TCS SAML demo background https www digicert comsso
TCS SAML demo background https: //www. digicert. com/sso David Groep TCS PMA and Nikhef TCS TNC 2015 Workshop June 16, 2015 Networks ∙ Services ∙ People www. geant. org
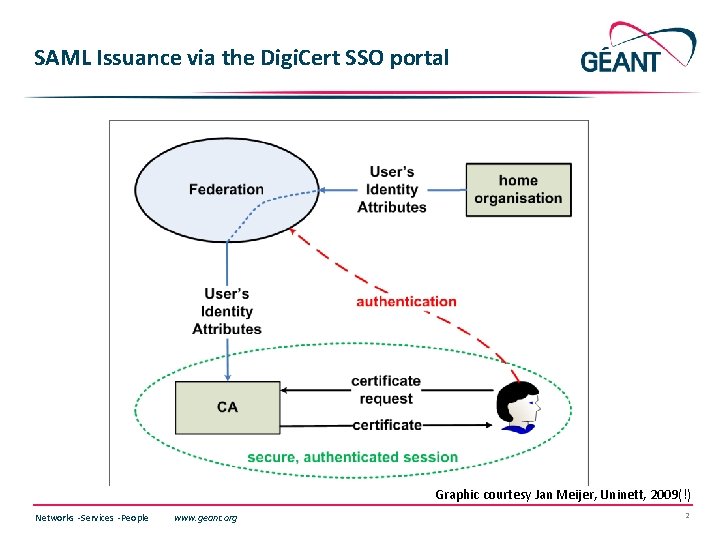
SAML Issuance via the Digi. Cert SSO portal Graphic courtesy Jan Meijer, Uninett, 2009(!) Networks ∙ Services ∙ People www. geant. org 2
SSO SAML portal now natively hosted by Digi. Cert • Scope: client certificates (and client certificates only, sorry!) • We no longer need a intermediary portal such as Djangora • Digi. Cert itself is a SAML 2 Int Service Provider <md: Entity. Descriptor entity. ID="https: //www. digicert. com/sso"> • visible to Federations and Id. Ps via the edu. GAIN meta-data • Digi. Cert will know about all Id. Ps in edu. GAIN (via edu. ID. at) Networks ∙ Services ∙ People www. geant. org 3
Supported products • Client Premium – email signing and authentication • Grid Premium – authentication with guaranteed unique subject name (DN) • Grid Robot Name – authentication for M 2 M communication Intentionally unsupported client products • Email Security Plus – this is a key-escrowing product that is only useful for managed deployment, is potentially dangerous, and the escrow isn’t available anyway … • Digital Signature Plus – this is just a dumbed down version of Premium • Grid Robot Email – the product has additional policy requirements that are unlikely to be satisfied by arbitrary users • Grid Robot FQDN – the product additional requires DCV-like validation that cannot be done at the user level Networks ∙ Services ∙ People www. geant. org 4
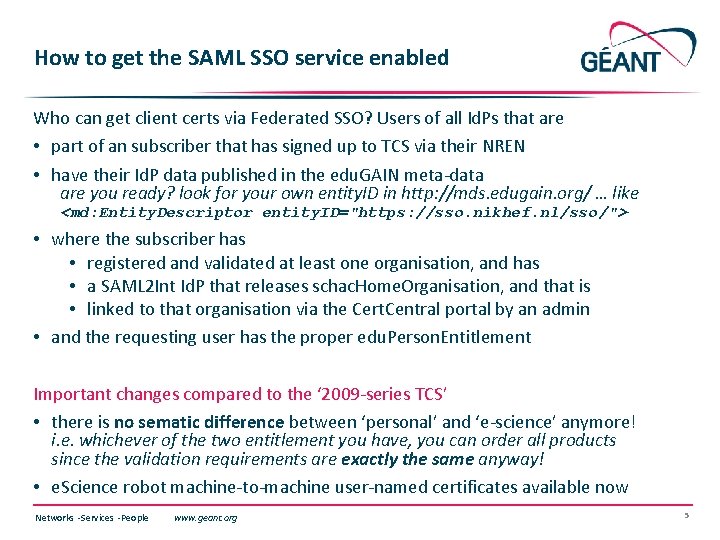
