System Hacking Techniques BAI 514 Security I System
System Hacking Techniques BAI 514 – Security I
System Hacking Techniques �Once the pretest phases are complete, the next goal is to hack the target system �The goal is to completely “own” the target �This requires � Passwords � Active usernames � Highest level of permissions �This is achieved by exploiting common operating system vulnerabilities
System Hacking Techniques �To successfully hack a system you need to �Identify various password cracking techniques and tools �Understand escalation of privilege �Understand keyloggers and rootkits �Understand how to hide files, cover tracks, perform steganography, and erase evidence
Password Guessing �Password guessing is the first step to owning the target �Common passwords are � Password � Root � Administrator � Admin � operator � Demo � Test webmaster backup trial guest member private {blank}
Password Guessing �Password guessing can be done by creating a null share, using a known username �Good candidate accounts include �Accounts that have never been logged in �Accounts that haven’t had a password change in a while �Administrator �Guest net use * \target_ipshare * /u: name
Password Guessing �Automated Password Guessing �Guessing passwords is seldom easy �Attackers need to hit as many accounts and try as many passwords as possible �Can be done by creating a simple script that loops the guessing with NET USE C: > FOR /F “token=1, 2*” %i in (credentials. txt) do net use \targetIPC$ %i /u: %j credentials. txt = a username/password text file
Password Guessing �Automated Password Guessing (cont. ) �Drawbacks � Can cause a Do. S if a password lockout policy exists � Target the guest account first to see if a policy exists �Automated password guessing tools � Legion � Net. BIOS Auditing Tool
Password Guessing �Password Sniffing �Often a preferred tactic to password guessing �Credentials are sniffed off the wire �Once captured, credentials are simply replayed
Password Guessing �Password Sniffing (cont. ) �L 0 phtcrack (LC 5) � Password auditing and recovery application � Includes a sniffer to extract user credentials � Purchased by Symantec and discontinued �Kerb. Crack � Another useful password sniffer � Two parts � Kerb. Sniff – listens on port 88 � Kerbcrack – used to brute force passwords
Password Guessing �Password Sniffing (cont. ) �Other sniffers � Scoop. LM – sniffs for Windows LM/NTLM authentication � Has a built-in dictionary and brute force cracker � Dsniff – Collection of Unix tools for network auditing and pen testing � Wireshark � Sniffit – general purpose sniffer � Snort – IDS and sniffer � TCPDump/Win. Dump
Password Guessing �Alternate means for acquiring passwords �Dumpster diving � Post-it notes are great! �Shoulder Surfing � Watch a user login or enter a code � Take pictures/video if you can
Password Guessing �Keystroke loggers (keyloggers) �Intercept the targets keystrokes � Stored in a file to be read later � Transmit them to the hacker � All keystrokes are recorded � Lots of useful information! � Lots of useless information too. . .
Password Guessing �Keyloggers (cont. ) �Two types � Hardware � Require physical access to the computer � Most difficult to detect with anti-spyware/firewall � Software � Installed directly on the target system � Typically part of a trojan � Some include screen capture capabilities � Spector and PCSpy � Some include audio/video capture capabilities
Password Guessing �Keyloggers (cont. ) �Keylogging tools � ISpy. Now � Invisible keylogger � PC Activity Monitor � IKS Software keylogger � Key. Captor � Remote Spy
Privilege Escalation �Often the Administrator account and password cannot be obtained �The attacker will have to settle for accessing the network with a non-administrator account �The attacker will need to escalate the privileges for this account
Privilege Escalation �Privilege escalation tools must be executed on the local machine �Some can be executed remotely �OS patches can reduce the ability of these tools to function
Privilege Escalation �Privilege escalation tools must be executed on the local machine �Some can be executed remotely �OS patches can reduce the ability of these tools to function
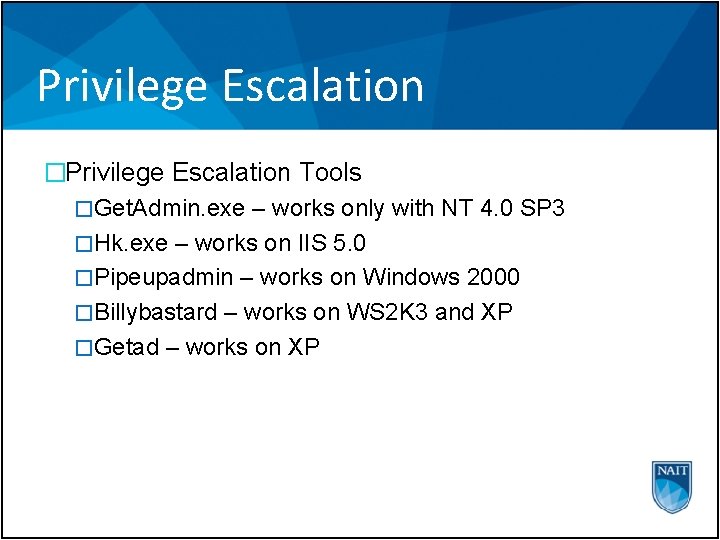
Privilege Escalation �Privilege Escalation Tools �Get. Admin. exe – works only with NT 4. 0 SP 3 �Hk. exe – works on IIS 5. 0 �Pipeupadmin – works on Windows 2000 �Billybastard – works on WS 2 K 3 and XP �Getad – works on XP
Password Cracking �Passwords are generally stored and transmitted in an encrypted form called a hash �When a user logs in, a password hash is generated and compared with a stored hash
