TCPIP Babu Ram Dawadi What is TCPIP TCPIP
TCP/IP Babu Ram Dawadi
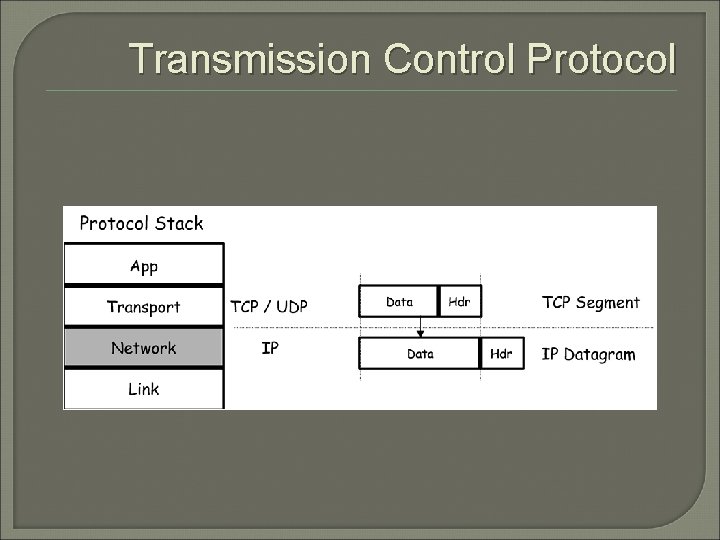
What is TCP/IP? TCP/IP is a set of protocols developed to allow cooperating computers to share resources across a network. TCP stands for “Transmission Control Protocol” IP stands for “Internet Protocol” They are Transport layer and Network layer protocols respectively of the protocol suite The most well known network that adopted TCP/IP is Internet – the biggest WAN in the world
What is a protocol? A protocol is a collection of rules and procedures for two computers to exchange information Protocol also defines the format of data that is being exchanged
Why TCP/IP? TCP/IP was developed very early Technologies were widely discussed and circulated in documents called “Request for Comments” (RFC) – free of charge Supported by UNIX operating system
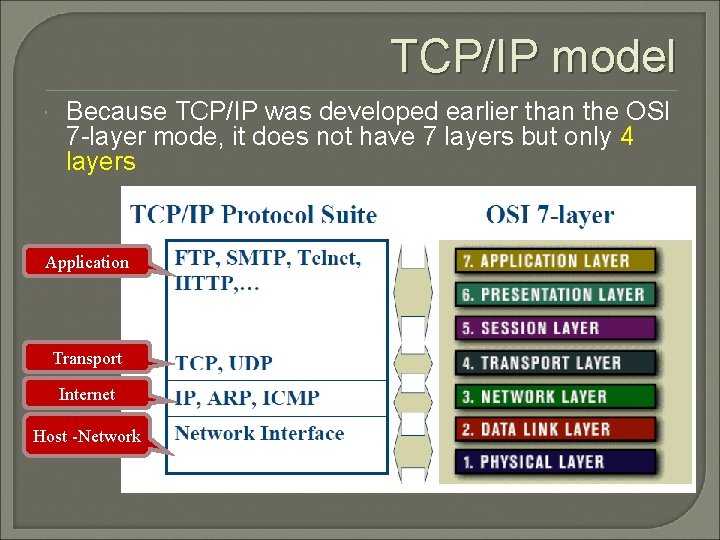
TCP/IP model Because TCP/IP was developed earlier than the OSI 7 -layer mode, it does not have 7 layers but only 4 layers Application Transport Internet Host Network
Application layer protocols define the rules when implementing specific network applications Rely on the underlying layers to provide accurate and efficient data delivery Typical protocols: • • FTP – File Transfer Protocol Telnet – Remote terminal protocol SMTP – Simple Mail Transfer Protocol HTTP – Hypertext Transfer Protocol
Transport layer TCP/IP is built on “connectionless” technology, each datagram finds its own way to its destination Transport Layer protocols define the rules of • Dividing a chunk of data into segments • Reassemble segments into the original chunk Typical protocols: • TCP – Transmission Control Protocol Provide further the functions such as reordering and data resend • UDP – User Datagram Service • Use when the message to be sent fit exactly into a datagram • Use also when a more simplified data format is required
Network layer protocols define the rules of how to find the routes for a packet to the destination It only gives best effort delivery. Packets can be delayed, corrupted, lost, duplicated, out-of-order Typical protocols: • IP – Internet Protocol Provide packet delivery • ARP – Address Resolution Protocol Define the procedures of network address / MAC address translation • ICMP – Internet Control Message Protocol Define the procedures of error message transfer
Example: Mail Application Transport Nework Host to Network
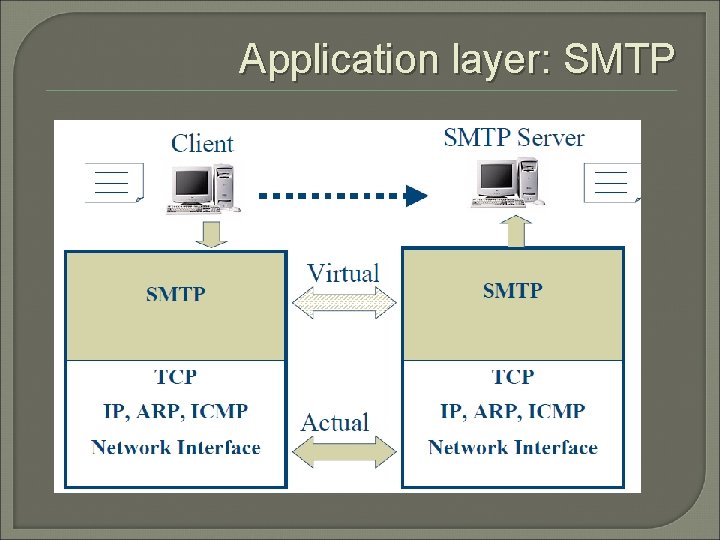
Application layer: SMTP
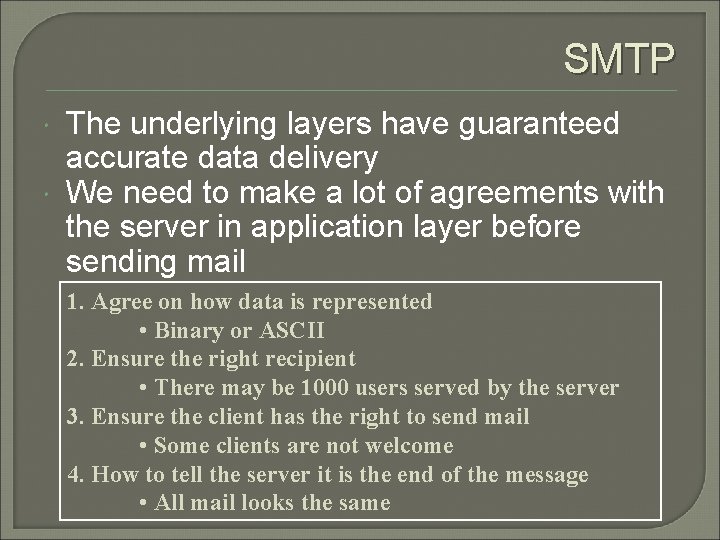
SMTP The underlying layers have guaranteed accurate data delivery We need to make a lot of agreements with the server in application layer before sending mail 1. Agree on how data is represented • Binary or ASCII 2. Ensure the right recipient • There may be 1000 users served by the server 3. Ensure the client has the right to send mail • Some clients are not welcome 4. How to tell the server it is the end of the message • All mail looks the same
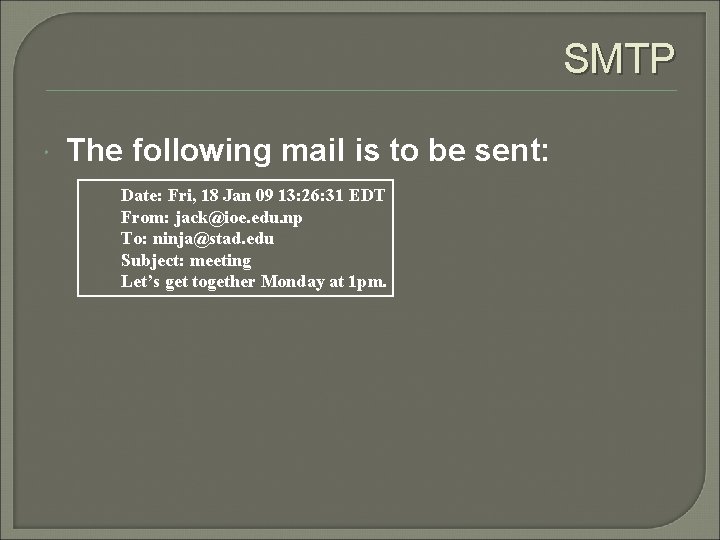
SMTP The following mail is to be sent: Date: Fri, 18 Jan 09 13: 26: 31 EDT From: jack@ioe. edu. np To: ninja@stad. edu Subject: meeting Let’s get together Monday at 1 pm.
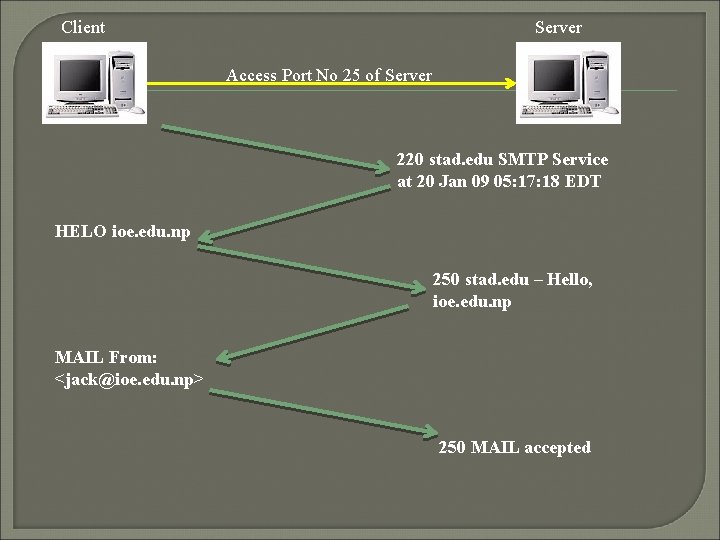
Client Server Access Port No 25 of Server 220 stad. edu SMTP Service at 20 Jan 09 05: 17: 18 EDT HELO ioe. edu. np 250 stad. edu – Hello, ioe. edu. np MAIL From: <jack@ioe. edu. np> 250 MAIL accepted
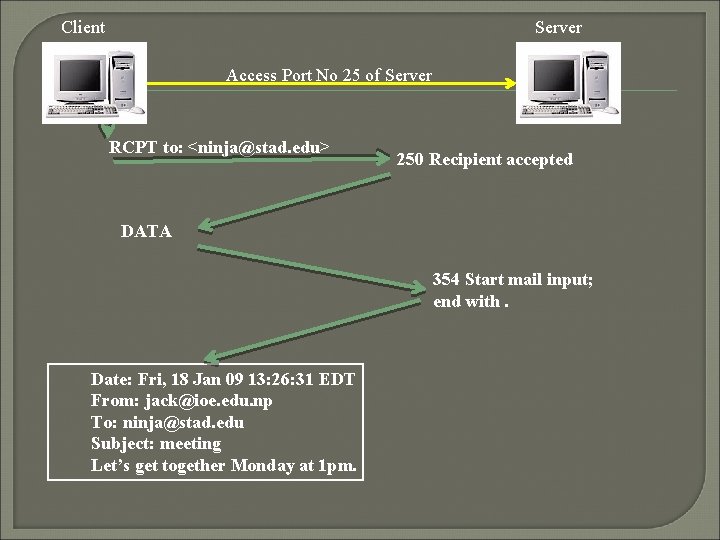
Client Server Access Port No 25 of Server RCPT to: <ninja@stad. edu> 250 Recipient accepted DATA 354 Start mail input; end with. Date: Fri, 18 Jan 09 13: 26: 31 EDT From: jack@ioe. edu. np To: ninja@stad. edu Subject: meeting Let’s get together Monday at 1 pm.
