Submarine Warfare Perimeter defense without walls Dan Houser
Submarine Warfare: Perimeter defense without walls Dan Houser, CISSP, CISM
Overview l Classic firewall perspective l Where firewalls fall short l Changes in the security space l Suggestions for improving network security • Strategic vision • Tactical focus l Q&A This presentation is designed to be the visit through the looking glass… Thinking about perimeter security with a different perspective. ©Copyright 2004 – Daniel D. Houser
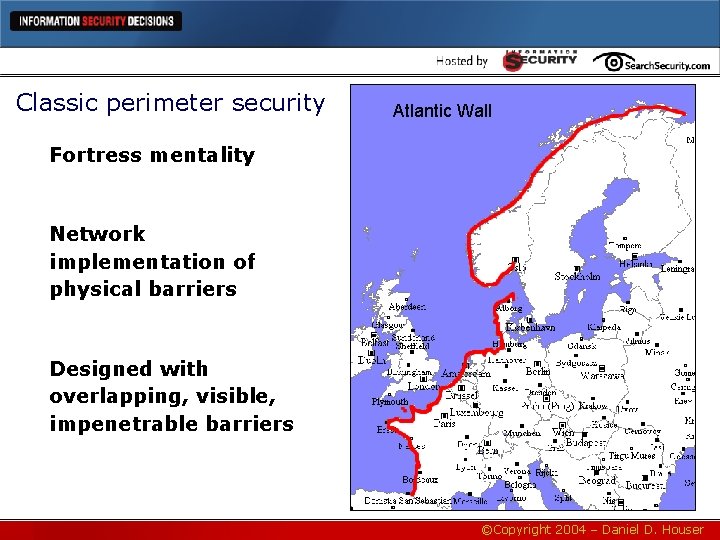
Classic perimeter security Atlantic Wall Fortress mentality Network implementation of physical barriers Designed with overlapping, visible, impenetrable barriers ©Copyright 2004 – Daniel D. Houser
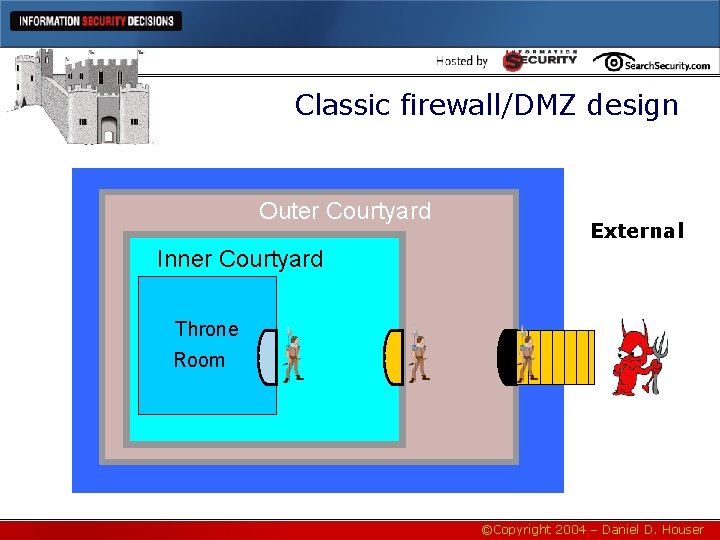
Classic firewall/DMZ design Outer Courtyard External Inner Courtyard Throne Room ©Copyright 2004 – Daniel D. Houser
Assumptions of the classic perimeter security model l Attackers are outside trying to break in l Attackers cannot breach the wall l Attackers are identified by guards l Guards are loyal l All contact comes through single path Unfortunately, these are all wrong. ©Copyright 2004 – Daniel D. Houser
Reality l Most attackers are inside l Attackers can breach the wall l Guards can’t identify all attackers l Guards can be subverted l Communication over MANY paths ©Copyright 2004 – Daniel D. Houser
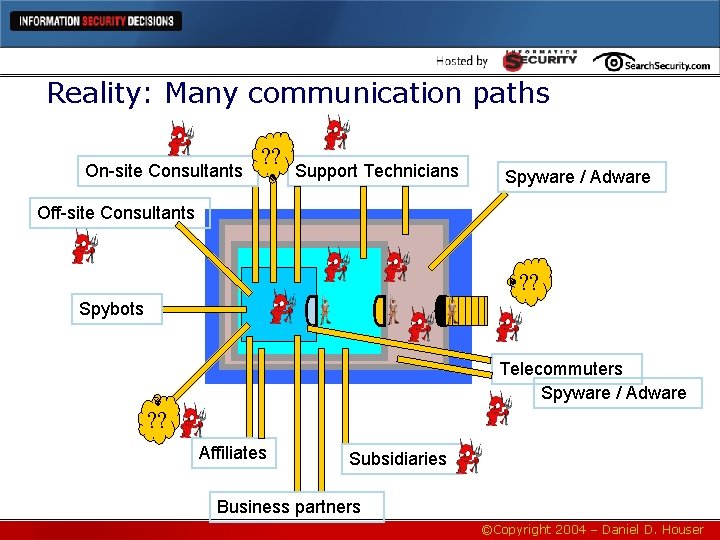
Reality: Many communication paths On-site Consultants ? ? Support Technicians Spyware / Adware Off-site Consultants ? ? Spybots Telecommuters Spyware / Adware ? ? Affiliates Subsidiaries Business partners ©Copyright 2004 – Daniel D. Houser
