Succinct Blind Quantum Computation Using a Random Oracle
Succinct Blind Quantum Computation Using a Random Oracle Jiayu Zhang, Boston University, jyz 16@bu. edu Ar. Xiv: 2004. 12621
![What is blind quantum computation? [Childs’ 06] Classical/Quantum interactions • A fundamental problem in What is blind quantum computation? [Childs’ 06] Classical/Quantum interactions • A fundamental problem in](http://slidetodoc.com/presentation_image_h2/8e592f95a31e7bf4686bbcfc77f2bd8a/image-2.jpg)
What is blind quantum computation? [Childs’ 06] Classical/Quantum interactions • A fundamental problem in quantum cryptography • New techniques often led to advances in related problems This work: universal BQC protocol with “succinct” client-side quantum computation, in the random oracle model Models idealized symmetric-key primitives
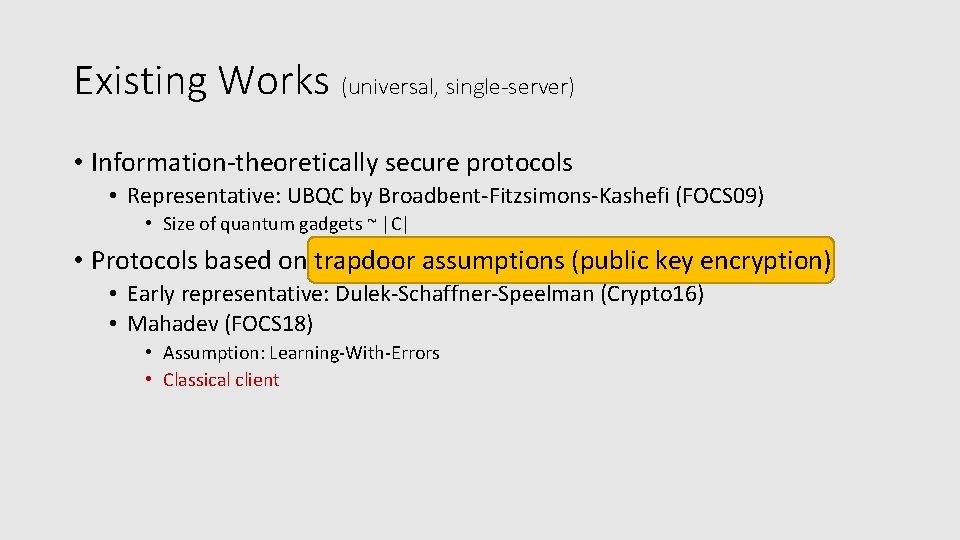
Existing Works (universal, single-server) • Information-theoretically secure protocols • Representative: UBQC by Broadbent-Fitzsimons-Kashefi (FOCS 09) • Size of quantum gadgets ~ |C| • Protocols based on trapdoor assumptions (public key encryption) • Early representative: Dulek-Schaffner-Speelman (Crypto 16) • Mahadev (FOCS 18) • Assumption: Learning-With-Errors • Classical client
What if we have only symmetric-key cryptographic primitives? Specific goal: Client side quantum computation independent of circuit size |C|
If we classify protocols based on client-side quantum computation and assumptions… Client side quantum computation IT (Informationtheoretically) secure IT-secure in Quantum Random Oracle Model (QROM) Classical Might be impossible ☠�[ACGK 17] Unknown ☹� This work [BFK 09] Models idealized symmetric-key primitives LWE-based [Mahadev 17] [DSS 16]
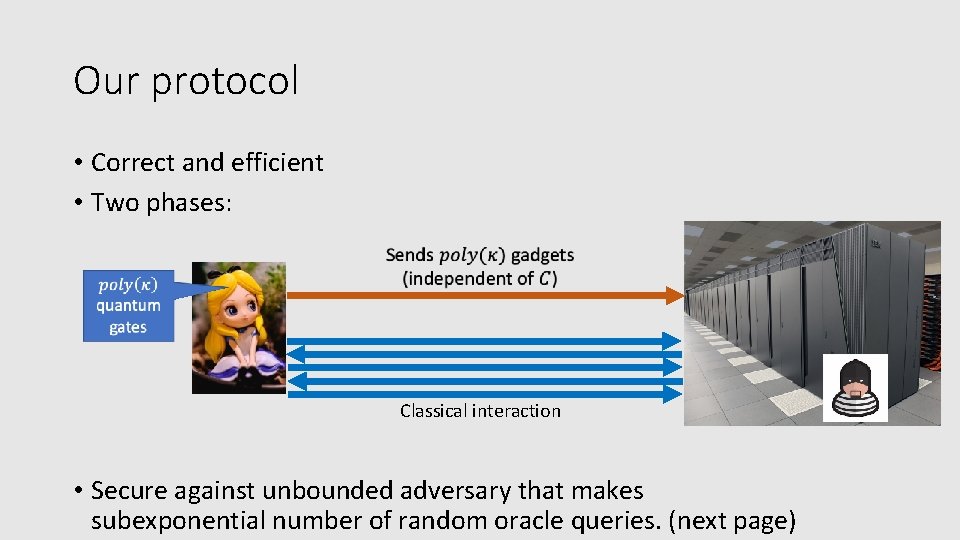
Our protocol • Correct and efficient • Two phases: Classical interaction • Secure against unbounded adversary that makes subexponential number of random oracle queries. (next page)
