Technical Community Events founded by the CIP Program


• Technical Community Events (founded by the CIP Program) • Deep Microsoft-technology based discussions and opportunity to network / bring technical community together • Opportunity to evangelize, promote and sell Microsoft Products and Services • Flagship Technical Community event for the Community Immersion program – Role-model for other events and communities+ • Over 3400 members!! • Location Information Links: http: //www. meetup. com/mttcharlotte http: //www. meetup. com/mtttempe http: //www. meetup. com/mttsocal http: //www. meetup. com/mttlasvegas http: //www. meetup. com/mttpacwest http: //www. meetup. com/mttdetroit http: //www. meetup. com/mttnorcal http: //www. meetup. com/mttatlanta https: //www. meetup. com/mttnewyork
http: //aka. ms/MTTCharlotte. March Troubleshooting Windows Application for the IT Admin – http: //aka. ms/MTTCharlotte. April (link not active yet) http: //www. meetup. com/mttcharlotte
https: //aka. ms/charlottesurvey
https: //aka. ms/grabit
Mark Bias & Darol Timberlake Enterprise Services
Presentation Agenda • • • Overview Configuration Suspicious Alert Discussion

Foundation of security assurances for all information assets in the organization: • Authenticates all user and computer accounts within the on-premises Active Directory infrastructure • Centralized delegation and authorization mechanism for many resources. Modern cyber-attackers actively target directories to get intellectual property and corporate assets 10
11
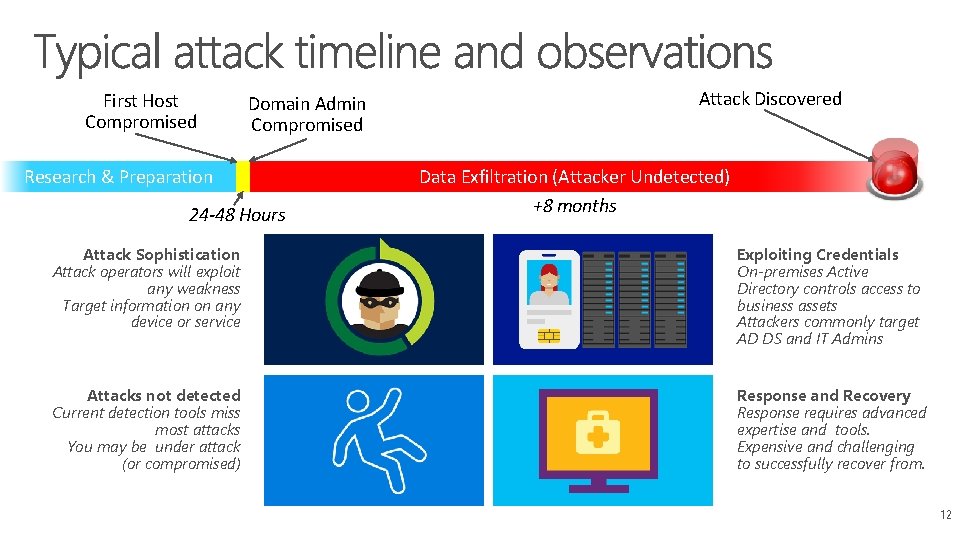
First Host Compromised Domain Admin Compromised Research & Preparation 24 -48 Hours Attack Discovered Data Exfiltration (Attacker Undetected) +8 months Attack Sophistication Attack operators will exploit any weakness Target information on any device or service Exploiting Credentials On-premises Active Directory controls access to business assets Attackers commonly target AD DS and IT Admins Attacks not detected Current detection tools miss most attacks You may be under attack (or compromised) Response and Recovery Response requires advanced expertise and tools. Expensive and challenging to successfully recover from. 12

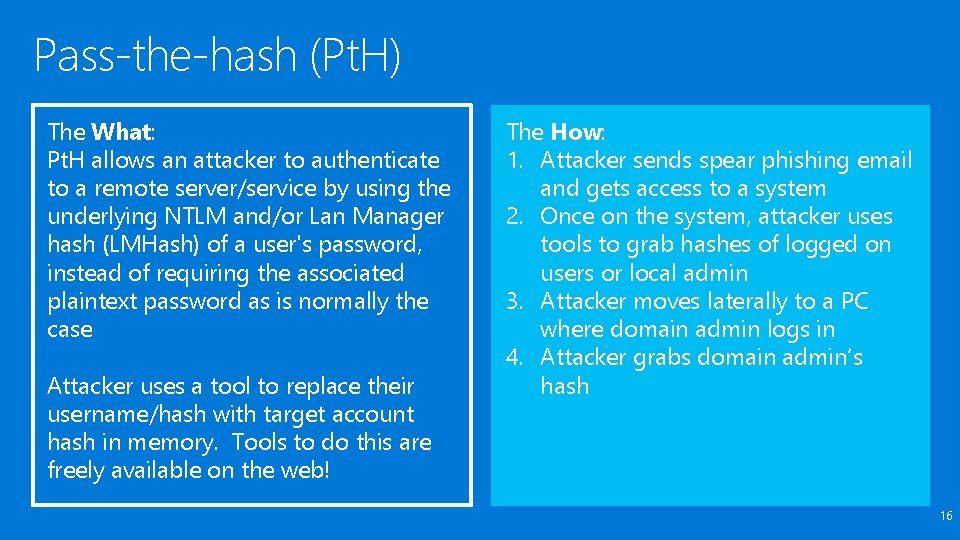
Pass-the-hash (Pt. H) The What: Pt. H allows an attacker to authenticate to a remote server/service by using the underlying NTLM and/or Lan Manager hash (LMHash) of a user's password, instead of requiring the associated plaintext password as is normally the case Attacker uses a tool to replace their username/hash with target account hash in memory. Tools to do this are freely available on the web! The How: 1. Attacker sends spear phishing email and gets access to a system 2. Once on the system, attacker uses tools to grab hashes of logged on users or local admin 3. Attacker moves laterally to a PC where domain admin logs in 4. Attacker grabs domain admin’s hash 16
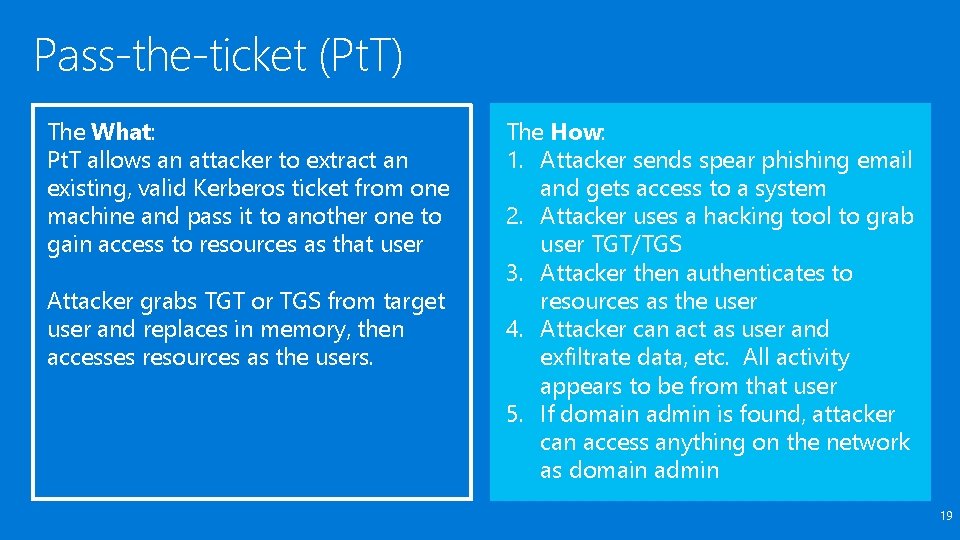
