Submitted By Varun Singh Roll no MRT 09
Submitted By: Varun Singh Roll no. : MRT 09 UGBCS 036
Contents: � 1. Introduction. � 2. History. � 3. Classic Techniques. � 4. Motivation. � 5. Stegnography in text. � 6. Stegnography in audio. � 7. Stegnography in video. � 8. Stegnography vs. Watermarking. � 9. Good Stegnography.
Introduction: � Stegnography : A secret manner of writing, … Generally, the art of writing or solving ciphers. — Oxford English Dictionary Stegno - Graphy Covered Writing
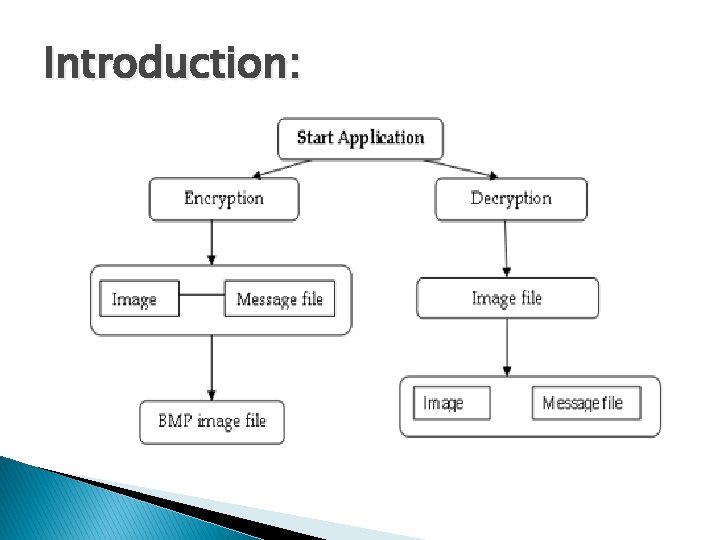
Introduction:
Introduction: Art and science of communicating in a way that hides the existence of a message signal or pattern imposed on content. ◦ persistent under transmission ◦ not encryption �original image/file is intact ◦ not fingerprinting �fingerprinting leaves separate file describing contents
Introduction: � This can be achieve by concealing the existence of information within seemingly harmless carriers or cover � Carrier: text, image, video, audio, etc.
History: � The first recorded uses of steganography can be traced back to 440 BC when Herodotus mentions two examples of steganography in his Histories. Demaratus sent a warning about a forthcoming attack to Greece by writing it directly on the wooden backing of a wax tablet before applying its beeswax surface. � In his work "Polygraphiae" Johannes Trithemius developed his socalled "Ave-Maria-Cipher" with which one can hide information in a Latin praise of God.
Classic techniques: � Invisible � Tatoo ink (1 st century AD - WW II) message on head � Overwrite pencil � Pin select characters in printed type in punctures in type � Microdots (WW II) � Newspaper clippings, knitting instructions, XOXO signatures, report cards.
Motivation: � Steganography computing. received little attention in � Renewed interest because of industry desire to protect copyrighted digital work. ◦ ◦ audio images video Text � Detect counterfeiter, unauthorized presentation, embed key, embed author ID � Steganography ≠ Copy protection
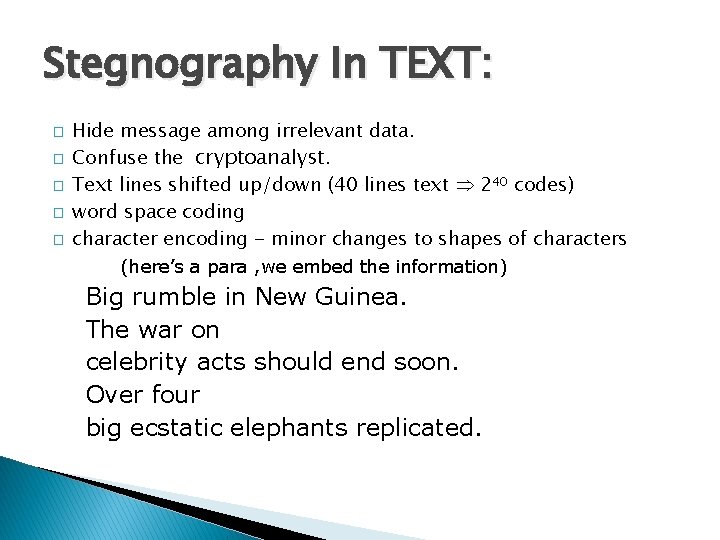
Stegnography In TEXT: � � � Hide message among irrelevant data. Confuse the cryptoanalyst. Text lines shifted up/down (40 lines text 240 codes) word space coding character encoding - minor changes to shapes of characters (here’s a para , we embed the information) Big rumble in New Guinea. The war on celebrity acts should end soon. Over four big ecstatic elephants replicated.
