SVA Binary translation and emulation Cryptographic secure computation
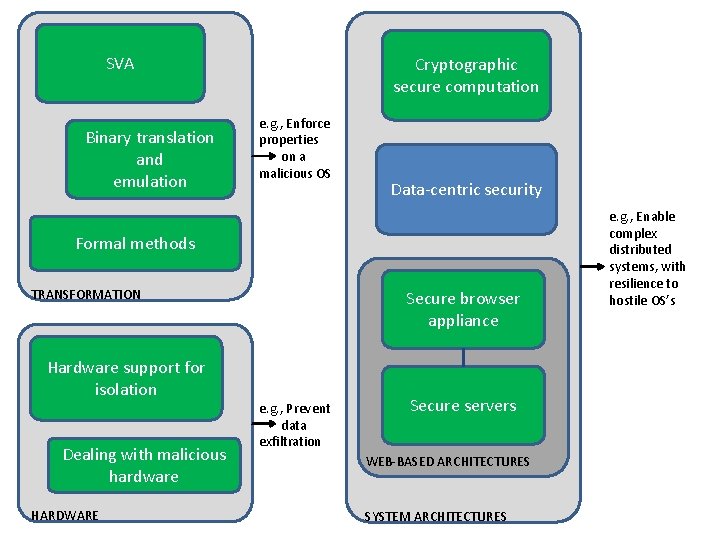
SVA Binary translation and emulation Cryptographic secure computation e. g. , Enforce properties on a malicious OS Data-centric security Formal methods TRANSFORMATION Hardware support for isolation Dealing with malicious hardware HARDWARE Secure browser appliance e. g. , Prevent data exfiltration Secure servers WEB-BASED ARCHITECTURES SYSTEM ARCHITECTURES e. g. , Enable complex distributed systems, with resilience to hostile OS’s
Platform for Private Data Mohit Tiwari, UC Berkeley with Krste Asanović, Dawn Song, Petros Maniatis, Prashanth Mohan, Christoforos Papamanthou, Elaine Shi, Emil Stefanov, Nguyen Tran
The Age of Big Data Plentiful, and Private
Rich Applications
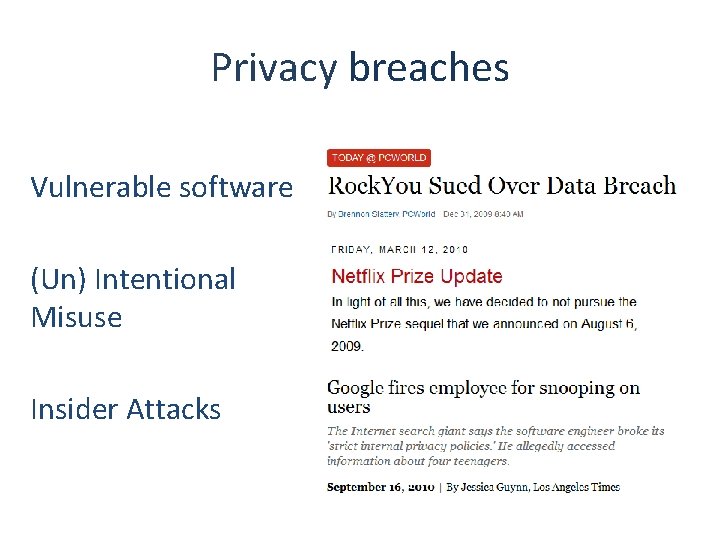
Privacy breaches Vulnerable software (Un) Intentional Misuse Insider Attacks
