SUBSTITUTION CIPHERS A substitution technique is one in
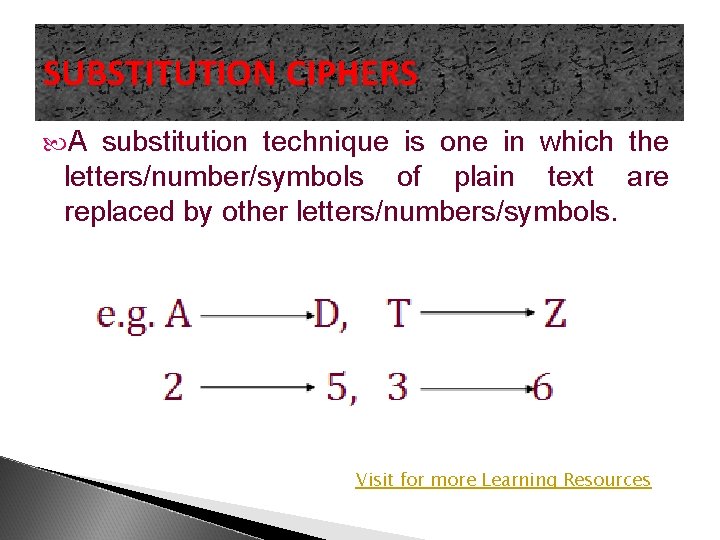
SUBSTITUTION CIPHERS A substitution technique is one in which the letters/number/symbols of plain text are replaced by other letters/numbers/symbols. Visit for more Learning Resources
Substitution cipher techniques 1. 2. 3. 4. 5. 6. Caesar's Cipher –right shift by 3 Mono-Alphabetic Cipher –random substitution A Homophonic Substitution Cipher-one to many substitution A Polygram Substitution Cipher-many to many substitution A Polyalphabetic Substitution Cipher-key to each plain text 1. e g. Vigenere Cipher One time Pad( Vernam Cipher) [Note: write plain text in lower letter and cipher text in capital letters]
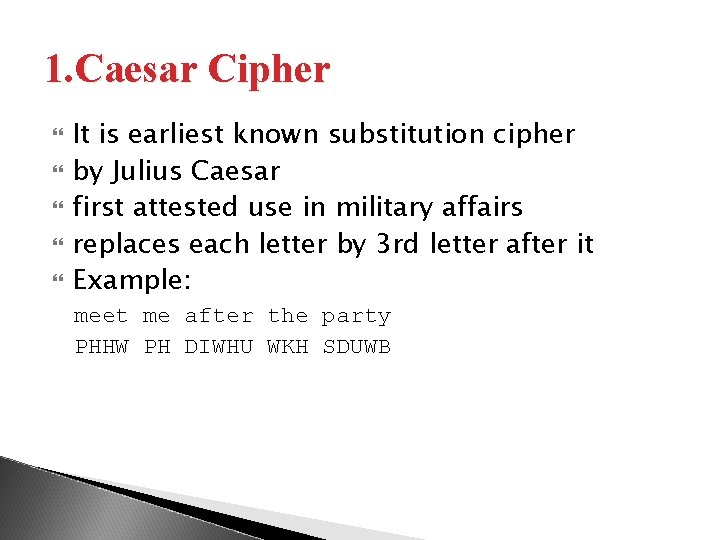
1. Caesar Cipher It is earliest known substitution cipher by Julius Caesar first attested use in military affairs replaces each letter by 3 rd letter after it Example: meet me after the party PHHW PH DIWHU WKH SDUWB
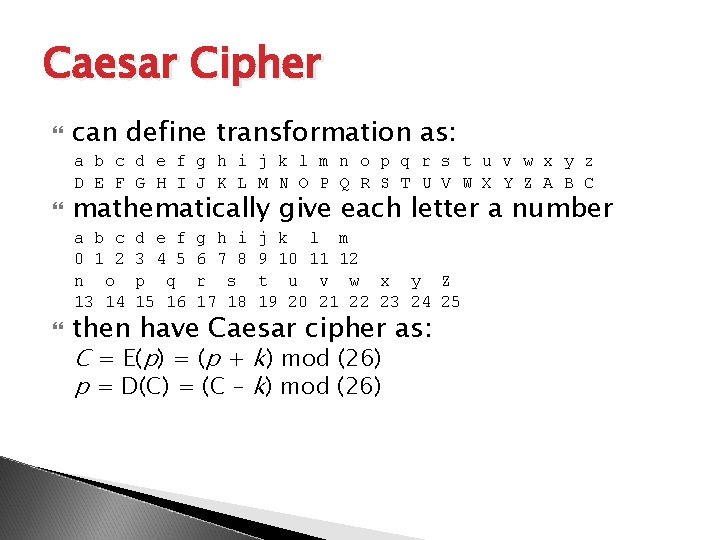
Caesar Cipher can define transformation as: a b c d e f g h i j k l m n o p q r s t u v w x y z D E F G H I J K L M N O P Q R S T U V W X Y Z A B C mathematically give each letter a number a b c 0 1 2 n o 13 14 d e f 3 4 5 p q 15 16 g h i 6 7 8 r s 17 18 j k l m 9 10 11 12 t u v w x y Z 19 20 21 22 23 24 25 then have Caesar cipher as: C = E(p) = (p + k) mod (26) p = D(C) = (C – k) mod (26)
2. Mono alphabetic Cipher The week ness of Caesar's cipher is it’s predictability. Instead of using a unique form for all alphabets in a plain text message use a random substitution. Rather than just shifting the alphabet we could shuffle (jumble) the letters arbitrarily Each plaintext letter maps to a different random cipher text letter hence key is 26 letters long
