Taxonomy of Computer Security Breaches CSH 6 Chapter
Taxonomy of Computer Security Breaches CSH 6 Chapter 8 “Using a Common Language for Computer Security Incident Information” John D. Howard 1 Copyright © 2020 M. E. Kabay. All rights reserved.
Topics Ø Ø Ø 2 What is a Common Descriptive Language? What is a Taxonomy? Why a Language/Taxonomy for Computer Crime? The Model as a Whole Actions Targets CSH 6 Chapter 8: Events “Using a Common Language for Vulnerability Computer Security Incident Information” Tool Unauthorized Result Objectives Attackers Copyright © 2020 M. E. Kabay. All rights reserved.
What is a Common Descriptive Language? Ø Set of terms that experts agree on in a field Ø Clear definitions to the extent possible q. Precise q. Unambiguous q. Easy to determine in the field Ø A common language does not necessarily imply a causal or structural model Ø Provides means of communication among experts Ø Supports analysis 3 Copyright © 2020 M. E. Kabay. All rights reserved.
What is a Taxonomy? Ø Structure relating terms in the common language Ø Permits classification of phenomena Ø Expresses (a) model(s) of the underlying phenomena Ø Supports hypothesis-building Ø Supports collection and analysis of statistical information 4 Copyright © 2020 M. E. Kabay. All rights reserved.
Why a Language/Taxonomy for Computer Crime? 5 Ø Field of information assurance growing q. More people q. Less common experience q. Growing variability in meaning of terms Ø What’s wrong with ambiguous terminology? q. Can cause confusion – talking at cross-purposes q. Can mislead investigators and others q. Wastes time in clarification time after time q. Interferes with data-gathering q. Makes comparisons and tests difficult or impossible Copyright © 2020 M. E. Kabay. All rights reserved.
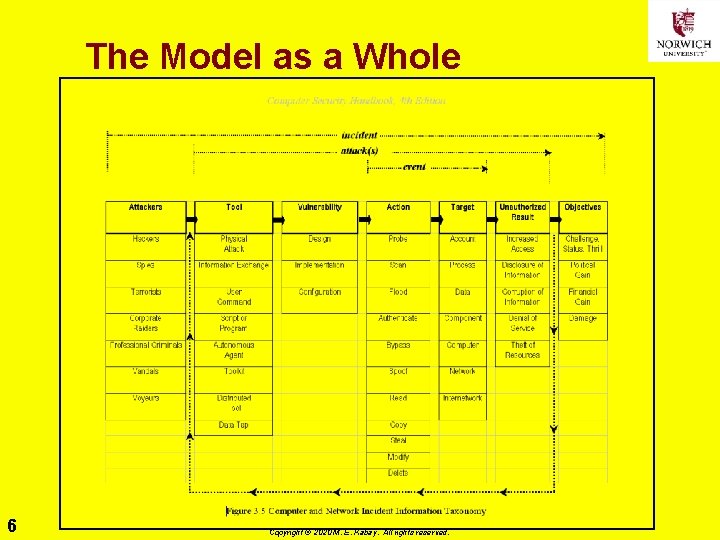
The Model as a Whole 6 Copyright © 2020 M. E. Kabay. All rights reserved.
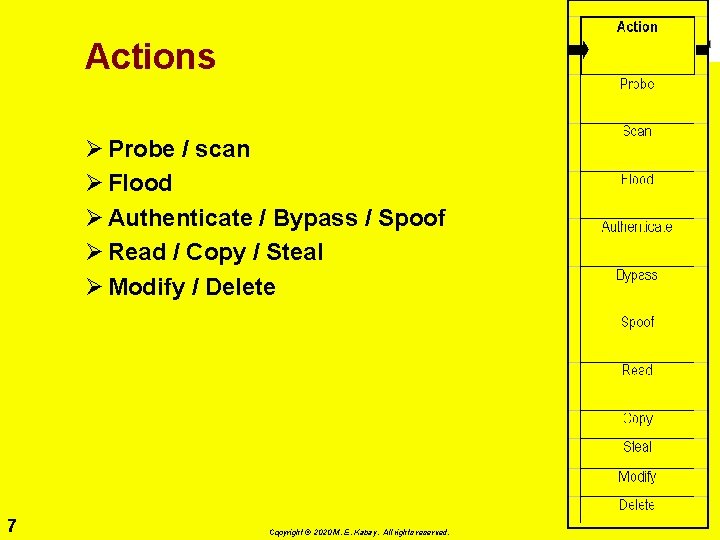
Actions Ø Probe / scan Ø Flood Ø Authenticate / Bypass / Spoof Ø Read / Copy / Steal Ø Modify / Delete 7 Copyright © 2020 M. E. Kabay. All rights reserved.