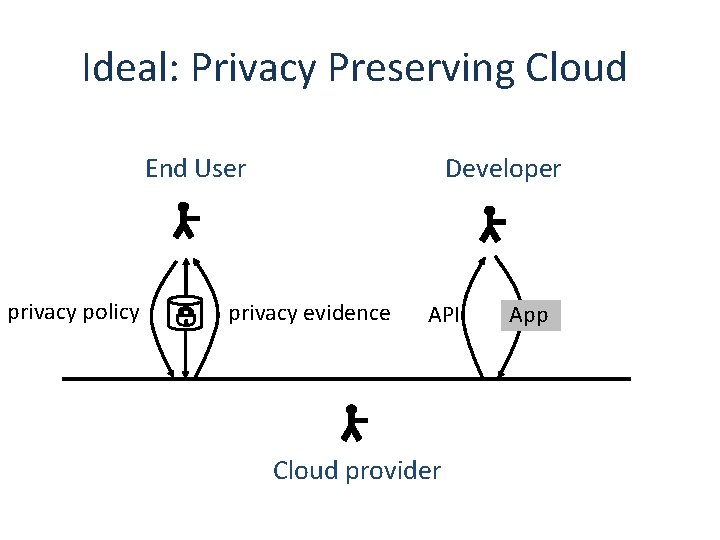
Ideal: Privacy Preserving Cloud Developer End User privacy policy privacy evidence API Cloud provider App
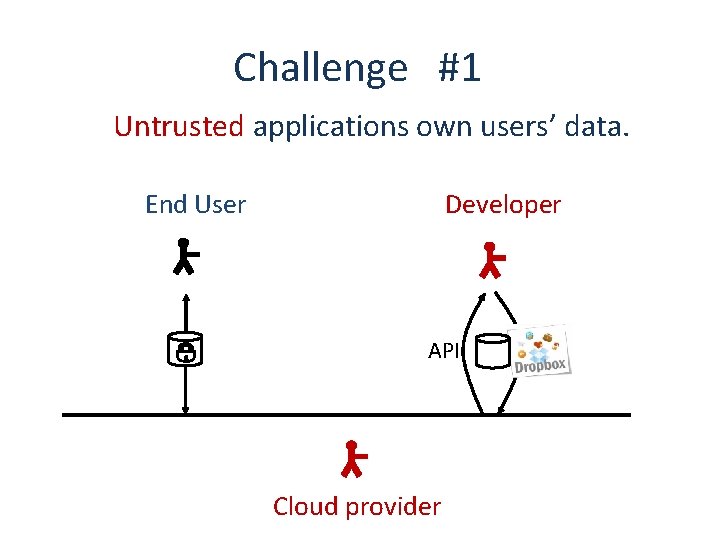
Challenge #1 Untrusted applications own users’ data. Developer End User API Cloud provider
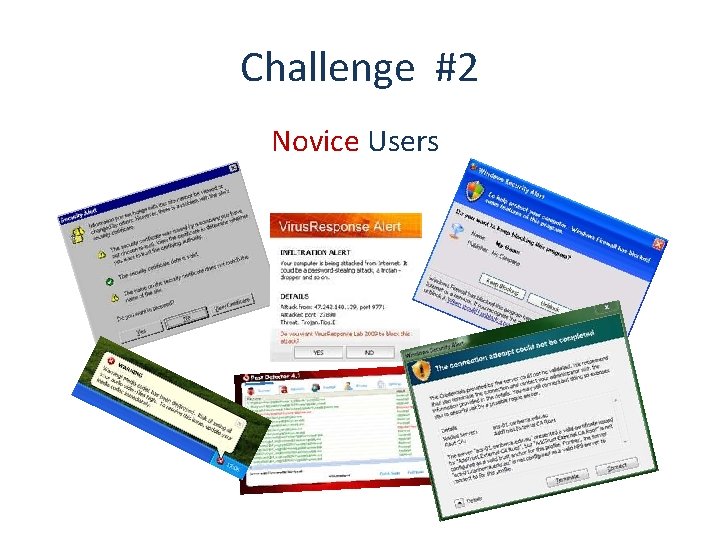
Challenge #2 Novice Users
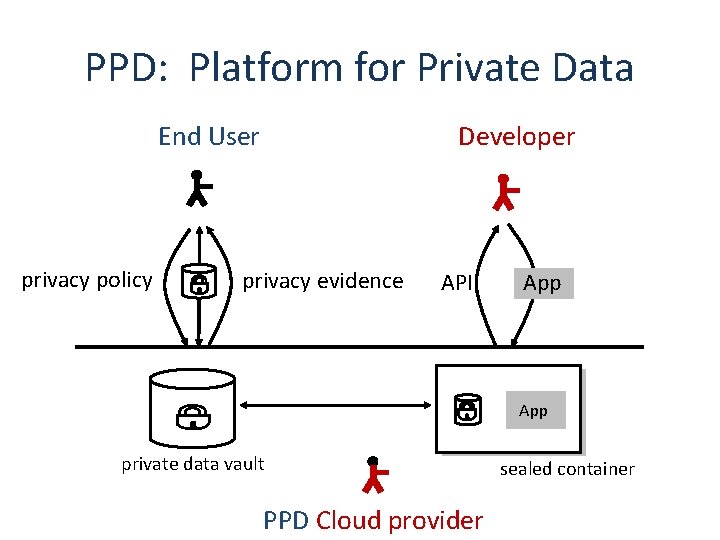
PPD: Platform for Private Data Developer End User privacy policy privacy evidence API App private data vault PPD Cloud provider sealed container
Outline of this talk • PPD: Platform for Private Data • PPD Architecture • PPD Prototype and Evaluation
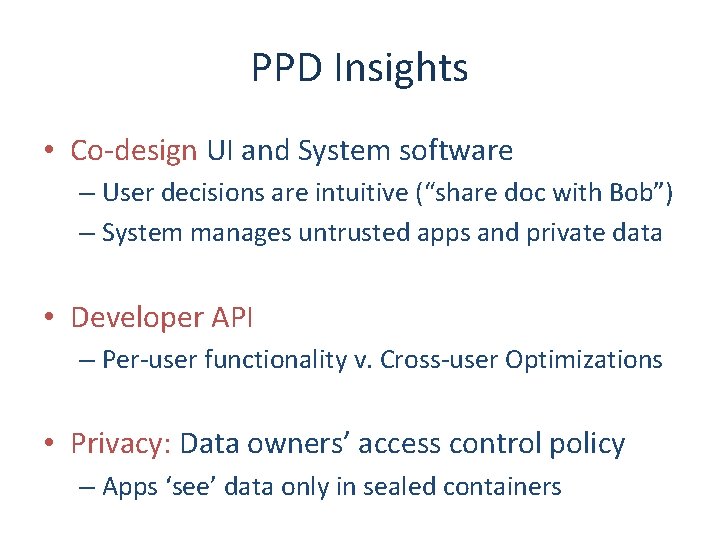
PPD Insights • Co-design UI and System software – User decisions are intuitive (“share doc with Bob”) – System manages untrusted apps and private data • Developer API – Per-user functionality v. Cross-user Optimizations • Privacy: Data owners’ access control policy – Apps ‘see’ data only in sealed containers
