TCPIP TCPIP architecture IP Internet Protocol and ICMP
- Slides: 31
TCP/IP • TCP/IP architecture • IP (Internet Protocol) and ICMP (Internet Control Message Protocol) • TCP (Transmission Control Protocol)/UDP (Used Datagram Protocol) • Internet Routing • Multicast routing • IPV 6, DHCP (Dynamic Host Configuration Protocol) and mobile IP (if time is allowed) 1
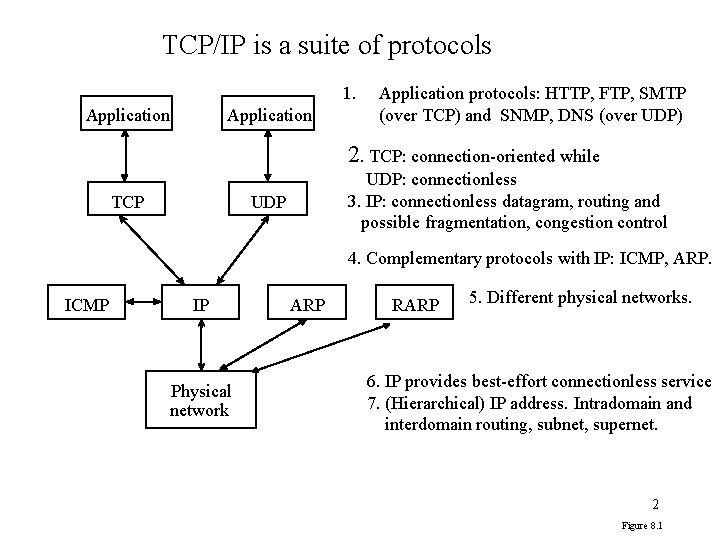
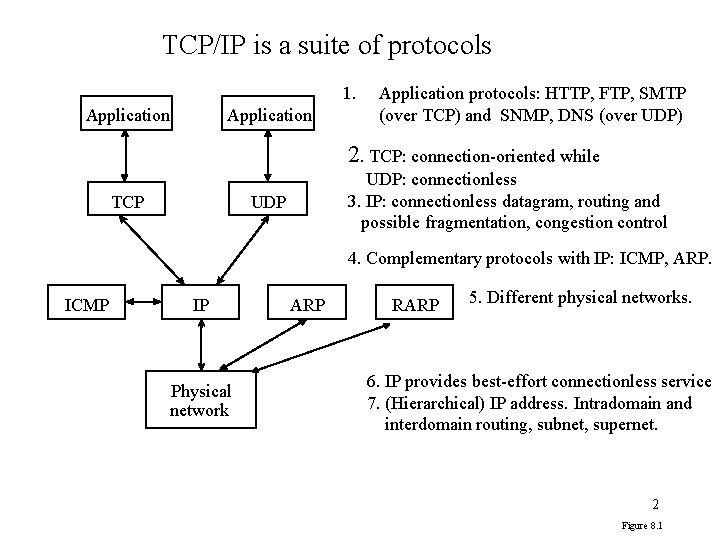
TCP/IP is a suite of protocols 1. Application protocols: HTTP, FTP, SMTP (over TCP) and SNMP, DNS (over UDP) 2. TCP: connection-oriented while TCP UDP: connectionless 3. IP: connectionless datagram, routing and possible fragmentation, congestion control UDP 4. Complementary protocols with IP: ICMP, ARP. ICMP IP Physical network ARP RARP 5. Different physical networks. 6. IP provides best-effort connectionless service 7. (Hierarchical) IP address. Intradomain and interdomain routing, subnet, supernet. 2 Figure 8. 1
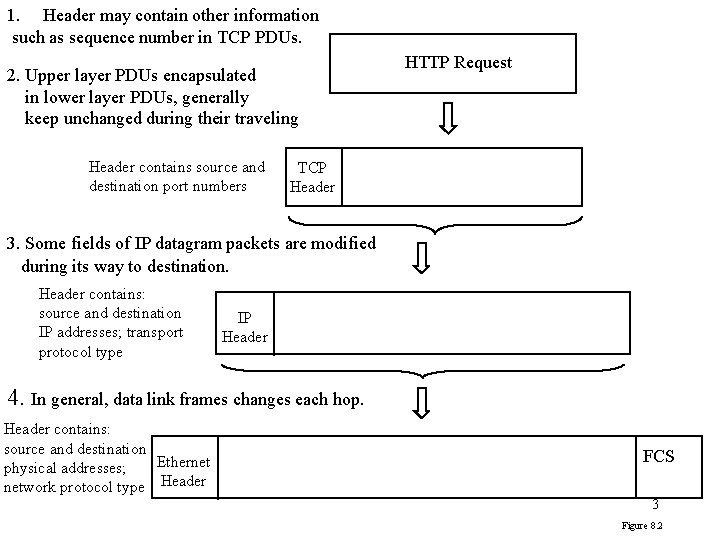
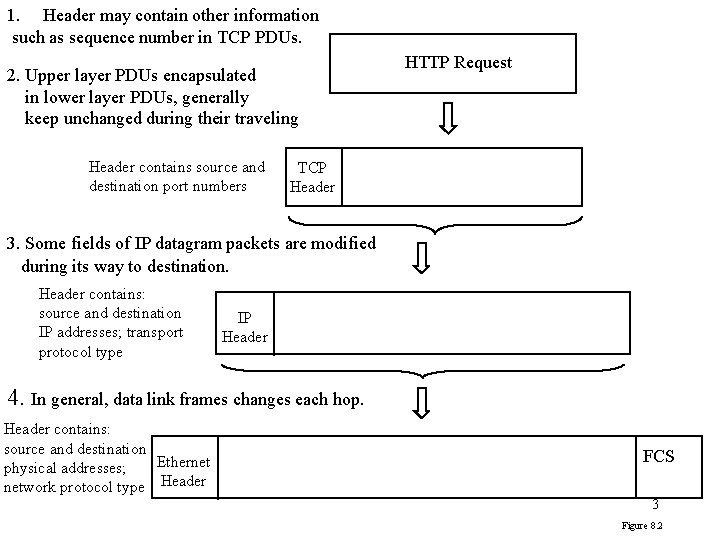
1. Header may contain other information such as sequence number in TCP PDUs. 2. Upper layer PDUs encapsulated in lower layer PDUs, generally keep unchanged during their traveling Header contains source and destination port numbers HTTP Request TCP Header 3. Some fields of IP datagram packets are modified during its way to destination. Header contains: source and destination IP addresses; transport protocol type IP Header 4. In general, data link frames changes each hop. Header contains: source and destination Ethernet physical addresses; network protocol type Header FCS 3 Figure 8. 2
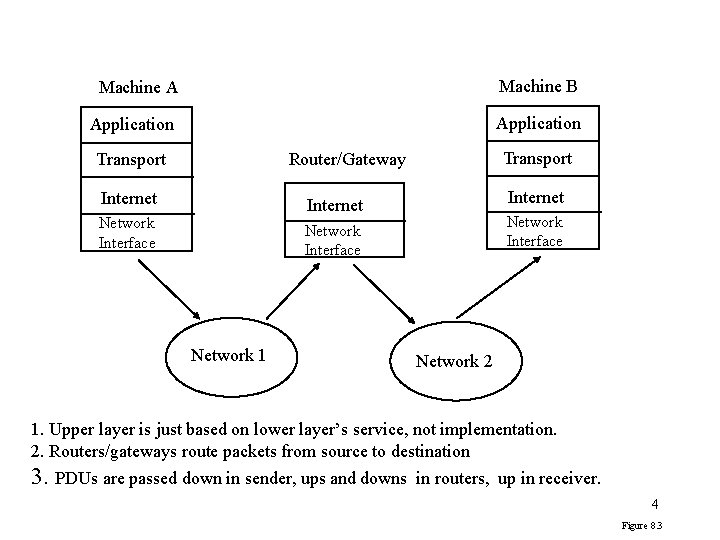
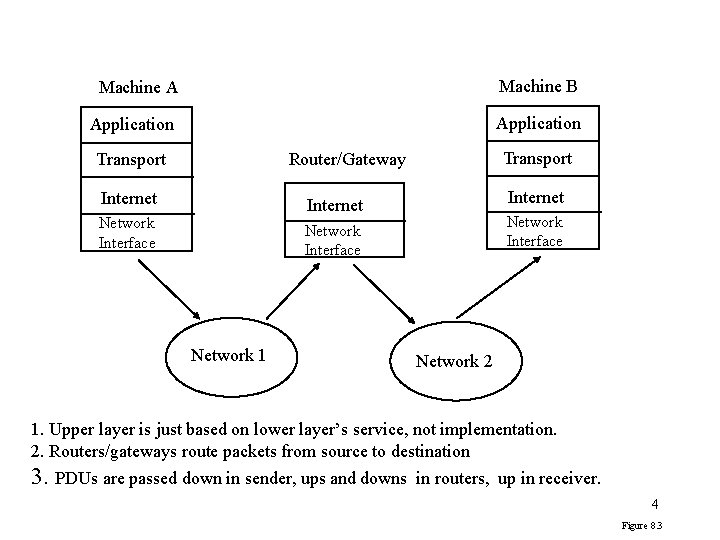
Machine A Machine B Application Transport Router/Gateway Internet Network Interface Network 1 Network 2 1. Upper layer is just based on lower layer’s service, not implementation. 2. Routers/gateways route packets from source to destination 3. PDUs are passed down in sender, ups and downs in routers, up in receiver. 4 Figure 8. 3
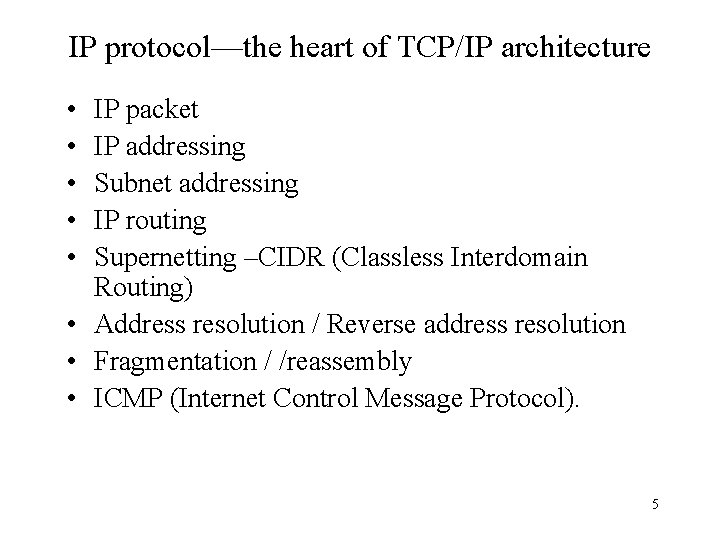
IP protocol—the heart of TCP/IP architecture • • • IP packet IP addressing Subnet addressing IP routing Supernetting –CIDR (Classless Interdomain Routing) • Address resolution / Reverse address resolution • Fragmentation / /reassembly • ICMP (Internet Control Message Protocol). 5
