Symbolic WordLevel Hardware Verification Randal E Bryant Carnegie
Symbolic, Word-Level Hardware Verification Randal E. Bryant Carnegie Mellon University http: //www. cs. cmu. edu/~bryant Contributions by graduate students: Sanjit Seshia, Shuvendu Lahiri
Outline Word-Level Abstraction of Hardware n Abstract details of data l While keeping detailed control and cycle-level timing n Enables verification of entire system Automated Formal Verification n n – 2– Provide capabilities similar to model checking Automate via automatic predicate abstraction
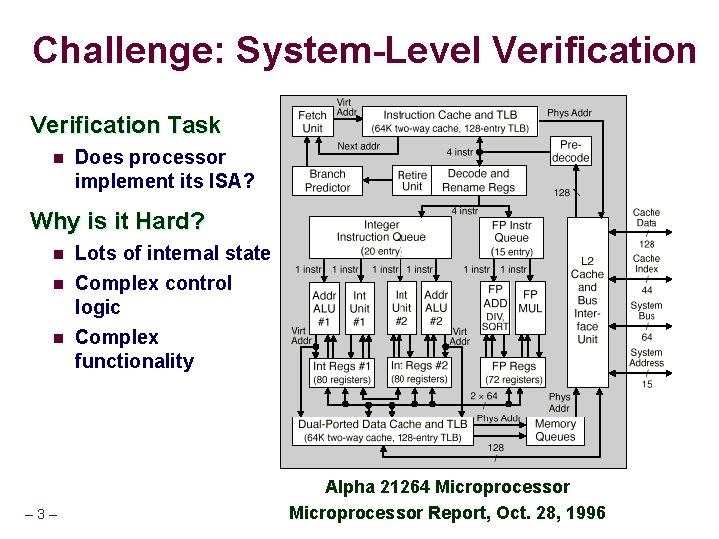
Challenge: System-Level Verification Task n Does processor implement its ISA? Why is it Hard? n n n – 3– Lots of internal state Complex control logic Complex functionality Alpha 21264 Microprocessor Report, Oct. 28, 1996
Sources of Complexity State n ISA: registers, memory n Microarchitectural: caches, buffers, reservation stations Conceptually finite state, but practically unbounded n Control n n Pipelines spread execution across multiple cycles Out-of-order execution modifies processing order Superscalar operation creates parallelism Control logic coordinates everything l Resulting behavior matches that of sequential ISA model Functionality n – 4– Arithmetic functions, instruction decoding
Existing Verification Methods n Simulators, equivalence checkers, model checkers, … All Operate at Bit Level n RTL model l State encoded as words and arrays of words l Comprised of bits Most Operate at Cycle or Subcycle Level n How each bit of state gets updated System Modeling Languages n n – 5– Abstract time up to transaction level Still view state as collection of bits
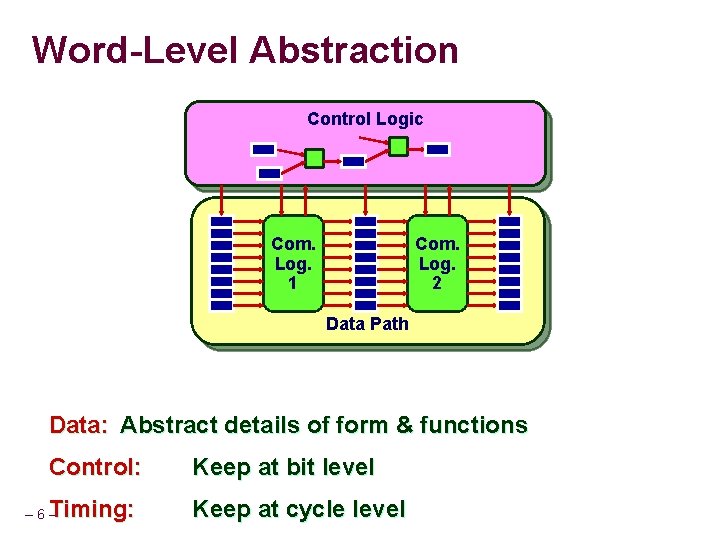
Word-Level Abstraction Control Logic Com. Log. 1 Com. Log. 2 Data Path Data: Abstract details of form & functions Control: Keep at bit level Timing: Keep at cycle level – 6–
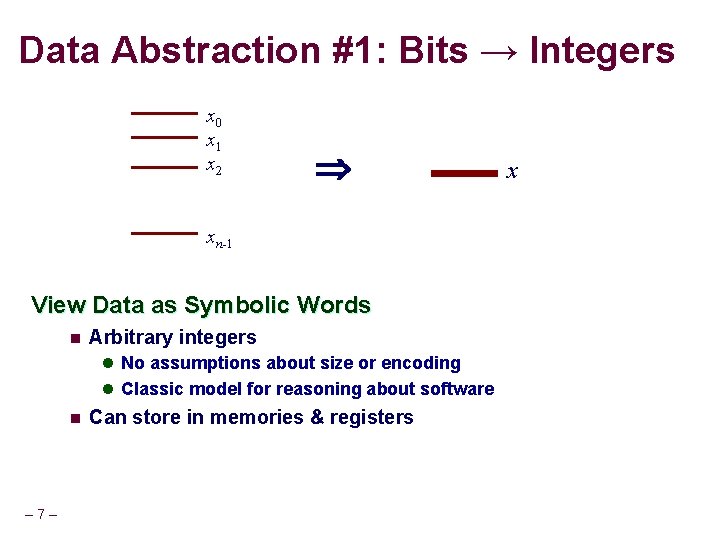
Data Abstraction #1: Bits → Integers x 0 x 1 x 2 xn-1 View Data as Symbolic Words n Arbitrary integers l No assumptions about size or encoding l Classic model for reasoning about software n – 7– Can store in memories & registers x