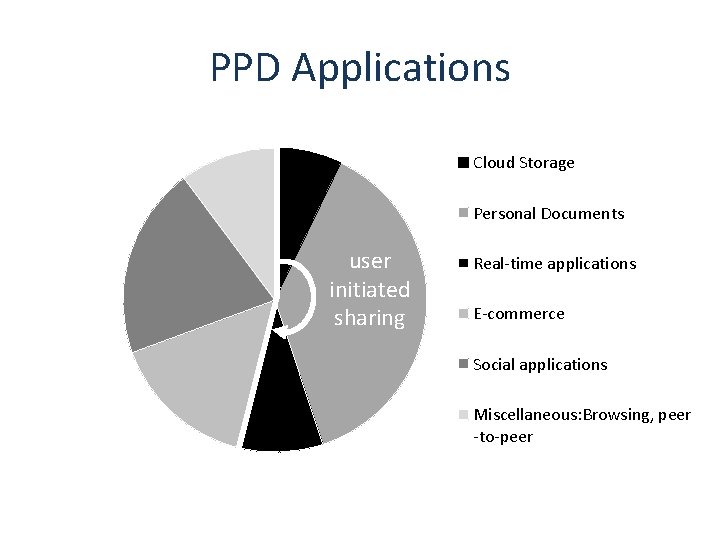
PPD Applications Cloud Storage Personal Documents user initiated sharing Real-time applications E-commerce Social applications Miscellaneous: Browsing, peer -to-peer
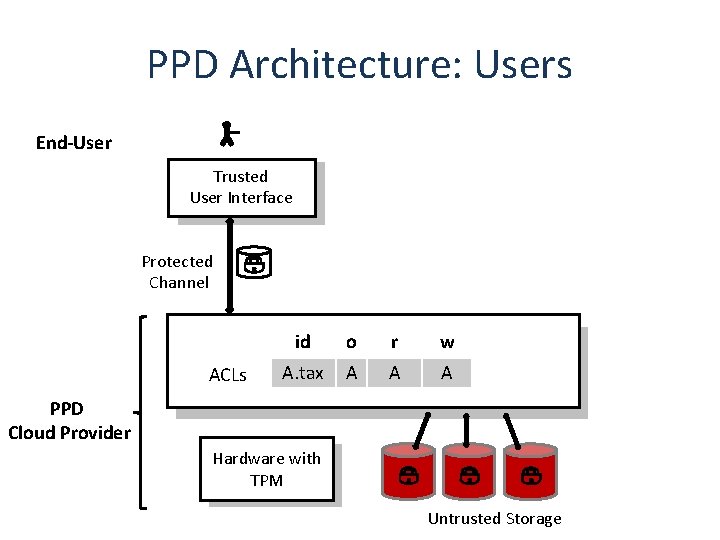
PPD Architecture: Users End-User Trusted User Interface Protected Channel ACLs id o r w A. tax A A A PPD Cloud Provider Hardware with TPM Untrusted Storage
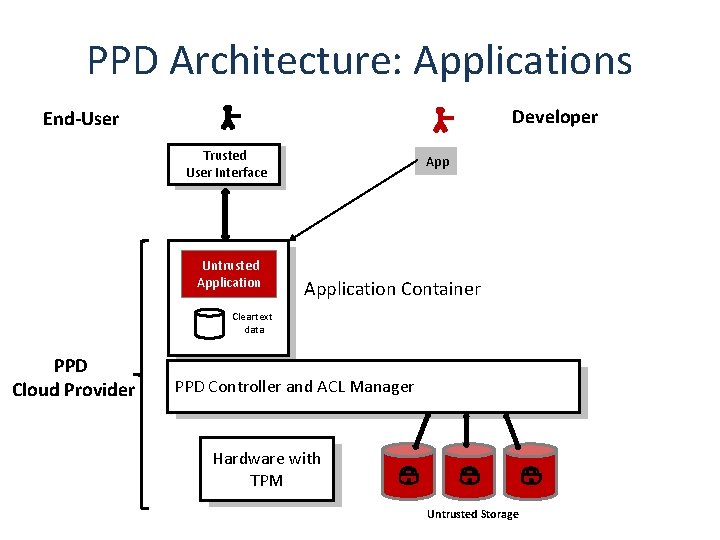
PPD Architecture: Applications Developer End-User Trusted User Interface Untrusted Application Container Cleartext data PPD Cloud Provider PPD Controller and ACL Manager Hardware with TPM Untrusted Storage
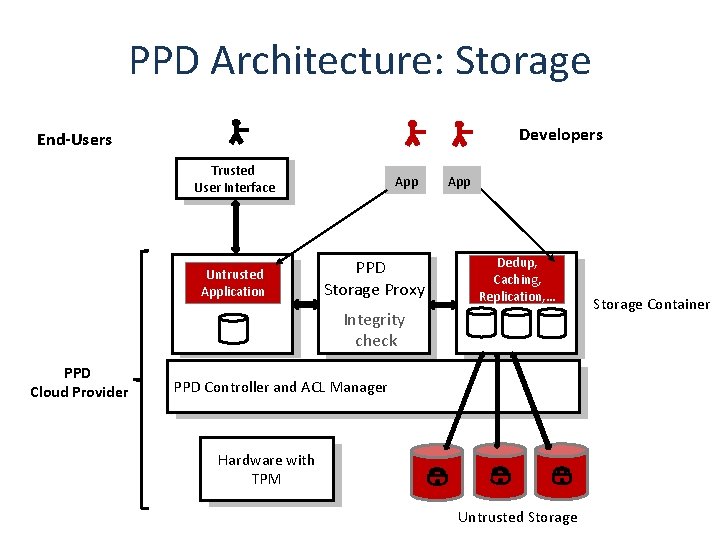