Red Queen race “You have to run faster and faster just to stay in the same place!” – The Red Queen, Alice in Wonderland Image courtesy www. rushlimbaugh. com ©Copyright 2004 – Daniel D. Houser
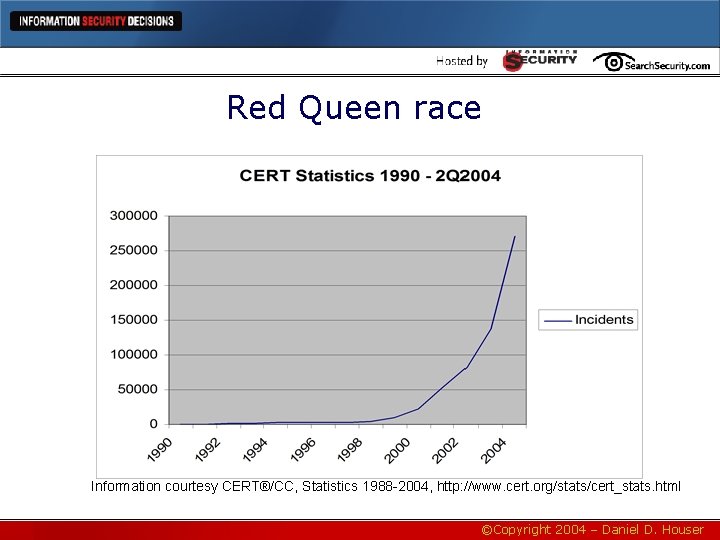
Red Queen race Information courtesy CERT®/CC, Statistics 1988 -2004, http: //www. cert. org/stats/cert_stats. html ©Copyright 2004 – Daniel D. Houser
Red Queen race l Web Services Security is changing the rules: • Outsourced authentication (federated) • Extranet access to core systems • RPC calls over HTTP using XML & SOAP l Offshore services, data processing l Highly connected networks l Very tight business integration In short, there is no network perimeter ©Copyright 2004 – Daniel D. Houser
New paradigms are needed We must migrate from ground-based warfare to a model that fits information warfare “He who does not learn from history is doomed to repeat it. ” • • The Maginot Line was bypassed The Atlantic Wall was pierced and defeated The Great Wall provided only partial protection The Alamo fell to a massive attack ©Copyright 2004 – Daniel D. Houser
New paradigm: Submarine warfare l In submarine warfare • Everyone is an enemy until proven otherwise • All contacts are tracked and logged • Hardened autonomous systems • Rules of engagement govern all response • Constant vigilance l Identify Friend or Foe (IFF) becomes vital l Hunter-killer units vital to protect strategic investments – offensive as well as defensive players l Environment “listeners” for ASW and tracking l Evade detection, hound and confuse the enemy ©Copyright 2004 – Daniel D. Houser