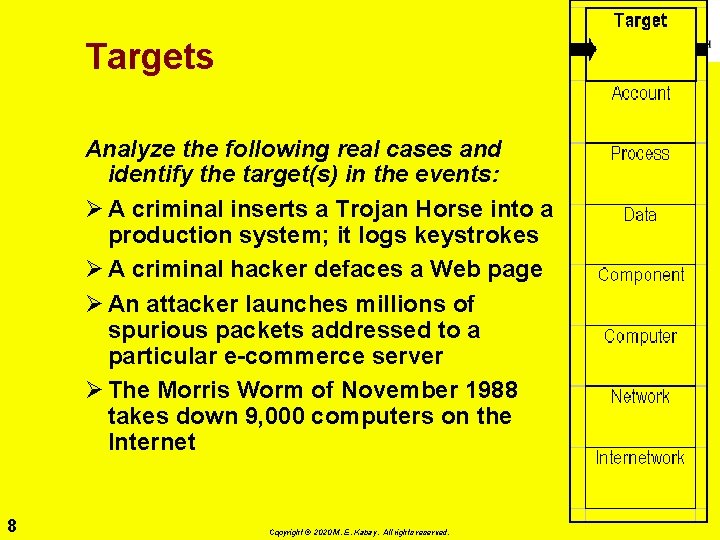
Targets Analyze the following real cases and identify the target(s) in the events: Ø A criminal inserts a Trojan Horse into a production system; it logs keystrokes Ø A criminal hacker defaces a Web page Ø An attacker launches millions of spurious packets addressed to a particular e-commerce server Ø The Morris Worm of November 1988 takes down 9, 000 computers on the Internet 8 Copyright © 2020 M. E. Kabay. All rights reserved.
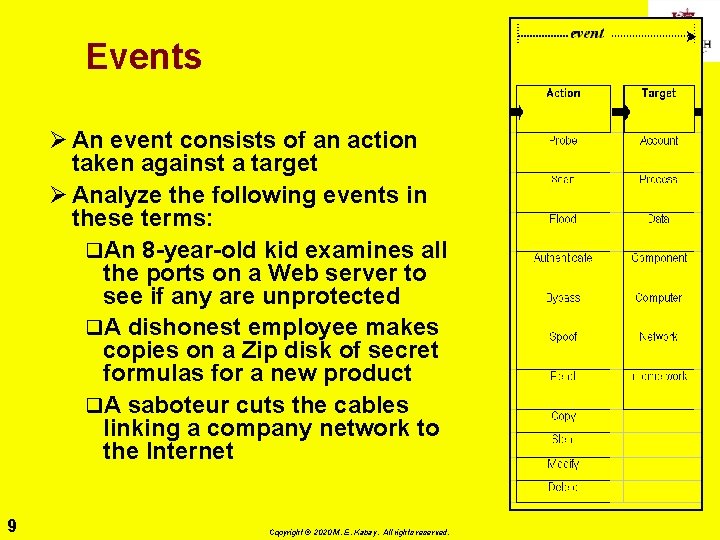
Events Ø An event consists of an action taken against a target Ø Analyze the following events in these terms: q. An 8 -year-old kid examines all the ports on a Web server to see if any are unprotected q. A dishonest employee makes copies on a Zip disk of secret formulas for a new product q. A saboteur cuts the cables linking a company network to the Internet 9 Copyright © 2020 M. E. Kabay. All rights reserved.
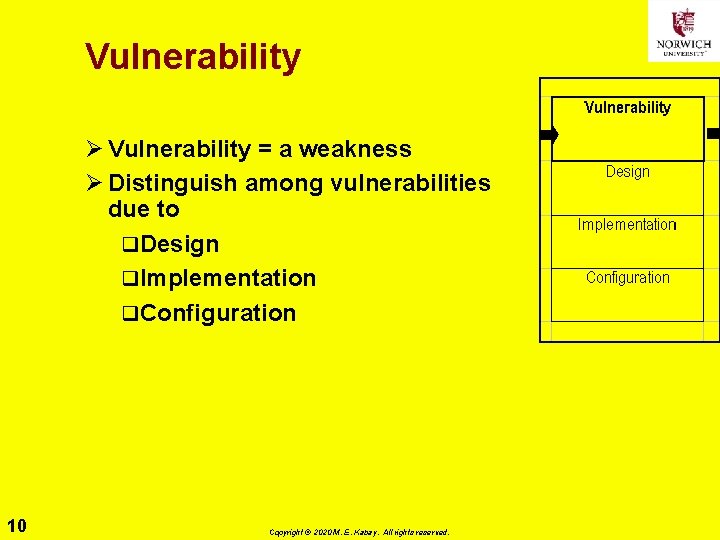
Vulnerability Ø Vulnerability = a weakness Ø Distinguish among vulnerabilities due to q. Design q. Implementation q. Configuration 10 Copyright © 2020 M. E. Kabay. All rights reserved.