PPD Architecture: Storage Developers End-Users Trusted User Interface Untrusted Application App PPD Storage Proxy App Dedup, Caching, Replication, … Integrity check PPD Cloud Provider PPD Controller and ACL Manager Hardware with TPM Untrusted Storage Container
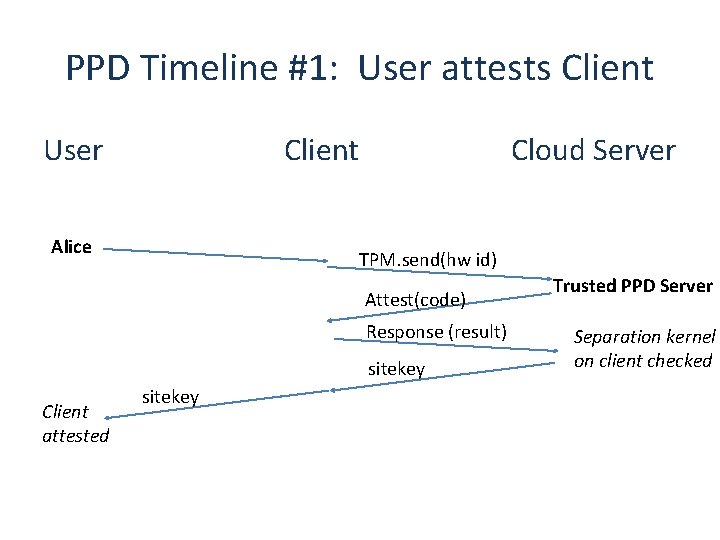
PPD Timeline #1: User attests Client User Client Alice Cloud Server TPM. send(hw id) Attest(code) Response (result) sitekey Client attested sitekey Trusted PPD Server Separation kernel on client checked
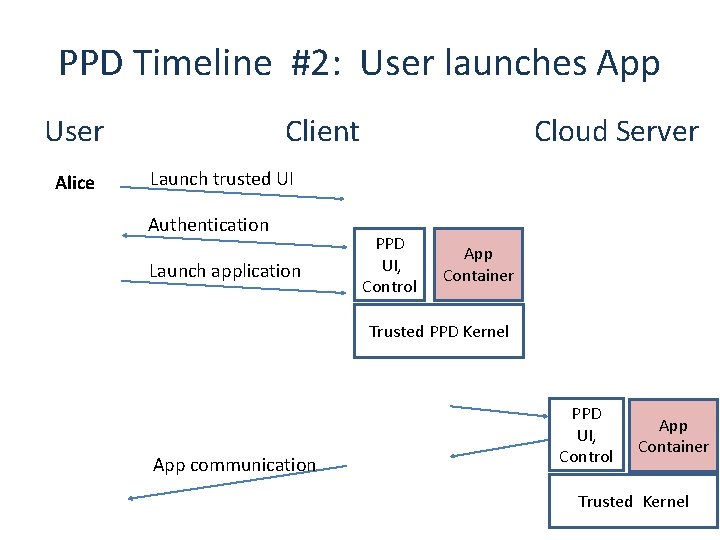
PPD Timeline #2: User launches App User Alice Client Cloud Server Launch trusted UI Authentication Launch application PPD UI, Control App Container Trusted PPD Kernel App communication PPD UI, Control App Container Trusted Kernel
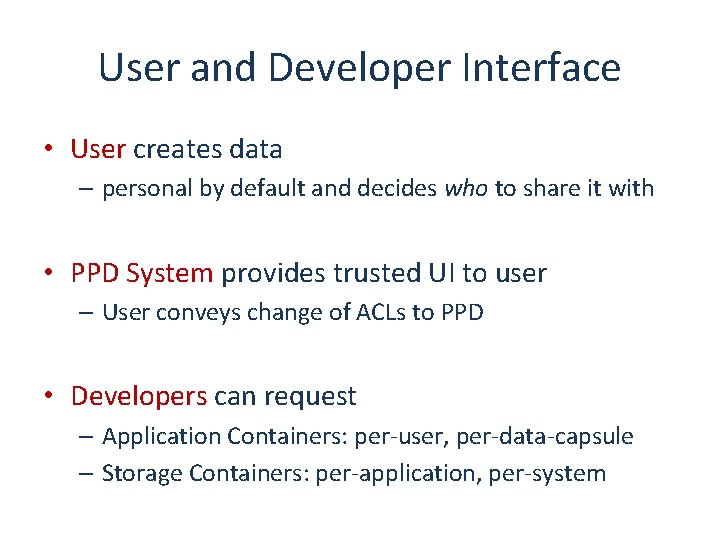
User and Developer Interface • User creates data – personal by default and decides who to share it with • PPD System provides trusted UI to user – User