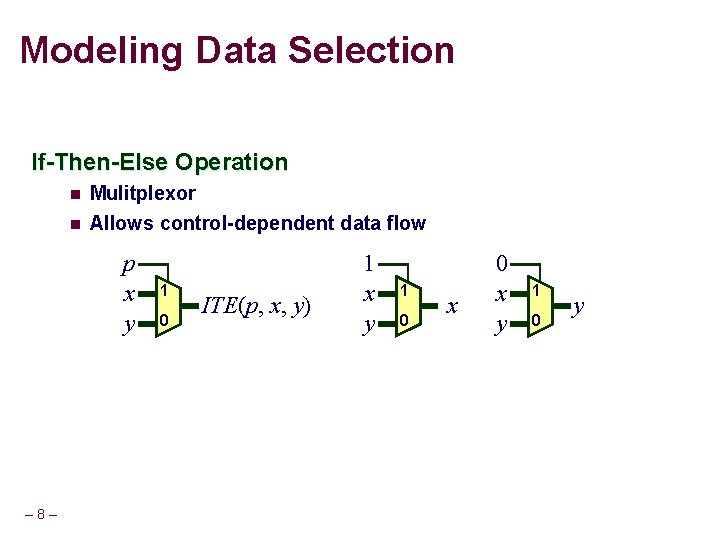
Modeling Data Selection If-Then-Else Operation n Mulitplexor n Allows control-dependent data flow p x y – 8– 1 0 ITE(p, x, y) 1 x y 1 0 y
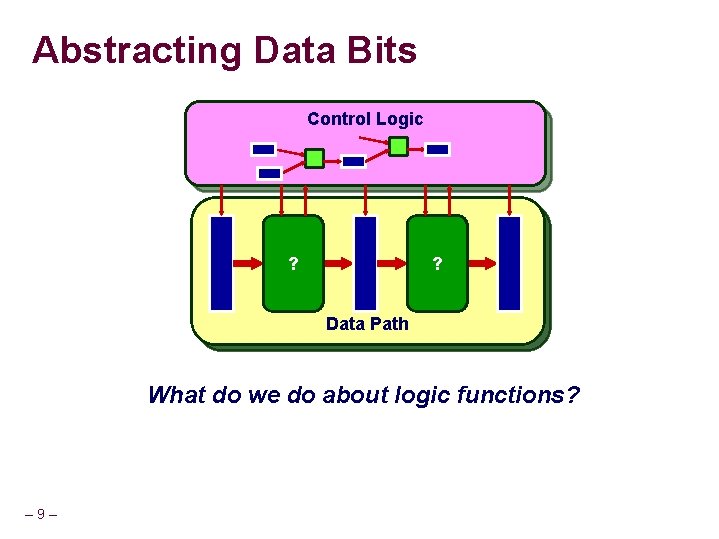
Abstracting Data Bits Control Logic Com. ? Log. 1 Com. ? Log. 2 1 Data Path What do we do about logic functions? – 9–
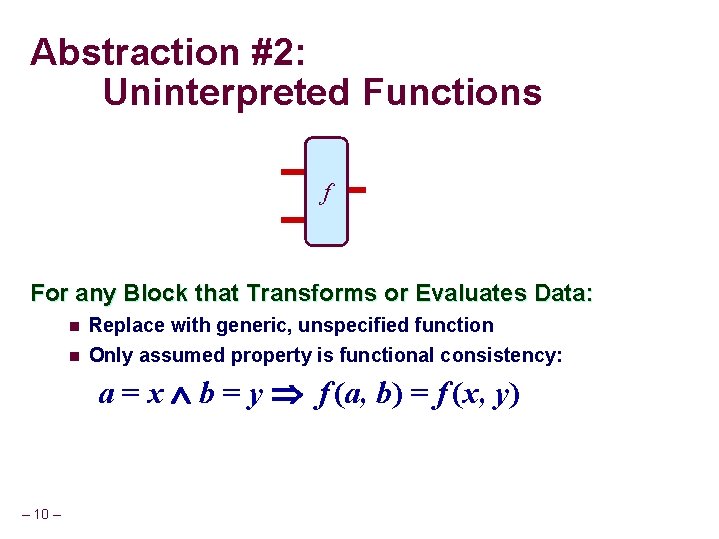
Abstraction #2: Uninterpreted Functions ALU f For any Block that Transforms or Evaluates Data: n Replace with generic, unspecified function n Only assumed property is functional consistency: a = x b = y f (a, b) = f (x, y) – 10 –
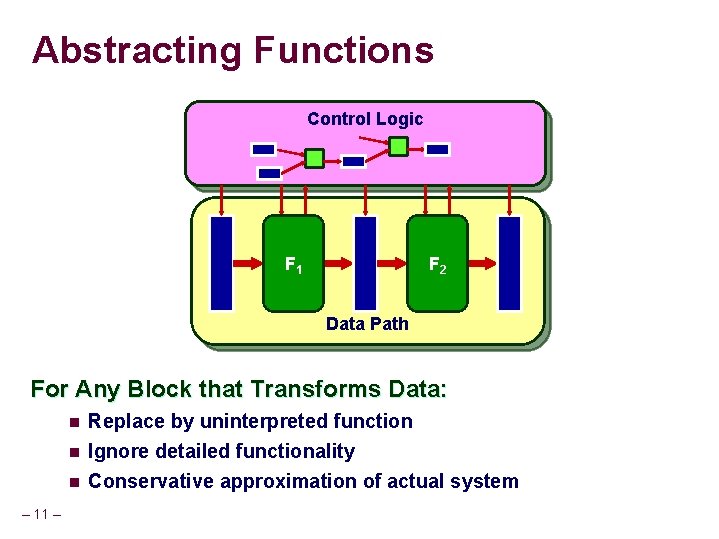
Abstracting Functions Control Logic Com. F 1 Log. 1 Com. F 2 Log. 1 Data Path For Any Block that Transforms Data: n Replace by uninterpreted function n Ignore detailed functionality Conservative approximation of actual system n – 11 –
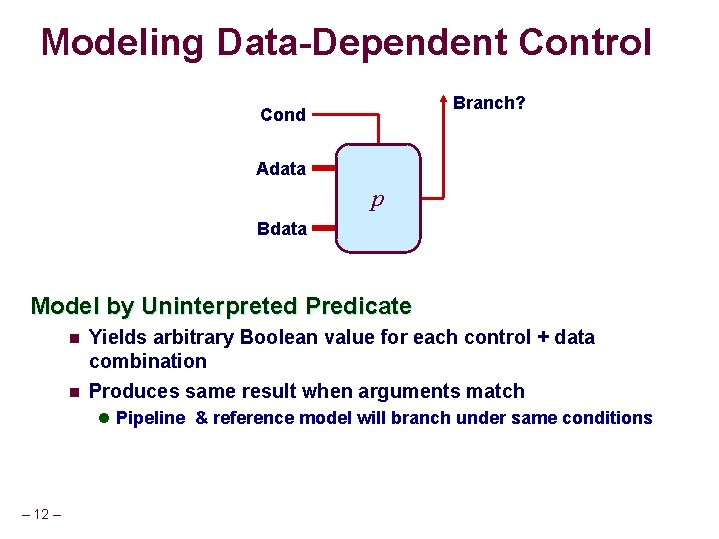
Modeling Data-Dependent Control Branch? Adata Branch Logic Cond p Bdata Model by Uninterpreted Predicate n n Yields arbitrary Boolean value for each control + data combination Produces same result when arguments match l Pipeline & reference model will branch under same conditions – 12 –
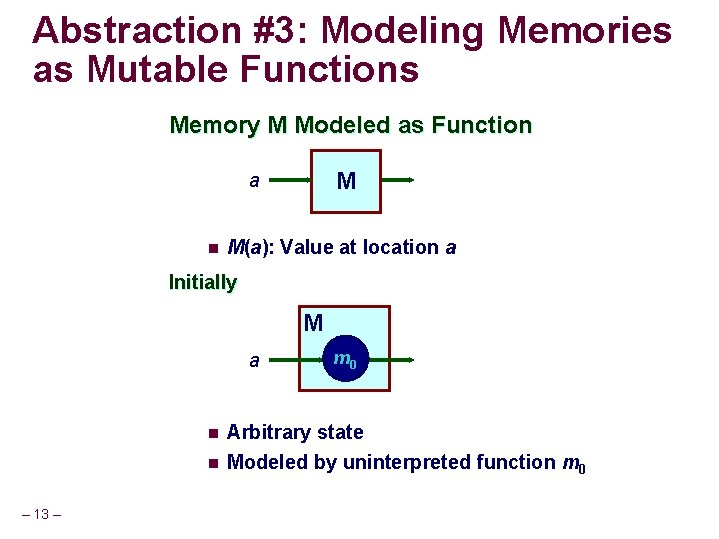
Abstraction #3: Modeling Memories as Mutable Functions Memory M Modeled as Function M a n M(a): Value at location a Initially M a n n – 13 – m 0 Arbitrary state Modeled by uninterpreted function m 0
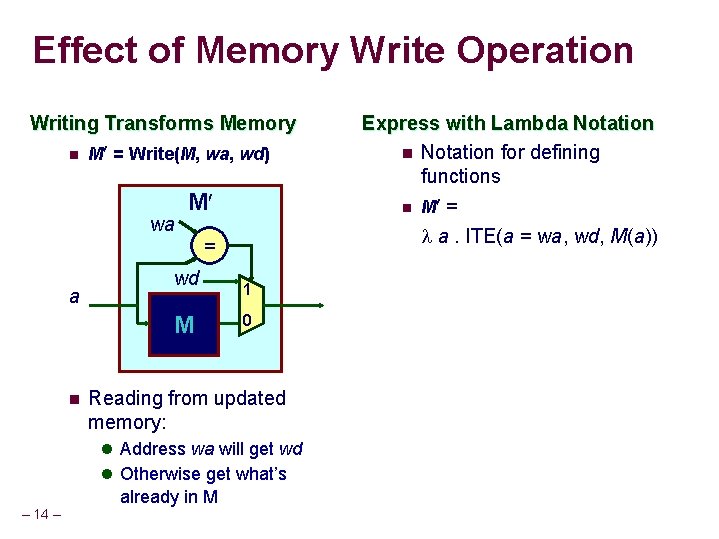
Effect of Memory Write Operation Writing Transforms Memory n M = Write(M, wa, wd) wa M = a wd M n 1 0 Reading from updated memory: l Address wa will get wd l Otherwise get what’s – 14 – already in M Express with Lambda Notation n Notation for defining functions n M = a. ITE(a = wa, wd, M(a))
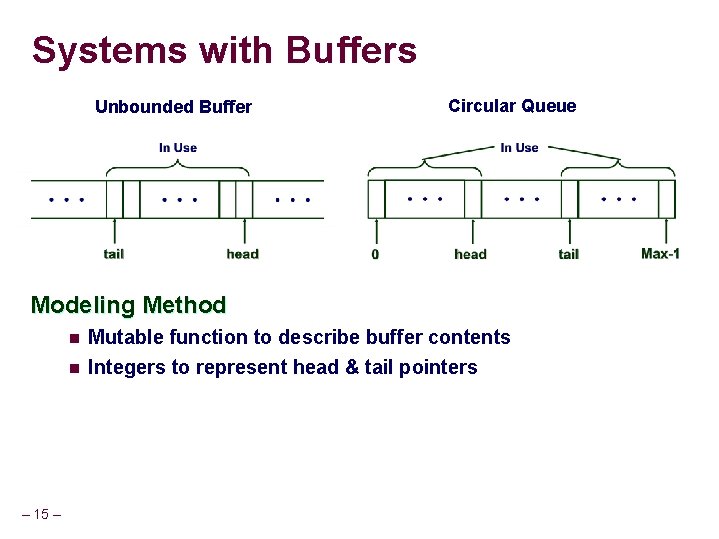
Systems with Buffers Unbounded Buffer Circular Queue Modeling Method – 15 – n Mutable function to describe buffer contents n Integers to represent head & tail pointers
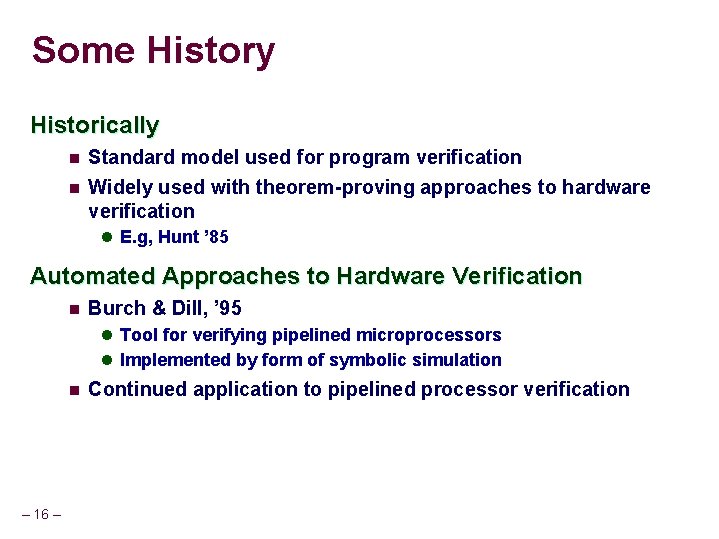