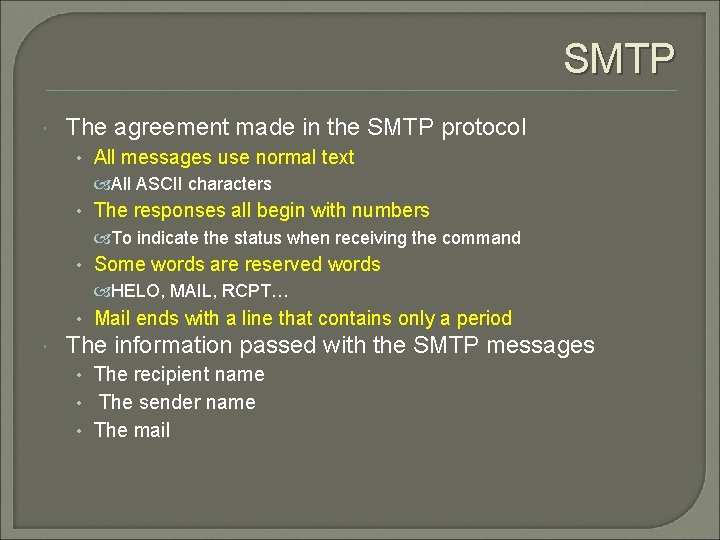
SMTP The agreement made in the SMTP protocol • All messages use normal text All ASCII characters • The responses all begin with numbers To indicate the status when receiving the command • Some words are reserved words HELO, MAIL, RCPT… • Mail ends with a line that contains only a period The information passed with the SMTP messages • The recipient name • The sender name • The mail
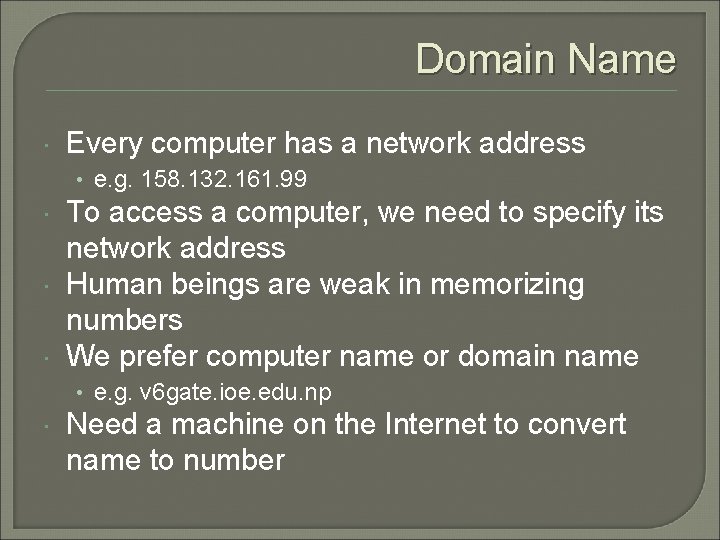
Domain Name Every computer has a network address • e. g. 158. 132. 161. 99 To access a computer, we need to specify its network address Human beings are weak in memorizing numbers We prefer computer name or domain name • e. g. v 6 gate. ioe. edu. np Need a machine on the Internet to convert name to number
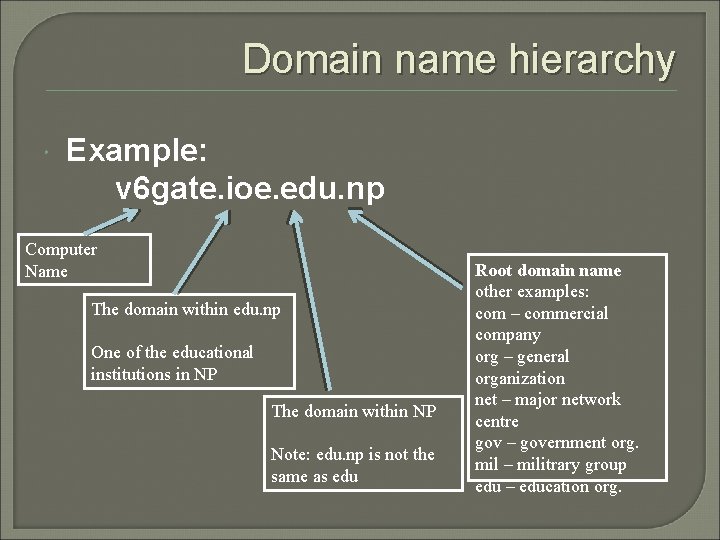
Domain name hierarchy Example: v 6 gate. ioe. edu. np Computer Name The domain within edu. np One of the educational institutions in NP The domain within NP Note: edu. np is not the same as edu Root domain name other examples: com – commercial company org – general organization net – major network centre gov – government org. mil – militrary group edu – education org.
Domain name registration An organization needs to register its domain name • e. g. ioe has registered its name to the domain of edu. np Once a domain name is assigned, the organization is free to assign other names belong to its domain • e. g. we can have election. ioe. edu. np Fsu. ioe. edu. np mail. ioe. edu. np ----
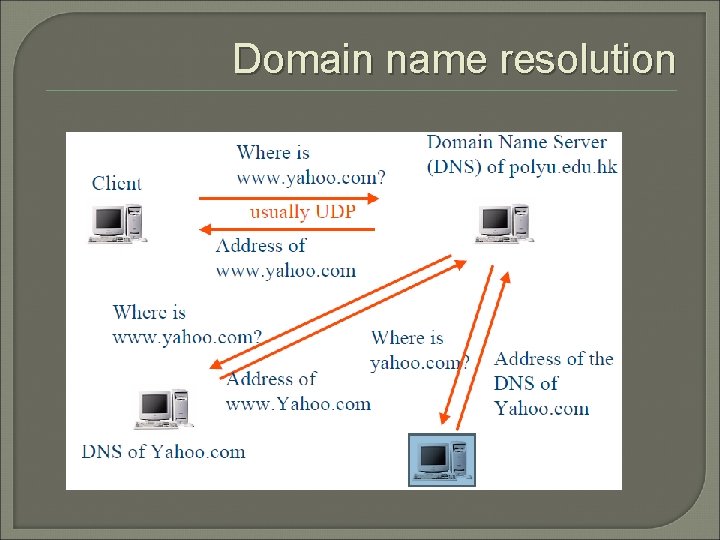
Domain name resolution
Domain name resolution Nevertheless, such a complicated procedure needs not perform in most cases Client computers usually remember the answers that it got before (DNS Cache) It reduces the loading to the root DNS To further reduce loading, there can be many root DNS on the Internet • e. g. there a few “com” root DNS
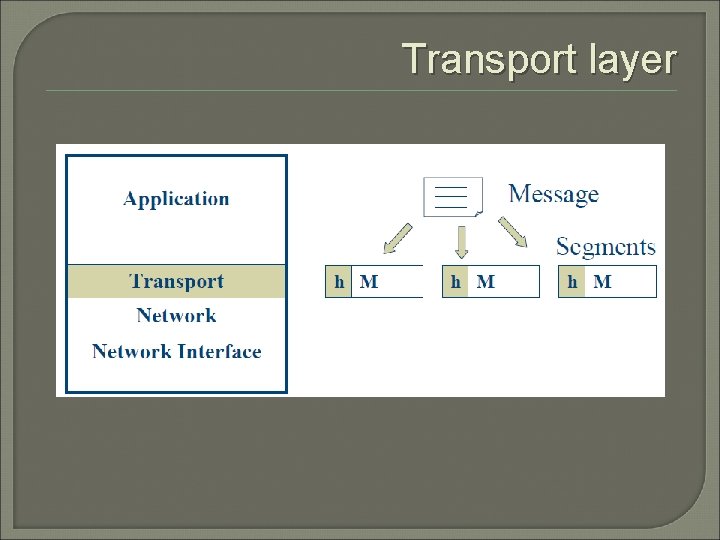
Transport layer
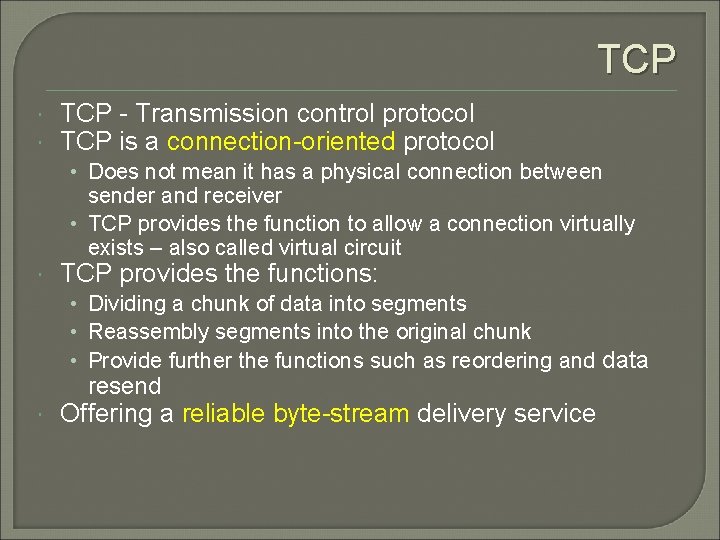
TCP - Transmission control protocol TCP is a connection-oriented protocol • Does not mean it has a physical connection between sender and receiver • TCP provides the function to allow a connection virtually exists – also called virtual circuit TCP provides the functions: • Dividing a chunk of data into segments • Reassembly segments into the original chunk • Provide further the functions such as reordering and data resend Offering a reliable byte-stream delivery service
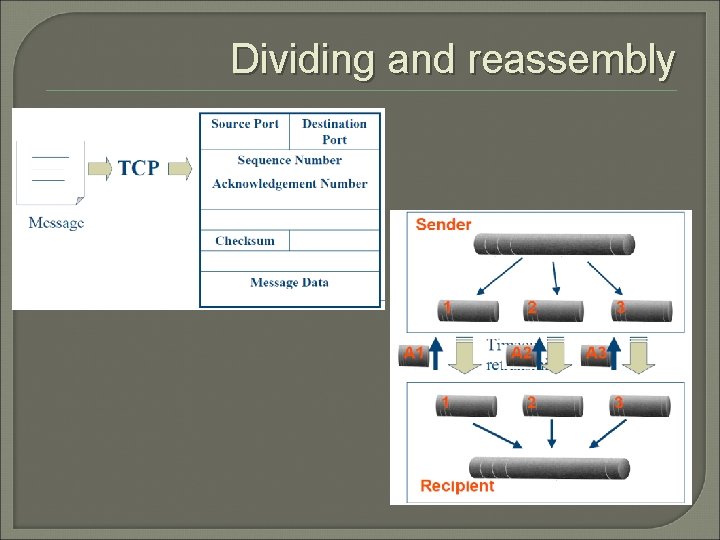
