T110 5140 Network Application Frameworks and XML Web
T-110. 5140 Network Application Frameworks and XML Web Service Security 06. 04. 2009 Sasu Tarkoma Based on slides by Pekka Nikander
Contents n n n n Web service security WS-Security Standard Security contexts SAML XACML Card. Space Open. ID Summary
Web Services Security Requirements n n Protect messaging across domains Convey security information in messages Make security decisions and communicate them between parties Tools at hand u u u WS-Security, XML-Signature SAML XACML Digital certificate validation Content-filtering XML F Filters based on data format (XSD) Filters based on content (XPath) Filters based on integrity (XML Signature)
WS Security I n Web Services Security: SOAP Message Security u u 1. 0 (Oasis Standard 2004) 1. 1 (Oasis Standard 2006) F n End-to-End security u n Headers are decrypted and processed as needed Selective processing u u u n Extensions in: security token support, message attachments and rights management. Some parts are plain text Some are encrypted Some are signed How does it work? u SOAP header carries security information (and other info as well)
WS Security II n n Ability to send security tokens as part of a message, message integrity, and message confidentiality Security model in terms of security tokens combined with digital signatures to protect and authenticate SOAP messages An X. 509 is an example of a signed security token endorsed by a CA. When third party support is not available, receiver may choose to accept the claims in the token based on trust on the entity that sent the message.

Goals n n n Multiple security token formats Multiple trust domains Multiple signature formats Multiple encryption technologies Targeted message content security and not just transport-level security

Non-goals n n n Establishing a security context or authentication mechanism Key derivation Advertisement and exchange of security policy How trust is established or determined Non-repudiation
Message Protection n Integrity mechanism designed to support multiple signatures Uses XML Signature and XML Encryption Syntax and semantics of signatures within a <wsse: Security> element u u n This is the security block in the SOAP header SOAP actor/role attribute is used to target header blocks Security element includes u u Security tokens Information about the use of XML Encryption & Signature in the SOAP header/body/combination
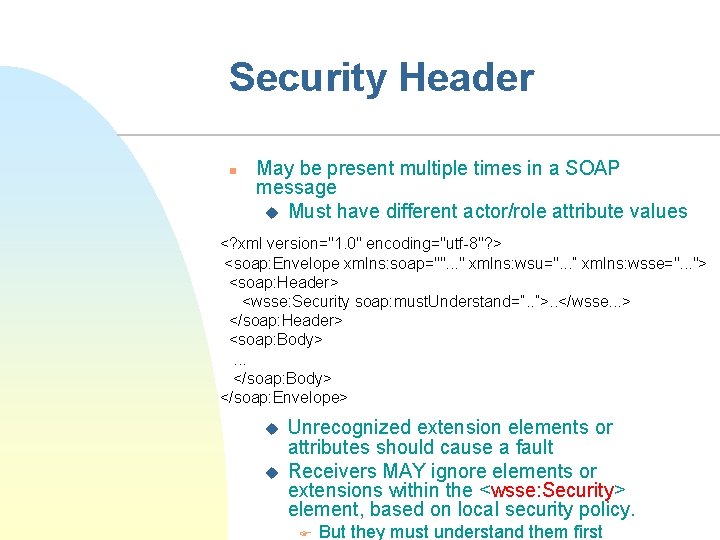
Security Header n May be present multiple times in a SOAP message u Must have different actor/role attribute values <? xml version="1. 0" encoding="utf-8"? > <soap: Envelope xmlns: soap="". . . " xmlns: wsu=". . . ” xmlns: wsse=". . . "> <soap: Header> <wsse: Security soap: must. Understand=”. . ”>. . </wsse. . . > </soap: Header> <soap: Body>. . . </soap: Body> </soap: Envelope> u u Unrecognized extension elements or attributes should cause a fault Receivers MAY ignore elements or extensions within the <wsse: Security> element, based on local security policy. F But they must understand them first
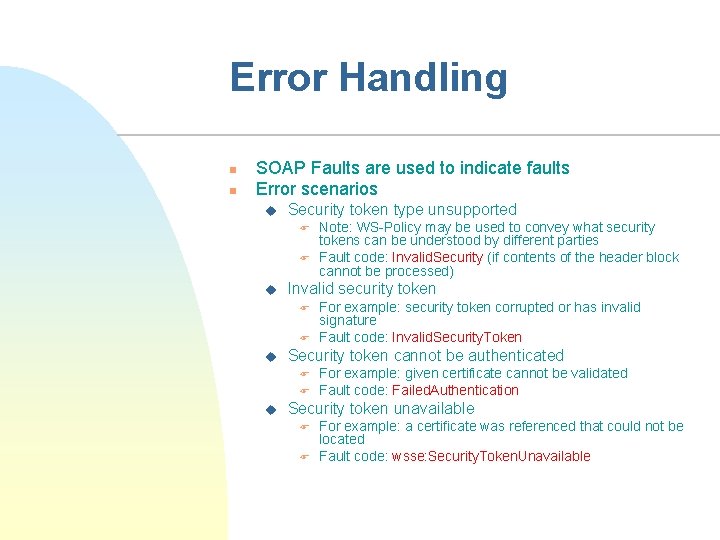
Error Handling n n SOAP Faults are used to indicate faults Error scenarios u Security token type unsupported F F u Invalid security token F F u For example: security token corrupted or has invalid signature Fault code: Invalid. Security. Token Security token cannot be authenticated F F u Note: WS-Policy may be used to convey what security tokens can be understood by different parties Fault code: Invalid. Security (if contents of the header block cannot be processed) For example: given certificate cannot be validated Fault code: Failed. Authentication Security token unavailable F F For example: a certificate was referenced that could not be located Fault code: wsse: Security. Token. Unavailable
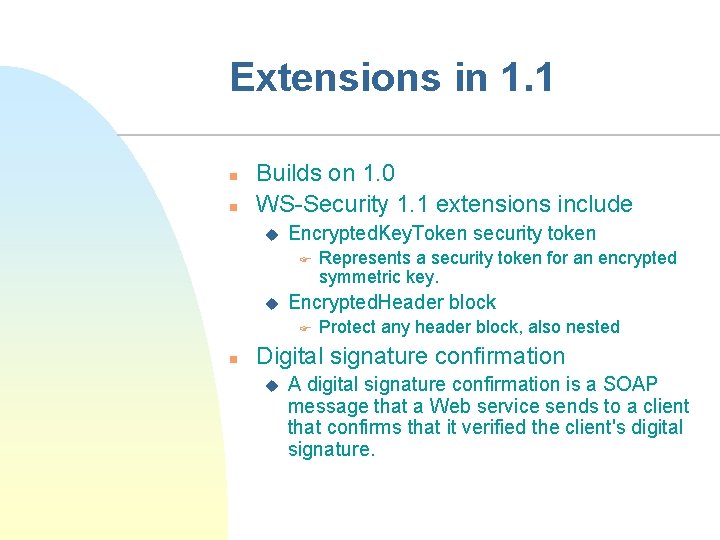
Extensions in 1. 1 n n Builds on 1. 0 WS-Security 1. 1 extensions include u Encrypted. Key. Token security token F u Encrypted. Header block F n Represents a security token for an encrypted symmetric key. Protect any header block, also nested Digital signature confirmation u A digital signature confirmation is a SOAP message that a Web service sends to a client that confirms that it verified the client's digital signature.