Plain text: Hello word Cipher text: ACDER PQSAK
3. A Homophonic Substitution Cipher In this technique one plain text is mapped with more than one cipher text alphabet. h-[ABXY] I –[MNQR] Plain text: hi Cipher text: ABXYMNQR
4. A Polygram Substitution Cipher Rather than replacing one plain text with another cipher text at time block of alphabet is replaced with another. Plain text: hi hello Cipher text: JH KNHPL
5. Polyalphabetic Ciphers It uses multiple one character key. Each of the key encrypts one plain text character. First key encrypts 1 st key , second key encrypts 2 nd key, so on. . E. g ◦ Vigenere cipher is example of poly alphabetic cipher
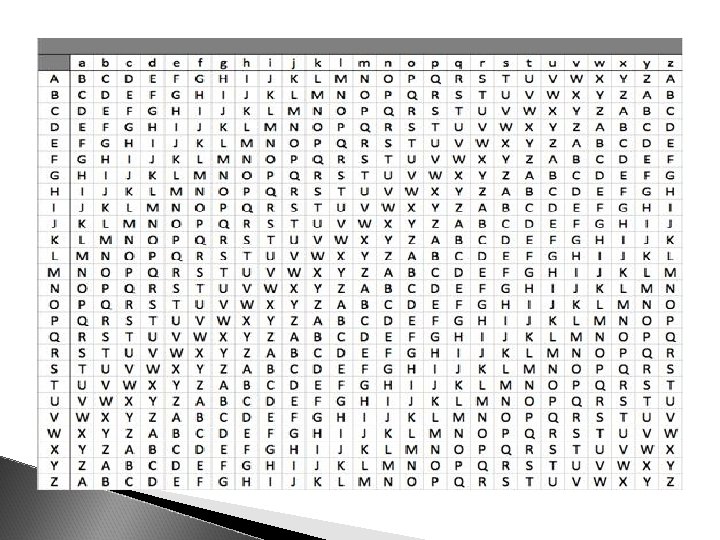
Vigenere Cipher It is based on vigenere table. It is made up of 27 rows. 1 st row of lower case letters represents plain text character. Each subsequent row represent cipher alphabet.
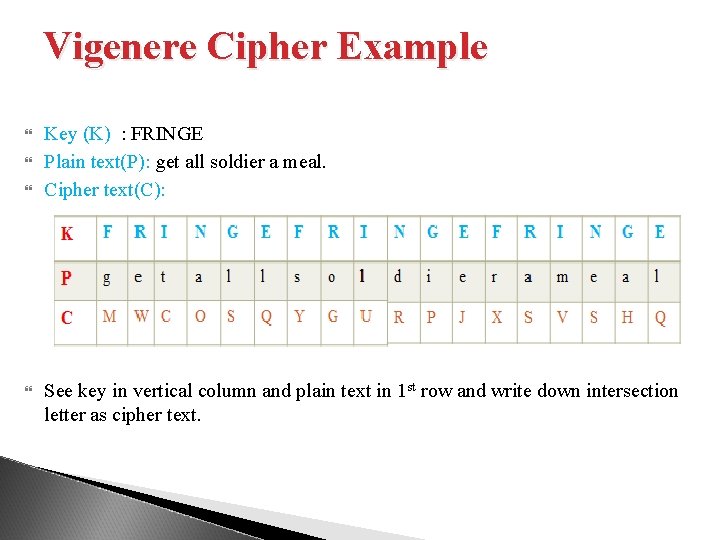
Vigenere Cipher Example Key (K) : FRINGE Plain text(P): get all soldier a meal. Cipher text(C): See key in vertical column and plain text in 1 st row and write down intersection letter as cipher text.
6. One time pad ( Vernam Cipher) It is implemented using random set of non repeating characters as the input cipher text. Once the key is used to encrypt and decrypt a single message it will never used again for any other message so it is called one time pad The length of key must equal to length of original plain text. Plain text: how are you One time pad: NCBTZQARX
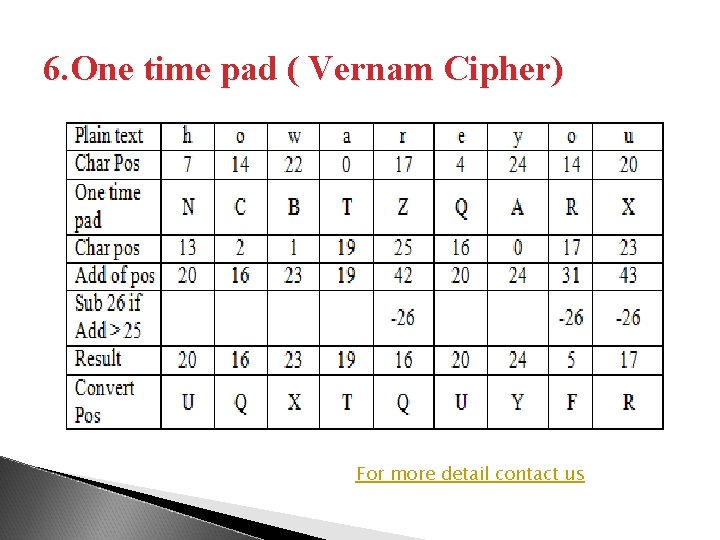
6. One time pad ( Vernam Cipher) For more detail contact us
- Slides: 14