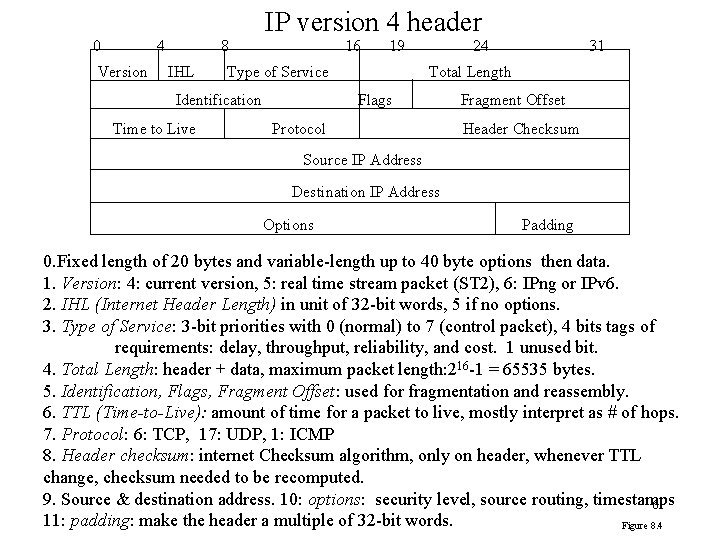
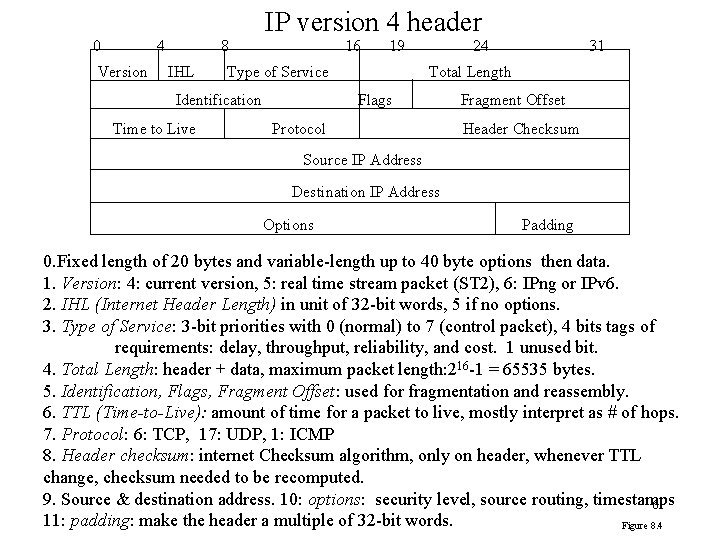
IP version 4 header 0 4 Version 8 IHL 16 Type of Service Identification Time to Live 19 24 31 Total Length Flags Protocol Fragment Offset Header Checksum Source IP Address Destination IP Address Options Padding 0. Fixed length of 20 bytes and variable-length up to 40 byte options then data. 1. Version: 4: current version, 5: real time stream packet (ST 2), 6: IPng or IPv 6. 2. IHL (Internet Header Length) in unit of 32 -bit words, 5 if no options. 3. Type of Service: 3 -bit priorities with 0 (normal) to 7 (control packet), 4 bits tags of requirements: delay, throughput, reliability, and cost. 1 unused bit. 4. Total Length: header + data, maximum packet length: 216 -1 = 65535 bytes. 5. Identification, Flags, Fragment Offset: used for fragmentation and reassembly. 6. TTL (Time-to-Live): amount of time for a packet to live, mostly interpret as # of hops. 7. Protocol: 6: TCP, 17: UDP, 1: ICMP 8. Header checksum: internet Checksum algorithm, only on header, whenever TTL change, checksum needed to be recomputed. 9. Source & destination address. 10: options: security level, source routing, timestamps 6 11: padding: make the header a multiple of 32 -bit words. Figure 8. 4
Router’s work for IP • When network interface passes over IP packet to IP layer – Compute the header checksum which is compared with the checksum in the header. – If valid, IP entity updates TTL and recompute checksum – Look up routing table to find next hop – Forward to the next hop. 7
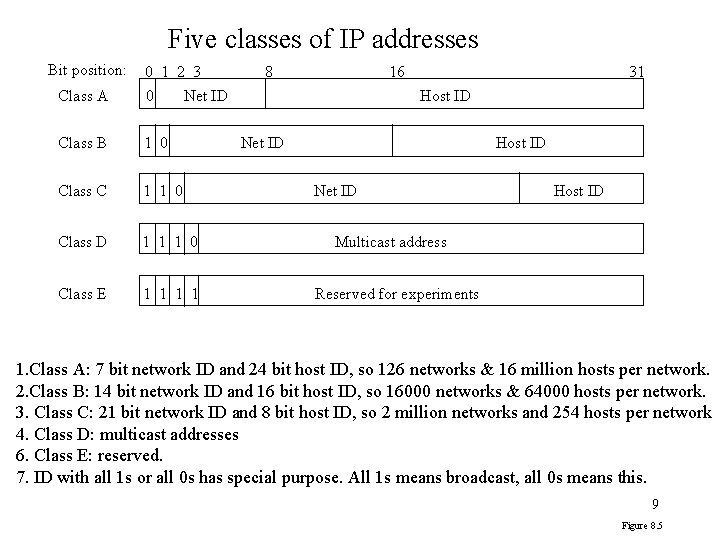
IP addressing • A computer may have multiple IP addresses • 32 bit address with two level hierarchies: – network ID + host ID • Routing could be based on network IDs to reduce the size of routing table • Network Ids are assigned by Internet Network Information Center while host IDs are assigned by local network administrator. • Five classes of networks and different number of bits for network IDs and host IDs. 8
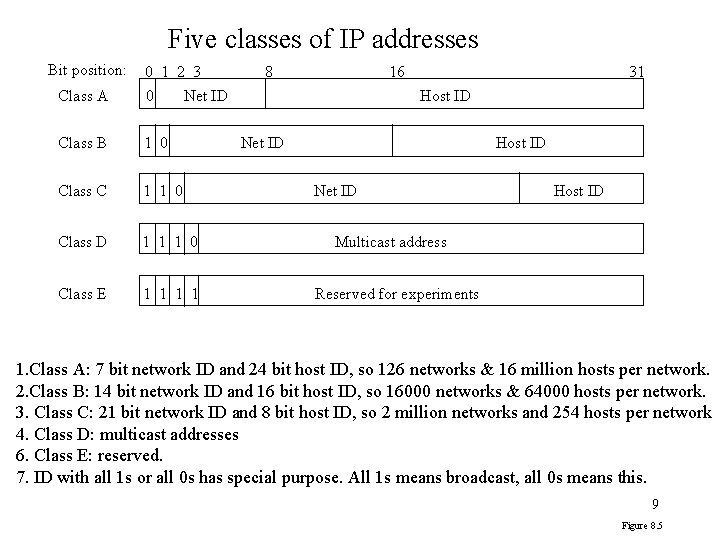