Dividing and reassembly
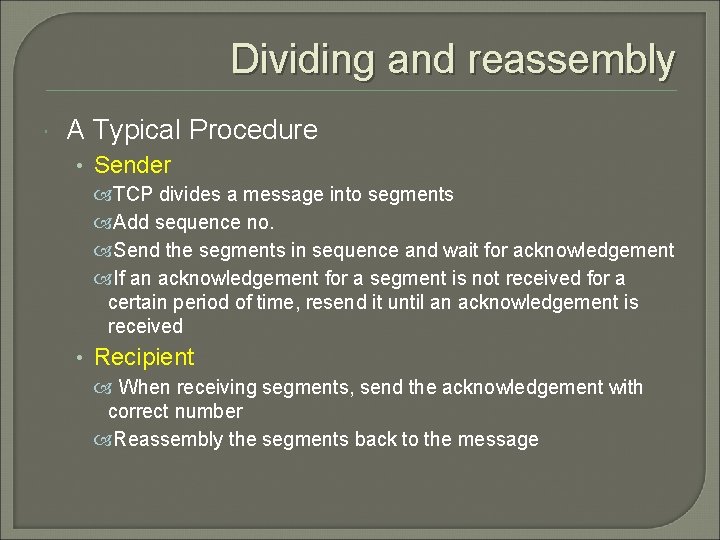
Dividing and reassembly A Typical Procedure • Sender TCP divides a message into segments Add sequence no. Send the segments in sequence and wait for acknowledgement If an acknowledgement for a segment is not received for a certain period of time, resend it until an acknowledgement is received • Recipient When receiving segments, send the acknowledgement with correct number Reassembly the segments back to the message
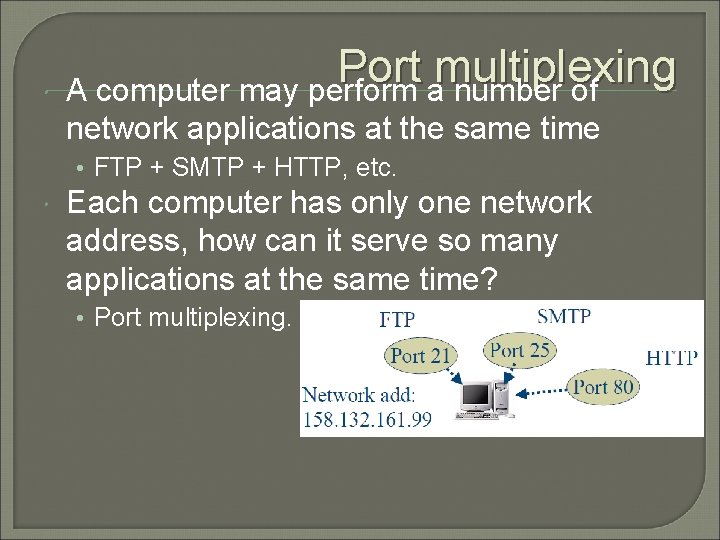
Port multiplexing A computer may perform a number of network applications at the same time • FTP + SMTP + HTTP, etc. Each computer has only one network address, how can it serve so many applications at the same time? • Port multiplexing.
Some port numbers are reserved for some purposes • • Port 21: FTP – file transfer Port 25: SMTP – mail transfer Port 23: TELNET – remote login Port 80: HTTP – Web access These port numbers are well known to all computers in the network E. g. whenever a client access port 25 of the server, it means the client needs SMTP service
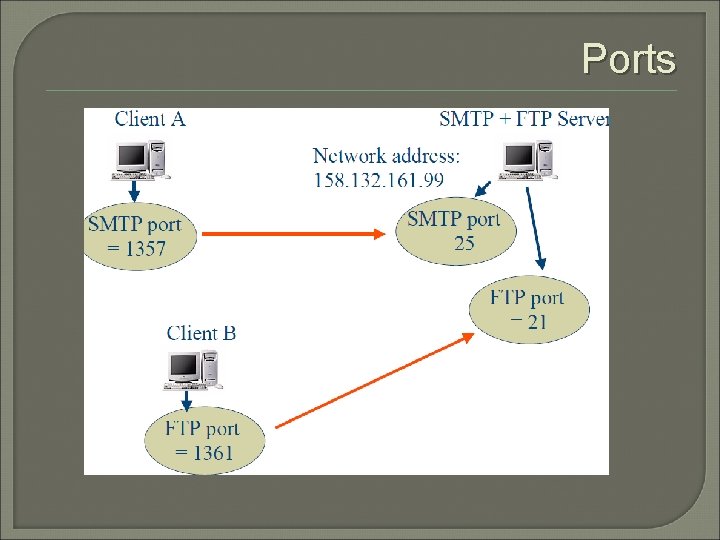
Ports
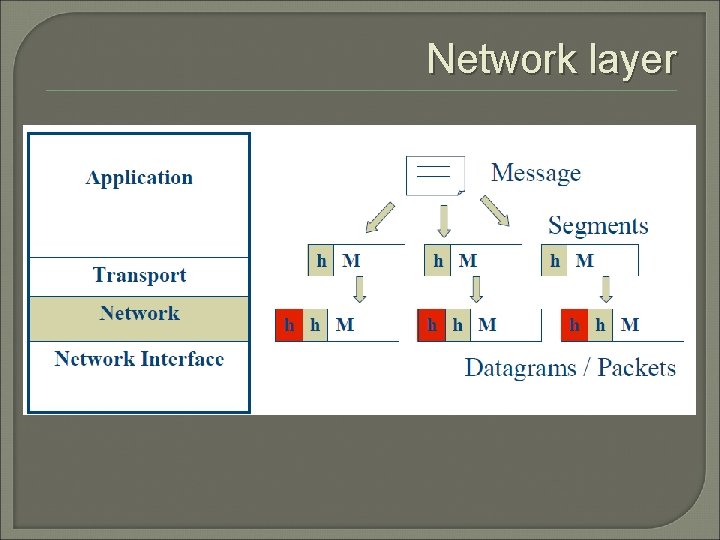
Network layer
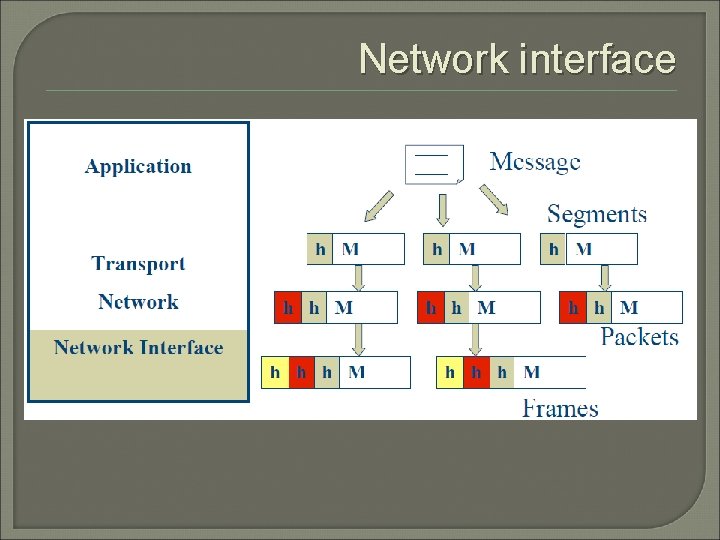
Network interface
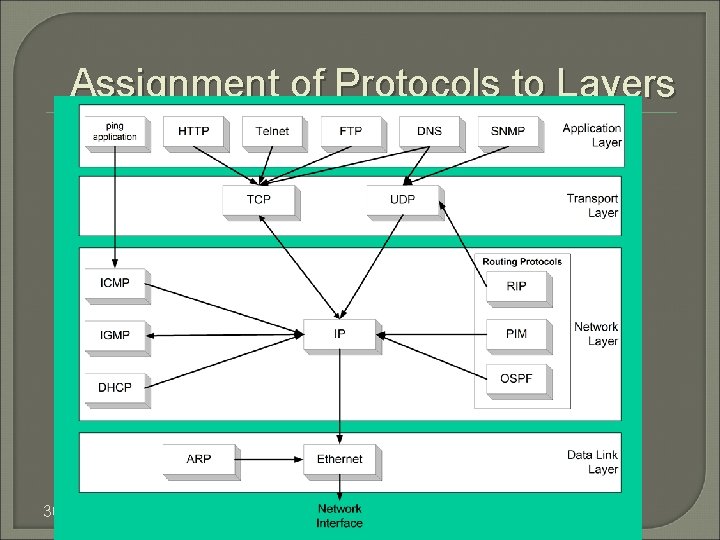
Assignment of Protocols to Layers 30
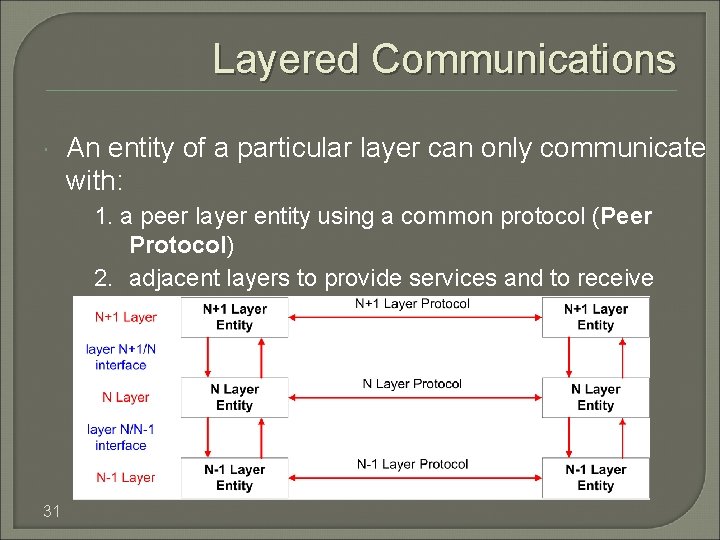
Layered Communications An entity of a particular layer can only communicate with: 1. a peer layer entity using a common protocol (Peer Protocol) 2. adjacent layers to provide services and to receive services 31
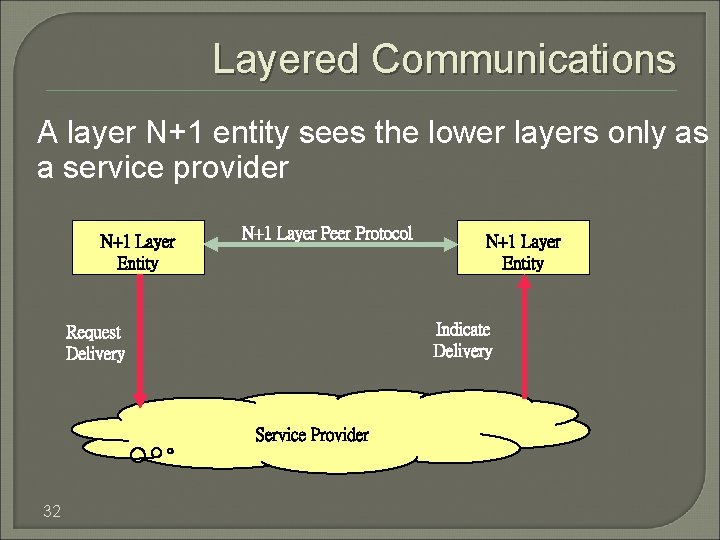
Layered Communications A layer N+1 entity sees the lower layers only as a service provider N+1 Layer Entity N+1 Layer Peer Protocol Indicate Delivery Request Delivery Service Provider 32 N+1 Layer Entity
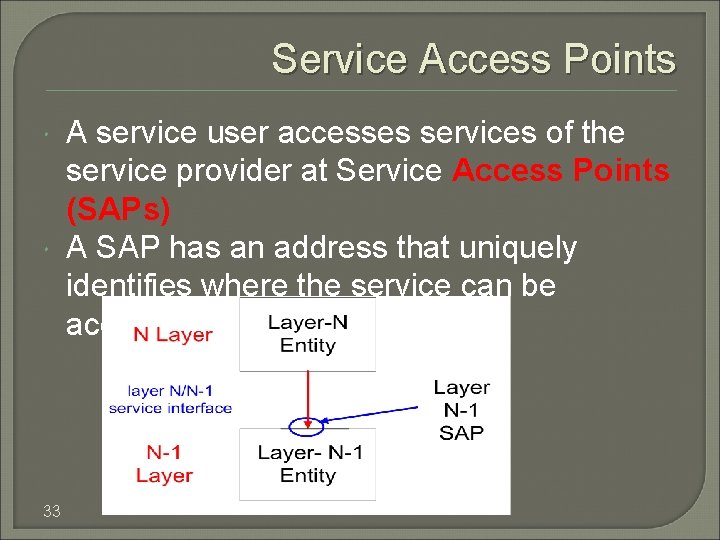
Service Access Points 33 A service user accesses services of the service provider at Service Access Points (SAPs) A SAP has an address that uniquely identifies where the service can be accessed
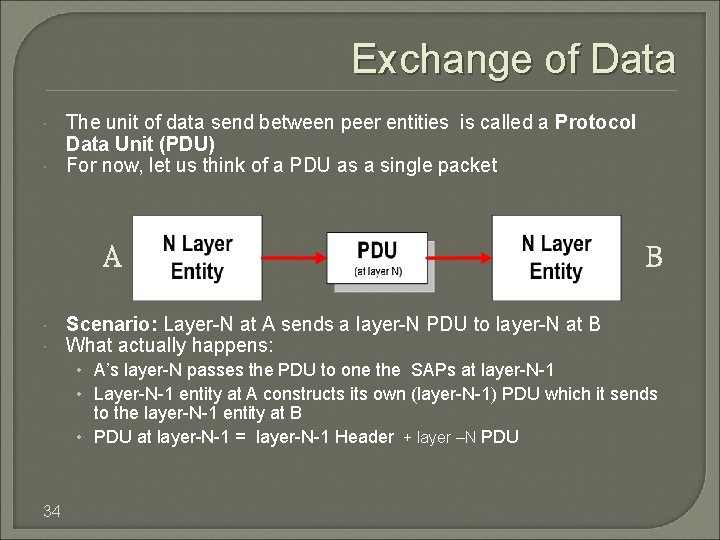
Exchange of Data The unit of data send between peer entities is called a Protocol Data Unit (PDU) For now, let us think of a PDU as a single packet A B Scenario: Layer-N at A sends a layer-N PDU to layer-N at B What actually happens: • A’s layer-N passes the PDU to one the SAPs at layer-N-1 • Layer-N-1 entity at A constructs its own (layer-N-1) PDU which it sends to the layer-N-1 entity at B • PDU at layer-N-1 = layer-N-1 Header + layer –N PDU 34
