Strong Password Authentication Protocols BY ROGER WONG What
Strong Password Authentication Protocols BY ROGER WONG
What is Authentication? Form of Identity Verification Showing the system that you are who you say you are Three general ways Something you know Something you have Something you are

Something you know Example: Passwords Pros: Easy to implement Most users understand it Cons: Fairly easy to crack if the password is simple enough Most people reuse passwords Some ways around this is to use One-Time Passwords

Something you have Example: Smart Cards Tamper-resistant, stores secret information Scan in card-reader. Like SMU ID Other examples are Tokens, ATM Cards, and i. Buttons All depends on the difficulty of forging
Something you are Mainly involves biometrics Extremely hard to break into Some cons are false negatives/positives, social acceptance, and key management
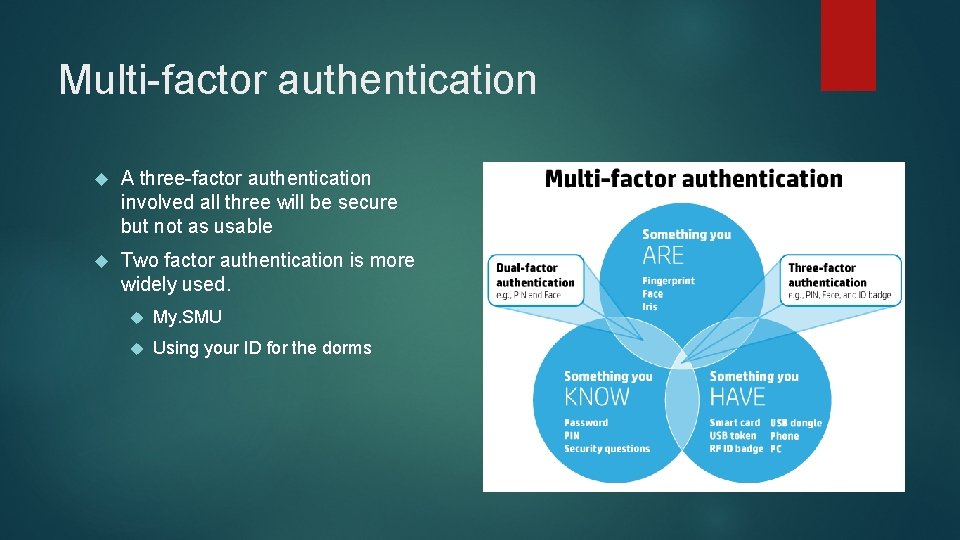
Multi-factor authentication A three-factor authentication involved all three will be secure but not as usable Two factor authentication is more widely used. My. SMU Using your ID for the dorms