Five classes of IP addresses Bit position: 0 1 2 3 Class A 0 Class B 1 0 Class C 1 1 0 Class D 1 1 1 0 Class E 1 1 8 16 Net ID 31 Host ID Net ID Host ID Multicast address Reserved for experiments 1. Class A: 7 bit network ID and 24 bit host ID, so 126 networks & 16 million hosts per network. 2. Class B: 14 bit network ID and 16 bit host ID, so 16000 networks & 64000 hosts per network. 3. Class C: 21 bit network ID and 8 bit host ID, so 2 million networks and 254 hosts per network 4. Class D: multicast addresses 6. Class E: reserved. 7. ID with all 1 s or all 0 s has special purpose. All 1 s means broadcast, all 0 s means this. 9 Figure 8. 5
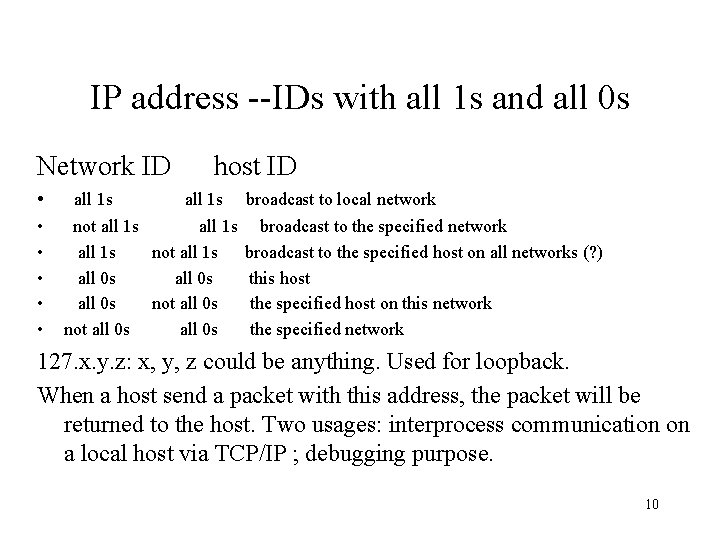
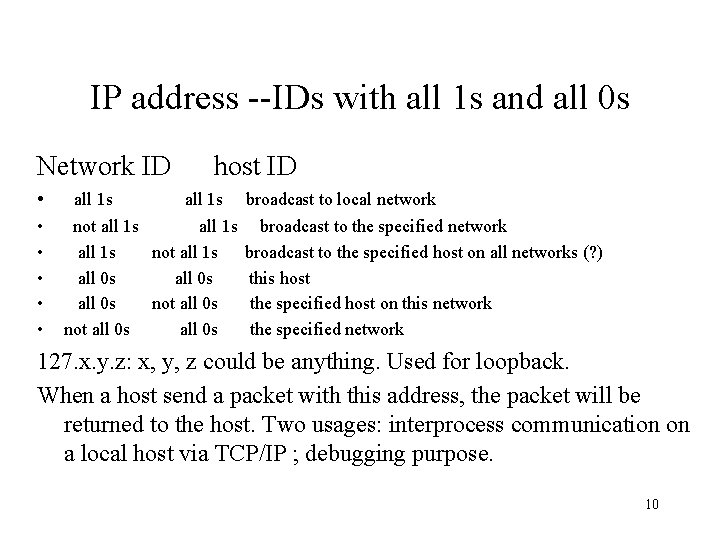
IP address --IDs with all 1 s and all 0 s Network ID • • • host ID all 1 s not all 1 s all 0 s not all 0 s broadcast to local network broadcast to the specified host on all networks (? ) this host the specified host on this network the specified network 127. x. y. z: x, y, z could be anything. Used for loopback. When a host send a packet with this address, the packet will be returned to the host. Two usages: interprocess communication on a local host via TCP/IP ; debugging purpose. 10
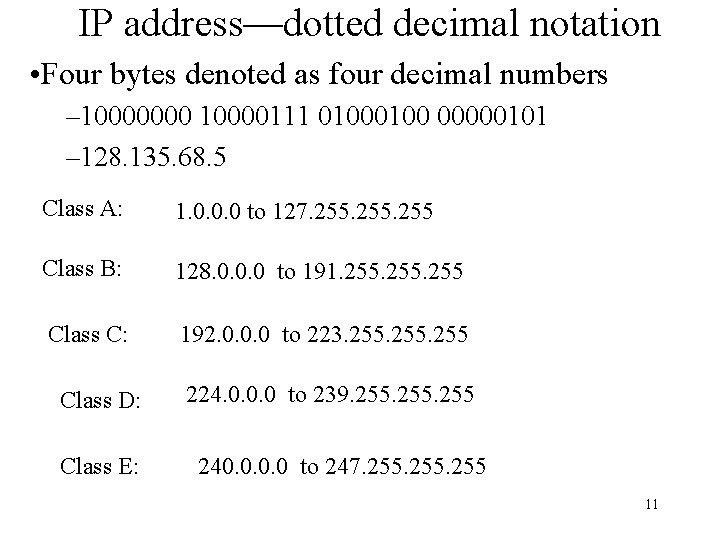
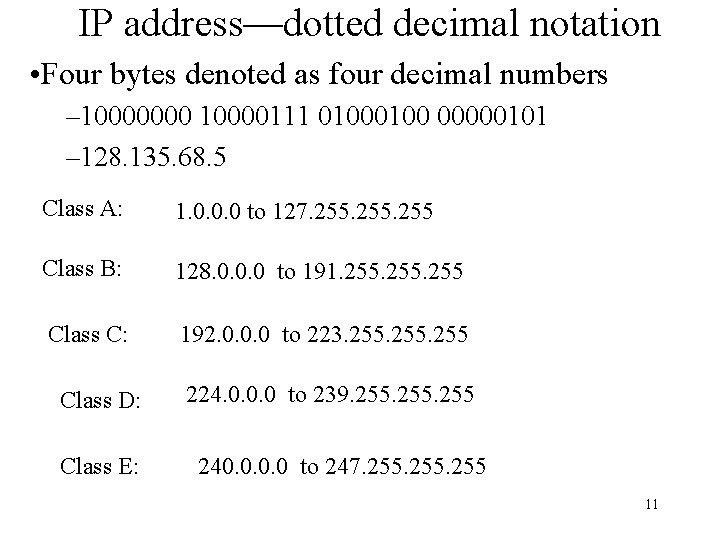
IP address—dotted decimal notation • Four bytes denoted as four decimal numbers – 10000000 10000111 0100 00000101 – 128. 135. 68. 5 Class A: 1. 0. 0. 0 to 127. 255 Class B: 128. 0. 0. 0 to 191. 255 Class C: 192. 0. 0. 0 to 223. 255 Class D: Class E: 224. 0. 0. 0 to 239. 255 240. 0 to 247. 255 11
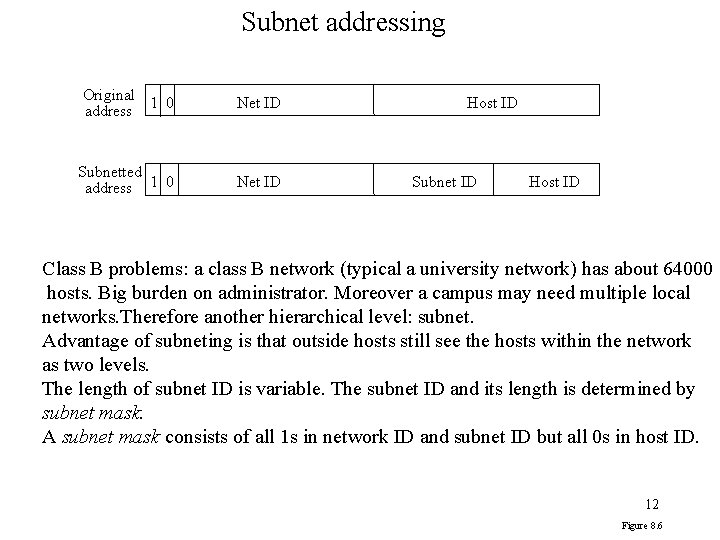
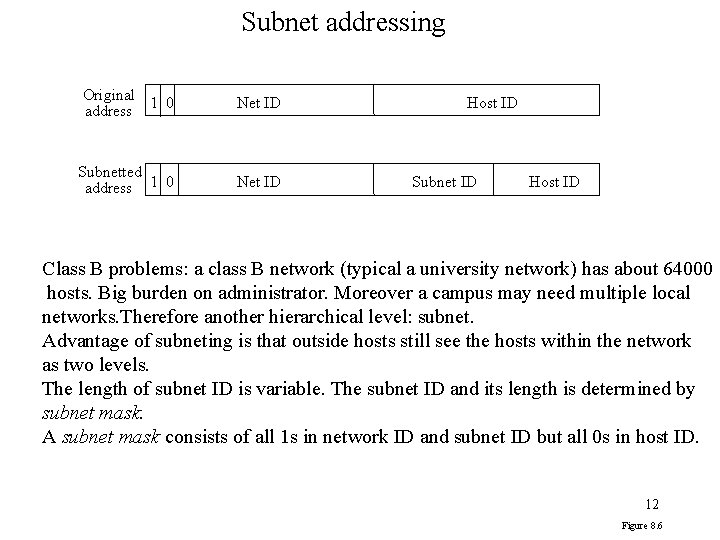
Subnet addressing Original 1 0 address Net ID Subnetted address 1 0 Net ID Host ID Subnet ID Host ID Class B problems: a class B network (typical a university network) has about 64000 hosts. Big burden on administrator. Moreover a campus may need multiple local networks. Therefore another hierarchical level: subnet. Advantage of subneting is that outside hosts still see the hosts within the network as two levels. The length of subnet ID is variable. The subnet ID and its length is determined by subnet mask. A subnet mask consists of all 1 s in network ID and subnet ID but all 0 s in host ID. 12 Figure 8. 6
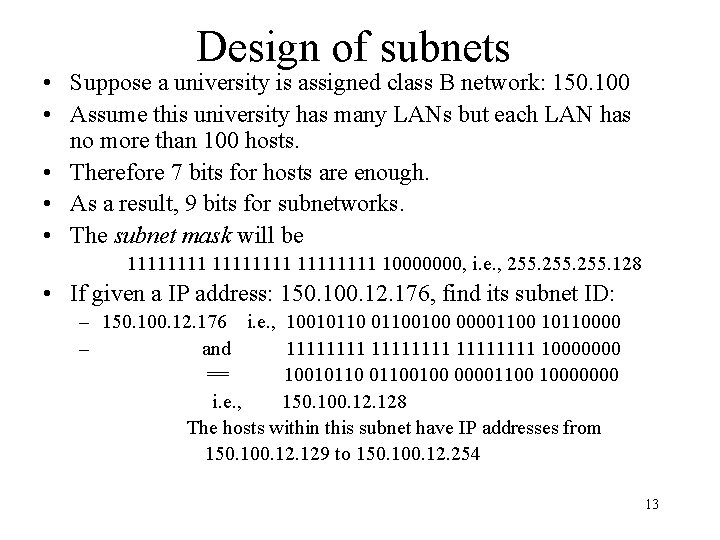
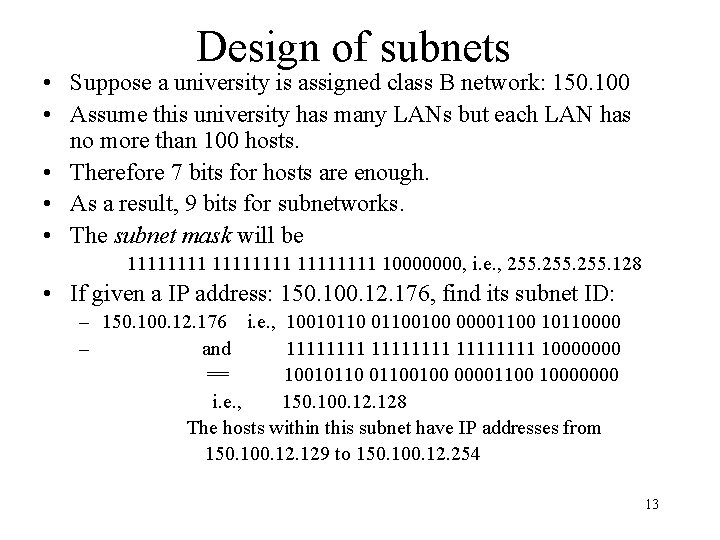