How to get the SAML SSO service enabled Who can get client certs via Federated SSO? Users of all Id. Ps that are • part of an subscriber that has signed up to TCS via their NREN • have their Id. P data published in the edu. GAIN meta-data are you ready? look for your own entity. ID in http: //mds. edugain. org/ … like <md: Entity. Descriptor entity. ID="https: //sso. nikhef. nl/sso/"> • where the subscriber has • registered and validated at least one organisation, and has • a SAML 2 Int Id. P that releases schac. Home. Organisation, and that is • linked to that organisation via the Cert. Central portal by an admin • and the requesting user has the proper edu. Person. Entitlement Important changes compared to the ‘ 2009 -series TCS’ • there is no sematic difference between ‘personal’ and ‘e-science’ anymore! i. e. whichever of the two entitlement you have, you can order all products since the validation requirements are exactly the same anyway! • e. Science robot machine-to-machine user-named certificates available now Networks ∙ Services ∙ People www. geant. org 5
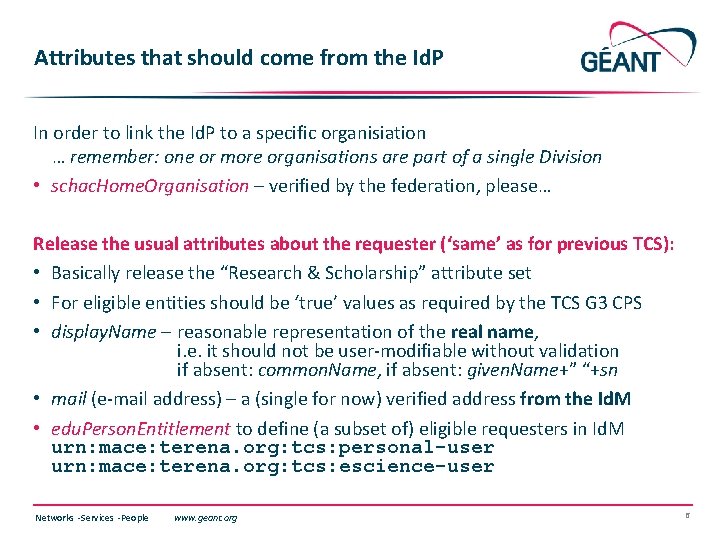
Attributes that should come from the Id. P In order to link the Id. P to a specific organisiation … remember: one or more organisations are part of a single Division • schac. Home. Organisation – verified by the federation, please… Release the usual attributes about the requester (‘same’ as for previous TCS): • Basically release the “Research & Scholarship” attribute set • For eligible entities should be ‘true’ values as required by the TCS G 3 CPS • display. Name – reasonable representation of the real name, i. e. it should not be user-modifiable without validation if absent: common. Name, if absent: given. Name+” “+sn • mail (e-mail address) – a (single for now) verified address from the Id. M • edu. Person. Entitlement to define (a subset of) eligible requesters in Id. M urn: mace: terena. org: tcs: personal-user urn: mace: terena. org: tcs: escience-user Networks ∙ Services ∙ People www. geant. org 6