conveys change of ACLs to PPD • Developers can request – Application Containers: per-user, per-data-capsule – Storage Containers: per-application, per-system
Outline of this talk • PPD: Platform for Private Data • PPD Architecture • PPD Prototype and Evaluation
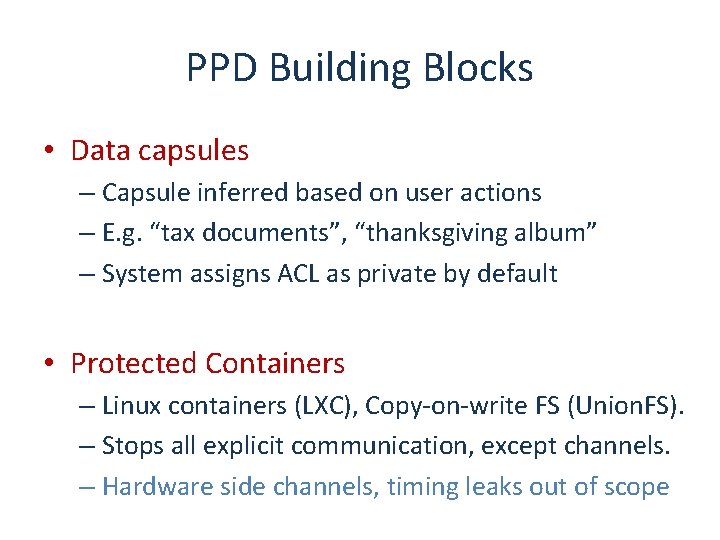
PPD Building Blocks • Data capsules – Capsule inferred based on user actions – E. g. “tax documents”, “thanksgiving album” – System assigns ACL as private by default • Protected Containers – Linux containers (LXC), Copy-on-write FS (Union. FS). – Stops all explicit communication, except channels. – Hardware side channels, timing leaks out of scope
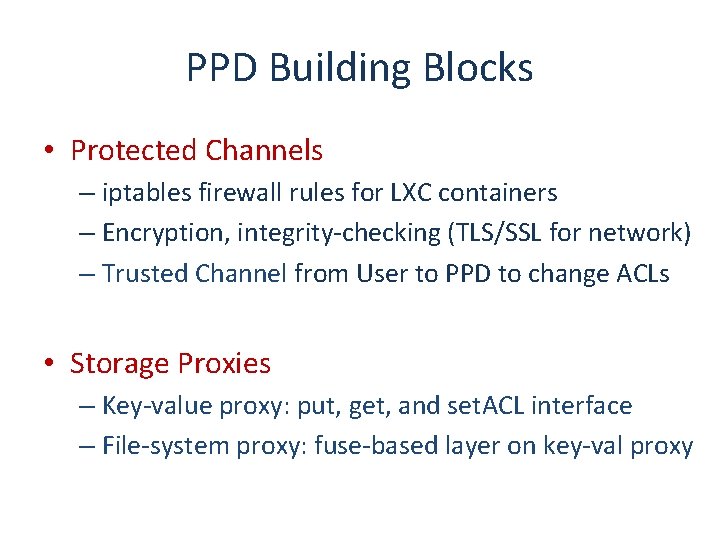
PPD Building Blocks • Protected Channels – iptables firewall rules for LXC containers – Encryption, integrity-checking (TLS/SSL for network) – Trusted Channel from User to PPD to change ACLs • Storage Proxies – Key-value proxy: put, get, and set. ACL interface – File-system proxy: fuse-based layer on key-val proxy