Design of subnets • Suppose a university is assigned class B network: 150. 100 • Assume this university has many LANs but each LAN has no more than 100 hosts. • Therefore 7 bits for hosts are enough. • As a result, 9 bits for subnetworks. • The subnet mask will be 11111111 10000000, i. e. , 255. 128 • If given a IP address: 150. 100. 12. 176, find its subnet ID: – 150. 100. 12. 176 i. e. , 100101100100 00001100 10110000 – and 11111111 10000000 == 100101100100 00001100 10000000 i. e. , 150. 100. 128 The hosts within this subnet have IP addresses from 150. 100. 129 to 150. 100. 12. 254 13
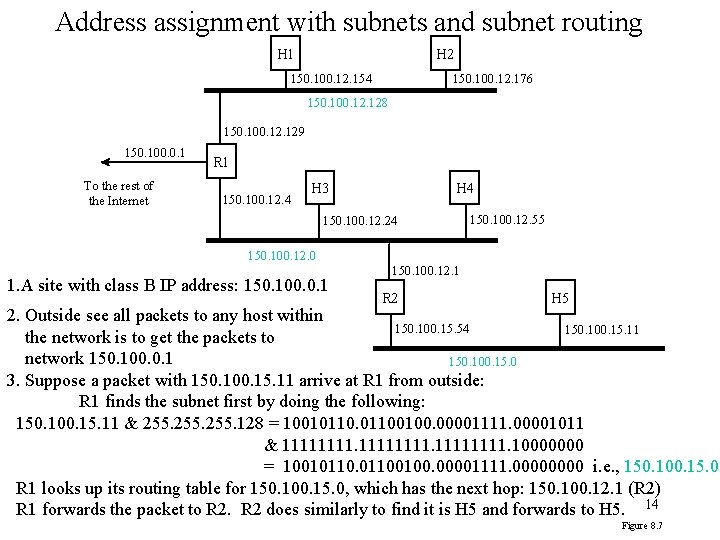
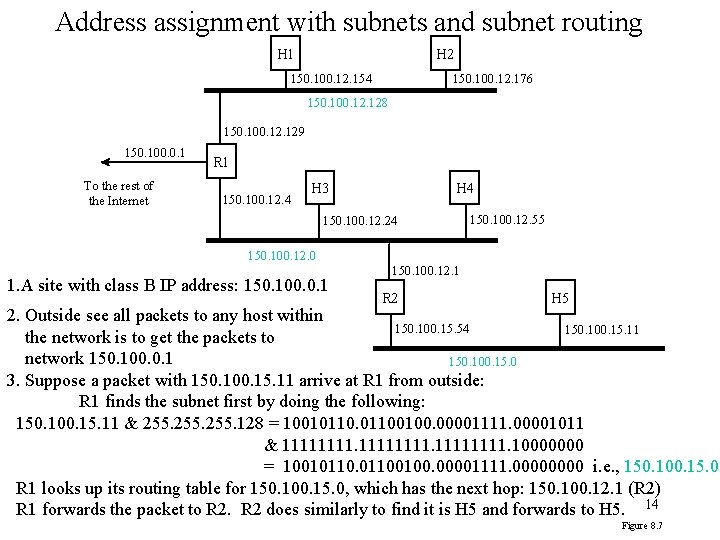
Address assignment with subnets and subnet routing H 1 H 2 150. 100. 12. 154 150. 100. 12. 176 150. 100. 128 150. 100. 129 150. 100. 0. 1 To the rest of the Internet R 1 150. 100. 12. 4 H 3 H 4 150. 100. 12. 24 150. 100. 12. 55 150. 100. 12. 0 1. A site with class B IP address: 150. 100. 0. 1 150. 100. 12. 1 R 2 H 5 2. Outside see all packets to any host within 150. 100. 15. 54 150. 100. 15. 11 the network is to get the packets to network 150. 100. 0. 1 150. 100. 15. 0 3. Suppose a packet with 150. 100. 15. 11 arrive at R 1 from outside: R 1 finds the subnet first by doing the following: 150. 100. 15. 11 & 255. 128 = 100101100100. 00001111. 00001011 & 11111111. 10000000 = 100101100100. 00001111. 0000 i. e. , 150. 100. 15. 0 R 1 looks up its routing table for 150. 100. 15. 0, which has the next hop: 150. 100. 12. 1 (R 2) R 1 forwards the packet to R 2 does similarly to find it is H 5 and forwards to H 5. 14 Figure 8. 7
IP routing • IP entities in sender and routers work together to route a packet from source to destination. – Sender’s IP entity first looks up its routing table. If the destination is directly connected to it by a link or a LAN, the sender sends the packet to the destination directly – Otherwise, the sender will send the packet to default router, which is directly connected to the sender. – The router first check whether a packet is for itself. If yes, pass up to its upper layer. Otherwise look up its routing table to find the next hop and forward to the next hop. • The routing table: – Destination IP, next hop ID, outgoing interface, flags – Flags: H flag, H=1 to a host, H=0: to a network G flag: G=1 to gateway, G=0: to destination 15
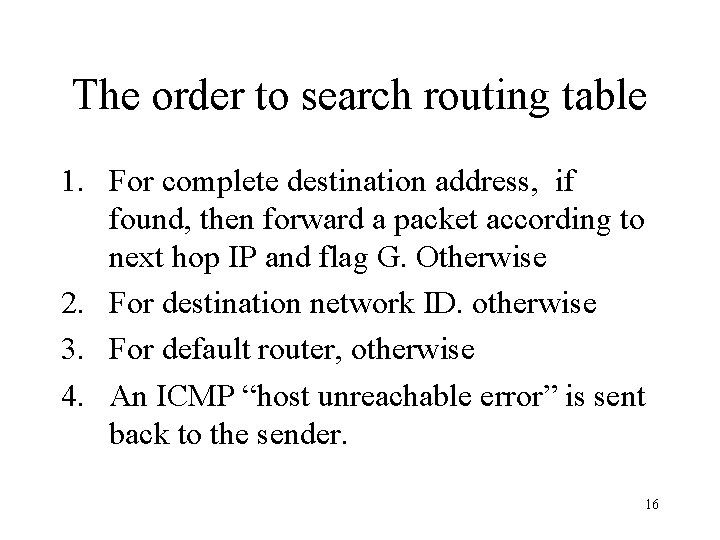
The order to search routing table 1. For complete destination address, if found, then forward a packet according to next hop IP and flag G. Otherwise 2. For destination network ID. otherwise 3. For default router, otherwise 4. An ICMP “host unreachable error” is sent back to the sender. 16