Pass-the-ticket (Pt. T) The What: Pt. T allows an attacker to extract an existing, valid Kerberos ticket from one machine and pass it to another one to gain access to resources as that user Attacker grabs TGT or TGS from target user and replaces in memory, then accesses resources as the users. The How: 1. Attacker sends spear phishing email and gets access to a system 2. Attacker uses a hacking tool to grab user TGT/TGS 3. Attacker then authenticates to resources as the user 4. Attacker can act as user and exfiltrate data, etc. All activity appears to be from that user 5. If domain admin is found, attacker can access anything on the network as domain admin 19
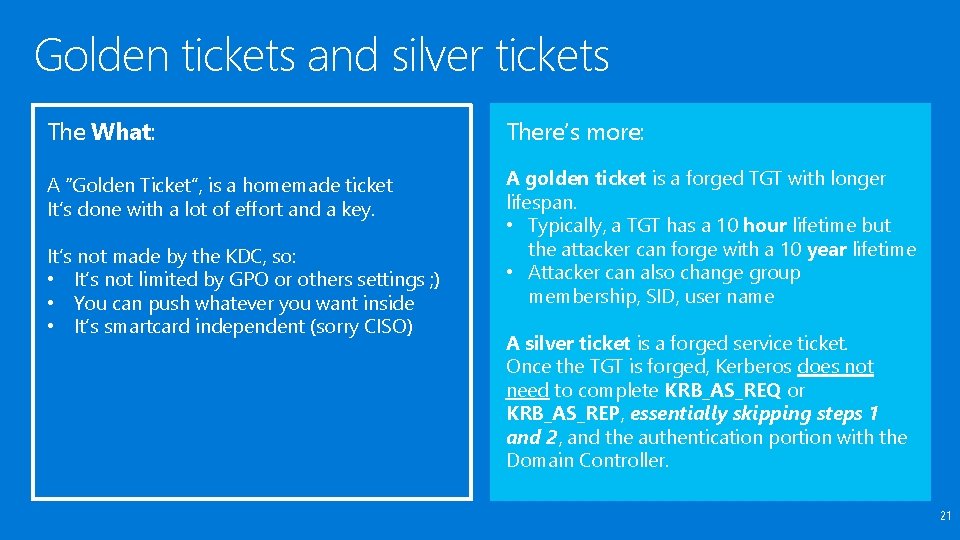
Golden tickets and silver tickets The What: There’s more: A “Golden Ticket”, is a homemade ticket It’s done with a lot of effort and a key. A golden ticket is a forged TGT with longer lifespan. • Typically, a TGT has a 10 hour lifetime but the attacker can forge with a 10 year lifetime • Attacker can also change group membership, SID, user name It’s not made by the KDC, so: • It’s not limited by GPO or others settings ; ) • You can push whatever you want inside • It’s smartcard independent (sorry CISO) A silver ticket is a forged service ticket. Once the TGT is forged, Kerberos does not need to complete KRB_AS_REQ or KRB_AS_REP, essentially skipping steps 1 and 2, and the authentication portion with the Domain Controller. 21
Overpass-the-hash The What: Ot. H is a hacking technique that allows an attacker to use the NTLM hash to obtain a valid user Kerberos ticket request. The user key (NTLM hash when using RC 4) is used to encrypt the Pre-Authentication & first data requests The How : 1. Attacker sends spear phishing email and gets access to a system 2. Attacker uses a hacking tool to grab user hash and generates Kerberos request 3. Attacker then authenticates to resources as the user 24

26
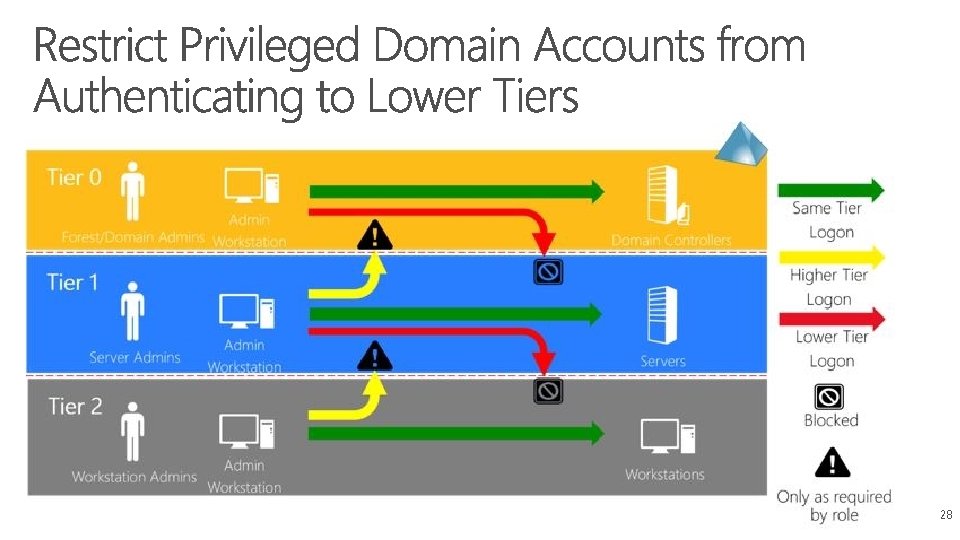
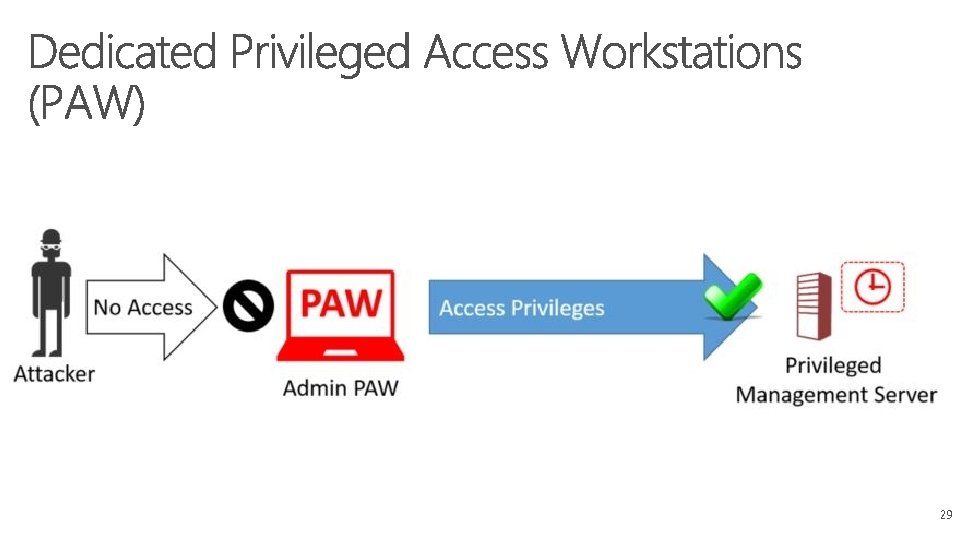
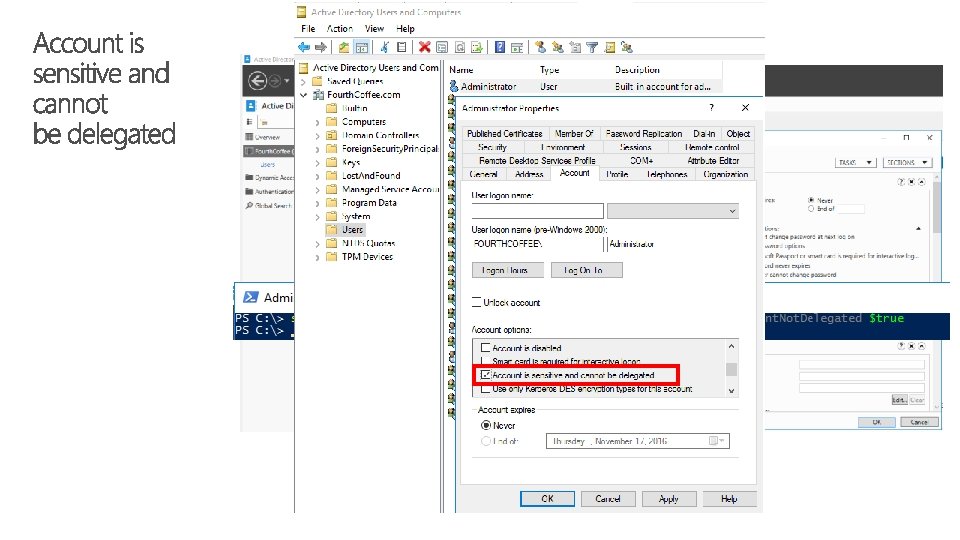
Restrict and protect high privileged domain accounts Restrict domain administrator accounts and other privileged accounts from authenticating to lower trust servers and workstations. An attacker cannot steal credentials for an account if the credentials are never used on the compromised computer. Provide admins with accounts to perform administrative duties that are separate from their normal user accounts. Using these mitigations significantly reduces the risk of attackers compromising privileged accounts. Assign dedicated workstations for administrative tasks. Mark privileged accounts as “sensitive and cannot be delegated” in Active Directory. Do not configure services or schedule tasks to use privileged domain accounts on lower trust systems, such as user workstations. 27
28
29
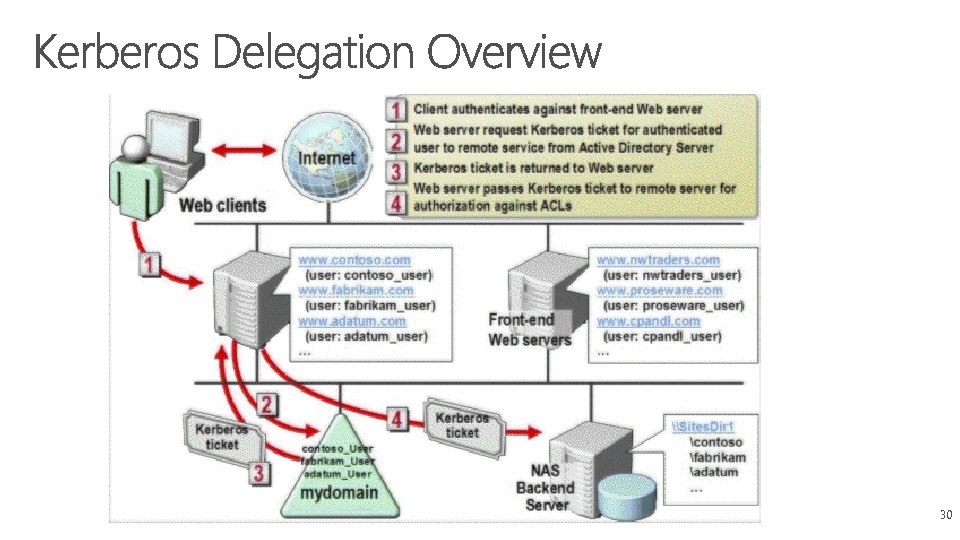
30