Security Contexts in Web Services n Remember Web Services goals: u u n Re-use existing services Combine services from several domains Security result: Must support several security domains u u SOAP intermediaries Reusing security tokens from one message in another message
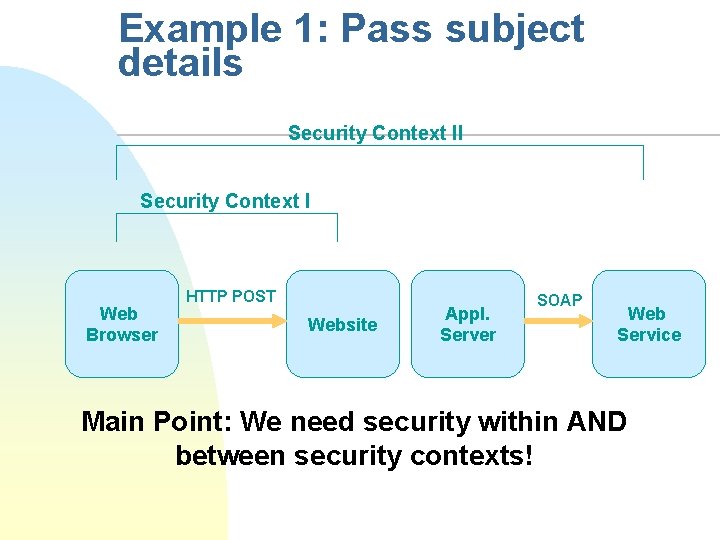
Example 1: Pass subject details Security Context II Security Context I Web Browser HTTP POST Website Appl. Server SOAP Web Service Main Point: We need security within AND between security contexts!
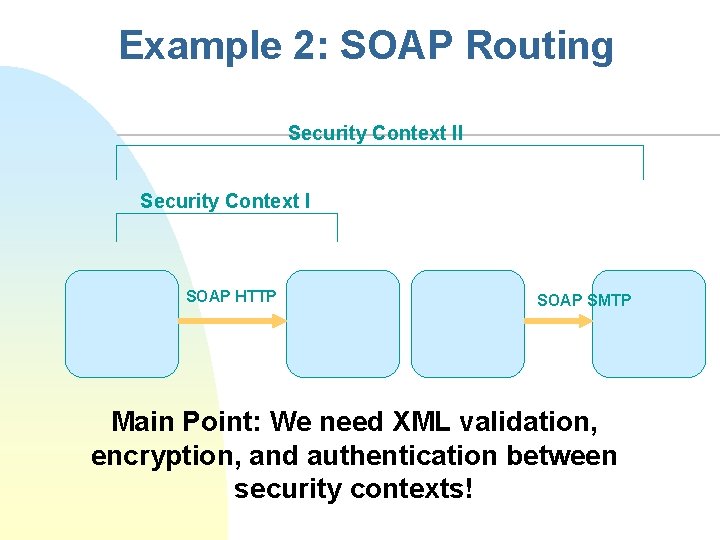
Example 2: SOAP Routing Security Context II Security Context I SOAP HTTP SOAP SMTP Main Point: We need XML validation, encryption, and authentication between security contexts!
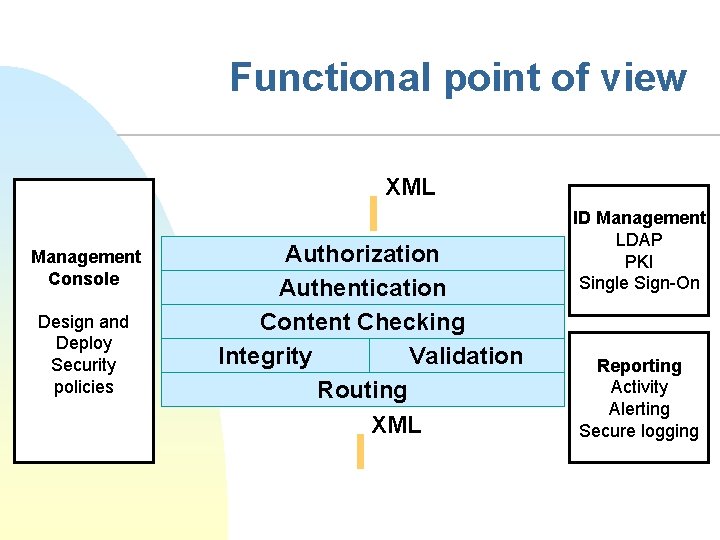
Functional point of view XML Management Console Design and Deploy Security policies Authorization Authentication Content Checking Integrity Validation Routing XML ID Management LDAP PKI Single Sign-On Reporting Activity Alerting Secure logging
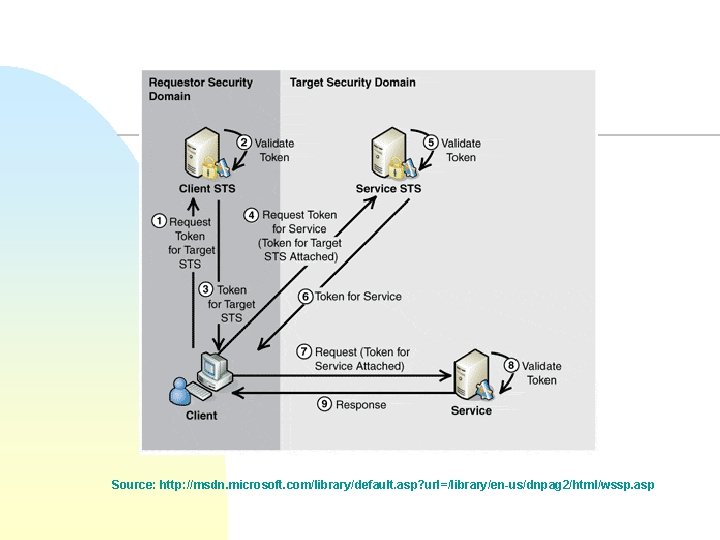
Source: http: //msdn. microsoft. com/library/default. asp? url=/library/en-us/dnpag 2/html/wssp. asp
SAML n n SAML (Security Assertion Markup Language) u A XML-based framework (schemas) for the exchange of authentication and authorization information u A standard message exchange protocol F How you ask and receive information Mainly for integration, up to relying parties to decide to what authentication authority to trust Assertions can convey information about authentication acts performed by subjects, attributes of subjects, and authorization decisions about whether subjects are allowed to access certain resources u Authentication statements merely describe acts of authentication that happened previously Specified by OASIS