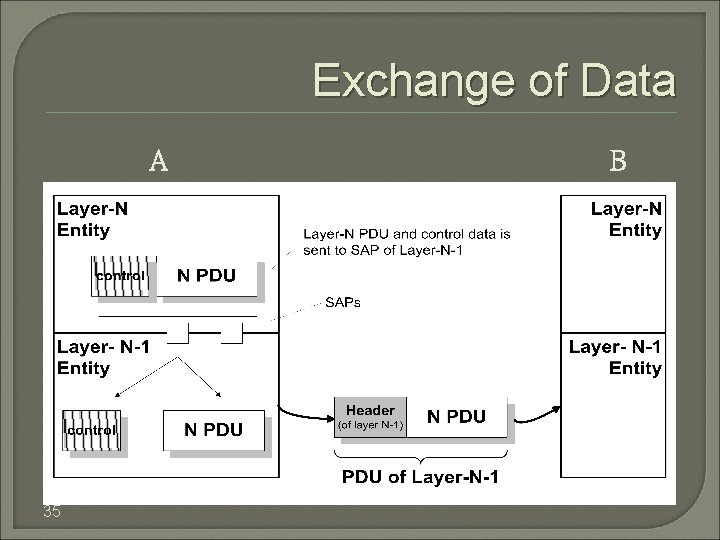
Exchange of Data A 35 B
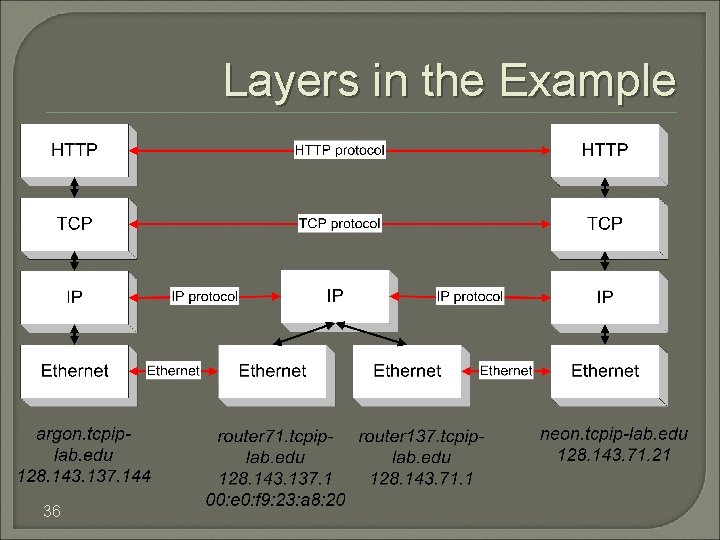
Layers in the Example 36
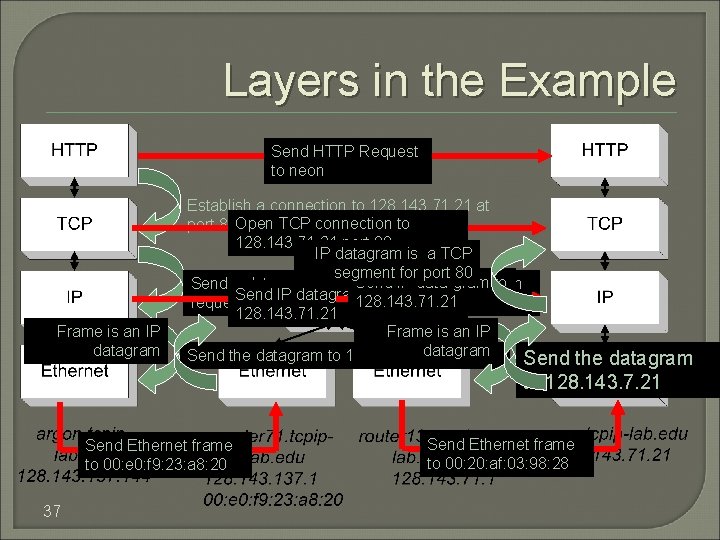
Layers in the Example Send HTTP Request to neon Frame is an IP datagram Establish a connection to 128. 143. 71. 21 at port 80 Open TCP connection to 128. 143. 71. 21 port 80 IP datagram is a TCP segment for port 80 Send IP data-gram to Send a datagram (which contains a connection Send IP datagram to 128. 143. 71. 21 request) to 128. 143. 71. 21 Frame is an IP datagram Send the datagram to 128. 143. 137. 1 Send the datagram to 128. 143. 7. 21 Send Ethernet frame to 00: e 0: f 9: 23: a 8: 20 37 Send Ethernet frame to 00: 20: af: 03: 98: 28
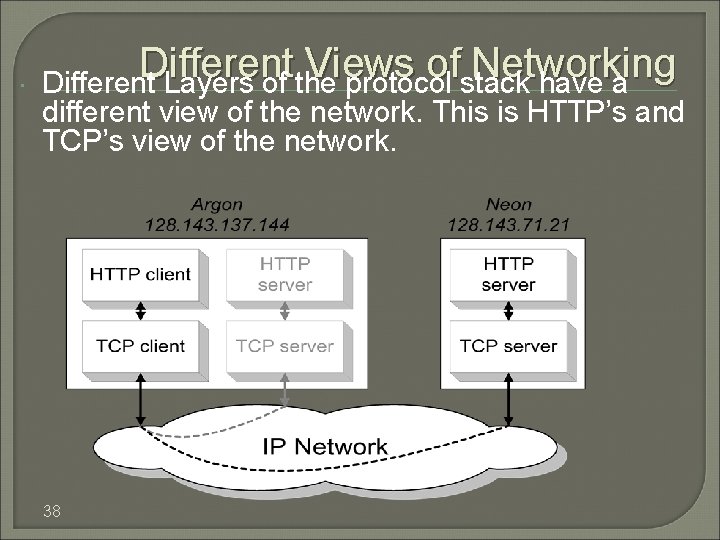
Different Views of Networking Different Layers of the protocol stack have a different view of the network. This is HTTP’s and TCP’s view of the network. 38
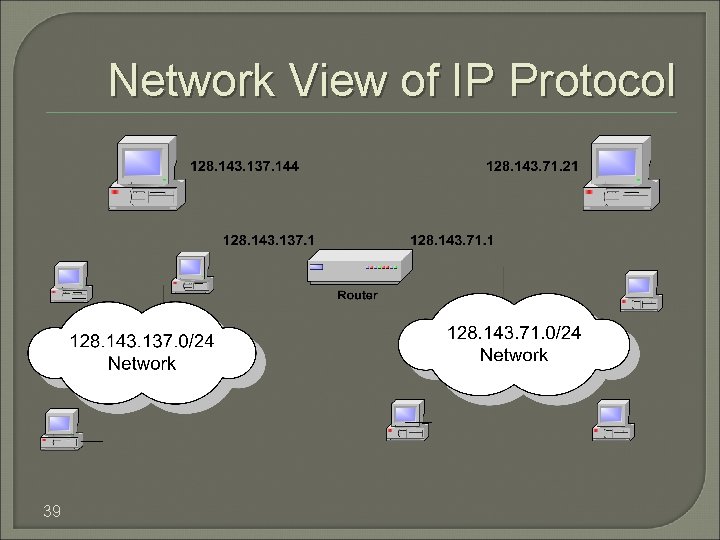
Network View of IP Protocol 39
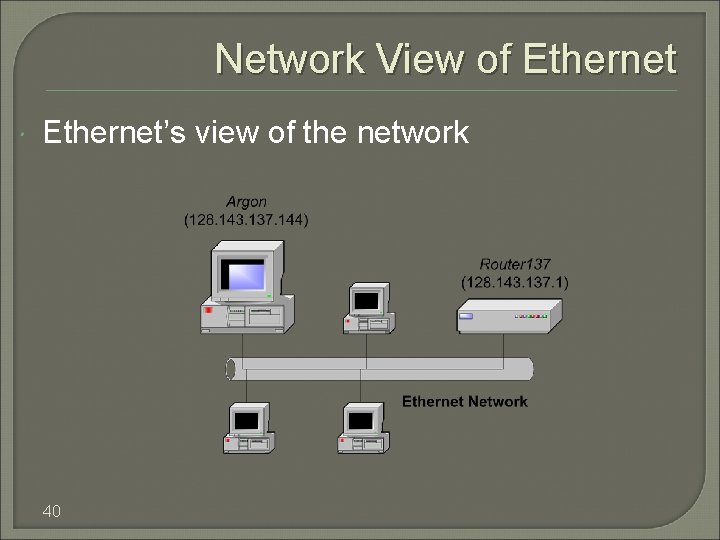
Network View of Ethernet’s view of the network 40
IP Addresses IP (Version 4) Addresses are 32 bits long IP Addresses Assigned Statically or Dynamically (DHCP) IPv 6 addresses are 128 bits long
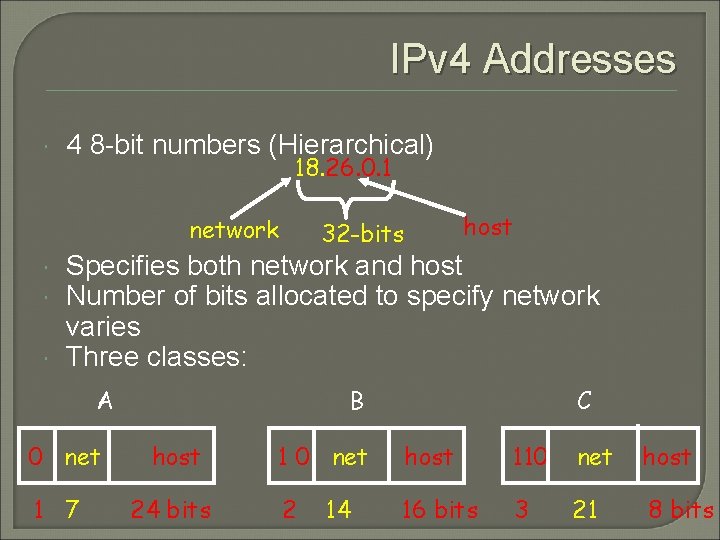
IPv 4 Addresses 4 8 -bit numbers (Hierarchical) 18. 26. 0. 1 network host 32 -bits Specifies both network and host Number of bits allocated to specify network varies Three classes: A 0 net 1 7 B host 24 bits C 1 0 net host 110 net host 2 16 bits 3 21 8 bits 14
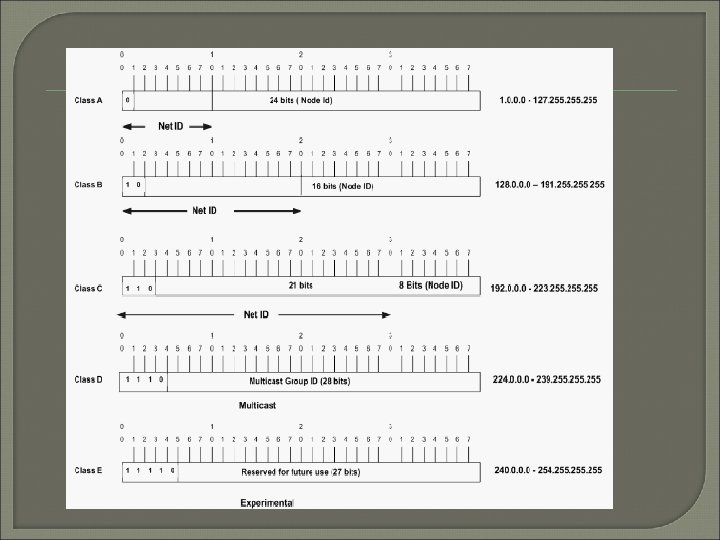
IPv 4 address: a 32 -bit number, usually written in dotted decimal form, that uniquely identifies an interface of some computer Host Address: another term for IP address Network: a group of hosts, all of which have an identical beginning position of their ip addresses. Network Number: a 32 -bit number that represent a network and it cant be assigned as ip address of a host Network address: another term for the network number. Broadcast address: a 32 -bit number that is used to address all hosts in the network. It cant be assigned as an ip address of a host.
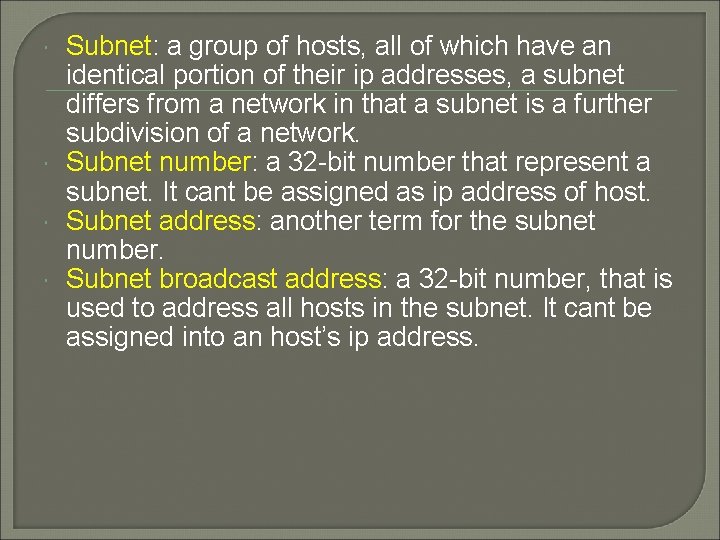
Subnet: a group of hosts, all of which have an identical portion of their ip addresses, a subnet differs from a network in that a subnet is a further subdivision of a network. Subnet number: a 32 -bit number that represent a subnet. It cant be assigned as ip address of host. Subnet address: another term for the subnet number. Subnet broadcast address: a 32 -bit number, that is used to address all hosts in the subnet. It cant be assigned into an host’s ip address.
