TAKING THE ARCHERS FOR GRANTED EMERGING THREATS TO

- Slides: 10
TAKING THE ARCHERS FOR GRANTED: EMERGING THREATS TO NUCLEAR WEAPONS SYSTEMS PONI 2016 Winter Conference Center for Strategic and International Studies Washington, DC Jesse T Wasson, Ph. D Systems Planning and Analysis, Inc. 2001 N. Beauregard St Alexandria, VA 22310 jwasson@spa. com Christopher E. Bluesteen Systems Planning and Analysis, Inc. 2001 N. Beauregard St Alexandria, VA 22310 cbluesteen@spa. com ***The views presented here are the authors’ alone and do not represent those of Systems Planning and Analysis, Inc. or its clients***
A QUICK THOUGHT EXPERIMENT… • F-35 A Joint Strike Fighter is expected to be nuclear certified in 2024 (Kristensen, 2016) • According to recent GAO and Do. D DOT&E reports though, the program has experienced serious software problems raising doubts about this timeline • Imagine for a minute that these problems were not self-inflicted. Imagine they were caused by a state actor intending to either compromise one or an entire F-35 variant - Why would an adversary do this? - Would they get caught? Would they want to get caught? What would be the consequences? - How long and at what cost would it take the U. S. to remedy? - Would this cause the U. S. and allies to have less confidence in the reliability of its deterrent? What if a submarine or missile silo also experienced weapon system failures? - Could this alter U. S. foreign policy decisions? 2
NUCLEAR WEAPONS & CYBERSECURITY • Current views on this issue tend to fall into one of three camps that focus on the weapons themselves and command control: - Unhackable - Anything is possible - Don’t know • Less attention paid to nuclear weapon delivery systems • Requires far more research and strategic thought 3
WHY DELIVERY SYSTEMS? • The arrows are useless without the archers • Larger attack surface than the weapons themselves: submarinelaunched ballistic missiles, land-ballistic missiles, fighters, and bombers • Less of an “air gap” than the actual weapons; computerized and seminetworked systems with numerous modernization efforts underway - Complex technology upgrades with greater networking of horizontal and vertical systems - Reliance on commercial off-the-shelf (COTS) components and distributed supply chains - Need for more frequent software / firmware updates • Cybersecurity of Do. D weapon systems questioned (Do. D OT&E, 2014; Defense Science Board, 2013) 4
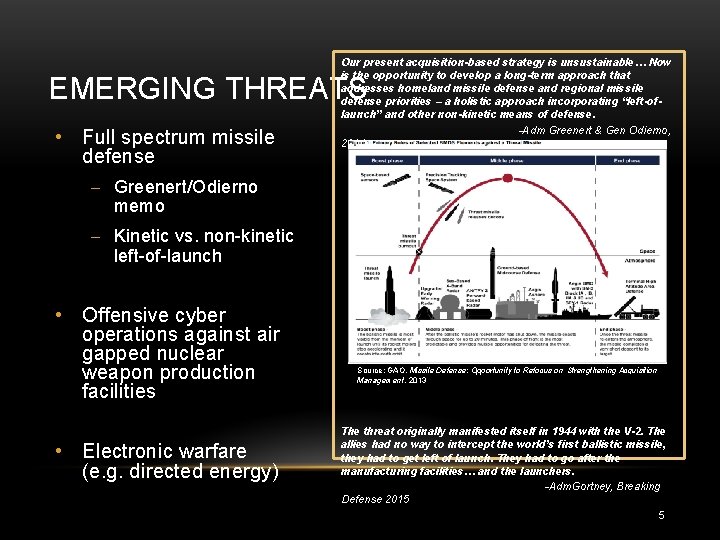
Our present acquisition-based strategy is unsustainable… Now is the opportunity to develop a long-term approach that addresses homeland missile defense and regional missile defense priorities – a holistic approach incorporating “left-oflaunch” and other non-kinetic means of defense. -Adm Greenert & Gen Odierno, 2014 EMERGING THREATS • Full spectrum missile defense - Greenert/Odierno memo - Kinetic vs. non-kinetic left-of-launch • Offensive cyber operations against air gapped nuclear weapon production facilities • Electronic warfare (e. g. directed energy) Source: GAO, Missile Defense: Opportunity to Refocus on Strengthening Acquisition Management, 2013 The threat originally manifested itself in 1944 with the V-2. The allies had no way to intercept the world’s first ballistic missile, they had to get left of launch. They had to go after the manufacturing facilities… and the launchers. -Adm. Gortney, Breaking Defense 2015 5
REASON TO WORRY • Current geopolitical environment - Growing offensive and defensive disparities in nuclear capabilities - Global and regional power struggles - Rise of hybrid warfare • Appeal of non-kinetic left-of launch attacks on nuclear weapon delivery systems - Less risky than C 2 attacks and more versatile than kinetic missile defense - May be done anonymously or with false flags - Victim’s perception of effects likely to be far greater than actual effects - Relatively cost-effective depending on objective 6