Restrict and protect local accounts with administrative privileges Restrict the ability of attackers to use administrative local accounts for lateral movement Pt. H attacks. Enforce the restrictions that prevent local accounts from being used for remote administration. An attacker who successfully obtains local account credentials from a compromised computer will not be able to use those credentials to perform lateral movement on the organization's network. Explicitly deny network and Remote Desktop logon rights for all administrative local accounts. Create unique passwords for local accounts with administrative privileges. 32
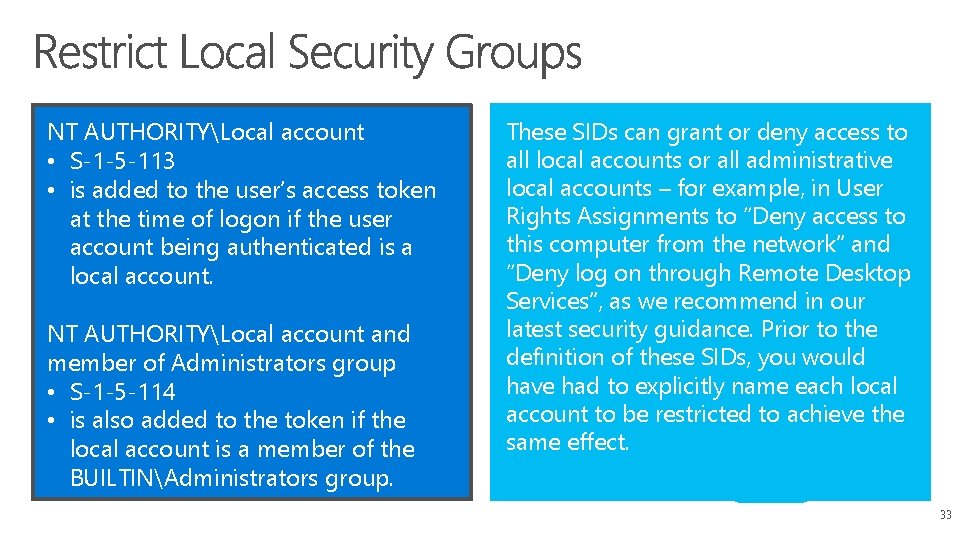
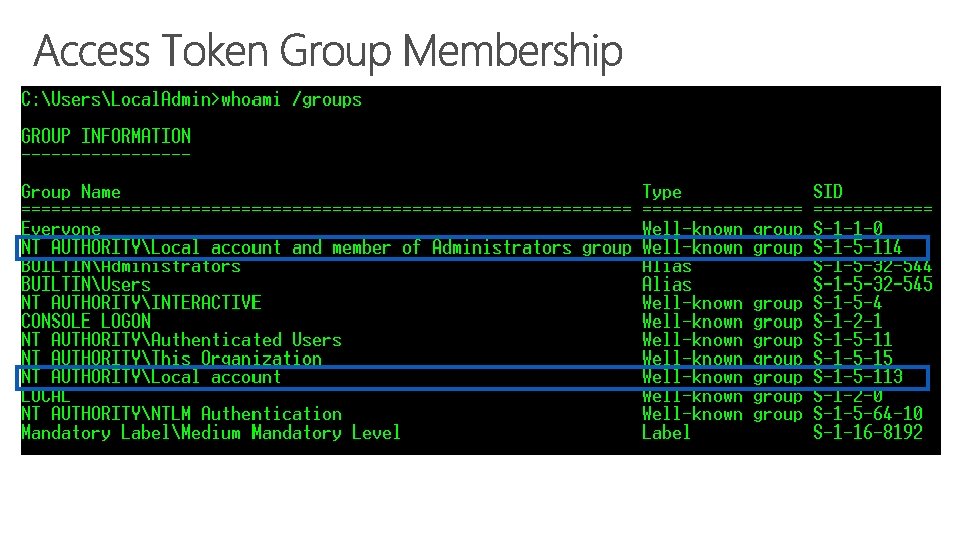
NT AUTHORITYLocal account • S-1 -5 -113 • is added to the user’s access token at the time of logon if the user account being authenticated is a local account. NT AUTHORITYLocal account and member of Administrators group • S-1 -5 -114 • is also added to the token if the local account is a member of the BUILTINAdministrators group. These SIDs can grant or deny access to all local accounts or all administrative local accounts – for example, in User Rights Assignments to “Deny access to this computer from the network” and “Deny log on through Remote Desktop Services”, as we recommend in our latest security guidance. Prior to the definition of these SIDs, you would have had to explicitly name each local account to be restricted to achieve the same effect. 33

Local Administrator Password Solution (LAPS) 35
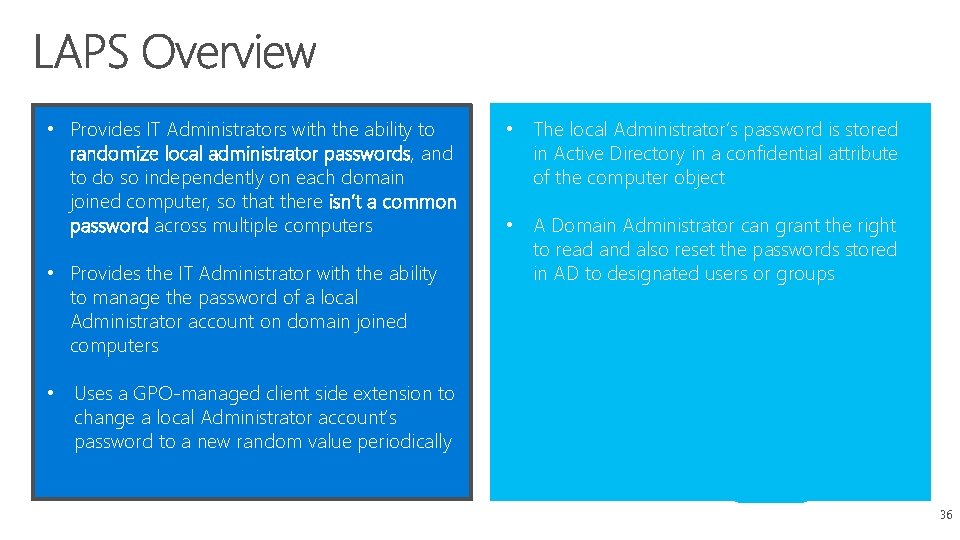
• Provides IT Administrators with the ability to randomize local administrator passwords, and to do so independently on each domain joined computer, so that there isn’t a common password across multiple computers • Provides the IT Administrator with the ability to manage the password of a local Administrator account on domain joined computers • The local Administrator’s password is stored in Active Directory in a confidential attribute of the computer object • A Domain Administrator can grant the right to read and also reset the passwords stored in AD to designated users or groups • Uses a GPO-managed client side extension to change a local Administrator account’s password to a new random value periodically 36
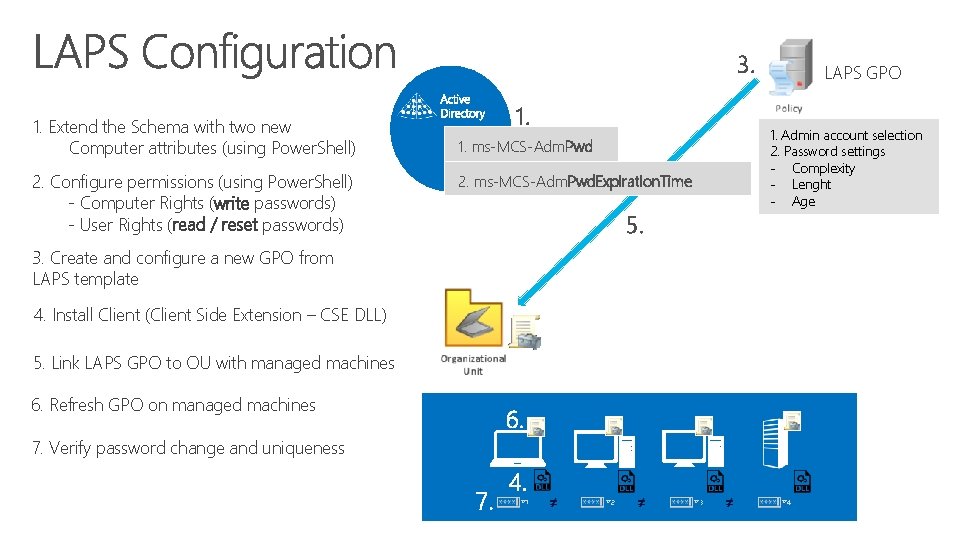
3. 1. Extend the Schema with two new Computer attributes (using Power. Shell) 2. Configure permissions (using Power. Shell) - Computer Rights (write passwords) - User Rights (read / reset passwords) 1. LAPS GPO 1. Admin account selection 2. Password settings - Complexity - Lenght - Age 1. ms-MCS-Adm. Pwd 2. ms-MCS-Adm. Pwd. Expiration. Time 5. 3. Create and configure a new GPO from LAPS template 4. Install Client (Client Side Extension – CSE DLL) 5. Link LAPS GPO to OU with managed machines 6. Refresh GPO on managed machines 6. 7. Verify password change and uniqueness 7. 4. #1 #2 #3 #4
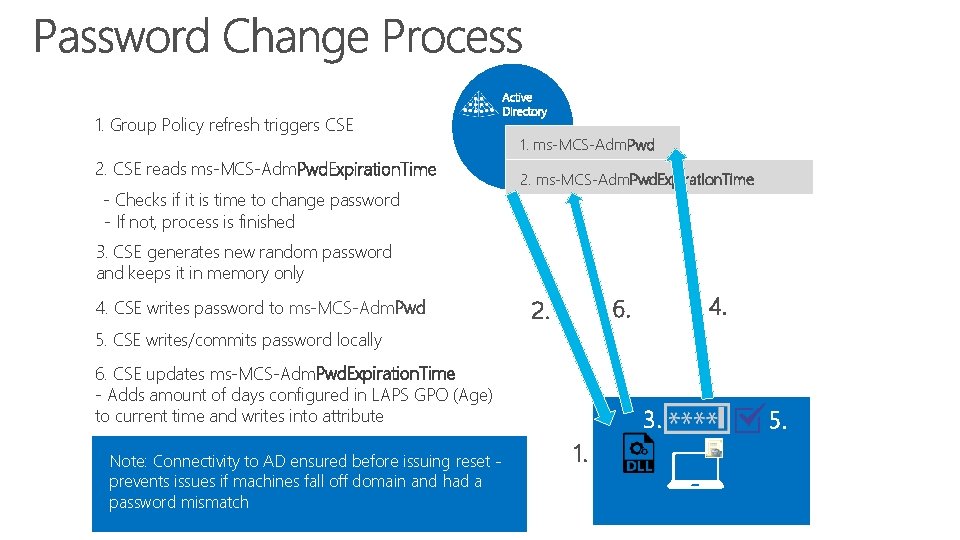