Some History Historically n Standard model used for program verification n Widely used with theorem-proving approaches to hardware verification l E. g, Hunt ’ 85 Automated Approaches to Hardware Verification n Burch & Dill, ’ 95 l Tool for verifying pipelined microprocessors l Implemented by form of symbolic simulation n – 16 – Continued application to pipelined processor verification
UCLID n Seshia, Lahiri, Bryant, CAV ‘ 02 Term-Level Verification System n Language for describing systems l Inspired by CMU SMV n Symbolic simulator l Generates integer expressions describing system state after sequence of steps n Decision procedure l Determines validity of formulas n Support for multiple verification techniques Available by Download http: //www. cs. cmu. edu/~uclid – 17 –
Challenge: Model Generation n n How to generate term-level model How to guarantee faithfulness to RTL description Comparison of Models n RTL l Abstracts functional elements from gate-level model l Synthesis allows automatic map to gate level n Term level l Abstracts bit-level data representations to words l Abstracts memories to mutable functions l No direct connection to synthesizable model – 18 –
Generating Term-Level Model Manually Generate from RTL n How do we know it is a valid abstraction? n Hard to keep consistent with changing RTL Automatically Generate from RTL n n Andraus & Sakallah, DAC ‘ 04 Must decide which signals to keep Boolean, which to abstract l Confused by bit field extraction primitives of HDL Synthesize RTL from Word-Level Model n – 19 – Difficult to make efficient
Underlying Logic Existing Approaches to Formal Verification n E. g. , symbolic model checking n State encoded as fixed set of bits l Finite state system l Amenable to Boolean methods (SAT, BDDs) Our Task n State encoded with unbounded data types l Arbitrary integers l Functions over integers n Must use decision procedures l Determine validity of formula in some subset of first-order logic l Adapt methods historically used by automated theorem provers – 20 –
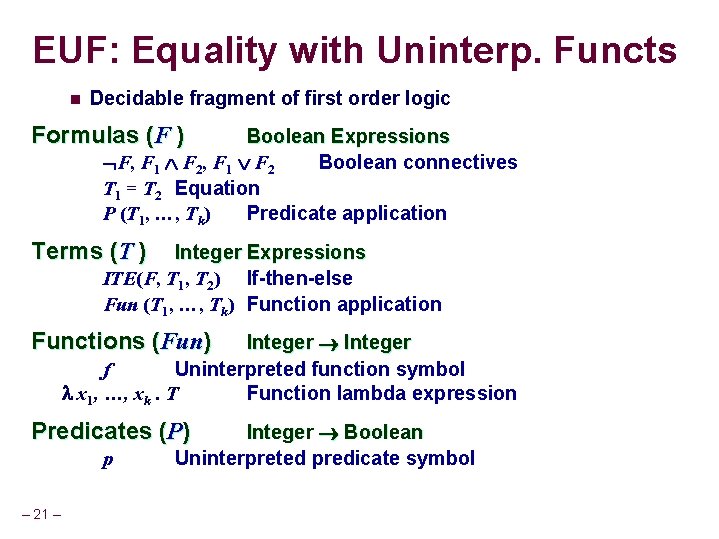
