Syed Sabih Haider Microsoft and Cyber Security Consultant

Syed Sabih Haider Microsoft and Cyber Security Consultant @ Techaccess Pakistan Technical Writer and Community Speaker @Microsoft
What is Security ? Security is the defense of digital information and IT assets against internal and external, malicious and accidental threats. This defense includes detection, prevention and response to threats through the use of security policies, software tools and IT services. Security is critical for enterprises and organizations of all sizes and in all industries. Weak security can result in compromised systems or data, either by a malicious threat actor or an unintentional internal threat. Not meeting security standards that are regulated by a separate organization or law, such as PCI DSS 3. 0 or HIPAA compliance, can also result in financial penalties.
What is Cyber Security ? Cyber Security is a set of principles and practices designed to safeguard your computing assets and online information against threats Cybersecurity is the body of technologies, processes and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access. In a computing context, security includes both cybersecurity and physical security.
Elements of Cyber Security q Application Security q Device Security q Identity Security q Network Security q Data Security
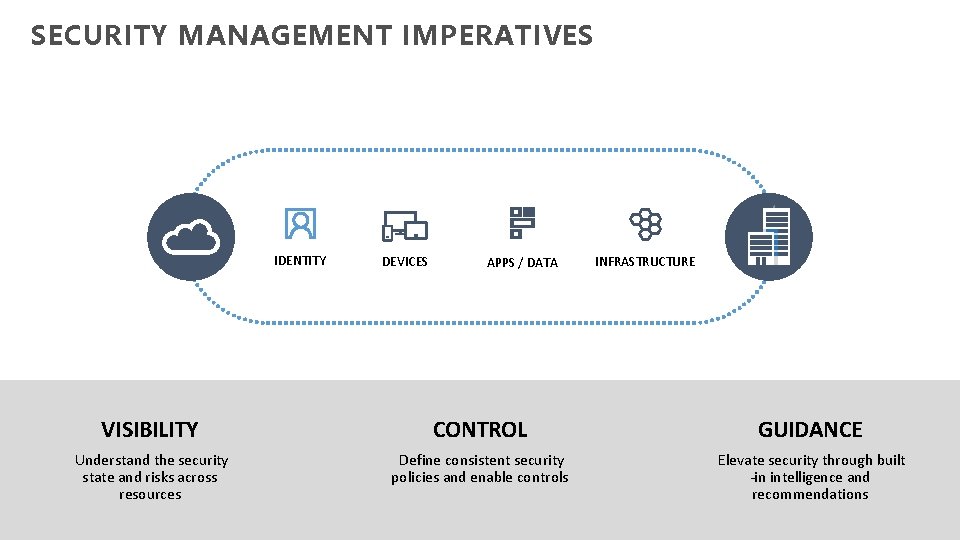
SECURITY MANAGEMENT IMPERATIVES IDENTITY DEVICES APPS / DATA INFRASTRUCTURE VISIBILITY CONTROL GUIDANCE Understand the security state and risks across resources Define consistent security policies and enable controls Elevate security through built -in intelligence and recommendations
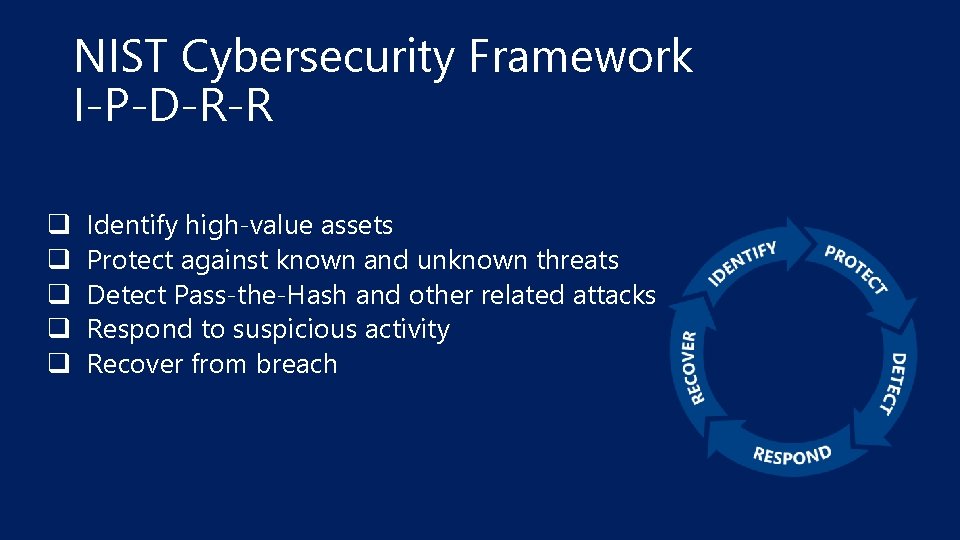
NIST Cybersecurity Framework I-P-D-R-R q q q Identify high-value assets Protect against known and unknown threats Detect Pass-the-Hash and other related attacks Respond to suspicious activity Recover from breach
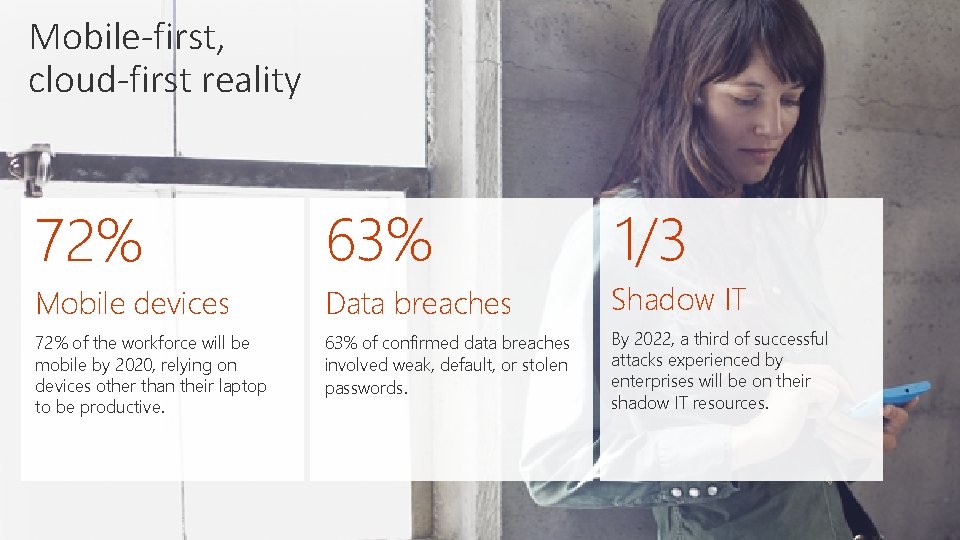
Mobile-first, cloud-first reality 72% 63% 1/3 Mobile devices Data breaches Shadow IT 72% of the workforce will be mobile by 2020, relying on devices other than their laptop to be productive. 63% of confirmed data breaches involved weak, default, or stolen passwords. By 2022, a third of successful attacks experienced by enterprises will be on their shadow IT resources.
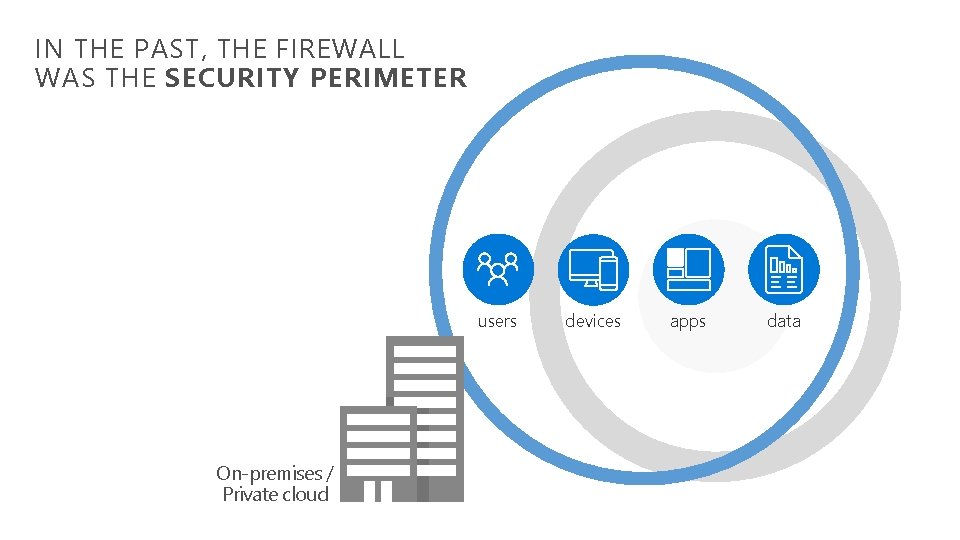
IN THE PAST, THE FIREWALL WAS THE SECURITY PERIMETER users On-premises / Private cloud devices apps data
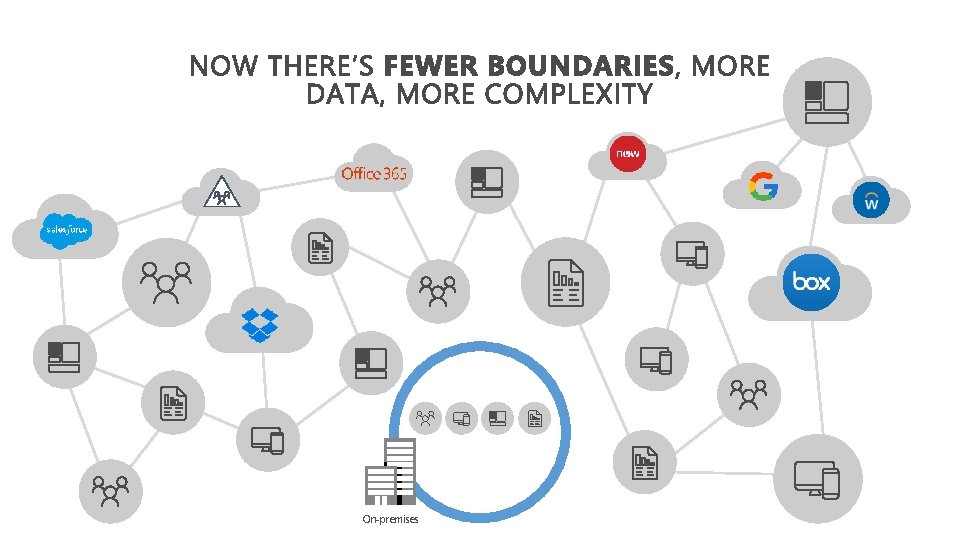
On-premises
Security Risks Intrusion – Unauthorized individuals trying to gain access to computer systems in order to steal information Virus, Worm, Trojan Horse (Malware) – programs that infect your machine and carry malicious codes to destroy the data on your machine or allow an intruder to take control over your machine Phishing – The practice of using email or fake website to lure the recipient in providing personal information Spyware – software that sends information from your computer to a third party without your consent Spam – programs designed to send a message to multiple users, mailing lists or email groups