How does submarine warfare translate into Info. Warfare? Harden all devices, not just DMZ • Use of hardened kernels for all servers • Harden all systems and run minimal services Minimal installations on desktops • Dumb terminals where available • Provide Office tools to knowledge workers only • Strip unneeded capabilities from kiosks • Remove the ability to install software Analyze traffic, not just headers • Application-based firewalls • XML Filtering ©Copyright 2004 – Daniel D. Houser
How does Submarine Warfare translate into Info. Warfare? (2) Segregate boot camp from theatre of operations • • VLAN development, test, DR & production Make change control your code firewall Only change control spans 2 security zones Production support segregated from source code Core network becomes the DMZ • • Since most attacks are from within, make cubicles a DMZ Create hardened subnets for accounting, HR, IT, operations • Publish intranets in the DMZ ©Copyright 2004 – Daniel D. Houser
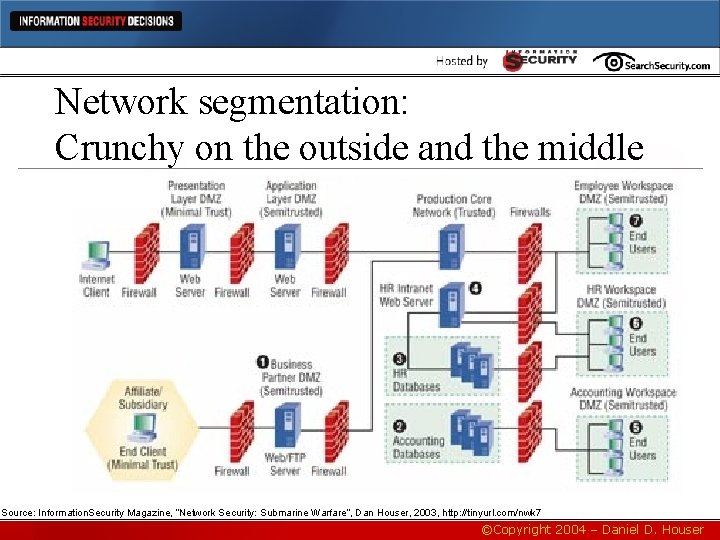
Network segmentation: Crunchy on the outside and the middle Source: Information. Security Magazine, “Network Security: Submarine Warfare”, Dan Houser, 2003, http: //tinyurl. com/nwk 7 ©Copyright 2004 – Daniel D. Houser