1. Group Policy refresh triggers CSE 2. CSE reads ms-MCS-Adm. Pwd. Expiration. Time - Checks if it is time to change password - If not, process is finished 1. ms-MCS-Adm. Pwd 2. ms-MCS-Adm. Pwd. Expiration. Time 3. CSE generates new random password and keeps it in memory only 4. CSE writes password to ms-MCS-Adm. Pwd 4. 6. 2. 5. CSE writes/commits password locally 6. CSE updates ms-MCS-Adm. Pwd. Expiration. Time - Adds amount of days configured in LAPS GPO (Age) to current time and writes into attribute Note: Connectivity to AD ensured before issuing reset prevents issues if machines fall off domain and had a password mismatch 3. 1. 5.
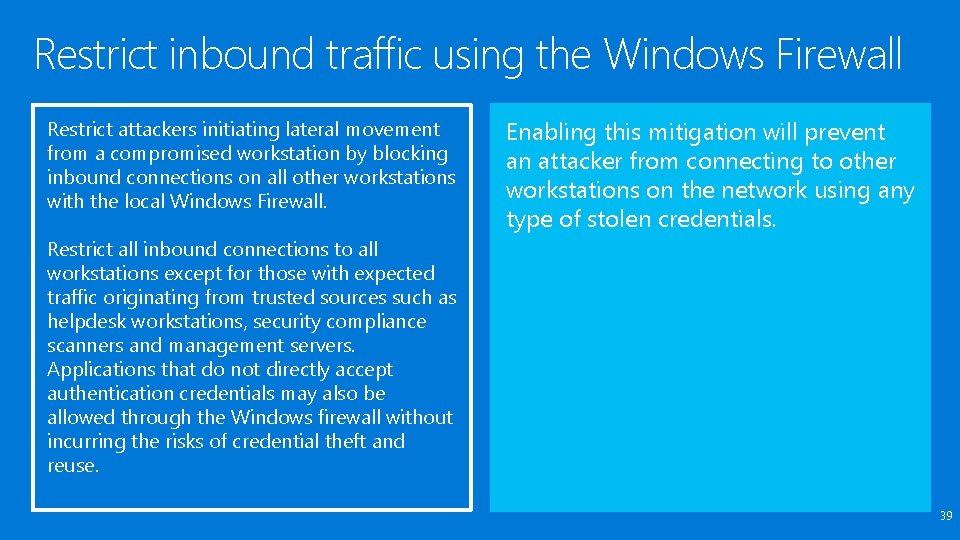
Restrict inbound traffic using the Windows Firewall Restrict attackers initiating lateral movement from a compromised workstation by blocking inbound connections on all other workstations with the local Windows Firewall. Enabling this mitigation will prevent an attacker from connecting to other workstations on the network using any type of stolen credentials. Restrict all inbound connections to all workstations except for those with expected traffic originating from trusted sources such as helpdesk workstations, security compliance scanners and management servers. Applications that do not directly accept authentication credentials may also be allowed through the Windows firewall without incurring the risks of credential theft and reuse. 39
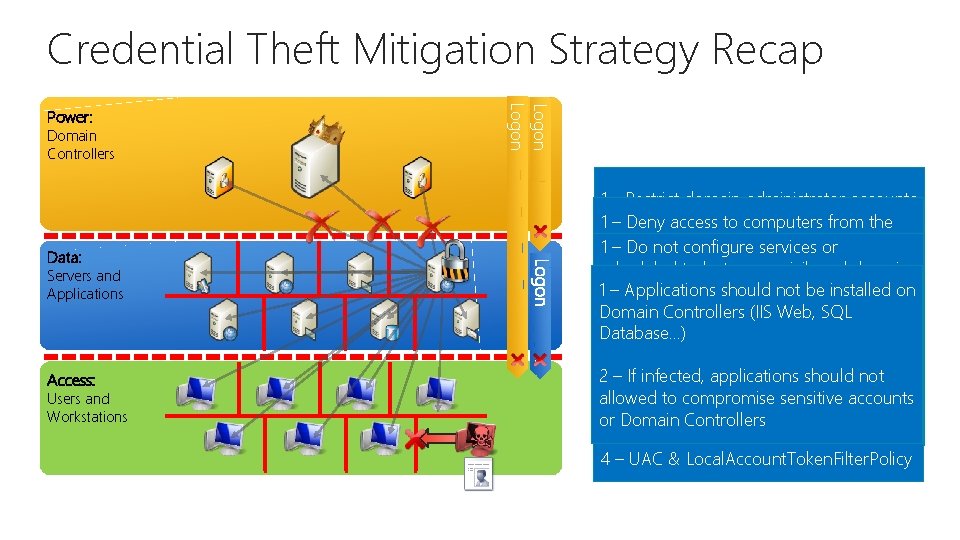
Credential Theft Mitigation Strategy Recap Domain Controllers Logon Power: 1. Privilege Elevation (Credential Partitioning) 2. Lateral Traversal - Local Accounts 1 - Restrict domain administrator accounts otheraccess privileged accounts from the 1 and – Deny to computers 4. 1 network Application andto Service Risks authenticating lower trust servers and & configure Deny logon through – Do not services or terminal workstations services to tasks all local accounts (S-1 -5 -114 & scheduled to use privileged domain S-1 -5 -113) Keep in mind bad guys can targetason 1 accounts – Applications should not bestill installed onthat lower trust systems, such individual computers users, but these 2 - Provide admins & with accounts to Domain Controllers (IIS Web, SQL user workstations mitigations make it passwords much duties harder to: perform are 2 – Haveadministrative unique forthat local Database…) ü Steal powerful credentials separate from their accounts administrative privileges 2 – Have awith list of all normal service /user taskaccounts Doand anything with stolen credentials 2 accounts – Ifüinfected, applications should not are on which machines they 3 –- Assign workstations for Restrict inbound traffic using Windows allowed to dedicated compromise sensitive accounts used administrative tasks Firewall or Domain Controllers 3. Lateral Traversal – Domain Accounts Data: Servers and Applications Access: Users and Workstations 4 – UAC & Local. Account. Token. Filter. Policy
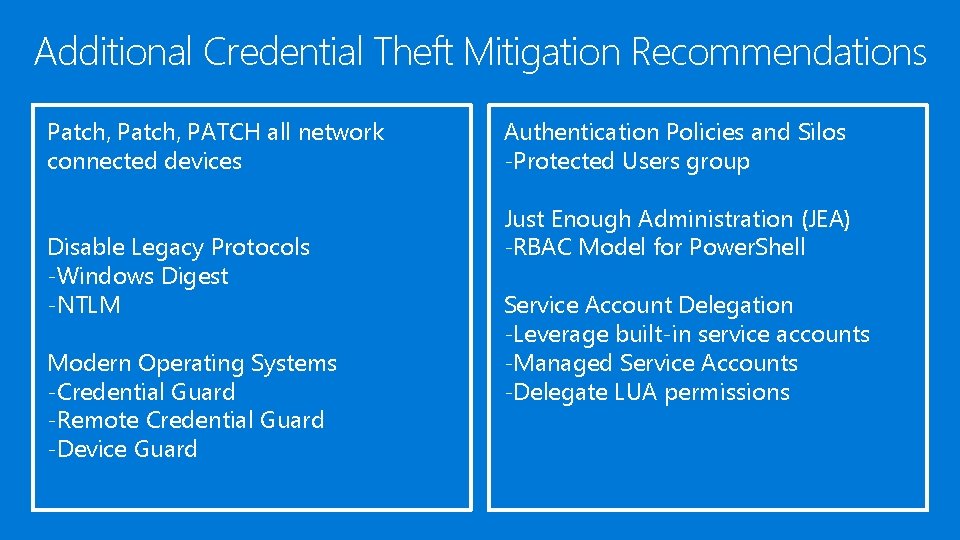
