System Scanning Intrusion Detection Security Management Firewall Authentication

- Slides: 75
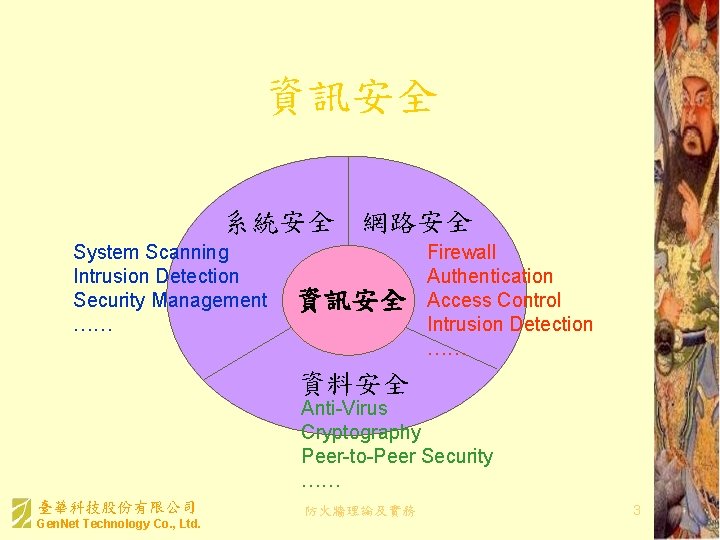
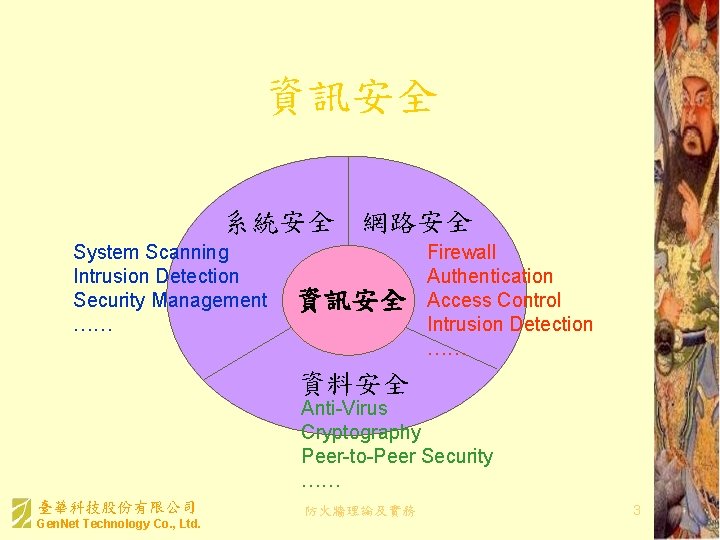
資訊安全 系統安全 網路安全 System Scanning Intrusion Detection Security Management …… 資訊安全 Firewall Authentication Access Control Intrusion Detection …… 資料安全 Anti-Virus Cryptography Peer-to-Peer Security …… 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 3
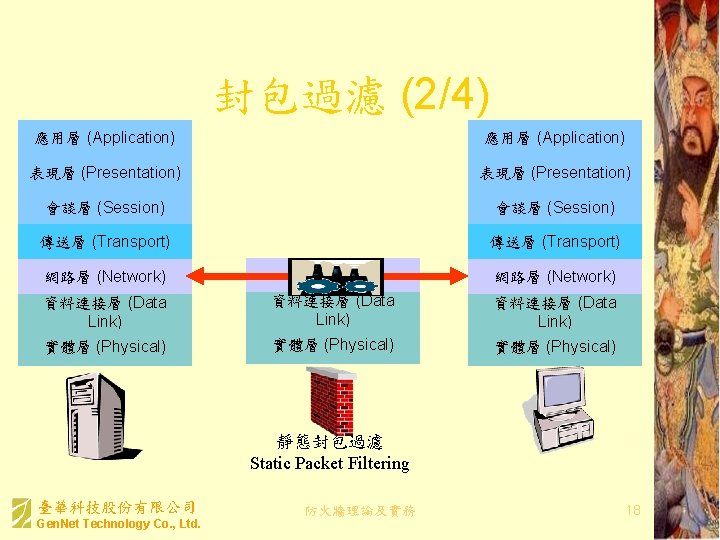
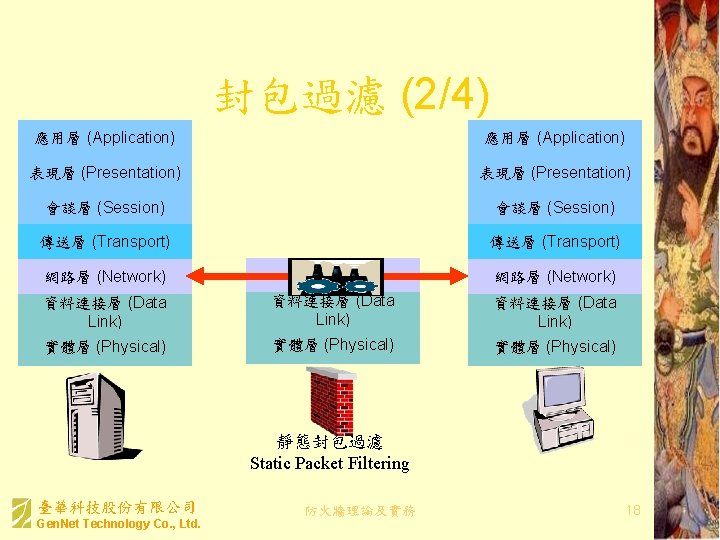
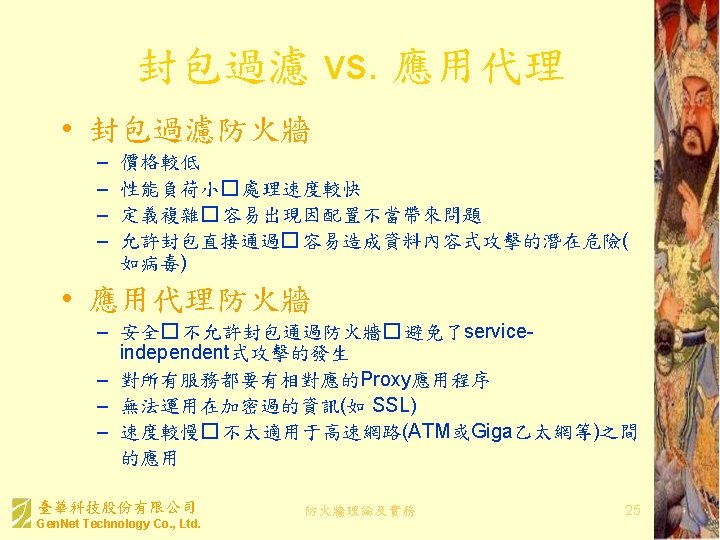
封包過濾 (2/4) 應用層 (Application) 表現層 (Presentation) 會談層 (Session) 傳送層 (Transport) 網路層 (Network) 資料連接層 (Data Link) 實體層 (Physical) 靜態封包過濾 Static Packet Filtering 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 18
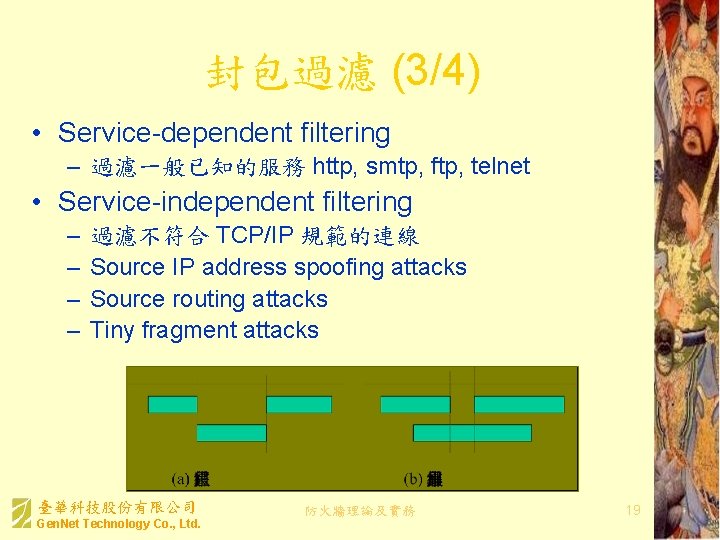
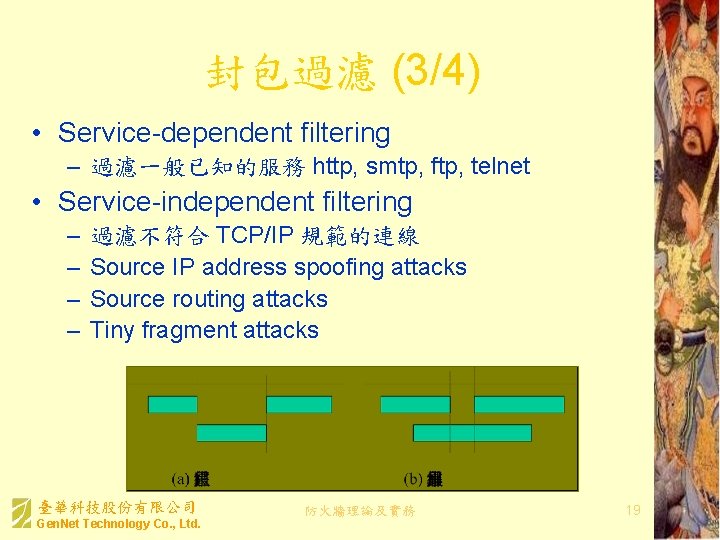