Some Malicious attacks q q q q q Pass-the-Ticket (Pt. T) Pass-the-Hash (Pt. H) Overpass-the-Hash Malicious replications Reconnaissance Brute Force Remote execution Phishing attacks Wanna. Cry Ransomware
Some Malicious attacks q Pass-the-Ticket (Pt. T) – It’s a technique in which attackers steals a Kerberos ticket from one computer and use it to gain access to another computer by reusing stolen tokens. q Pass-the-Hash (Pt. H) – It’s a technique in which attackers steal a user’s NTLM hash from one computer and use it to gain access to another computer q Over-the-Hash (Ot. H) – It’s another technique of Pass-the-Hash type attach except that the attacker is passing a key instead of an NTLM hash. As such, it is technically a Kerberos based attack. This type is useful once an environment is already compromised.
Some Malicious attacks q Malicious replications – Active Directory replication is the process by which changes that are made on one domain controller are synchronized with the all other domain controllers. Given necessary permissions, attacker can initiate a replication request, allowing them to retrieve the data stored in your premises q Reconnaissance – During which attackers gather information on how the environment is built, what the different assets are, and which entities exist. They generally building their plan for the next phases of the attack
Some Malicious attacks q Brute Force – It’s a technique where attackers continuously tries guesses your password or any confidential data until he will be able to get into your resources q Remote execution – Attackers who compromised administrative credentials or use zero-day exploit can execute remote commands on your Domain controller. This can be used for gaining persistency collecting information, Denial of Service (Do. S) attacks.
Some Malicious attacks q Phishing attacks - Phishing is the attempt to obtain sensitive information such as usernames, passwords, and credit card details (and money), often for malicious reasons, by disguising as a trustworthy entity in an electronic communication. Phishing is typically carried out by email spoofing or instant messaging, and it often directs users to enter personal information at a fake website q Wanna. Cry Ransomware – It’s an attack where attackers control your system and encrypt your drives and then ask payments from victim to decrypt the data otherwise your data will be remained encrypted or data will be deleted by attackers
Cyber Security recent attacks These attacks are wide-ranging, global and do not seem to discriminate among governments and companies. q Operation Shady RAT q World of Hell q Red October, discovered in 2012, was reportedly operating worldwide for up to five years prior to discovery, transmitting information ranging from diplomatic secrets to personal information, including from mobile devices. q Wanna. Cry ransomware attack on 12 May 2017 affecting hundreds of thousands of computers in more than 150 countries. q 2017 Petya cyberattack