SAML in a nutshell n XML-based framework for exchanging security information u u u n XML-encoded security assertions XML-encoded request/response protocol Rules on using assertions with standard transport and messaging frameworks SAML & WS-Security allow a SOAP message to include information about the end-user’s authentication status
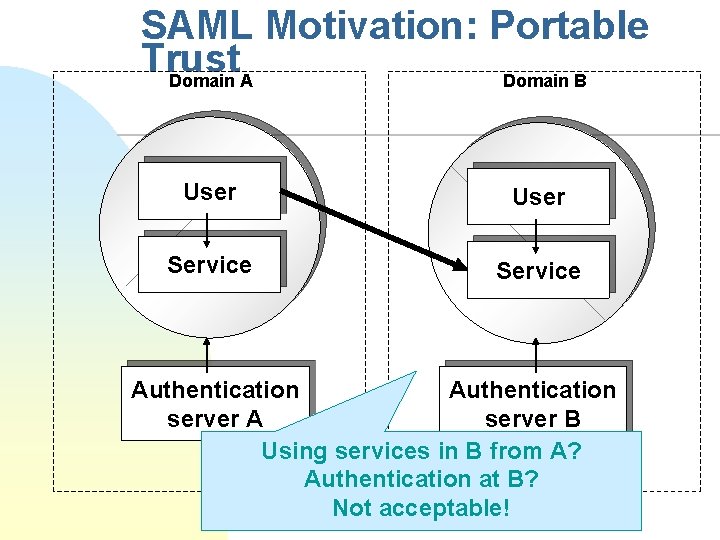
SAML Motivation: Portable Trust Domain A Domain B User Service Authentication server A server B Using services in B from A? Authentication at B? Not acceptable!
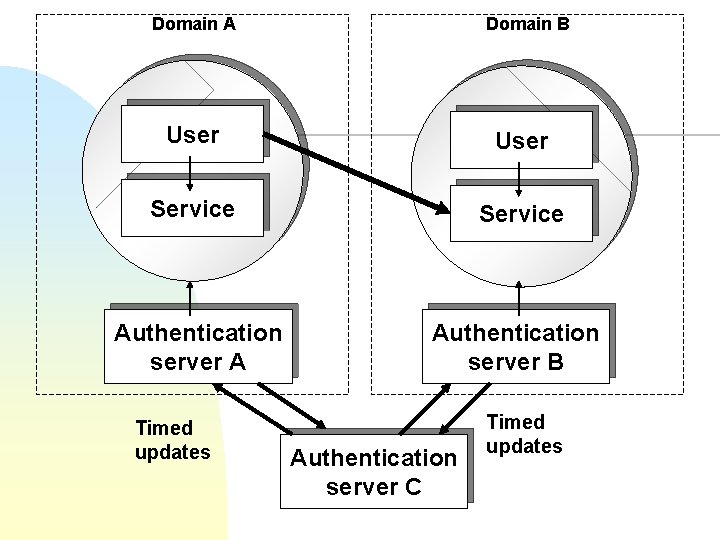
Domain A Domain B User Service Authentication server A Authentication server B Timed updates Authentication server C Timed updates
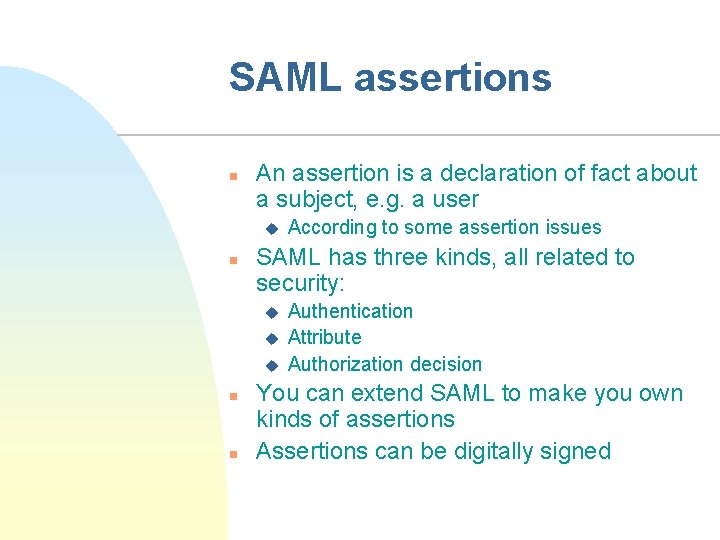
SAML assertions n An assertion is a declaration of fact about a subject, e. g. a user u n SAML has three kinds, all related to security: u u u n n According to some assertion issues Authentication Attribute Authorization decision You can extend SAML to make you own kinds of assertions Assertions can be digitally signed
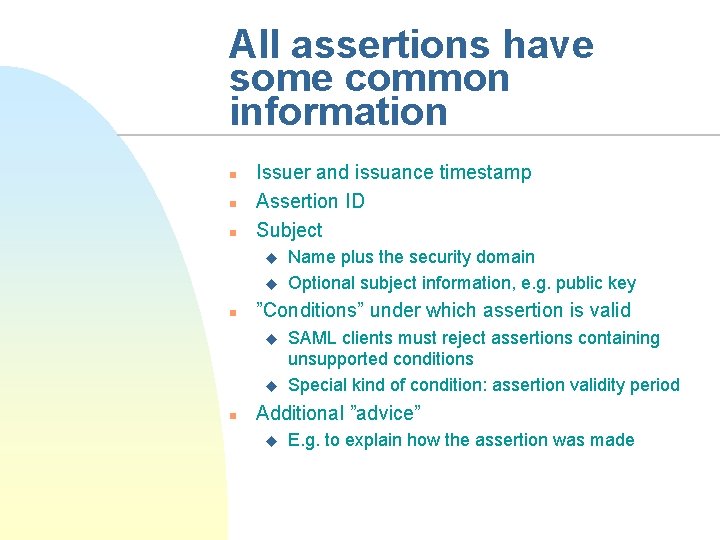
All assertions have some common information n Issuer and issuance timestamp Assertion ID Subject u u n ”Conditions” under which assertion is valid u u n Name plus the security domain Optional subject information, e. g. public key SAML clients must reject assertions containing unsupported conditions Special kind of condition: assertion validity period Additional ”advice” u E. g. to explain how the assertion was made
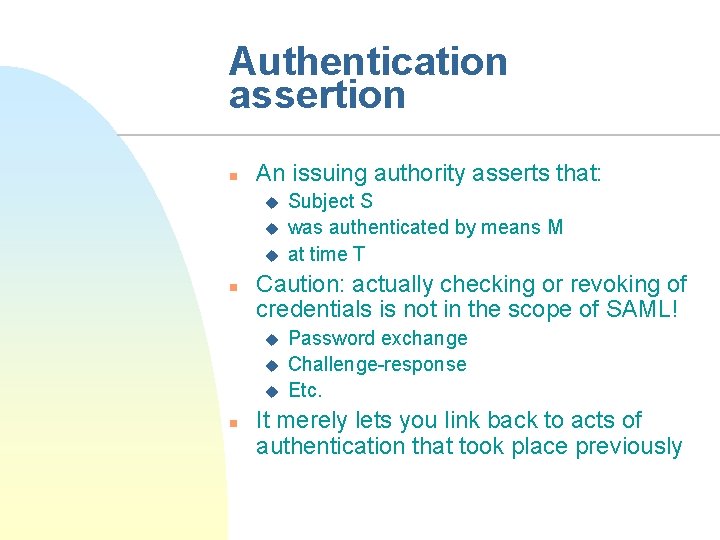
Authentication assertion n An issuing authority asserts that: u u u n Caution: actually checking or revoking of credentials is not in the scope of SAML! u u u n Subject S was authenticated by means M at time T Password exchange Challenge-response Etc. It merely lets you link back to acts of authentication that took place previously