封包過濾 (3/4) • Service-dependent filtering – 過濾一般已知的服務 http, smtp, ftp, telnet • Service-independent filtering – – 過濾不符合 TCP/IP 規範的連線 Source IP address spoofing attacks Source routing attacks Tiny fragment attacks 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 19
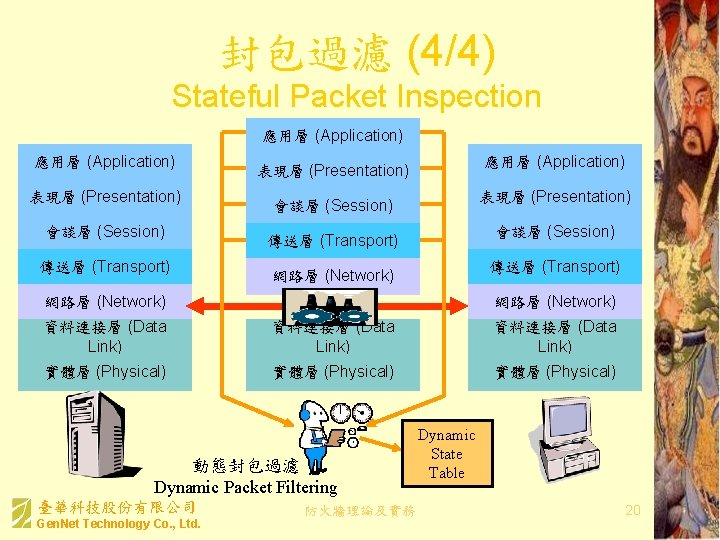
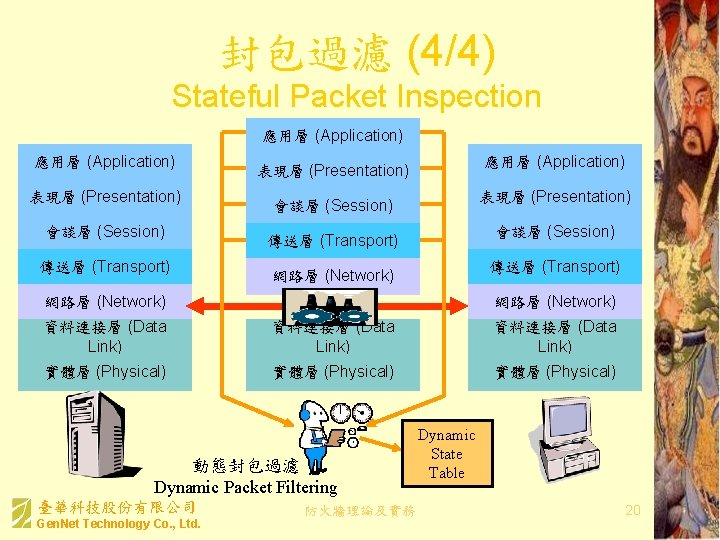
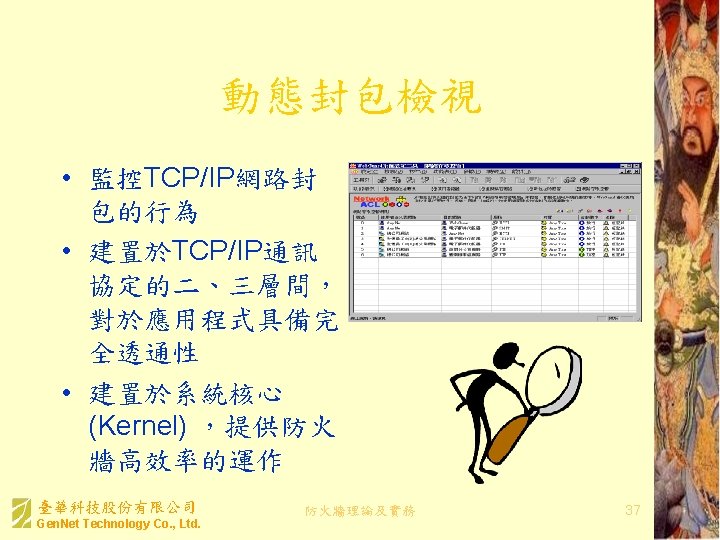
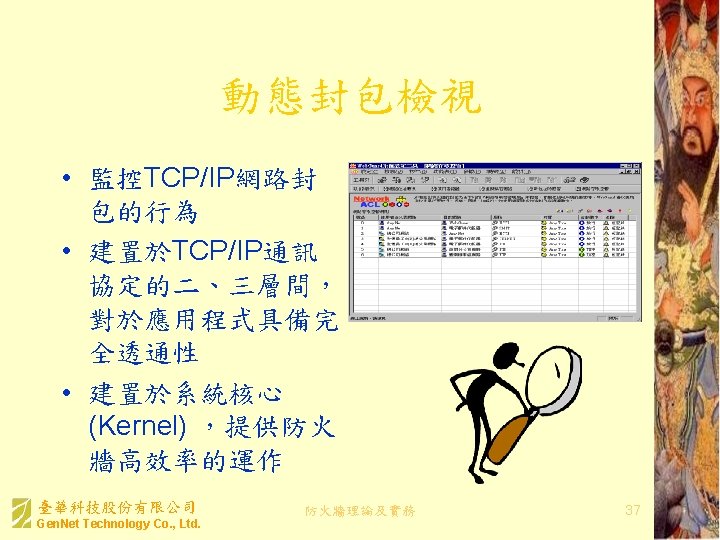
封包過濾 (4/4) Stateful Packet Inspection 應用層 (Application) 表現層 (Presentation) 會談層 (Session) 傳送層 (Transport) 網路層 (Network) 資料連接層 (Data Link) 實體層 (Physical) 動態封包過濾 Dynamic Packet Filtering 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 Dynamic State Table 20
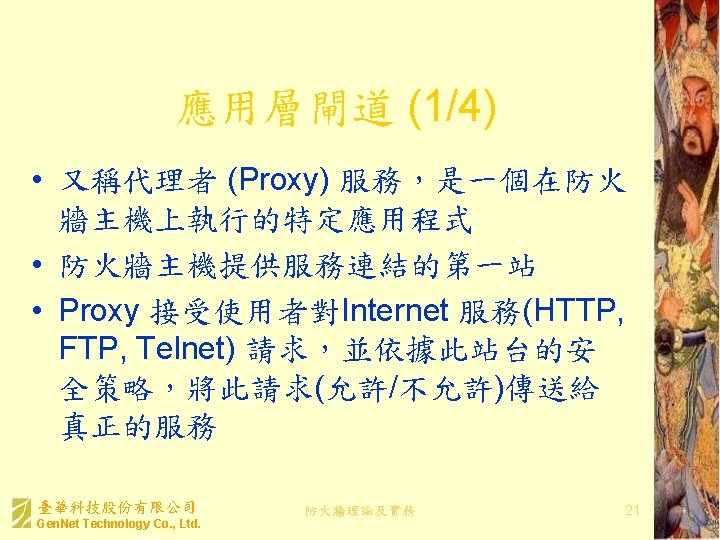
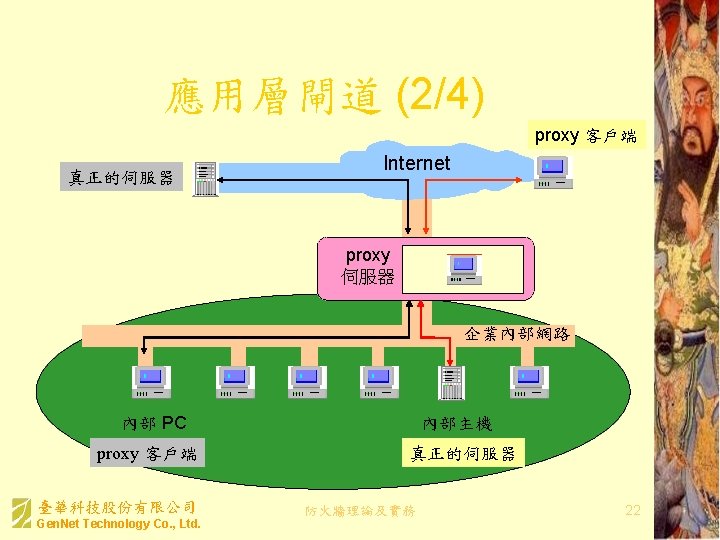
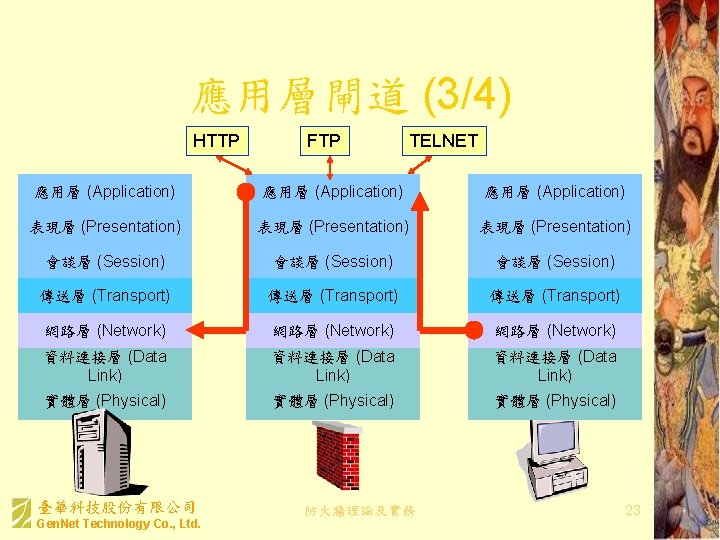
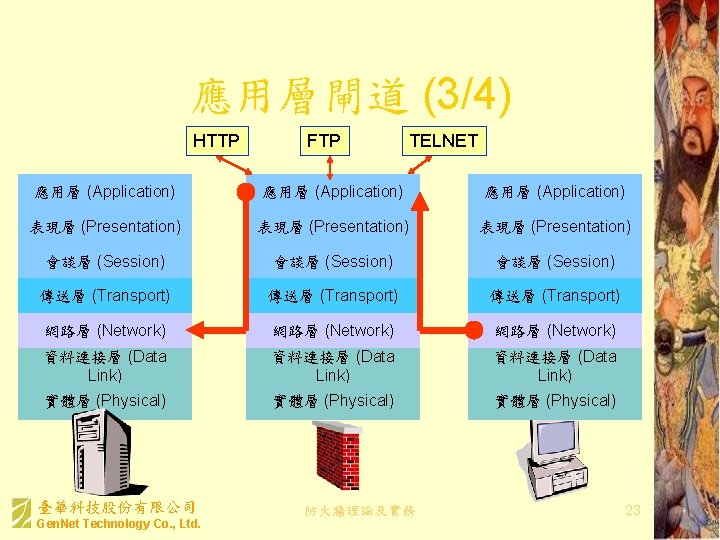
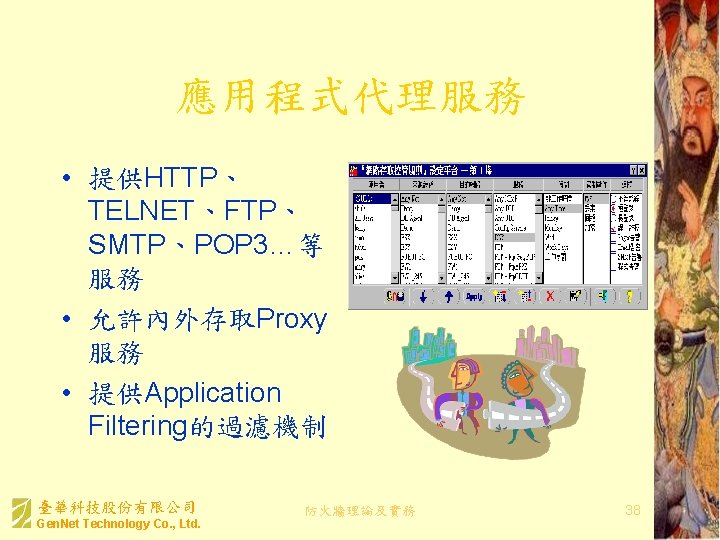
應用層閘道 (3/4) HTTP FTP TELNET 應用層 (Application) 表現層 (Presentation) 會談層 (Session) 傳送層 (Transport) 網路層 (Network) 資料連接層 (Data Link) 實體層 (Physical) 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 23