EUF: Equality with Uninterp. Functs n Decidable fragment of first order logic Formulas (F ) Boolean Expressions F, F 1 F 2 Boolean connectives T 1 = T 2 Equation P (T 1, …, Tk) Predicate application Terms (T ) Integer Expressions ITE(F, T 1, T 2) If-then-else Fun (T 1, …, Tk) Function application Functions (Fun) Integer f Uninterpreted function symbol x 1, …, xk. T Function lambda expression Predicates (P) p – 21 – Integer Boolean Uninterpreted predicate symbol
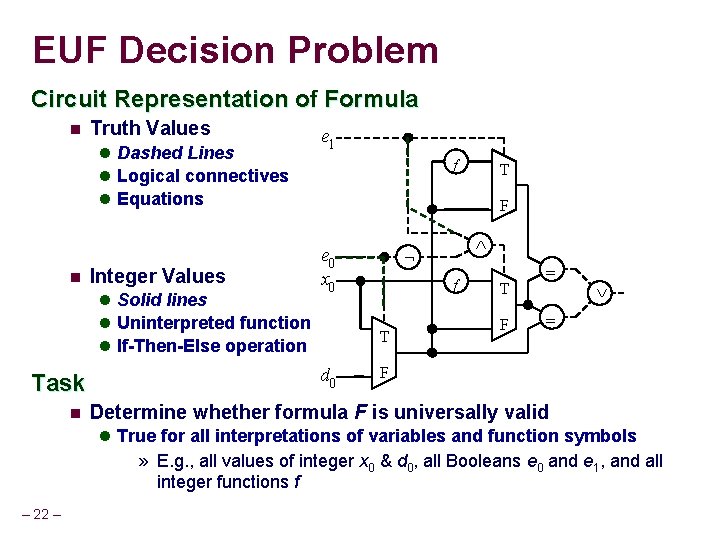
EUF Decision Problem Circuit Representation of Formula n Truth Values l Dashed Lines l Logical connectives l Equations n Integer Values l Solid lines l Uninterpreted functions l If-Then-Else operation Task n e 1 ff T F e 0 x 0 ff T d 0 ÙÙ ØØ T F == ÚÚ == F Determine whether formula F is universally valid l True for all interpretations of variables and function symbols » E. g. , all values of integer x 0 & d 0, all Booleans e 0 and e 1, and all integer functions f – 22 –
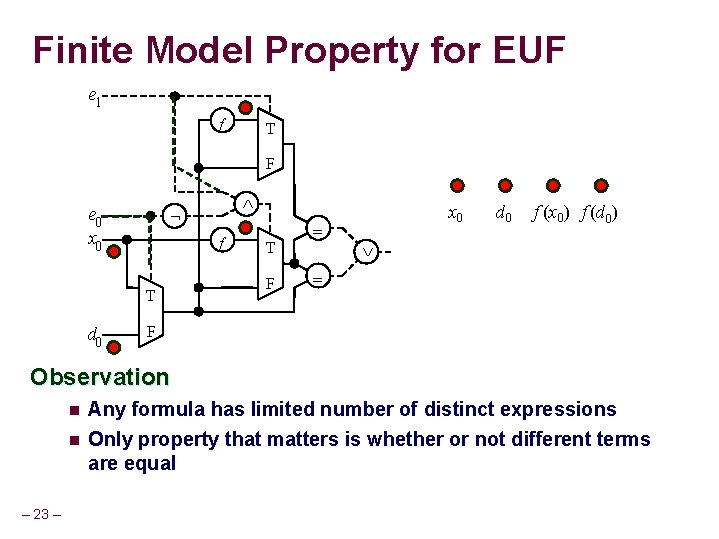
Finite Model Property for EUF e 1 ff T F ØØ e 0 x 0 ff T d 0 ÙÙ T F == x 0 d 0 f (x 0) f (d 0) ÚÚ == F Observation – 23 – n Any formula has limited number of distinct expressions n Only property that matters is whether or not different terms are equal
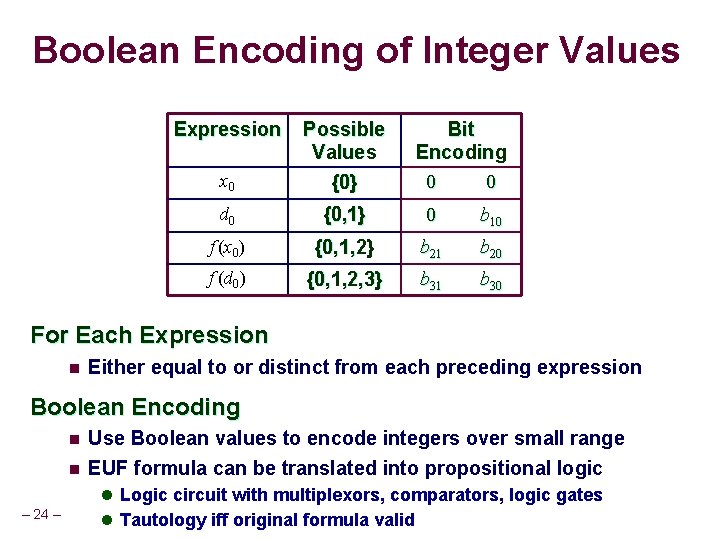
Boolean Encoding of Integer Values Expression x 0 Possible Values {0} Bit Encoding 0 0 d 0 {0, 1} 0 b 10 f (x 0) {0, 1, 2} b 21 b 20 f (d 0) {0, 1, 2, 3} b 31 b 30 For Each Expression n Either equal to or distinct from each preceding expression Boolean Encoding n n Use Boolean values to encode integers over small range EUF formula can be translated into propositional logic l Logic circuit with multiplexors, comparators, logic gates – 24 – l Tautology iff original formula valid
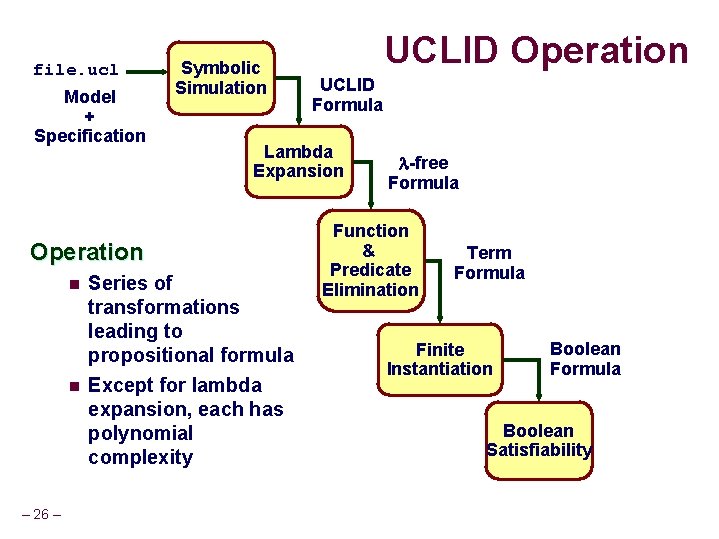
file. ucl Model + Specification Symbolic Simulation n – 26 – UCLID Formula Lambda Expansion Operation n UCLID Operation Series of transformations leading to propositional formula Except for lambda expansion, each has polynomial complexity -free Formula Function & Predicate Elimination Term Formula Finite Instantiation Boolean Formula Boolean Satisfiability