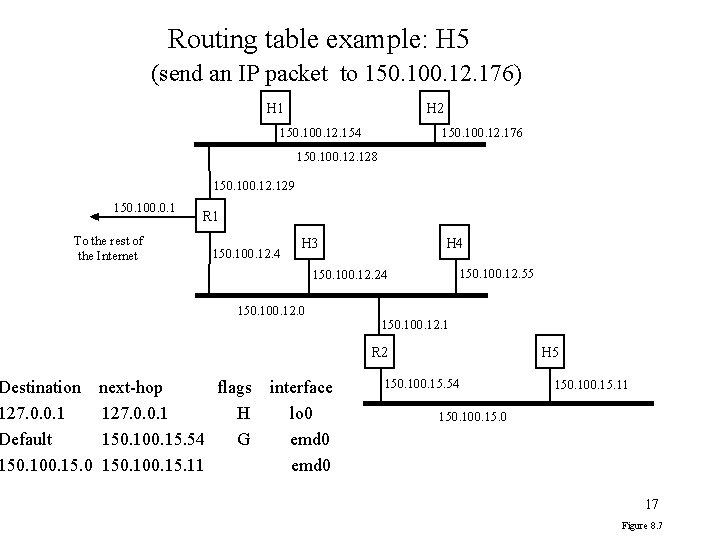
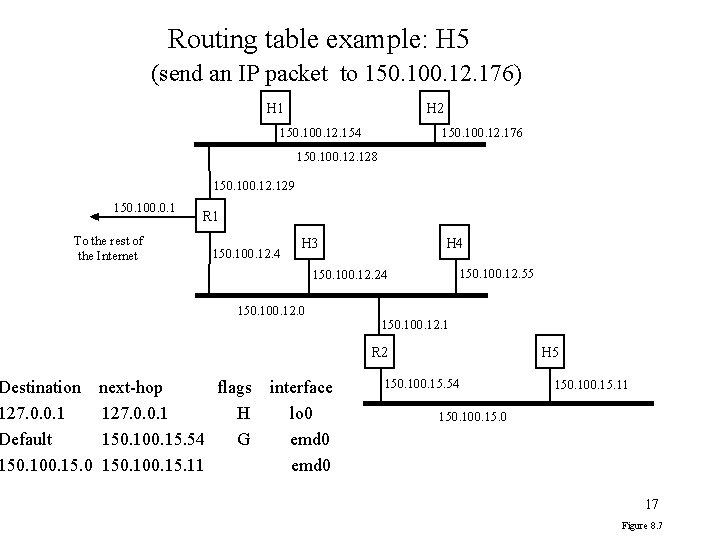
Routing table example: H 5 (send an IP packet to 150. 100. 12. 176) H 1 H 2 150. 100. 12. 154 150. 100. 12. 176 150. 100. 128 150. 100. 129 150. 100. 0. 1 To the rest of the Internet Destination 127. 0. 0. 1 Default 150. 100. 15. 0 R 1 150. 100. 12. 4 H 3 H 4 150. 100. 12. 55 150. 100. 12. 24 150. 100. 12. 0 150. 100. 12. 1 R 2 next-hop flags 127. 0. 0. 1 H 150. 100. 15. 54 G 150. 100. 15. 11 interface lo 0 emd 0 H 5 150. 100. 15. 54 150. 100. 15. 11 150. 100. 15. 0 17 Figure 8. 7
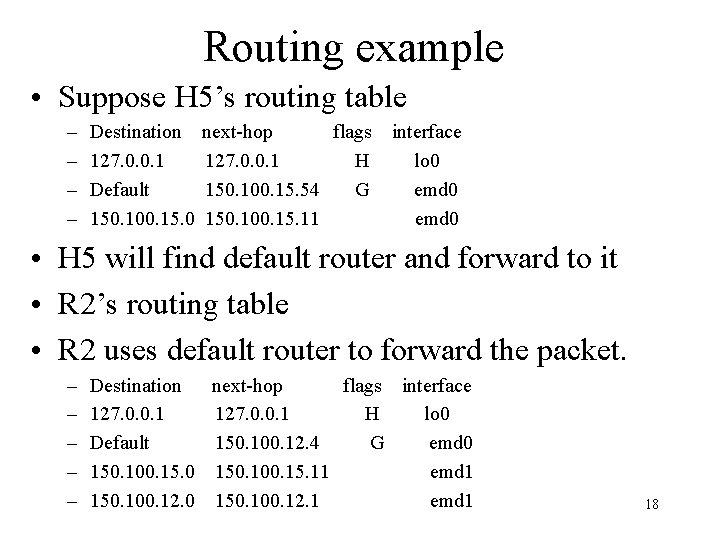
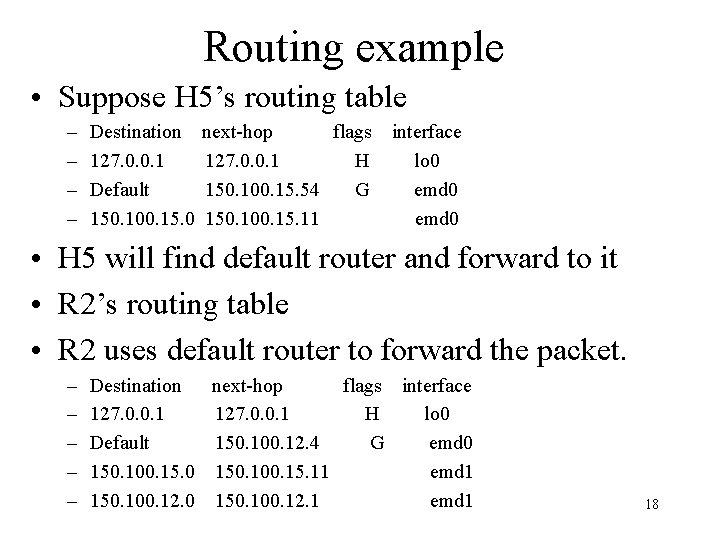
Routing example • Suppose H 5’s routing table – – Destination 127. 0. 0. 1 Default 150. 100. 15. 0 next-hop flags 127. 0. 0. 1 H 150. 100. 15. 54 G 150. 100. 15. 11 interface lo 0 emd 0 • H 5 will find default router and forward to it • R 2’s routing table • R 2 uses default router to forward the packet. – – – Destination next-hop flags interface 127. 0. 0. 1 H lo 0 Default 150. 100. 12. 4 G emd 0 150. 100. 15. 11 emd 1 150. 100. 12. 0 150. 100. 12. 1 emd 1 18
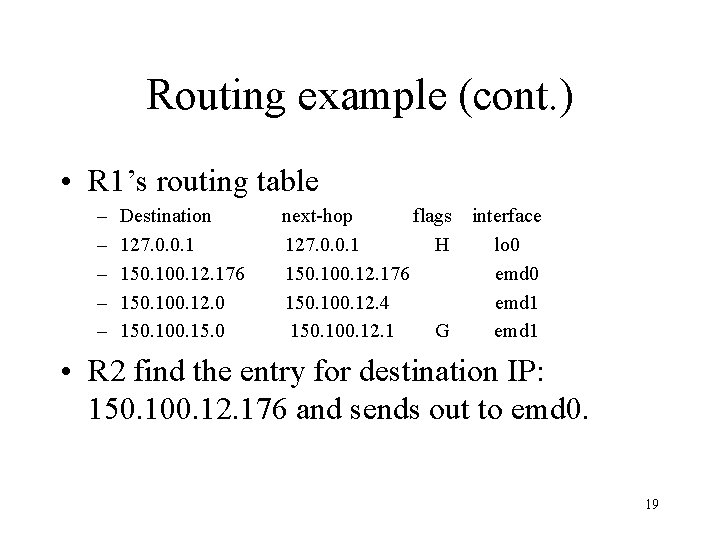
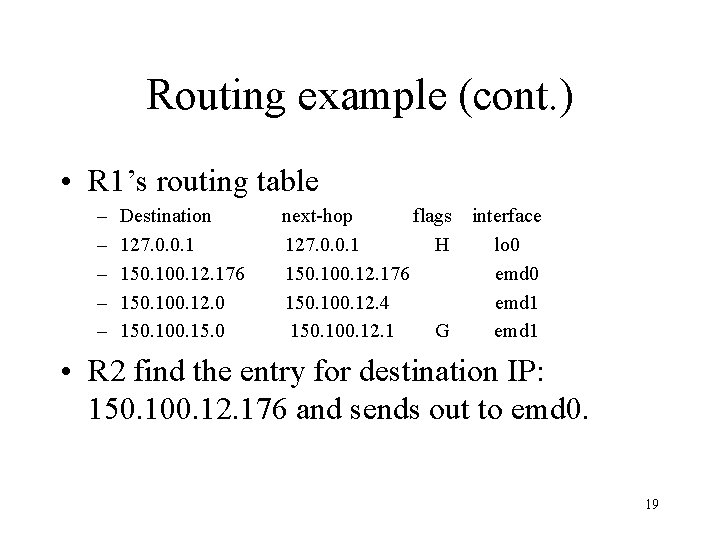
Routing example (cont. ) • R 1’s routing table – – – Destination 127. 0. 0. 1 150. 100. 12. 176 150. 100. 12. 0 150. 100. 15. 0 next-hop flags 127. 0. 0. 1 H 150. 100. 12. 176 150. 100. 12. 4 150. 100. 12. 1 G interface lo 0 emd 1 • R 2 find the entry for destination IP: 150. 100. 12. 176 and sends out to emd 0. 19
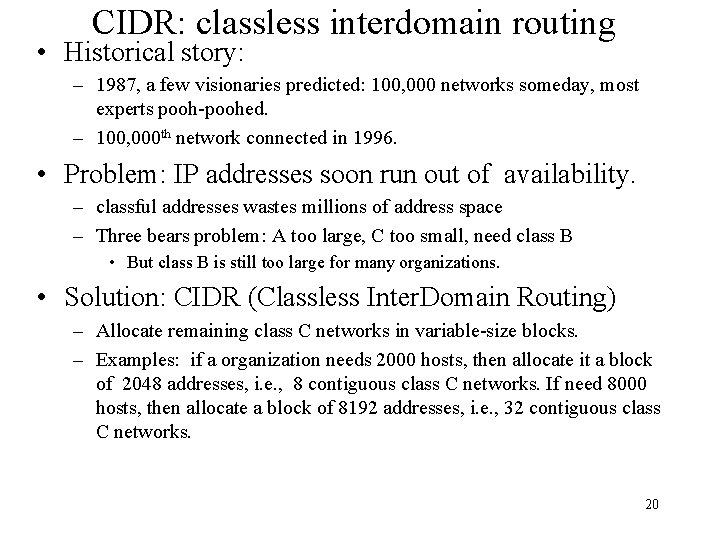
CIDR: classless interdomain routing • Historical story: – 1987, a few visionaries predicted: 100, 000 networks someday, most experts pooh-poohed. – 100, 000 th network connected in 1996. • Problem: IP addresses soon run out of availability. – classful addresses wastes millions of address space – Three bears problem: A too large, C too small, need class B • But class B is still too large for many organizations. • Solution: CIDR (Classless Inter. Domain Routing) – Allocate remaining class C networks in variable-size blocks. – Examples: if a organization needs 2000 hosts, then allocate it a block of 2048 addresses, i. e. , 8 contiguous class C networks. If need 8000 hosts, then allocate a block of 8192 addresses, i. e. , 32 contiguous class C networks. 20