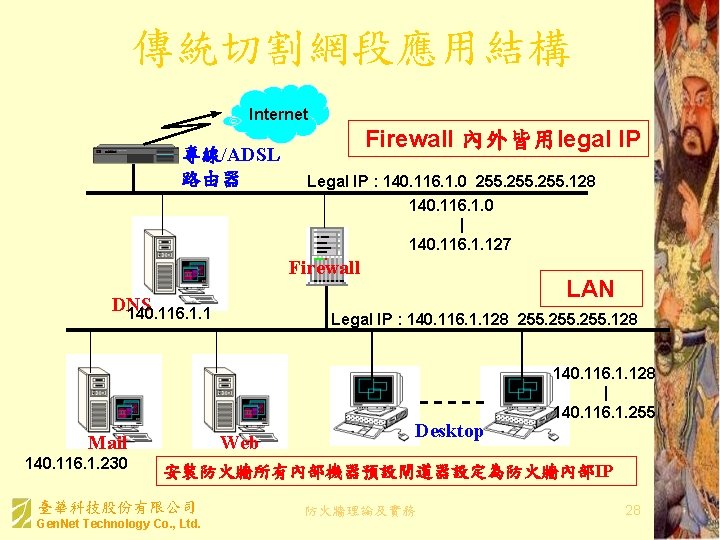
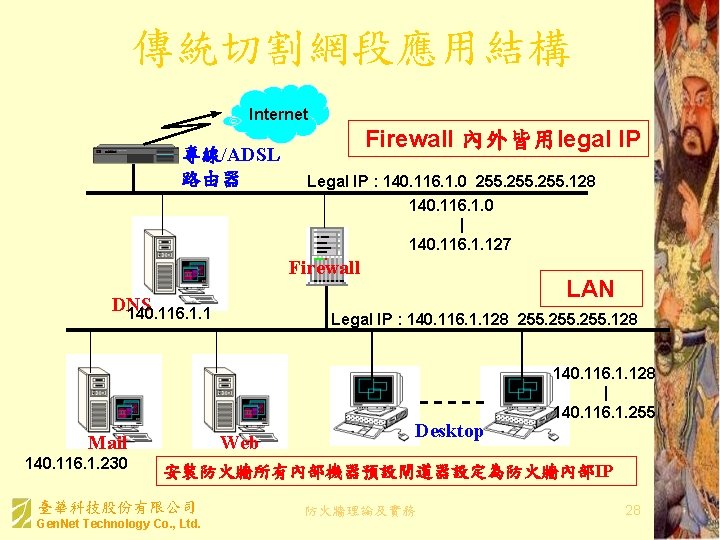
傳統切割網段應用結構 Internet 專線/ADSL 路由器 Firewall 內外皆用legal IP Legal IP : 140. 116. 1. 0 255. 128 140. 116. 1. 0 | 140. 116. 1. 127 Firewall DNS 140. 116. 1. 1 Mail 140. 116. 1. 230 LAN Legal IP : 140. 116. 1. 128 255. 128 Web Desktop 140. 116. 1. 128 | 140. 116. 1. 255 安裝防火牆所有內部機器預設閘道器設定為防火牆內部IP 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 28
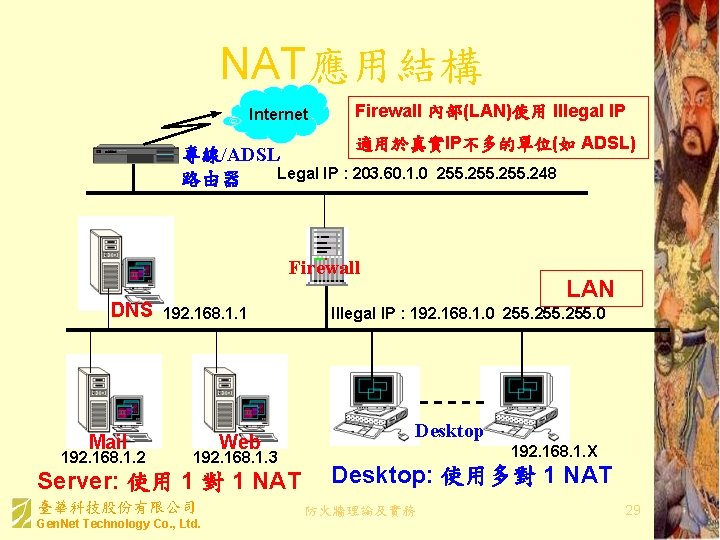
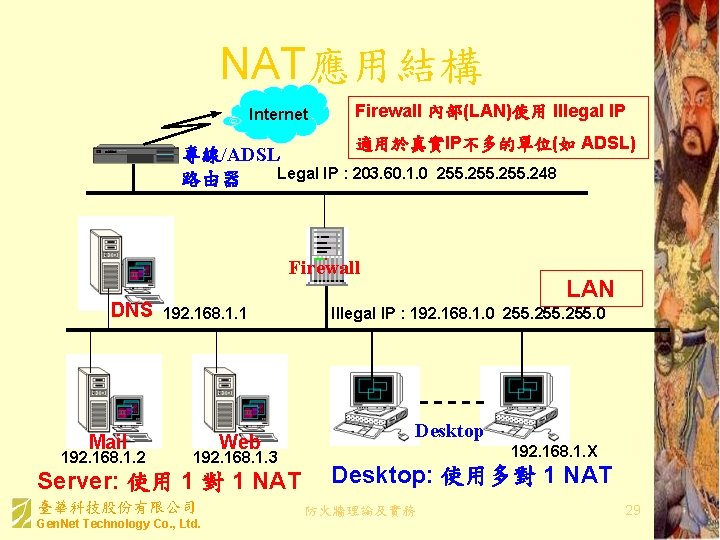
NAT應用結構 Internet Firewall 內部(LAN)使用 Illegal IP 適用於真實IP不多的單位(如 ADSL) 專線/ADSL Legal IP : 203. 60. 1. 0 路由器 255. 248 Firewall DNS Mail 192. 168. 1. 2 192. 168. 1. 1 Web 192. 168. 1. 3 Server: 使用 1 對 1 NAT 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. LAN Illegal IP : 192. 168. 1. 0 255. 0 Desktop 192. 168. 1. X Desktop: 使用多對 1 NAT 防火牆理論及實務 29
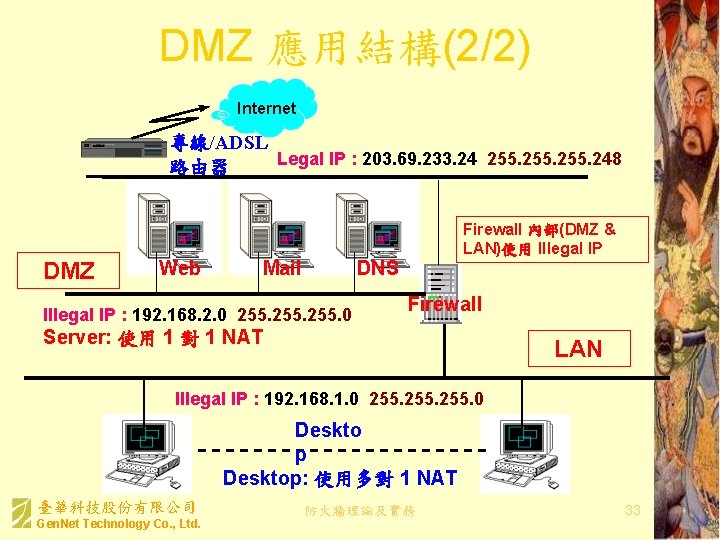