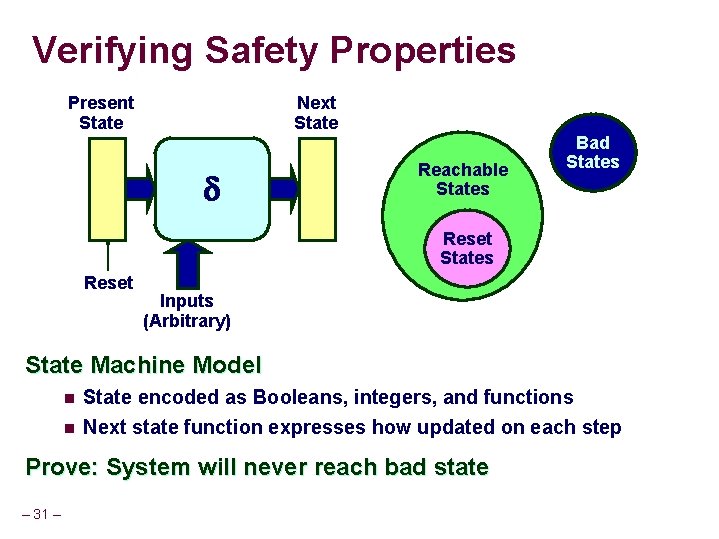
Verifying Safety Properties Present State Next State Reachable States Bad States Reset Inputs (Arbitrary) State Machine Model n State encoded as Booleans, integers, and functions n Next state function expresses how updated on each step Prove: System will never reach bad state – 31 –
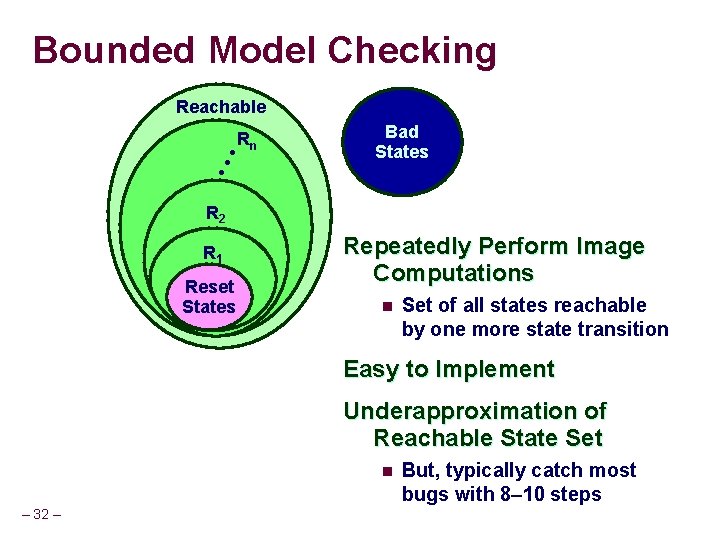
Bounded Model Checking Reachable Bad States • • • Rn R 2 R 1 Reset States Repeatedly Perform Image Computations n Set of all states reachable by one more state transition Easy to Implement Underapproximation of Reachable State Set n – 32 – But, typically catch most bugs with 8– 10 steps
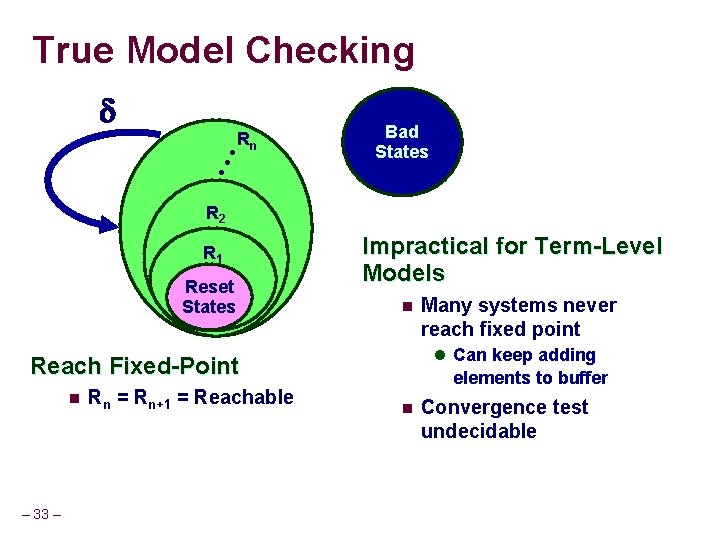
True Model Checking Bad States • • • Rn R 2 R 1 Reset States Impractical for Term-Level Models n l Can keep adding Reach Fixed-Point n – 33 – Rn = Rn+1 = Reachable Many systems never reach fixed point elements to buffer n Convergence test undecidable
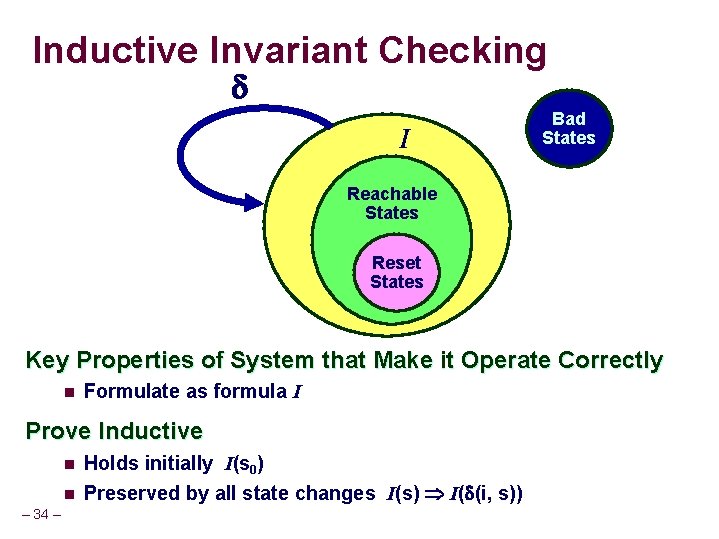
Inductive Invariant Checking I Bad States Reachable States Reset States Key Properties of System that Make it Operate Correctly n Formulate as formula I Prove Inductive n n – 34 – Holds initially I(s 0) Preserved by all state changes I(s) I( (i, s))
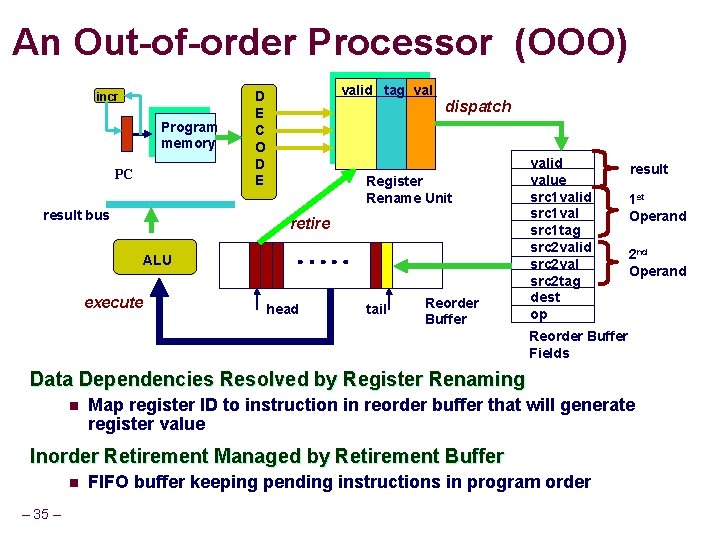
An Out-of-order Processor (OOO) incr Program memory PC result bus valid tag val D E C O D E dispatch Register Rename Unit retire ALU execute head tail Reorder Buffer valid value src 1 valid src 1 val src 1 tag src 2 valid src 2 val src 2 tag dest op result 1 st Operand 2 nd Operand Reorder Buffer Fields Data Dependencies Resolved by Register Renaming n Map register ID to instruction in reorder buffer that will generate register value Inorder Retirement Managed by Retirement Buffer n – 35 – FIFO buffer keeping pending instructions in program order
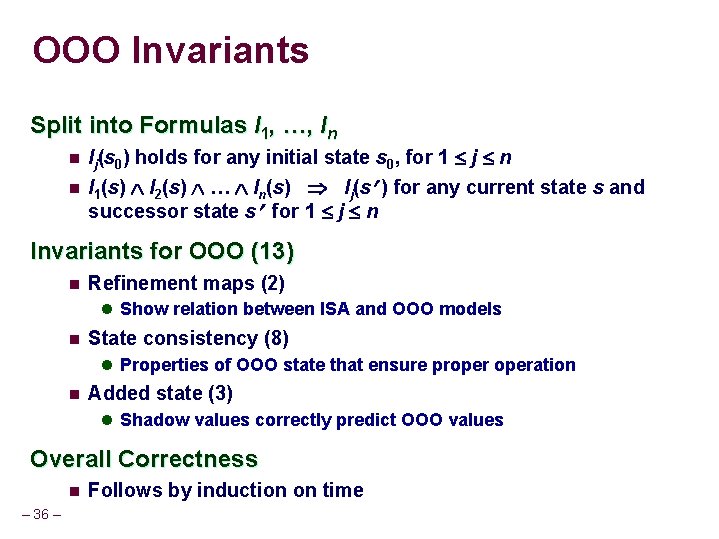