Additional Credential Theft Mitigation Recommendations Patch, PATCH all network connected devices Disable Legacy Protocols -Windows Digest -NTLM Modern Operating Systems -Credential Guard -Remote Credential Guard -Device Guard Authentication Policies and Silos -Protected Users group Just Enough Administration (JEA) -RBAC Model for Power. Shell Service Account Delegation -Leverage built-in service accounts -Managed Service Accounts -Delegate LUA permissions

Security, Identity and Cybersecurity Services Microsoft Advanced Threat Analytics (ATA) Technical Overview

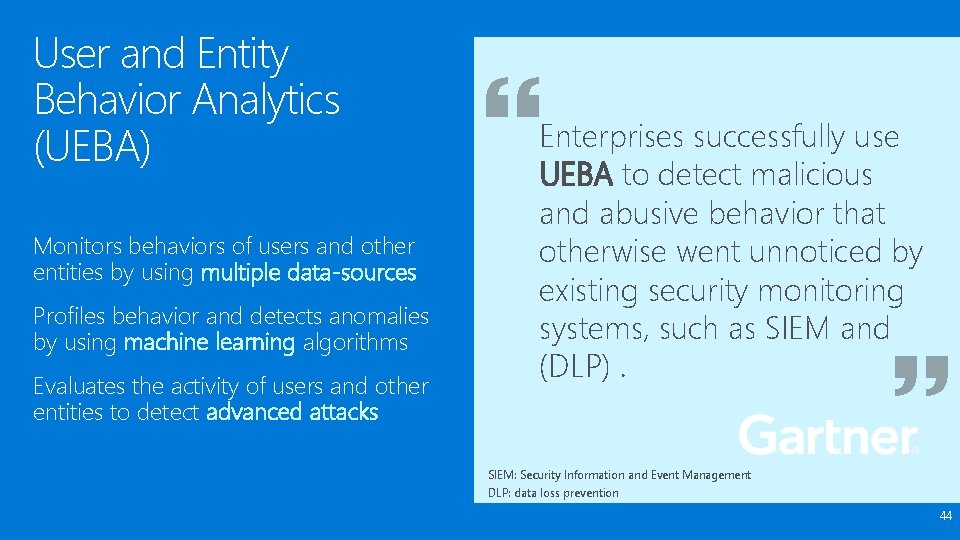
User and Entity Behavior Analytics (UEBA) Monitors behaviors of users and other entities by using multiple data-sources Profiles behavior and detects anomalies by using machine learning algorithms Evaluates the activity of users and other entities to detect advanced attacks Enterprises successfully use UEBA to detect malicious and abusive behavior that otherwise went unnoticed by existing security monitoring systems, such as SIEM and (DLP). SIEM: Security Information and Event Management DLP: data loss prevention 44
Behavior Analytics In Practice Credit card companies monitor cardholders’ behavior. By observing purchases, they learn what is typical behavior for each buyer. $ $$ $ If there is any abnormal activity, they will notify the cardholder to verify charge. 45
Microsoft Advanced Threat Analytics An on-premises platform to identify advanced security attacks before they cause damage Behavioral Analytics Detection for known attacks and issues Advanced Threat Detection Microsoft Advanced Threat Analytics brings the behavioral analytics concept to IT and the organization’s users. 46
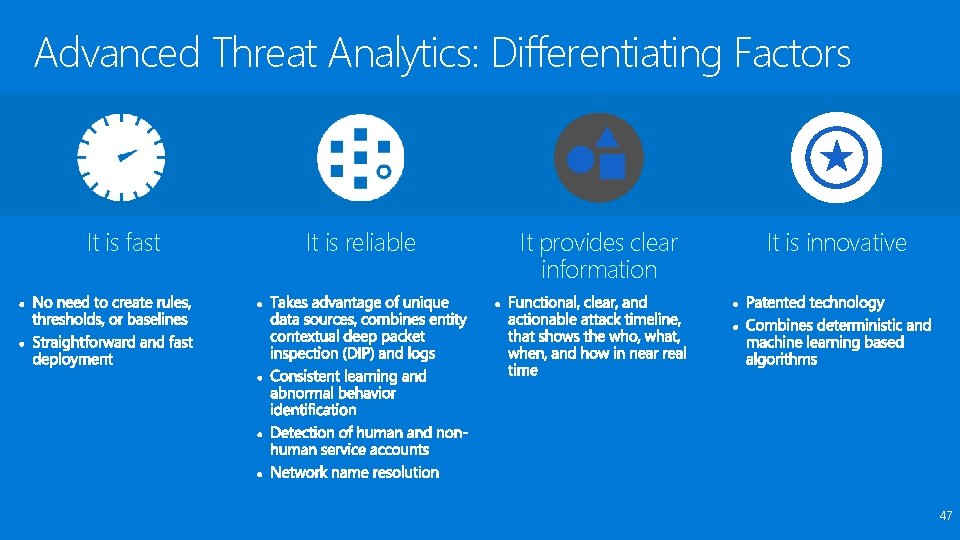
Advanced Threat Analytics: Differentiating Factors It is fast It is reliable It provides clear information It is innovative 47
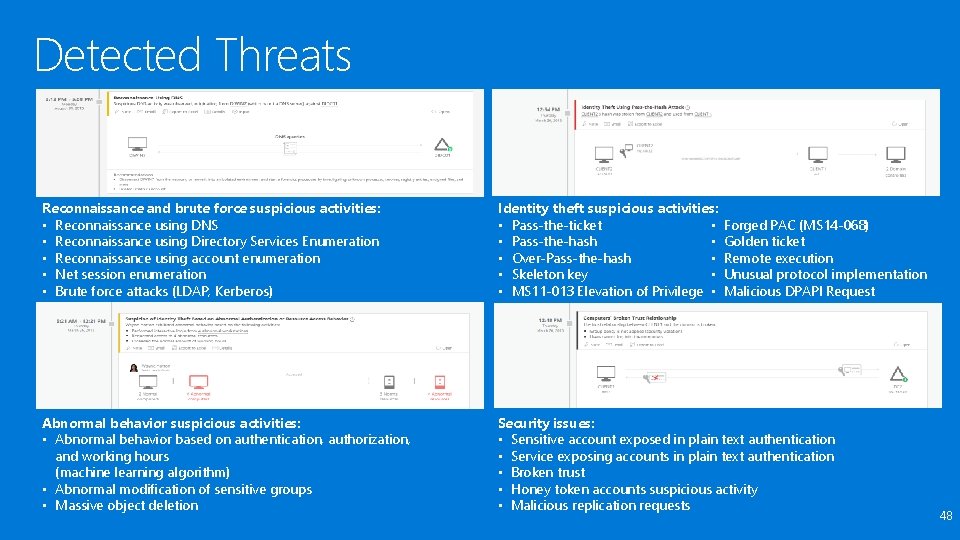
Detected Threats Reconnaissance and brute force suspicious activities: • Reconnaissance using DNS • Reconnaissance using Directory Services Enumeration • Reconnaissance using account enumeration • Net session enumeration • Brute force attacks (LDAP, Kerberos) Identity theft suspicious activities: • Pass-the-ticket • • Pass-the-hash • • Over-Pass-the-hash • • Skeleton key • • MS 11 -013 Elevation of Privilege • Abnormal behavior suspicious activities: • Abnormal behavior based on authentication, authorization, and working hours (machine learning algorithm) • Abnormal modification of sensitive groups • Massive object deletion Security issues: • Sensitive account exposed in plain text authentication • Service exposing accounts in plain text authentication • Broken trust • Honey token accounts suspicious activity • Malicious replication requests Forged PAC (MS 14 -068) Golden ticket Remote execution Unusual protocol implementation Malicious DPAPI Request 48
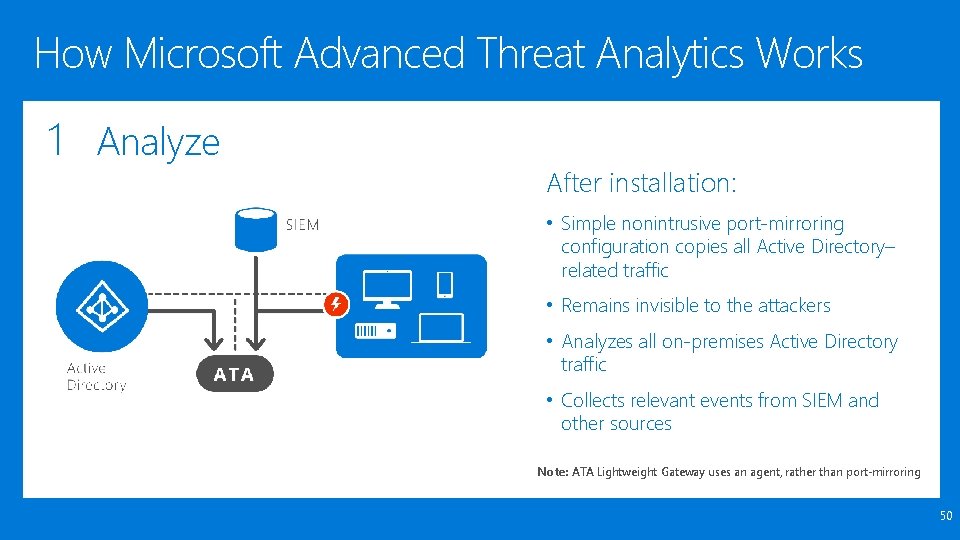