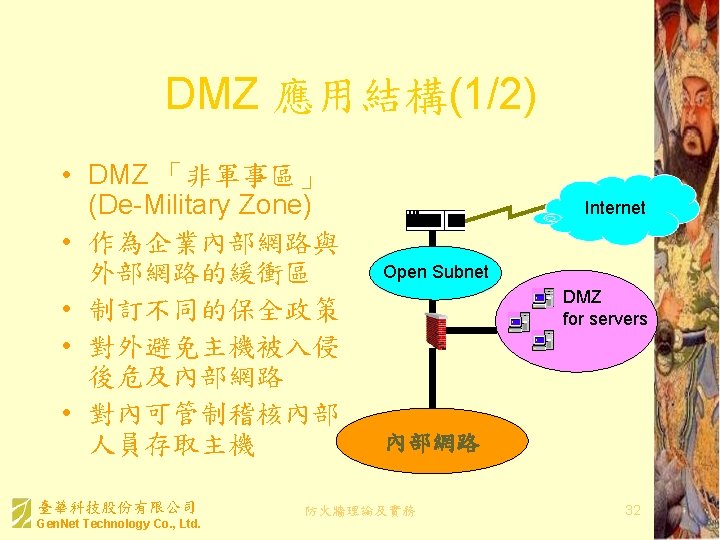
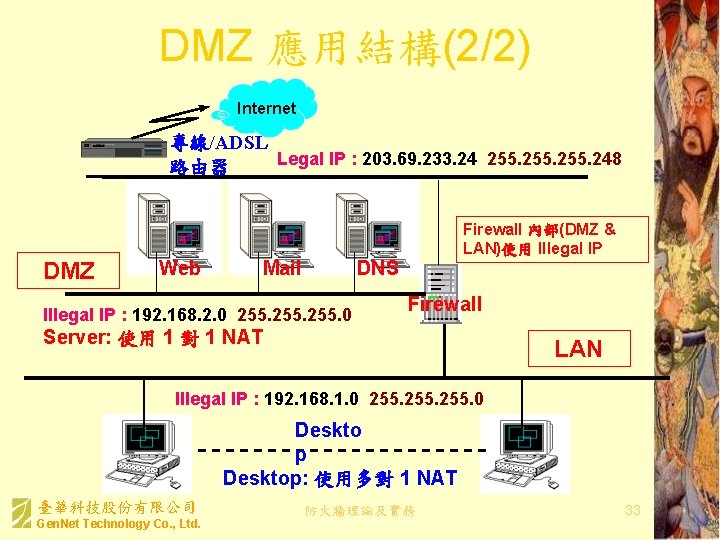
DMZ 應用結構(2/2) Internet 專線/ADSL Legal IP : 203. 69. 233. 24 255. 248 路由器 DMZ Web Firewall 內部(DMZ & LAN)使用 Illegal IP DNS Mail Illegal IP : 192. 168. 2. 0 255. 0 Firewall Server: 使用 1 對 1 NAT LAN Illegal IP : 192. 168. 1. 0 255. 0 Deskto p Desktop: 使用多對 1 NAT 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 33
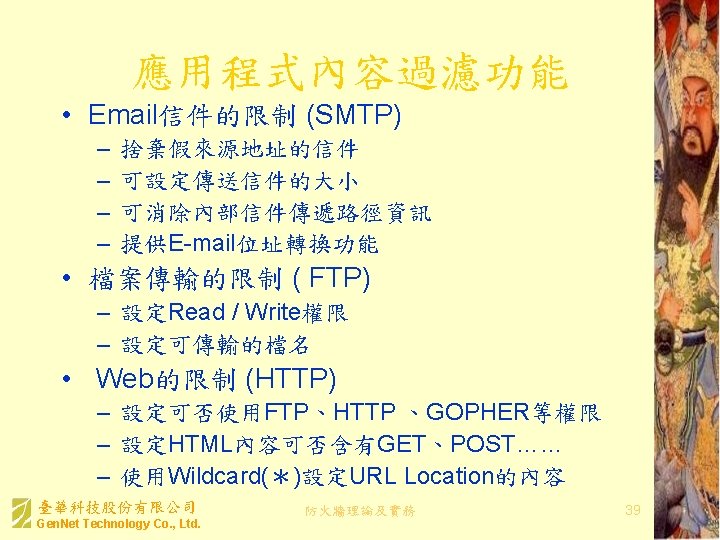
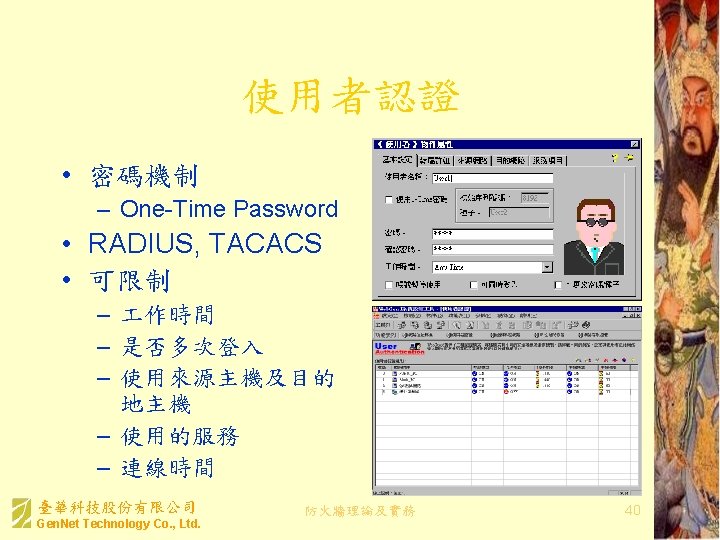
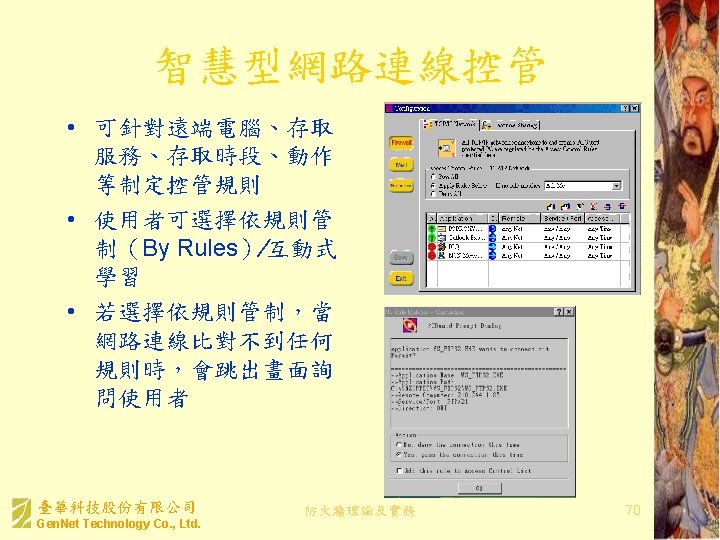
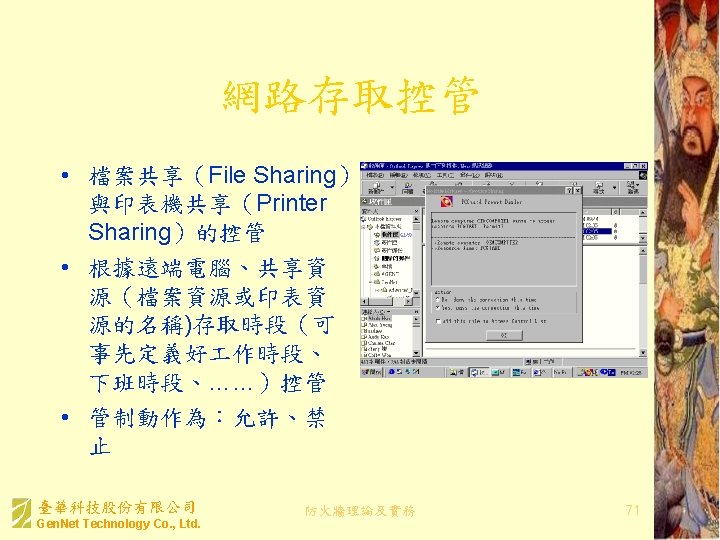
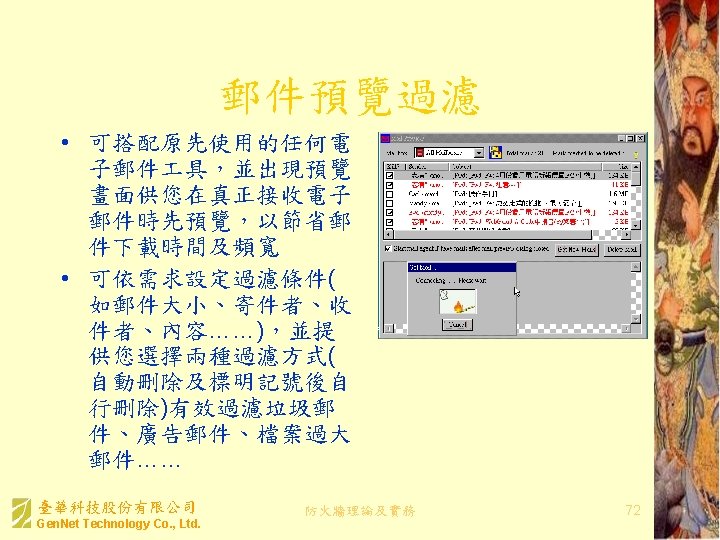
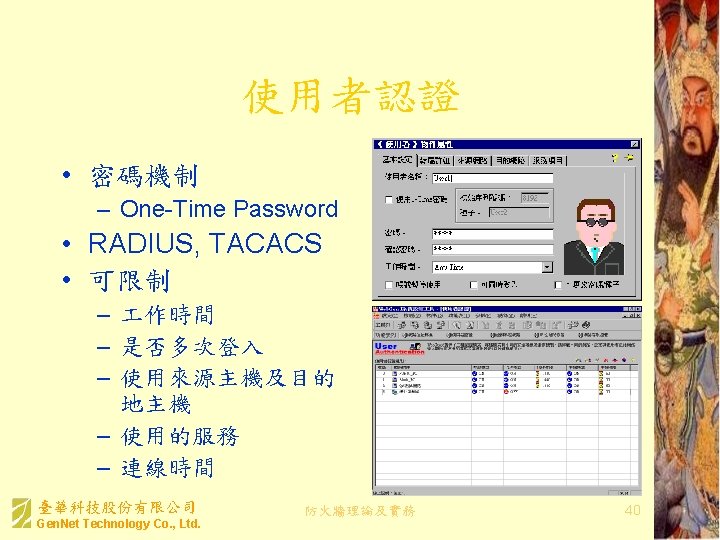
防火牆產品的常見功能 (1/2) • • • 動態封包檢視 (Dynamic Packet Filter) 應用程式代理服務 (Application Proxy) 應用程式內容過濾功能 (Application Filtering) 使用者認證 (User Authentication) 網路安全防範機制 (Network System Security) 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 35
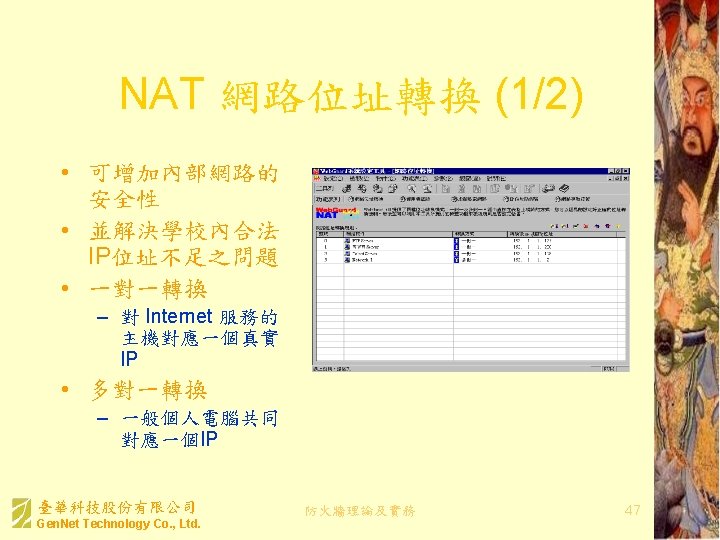