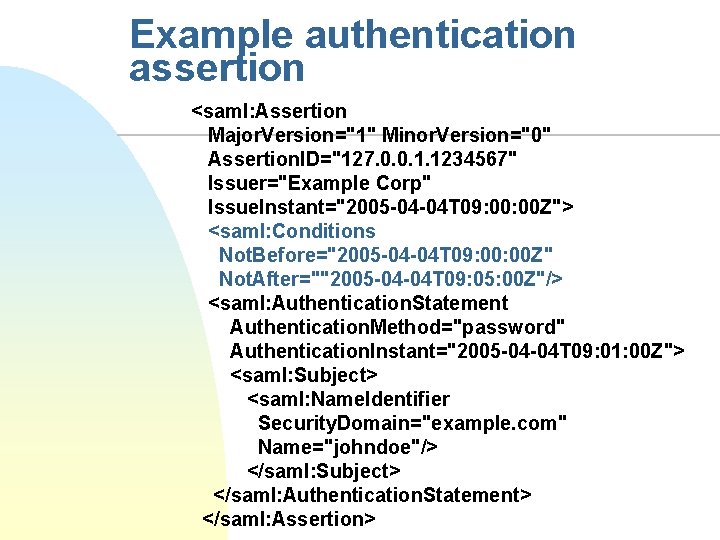
Example authentication assertion <saml: Assertion Major. Version="1" Minor. Version="0" Assertion. ID="127. 0. 0. 1. 1234567" Issuer="Example Corp" Issue. Instant="2005 -04 -04 T 09: 00 Z"> <saml: Conditions Not. Before="2005 -04 -04 T 09: 00 Z" Not. After=""2005 -04 -04 T 09: 05: 00 Z"/> <saml: Authentication. Statement Authentication. Method="password" Authentication. Instant="2005 -04 -04 T 09: 01: 00 Z"> <saml: Subject> <saml: Name. Identifier Security. Domain="example. com" Name="johndoe"/> </saml: Subject> </saml: Authentication. Statement> </saml: Assertion>
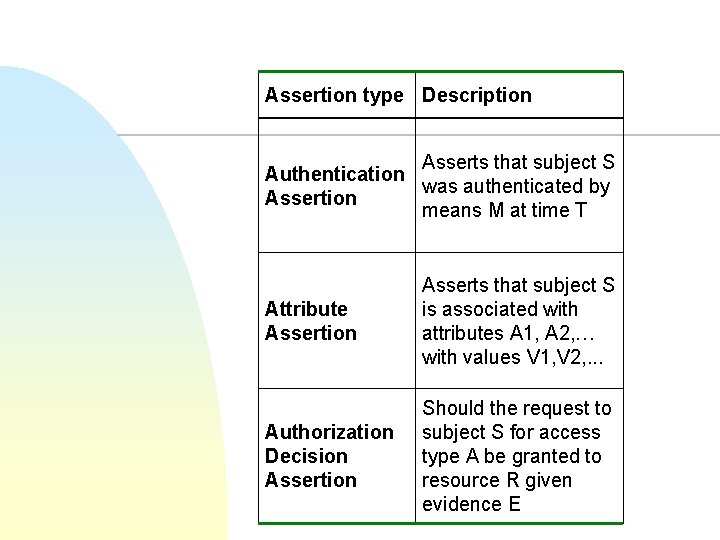
Assertion type Description Asserts that subject S Authentication was authenticated by Assertion means M at time T Attribute Assertion Asserts that subject S is associated with attributes A 1, A 2, … with values V 1, V 2, . . . Authorization Decision Assertion Should the request to subject S for access type A be granted to resource R given evidence E
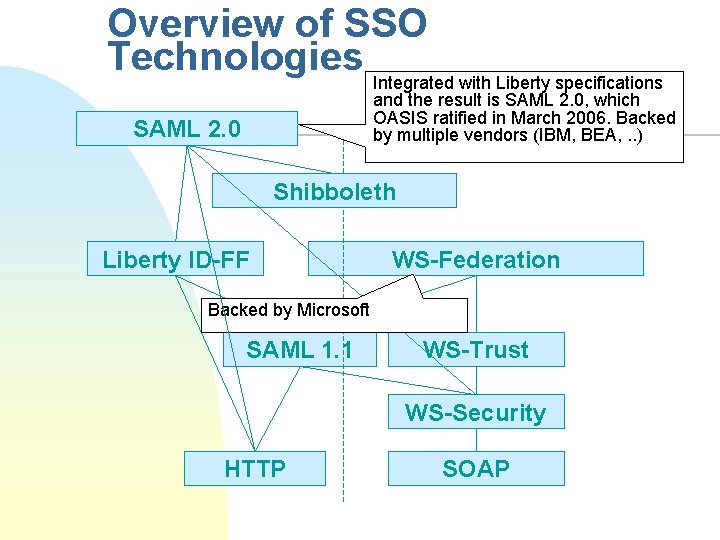
Overview of SSO Technologies Integrated with Liberty specifications and the result is SAML 2. 0, which OASIS ratified in March 2006. Backed by multiple vendors (IBM, BEA, . . ) SAML 2. 0 Shibboleth Liberty ID-FF WS-Federation Backed by Microsoft SAML 1. 1 WS-Trust WS-Security HTTP SOAP
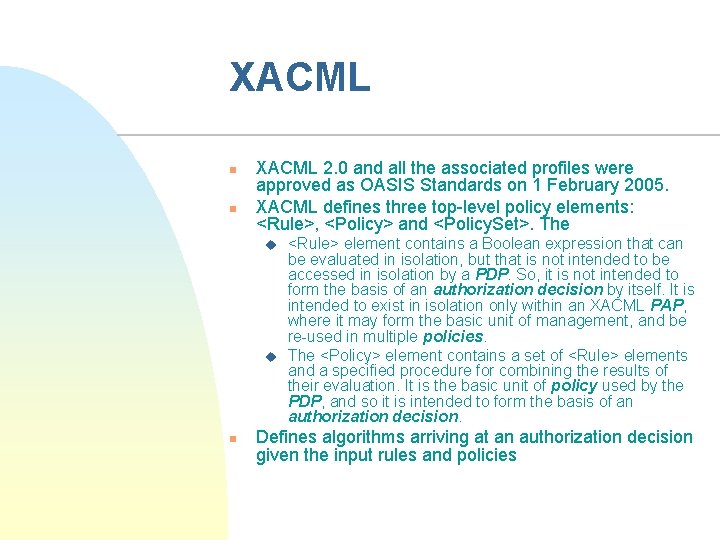
XACML n n XACML 2. 0 and all the associated profiles were approved as OASIS Standards on 1 February 2005. XACML defines three top-level policy elements: <Rule>, <Policy> and <Policy. Set>. The u u n <Rule> element contains a Boolean expression that can be evaluated in isolation, but that is not intended to be accessed in isolation by a PDP. So, it is not intended to form the basis of an authorization decision by