Subnetting: the process of subdividing networks into smaller subnets. Subnet mask: A 32 -bit combination used to describe which portion of an address refers to the subnet and which part refers to the host. Network mask: 32 -bit number. The mask is used by computers to calculate the network number of a given IP address by performing a Boolean AND operation of the address and mask. Address mask: another term for a mask Interface: A network connection.
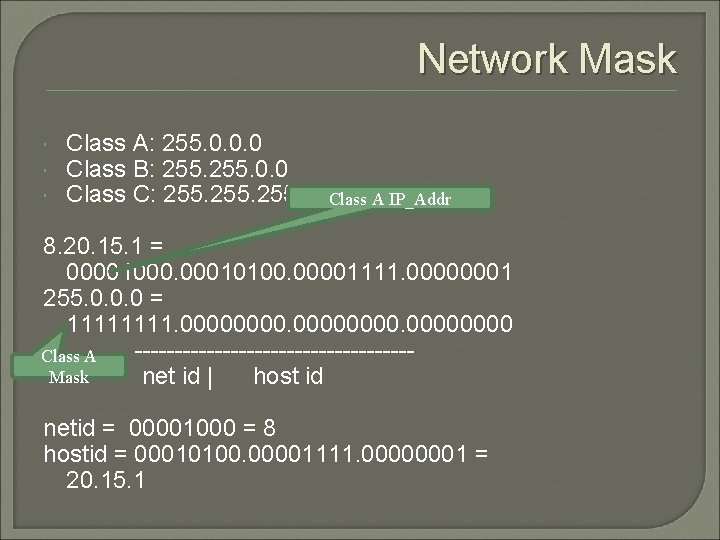
Network Mask Class A: 255. 0. 0. 0 Class B: 255. 0. 0 Class C: 255. 0 Class A IP_Addr 8. 20. 15. 1 = 00001000. 00010100. 00001111. 00000001 255. 0. 0. 0 = 1111. 00000000 Class A -----------------Mask net id | host id netid = 00001000 = 8 hostid = 00010100. 00001111. 00000001 = 20. 15. 1
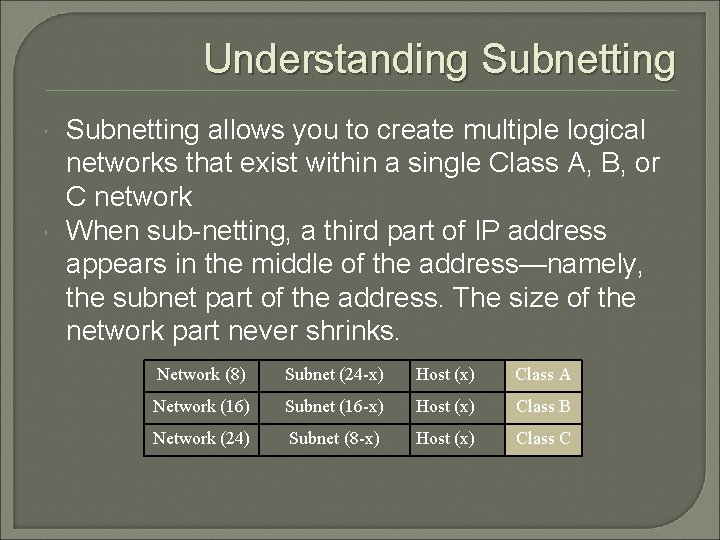
Understanding Subnetting allows you to create multiple logical networks that exist within a single Class A, B, or C network When sub-netting, a third part of IP address appears in the middle of the address—namely, the subnet part of the address. The size of the network part never shrinks. Network (8) Subnet (24 x) Host (x) Class A Network (16) Subnet (16 x) Host (x) Class B Network (24) Subnet (8 x) Host (x) Class C
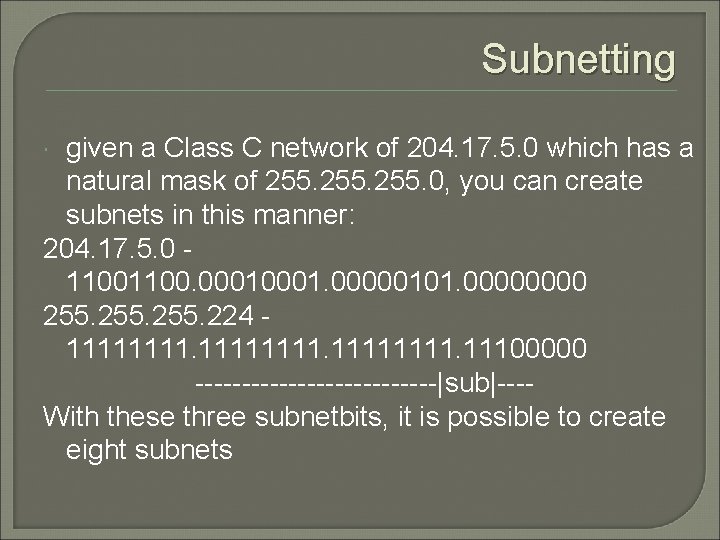
Subnetting given a Class C network of 204. 17. 5. 0 which has a natural mask of 255. 0, you can create subnets in this manner: 204. 17. 5. 0 - 1100. 0001. 00000101. 0000 255. 224 - 11111111. 11100000 -------------|sub|---With these three subnetbits, it is possible to create eight subnets
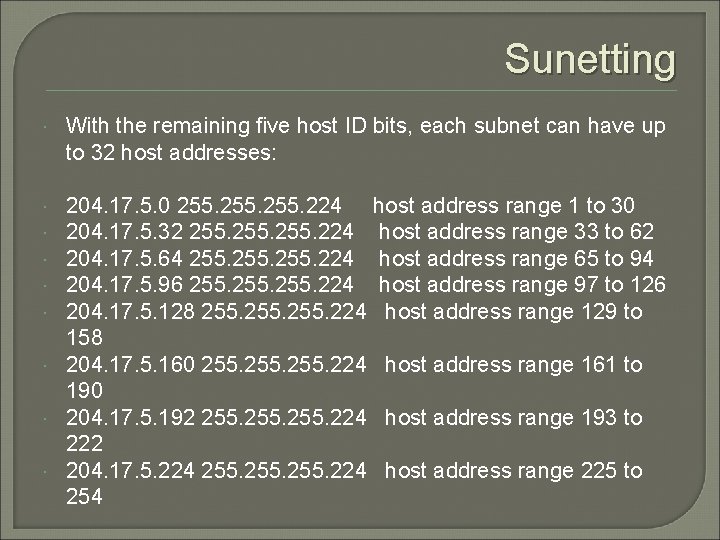
Sunetting With the remaining five host ID bits, each subnet can have up to 32 host addresses: 204. 17. 5. 0 255. 224 host address range 1 to 30 204. 17. 5. 32 255. 224 host address range 33 to 62 204. 17. 5. 64 255. 224 host address range 65 to 94 204. 17. 5. 96 255. 224 host address range 97 to 126 204. 17. 5. 128 255. 224 host address range 129 to 158 204. 17. 5. 160 255. 224 host address range 161 to 190 204. 17. 5. 192 255. 224 host address range 193 to 222 204. 17. 5. 224 255. 224 host address range 225 to 254
the mask of 255. 224 can also be denoted as /27 as there are 27 bits that are set in the mask This second method is used with CIDR For example, 204. 17. 5. 32/27 denotes the network 204. 17. 5. 32 255. 224.
