TAM STE Series 2008 Web SEAL SSO Session
TAM STE Series 2008 - Web. SEAL SSO, Session 1 Presented by: Andrew Quap Web. SEAL SSO, Session 1 08/2008 © 2008 IBM Corporation
Itinerary for Web. SEAL single-signon (SSO) § Simple and Protected GSSAPI Negotiation Mechanism (SPNEGO) § CDSSO § e. CDSSO 2 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
SPNEGO § Generic Security Service Application Program Interface (GSS-API) – “an application programming interface for programs to access security services. “-wikipedia – RFC 2478 – Describes a set of standard API’s § GSS-API can implement any security protocol – GSS-API implementation of Kerberos is best known 3 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
SPNEGO § Microsoft started to use SPNEGO in IE 5. 01 and IIS 5. 0 as an authentication extension – wikipedia – Requires the use of AD server acting as KDC – Nowadays Microsoft markets the use of NTLM instead of SPNEGO – Used to provide desktop single sign-on into IIS server § TAM Web. SEAL SPNEGO allows users to SSO into Web. SEAL 4 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
Kerberos basics § MIT Kerberos v 5 § RFC 1510 – Kerberos tickets – Kerberos Realm – KDC (Key Distribution Center) • Server that issues Kerberos tickets • Typically listen on port 88 § For UNIX implementations “krb 5. conf” contains Kerberos client configuration 5 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
Kerberos basics § keytab file – Allows a service (ie a server) to automatically authenticate into Kerberos realm § ‘kinit’ command – Command used to authenticate a user into a Kerberos realm • Input User/password • Or input keytab file 6 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
SPNEGO § SPNEGO uses GSS-API Kerberos implementation § Web. SEAL and Web. PI use the "HTTP Negotiate" extension defined by Microsoft. § Client Web Browser does HTTP request to Web. SEAL. § Web. SEAL returns HTTP 401 (Unauthorized) status and the following header: "WWW-Authenticate: Negotiate". § Client chooses a Service Principal Name for the host and calls Initialize. Security. Context() to generate a Neg. Token. Init token. 7 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
SPNEGO § Client resends the request with the following header: "Authorization: Negotiate <base 64 encoding>" (e. g. Authorization: Negotiate YIIGUQY<remainder of base 64 encoded string>). § Web. SEAL decodes the Neg. Token. Init token. § Web. SEAL verifies the encryption type and authenticates using gss_accept_sec_context. § The next step depends on what the gss_accept_sec_context function returns. 8 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
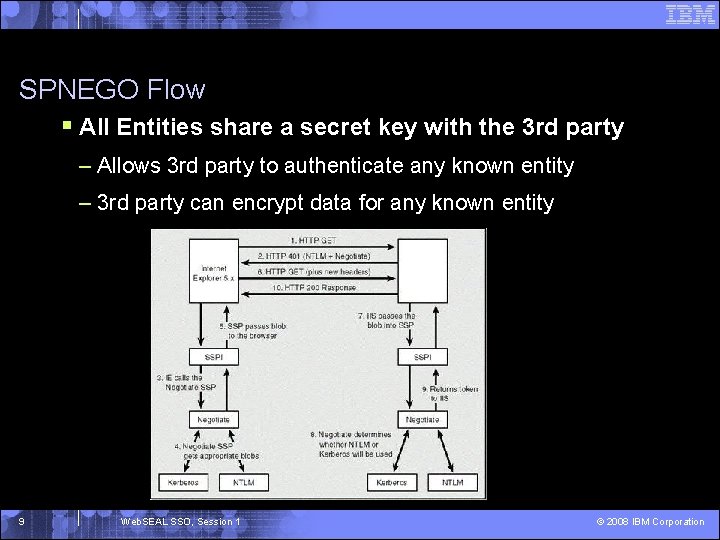
SPNEGO Flow § All Entities share a secret key with the 3 rd party – Allows 3 rd party to authenticate any known entity – 3 rd party can encrypt data for any known entity 9 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
Web. SEAL SPNEGO configuration and setup § AD server typically is configured as TAM registry – Can have separate LDAP server, but AD and LDAP server must be user synchronized § Web. SEAL administration document, v 6, on SPNEGO is very detailed. 10 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
Web. SEAL SPNEGO configuration and setup § Web. SEAL installed on Windows OS – ‘ktpass’ command creates Server Principal Names (SPN’s) in AD server – Setup Web. SEAL service to authenticate as new SPN – The Web. SEAL server must be configured as a client into the AD domain 11 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
Web. SEAL SPNEGO configuration and setup § Web. SEAL installed on UNIX setup – Requires keytab file generated from ‘ktpass’ command – Modify Web. SEAL configuration file to include principal name and keytab file – Setup Kerberos client on Web. SEAL machine 12 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