Now for the real demo • http: //www. digicert. com/sso (for requesters) • https: //www. digicert. com/secure/saml/org-map/ (for Org-Division admins) In due time (by July 1 st) • https: //tcs-escience-portal. terena. org/ • https: //tcs-personal-portal. terena. org/ will start to contain text that informs users about the new service location • the actual URLs will remain (since external things link to it) • If you have your own custom URLs, these should be pointed to a server that hosts a similar page (or does a HTTP redirect to the above URL) Networks ∙ Services ∙ People www. geant. org 7
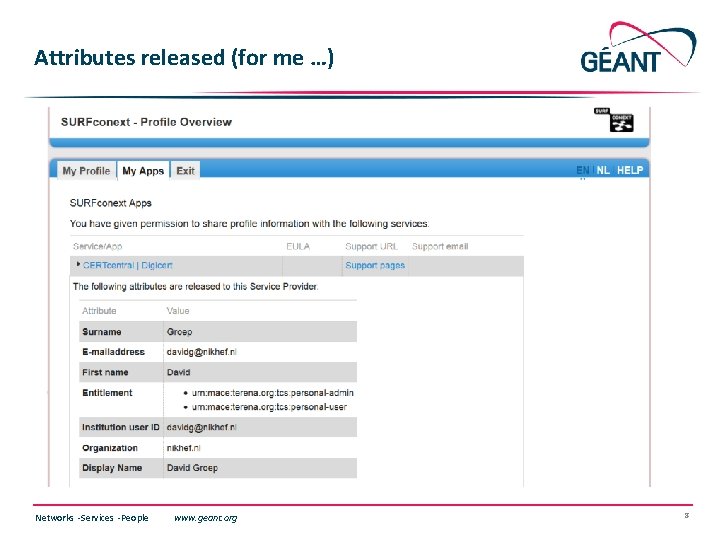
Attributes released (for me …) Networks ∙ Services ∙ People www. geant. org 8
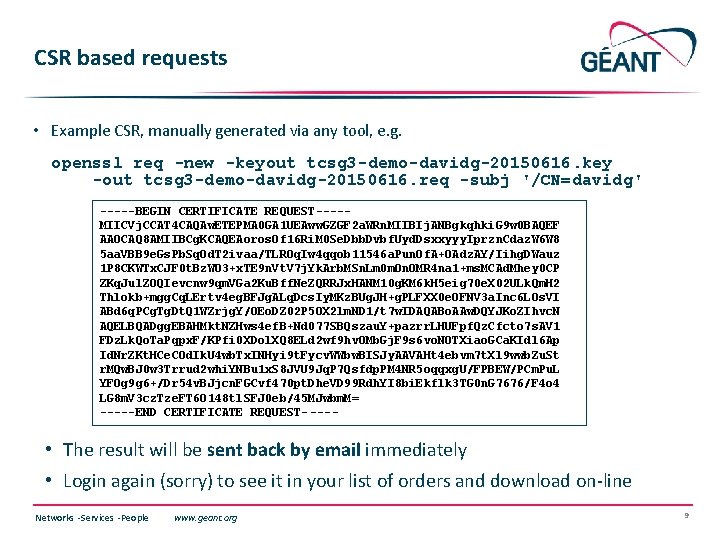
CSR based requests • Example CSR, manually generated via any tool, e. g. openssl req -new -keyout tcsg 3 -demo-davidg-20150616. key -out tcsg 3 -demo-davidg-20150616. req -subj '/CN=davidg' -----BEGIN CERTIFICATE REQUEST----MIICVj. CCAT 4 CAQAw. ETEPMA 0 GA 1 UEAww. GZGF 2 a. WRn. MIIBIj. ANBgkqhki. G 9 w 0 BAQEF AAOCAQ 8 AMIIBCg. KCAQEAoros. Of 16 Ri. M 0 Se. Dbb. Dvbf. Uyd. Dsxxyyy. Iprzn. Cdaz. W 6 W 8 5 aa. VBB 9 e. Gs. Pb. Sq. Od. T 2 ivaa/TLROq. Iw 4 qqob 11546 a. Pun. Of. A+OAdz. AY/Iihg. DWauz 1 P 8 CKWTx. CJF 0 t. Bz. WO 3+x. TE 9 n. Vt. V 7 j. Yk. Arb. MSn. Lm 0 m. On. OMR 4 na 1+ms. MCAd. Mhey 0 CP ZKq. Jul. ZOQIevcnw 9 qm. VGa 2 Ku. Bff. Ne. ZQRRJx. HANM 10 g. KM 6 k. H 5 eig 70 e. X 02 ULk. Qm. H 2 Thlokb+mgg. Cq. LErtv 4 eg. BFJg. ALq. Dcs. Iy. MKz. BUg. JH+g. PLFXX 0 