Surveillance webinar Wednesday 3 May 12 pm Surveillance

Surveillance webinar Wednesday 3 May 12 pm

Surveillance Webinar

Benefits Privacy
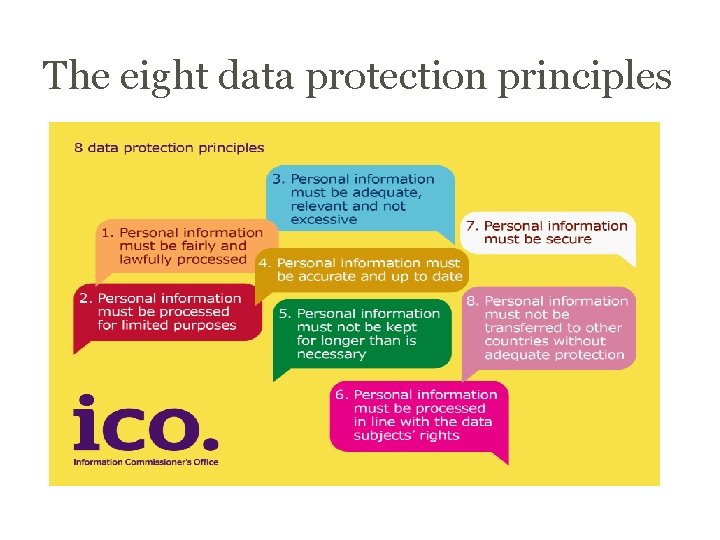
The eight data protection principles

Privacy impact assessments - a risk based, proportionate approach What? When? Why? NOT JUST A CHECKLIST AT THE VERY BEGINNING IDENTIFY RISKS & MITIGATE
ICO code of practice Designed to help those who use surveillance cameras to collect personal data to stay within the law. https: //ico. org. uk/media/fororganisations/documents/154 2/cctv-code-of-practice. pdf

Continuous recording
Use of audio
Have you told individuals what you’re doing? https: //ico. org. uk/fororganisations/guide-todata-protection/privacynotices-transparency-andcontrol

Principle seven – security Appropriate technical & organisational measures
Other considerations • What else do I need to consider? o governance o disclosures
Case Studies



Good Practice



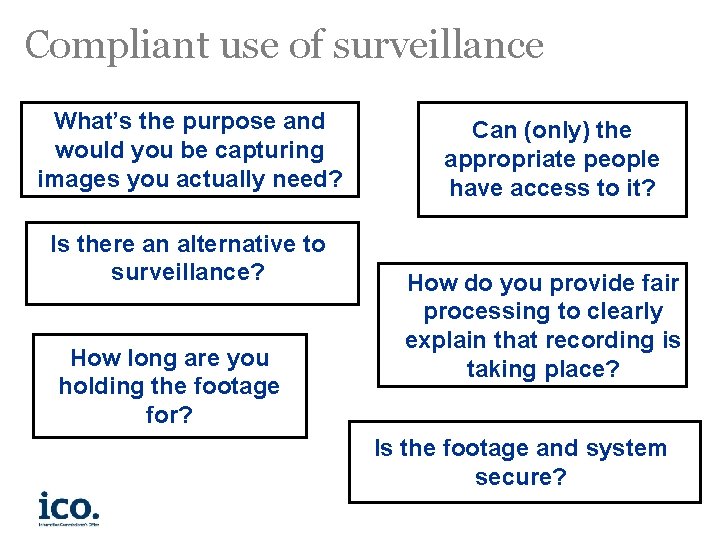
Compliant use of surveillance What’s the purpose and would you be capturing images you actually need? Is there an alternative to surveillance? How long are you holding the footage for? Can (only) the appropriate people have access to it? How do you provide fair processing to clearly explain that recording is taking place? Is the footage and system secure?
An effective PIA will allow organisations to identify and fix problems at an early stage, reducing the associated costs and damage to reputation which might otherwise occur. PIAs are an integral part of taking a privacy by design approach https: //ico. org. uk/media/fororganisations/documents/1595 /pia-code-of-practice. pdf