How does submarine warfare translate into Info. Warfare? (3) Heavy use of crypto for IFF functions • Accelerators & HSM will be key technologies • Require all packets to be signed (e. g. Kerberos) • Certificate revocation for intrusion prevention • Network PKI becomes mission critical at layer 2 • Some early products emerging in this space (e. g. End. Force) Network IDS is key • Analyzing packets for IFF analysis, heuristics • ISP pre-filtered IDS • Analog threat tagging • Identifying and tracking intruders • Isolating subnets with hostile traffic • Revoke certificates for hostile servers • Vectoring CIRT ©Copyright 2004 – Daniel D. Houser
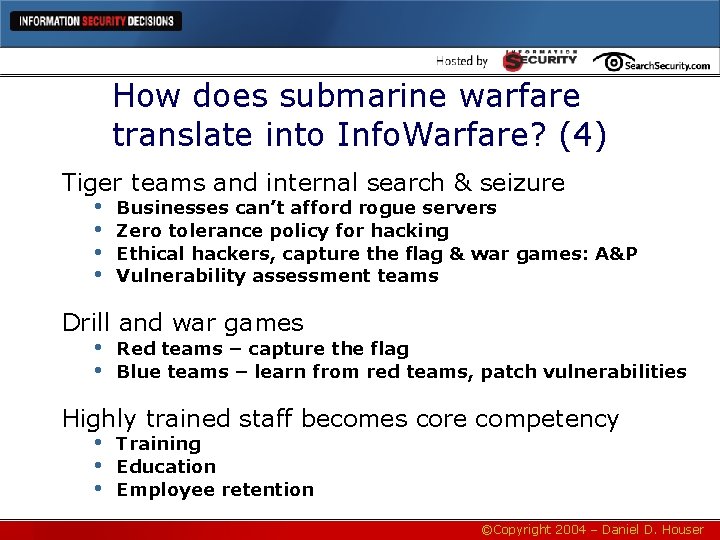
How does submarine warfare translate into Info. Warfare? (4) Tiger teams and internal search & seizure • Businesses can’t afford rogue servers • Zero tolerance policy for hacking • Ethical hackers, capture the flag & war games: A&P • Vulnerability assessment teams Drill and war games • Red teams – capture the flag • Blue teams – learn from red teams, patch vulnerabilities Highly trained staff becomes core competency • Training • Education • Employee retention ©Copyright 2004 – Daniel D. Houser
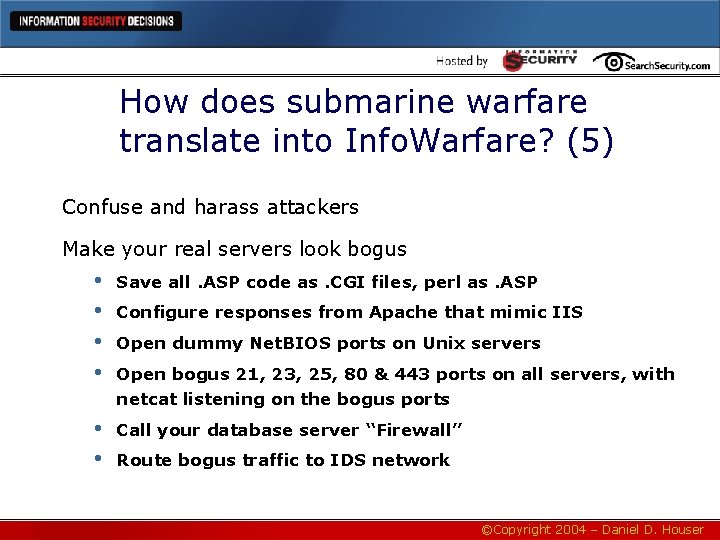
How does submarine warfare translate into Info. Warfare? (5) Confuse and harass attackers Make your real servers look bogus • • Save all. ASP code as. CGI files, perl as. ASP • • Call your database server “Firewall” Configure responses from Apache that mimic IIS Open dummy Net. BIOS ports on Unix servers Open bogus 21, 23, 25, 80 & 443 ports on all servers, with netcat listening on the bogus ports Route bogus traffic to IDS network ©Copyright 2004 – Daniel D. Houser