Web. SEAL SPNEGO configuration and setup § Supports load balanced Web. SEAL setup – Web. SEAL admin guide details steps needed for basic setup, case does matter – Forward and reverse lookup must match on the Web. SEAL machine for the load balanced hostname – Web. SEAL on windows • The server instances must all be running under the same ID – Web. SEAL on UNIX • The servers must all share the same keytab 13 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
Web. SEAL SPNEGO problem determination § Invoke ‘bst’ trace or per-process trace § Determine if Kerberos error – Review Kerberos client config in ‘krb 5. conf’ § UNIX – Ensure keytab file is valid • Use ‘kinit’ test § Windows – Ensure Web. SEAL service authenticates as user created during ‘ktpass’ command 14 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
Web. SEAL SPNEGO typical issues § TAM 6. 0 provides SPNEGO problem determination guide § Web. SEAL will not start – Invoke per-process tracing • Look for Kerberos error – Example of error 15 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
Web. SEAL SPNEGO typical issues § Web. SEAL starts but user SSO fails – Invoke ‘bst’ tracing – Invoke network trace from end user’s browser • Look for AD server response – Check ‘krb 5. conf’ • Make sure AD domain is defined or default • If Web. SEAL domain is different from AD domain make sure both domains are mapped – Ensure trusted site is entered in IE browser 16 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
Web. SEAL SPNEGO typical issues § Multiple SPN’s mapped into Web. SEAL AD account – Issue only occurs when Web. SEAL is installed on UNIX – Must use ‘-map. Op set’ option for ktpass command. – When you use ‘–map. Op set’ which is required to create a keytab it removes the other SPN’s that existed on the account – One account per SPN when using Unix 17 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
Web. SEAL SPNEGO limitations § Does not provide SSO into a IIS backend server § If SPNEGO fails, fallback using Web. SEAL forms login requires IE fix – Web. SEAL’s NTLM error page can be modified for ‘pkmslogin’ – Use E-community SSO to login user § Web. SEAL cannot handle NTLM responses from IE § SPNEGO clients cannot log out 18 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
Kerberos Junctions § Not SSO to Web. SEAL, but SSO from Web. SEAL to IIS 19 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
SPNEGO questions 20 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
Cross Domain Single Signon (CDSSO) § “A mechanism to transfer a user credentials between servers in different domains-”Web. SEAL administration guide § Uses an encrypted token to transfer an user identity – “token creation” creates and encrypts the token – “token consumption” decrypts the token § Can use CDSSO between TAM Web plug-in and Web. SEAL 21 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
Cross Domain Single Sign-on (CDSSO) § Supports cross-domain mapping framework (CDMF) – Allows additional attributes to be encrypted in token in addition to user’s identity – Provides the ability to customized CDSSO using TAM Capi’s 22 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
CDSSO configuration and setup § Configuring CDSSO token create functionality – The following procedures are appropriate for the initial Web. SEAL server • Enable Web. SEAL to generate CDSSO tokens (cdsso-create). • Configure the built-in token creation module (sso-create). • Create the key file used to encode and decode the token. Copy the key file to all appropriate participating servers ([cdsso-peers] stanza). • Configure the token time stamp (authtoken-lifetime) • Configure the token label (cdsso-argument). • Create the CDSSO HTML link (/pkmscdsso? destination-URL). 23 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