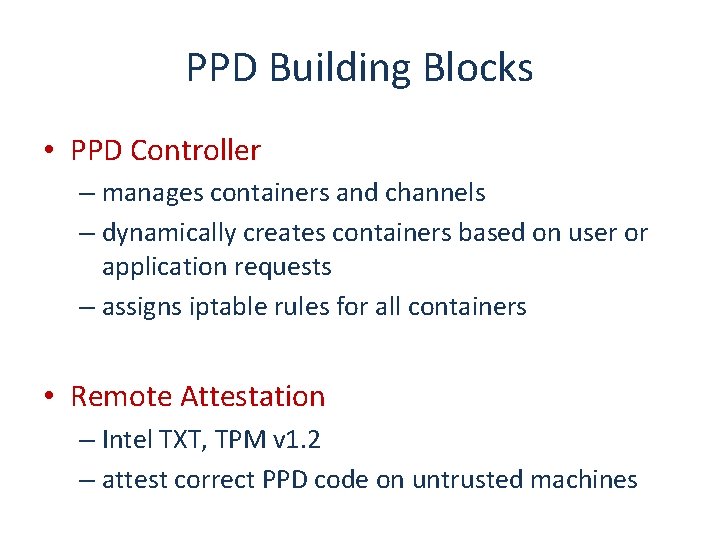
PPD Building Blocks • PPD Controller – manages containers and channels – dynamically creates containers based on user or application requests – assigns iptable rules for all containers • Remote Attestation – Intel TXT, TPM v 1. 2 – attest correct PPD code on untrusted machines
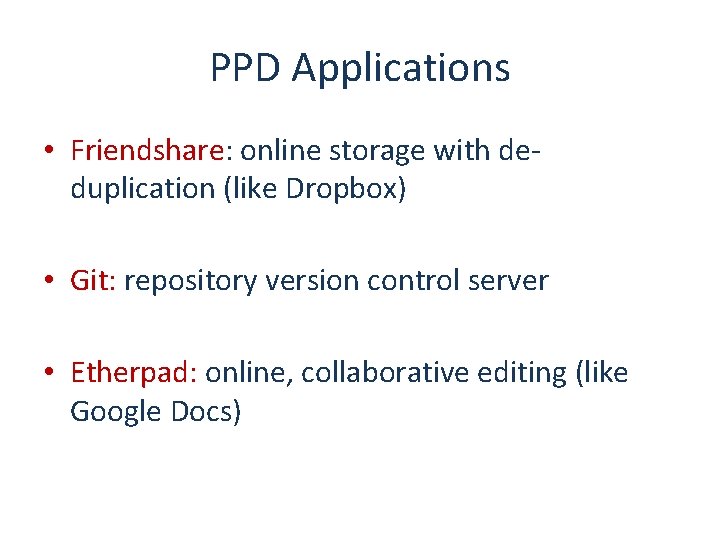
PPD Applications • Friendshare: online storage with deduplication (like Dropbox) • Git: repository version control server • Etherpad: online, collaborative editing (like Google Docs)
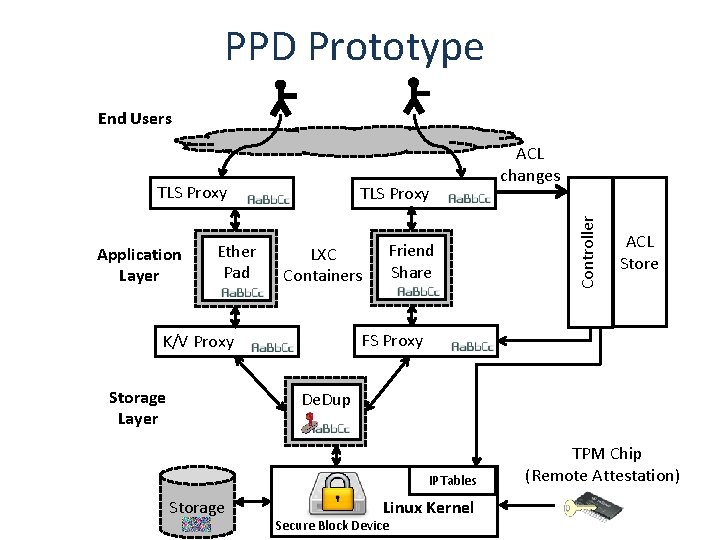
PPD Prototype End Users Application Layer Ether Pad TLS Proxy LXC Containers ACL Store FS Proxy K/V Proxy Storage Layer Friend Share Controller TLS Proxy ACL changes De. Dup IPTables Storage Linux Kernel Secure Block Device TPM Chip (Remote Attestation)