Computer Authentication What about computer to computer authentication? Three types of computer authentication Client authentication – server verifying the client’s identity Server authentication – client verifying the server’s identity Mutual authentication – client and server verifying each other’s identity
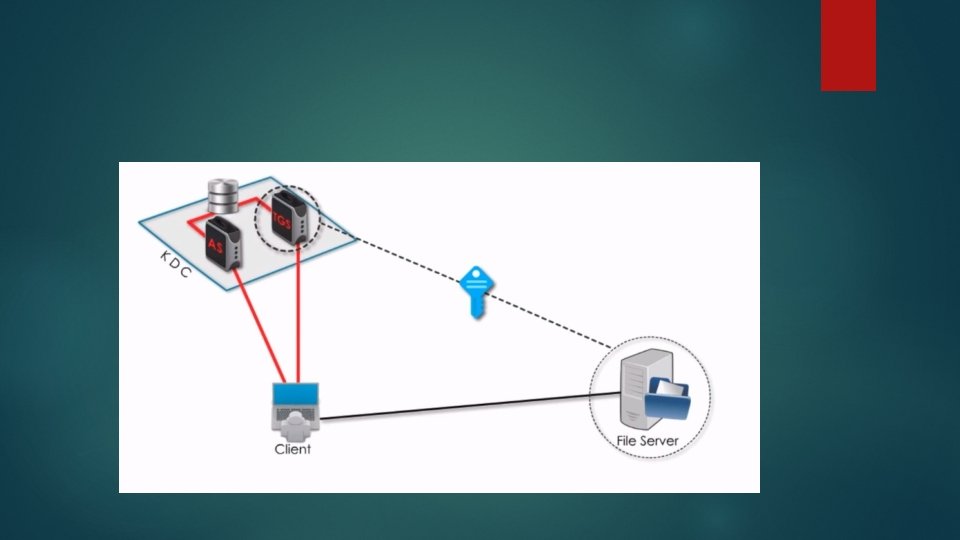
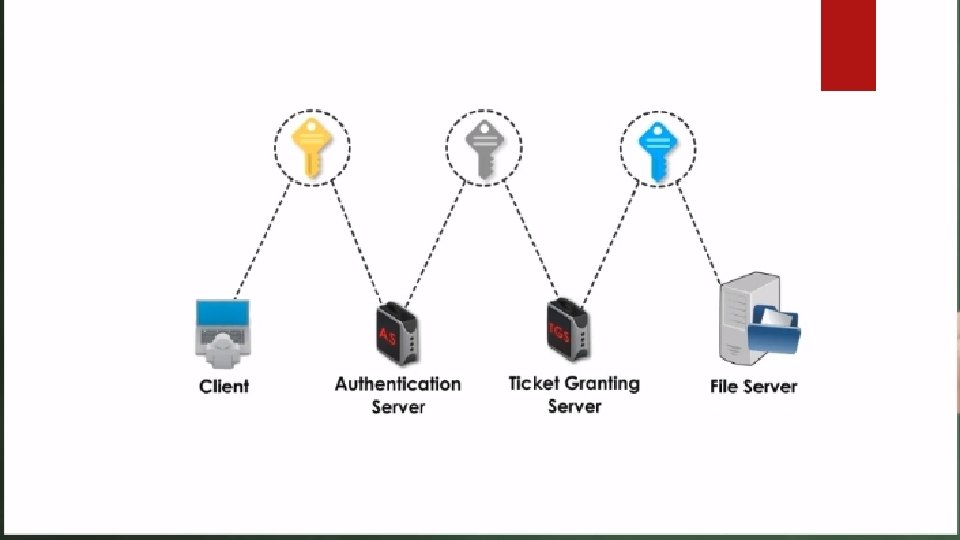
Some methods of mutual authentication Kerberos – a computer network authentication protocol Diffie-Hellman key exchange – one of the first public-key protocols
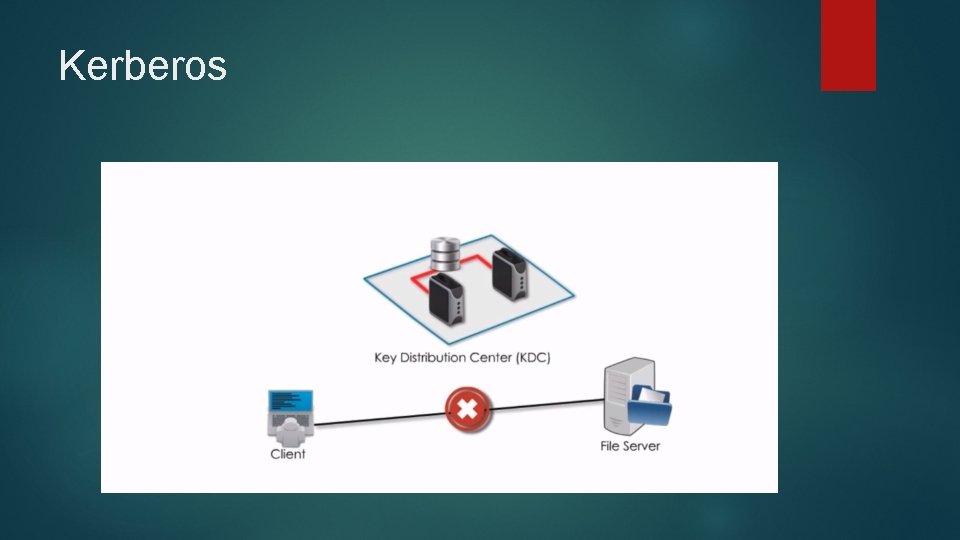
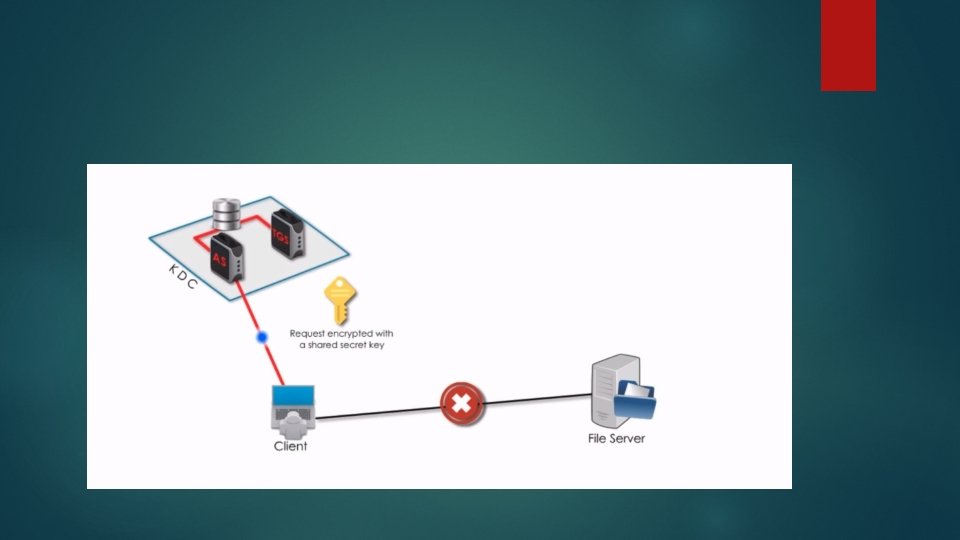
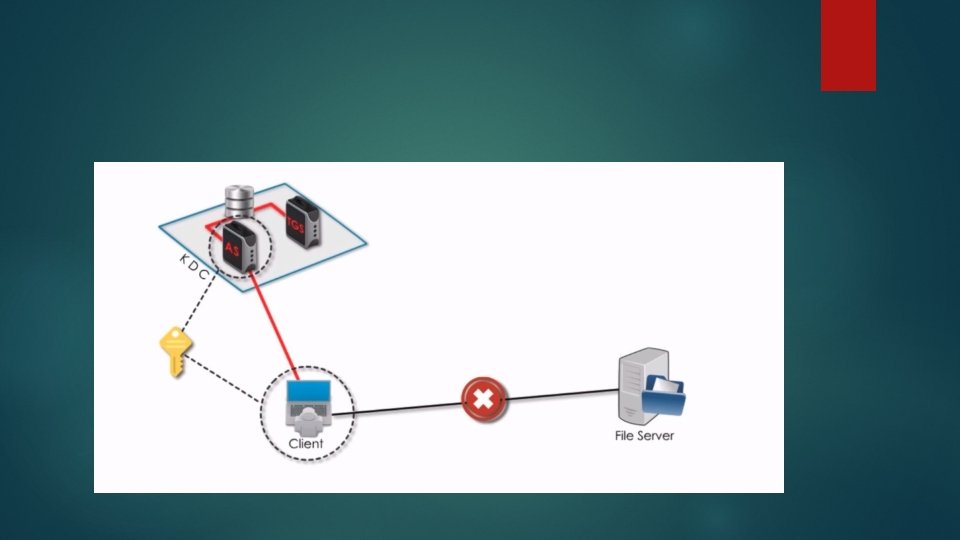