OOO Invariants Split into Formulas I 1, …, In n Ij(s 0) holds for any initial state s 0, for 1 j n I 2(s) … In(s) Ij(s ) for any current state s and successor state s for 1 j n n I 1(s) Invariants for OOO (13) n Refinement maps (2) l Show relation between ISA and OOO models n State consistency (8) l Properties of OOO state that ensure properation n Added state (3) l Shadow values correctly predict OOO values Overall Correctness n – 36 – Follows by induction on time
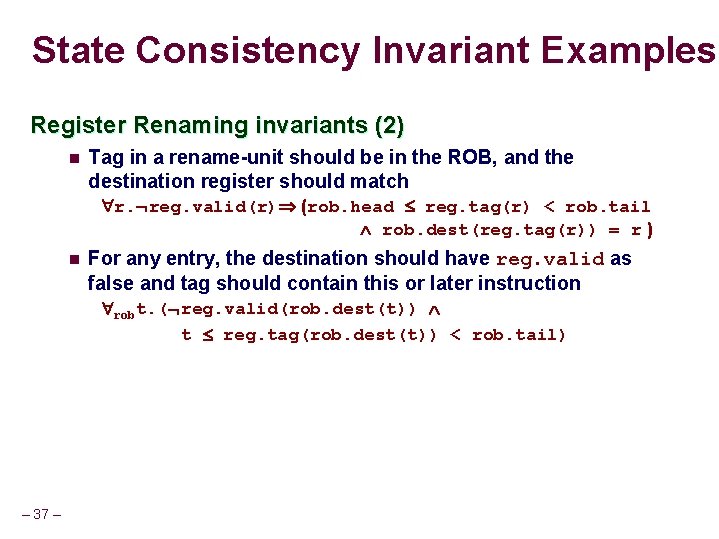
State Consistency Invariant Examples Register Renaming invariants (2) n Tag in a rename-unit should be in the ROB, and the destination register should match r. reg. valid(r) (rob. head reg. tag(r) < rob. tail rob. dest(reg. tag(r)) = r ) n For any entry, the destination should have reg. valid as false and tag should contain this or later instruction robt. ( reg. valid(rob. dest(t)) t reg. tag(rob. dest(t)) < rob. tail) – 37 –
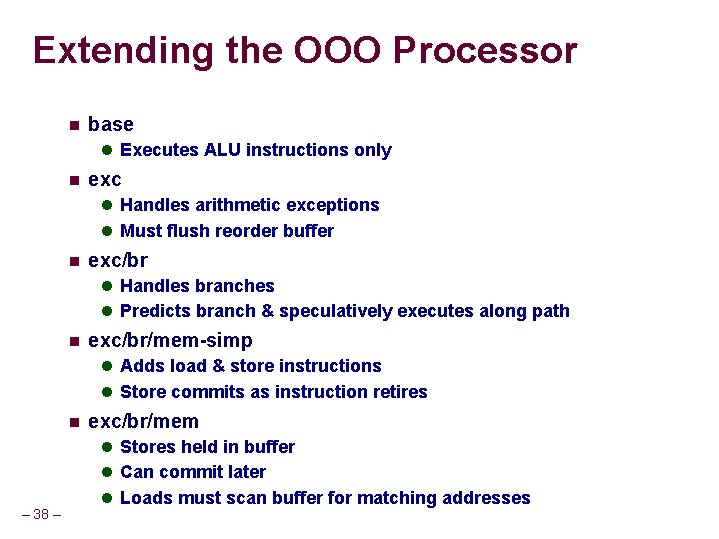
Extending the OOO Processor n base l Executes ALU instructions only n exc l Handles arithmetic exceptions l Must flush reorder buffer n exc/br l Handles branches l Predicts branch & speculatively executes along path n exc/br/mem-simp l Adds load & store instructions l Store commits as instruction retires n exc/br/mem l Stores held in buffer l Can commit later – 38 – l Loads must scan buffer for matching addresses
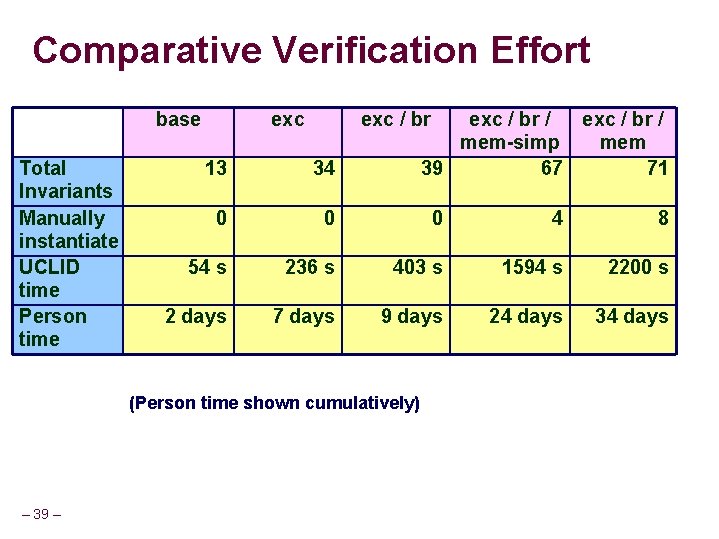
Comparative Verification Effort base Total Invariants Manually instantiate UCLID time Person time exc / br / mem-simp mem 39 67 71 13 34 0 0 0 4 8 54 s 236 s 403 s 1594 s 2200 s 2 days 7 days 9 days 24 days 34 days (Person time shown cumulatively) – 39 –
“I Just Want a Loaf of Bread” Ingredients Recipe – 40 – Result
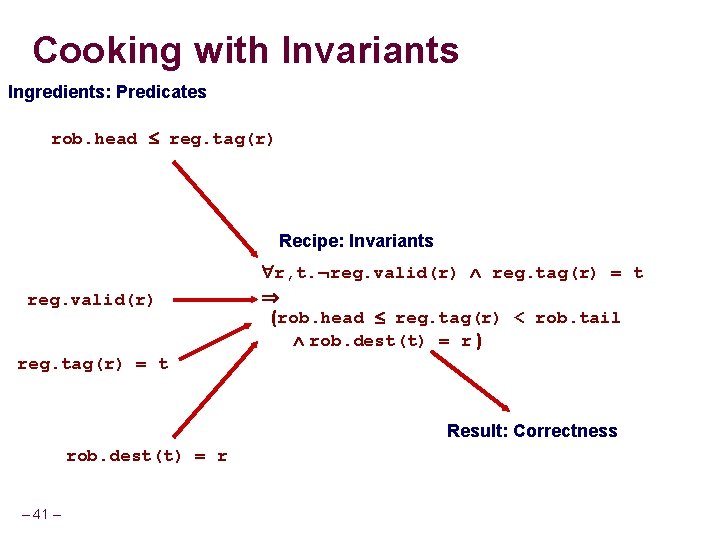
Cooking with Invariants Ingredients: Predicates rob. head reg. tag(r) Recipe: Invariants reg. valid(r) r, t. reg. valid(r) reg. tag(r) = t (rob. head reg. tag(r) < rob. tail rob. dest(t) = r ) reg. tag(r) = t Result: Correctness rob. dest(t) = r – 41 –
Automatic Recipe Generation Ingredients Recipe Creator Result Want Something More n n – 42 – Given any set of ingredients Generate best recipe possible
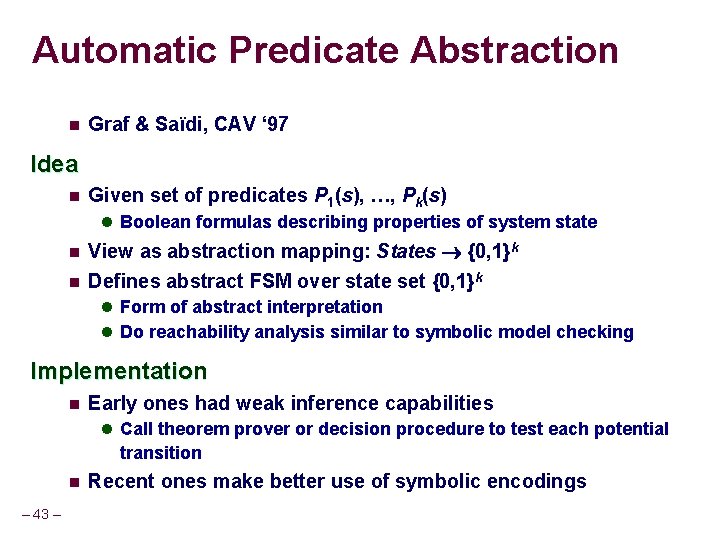