Internet attacks have changed… Photo Courtesy NASA ©Copyright 2004 – Daniel D. Houser
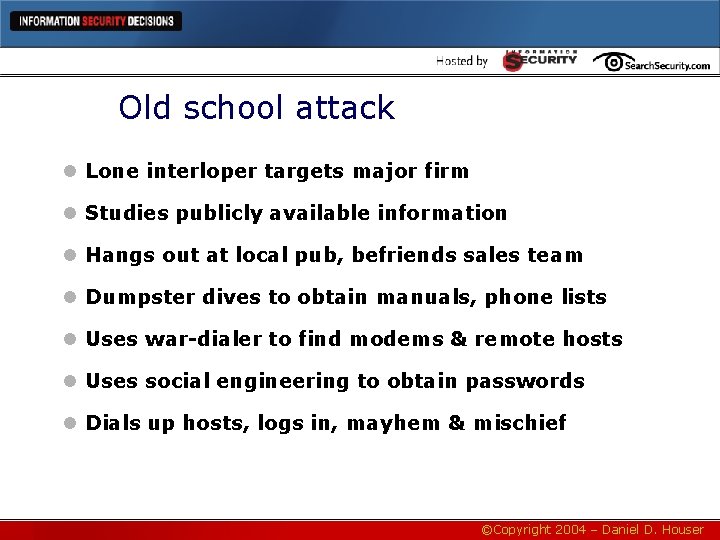
Old school attack l Lone interloper targets major firm l Studies publicly available information l Hangs out at local pub, befriends sales team l Dumpster dives to obtain manuals, phone lists l Uses war-dialer to find modems & remote hosts l Uses social engineering to obtain passwords l Dials up hosts, logs in, mayhem & mischief ©Copyright 2004 – Daniel D. Houser
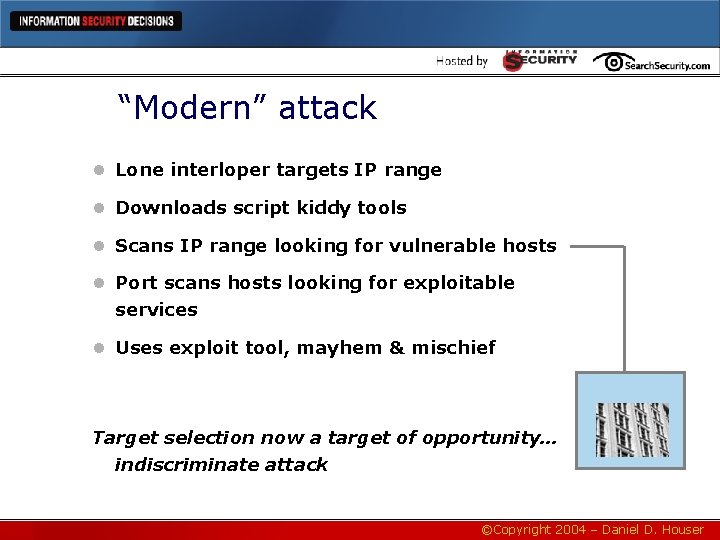
“Modern” attack l Lone interloper targets IP range l Downloads script kiddy tools l Scans IP range looking for vulnerable hosts l Port scans hosts looking for exploitable services l Uses exploit tool, mayhem & mischief Target selection now a target of opportunity… indiscriminate attack ©Copyright 2004 – Daniel D. Houser
Worms hit 10, 000 networks at once… Photo Courtesy The Weather Channel ©Copyright 2004 – Daniel D. Houser
What we need is early warning Photo Courtesy NASA ©Copyright 2004 – Daniel D. Houser
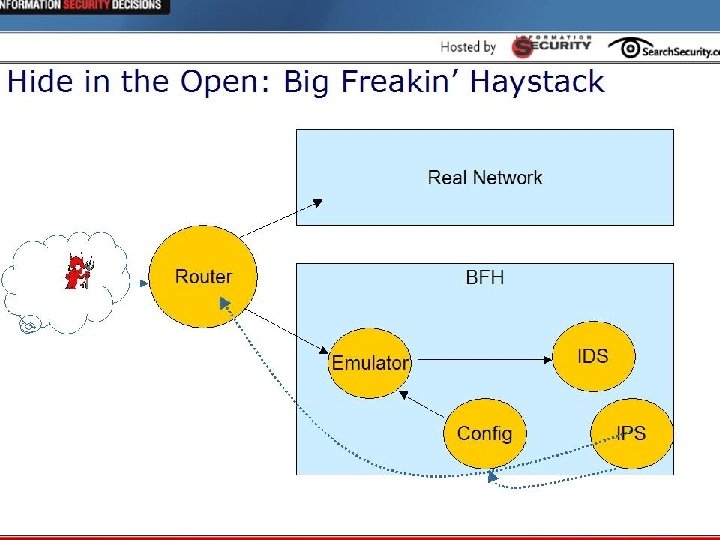
Hide in the open: Big freakin’ haystack • • • Virtual honeynets + Intrusion Management Create server that emulates address range: 10. x. x. x Open tons of ports: 20, 21, 23, 25, 37, 42, 43, 49, 67, 68, 69, 80, 109, 110, 137 -139, 389, 443, 6667 • Emulate good hosts: MS-Exchange, Solaris/Oracle, MS-SQL, Red. Hat/Apache/Tomcat, Win. XP Pro • Emulate bad boxes: botnet servers, Warez server, trojaned workstations, Win 95 workstation, backdoor • Honeyd likely tool, or at least a starting point ©Copyright 2004 – Daniel D. Houser