Writing & Porting Apps for PPD • Scripts to install and configure apps in containers • Application v. Storage containers – Friendshare • Application: Scan directories, chunk files, change ACL • Storage: De-duplication – Git, Etherpad • Application: entire functionality
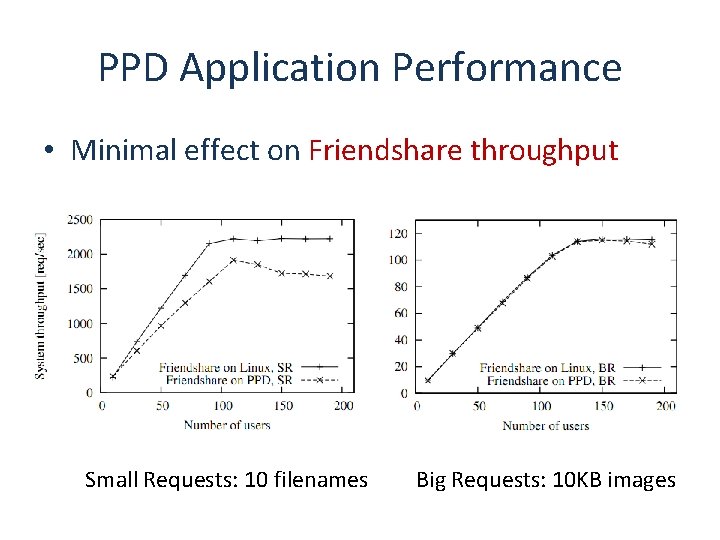
PPD Application Performance • Minimal effect on Friendshare throughput Small Requests: 10 filenames Big Requests: 10 KB images
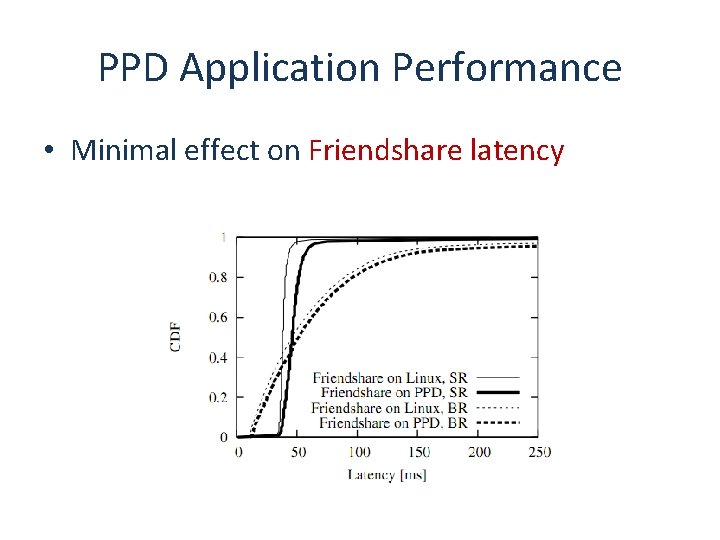
PPD Application Performance • Minimal effect on Friendshare latency
Current and Future Work • Applications – medical applications, business data analytics • Client-side PPD on Android – light-weight containers and channels on Nexus S • Application initiated sharing – differential privacy