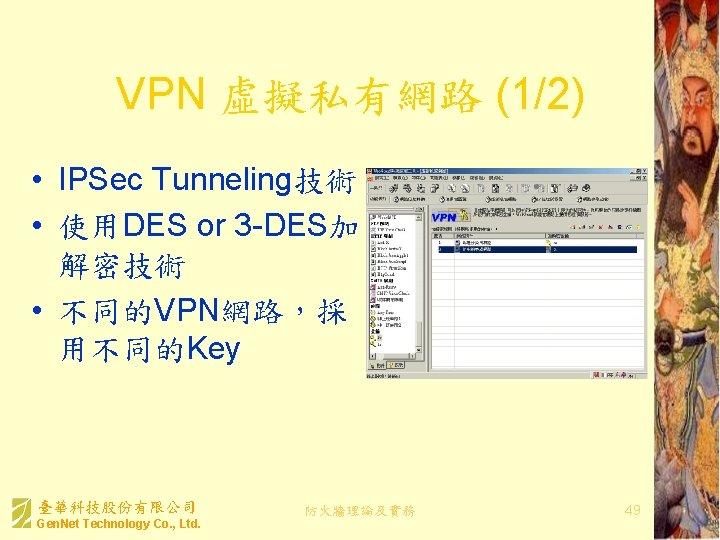
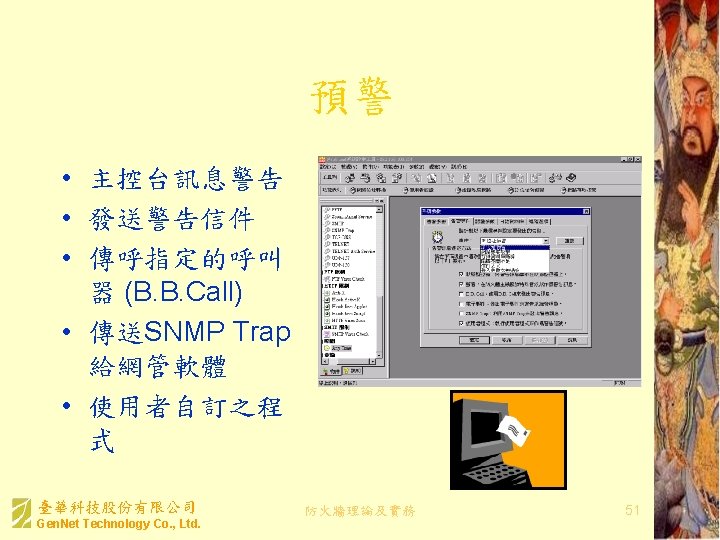
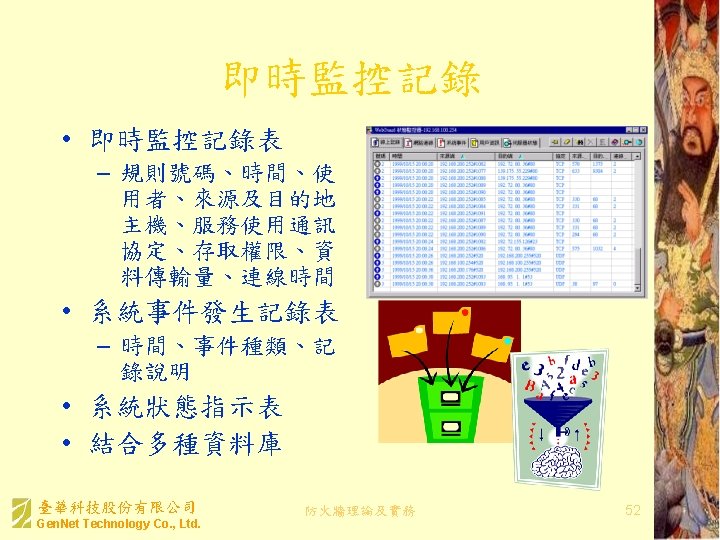
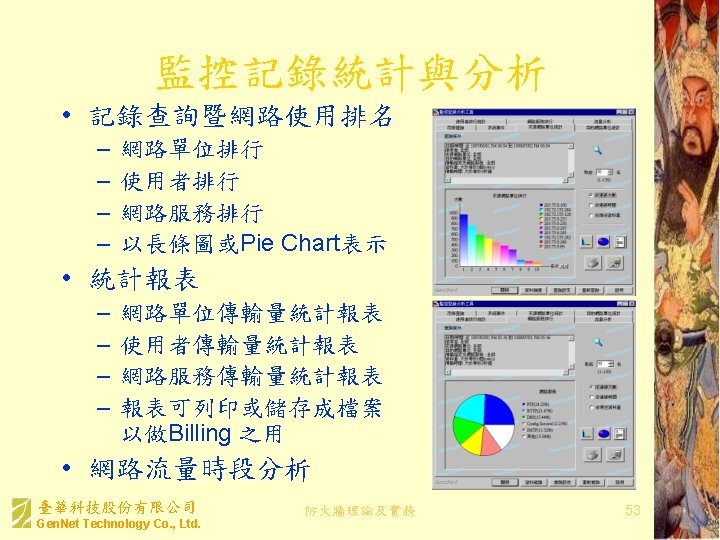
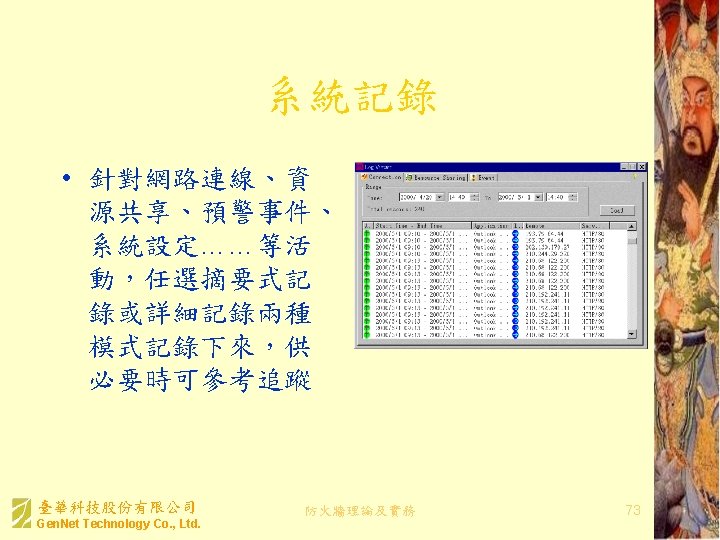
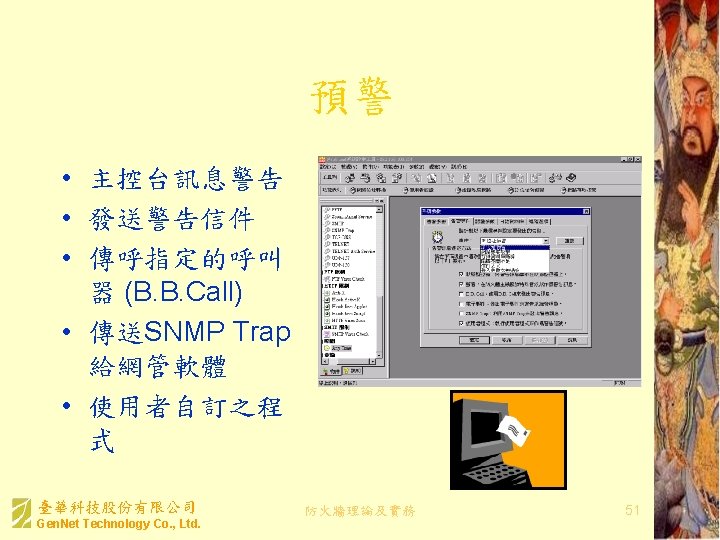
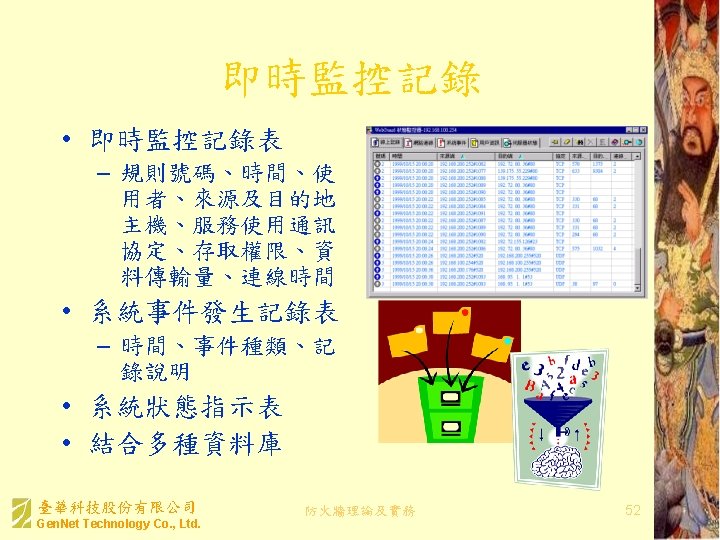
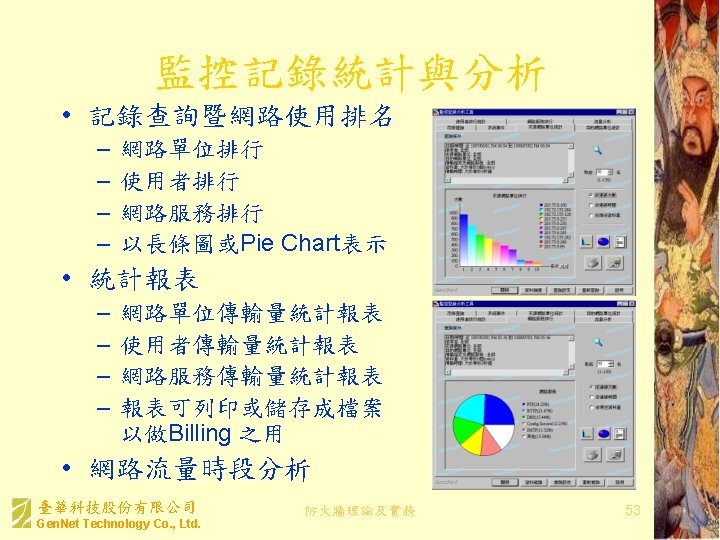
防火牆產品的常見功能 (2/2) • • • 網路位址轉換 (Network Address Translation) 虛擬私有網路 (Virtual Private Network) 預警 (Alert) 即時監控記錄 (Status Monitoring and Logging) 監控記錄統計與分析 (Accounting and Log Analysis) 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 36
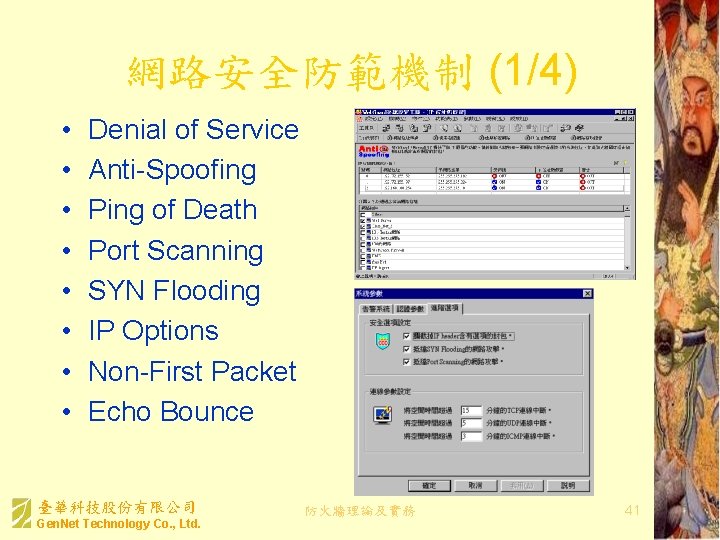
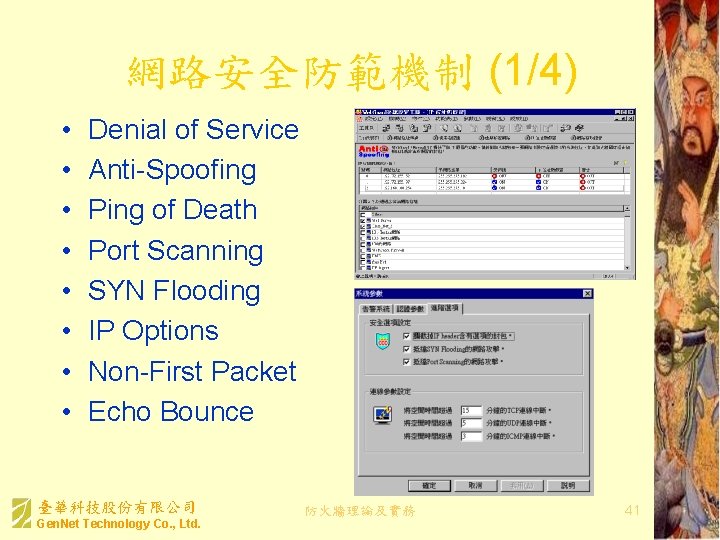
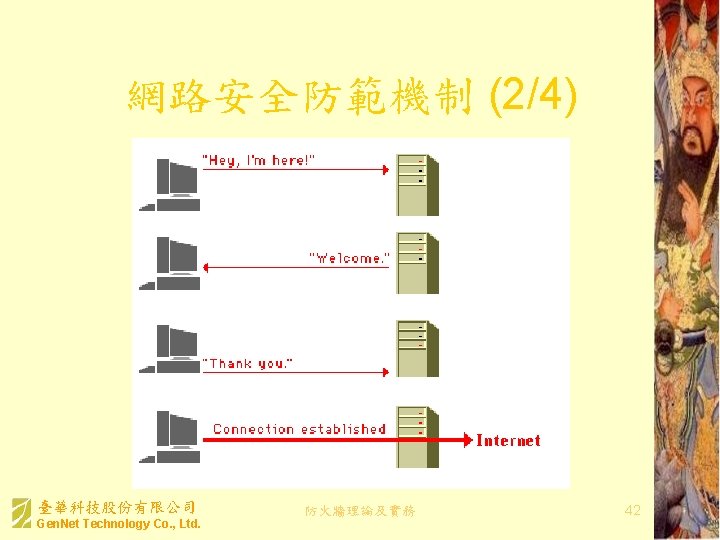
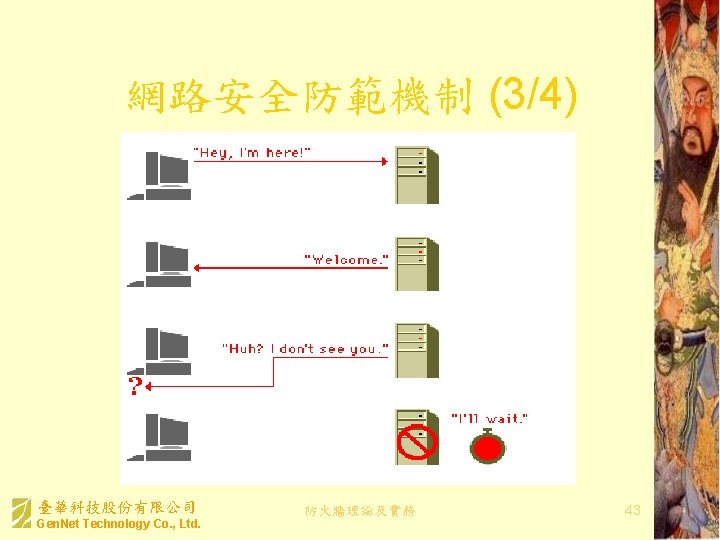
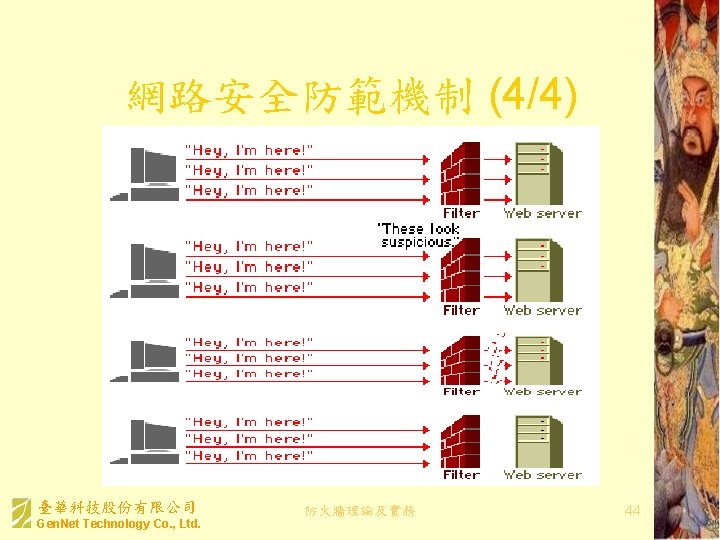
網路安全防範機制 (1/4) • • Denial of Service Anti-Spoofing Ping of Death Port Scanning SYN Flooding IP Options Non-First Packet Echo Bounce 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 41