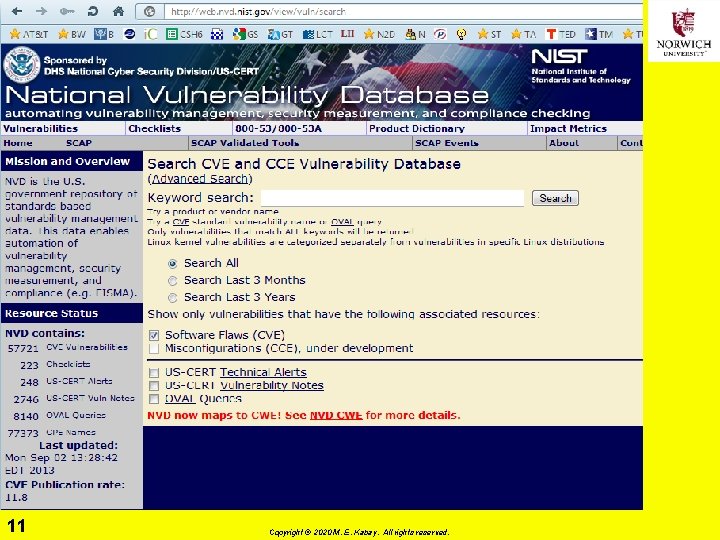
Common Vulnerabilities and Exposures Dictionary 11 Copyright © 2020 M. E. Kabay. All rights reserved.
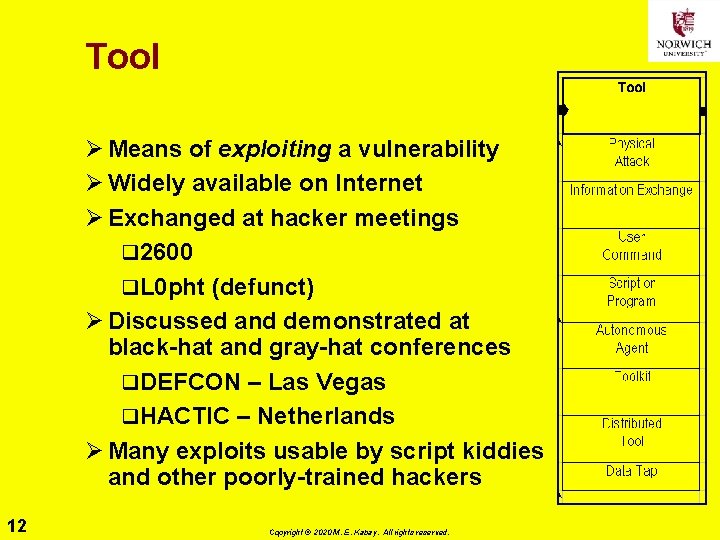
Tool Ø Means of exploiting a vulnerability Ø Widely available on Internet Ø Exchanged at hacker meetings q 2600 q. L 0 pht (defunct) Ø Discussed and demonstrated at black-hat and gray-hat conferences q. DEFCON – Las Vegas q. HACTIC – Netherlands Ø Many exploits usable by script kiddies and other poorly-trained hackers 12 Copyright © 2020 M. E. Kabay. All rights reserved.