Cyber Security recent attacks These attacks relate to stealing login information for specific web resources. q 2011 Play. Station Network outage, 2011 attack resulting in stolen credentials and incidentally causing network disruption q Vestige – in 2010, a band of anonymous hackers has rooted the servers of the site and leaked half a gigabyte's worth of its private data. q IEEE – in September 2012, it exposed user names, plaintext passwords, and website activity for almost 100, 000 of its members. q Living. Social – in 2014, the company suffered a security breach that has exposed names, email addresses and password data for up to 50 million of its users. q Adobe – in 2013, Hackers obtained access to Adobe's networks and stole user information and downloaded the source code for some of Adobe programs. It attacked 150 million customers. q Rock. You – in 2009, the company experienced a data breach resulting in the exposure of over 32 million user accounts. q Yahoo! – in 2012, hackers posted login credentials for more than 453, 000 user accounts. Again in January 2013 and in January 2014
How attackers enter into your environment
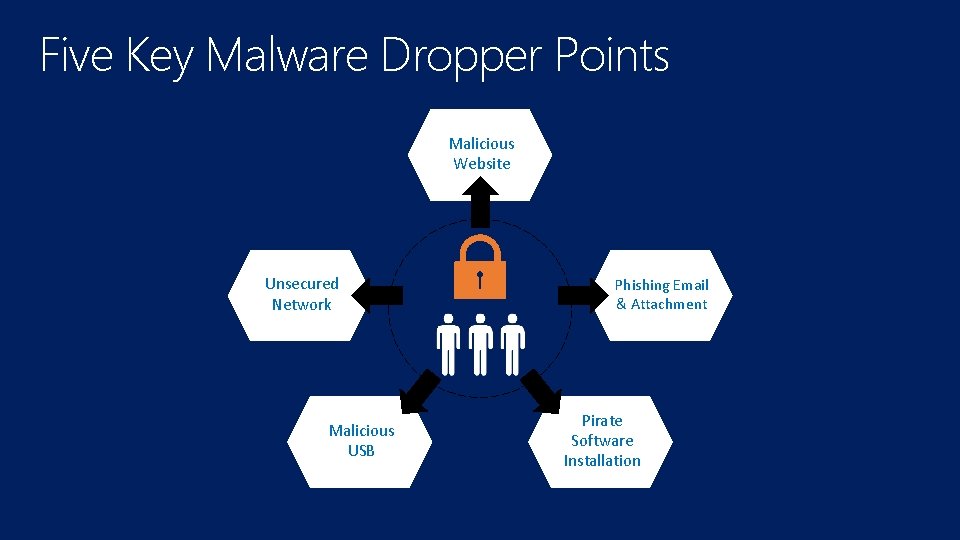
Five Key Malware Dropper Points Malicious Website Unsecured Network Malicious USB Phishing Email & Attachment Pirate Software Installation
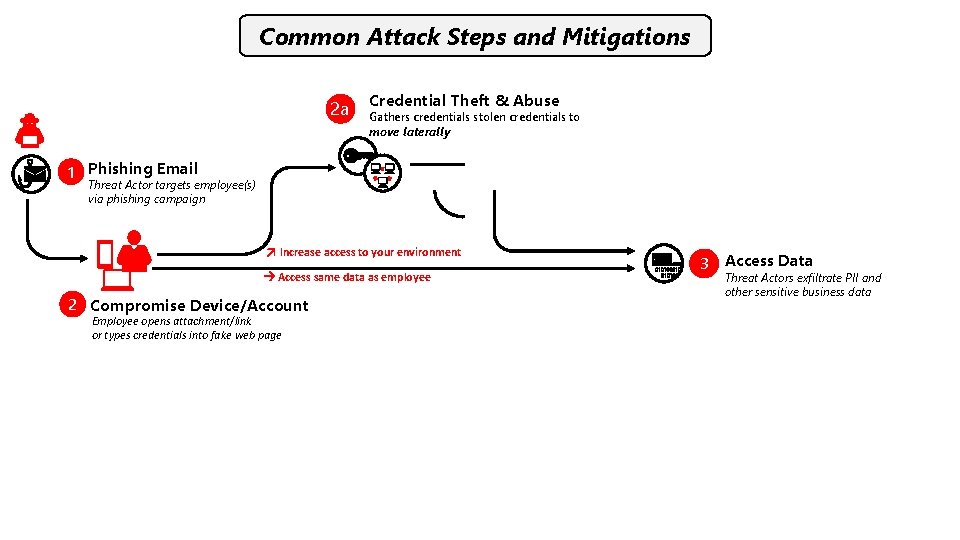
Common Attack Steps and Mitigations 2 a Credential Theft & Abuse Gathers credentials stolen credentials to move laterally 1 Phishing Email Threat Actor targets employee(s) via phishing campaign Increase access to your environment Access same data as employee 2 Compromise Device/Account Employee opens attachment/link or types credentials into fake web page 3 Access Data Threat Actors exfiltrate PII and other sensitive business data
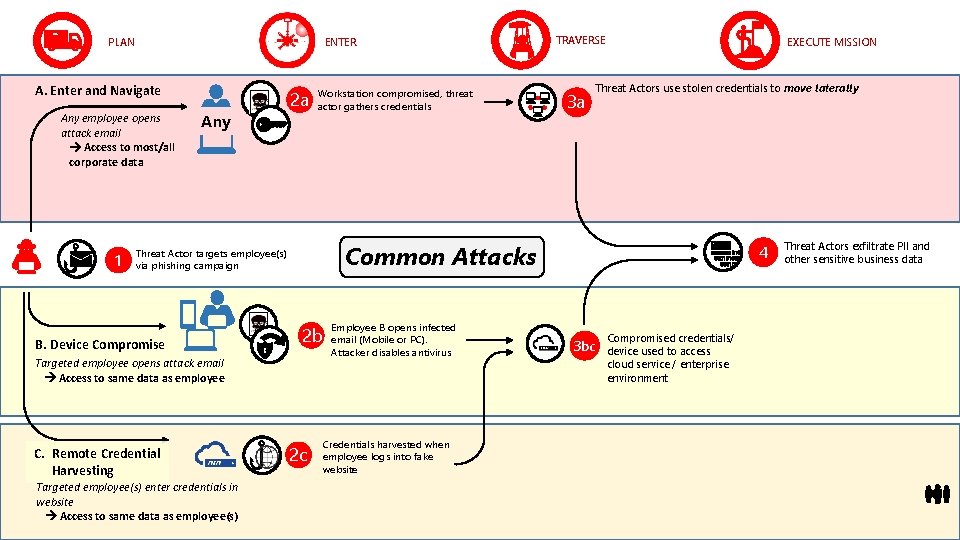
ENTER PLAN A. Enter and Navigate Any employee opens attack email Access to most/all corporate data 1 Any 2 a Workstation compromised, threat actor gathers credentials 2 b Targeted employee opens attack email Access to same data as employee C. Remote Credential Harvesting Targeted employee(s) enter credentials in website Access to same data as employee(s) 3 a EXECUTE MISSION Threat Actors use stolen credentials to move laterally Common Attacks Threat Actor targets employee(s) via phishing campaign B. Device Compromise TRAVERSE 2 c Employee B opens infected email (Mobile or PC). Attacker disables antivirus Credentials harvested when employee logs into fake website 4 3 bc Compromised credentials/ device used to access cloud service / enterprise environment Threat Actors exfiltrate PII and other sensitive business data
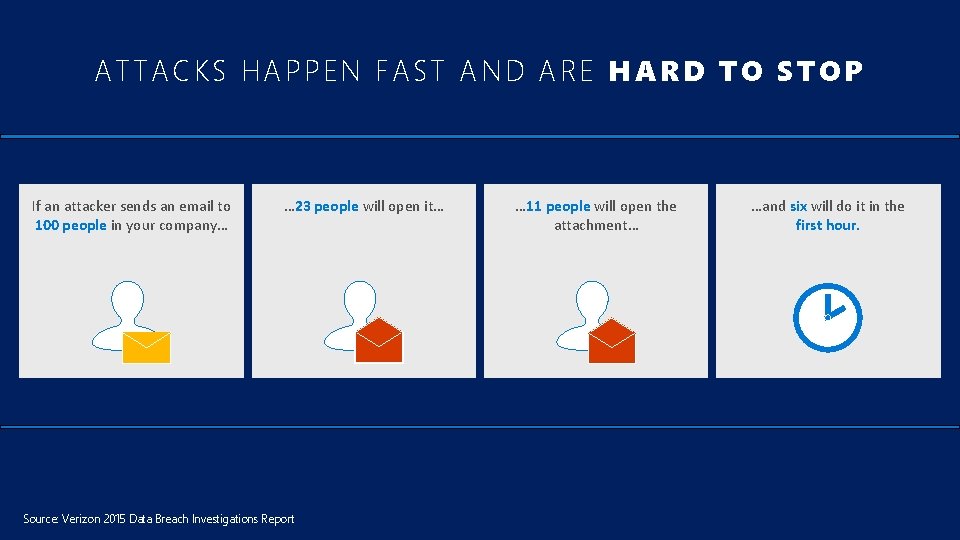
ATTACKS HAPPEN FAST AND ARE HARD TO STOP If an attacker sends an email to 100 people in your company… … 23 people will open it… Source: Verizon 2015 Data Breach Investigations Report … 11 people will open the attachment… …and six will do it in the first hour.
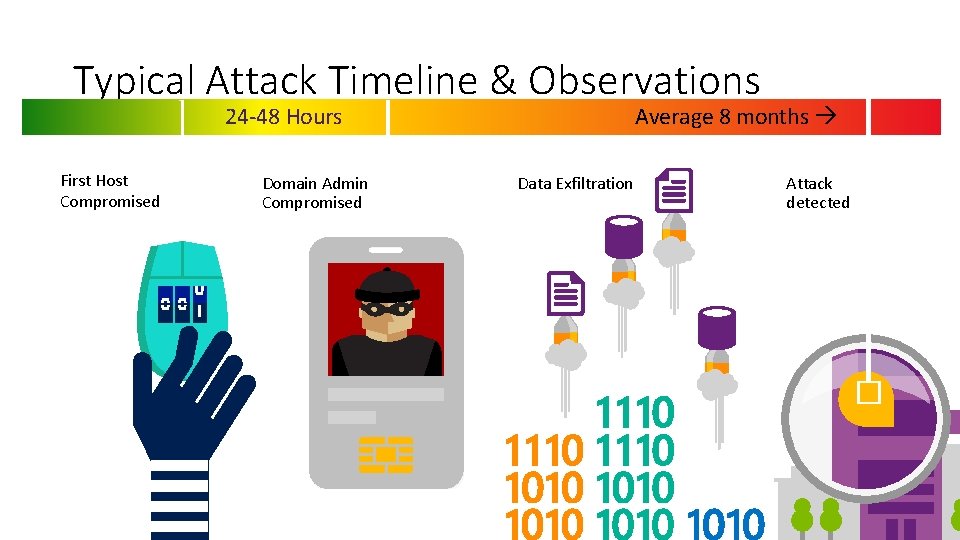
Typical Attack Timeline & Observations 24 -48 Hours First Host Compromised Domain Admin Compromised Average 8 months Data Exfiltration Attack detected �

Criticality of risk management Risk management: A balancing act Mitigate risk Avoid risk Accept risk Transfer risk In a globalized world where all Internet-connected systems are potentially vulnerable and where cyber attacks may be difficult to detect, there is no such thing as absolute cyber security. Therefore, when a company is assessing, prioritizing and resourcing cyber security activities it should consider where the greatest areas of risk are based on an assessment of risk that considers factors such as: uniqueness, importance, vulnerability and attractiveness to potential adversaries. ”

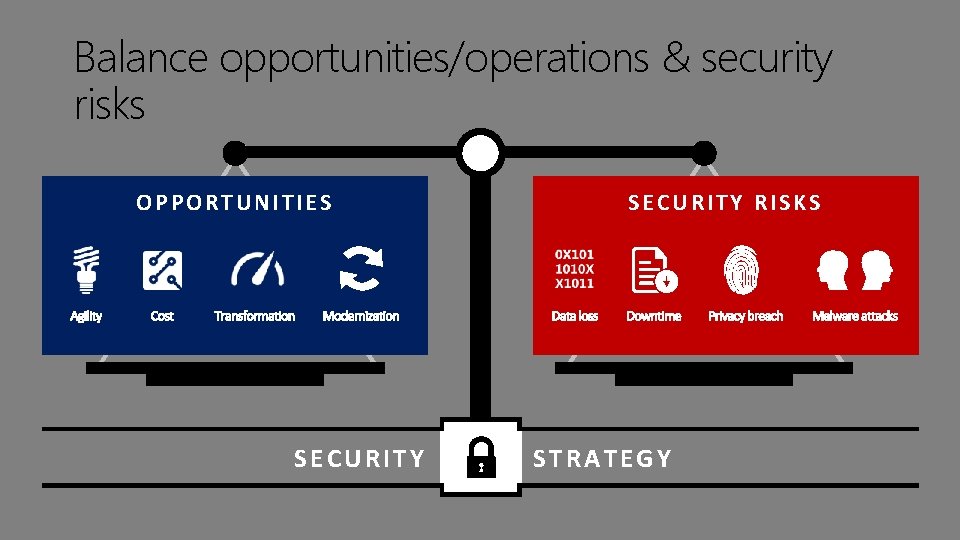
Balance opportunities/operations & security risks OPPORTUNITIES SECURITY RISKS STRATEGY

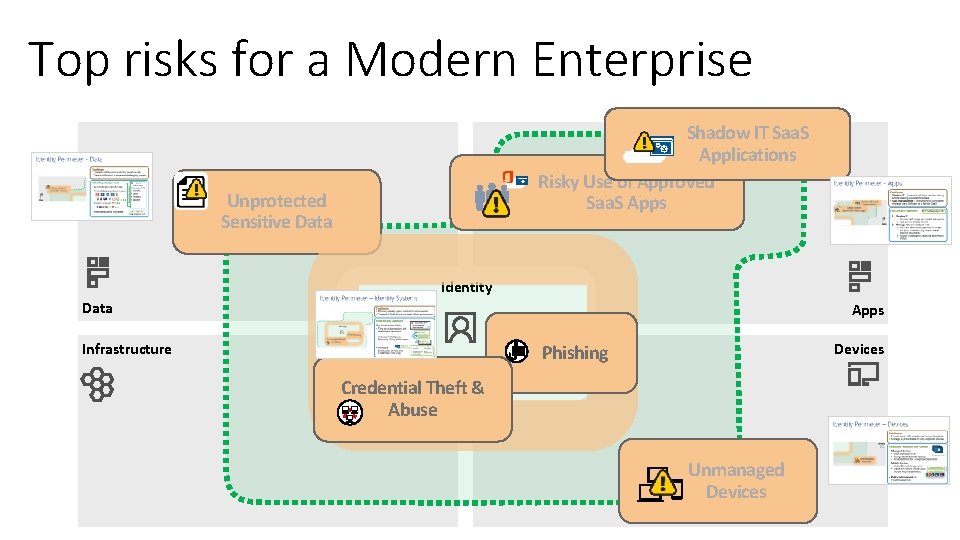
Top risks for a Modern Enterprise Shadow IT Saa. S Applications Risky Use of Approved Saa. S Apps Unprotected Sensitive Data Identity Data Apps Infrastructure Devices Phishing Credential Theft & Abuse Unmanaged Devices
What type of Security Breach ? q Compromised Personally Identifiable Information (PII); PII data refers to name, SSN, D. Licenses, bank accounts q Identity Theft – Computer intruders intent on stealing your personal information to commit fraud or theft q The use of unsecure settings of Peer to Peer File Sharing applications. q Compromised computer – A computer experiencing unexpected and unexplainable - Disk activities - Performance degradation - Repeated login failure or connections to unfamiliar services - Third party complaint of a suspicious activity - Or a stolen or lost computer
Security Measures q q q Safely mange your password Safely manage your email account Secure your computer Protect the data you are handling Avoid risky behavior online Be aware of security guidelines, policies, and procedures