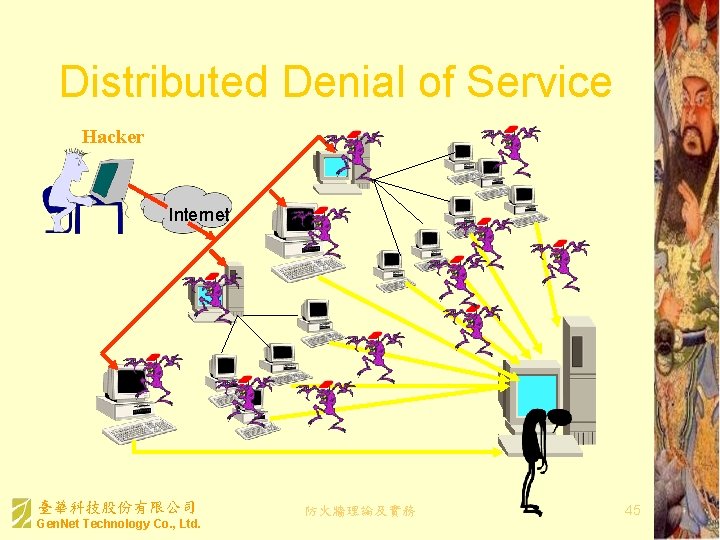
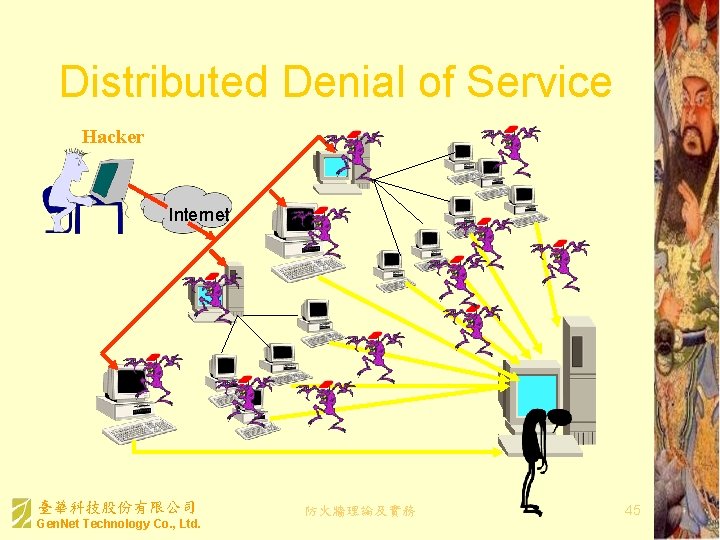
Distributed Denial of Service Hacker Internet 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 45

知名阻斷服務攻擊 • DOS – Bonk, Tear Drop – LAND – Jolt • DDOS – Trinoo – TFN, TFN 2 K – Stacheldraht • 新一代DOS – Code. Red – Nimda 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. XXXXXXXXXXXXXXXXX%u 9090%u 68 58%ucbd 3% u 7801%u 9090%u 6858%ucbd 3%u 7801%u 9090 %u 8190%u 00 c 3%u 0003%u 8 b 00%u 531 b%u 53 ff %u 0078%u 0000%u 00=a HTTP/1. 0" 400 - 防火牆理論及實務 46
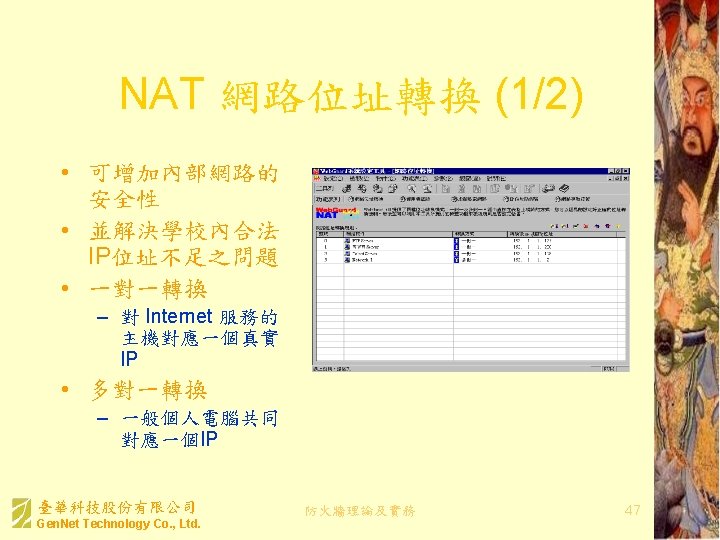
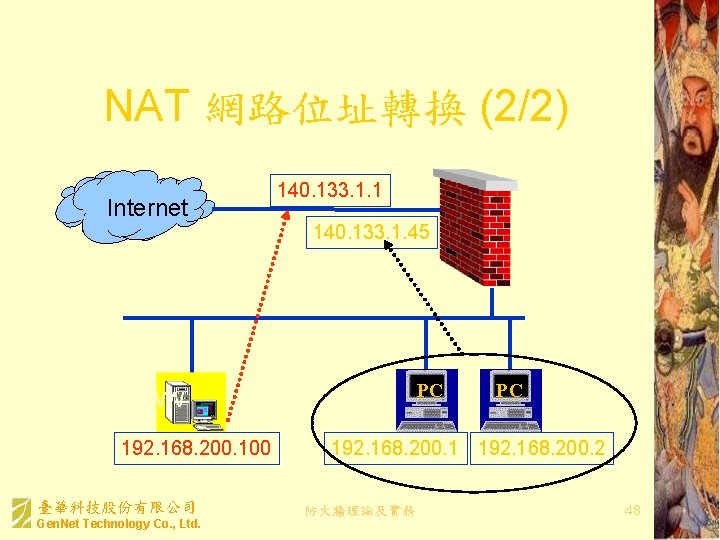
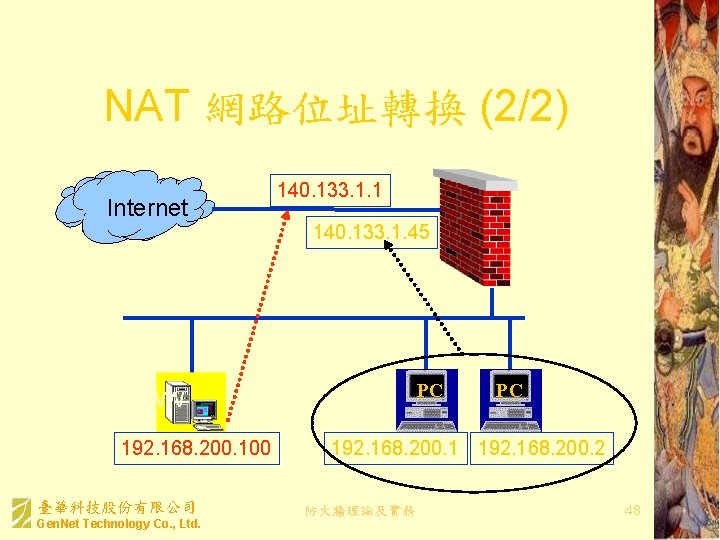
NAT 網路位址轉換 (2/2) Internet 140. 133. 1. 1 140. 133. 1. 45 PC WWW 192. 168. 200. 100 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. PC 192. 168. 200. 1 192. 168. 200. 2 防火牆理論及實務 48
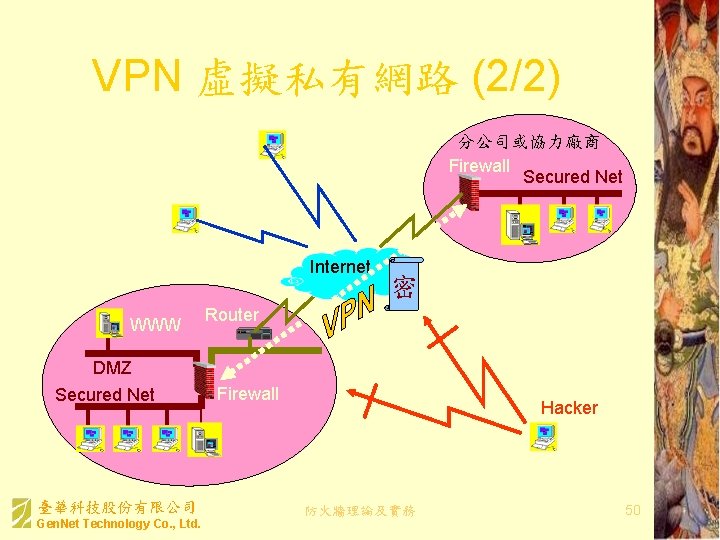
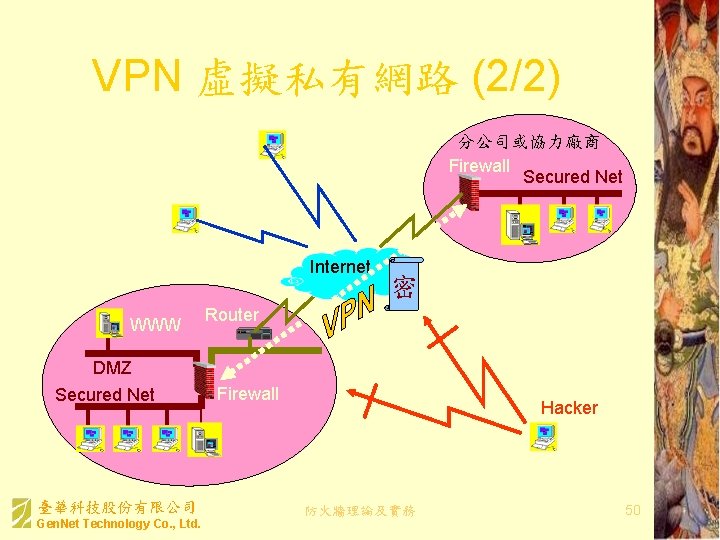
