data Confidential Card Content Management (CCCM of GP standards) Guaranty the confidentiality of application code, commands and data exchanged OTA Authorized Management Levels for MNO and TSM SD separate in USIM Enables a TSM to create new SD, download & personalize applications in total freedom
Agenda The changing POS payment environment Mag-Stripe, EMV, NFC…. NFC - TSM ecosystem NFC Payment examples Conclusion
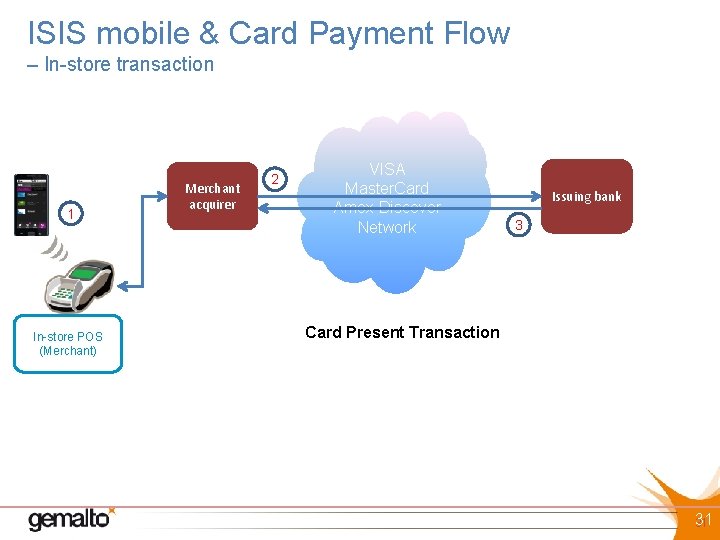
ISIS mobile & Card Payment Flow – In-store transaction 1 In-store POS (Merchant) Merchant acquirer 2 VISA Master. Card Amex Discover Network Issuing bank 3 Card Present Transaction 31 31
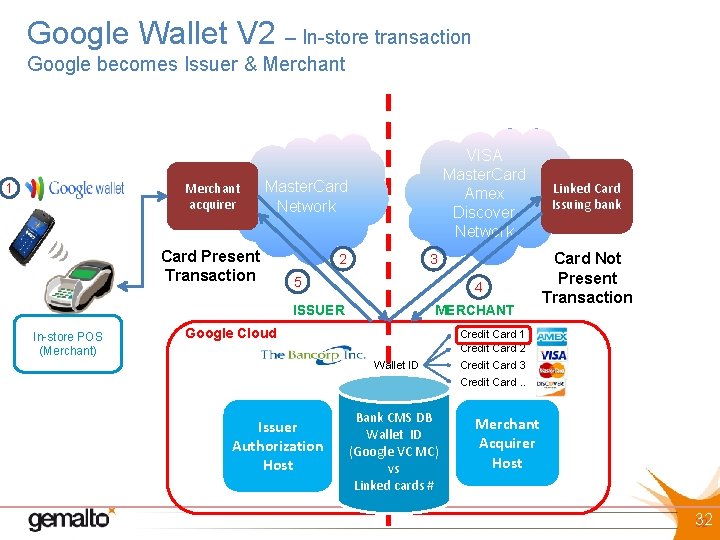
Google Wallet V 2 – In-store transaction Google becomes Issuer & Merchant acquirer 1 VISA Master. Card Amex Discover Network Master. Card Network Card Present Transaction 2 3 5 4 ISSUER In-store POS (Merchant) MERCHANT Google Cloud Linked Card Issuing bank Card Not Present Transaction Credit Card 1 Credit Card 2 Wallet ID Credit Card 3 Credit Card. . Issuer Authorization Host Bank CMS DB Wallet ID (Google VC MC) vs Linked cards # Merchant Acquirer Host 32 32
Conclusion EMV infrastructure is much more secure than the existing mag-stripe card infrastructure. NFC mobile payment leverages existing EMV POS methodology to enhance mobile payment security Payment risk ownership will be predicated on the back office model adopted by the mobile provider & Issuing bank

Technology in Retail Payment Innovations Jack Jania SVP Gemalto Jack. Jania@gemalto. com October 2012
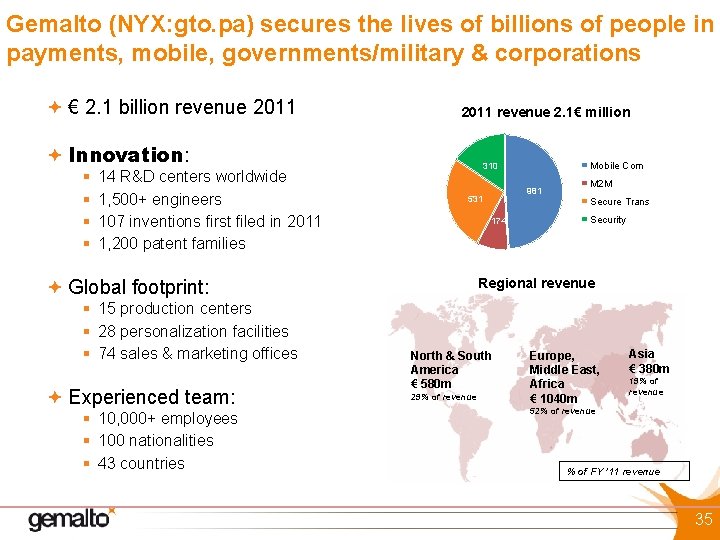
Gemalto (NYX: gto. pa) secures the lives of billions of people in payments, mobile, governments/military & corporations € 2. 1 billion revenue 2011 revenue 2. 1€ million Innovation: § § 14 R&D centers worldwide 1, 500+ engineers 107 inventions first filed in 2011 1, 200 patent families Experienced team: § 10, 000+ employees § 100 nationalities § 43 countries 981 531 174 M 2 M Secure Trans Security Regional revenue Global footprint: § 15 production centers § 28 personalization facilities § 74 sales & marketing offices Mobile Com 310 North & South America € 580 m 29% of revenue Europe, Middle East, Africa € 1040 m Asia € 380 m 19% of revenue 52% of revenue % of FY ’ 11 revenue 35
- Slides: 35