![A Top-down Overview of Our Construction Each gadget: [BCMVV 18] expand to enough gadgets A Top-down Overview of Our Construction Each gadget: [BCMVV 18] expand to enough gadgets](http://slidetodoc.com/presentation_image_h2/8e592f95a31e7bf4686bbcfc77f2bd8a/image-7.jpg)
A Top-down Overview of Our Construction Each gadget: [BCMVV 18] expand to enough gadgets via classical interaction. This step is the most work…�� �� “Remote gadget preparation” via: 1. Designing a weakly-secure gadget -increasing protocol • Robust reversible garbled tables, padded Hadamard test, parallel repetition etc… 2. Amplifying security Time arrow Also nontrivial…�� • “Repeat-and-combine”
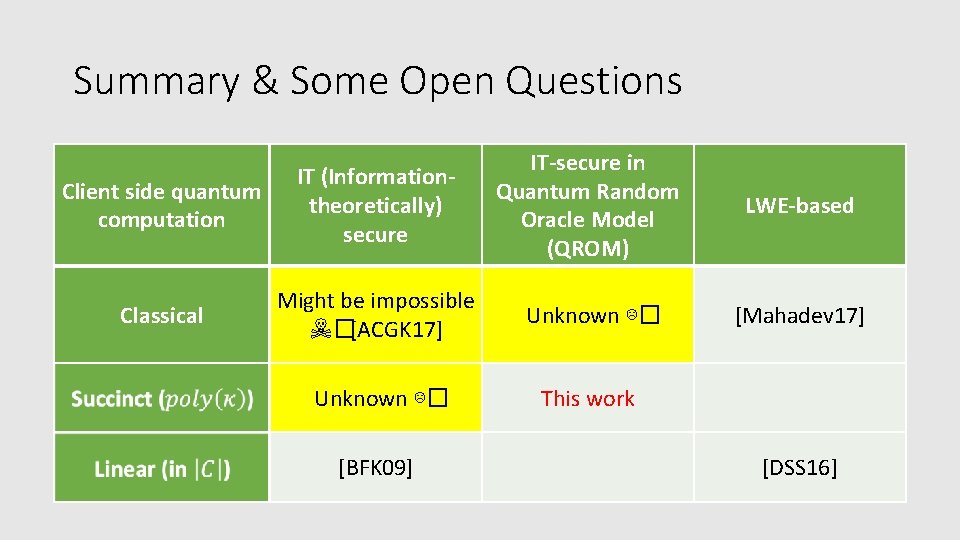
Summary & Some Open Questions IT-secure in • Repeat table from. ITbeginning (smaller) (Information- Client side quantum computation theoretically) secure Quantum Random Oracle Model (QROM) LWE-based • Mention trapdoor functions from QROM? Classical Might be impossible ☠�[ACGK 17] Unknown ☹� This work [Mahadev 17] • Verification? [BFK 09] [DSS 16]
![Thank You! • [BDFLSZ 11] Boneh, Dan & Dagdelen, Özgür & Fischlin, Marc & Thank You! • [BDFLSZ 11] Boneh, Dan & Dagdelen, Özgür & Fischlin, Marc &](http://slidetodoc.com/presentation_image_h2/8e592f95a31e7bf4686bbcfc77f2bd8a/image-9.jpg)
Thank You! • [BDFLSZ 11] Boneh, Dan & Dagdelen, Özgür & Fischlin, Marc & Lehmann, Anja & Schaffner, Christian & Zhandry, Mark. Random Oracles in a Quantum World. Asiacrypt 2011 • [CGH 00] Canetti, Ran and Goldreich, Oded and Halevi, Shai. The Random Oracle Methodology, Revisited. J. ACM 2004 • [BCMVV 18] Zvika Brakerski, Paul Christiano, Urmila Mahadev, Umesh Vazirani, Thomas Vidick. A Cryptographic Test of Quantumness and Certifiable Randomness from a Single Quantum Device. FOCS 18 • [Mahadev 18] Urmila Mahadev. Classical Verification of Quantum Computation. FOCS 18. • [ACGK 17] Scott Aaronson, Alexandru Cojocaru, Alexandru Gheorghiu, Elham Kashefi Complexity Theoretic Limitation of Information-theoretically Secure Blind Quantum Computation. ICALP 2019 • [DSS 16] Yfke Dulek, Christian Schaffner, Florian Speelman, Quantum Homomorphic Encryption for Polynomial-Sized Circuits, CRYPTO 2016
- Slides: 9