VPN 虛擬私有網路 (2/2) 分公司或協力廠商 Firewall Secured Net Mobile User Internet WWW DMZ Secured Net 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 密 Router Firewall Hacker 防火牆理論及實務 50
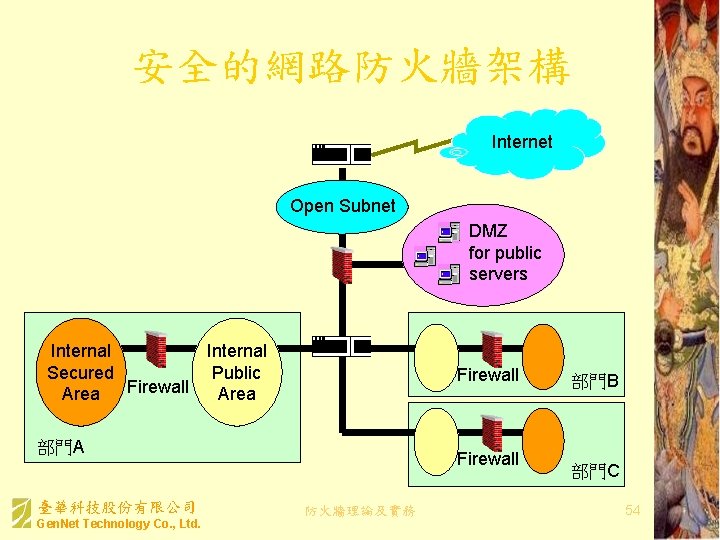
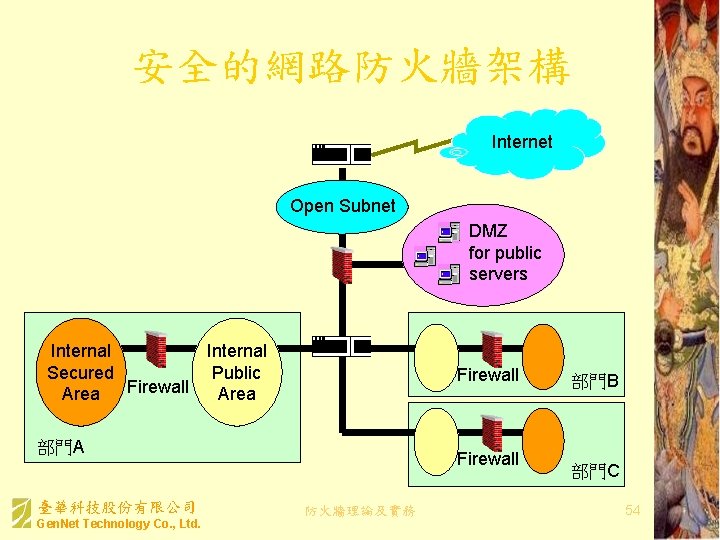
安全的網路防火牆架構 Internet Router Open Subnet Firewall Internal Secured Public Firewall Area Firewall 部門A 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. DMZ for public servers Firewall 防火牆理論及實務 部門B 部門C 54
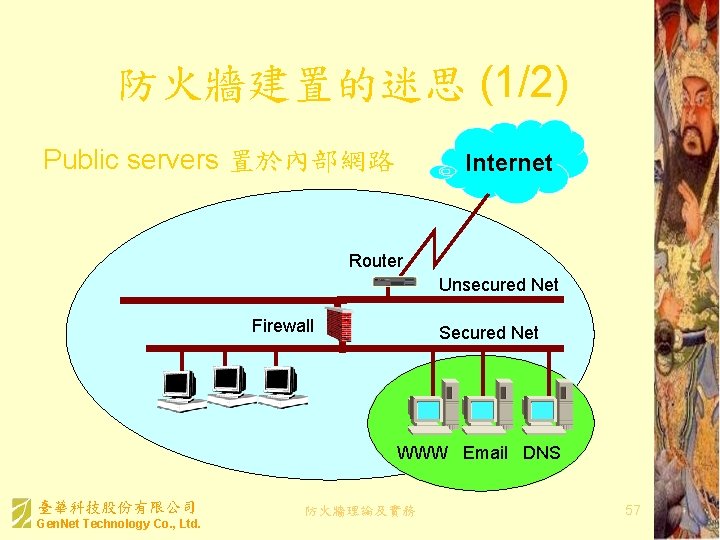
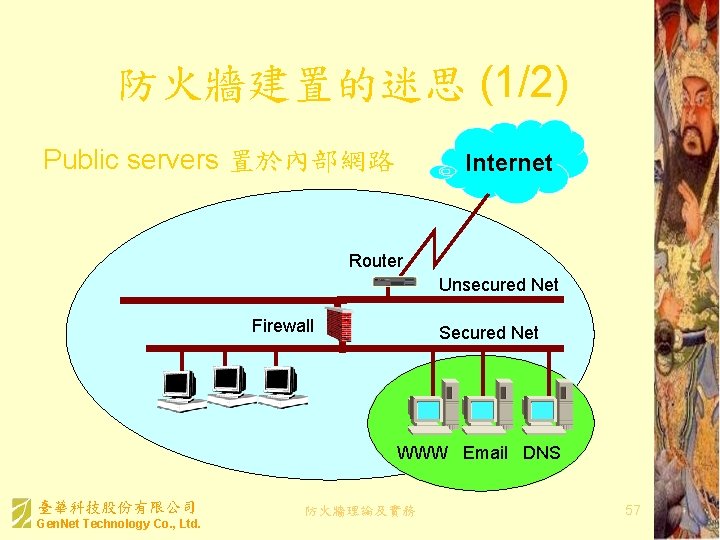
防火牆建置的迷思 (1/2) Public servers 置於內部網路 Internet Router Unsecured Net Firewall Secured Net WWW Email DNS 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 57
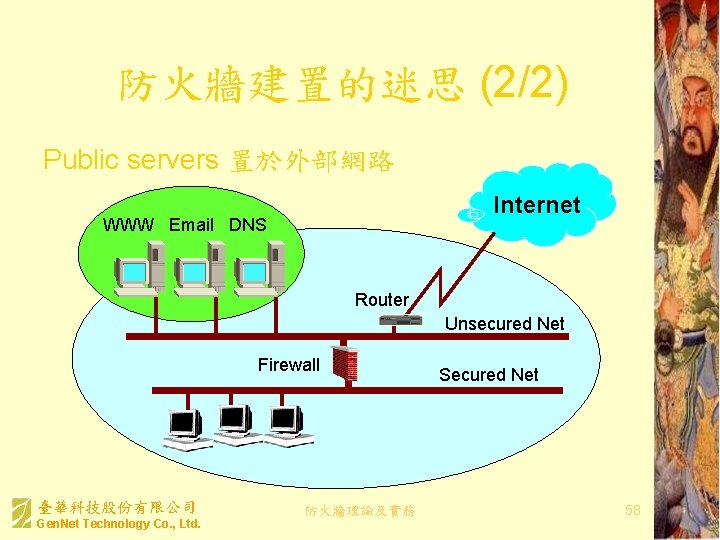
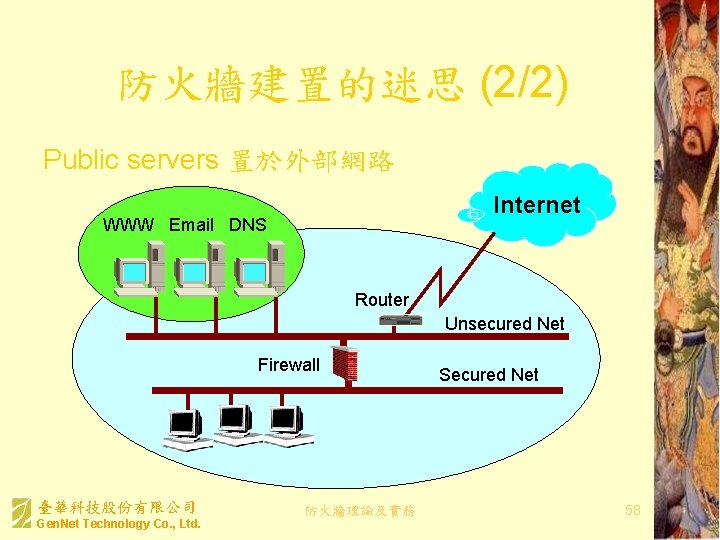
防火牆建置的迷思 (2/2) Public servers 置於外部網路 Internet WWW Email DNS Router Unsecured Net Firewall 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 Secured Net 58