CDSSO setup and configuration § Configuring CDSSO token consume functionality – The following procedures are appropriate for the destination Web. SEAL server: • Enable Web. SEAL to consume CDSSO tokens (cdsso-auth) for authentication. • Configure the built-in token consumption module (ssoconsume). • Assign the appropriate key file ([cdsso-peers] stanza). • Configure the token time stamp (authtoken-lifetime) • Configure the token label (cdsso-argument). 24 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
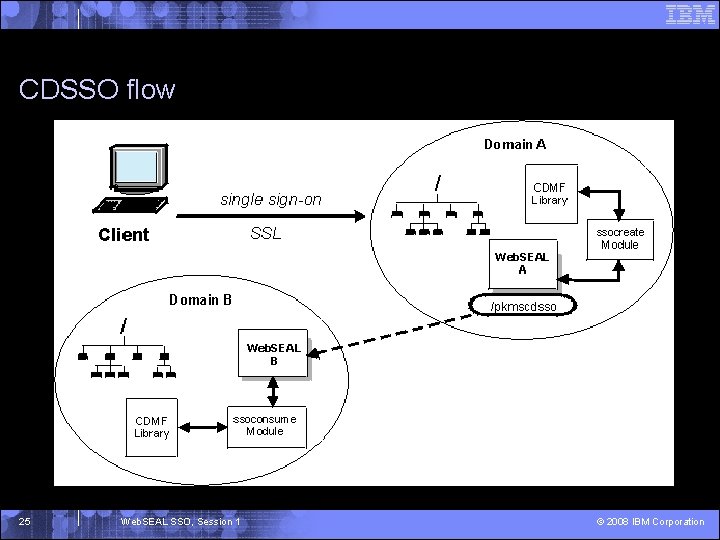
CDSSO flow 25 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
CDSSO requirements § “All Web. SEAL servers participating in CDSSO must have machine times synchronized. ”Web. SEAL administration guide § “For CDSSO to function successfully, each participating Web. SEAL server must reveal its fully qualified host name to the other participating servers in the cross-domain environment. ”Web. SEAL administration guide 26 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
CDSSO requirements § “Do not reuse key pairs (used to encrypt and decrypt token data) generated for a specific CDSSO environment in any other CDSSO environments. ” –Web. SEAL administration guide 27 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
CDSSO problem determination § Determine if error occurs during “token creation” or “token consumption” § Enable specific CDSSO tracing pdweb. wan. cdsso § Enable ‘pdweb. snoop’ trace § Analyze ‘msg__Web. SEALd-<instance name>. log’ § Is customer using default libraries 28 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
CDSSO typical issues § Time issues different timezones not setup correctly or skew § Mismatched keys § CDSSO peers incorrectly set up 29 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
CDSSO limitations § UTF-8 encoding for strings § Providing compatibility for tokens across Web. SEAL versions 30 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
CDSSO questions 31 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
E-community Single Sign-on (ECSSO) § Concept is similar to CDSSO § Master authentication server (MAS) provides single point for authentication – Web. SEAL and Web. PI provides MAS functionality § Domain-specific cookies are used to identify the server that can provide "vouch for" services § The e-community implementation allows for "local" authentication in remote domains 32 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
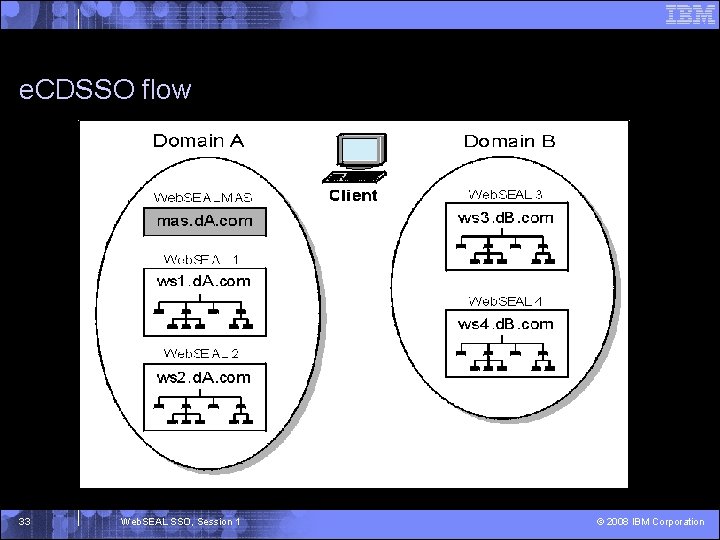
e. CDSSO flow 33 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
ECSSO setup and configuration § Enabling and Disabling e-Community Members § Including credential attributes in the vouch-for tokens § Specify the sso-create and sso-consume libraries 34 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
ECSSO problem determination § Determine if error occurs during “token creation” or “token consumption” § Enable ‘pdweb. snoop’ trace on servers involved § Analyze ‘msg__Web. SEALd-<instance name>. log 35 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
ECSSO typical issues § Time issues different timezones not setup correctly or skew § Mismatched keys § ECDSSO domains incorrectly set up 36 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
ECSSO limitations § One server, or group, provides authentication for a group of servers – Each server can still do local authentication 37 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
e. CDSSO questions 38 Web. SEAL SSO, Session 1 © 2008 IBM Corporation
- Slides: 38