How Microsoft Advanced Threat Analytics Works 1 Analyze After installation: • Simple nonintrusive port-mirroring configuration copies all Active Directory– related traffic • Remains invisible to the attackers • Analyzes all on-premises Active Directory traffic • Collects relevant events from SIEM and other sources Note: ATA Lightweight Gateway uses an agent, rather than port-mirroring 50
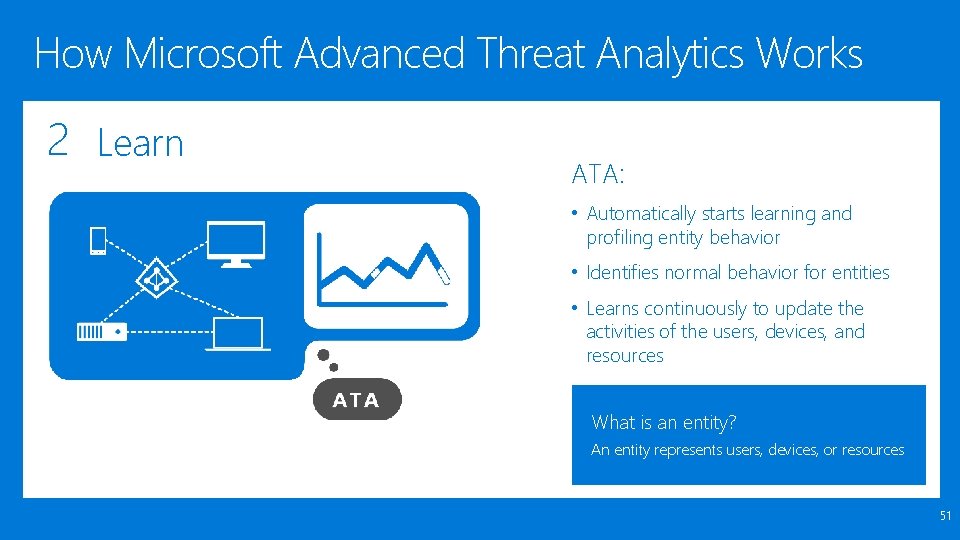
How Microsoft Advanced Threat Analytics Works 2 Learn ATA: • Automatically starts learning and profiling entity behavior • Identifies normal behavior for entities • Learns continuously to update the activities of the users, devices, and resources What is an entity? An entity represents users, devices, or resources 51
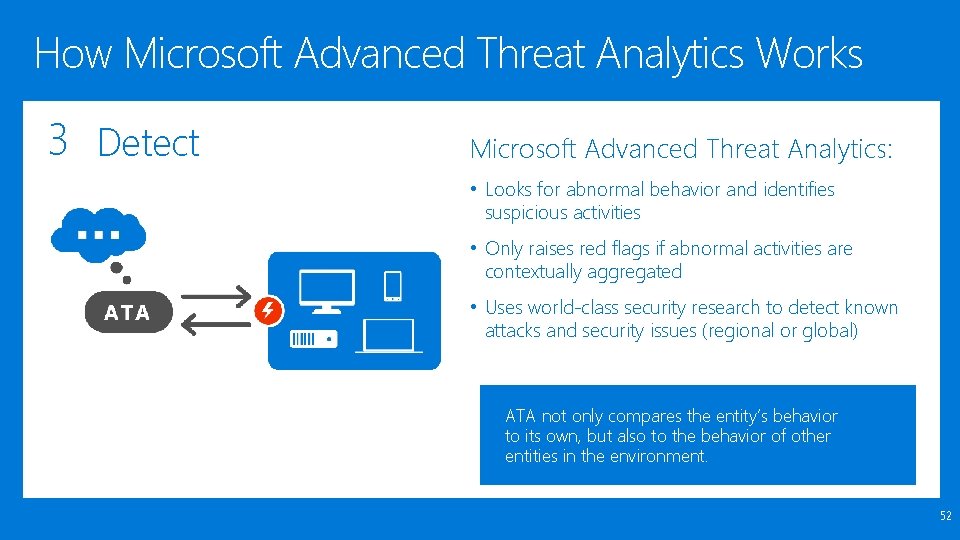
How Microsoft Advanced Threat Analytics Works 3 Detect Microsoft Advanced Threat Analytics: • Looks for abnormal behavior and identifies suspicious activities • Only raises red flags if abnormal activities are contextually aggregated • Uses world-class security research to detect known attacks and security issues (regional or global) ATA not only compares the entity’s behavior to its own, but also to the behavior of other entities in the environment. 52
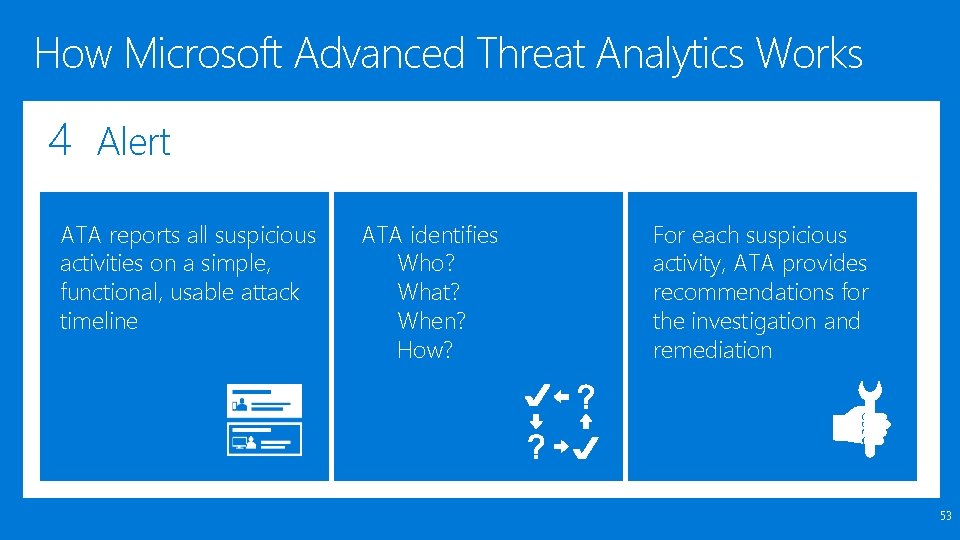
How Microsoft Advanced Threat Analytics Works 4 Alert ATA reports all suspicious activities on a simple, functional, usable attack timeline ATA identifies Who? What? When? How? For each suspicious activity, ATA provides recommendations for the investigation and remediation 53

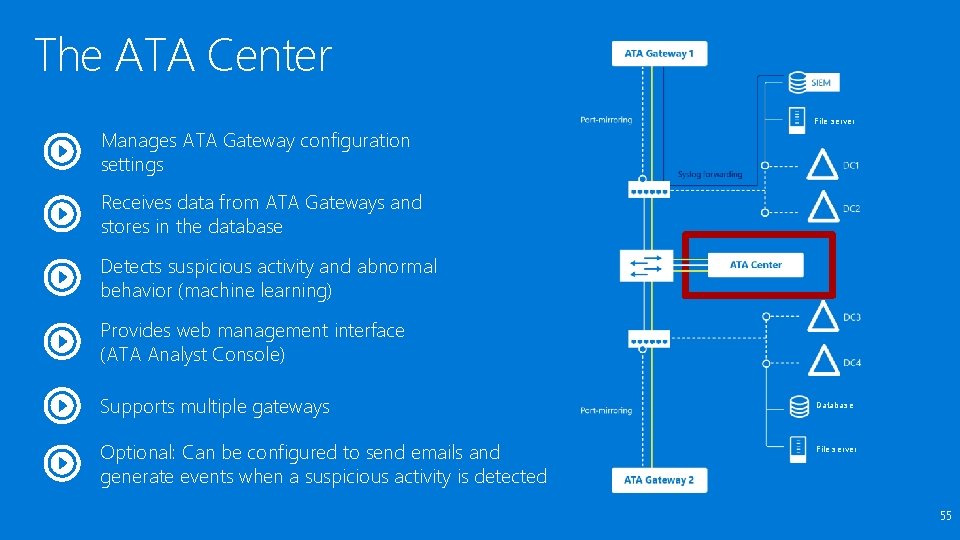
The ATA Center Manages ATA Gateway configuration settings File server Receives data from ATA Gateways and stores in the database Detects suspicious activity and abnormal behavior (machine learning) Provides web management interface (ATA Analyst Console) Supports multiple gateways Optional: Can be configured to send emails and generate events when a suspicious activity is detected Database File server 55
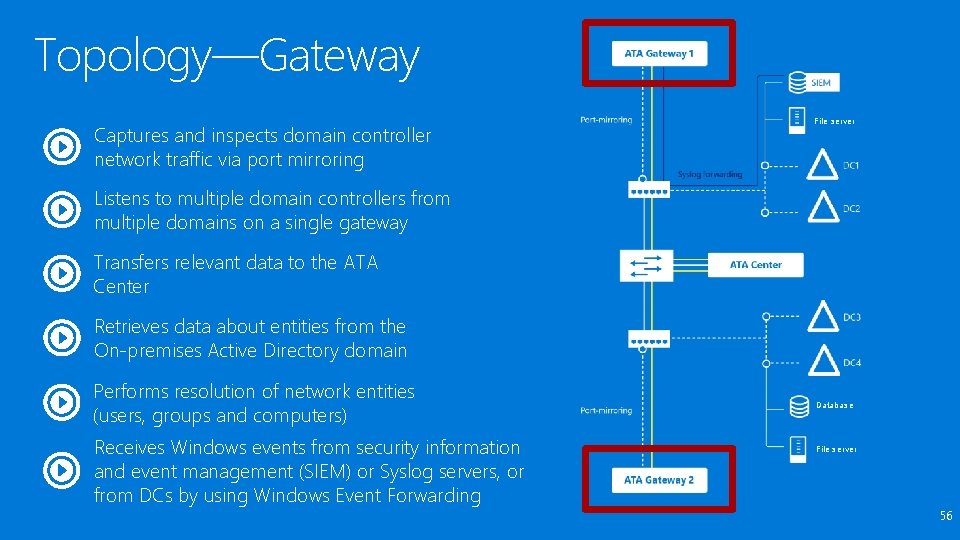
Topology—Gateway Captures and inspects domain controller network traffic via port mirroring File server Listens to multiple domain controllers from multiple domains on a single gateway Transfers relevant data to the ATA Center Retrieves data about entities from the On-premises Active Directory domain Performs resolution of network entities (users, groups and computers) Receives Windows events from security information and event management (SIEM) or Syslog servers, or from DCs by using Windows Event Forwarding Database File server 56
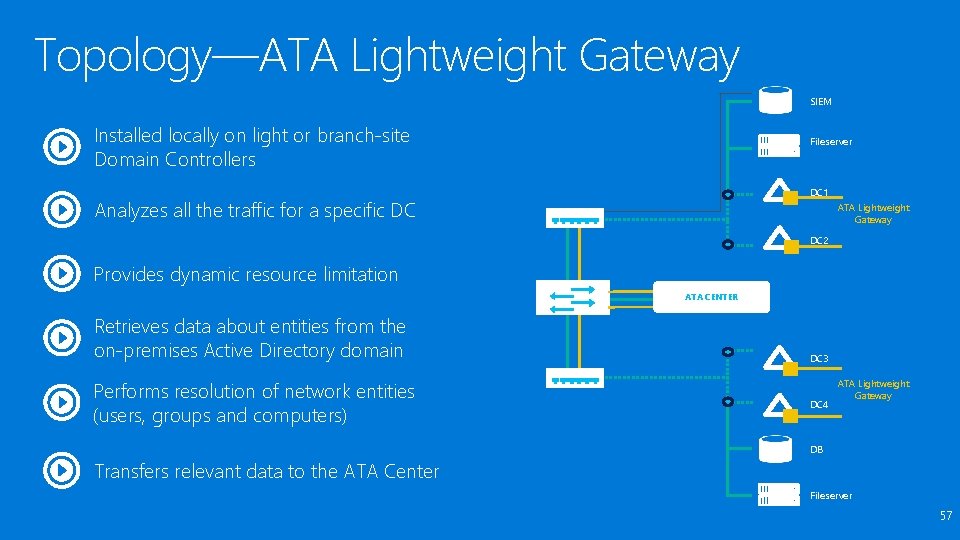
Topology—ATA Lightweight Gateway SIEM Installed locally on light or branch-site Domain Controllers Fileserver DC 1 Analyzes all the traffic for a specific DC ATA Lightweight Gateway DC 2 Provides dynamic resource limitation ATA CENTER Retrieves data about entities from the on-premises Active Directory domain Performs resolution of network entities (users, groups and computers) DC 3 DC 4 ATA Lightweight Gateway DB Transfers relevant data to the ATA Center Fileserver 57