https: //www. gov. uk/government/organisations/surveillance-camera-commissioner

Data protection reforms
Implement data protection by design and default (Art 25). • Pseudonymisation • Transparency • Data minimisation
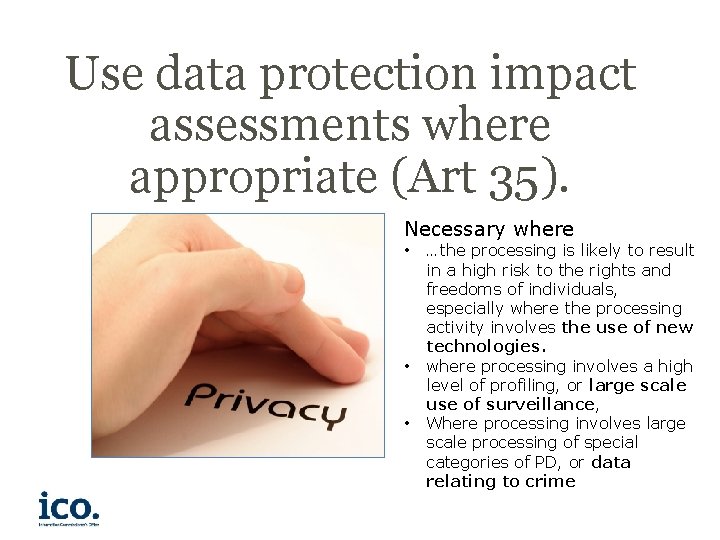
Use data protection impact assessments where appropriate (Art 35). Necessary where • • • …the processing is likely to result in a high risk to the rights and freedoms of individuals, especially where the processing activity involves the use of new technologies. where processing involves a high level of profiling, or large scale use of surveillance, Where processing involves large scale processing of special categories of PD, or data relating to crime
Security requirements Pseudonymisation and encryption – specifically mentioned as security measures. You must be able to ensure the confidentiality, integrity, availability and resilience of your systems. The ability to restore the availability of and access to data in a timely manner. Have a process to test, assess and evaluate the effectiveness of the measures you have in place.

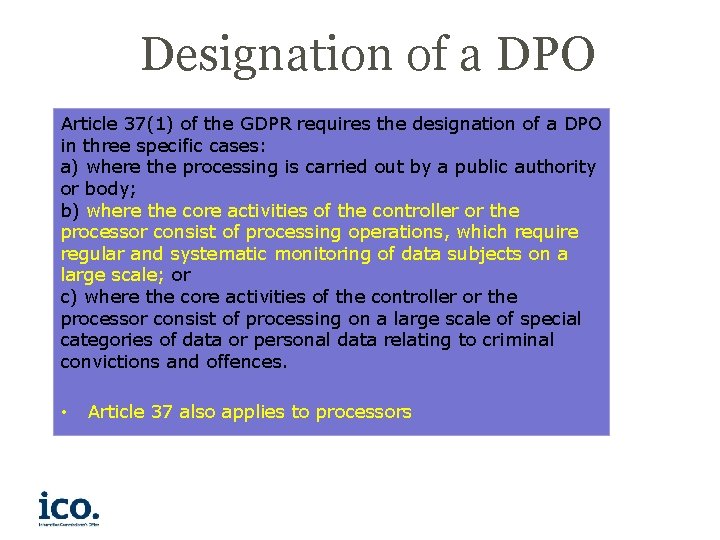
Designation of a DPO Article 37(1) of the GDPR requires the designation of a DPO in three specific cases: a) where the processing is carried out by a public authority or body; b) where the core activities of the controller or the processor consist of processing operations, which require regular and systematic monitoring of data subjects on a large scale; or c) where the core activities of the controller or the processor consist of processing on a large scale of special categories of data or personal data relating to criminal convictions and offences. • Article 37 also applies to processors

ico. org. uk/dpreform

Any Questions? Helpline: 0303 123 1313 Keep in touch by subscribing to our e-newsletter at www. ico. org. uk or find us on… • www. twitter. com/icone ws
- Slides: 33