Companies offering Security Solutions

Microsoft Security Solutions
Microsoft has solution for Cyber Security and we call it

”Microsoft Enterprise Mobility + Security” OR Microsoft EMS Solution

Microsoft Enterprise Mobility + Security
Microsoft Enterprise Mobility + Security Components q Microsoft Intune q Cloud Application Security q Azure Information Protection q Advance Threat Analytics q Advance Threat Protection

Microsoft Intune
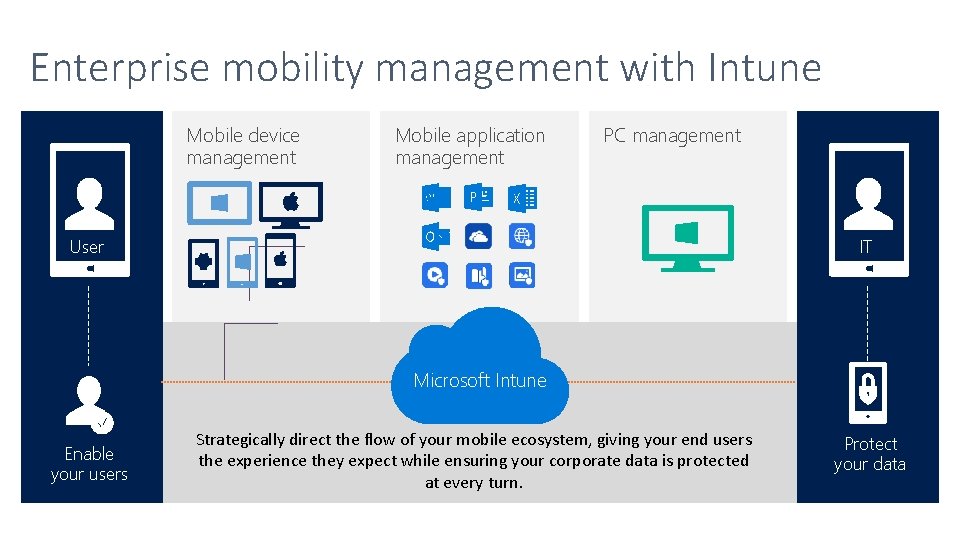
Enterprise mobility management with Intune Mobile device management Mobile application management PC management User IT Microsoft Intune Enable your users Strategically direct the flow of your mobile ecosystem, giving your end users the experience they expect while ensuring your corporate data is protected at every turn. Protect your data

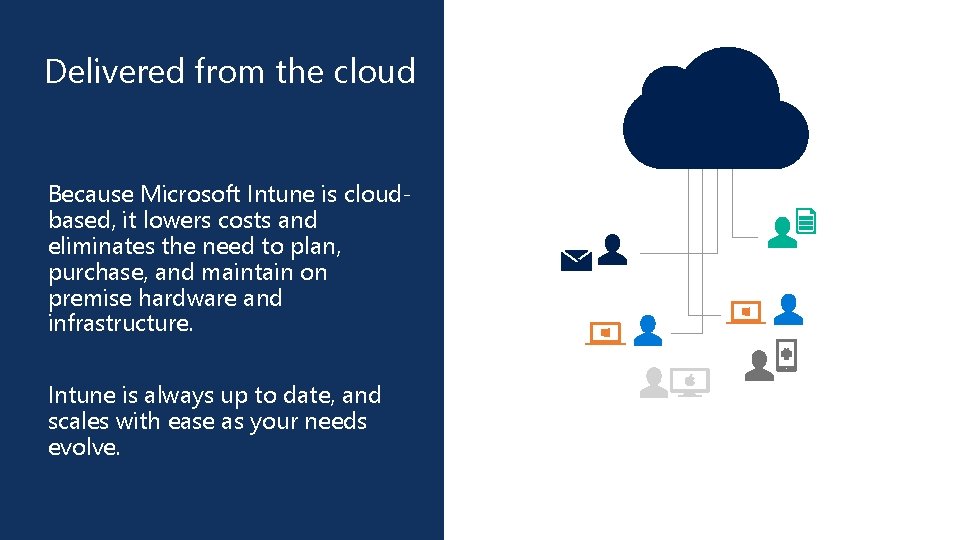
Click to edit Master title Delivered from the cloud style Because Microsoft Intune is cloudbased, it lowers costs and eliminates the need to plan, purchase, and maintain on premise hardware and infrastructure. Intune is always up to date, and scales with ease as your needs evolve.

Microsoft Cloud App Security
How do I gain visibility into cloud apps used in my organization and get a risk assessment? How can I control and limit access to data in cloud apps? How can I prevent data loss in cloud apps and stay compliant with regulations? How do I protect cloud apps and the data in them from security attacks?
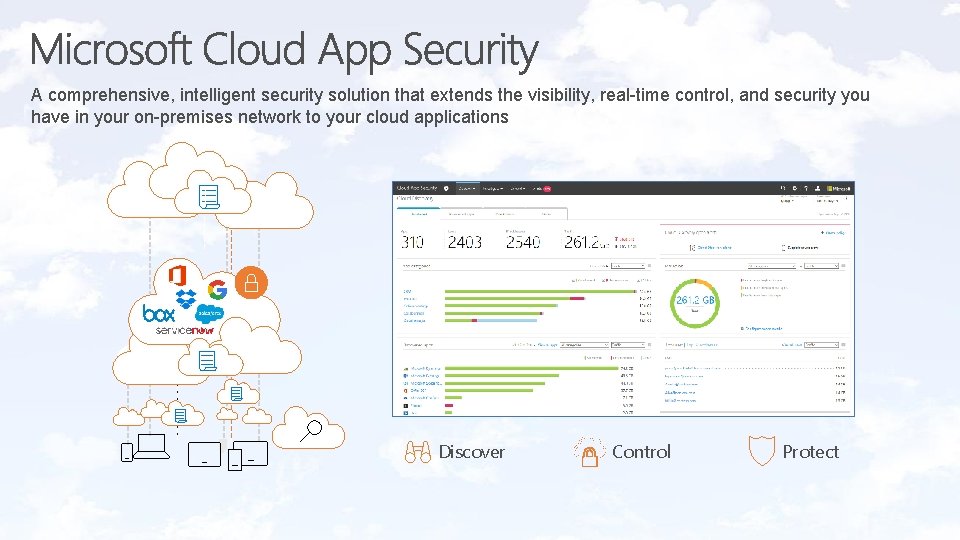
A comprehensive, intelligent security solution that extends the visibility, real-time control, and security you have in your on-premises network to your cloud applications Discover Control Protect

Microsoft Cloud App Security Discover and assess risks Identify cloud apps on your network, gain visibility into shadow IT, and get risk assessments and ongoing analytics. Control access in real time Manage and limit cloud app access based on conditions and session context, including user identity, device, and location. Protect your information Get granular control over data and use built-in or custom policies for data sharing and data loss prevention. Extend Microsoft security Threat detection: Microsoft Intelligent Security Graph, Office ATP Information Protection: Office 365 & Azure Information Protection Identity: Azure AD and Conditional Access Detect threats Identify high-risk usage and detect unusual behavior using Microsoft threat intelligence and research. To your cloud apps + more