itself. It is intended to exist in isolation only within an XACML PAP, where it may form the basic unit of management, and be re-used in multiple policies. The <Policy> element contains a set of <Rule> elements and a specified procedure for combining the results of their evaluation. It is the basic unit of policy used by the PDP, and so it is intended to form the basis of an authorization decision. Defines algorithms arriving at an authorization decision given the input rules and policies
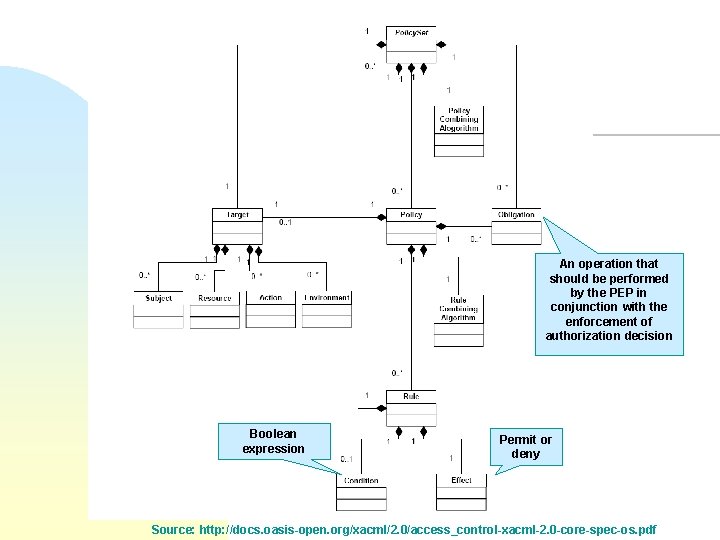
An operation that should be performed by the PEP in conjunction with the enforcement of authorization decision Boolean expression Permit or deny Source: http: //docs. oasis-open. org/xacml/2. 0/access_control-xacml-2. 0 -core-spec-os. pdf
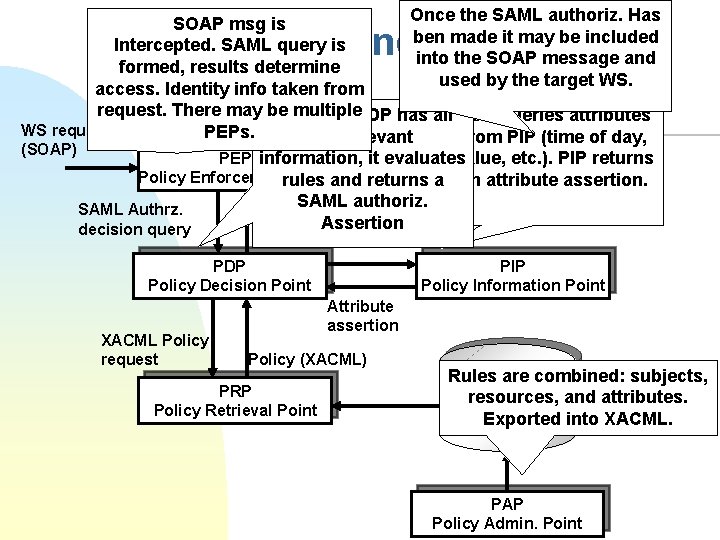
Once the SAML authoriz. Has SOAP msg is ben made it may be included Intercepted. SAML query is into the SOAP message and formed, results determine used by the target WS. access. Identity info taken from request. There may be multiple Once the PDP has all PDP queries attributes WS request PEPs. the relevant from PIP (time of day, (SOAP) value, etc. ). PIP returns PEP information, it evaluates Web Service Policy Enforcementrules Pointand returns a an attribute assertion. SAML authoriz. SAML Authrz. Reply Assertion decision query SAML and XACML Info request PDP Policy Decision Point XACML Policy request PIP Policy Information Point Attribute assertion Policy (XACML) PRP Policy Retrieval Point Rules are combined: subjects, Policy Store and attributes. resources, (XACML) Exported into XACML. PAP Policy Admin. Point
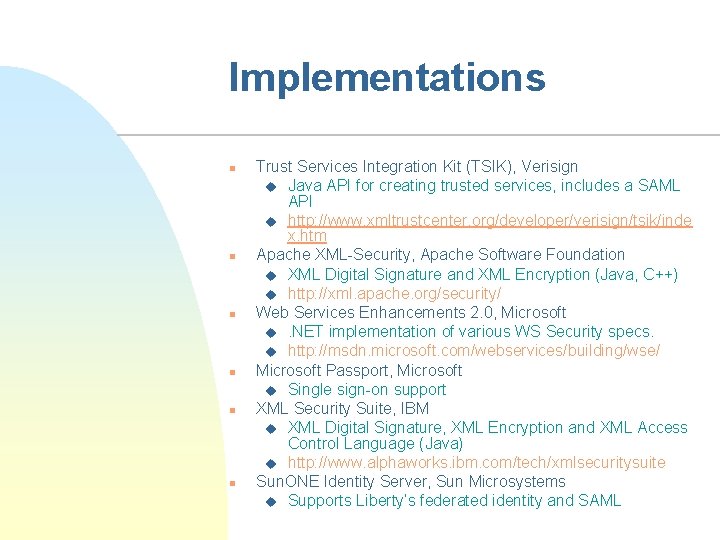