Automatic Predicate Abstraction n Graf & Saïdi, CAV ‘ 97 Idea n Given set of predicates P 1(s), …, Pk(s) l Boolean formulas describing properties of system state n n View as abstraction mapping: States {0, 1}k Defines abstract FSM over state set {0, 1}k l Form of abstract interpretation l Do reachability analysis similar to symbolic model checking Implementation n Early ones had weak inference capabilities l Call theorem prover or decision procedure to test each potential transition n – 43 – Recent ones make better use of symbolic encodings
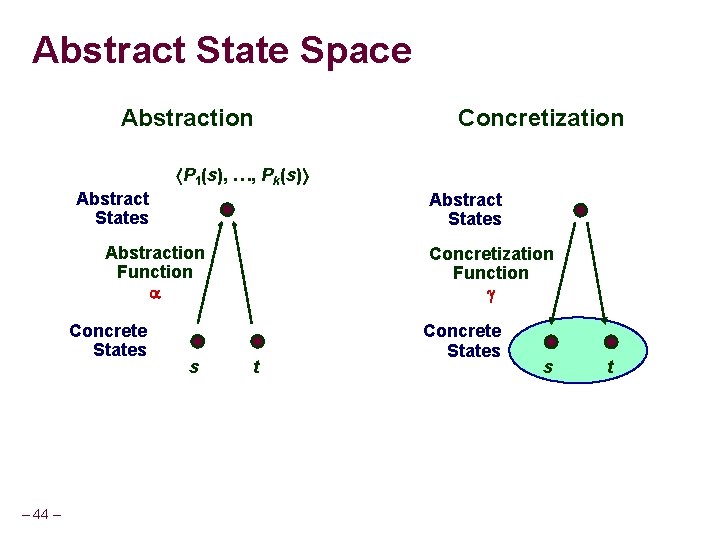
Abstract State Space Abstraction Concretization P 1(s), …, Pk(s) Abstract States Abstraction Function Concrete States – 44 – s Concretization Function t Concrete States s t
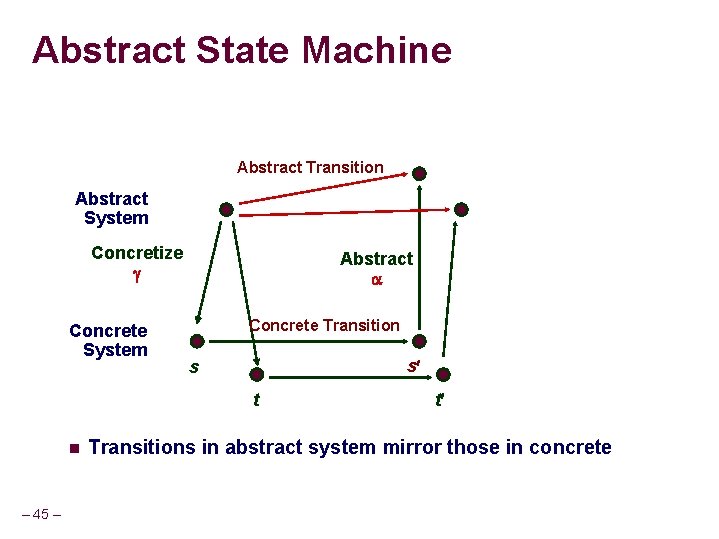
Abstract State Machine Abstract Transition Abstract System Concretize Concrete System Abstract Concrete Transition s s t n – 45 – t Transitions in abstract system mirror those in concrete
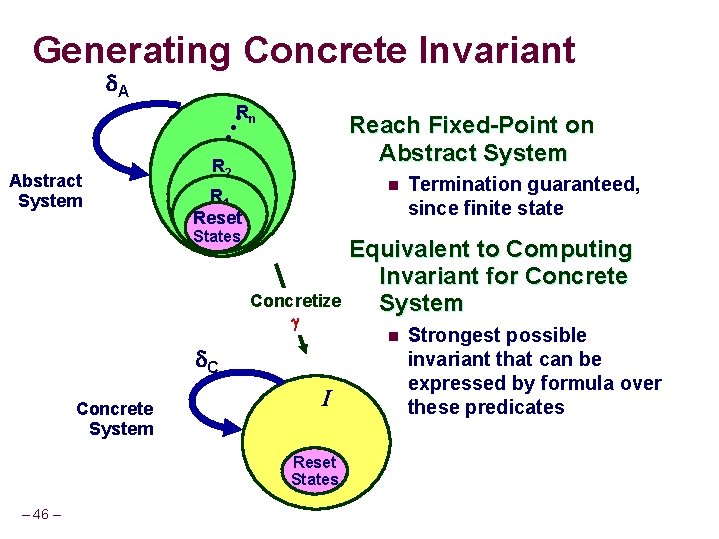
Generating Concrete Invariant A Rn • • • Reach Fixed-Point on Abstract System R 2 n R 1 Reset States Concretize C Concrete System I Reset States – 46 – Termination guaranteed, since finite state Equivalent to Computing Invariant for Concrete System n Strongest possible invariant that can be expressed by formula over these predicates
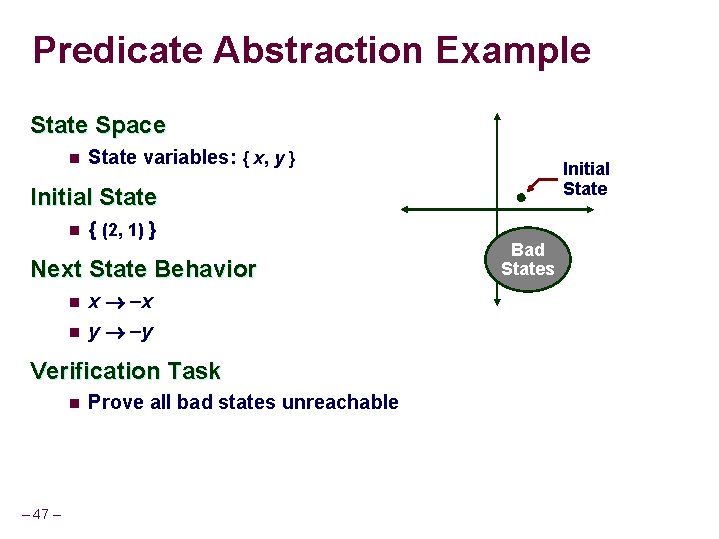
Predicate Abstraction Example State Space n State variables: { x, y } Initial State n { (2, 1) } Next State Behavior n n x x y y Verification Task n – 47 – Prove all bad states unreachable Bad States
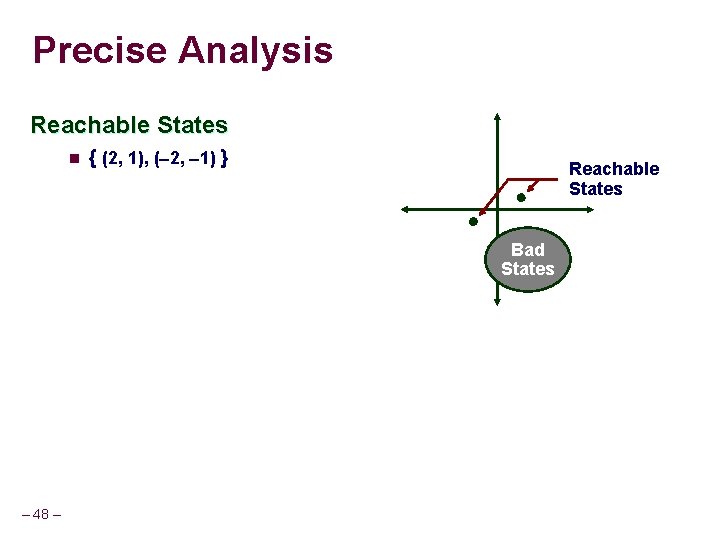
Precise Analysis Reachable States n { (2, 1), ( 2, 1) } Reachable States Bad States – 48 –
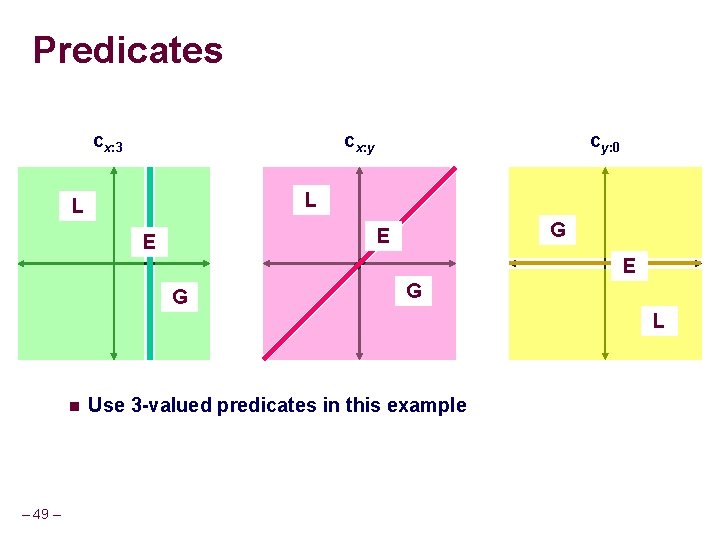
Predicates cx: 3 cx: y cy: 0 L L G E E E G G L n – 49 – Use 3 -valued predicates in this example
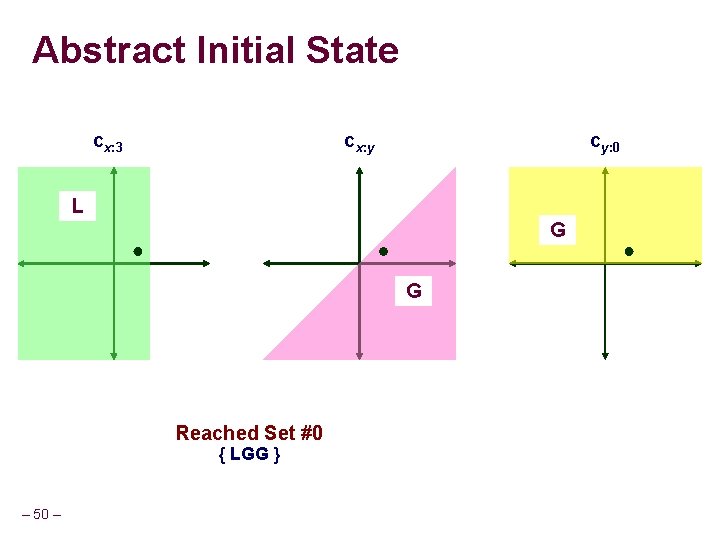
Abstract Initial State cx: 3 cx: y cy: 0 L G G Reached Set #0 { LGG } – 50 –
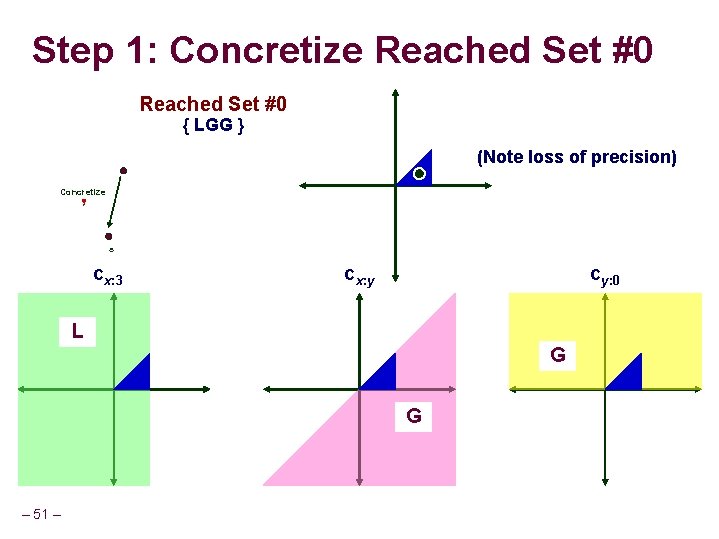
Step 1: Concretize Reached Set #0 { LGG } (Note loss of precision) Concretize s cx: 3 cx: y cy: 0 L G G – 51 –
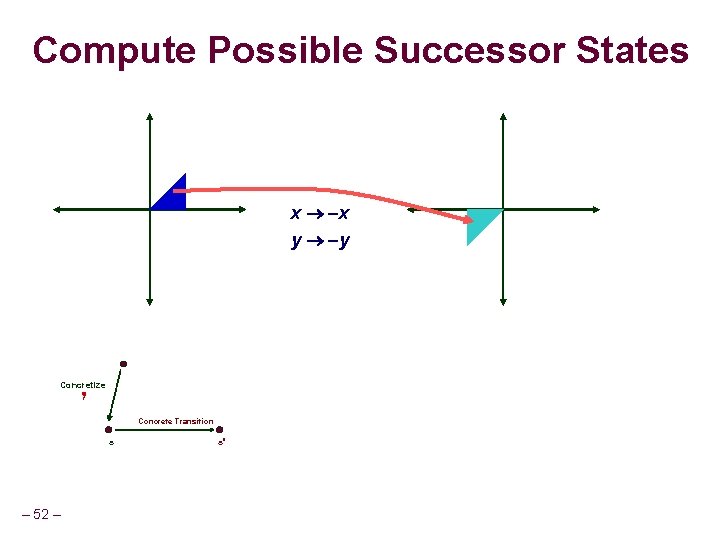