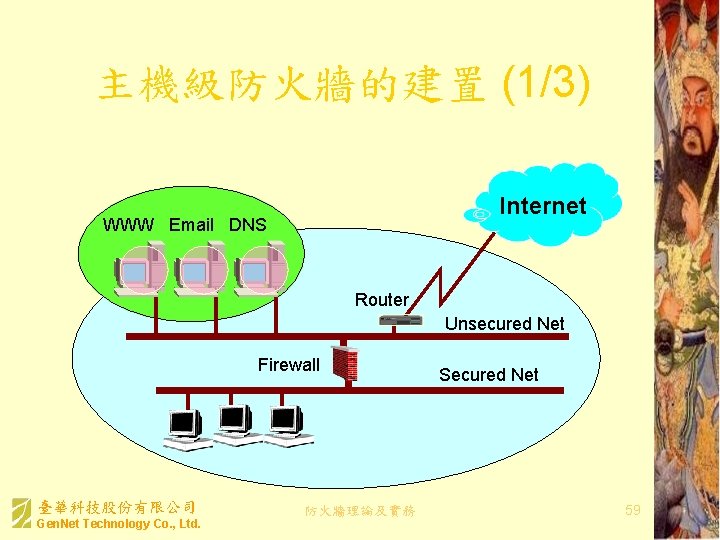
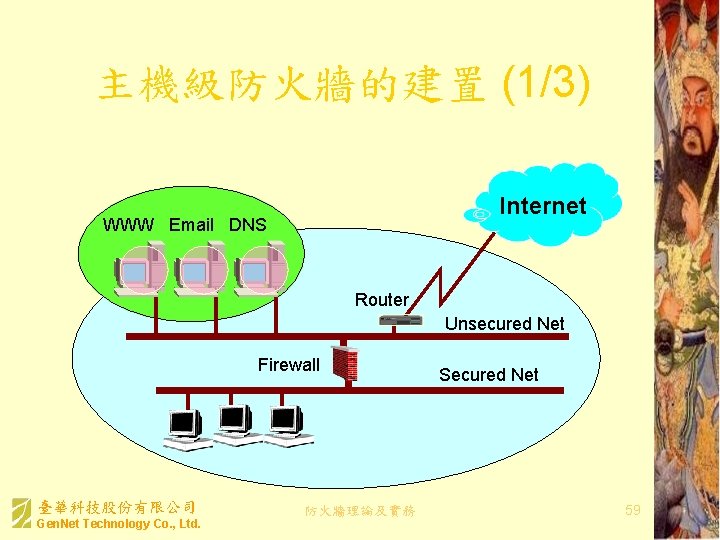
主機級防火牆的建置 (1/3) Internet WWW Email DNS Router Unsecured Net Firewall 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 Secured Net 59
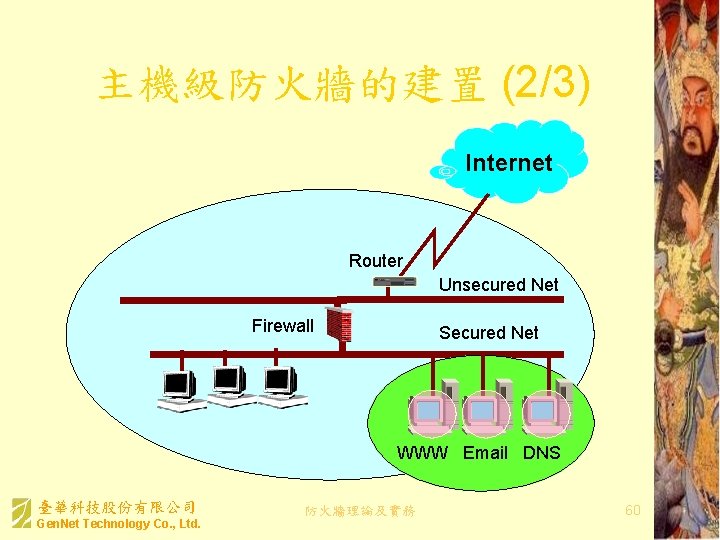
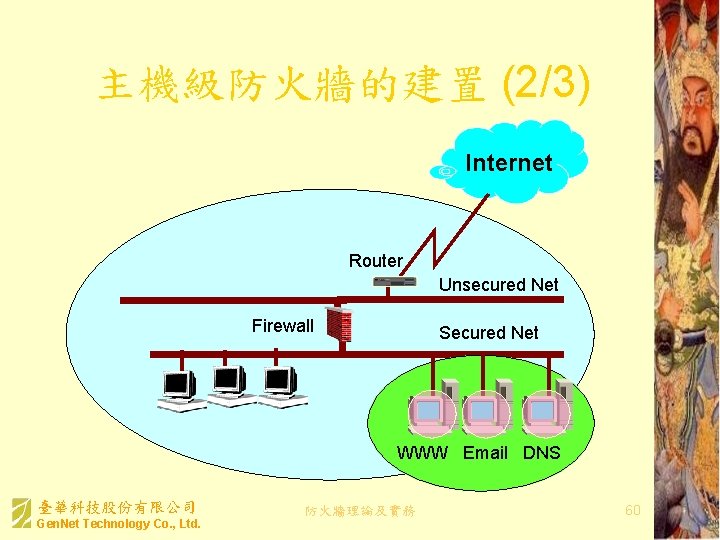
主機級防火牆的建置 (2/3) Internet Router Unsecured Net Firewall Secured Net WWW Email DNS 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 60
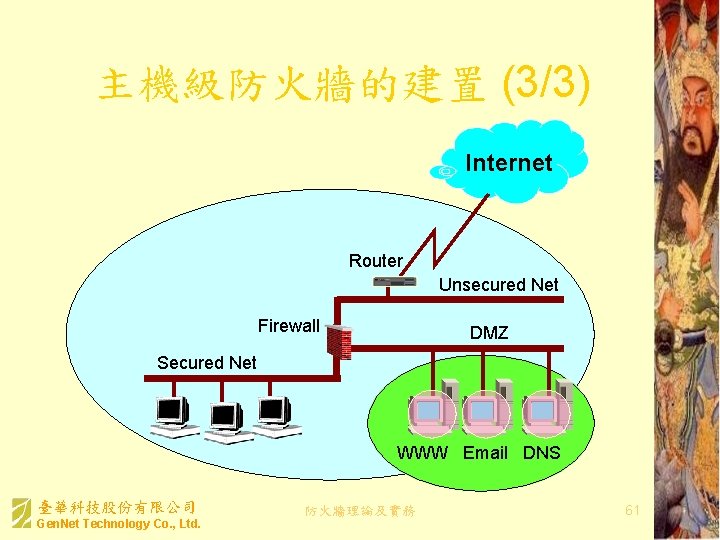
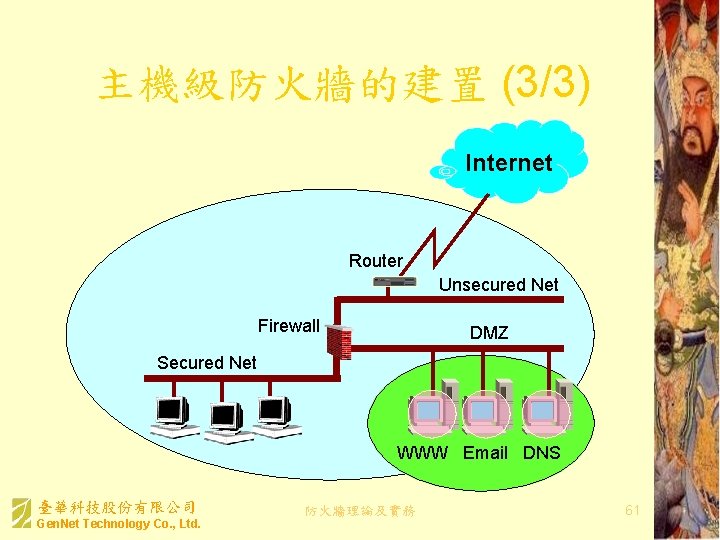
主機級防火牆的建置 (3/3) Internet Router Unsecured Net Firewall DMZ Secured Net WWW Email DNS 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. 防火牆理論及實務 61
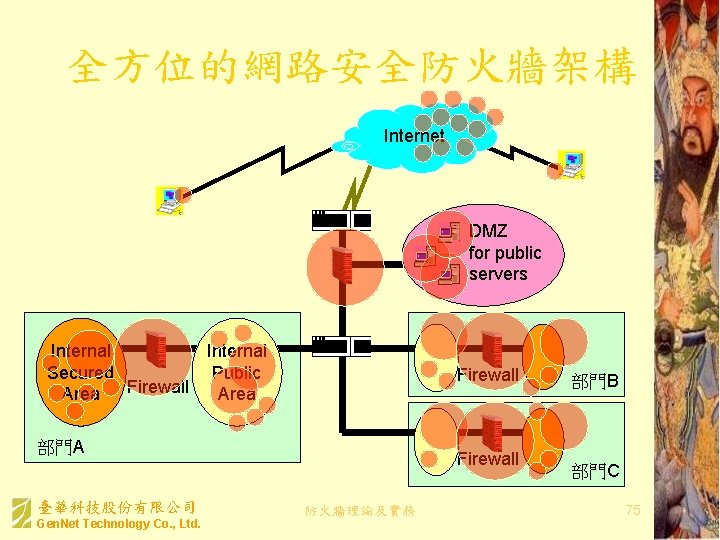
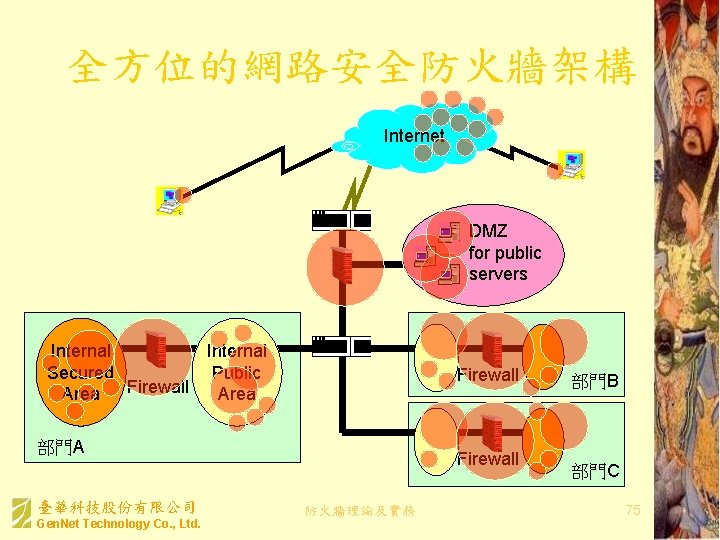
全方位的網路安全防火牆架構 Internet User Mobile User Router Firewall Internal Secured Public Firewall Area Firewall 部門A 臺華科技股份有限公司 Gen. Net Technology Co. , Ltd. DMZ for public servers Firewall 防火牆理論及實務 部門B 部門C 75