Example Given the network number and a mask, how many subnets are there and how many hosts per subnet. Given an address and mask, what is the subnet number Given an address and mask, what is the subnet broadcast address and valid ip address on the subnet Subnet bits=32 -(network bits+ hosts bits)
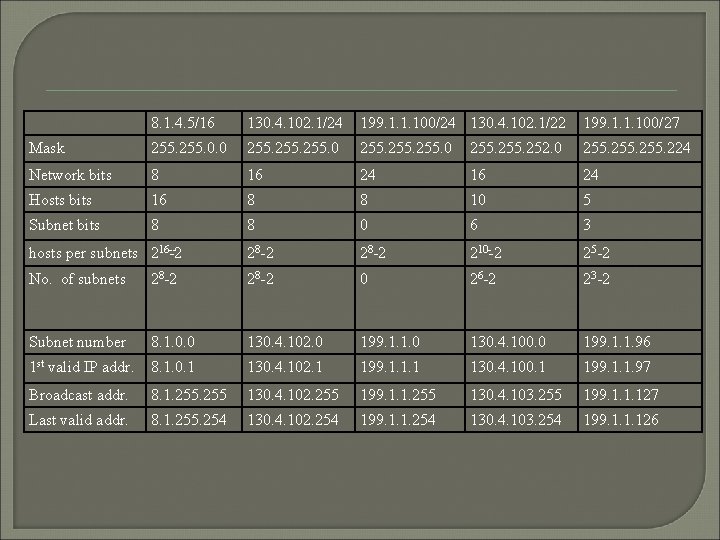
8. 1. 4. 5/16 130. 4. 102. 1/24 199. 1. 1. 100/24 130. 4. 102. 1/22 199. 1. 1. 100/27 Mask 255. 0. 0 255. 0 255. 252. 0 255. 224 Network bits 8 16 24 Hosts bits 16 8 8 10 5 Subnet bits 8 8 0 6 3 hosts per subnets 216 2 28 2 210 2 25 2 No. of subnets 28 2 0 26 2 23 2 Subnet number 8. 1. 0. 0 130. 4. 102. 0 199. 1. 1. 0 130. 4. 100. 0 199. 1. 1. 96 1 st valid IP addr. 8. 1. 0. 1 130. 4. 102. 1 199. 1. 1. 1 130. 4. 100. 1 199. 1. 1. 97 Broadcast addr. 8. 1. 255 130. 4. 102. 255 199. 1. 1. 255 130. 4. 103. 255 199. 1. 1. 127 Last valid addr. 8. 1. 255. 254 130. 4. 102. 254 199. 1. 1. 254 130. 4. 103. 254 199. 1. 1. 126
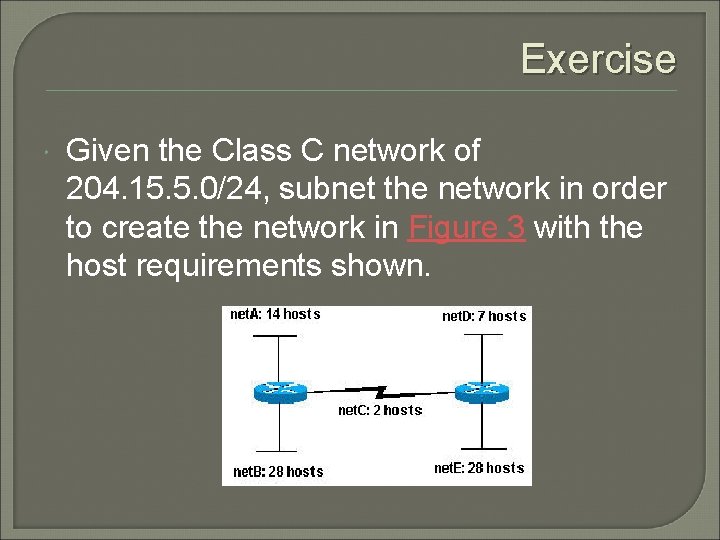
Exercise Given the Class C network of 204. 15. 5. 0/24, subnet the network in order to create the network in Figure 3 with the host requirements shown.

Exercise net. A: must support 14 hosts net. B: must support 28 hosts net. C: must support 2 hosts net. D: must support 7 hosts net. E: must support 28 host VLSM!!!
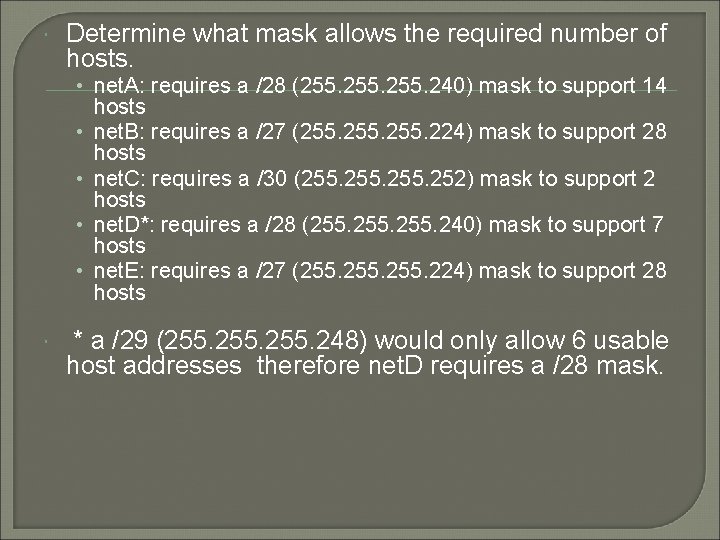
Determine what mask allows the required number of hosts. • net. A: requires a /28 (255. 240) mask to support 14 • • hosts net. B: requires a /27 (255. 224) mask to support 28 hosts net. C: requires a /30 (255. 252) mask to support 2 hosts net. D*: requires a /28 (255. 240) mask to support 7 hosts net. E: requires a /27 (255. 224) mask to support 28 hosts * a /29 (255. 248) would only allow 6 usable host addresses therefore net. D requires a /28 mask.