Implementations n n n Trust Services Integration Kit (TSIK), Verisign u Java API for creating trusted services, includes a SAML API u http: //www. xmltrustcenter. org/developer/verisign/tsik/inde x. htm Apache XML-Security, Apache Software Foundation u XML Digital Signature and XML Encryption (Java, C++) u http: //xml. apache. org/security/ Web Services Enhancements 2. 0, Microsoft u. NET implementation of various WS Security specs. u http: //msdn. microsoft. com/webservices/building/wse/ Microsoft Passport, Microsoft u Single sign-on support XML Security Suite, IBM u XML Digital Signature, XML Encryption and XML Access Control Language (Java) u http: //www. alphaworks. ibm. com/tech/xmlsecuritysuite Sun. ONE Identity Server, Sun Microsystems u Supports Liberty’s federated identity and SAML
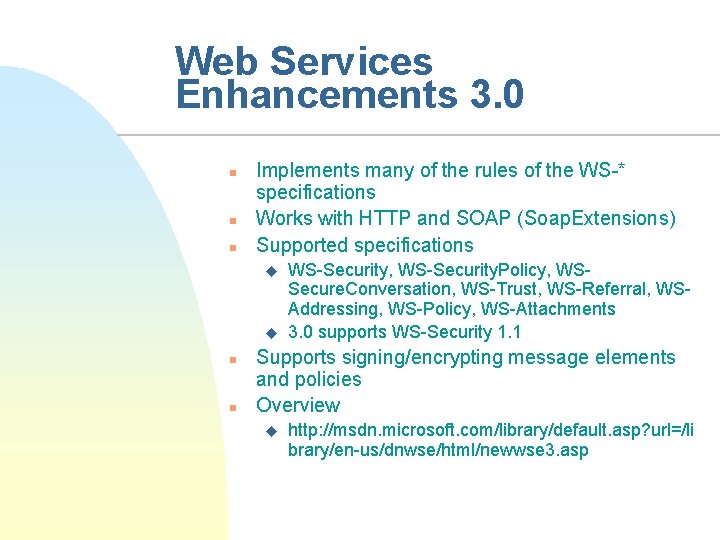
Web Services Enhancements 3. 0 n n n Implements many of the rules of the WS-* specifications Works with HTTP and SOAP (Soap. Extensions) Supported specifications u u n n WS-Security, WS-Security. Policy, WSSecure. Conversation, WS-Trust, WS-Referral, WSAddressing, WS-Policy, WS-Attachments 3. 0 supports WS-Security 1. 1 Supports signing/encrypting message elements and policies Overview u http: //msdn. microsoft. com/library/default. asp? url=/li brary/en-us/dnwse/html/newwse 3. asp
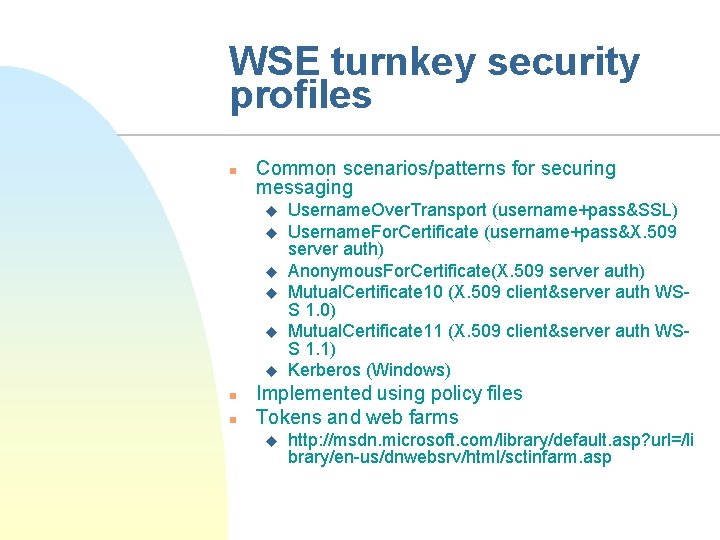
WSE turnkey security profiles n Common scenarios/patterns for securing messaging u u u n n Username. Over. Transport (username+pass&SSL) Username. For. Certificate (username+pass&X. 509 server auth) Anonymous. For. Certificate(X. 509 server auth) Mutual. Certificate 10 (X. 509 client&server auth WSS 1. 0) Mutual. Certificate 11 (X. 509 client&server auth WSS 1. 1) Kerberos (Windows) Implemented using policy files Tokens and web farms u http: //msdn. microsoft. com/library/default. asp? url=/li brary/en-us/dnwebsrv/html/sctinfarm. asp
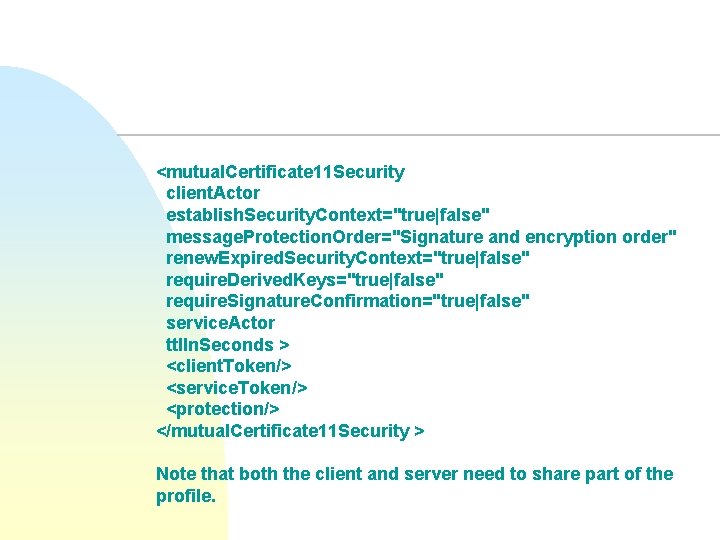