Related Approaches • PPD v. DIFC – PPD does not do fine-grained sharing – Constrained containers: simple, yet most benefits of finegrained information flow tracking. – Developer API: reduce run-time exceptions • PPD v. Capabilities – Can be used to implement containers and channels – Re-write legacy applications • PPD v. Android Security – Static, Coarse-grained permissions – User does not own data
Summary • PPD: New Data-Centric Cloud Platform – user controlled sharing – rich, mostly legacy applications • PPD Architecture – untrusted application and storage components • PPD Prototype and Evaluation – small performance and porting cost
The PPD Team
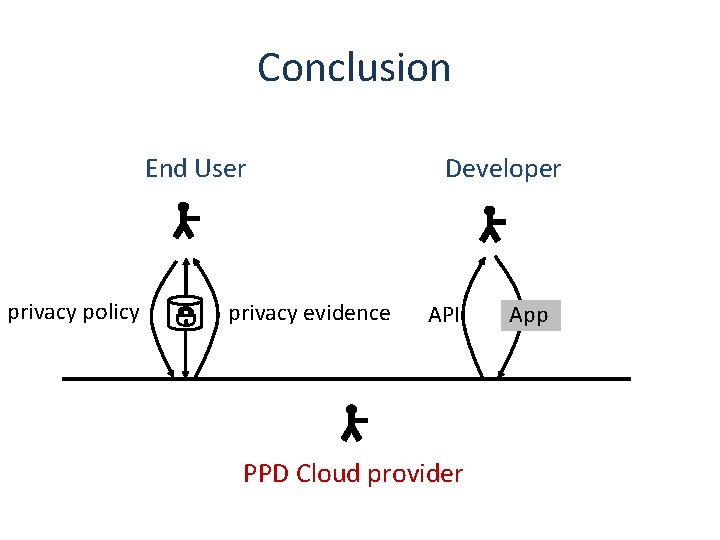
Conclusion End User privacy policy privacy evidence Developer API PPD Cloud provider App
Backups
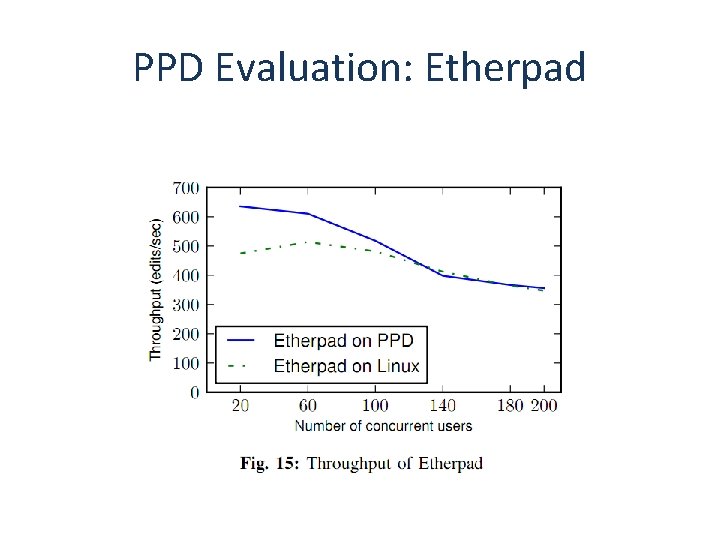
PPD Evaluation: Etherpad
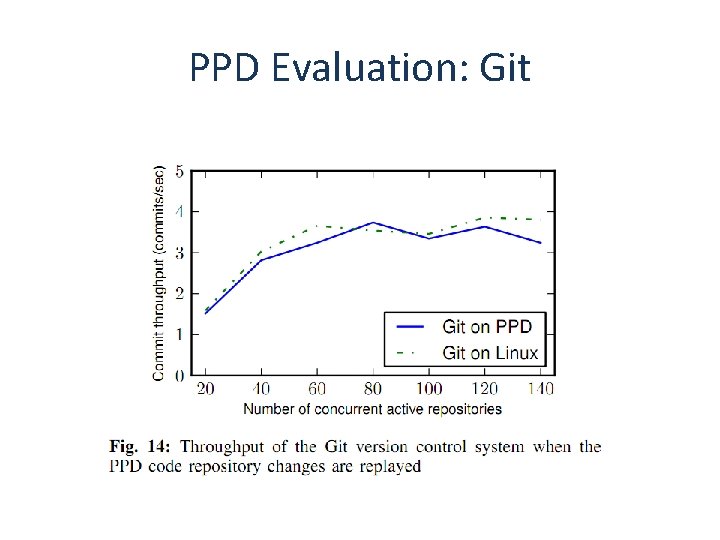
PPD Evaluation: Git
- Slides: 35