Microsoft Azure Information Protection
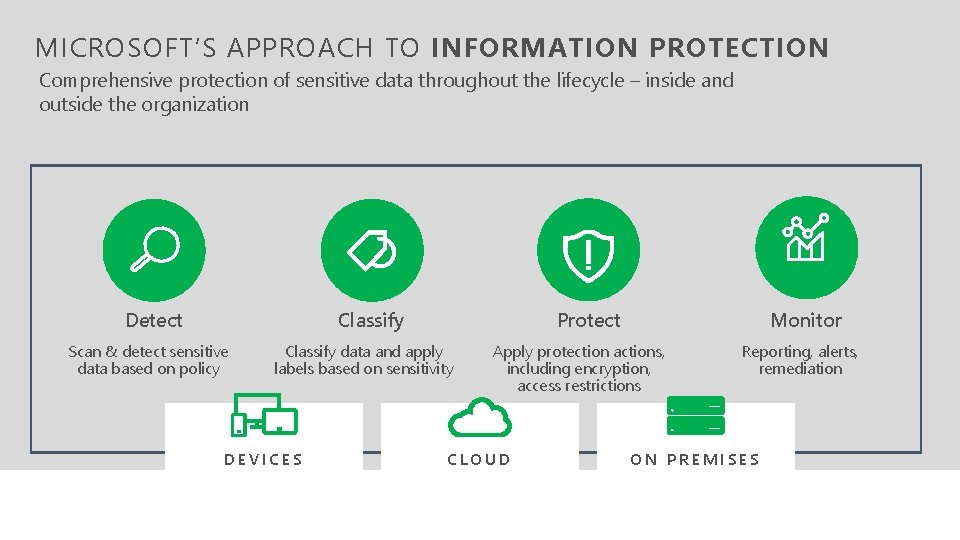
MICROSOFT’S APPROACH TO INFORMATION PROTECTION Comprehensive protection of sensitive data throughout the lifecycle – inside and outside the organization Detect Classify Scan & detect sensitive data based on policy Protect Classify data and apply labels based on sensitivity DEVICES Monitor Apply protection actions, including encryption, access restrictions CLOUD Reporting, alerts, remediation ON PREMISES
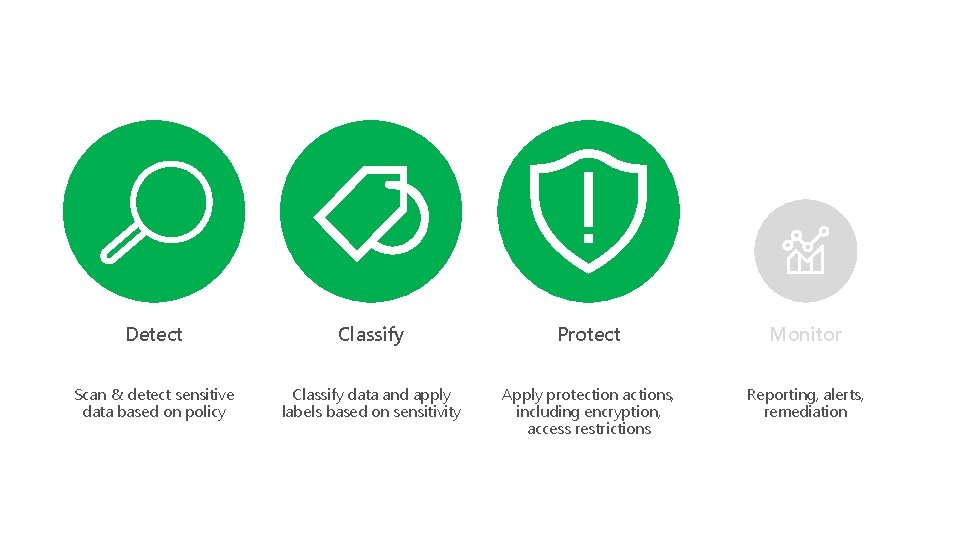
Detect Classify Protect Monitor Scan & detect sensitive data based on policy Classify data and apply labels based on sensitivity Apply protection actions, including encryption, access restrictions Reporting, alerts, remediation
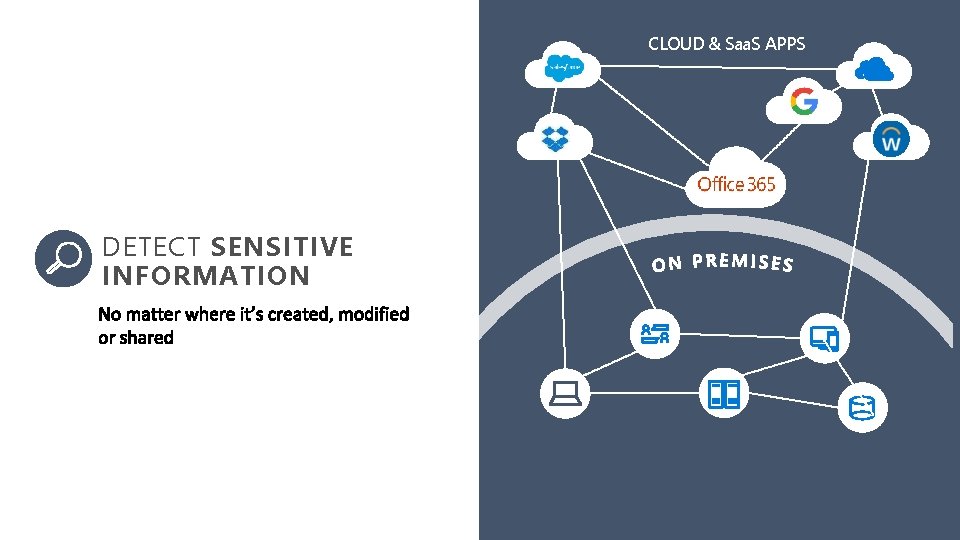
CLOUD & Saa. S APPS DETECT SENSITIVE INFORMATION a
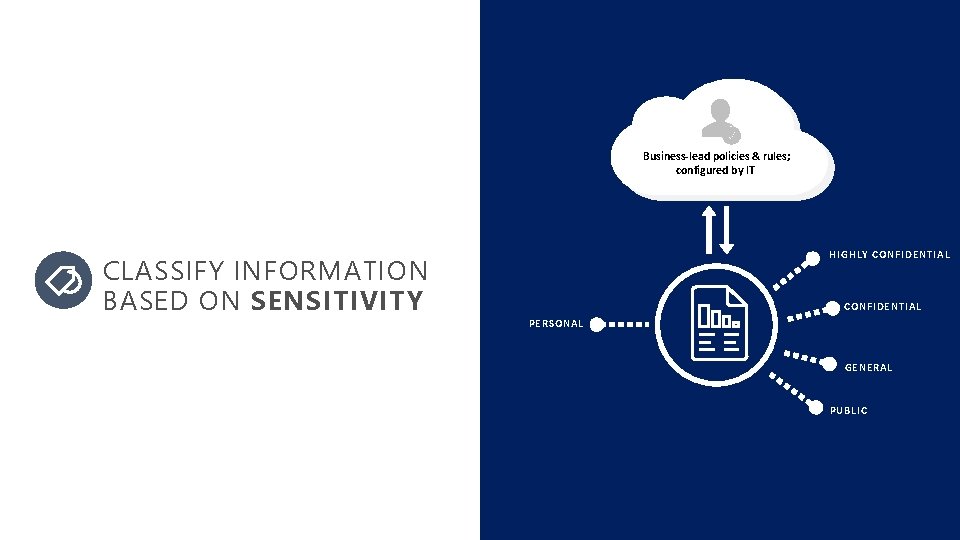
Business-lead policies & rules; configured by IT CLASSIFY INFORMATION BASED ON SENSITIVITY HIGHLY CONFIDENTIAL PERSONAL GENERAL PUBLIC
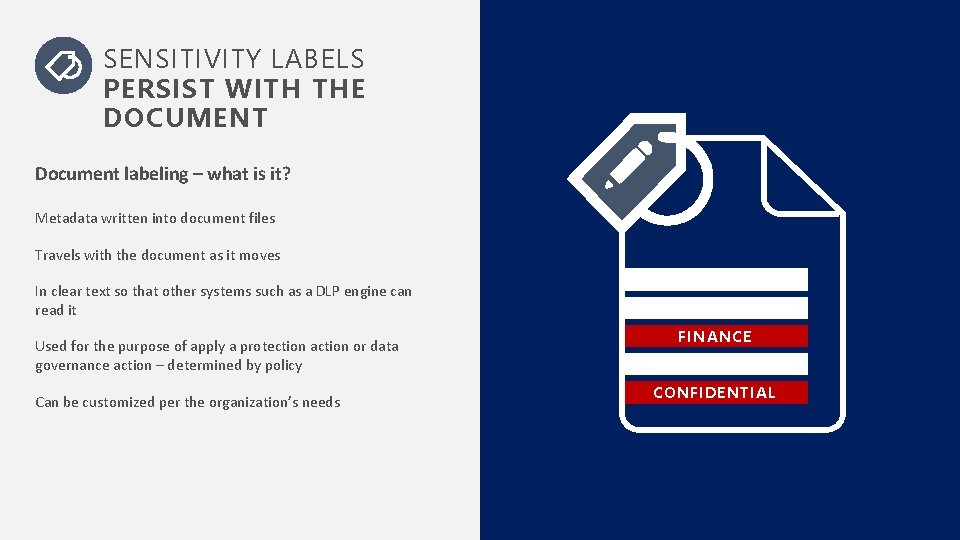
SENSITIVITY LABELS PERSIST WITH THE DOCUMENT Document labeling – what is it? Metadata written into document files Travels with the document as it moves In clear text so that other systems such as a DLP engine can read it Used for the purpose of apply a protection action or data governance action – determined by policy Can be customized per the organization’s needs FINANCE CONFIDENTIAL
Detect Classify Protect Monitor Scan & detect sensitive data based on policy Classify data and apply labels based on sensitivity Apply protection actions, including encryption, access restrictions Reporting, alerts, remediation
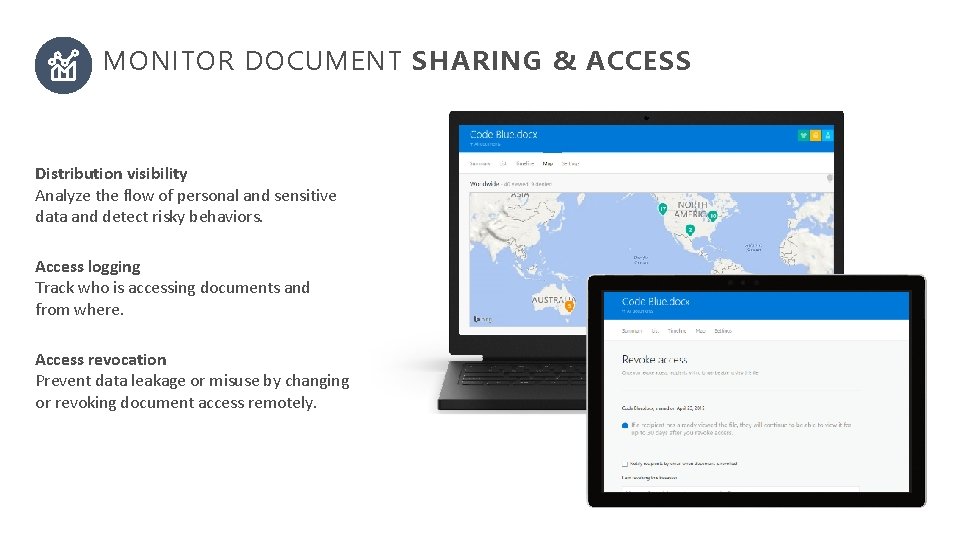
MONITOR DOCUMENT SHARING & ACCESS Distribution visibility Analyze the flow of personal and sensitive data and detect risky behaviors. Access logging Track who is accessing documents and from where. Access revocation Prevent data leakage or misuse by changing or revoking document access remotely.