Hide in the open: Big freakin’ haystack (2) • Convert unused address space into decoy tripwire nets - 16, 320, 000 decoys to 200 "real" servers • Stop swallowing packets: route unreachable hosts to the virtual honeynet • • 190, 000 decoys per “real” server = 99. 9995% detection • Any hits are malicious – route to IDS / IPS § Research attack profile. § Block attackers for 1 hour, 2 hours, 24 hours, 1 week. You’ve gained breathing room to respond to real attacks ©Copyright 2004 – Daniel D. Houser
©Copyright 2004 – Daniel D. Houser
Hide in the open ©Copyright 2004 – Daniel D. Houser
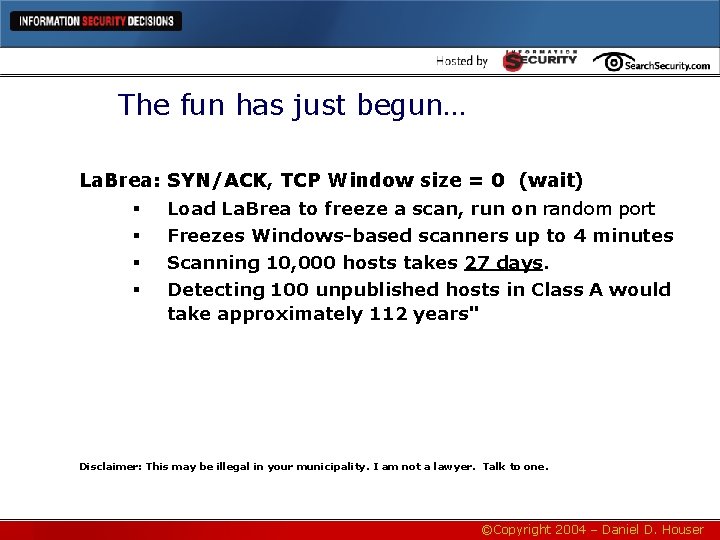
The fun has just begun… La. Brea: § § SYN/ACK, TCP Window size = 0 (wait) Load La. Brea to freeze a scan, run on random port Freezes Windows-based scanners up to 4 minutes Scanning 10, 000 hosts takes 27 days. Detecting 100 unpublished hosts in Class A would take approximately 112 years" Disclaimer: This may be illegal in your municipality. I am not a lawyer. Talk to one. ©Copyright 2004 – Daniel D. Houser
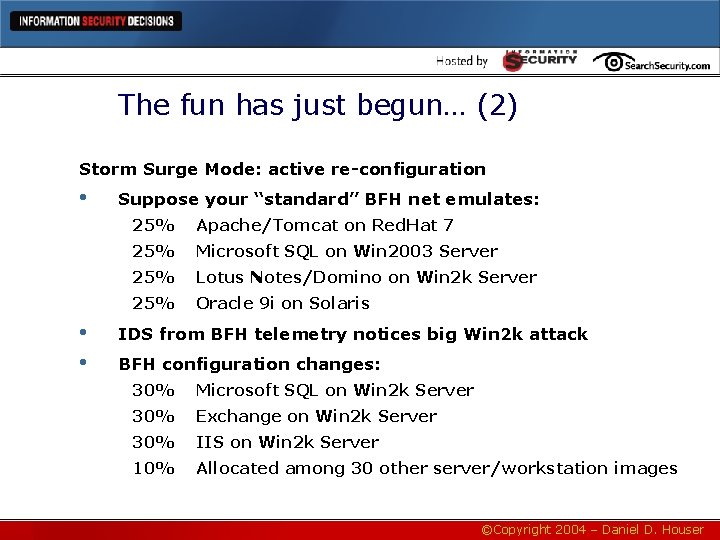
The fun has just begun… (2) Storm Surge Mode: active re-configuration • • • Suppose your “standard” BFH net emulates: 25% Apache/Tomcat on Red. Hat 7 25% Microsoft SQL on Win 2003 Server 25% Lotus Notes/Domino on Win 2 k Server 25% Oracle 9 i on Solaris IDS from BFH telemetry notices big Win 2 k attack BFH configuration changes: 30% Microsoft SQL on Win 2 k Server 30% Exchange on Win 2 k Server 30% IIS on Win 2 k Server 10% Allocated among 30 other server/workstation images ©Copyright 2004 – Daniel D. Houser