SOME NOTIONAL SCENARIOS • Defense: Country X seeks to protect their cities by deterring or mitigating countervalue threats posed by a rogue state. Because of the expense and ineffectiveness of traditional ballistic missile defense they develop a non-kinetic left-of-launch capability. Country X either then anonymously demonstrates this capability to deter adversaries or keeps it dormant until a launch is imminent • Hybrid Warfare: Country Y fears they can no longer maintain a secure second strike capability vis-à-vis another major power. To attrite counter-force threats they develop a non-kinetic left-of-launch missile defense capability and use it anonymously during peace time to cause adversary weapon system tests to fail. Alternatively, they use it during a crisis to show fallibility of adversary’s deterrent and compel restraint • Nuclear War: Country Z develops non-kinetic left-of-launch capability in preparation for possible nuclear with regional rival. Should conflict escalate, they use it to enable a counterforce first strike attack in combination with traditional ballistic missile defense, anti-submarine warfare, strategic weapons, etc. 7
THEORETICAL DISCUSSION • • Deterrence Stability - Capable systems and credible threats essential for deterrence success (Kaufmann, 1956; Zagare & Kilgour, 2004) - Arguments for the destabilizing effect of ballistic missile defense have raged for decades (Snyder, 1961; Brams & Kilgour, 1988; Glaser & Fetter, 2001; Powell, 2003; Quackenbush & Drury, 2011) - Left-of-launch non-kinetic missile defense is potentially a much more dangerous evolution Early results of modeling non-kinetic left-of-launch missile defense capability suggests: - Asymmetric (one-sided) development is destabilizing in most cases - Mutual development may be stabilizing provided its balanced and both sides exaggerate the effectiveness of the other’s capability - There may be a strong incentive for all states to pursue these capabilities, increasing uncertainty/instability along the development path 8

STRATEGIC POLICY IMPLICATIONS • Non-kinetic left-of-launch missile defense is no longer fantasy • More careful thought is needed regarding deterrence and its relationship to emerging missile defense technologies • - Military leaders and policy makers must understand how these “defensive” capabilities can undermine the larger deterrence mission - There is significant risk of further aggravating existing nuclear arms race pressures and fears of preemptive war - Greater transparency is warranted, and perhaps arms control agreements regulating these types of capabilities among nuclear powers A nuclear triad is probably more important now than ever before; reliability and resilience of nuclear weapons systems critical for deterrence stability in the face of these emerging threats 9
SECURITY POLICY IMPLICATIONS • • • Re-think the purpose of U. S. nuclear weapons security - Do. D nuclear weapons security policy is centered on the principal of access denial with billions of dollars spent since 9/11 to improve the physical protection of U. S. weapons - Greater attention must be paid to ensuring the strategic force can meet its deterrence mission Re-think cybersecurity and what it means for the U. S. nuclear deterrent - Information assurance controls are largely aimed at mitigating known technical vulnerabilities - Red team performance-based approaches are required in addition to compliancebased checklists Re-think design of U. S. delivery systems - Modernization efforts bring strong incentives to adopt more integrated and complex technology - Advantages need to be weighed against mission risks early in the design process 10