Stegnography In TEXT: Big rumble in New Guinea. The war on celebrity acts should end soon. Over four big ecstatic elephants replicated. Bring two cases of beer. [this is the information hiding in the paragraphy by stegnography technique. ]
Stegnography In Audio: Perceptual coding ◦ inject signal into areas that will not be detected by humans ◦ may be obliterated by compression. Hardware with copy-protection ◦ ◦ not true watermarking - metadata present on media DAT. minidisc presence of copy protection mechanisms often failed to give the media wide-spread acceptance
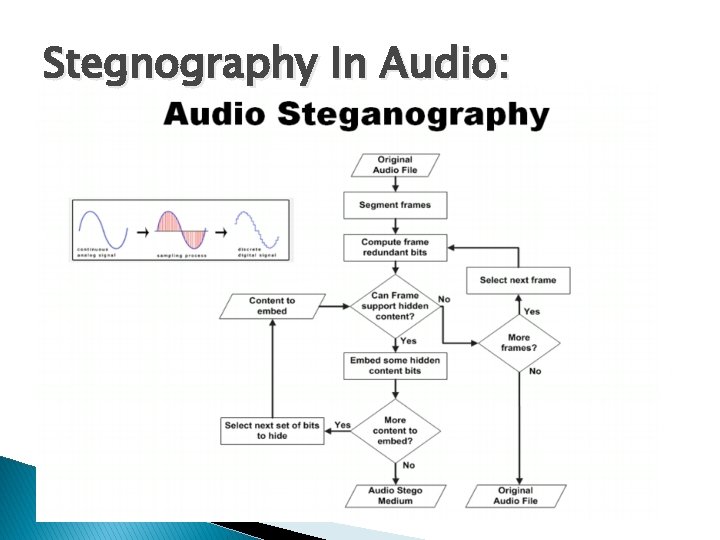
Stegnography In Audio:
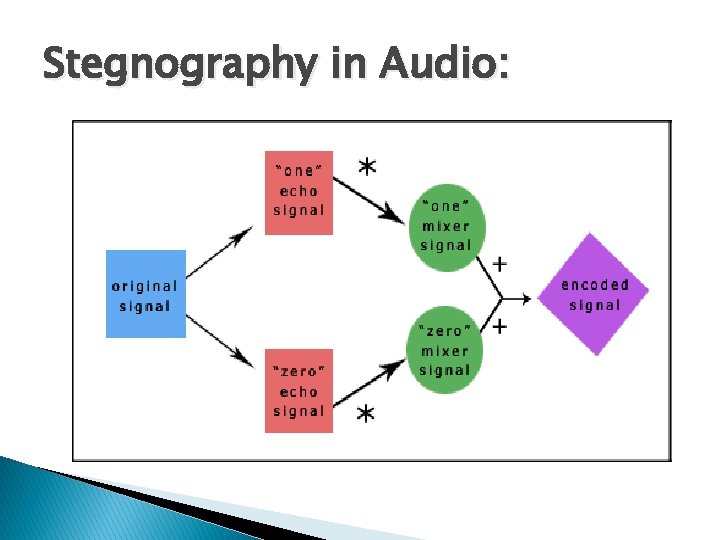
Stegnography in Audio:
Stegnography In Video: � Coding � data still frames - spatial or frequency encoded during refresh. ◦ closed captioning � visible watermarking ◦ used by most networks.
Stegnography In Video: � Although BMP files are perfect for steganographic use, they are able to carry only small files. So there is a problem, how to get much enough files to hide our message, and what to do to read them in a correct order? Good way out is to hide information in a video file, because as we know, AVI files are created out of bitmaps, combined into one piece, which are played in correct order and with appropriate time gap. Keeping that in mind all we have to do is to get out is file single frames and save them as BMP files. If we’ll use algorithm for hiding data in digital pictures, we can hide our message in bitmap obtained in this way, and then save it into new AVI file. � We’ll analyze only uncompressed AVI file, because if any compression is executed files loses its data.
Watermarking vs. Steganography: Goal of steganography ◦ Intruder cannot detect a message ◦ Primarily 1 to 1 communication. Goal of watermarking ◦ Intruder cannot remove or replace the message ◦ Primarily 1: many communication
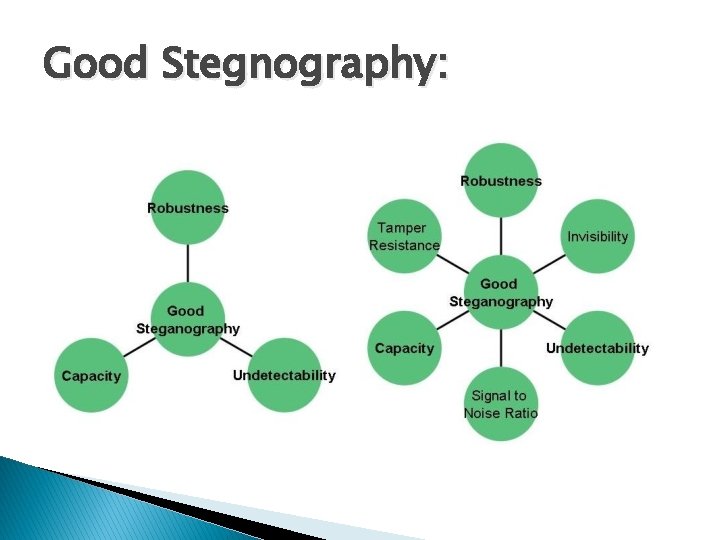
Good Stegnography:
Refrences: � www. wikipedia. com � www. projecttoseminars. com � www. answers. com � http: //brasil. cel. agh. edu. pl/~11 ugbogusz/in dex. php? option=com_content&view=article&i d=11&Itemid=16&lang=en � http: //www. snotmonkey. com/work/school/4 05/methods. html
THANK YOU Any Ques? ?
- Slides: 20