<mutual. Certificate 11 Security client. Actor establish. Security. Context="true|false" message. Protection. Order="Signature and encryption order" renew. Expired. Security. Context="true|false" require. Derived. Keys="true|false" require. Signature. Confirmation="true|false" service. Actor ttl. In. Seconds > <client. Token/> <service. Token/> <protection/> </mutual. Certificate 11 Security > Note that both the client and server need to share part of the profile.
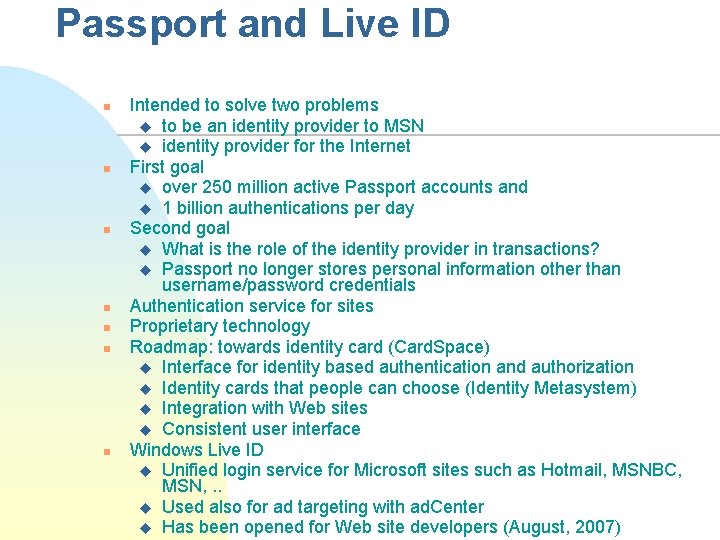
Passport and Live ID n n n n Intended to solve two problems u to be an identity provider to MSN u identity provider for the Internet First goal u over 250 million active Passport accounts and u 1 billion authentications per day Second goal u What is the role of the identity provider in transactions? u Passport no longer stores personal information other than username/password credentials Authentication service for sites Proprietary technology Roadmap: towards identity card (Card. Space) u Interface for identity based authentication and authorization u Identity cards that people can choose (Identity Metasystem) u Integration with Web sites u Consistent user interface Windows Live ID u Unified login service for Microsoft sites such as Hotmail, MSNBC, MSN, . . u Used also for ad targeting with ad. Center u Has been opened for Web site developers (August, 2007)
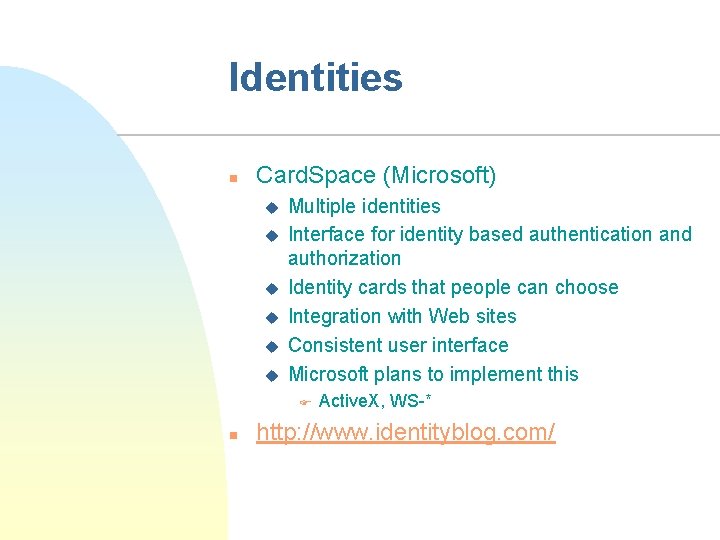
Identities n Card. Space (Microsoft) u u u Multiple identities Interface for identity based authentication and authorization Identity cards that people can choose Integration with Web sites Consistent user interface Microsoft plans to implement this F n Active. X, WS-* http: //www. identityblog. com/
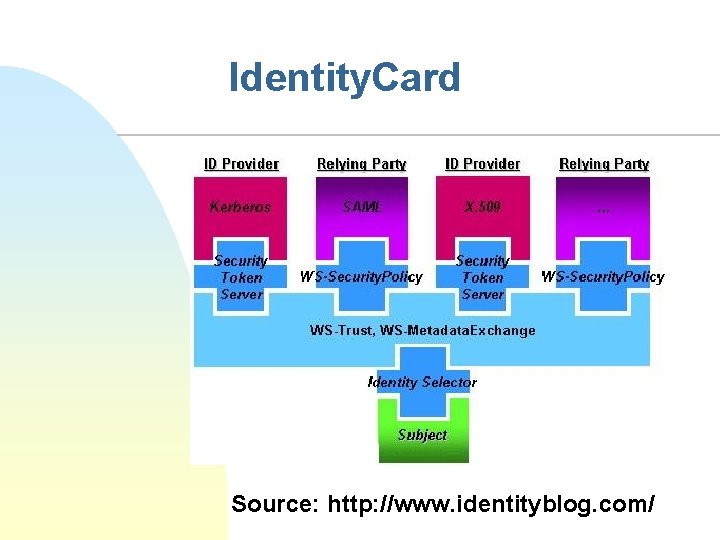
Identity. Card Source: http: //www. identityblog. com/
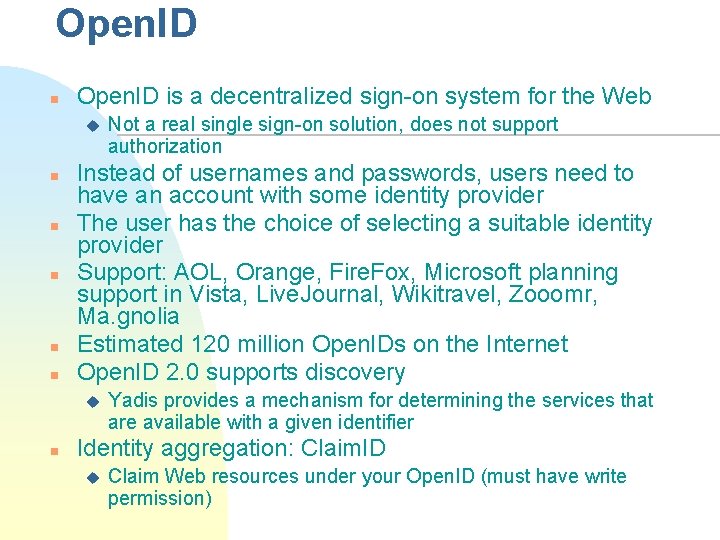