e. OFNV 3 a. Inc 6 LOs. VI ABd 6 q. PCg. Tg. Dt. Q 1 WZrjg. Y/OEo. DZ 02 P 5 OX 2 lm. ND 1/t 7 w. IDAQABo. AAw. DQYJKo. ZIhvc. N AQELBQADgg. EBAHMkt. NZHws 4 ef. B+Nd 077 SBQszau. Y+pazrr. LHUFpf. Qz. Cfcto 7 s. AV 1 FDz. Lk. Qo. Ta. Pqpx. F/KPfi 0 XDol. XQ 8 ELd 2 wf 9 hv. OMb. Gj. F 9 s 6 vo. NOTXiao. GCa. KIdl 6 Ap Id. Nr. ZKt. HCe. COd. Ik. U 4 wb. Tx. INHyi 9 t. Fycv. WWbw. BISJy. AAVAHt 4 ebvm 7 t. Xl 9 wwb. Zu. St r. MQw. BJ 0 w 3 Trrud 2 whi. YNBu 1 x. S 8 JVU 9 Jq. P 7 Qsfdp. PM 4 NR 5 oqqxg. U/FPBEW/PCm. Pu. L YFOg 9 g 6+/Dr 54 v. BJjcn. FGCvf 470 pt. Dhe. VD 99 Rdh. YI 8 bi. Ekflk 3 TG 0 n. G 7676/F 4 o 4 LG 8 m. V 3 cz. Tze. FT 6 O 148 tl. SFJ 0 eb/45 MJwbm. M= -----END CERTIFICATE REQUEST- ---- • The result will be sent back by email immediately • Login again (sorry) to see it in your list of orders and download on-line Networks ∙ Services ∙ People www. geant. org 9
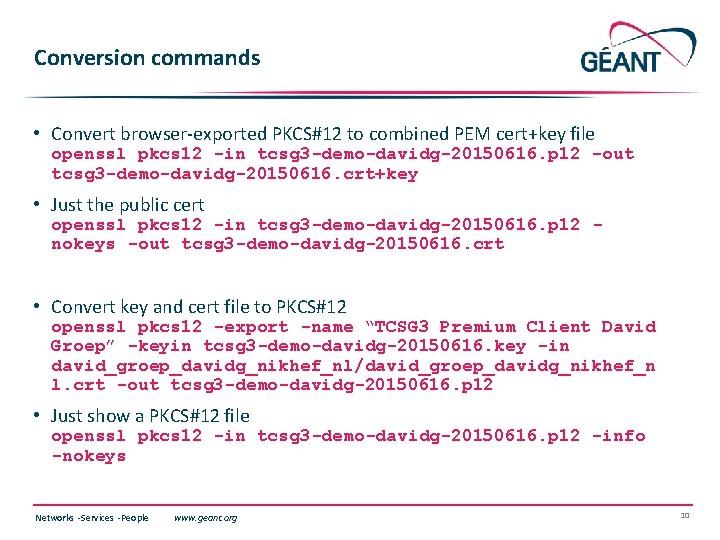
Conversion commands • Convert browser-exported PKCS#12 to combined PEM cert+key file openssl pkcs 12 -in tcsg 3 -demo-davidg-20150616. p 12 -out tcsg 3 -demo-davidg-20150616. crt+key • Just the public cert openssl pkcs 12 -in tcsg 3 -demo-davidg-20150616. p 12 nokeys -out tcsg 3 -demo-davidg-20150616. crt • Convert key and cert file to PKCS#12 openssl pkcs 12 -export -name “TCSG 3 Premium Client David Groep” -keyin tcsg 3 -demo-davidg-20150616. key -in david_groep_davidg_nikhef_nl/david_groep_davidg_nikhef_n l. crt -out tcsg 3 -demo-davidg-20150616. p 12 • Just show a PKCS#12 file openssl pkcs 12 -in tcsg 3 -demo-davidg-20150616. p 12 -info -nokeys Networks ∙ Services ∙ People www. geant. org 10
Thank you https: //www. digicert. com/sso davidg@nikhef. nl Networks ∙ Services ∙ People www. geant. org 11
- Slides: 11