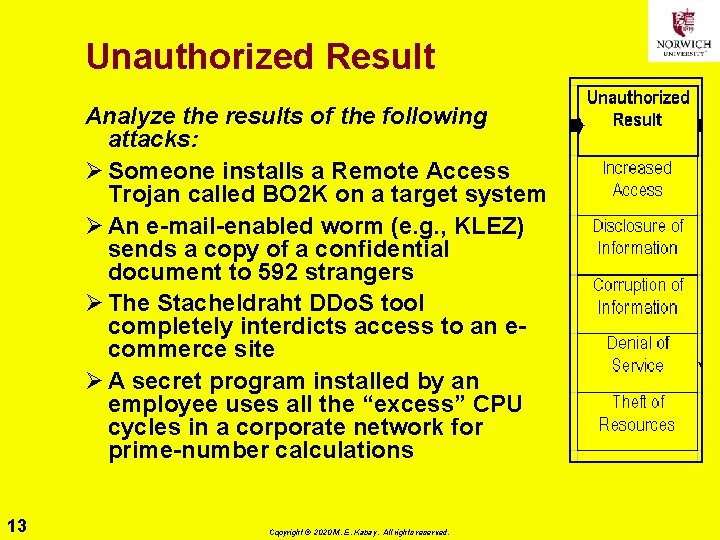
Unauthorized Result Analyze the results of the following attacks: Ø Someone installs a Remote Access Trojan called BO 2 K on a target system Ø An e-mail-enabled worm (e. g. , KLEZ) sends a copy of a confidential document to 592 strangers Ø The Stacheldraht DDo. S tool completely interdicts access to an ecommerce site Ø A secret program installed by an employee uses all the “excess” CPU cycles in a corporate network for prime-number calculations 13 Copyright © 2020 M. E. Kabay. All rights reserved.
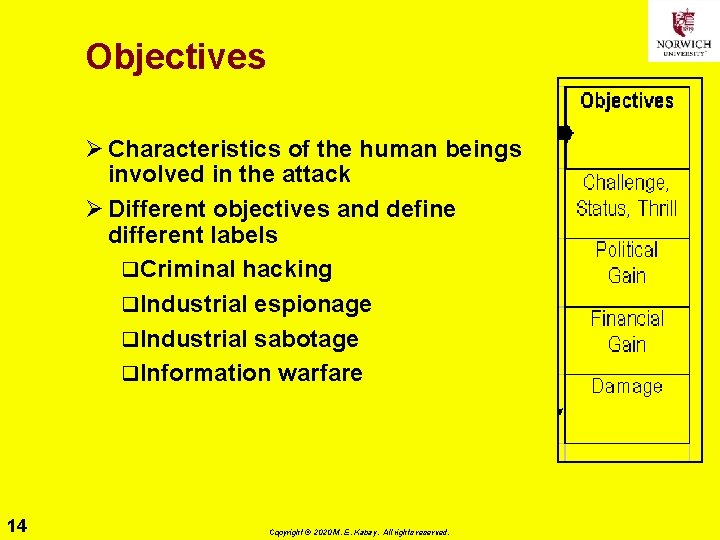
Objectives Ø Characteristics of the human beings involved in the attack Ø Different objectives and define different labels q. Criminal hacking q. Industrial espionage q. Industrial sabotage q. Information warfare 14 Copyright © 2020 M. E. Kabay. All rights reserved.
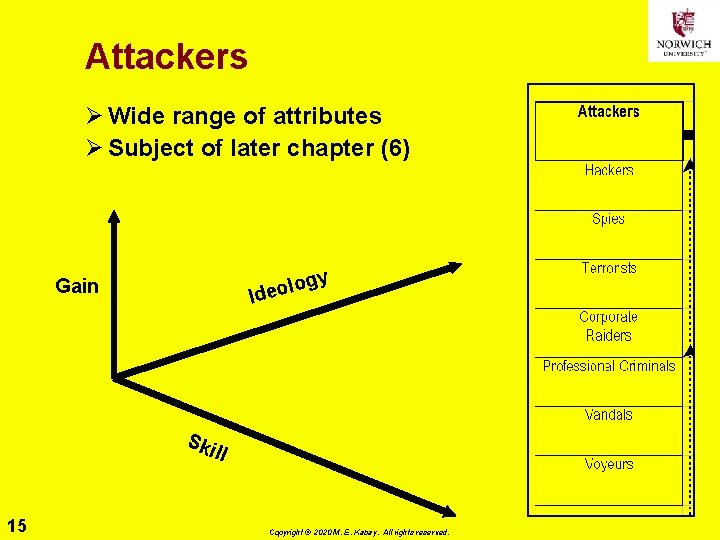
Attackers Ø Wide range of attributes Ø Subject of later chapter (6) gy lo Ideo Gain Ski ll 15 Copyright © 2020 M. E. Kabay. All rights reserved.

The Model as a Whole (again) 16 Copyright © 2020 M. E. Kabay. All rights reserved.
Now go and study 17 Copyright © 2020 M. E. Kabay. All rights reserved.
- Slides: 17