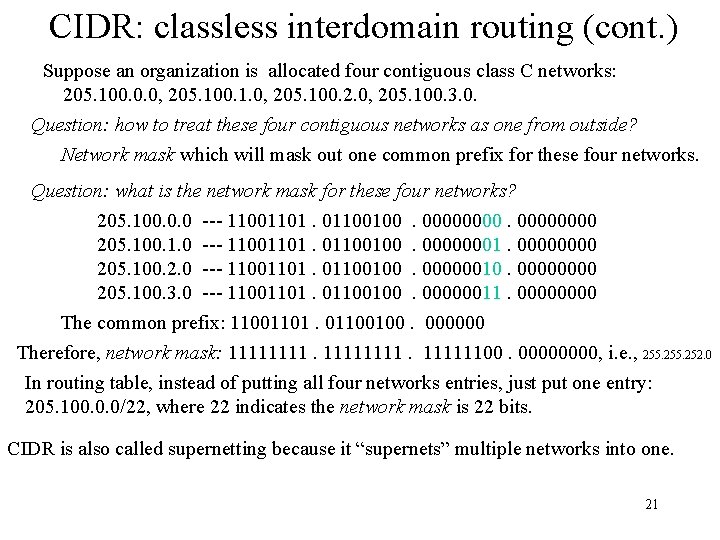
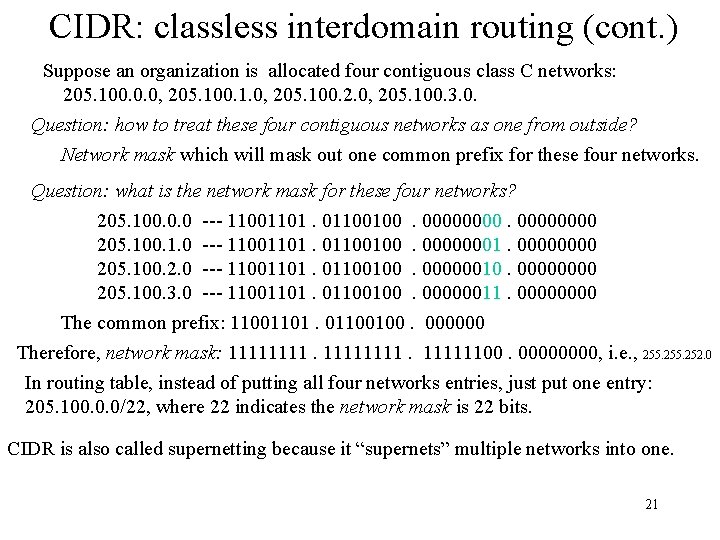
CIDR: classless interdomain routing (cont. ) Suppose an organization is allocated four contiguous class C networks: 205. 100. 0. 0, 205. 100. 1. 0, 205. 100. 2. 0, 205. 100. 3. 0. Question: how to treat these four contiguous networks as one from outside? Network mask which will mask out one common prefix for these four networks. Question: what is the network mask for these four networks? 205. 100. 0. 0 --- 11001101. 01100100. 00000000 205. 100. 1. 0 --- 11001101. 01100100. 00000001. 0000 205. 100. 2. 0 --- 11001101. 01100100. 00000010. 0000 205. 100. 3. 0 --- 11001101. 01100100. 00000011. 0000 The common prefix: 11001101. 01100100. 000000 Therefore, network mask: 1111111100. 0000, i. e. , 255. 252. 0 In routing table, instead of putting all four networks entries, just put one entry: 205. 100. 0. 0/22, where 22 indicates the network mask is 22 bits. CIDR is also called supernetting because it “supernets” multiple networks into one. 21
A few discussions about CIDR • it is possible that both supernet 205. 100. 0. 0/22 and 205. 100. 0. 0/20 appear in the routing table. – Therefore, the IP address 205. 100. 1. 1 will match both of them. – Solution: longest prefix match. 205. 100. 1. 1 will match 205. 100. 0. 0/22. • A prefix of arbitrary length, along with the network mask of the same length, indicates a network number. • The multiple contiguous networks can not begin at a random class C network address but must begin at certain boundary. – E. g. , 16 contiguous networks (i. e. , 4096 addresses) can not begin at 194. 24. 8. 0. Instead, they must lie on a 4096 -byte boundary. Such as begin from 194. 24. 16. 0 through 194. 24. 31. 0. • Go to Tanenbaum for more discussion. 22
Fragmentation and Reassembly • MTU (maximum transmission unit): a network generally has its MTU – Ethernet: 1500 bytes, FDDI: 4464 bytes • Fragmentation an IP packet if it is larger than MTU • Reassembly all packets of an IP packet into the original IP packet at receiver. 23
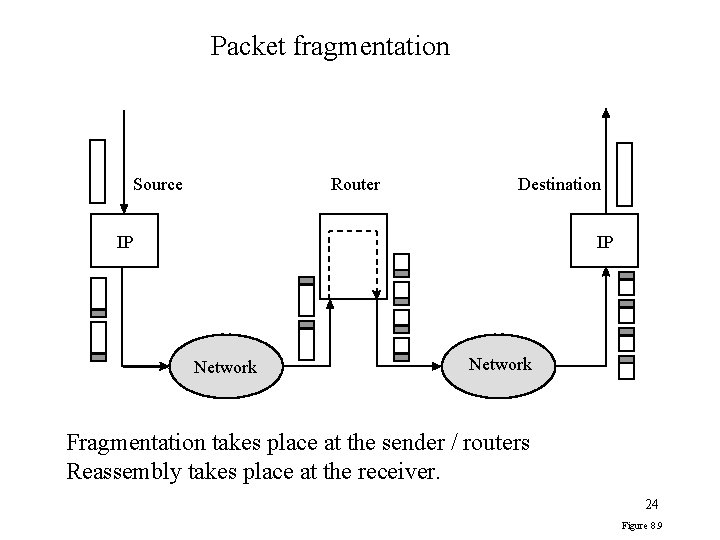
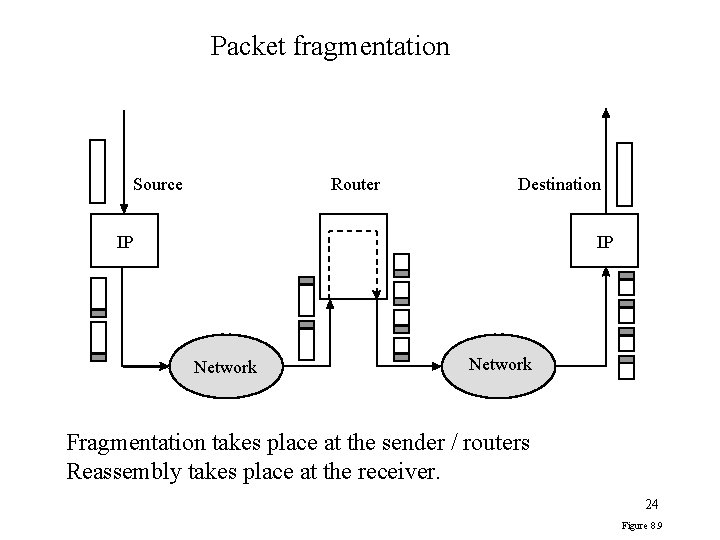
Packet fragmentation Source Router Destination IP IP Network Fragmentation takes place at the sender / routers Reassembly takes place at the receiver. 24 Figure 8. 9
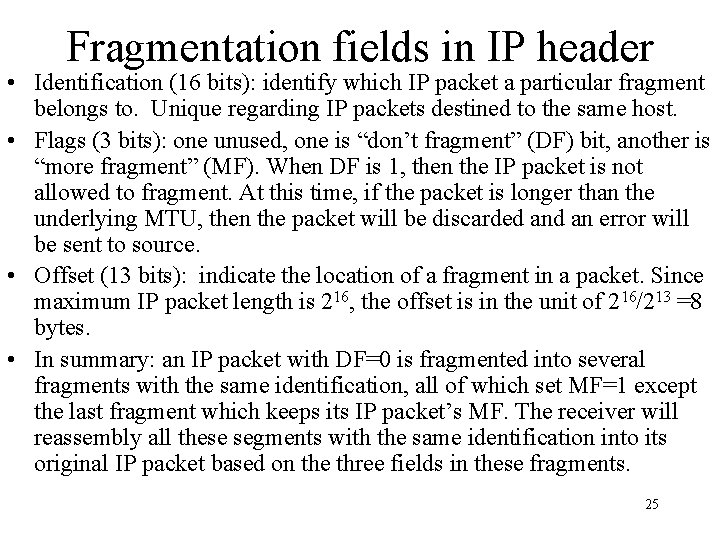