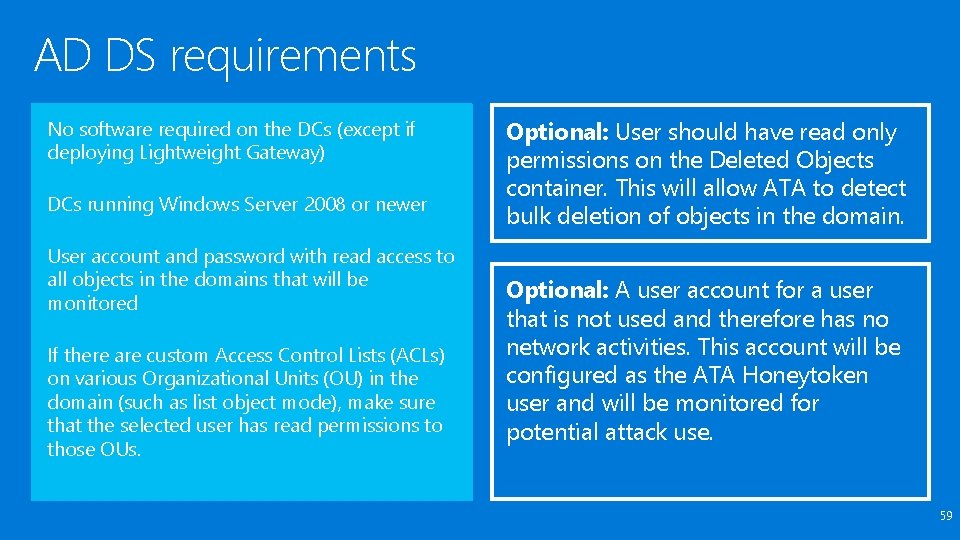
AD DS requirements No software required on the DCs (except if deploying Lightweight Gateway) DCs running Windows Server 2008 or newer User account and password with read access to all objects in the domains that will be monitored If there are custom Access Control Lists (ACLs) on various Organizational Units (OU) in the domain (such as list object mode), make sure that the selected user has read permissions to those OUs. Optional: User should have read only permissions on the Deleted Objects container. This will allow ATA to detect bulk deletion of objects in the domain. Optional: A user account for a user that is not used and therefore has no network activities. This account will be configured as the ATA Honeytoken user and will be monitored for potential attack use. 59
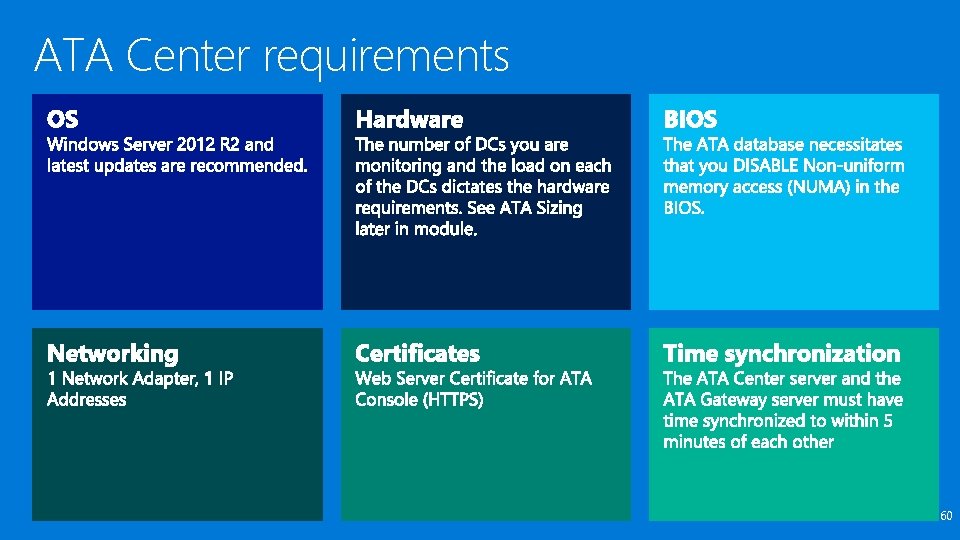
ATA Center requirements 60
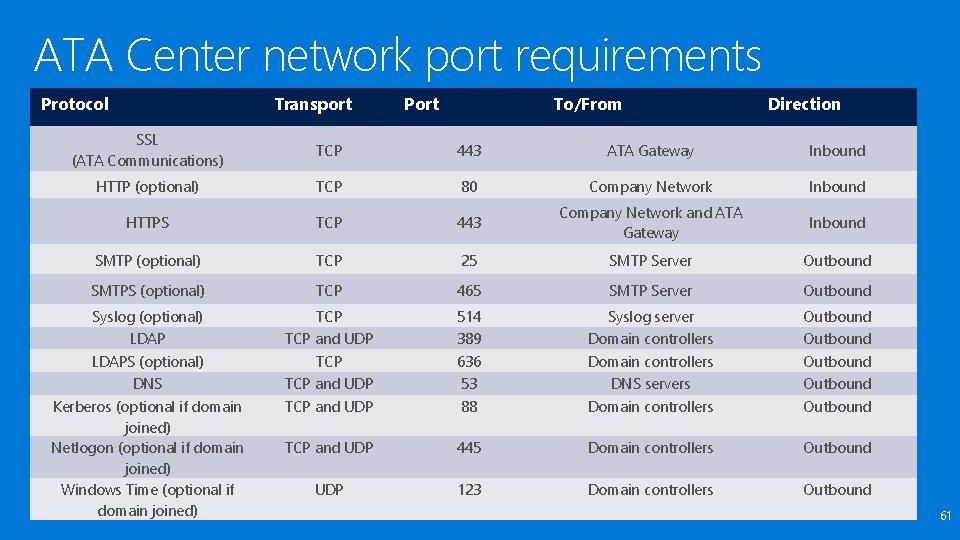
ATA Center network port requirements Protocol Transport Port To/From Direction SSL (ATA Communications) TCP 443 ATA Gateway Inbound HTTP (optional) TCP 80 Company Network Inbound HTTPS TCP 443 Company Network and ATA Gateway Inbound SMTP (optional) TCP 25 SMTP Server Outbound SMTPS (optional) TCP 465 SMTP Server Outbound Syslog (optional) LDAP TCP and UDP 514 389 Syslog server Domain controllers Outbound LDAPS (optional) TCP 636 Domain controllers Outbound DNS TCP and UDP 53 DNS servers Outbound Kerberos (optional if domain joined) Netlogon (optional if domain joined) Windows Time (optional if domain joined) TCP and UDP 88 Domain controllers Outbound TCP and UDP 445 Domain controllers Outbound UDP 123 Domain controllers Outbound 61
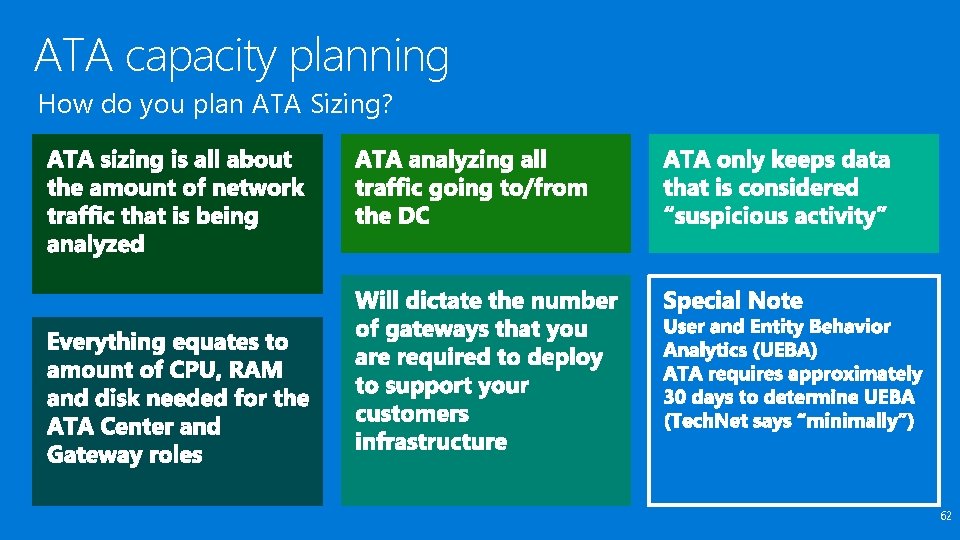
ATA capacity planning How do you plan ATA Sizing? 62
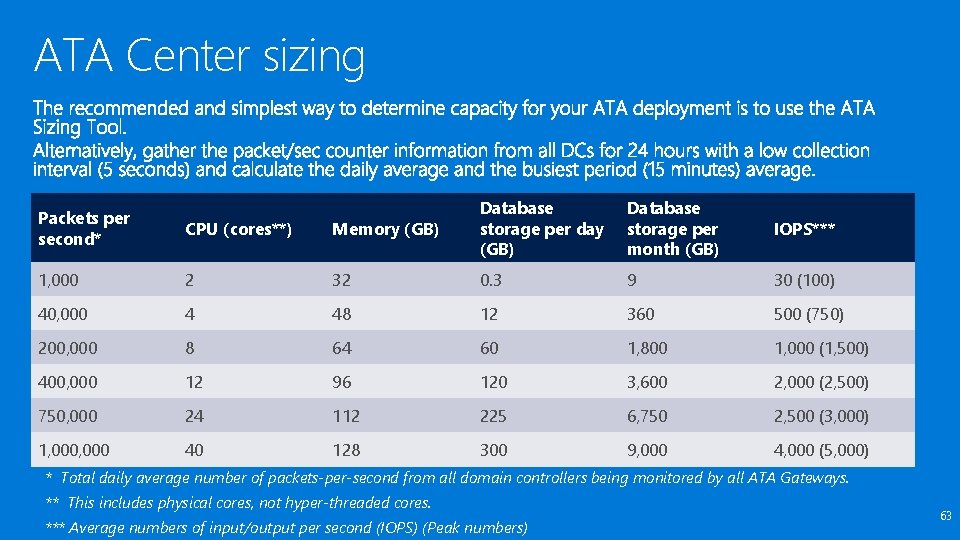
ATA Center sizing Memory (GB) Database storage per day (GB) Database storage per month (GB) IOPS*** 2 32 0. 3 9 30 (100) 40, 000 4 48 12 360 500 (750) 200, 000 8 64 60 1, 800 1, 000 (1, 500) 400, 000 12 96 120 3, 600 2, 000 (2, 500) 750, 000 24 112 225 6, 750 2, 500 (3, 000) 1, 000 40 128 300 9, 000 4, 000 (5, 000) Packets per second* CPU (cores**) 1, 000 * Total daily average number of packets-per-second from all domain controllers being monitored by all ATA Gateways. ** This includes physical cores, not hyper-threaded cores. *** Average numbers of input/output per second (IOPS) (Peak numbers) 63
ATA Center sizing notes 64
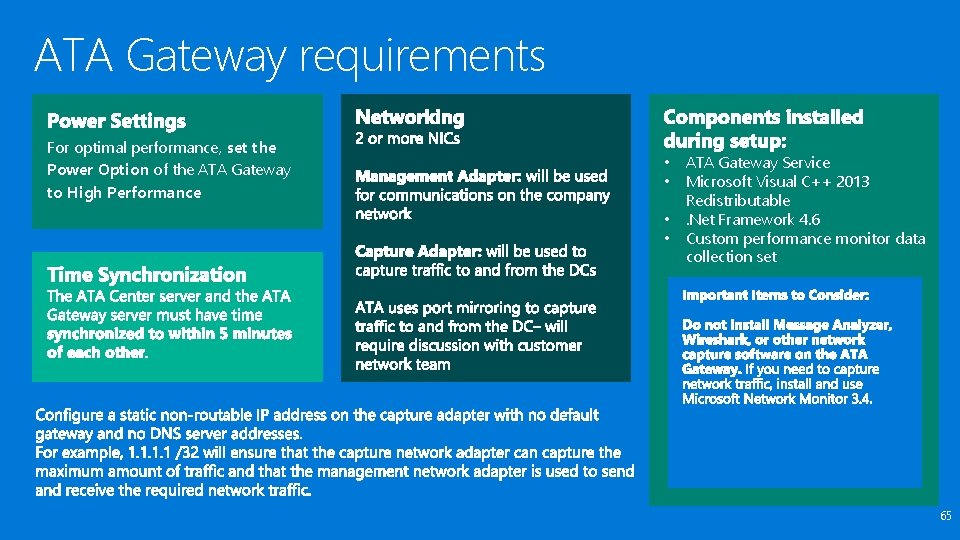
ATA Gateway requirements For optimal performance, set the Power Option of the ATA Gateway to High Performance • • ATA Gateway Service Microsoft Visual C++ 2013 Redistributable. Net Framework 4. 6 Custom performance monitor data collection set 65
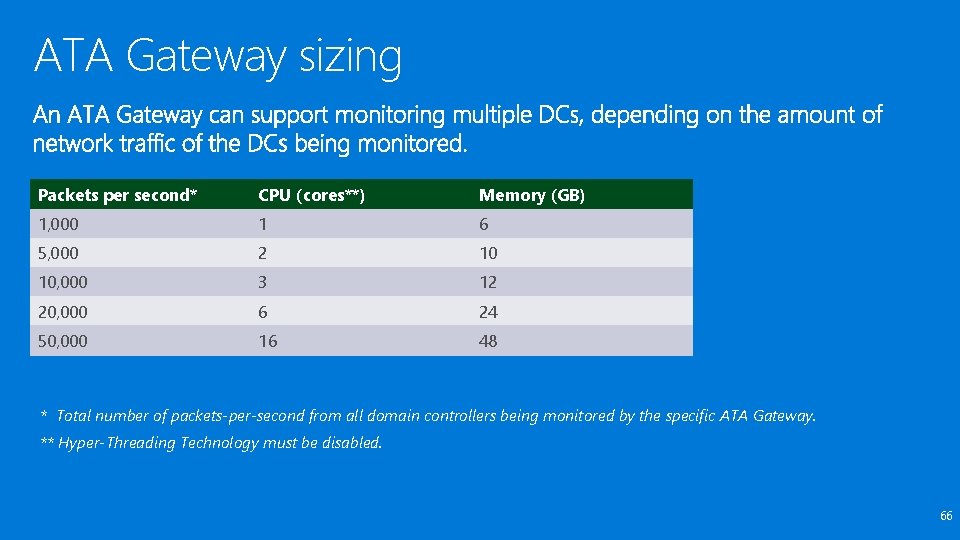
ATA Gateway sizing Packets per second* CPU (cores**) Memory (GB) 1, 000 1 6 5, 000 2 10 10, 000 3 12 20, 000 6 24 50, 000 16 48 * Total number of packets-per-second from all domain controllers being monitored by the specific ATA Gateway. ** Hyper-Threading Technology must be disabled. 66