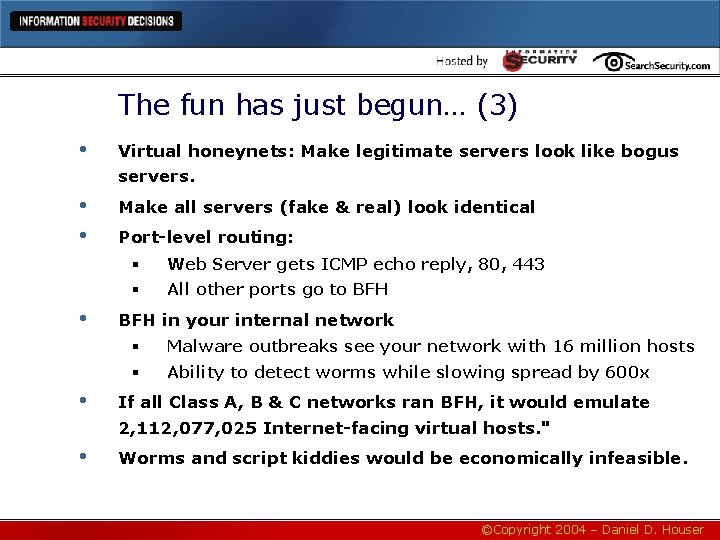
The fun has just begun… (3) • Virtual honeynets: Make legitimate servers look like bogus servers. • • Make all servers (fake & real) look identical • Port-level routing: § Web Server gets ICMP echo reply, 80, 443 § All other ports go to BFH in your internal network § Malware outbreaks see your network with 16 million hosts § Ability to detect worms while slowing spread by 600 x • If all Class A, B & C networks ran BFH, it would emulate 2, 112, 077, 025 Internet-facing virtual hosts. " • Worms and script kiddies would be economically infeasible. ©Copyright 2004 – Daniel D. Houser
Where to get started? Switching models will take time… What do we do in the interim? ©Copyright 2004 – Daniel D. Houser
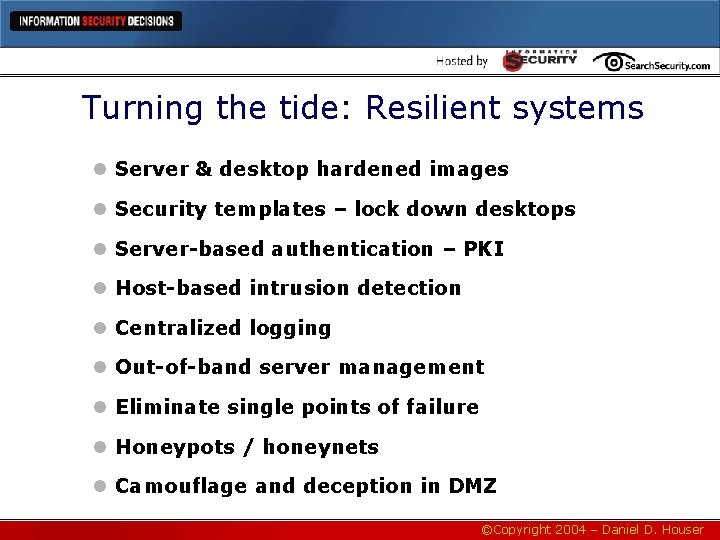
Turning the tide: Resilient systems l Server & desktop hardened images l Security templates – lock down desktops l Server-based authentication – PKI l Host-based intrusion detection l Centralized logging l Out-of-band server management l Eliminate single points of failure l Honeypots / honeynets l Camouflage and deception in DMZ ©Copyright 2004 – Daniel D. Houser
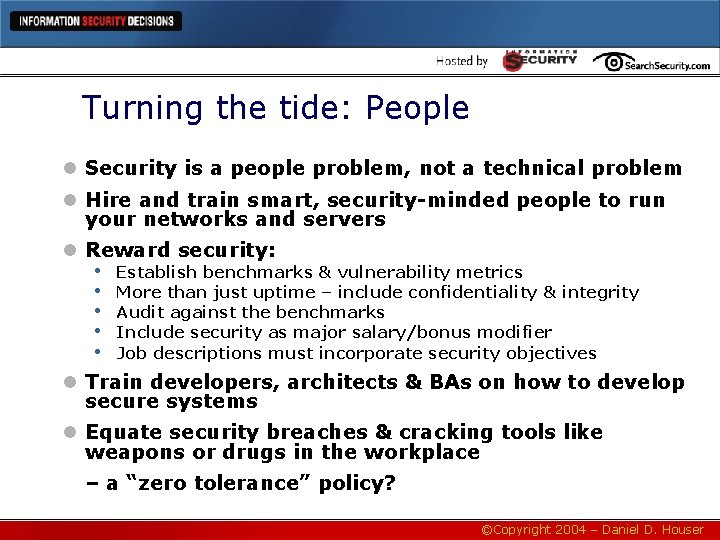
Turning the tide: People l Security is a people problem, not a technical problem l Hire and train smart, security-minded people to run your networks and servers l Reward security: • Establish benchmarks & vulnerability metrics • More than just uptime – include confidentiality & integrity • Audit against the benchmarks • Include security as major salary/bonus modifier • Job descriptions must incorporate security objectives l Train developers, architects & BAs on how to develop secure systems l Equate security breaches & cracking tools like weapons or drugs in the workplace – a “zero tolerance” policy? ©Copyright 2004 – Daniel D. Houser
Turning the tide: Process l Assess risk & vulnerability: BIA l Include security in feature sets & requirements l Segregation of Developers, Testers & Production, and particularly Prod Support from source code l Change management & access rights l Certification & Accreditation • Engage security team in charter & proposal phase • Bake security into the systems lifecycle • Require sponsor risk acceptance & authorization • Embed accreditation into change control l Include security in contract review and ROI l Configuration Management security patch lists ©Copyright 2004 – Daniel D. Houser
Summary l Use firewalls, but as one of many tools l Start network security with people, process and host security l Think outside the box when developing security architectures l Be prepared to dump your perimeter l Focus on malleable networking l Protect assets according to their value ©Copyright 2004 – Daniel D. Houser
Q&A Copyright Far. Works & Gary Larson ©Copyright 2004 – Daniel D. Houser
Contact information Dan Houser, CISSP, CISM, CCP dan. houser@gmail. com See Submarine Warfare article: http: //tinyurl. com/nwk 7 ©Copyright 2004 – Daniel D. Houser
- Slides: 37