Microsoft Advance Threat Analytics
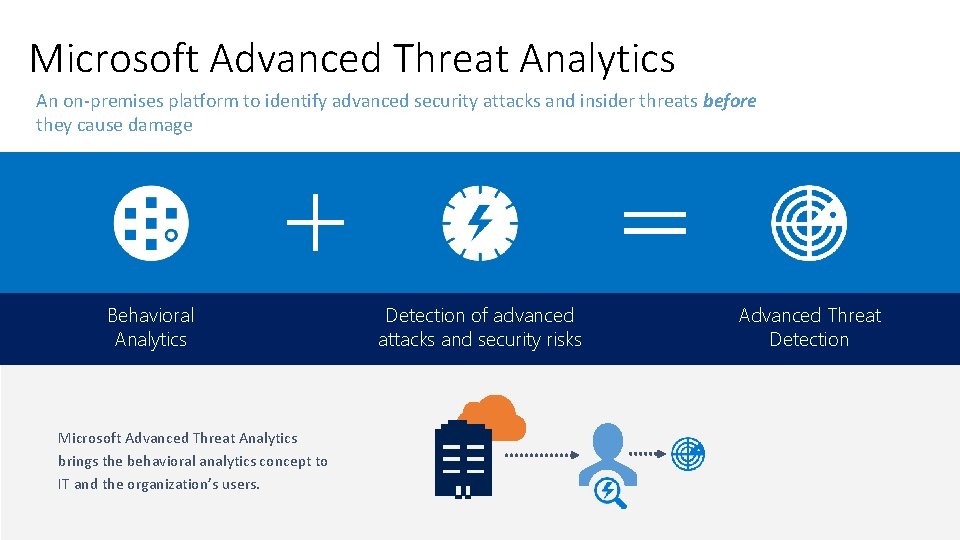
Microsoft Advanced Threat Analytics An on-premises platform to identify advanced security attacks and insider threats before they cause damage Behavioral Analytics Microsoft Advanced Threat Analytics brings the behavioral analytics concept to IT and the organization’s users. Detection of advanced attacks and security risks Advanced Threat Detection