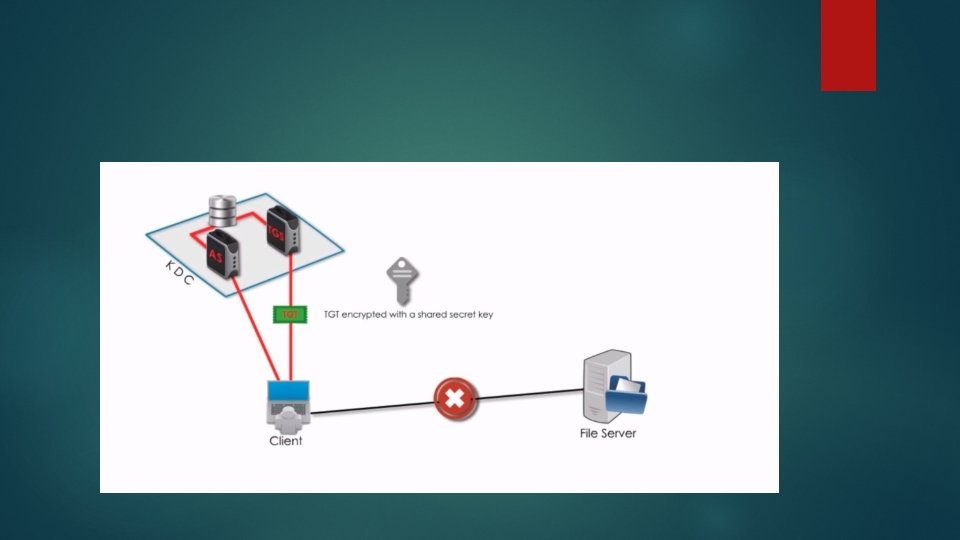
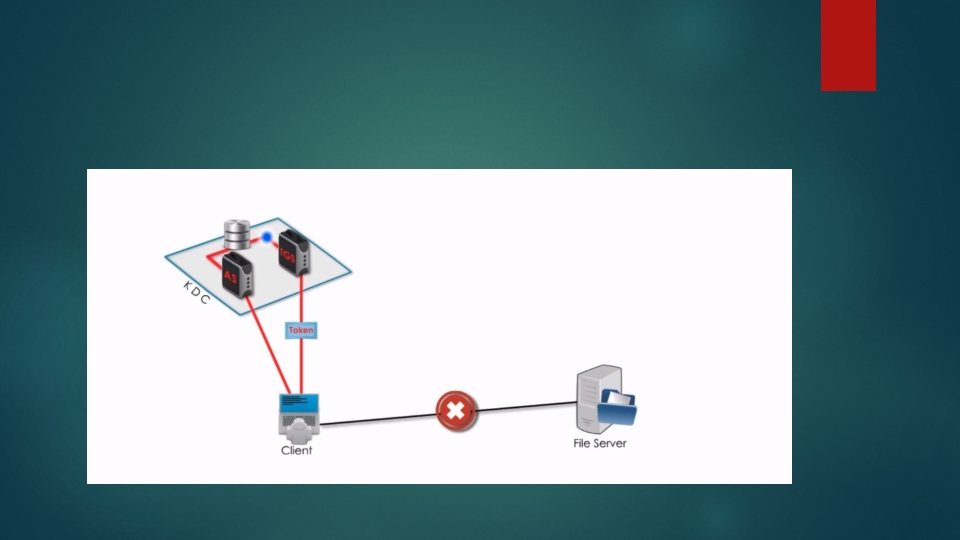
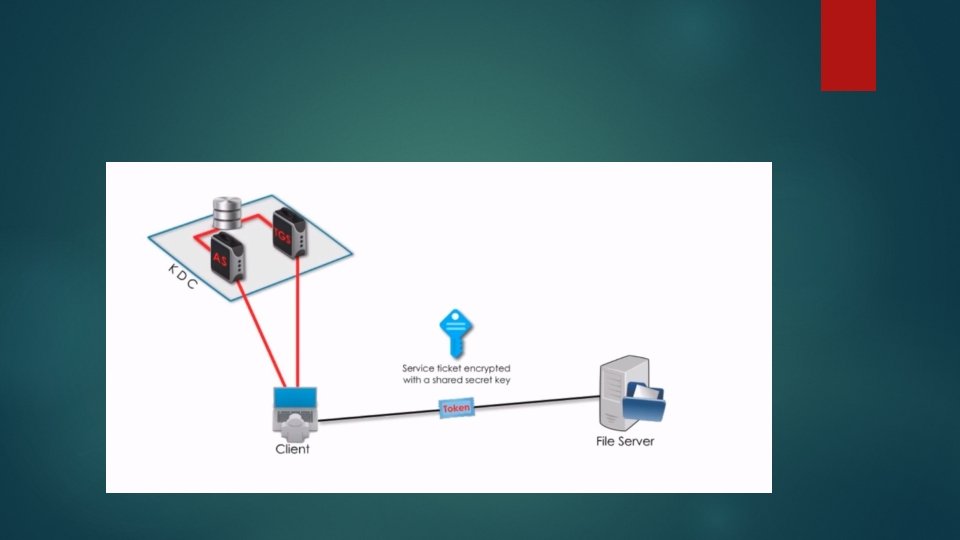
Kerberos

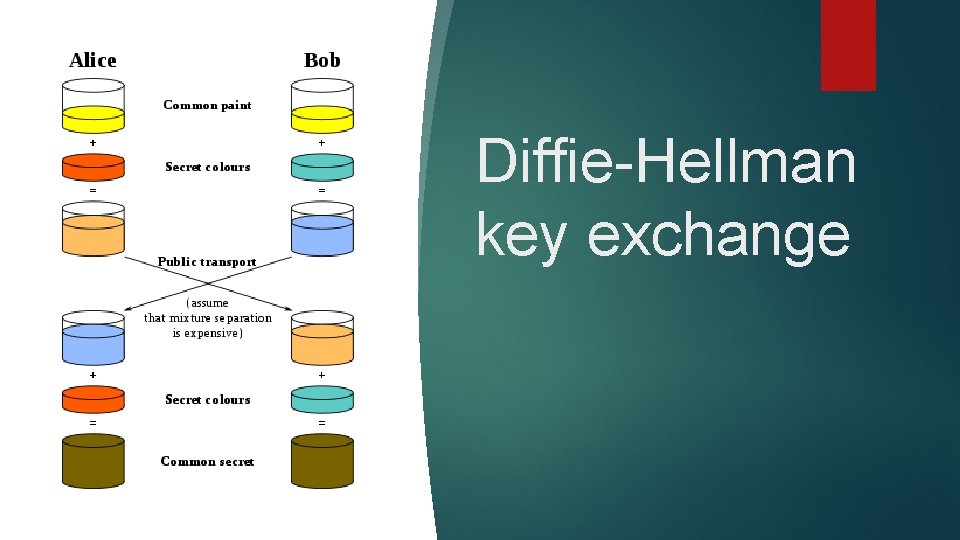
Diffie-Hellman key exchange
Conclusion These are just some of the strong password authentication protocols Person authenticating themselves Something you have Something you know Something you are Computer authenticating themselves Client authentication – server verifying the client’s identity Server authentication – client verifying the server’s identity Mutual authentication – client and server verifying each other’s identity
- Slides: 19