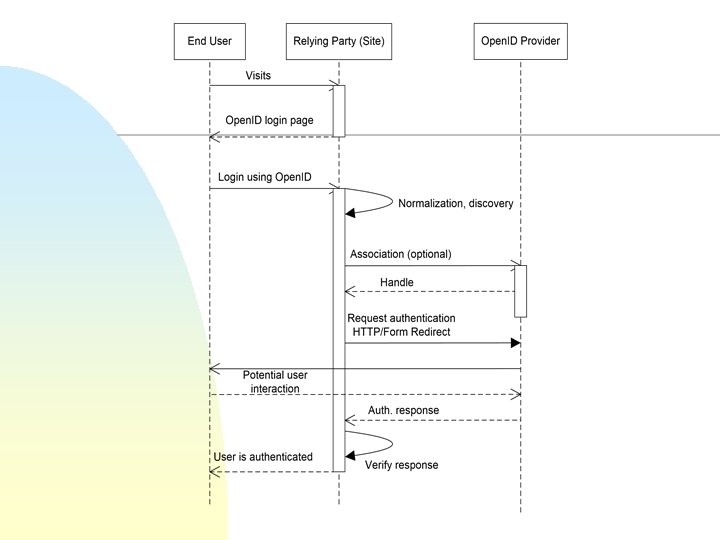
Open. ID n Open. ID is a decentralized sign-on system for the Web u n n n Instead of usernames and passwords, users need to have an account with some identity provider The user has the choice of selecting a suitable identity provider Support: AOL, Orange, Fire. Fox, Microsoft planning support in Vista, Live. Journal, Wikitravel, Zooomr, Ma. gnolia Estimated 120 million Open. IDs on the Internet Open. ID 2. 0 supports discovery u n Not a real single sign-on solution, does not support authorization Yadis provides a mechanism for determining the services that are available with a given identifier Identity aggregation: Claim. ID u Claim Web resources under your Open. ID (must have write permission)
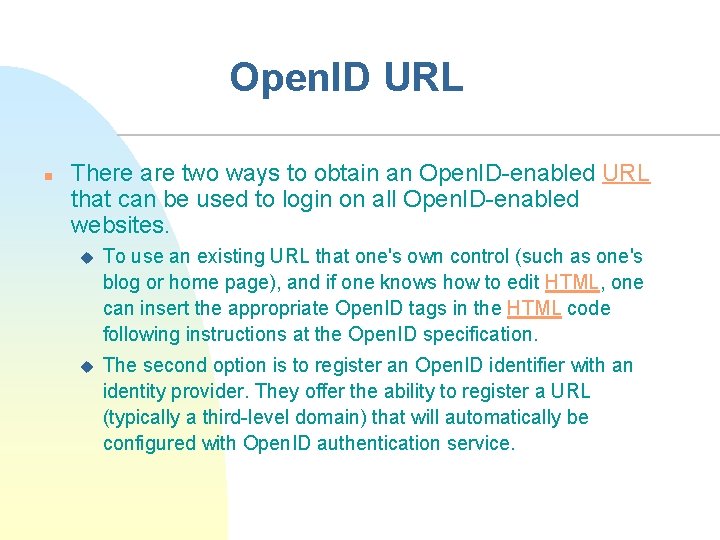
Open. ID URL n There are two ways to obtain an Open. ID-enabled URL that can be used to login on all Open. ID-enabled websites. u To use an existing URL that one's own control (such as one's blog or home page), and if one knows how to edit HTML, one can insert the appropriate Open. ID tags in the HTML code following instructions at the Open. ID specification. u The second option is to register an Open. ID identifier with an identity provider. They offer the ability to register a URL (typically a third-level domain) that will automatically be configured with Open. ID authentication service.
Lecture Summary n Security contexts u u n WS security standard revisited u u n SOAP header carries security information (and other info as well) Selective processing SAML u n Security needed within and between contexts XML validation, encryption, and authentication needed between security contexts! Statements about authorization, authentication, attributes SAML & WS-Security & XACML Open. ID and Live ID Implementations available
- Slides: 40