Microsoft Advance Threat Protection
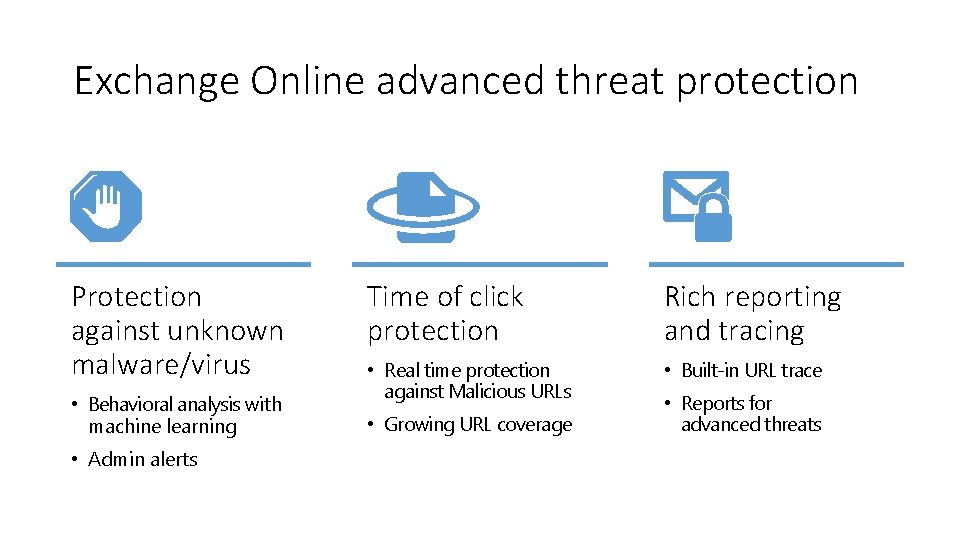
Exchange Online advanced threat protection Protection against unknown malware/virus • Behavioral analysis with machine learning • Admin alerts Time of click protection Rich reporting and tracing • Real time protection against Malicious URLs • Built-in URL trace • Growing URL coverage • Reports for advanced threats
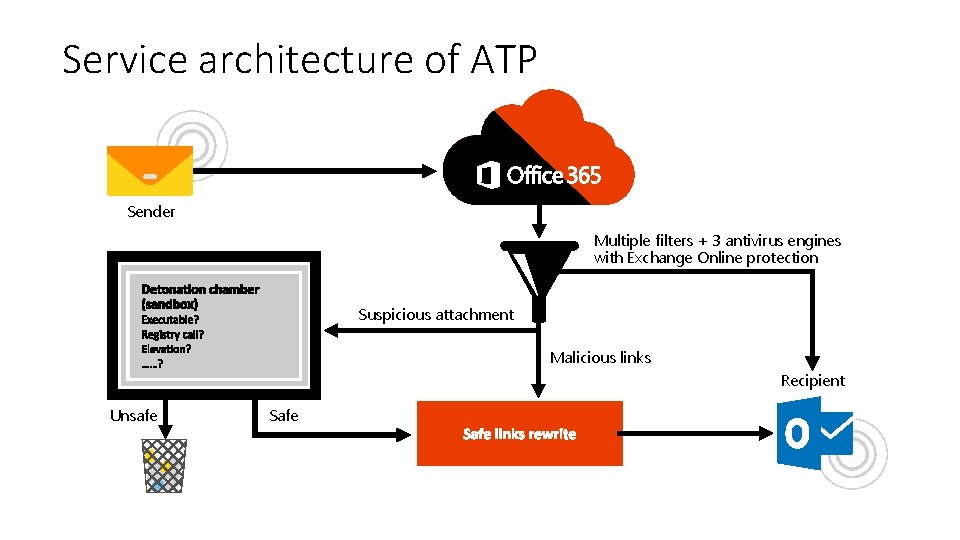
Service architecture of ATP Sender Multiple filters + 3 antivirus engines with Exchange Online protection Suspicious attachment Malicious links Recipient Unsafe Safe
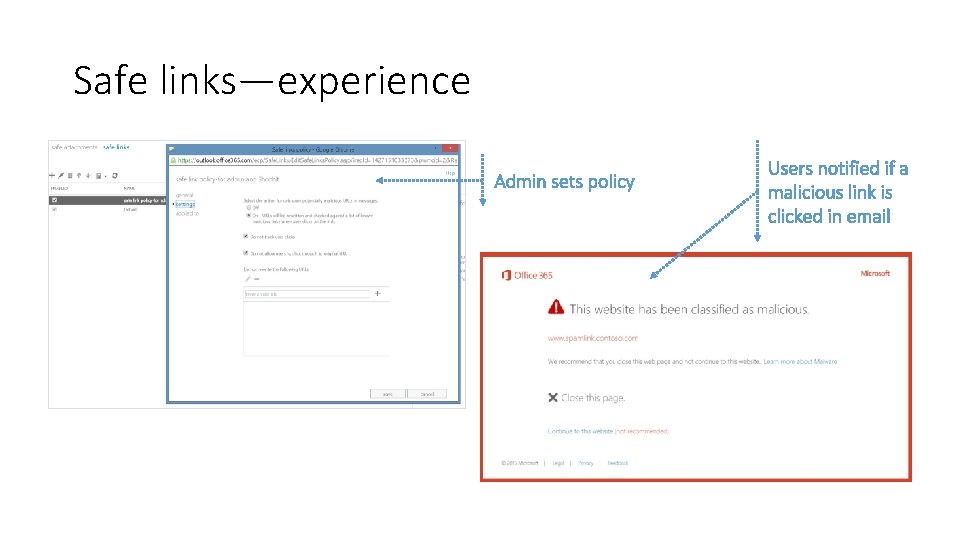
Safe links—experience
Conclusion talk
Threat Prevention Threat Detection Response Lessons Learned At some point the adversary has to do something anomalous – You have to be able to spot that and quickly take action on it
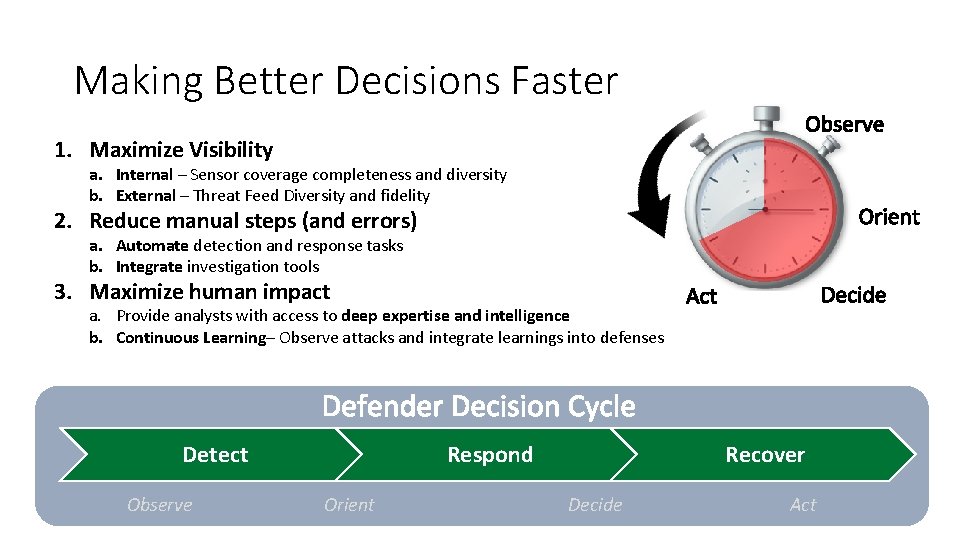
Making Better Decisions Faster 1. Maximize Visibility a. Internal – Sensor coverage completeness and diversity b. External – Threat Feed Diversity and fidelity 2. Reduce manual steps (and errors) a. Automate detection and response tasks b. Integrate investigation tools 3. Maximize human impact a. Provide analysts with access to deep expertise and intelligence b. Continuous Learning– Observe attacks and integrate learnings into defenses Detect Observe Respond Orient Recover Decide Act

My Social Connections /Syed. Sabhi

- Slides: 63