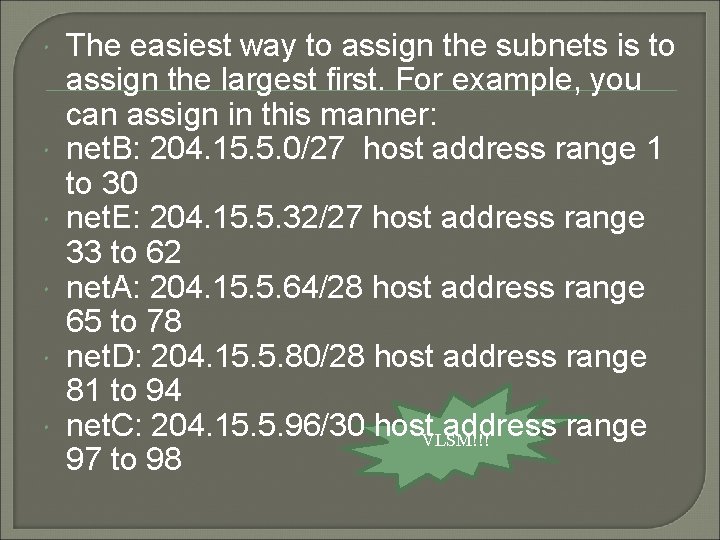
The easiest way to assign the subnets is to assign the largest first. For example, you can assign in this manner: net. B: 204. 15. 5. 0/27 host address range 1 to 30 net. E: 204. 15. 5. 32/27 host address range 33 to 62 net. A: 204. 15. 5. 64/28 host address range 65 to 78 net. D: 204. 15. 5. 80/28 host address range 81 to 94 net. C: 204. 15. 5. 96/30 host address range VLSM!!! 97 to 98
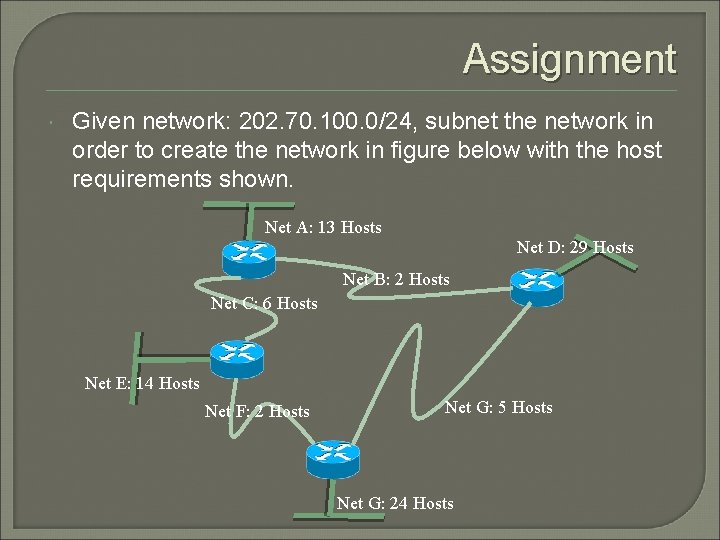
Assignment Given network: 202. 70. 100. 0/24, subnet the network in order to create the network in figure below with the host requirements shown. Net A: 13 Hosts Net D: 29 Hosts Net B: 2 Hosts Net C: 6 Hosts Net E: 14 Hosts Net F: 2 Hosts Net G: 5 Hosts Net G: 24 Hosts
IP Address Space Originally, 3 Classes • A, B, C Problem • Classes too rigid (C too small, B too big) Solution • Subnetting • Classless Interdomain Routing (CIDR)
IP Routing Routers are not omniscient • Next-Hop Hop-by-Hop Thus IP makes no guarantees • except to try it’s best (”Best Effort”) • packets may get there out of order, garbled, duplicated • may not get there at all! • Unreliable datagram service
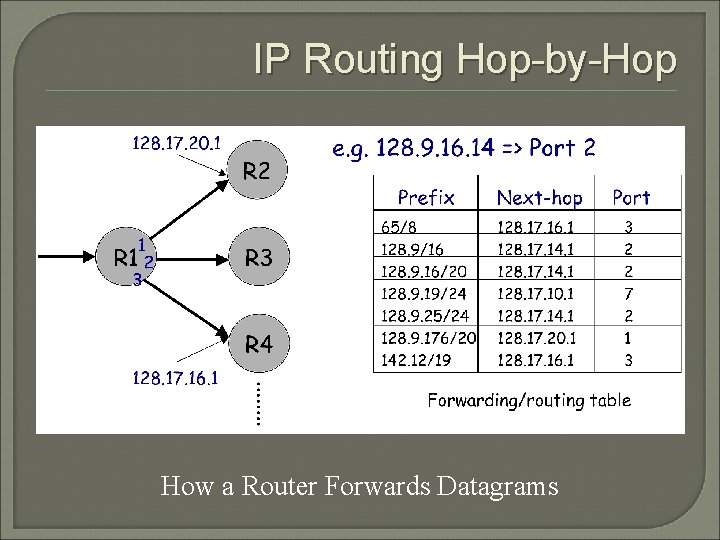
IP Routing Hop-by-Hop How a Router Forwards Datagrams
Classless Interdomain Routing (CIDR) 0 232 -1
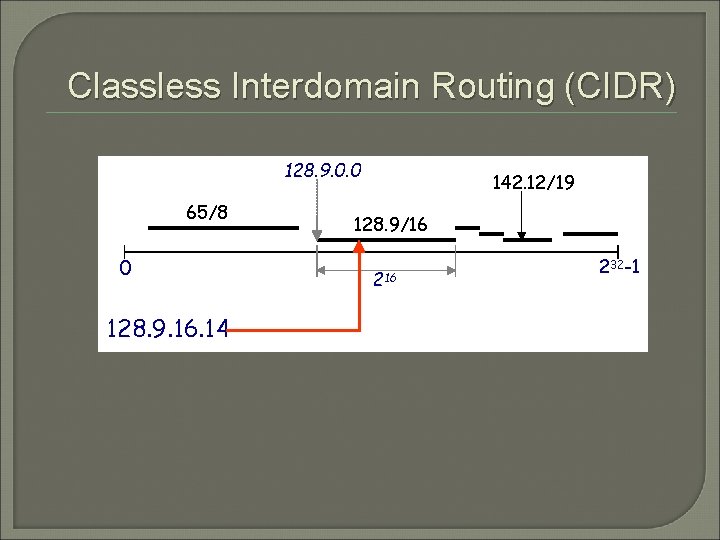
Classless Interdomain Routing (CIDR) 128. 9. 0. 0 65/8 0 128. 9. 16. 14 142. 12/19 128. 9/16 232 -1
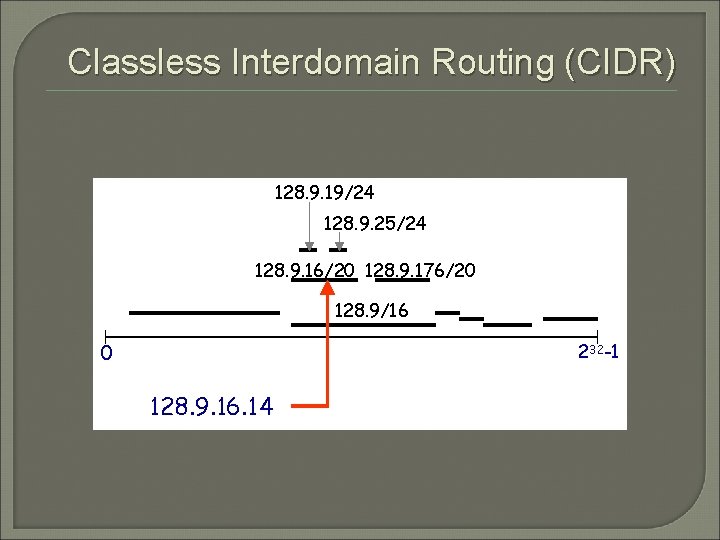
Classless Interdomain Routing (CIDR) 128. 9. 19/24 128. 9. 25/24 128. 9. 16/20 128. 9. 176/20 128. 9/16 0 232 -1 128. 9. 16. 14
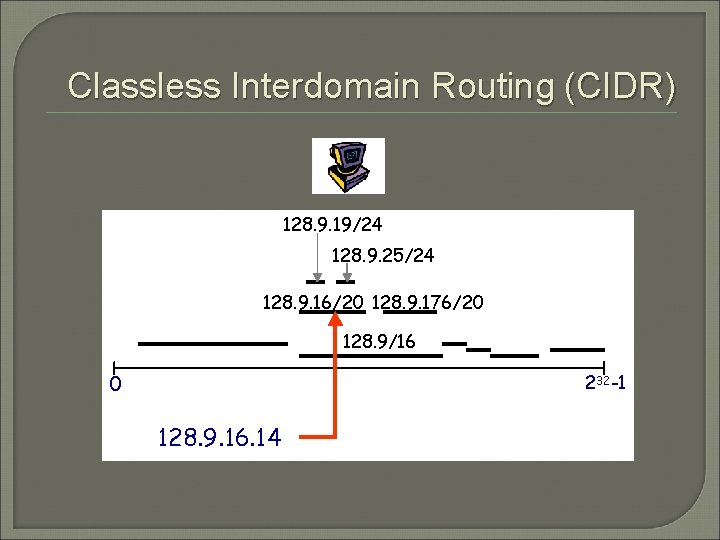
Classless Interdomain Routing (CIDR) 128. 9. 19/24 128. 9. 25/24 128. 9. 16/20 128. 9. 176/20 128. 9/16 0 232 -1 128. 9. 16. 14
Transmission Control Protocol
Characteristics Connection-Oriented Reliable Byte-Stream Flow Control (aka Congestion Control)
Three Phases Establish Connection Data Transfer Terminate Connection
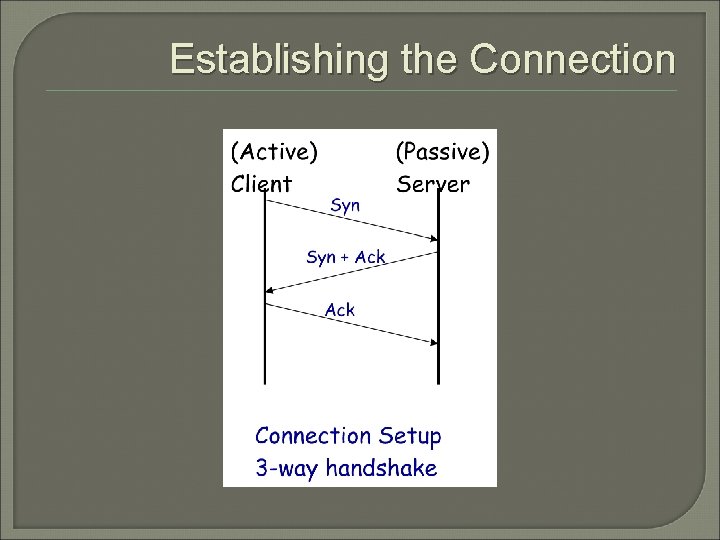
Establishing the Connection
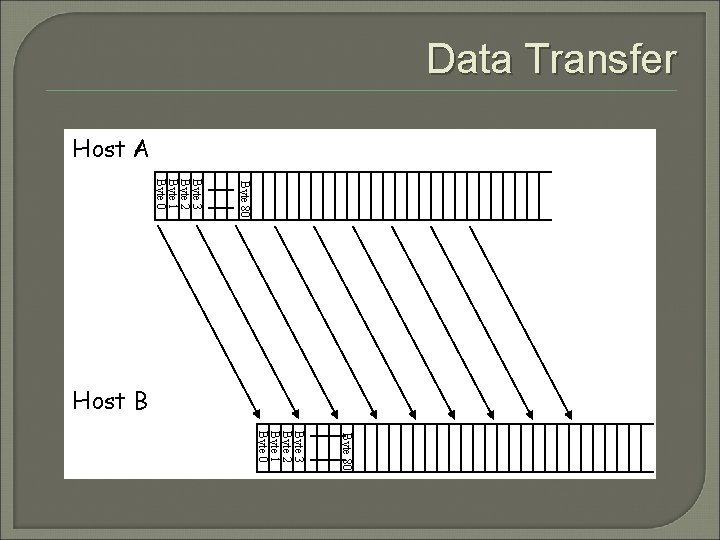
Data Transfer Host A Byte 80 Byte 3 Byte 2 Byte 1 Byte 0 Host B Byte 80 Byte 3 Byte 2 Byte 1 Byte 0
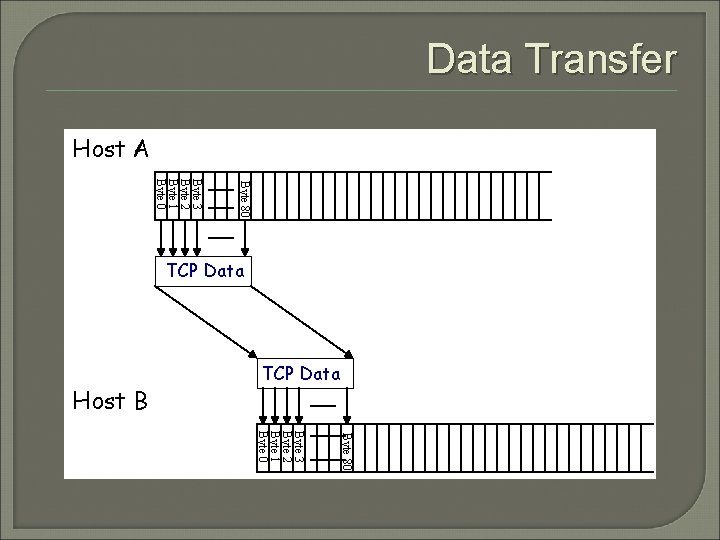
Data Transfer Host A TCP Data Host B Byte 80 Byte 3 Byte 2 Byte 1 Byte 0 TCP Data Byte 80 Byte 3 Byte 2 Byte 1 Byte 0