Fragmentation fields in IP header • Identification (16 bits): identify which IP packet a particular fragment belongs to. Unique regarding IP packets destined to the same host. • Flags (3 bits): one unused, one is “don’t fragment” (DF) bit, another is “more fragment” (MF). When DF is 1, then the IP packet is not allowed to fragment. At this time, if the packet is longer than the underlying MTU, then the packet will be discarded an error will be sent to source. • Offset (13 bits): indicate the location of a fragment in a packet. Since maximum IP packet length is 216, the offset is in the unit of 216/213 =8 bytes. • In summary: an IP packet with DF=0 is fragmented into several fragments with the same identification, all of which set MF=1 except the last fragment which keeps its IP packet’s MF. The receiver will reassembly all these segments with the same identification into its original IP packet based on the three fields in these fragments. 25
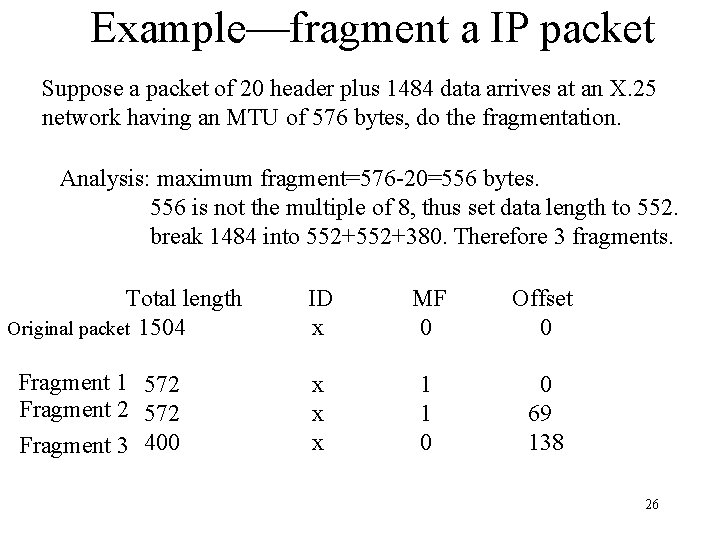
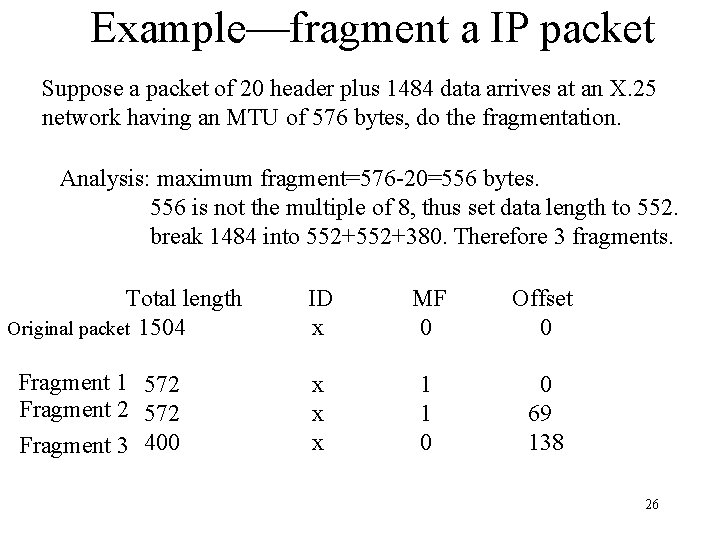
Example—fragment a IP packet Suppose a packet of 20 header plus 1484 data arrives at an X. 25 network having an MTU of 576 bytes, do the fragmentation. Analysis: maximum fragment=576 -20=556 bytes. 556 is not the multiple of 8, thus set data length to 552. break 1484 into 552+380. Therefore 3 fragments. Total length Original packet 1504 Fragment 1 572 Fragment 2 572 Fragment 3 400 ID x MF 0 Offset 0 x x x 1 1 0 0 69 138 26
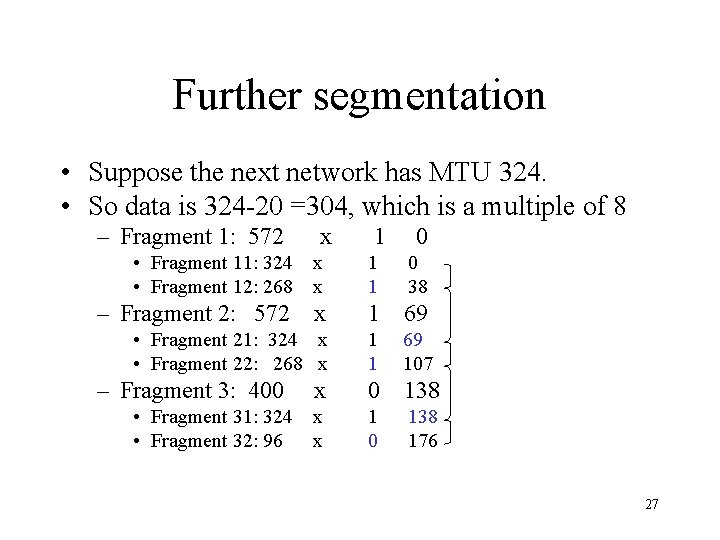
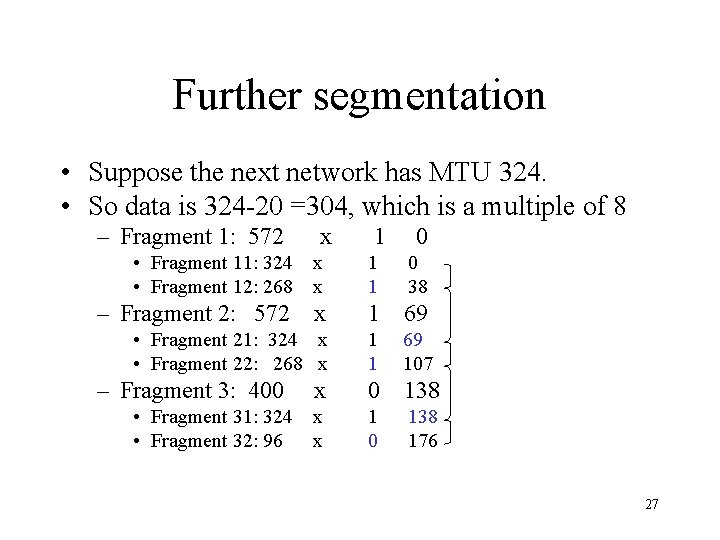
Further segmentation • Suppose the next network has MTU 324. • So data is 324 -20 =304, which is a multiple of 8 – Fragment 1: 572 x 1 0 • Fragment 11: 324 x • Fragment 12: 268 x 1 1 0 38 – Fragment 2: 572 x 1 69 • Fragment 21: 324 x • Fragment 22: 268 x 1 1 69 107 x 0 138 • Fragment 31: 324 x • Fragment 32: 96 x 1 0 138 176 – Fragment 3: 400 27
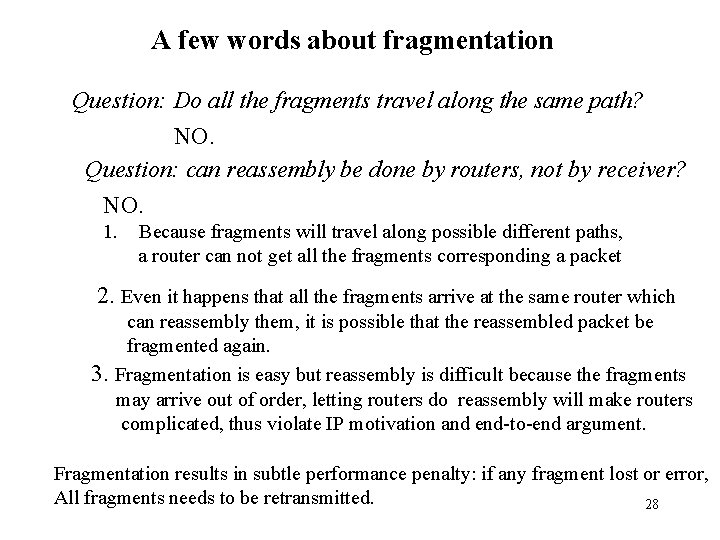
A few words about fragmentation Question: Do all the fragments travel along the same path? NO. Question: can reassembly be done by routers, not by receiver? NO. 1. Because fragments will travel along possible different paths, a router can not get all the fragments corresponding a packet 2. Even it happens that all the fragments arrive at the same router which can reassembly them, it is possible that the reassembled packet be fragmented again. 3. Fragmentation is easy but reassembly is difficult because the fragments may arrive out of order, letting routers do reassembly will make routers complicated, thus violate IP motivation and end-to-end argument. Fragmentation results in subtle performance penalty: if any fragment lost or error, All fragments needs to be retransmitted. 28