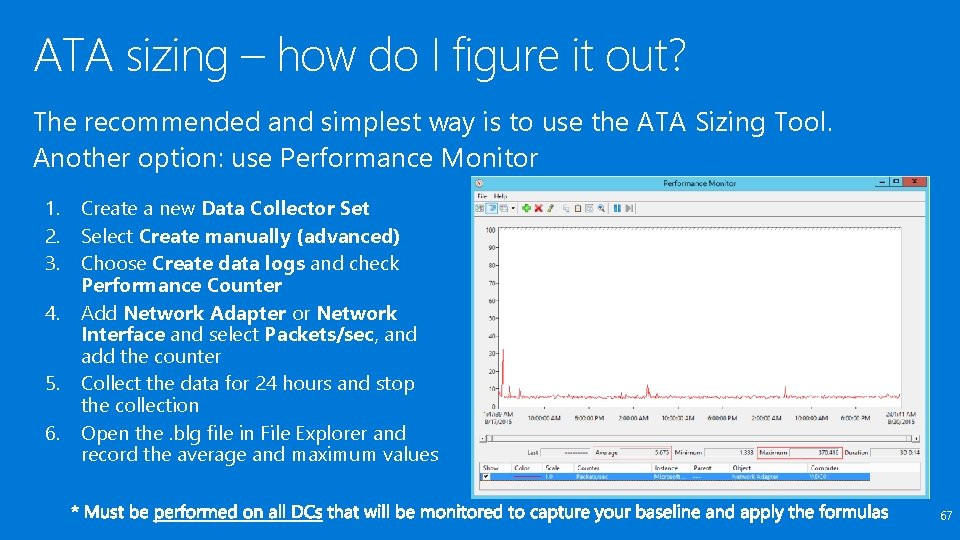
ATA sizing – how do I figure it out? The recommended and simplest way is to use the ATA Sizing Tool. Another option: use Performance Monitor 1. 2. 3. 4. 5. 6. Create a new Data Collector Set Select Create manually (advanced) Choose Create data logs and check Performance Counter Add Network Adapter or Network Interface and select Packets/sec, and add the counter Collect the data for 24 hours and stop the collection Open the. blg file in File Explorer and record the average and maximum values 67
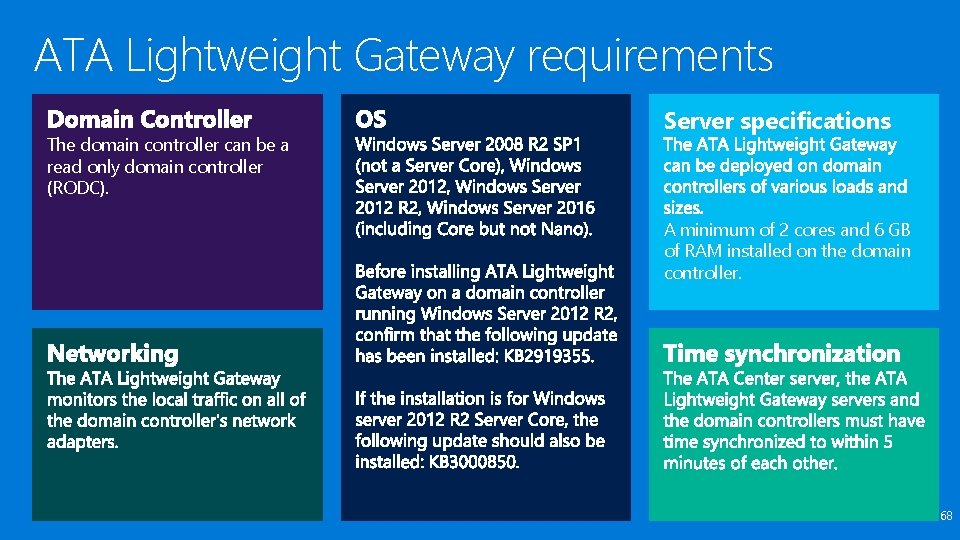
ATA Lightweight Gateway requirements The domain controller can be a read only domain controller (RODC). Server specifications A minimum of 2 cores and 6 GB of RAM installed on the domain controller. 68
ATA Console The ATA Management console is accessed via a browser. The following browsers are supported: • Internet Explorer version 10 and above • Google Chrome 40 and above • Minimum screen width resolution of 1700 pixels 69
Administrative requirements ATA Gateway: Configured via ATA Center and install package downloaded to ATA Gateway server. Requires an AD DS account with readonly access (does not need interactive logon) used to enumerate users and devices for event correlation and behavioral analysis in ATA Center Nothing special added (not even an administrative local group) ATA Center: Creates “Microsoft Advanced Threat Analytics Administrators” local group Consider how it will be managed if in a non-domain joined configuration. 70
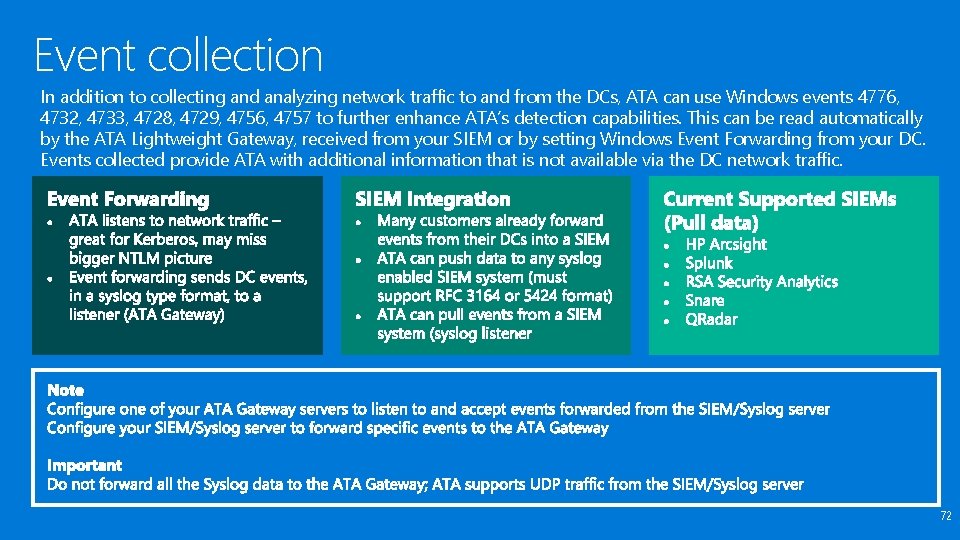
Event collection In addition to collecting and analyzing network traffic to and from the DCs, ATA can use Windows events 4776, 4732, 4733, 4728, 4729, 4756, 4757 to further enhance ATA’s detection capabilities. This can be read automatically by the ATA Lightweight Gateway, received from your SIEM or by setting Windows Event Forwarding from your DC. Events collected provide ATA with additional information that is not available via the DC network traffic. 72
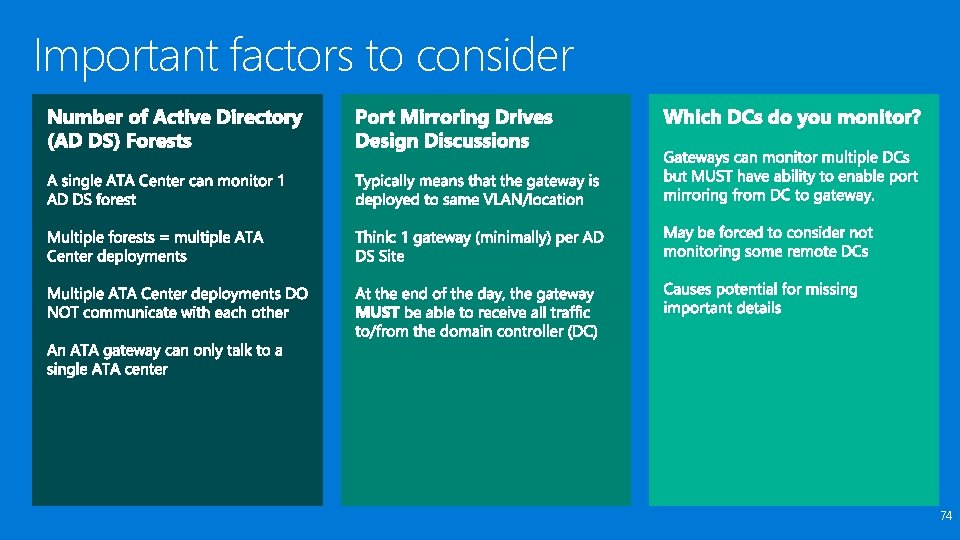
Important factors to consider 74
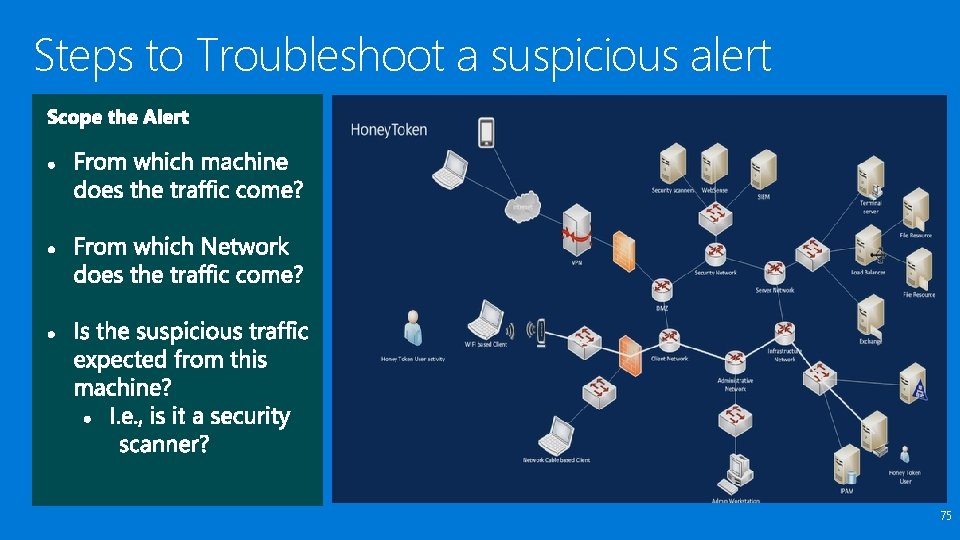
Steps to Troubleshoot a suspicious alert 75
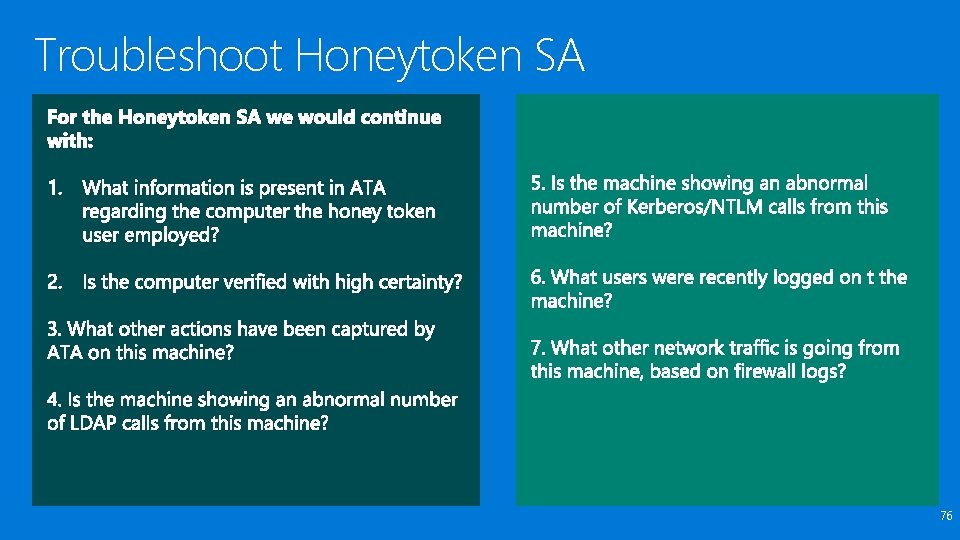
Troubleshoot Honeytoken SA 76
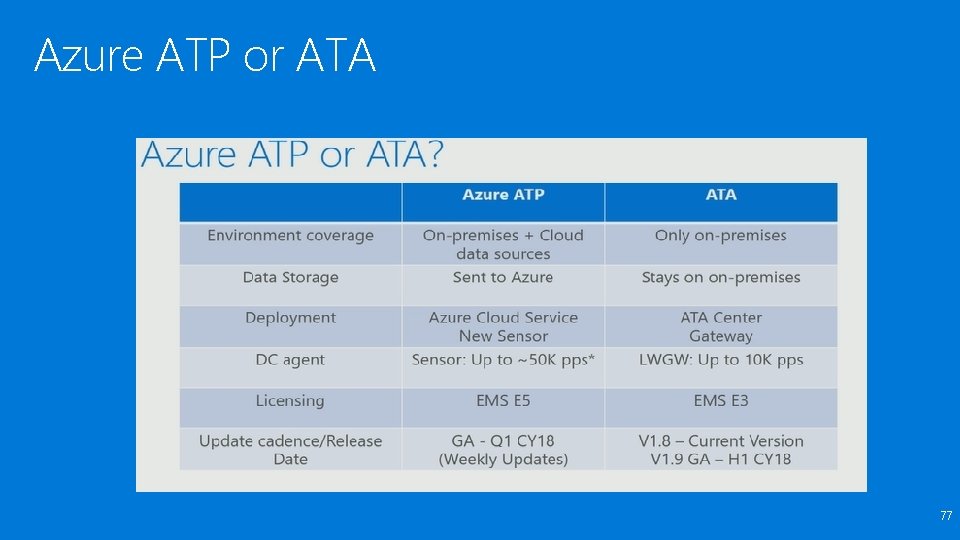
Azure ATP or ATA 77
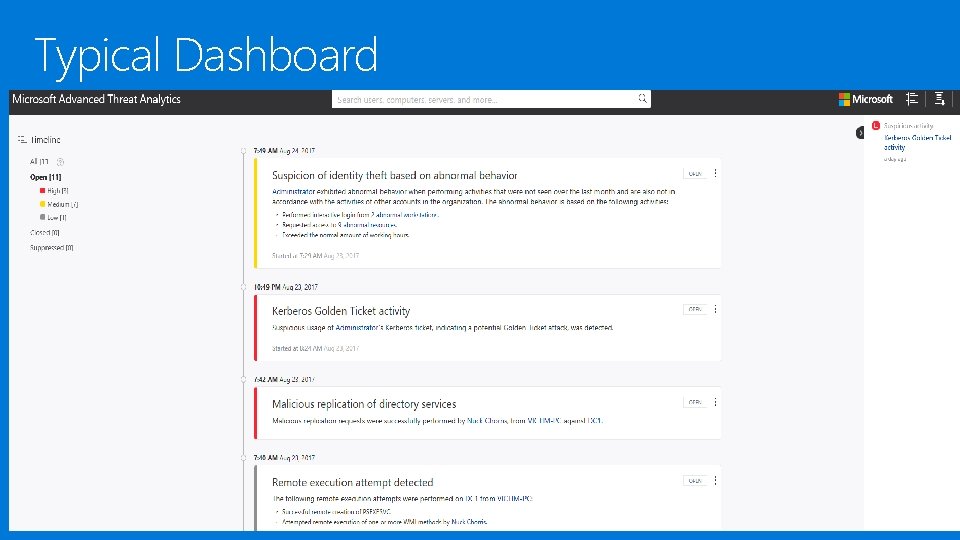
Typical Dashboard 78


Next Microsoft Tech Events Rodney. J@microsoft. com http: //www. meetup. com/mttcharlotte
Microsoft Offerings POP-SLAM (Securing Lateral Account Movement) POP - ATA (Advanced Threat Analytics) Fundamentals OA - Deployment and Migration Assistance for Advanced Threat Analytics (ATA) Active Directory Security Risk Assessment POP - Active Directory Delegation Access Control Visualization and Reporting Assessment
https: //aka. ms/charlottesurvey
- Slides: 74