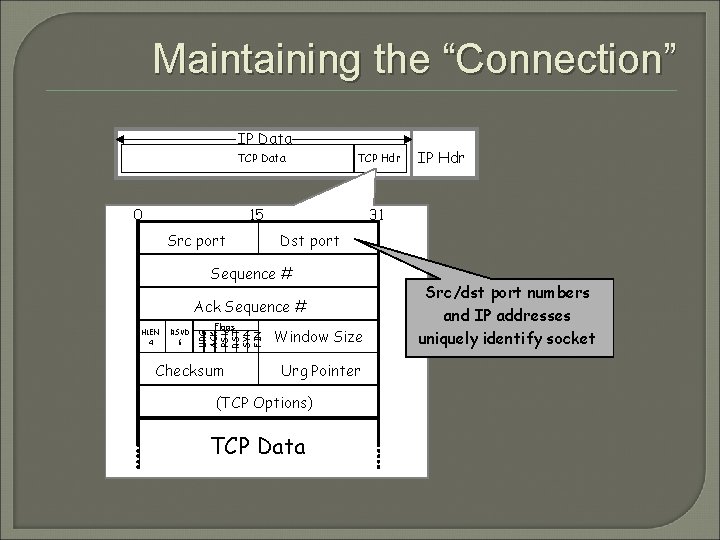
Maintaining the “Connection” IP Data TCP Data 0 TCP Hdr 15 Src port 31 Dst port Sequence # Ack Sequence # RSVD 6 Flags URG ACK PSH RST SYN FIN HLEN 4 Checksum IP Hdr Window Size Urg Pointer (TCP Options) TCP Data Src/dst port numbers and IP addresses uniquely identify socket
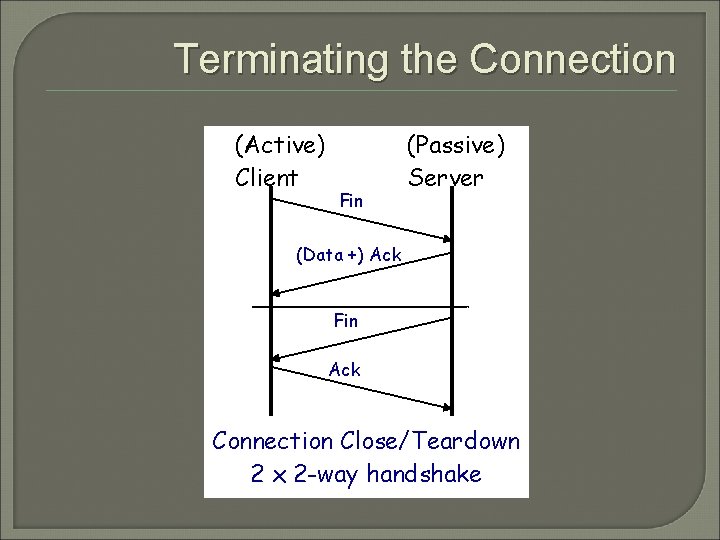
Terminating the Connection (Active) Client Fin (Passive) Server (Data +) Ack Fin Ack Connection Close/Teardown 2 x 2 -way handshake
Connection-Oriented Reliable Byte-Stream Flow Control (aka Congestion Control)
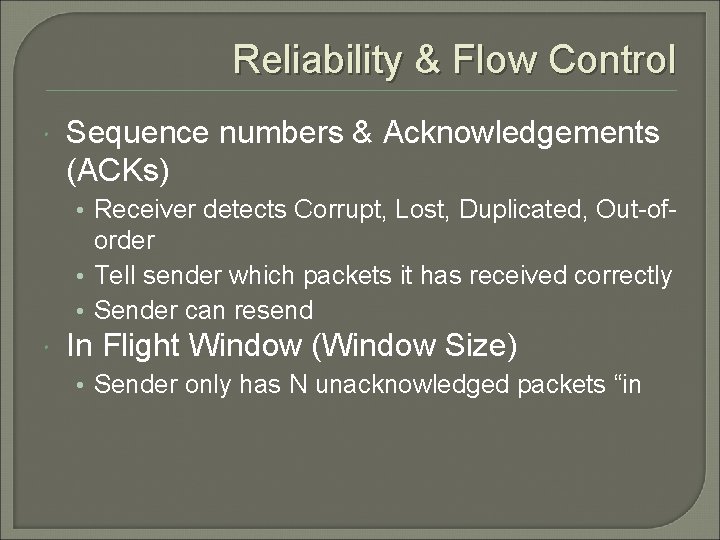
Reliability & Flow Control Sequence numbers & Acknowledgements (ACKs) • Receiver detects Corrupt, Lost, Duplicated, Out-of- order • Tell sender which packets it has received correctly • Sender can resend In Flight Window (Window Size) • Sender only has N unacknowledged packets “in
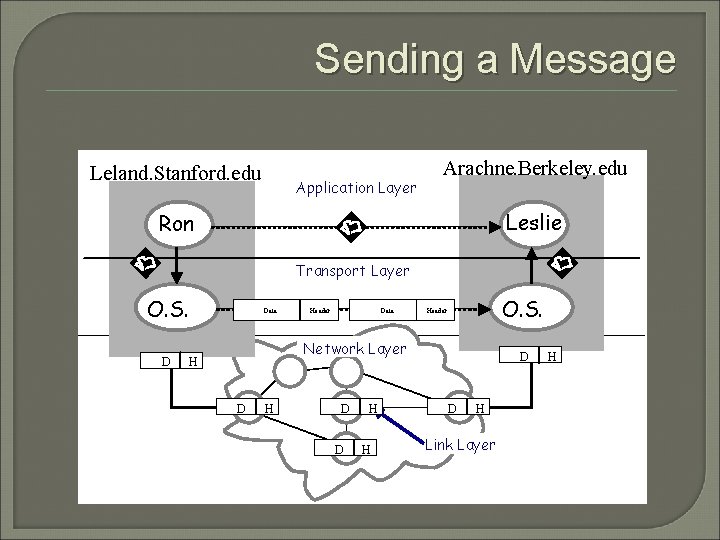
Sending a Message Leland. Stanford. edu Application Layer Arachne. Berkeley. edu Leslie Ron Transport Layer O. S. D Data Header Data O. S. Header Network Layer H D D H Link Layer H
UDP
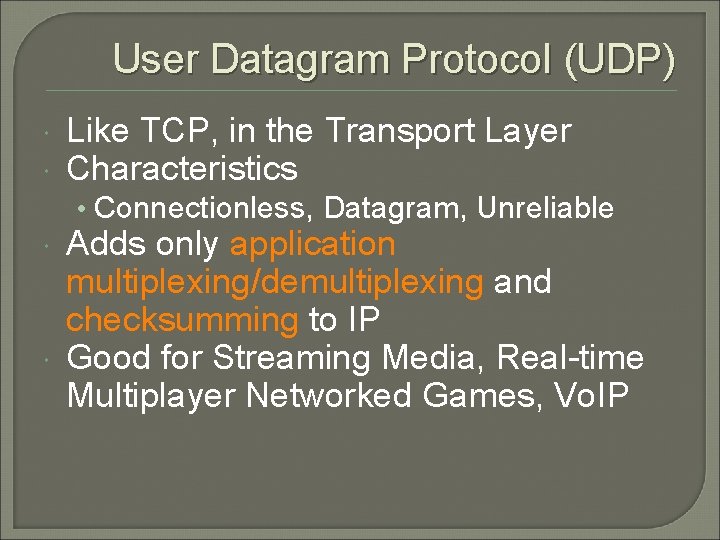
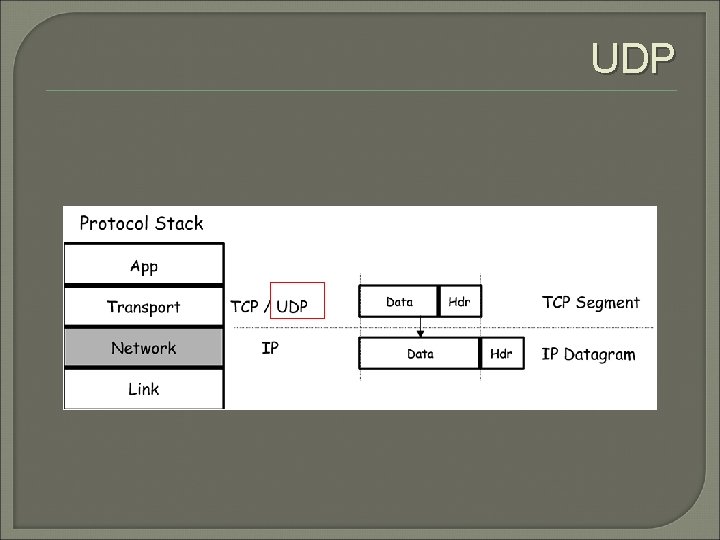
User Datagram Protocol (UDP) Like TCP, in the Transport Layer Characteristics • Connectionless, Datagram, Unreliable Adds only application multiplexing/demultiplexing and checksumming to IP Good for Streaming Media, Real-time Multiplayer Networked Games, Vo. IP
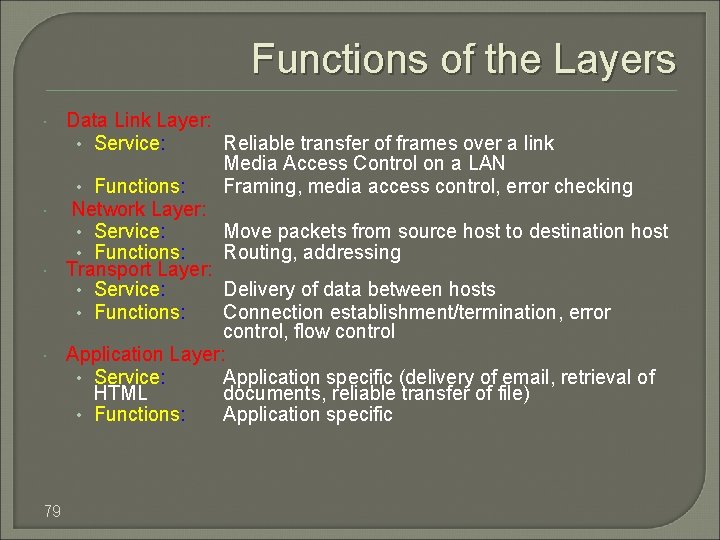
Functions of the Layers 79 Data Link Layer: • Service: Reliable transfer of frames over a link Media Access Control on a LAN • Functions: Framing, media access control, error checking Network Layer: • Service: Move packets from source host to destination host • Functions: Routing, addressing Transport Layer: • Service: Delivery of data between hosts • Functions: Connection establishment/termination, error control, flow control Application Layer: • Service: Application specific (delivery of email, retrieval of HTML documents, reliable transfer of file) • Functions: Application specific
Summary IP is the basis of Internetworking TCP builds on top of IP adds reliable, congestion-controlled, connection-oriented byte-stream. UDP builds on top of IP allows access to IP functionality
- Slides: 80