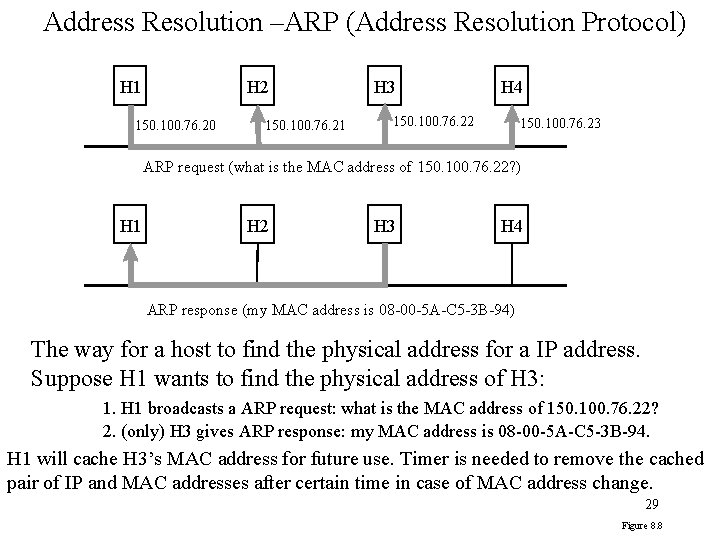
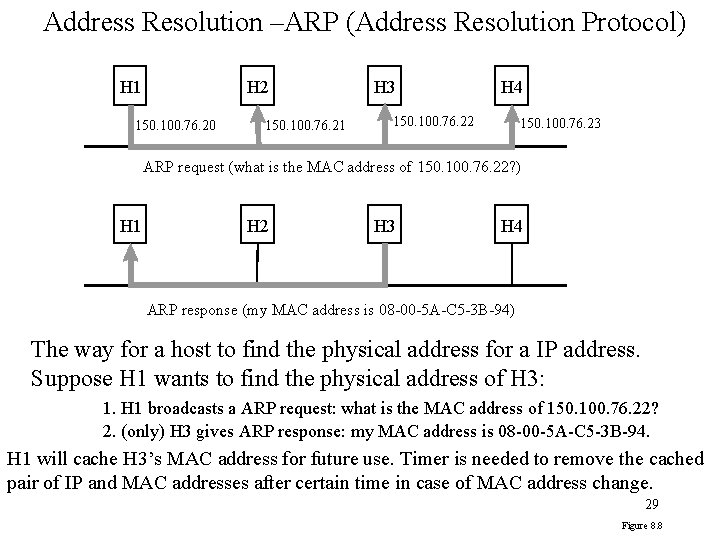
Address Resolution –ARP (Address Resolution Protocol) H 1 H 2 150. 100. 76. 20 150. 100. 76. 21 H 3 H 4 150. 100. 76. 22 150. 100. 76. 23 ARP request (what is the MAC address of 150. 100. 76. 22? ) H 1 H 2 H 3 H 4 ARP response (my MAC address is 08 -00 -5 A-C 5 -3 B-94) The way for a host to find the physical address for a IP address. Suppose H 1 wants to find the physical address of H 3: 1. H 1 broadcasts a ARP request: what is the MAC address of 150. 100. 76. 22? 2. (only) H 3 gives ARP response: my MAC address is 08 -00 -5 A-C 5 -3 B-94. H 1 will cache H 3’s MAC address for future use. Timer is needed to remove the cached pair of IP and MAC addresses after certain time in case of MAC address change. 29 Figure 8. 8
RARP---Reverse Address Resolution Protocol • The MAC address of a host may be known, but the IP address is not. – E. g. , a diskless computer at boot time can read its MAC address but does not know its IP address, which is stored at a server. • RARP: getting IP address of a MAC address. – The host broadcasts a RARP request: what is the IP address of such a MAC address – The server containing the IP address gives RARP response: the IP address of such a MAC address is so so. 30
ICMP: Intenet Control Message Protocol • Deal with error and control messages • ICMP messages are encapsulated in IP packet, but ICMP is considered in the same layer as IP. • Some message types: echo request/reply, timestamp request/reply, destination unreachable, source quench, redirect, time exceeded, parameter problem • Examples: – echo request/reply is used by ping program. – Time exceeded message is used in traceroute program: • Source host (running traceroute) sends messages to the destination with TTL incremented by one per message, beginning from 1. • When a message arrive at a router and its TTL =0, the router will send a time exceeded message back to source host, with the router included in the message. 31