Password Cracking �Prior to Windows NT 4. 0 SP 4, windows supported two kinds of challenge/response �Lan. Manager (LM) � Not case sensitive � Converts all characters to upper case � All passwords are stored as two 7 -character hashes � Passwords exactly 14 characters will be split into two 7 character hashes � Passwords fewer than 14 characters will be padded upto 14 characters, then split in two � Due to the mathematics of password cracking, it is easier to crack two 7 -character hashes than one 14 -character hash
Password Cracking �Lan. Manager (cont. ) � Example – password is “ 123456 qwerty” � Password converted to upper case � “ 123456 QWERTY” � Password is padded with NULL to 14 characters � “ 123456 QWERTY. . “ � Password split in two � “ 123456 Q” and “WERTY. . ” � Each half is hashed � “ 123456 Q” = 6 BF 11 E 04 AFAB 197 F � “WERTY. . ” = F 1 E 9 FFDCC 75575 B 15 � The two hashes are concatenated � 6 BF 11 E 04 AFAB 197 F F 1 E 9 FFDCC 75575 B 15
Password Cracking �NTLM � Uses all 14 characters � Allows upper and lowercase letters �The LM hash has been replaced with Win. NT Challenge/Response NTLMv 2 � Key space is now 128 bits �Windows 2000 SP 2 and later allowed the disabling of LAN Manager password storing
Password Cracking �Password Cracking Techniques �Once a hash is obtained, it can be cracked �Tools must be used to generate hashes until a match is found �Automated password crackers employ one or more types of password attacks � Brute force � Dictionary attack � Hybrid attack � Rainbow attack
Password Cracking �Password Cracking Techniques (cont. ) �Dictionary attack � Fastest method for generating hashes � Many dictionaries are available � Most tools include a base dictionary
Password Cracking �Password Cracking Techniques (cont. ) �Brute Force Attack � Most powerful method � Randomly generates passwords and their hashes � Can take a very long time (months, years? ) � All passwords can be cracked with brute force
Password Cracking �Password Cracking Techniques (cont. ) �Hybrid Attack � Builds on the dictionary method by adding numeric and symbolic characters to dictionary words � Examples � p@ssword � p@ssw 0 rd � p@55 w 0 rd
Password Cracking �Password Cracking Techniques (cont. ) �Rainbow Attack � Trades off the time-consuming process of creating all possible password hashes � Builds a hash table in advance � Extremely fast � Hash table is stored in order for rapid indexing of the target hash
Password Cracking �Stealing SAM �SAM file in Windows NT/2000/2003 contains the usernames and encrypted passwords �Located in: %systemroot%system 32config �The file is locked when the system is running � Boot the system from an alternate OS �Starting with Win. NT SP 3, a second layer of 128 -bit encryption was added called SYSKEY � This makes cracking the passwords MUCH harder
Password Cracking �Cracking Tools �Once password hashes have been collected, a password cracking tool can be used � L 0 phtcrack – mentioned earlier � John the Ripper – currently available for Unix, DOS, Win 32, Be. OS � Brutus – uses dictionary and brute force attacks � Ophcrack – uses Rainbow Tables � Rainbow. Crack – uses Rainbow Tables � Pwdump – password extraction tool that can bypass SYSKEY
Covering Tracks �Once a system has been compromised, the attacker is not finished. . . �The attacker must cover their tracks �Disable logging �Clear log files �Eliminate evidence �Plant additional tools
Covering Tracks �Disable Auditing �Auditpol. exe � Included in the Win. NT Resource Kit � Disables auditing c: >auditpol \10. 1. 1. 13 /disable �Once the system is compromised and all tools are installed, auditing can be enabled again
Covering Tracks �Clearing the Event Log �The attacker will want to clear the logs in Event Viewer �Tools � Eslave – clears the security log � This method will draw attention � Evidence Eliminator – very powerful, easy to use log cleanser � Winzapper – can erase event records selectively
Covering Tracks �Planting Rootkits �One of the goals of hacking is to allow the attacker to access the box at a later time �This can be done by installing a rootkit �Rootkit �A collection of software tools that a cracker uses to obtain administrator access to a computer or network � Can also monitor traffic, keystrokes, create backdoors, alter log files, attack other systems, alter existing tools to circumvent detection
Covering Tracks �Planting Rootkits �Ntrootkit � Can do all of the afore mentioned � Hide processes � Hide files � Hide registry entries � Intercept keystrokes � Issue a debug interrupt, causing a BSo. D � Redirect EXE files
Covering Tracks �File Hiding �Two ways of hiding files in Windows (other than rootkits) � File attributes � Attrib. exe +h [file/directory] � Using NTFS Alternate Data Streaming (ADS)
Countermeasures �Password guessing/cracking �Enforce 7 -12 character alphanumeric, upper/lower case, passwords �Force password changing on a regular basis �Physically isolate and protect servers �Use SYSKEY utility to store hashes on disk �Monitor server logs �Block access to TCP 135 -139 �Disable WINS �Log failed login attempts �Log successful login attempts
�File hiding/rootkits
FIN
- Slides: 38