Compute Possible Successor States x x y y Concretize Concrete Transition s – 52 – s
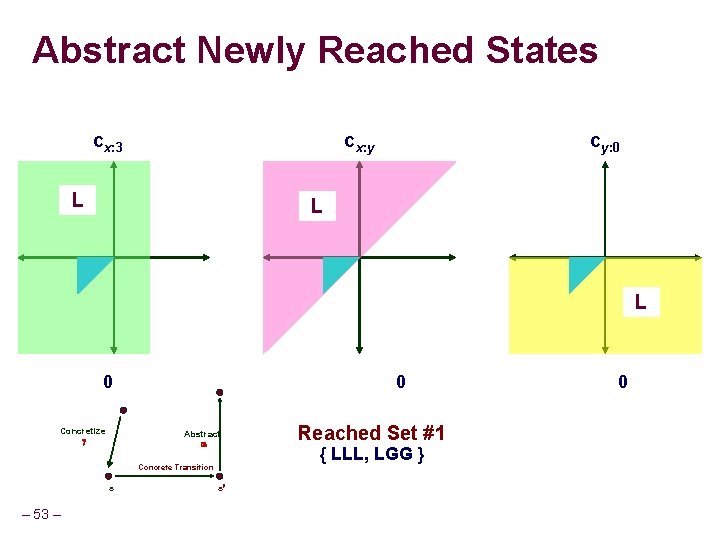
Abstract Newly Reached States cx: 3 cx: y L cy: 0 L L 0 Concretize 0 Abstract Concrete Transition s – 53 – s Reached Set #1 { LLL, LGG } 0
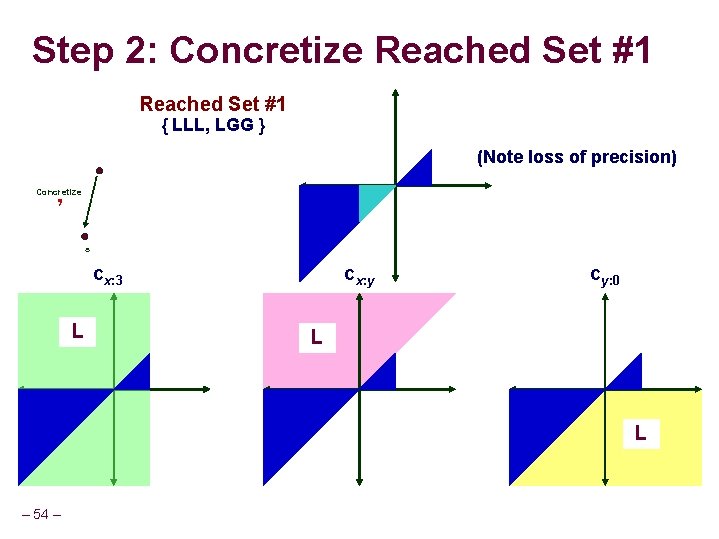
Step 2: Concretize Reached Set #1 { LLL, LGG } (Note loss of precision) Concretize s cx: 3 L cx: y cy: 0 L L – 54 –
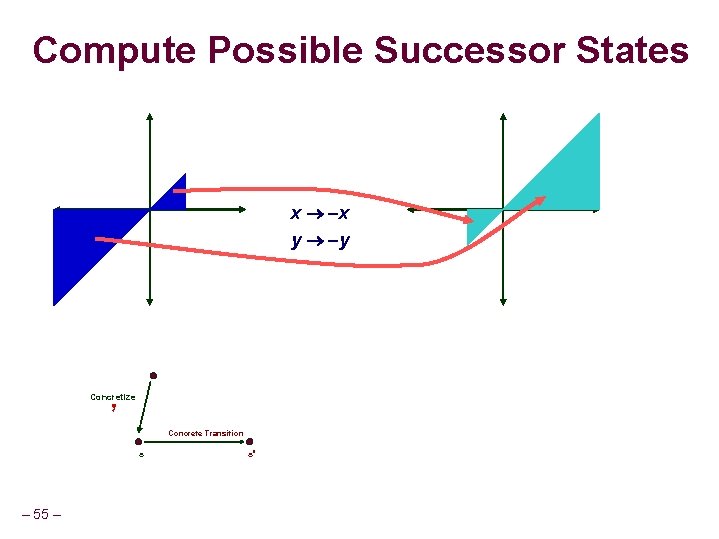
Compute Possible Successor States x x y y Concretize Concrete Transition s – 55 – s
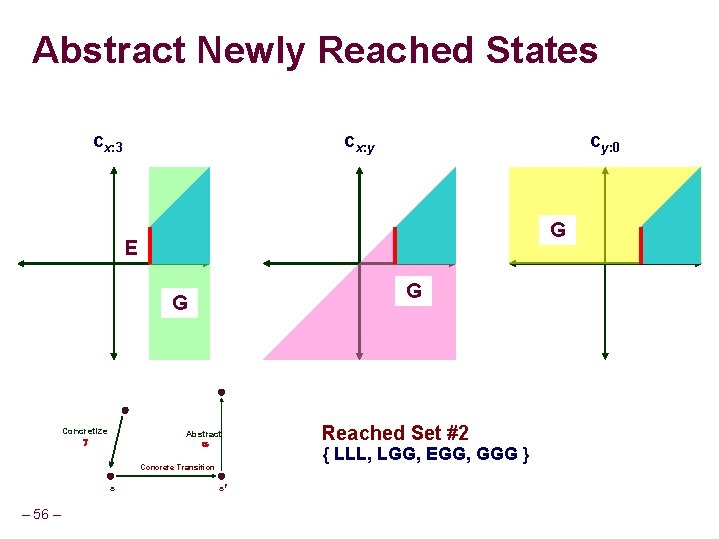
Abstract Newly Reached States cx: 3 cx: y cy: 0 G E G G Concretize Abstract Concrete Transition s – 56 – s Reached Set #2 { LLL, LGG, EGG, GGG }
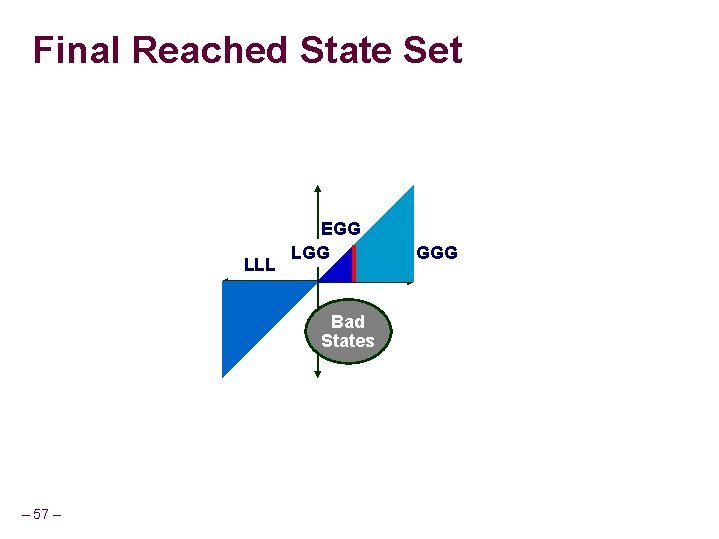
Final Reached State Set LLL EGG LGG Bad States – 57 – GGG
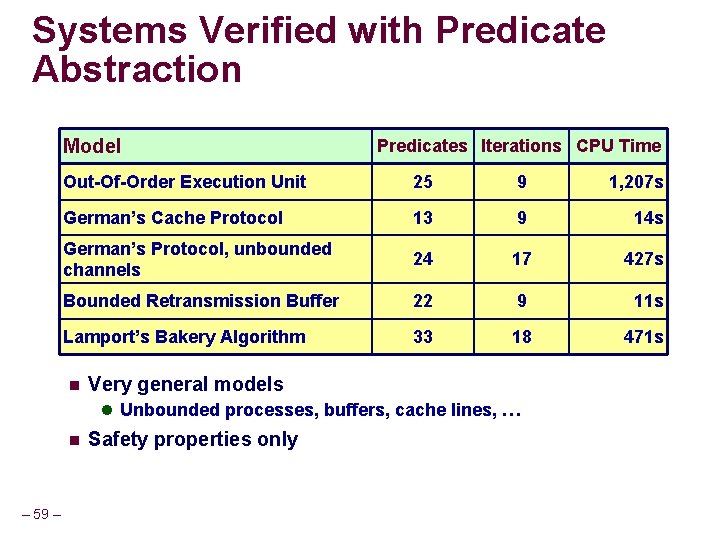
Systems Verified with Predicate Abstraction Model Predicates Iterations CPU Time Out-Of-Order Execution Unit 25 9 1, 207 s German’s Cache Protocol 13 9 14 s German’s Protocol, unbounded channels 24 17 427 s Bounded Retransmission Buffer 22 9 11 s Lamport’s Bakery Algorithm 33 18 471 s n Very general models l Unbounded processes, buffers, cache lines, … n – 59 – Safety properties only
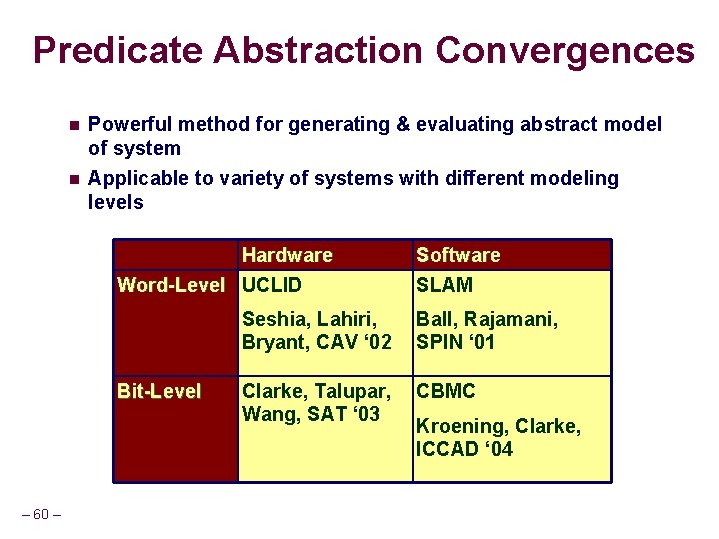
Predicate Abstraction Convergences n Powerful method for generating & evaluating abstract model of system n Applicable to variety of systems with different modeling levels Hardware Word-Level UCLID Bit-Level – 60 – Software SLAM Seshia, Lahiri, Bryant, CAV ‘ 02 Ball, Rajamani, SPIN ‘ 01 Clarke, Talupar, Wang, SAT ‘ 03 CBMC Kroening, Clarke, ICCAD ‘ 04
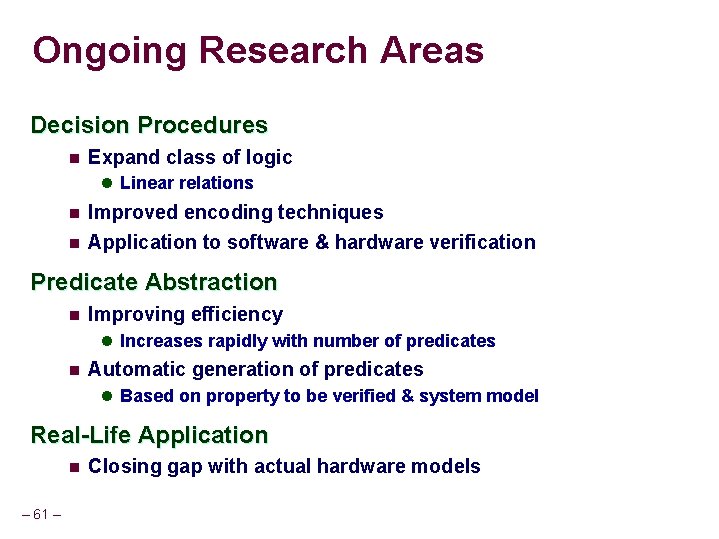
Ongoing Research Areas Decision Procedures n Expand class of logic l Linear relations n n Improved encoding techniques Application to software & hardware verification Predicate Abstraction n Improving efficiency l Increases rapidly with number of predicates n Automatic generation of predicates l Based on property to be verified & system model Real-Life Application n – 61 – Closing gap with actual hardware models
- Slides: 55