Storage Routing based Congestion control in Delay Tolerant
Storage Routing based Congestion control in Delay Tolerant Network (DTN) Presenter: Anika Aziz National Institute of Informatics (NII), The Graduate University for Advanced Studies, Tokyo, Japan
Objective In a Delay Tolerant Network (DTN), a custodian node which is storage constrained, can mitigate the congestion by reserving buffer space and applying queuing algorithm as a function of priority classes that is Class Of Services(COS). These COS can be mapped to a shared Priority Queuing (PQ) approach or to the separate PQs with different thresholds of the buffer.
Outline The DTN architecture, the Bundle protocol Custody transfer in DTN Congestion in DTN The Storage Routing (SR) Proposed algorithms Analysis & comparison of the algorithms Conclusion Q & A
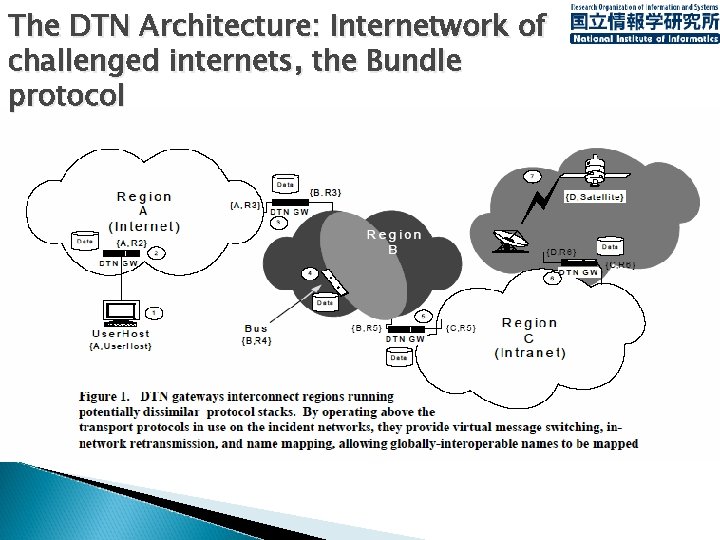
The DTN Architecture: Internetwork of challenged internets, the Bundle protocol
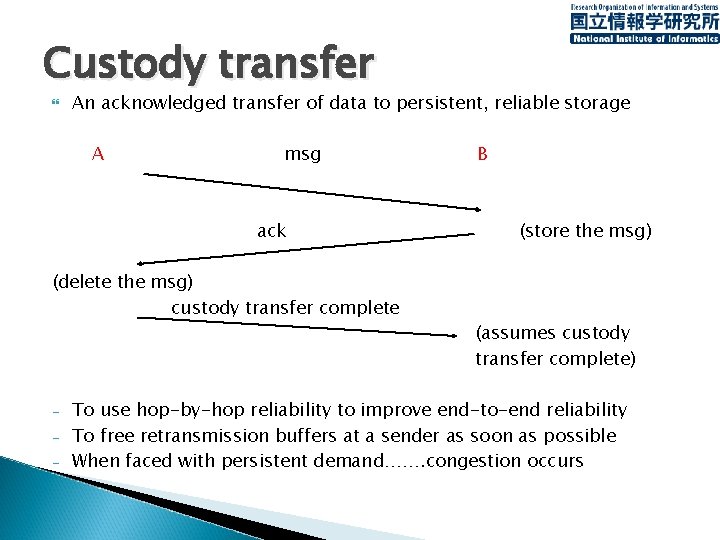
Custody transfer An acknowledged transfer of data to persistent, reliable storage A msg ack (delete the msg) custody transfer complete - B (store the msg) (assumes custody transfer complete) To use hop-by-hop reliability to improve end-to-end reliability To free retransmission buffers at a sender as soon as possible When faced with persistent demand……. congestion occurs
DTN congestion Rate based or window based congestion control techniques-nearly ineffective A region under the administrative control of a single entity can apply some form of admission control as a proactive means If its insufficient or unavailable, reactive means ( involving direct flow control) must be used Different solutions…cease accepting bundles with custody transfer & move bundles somewhere else
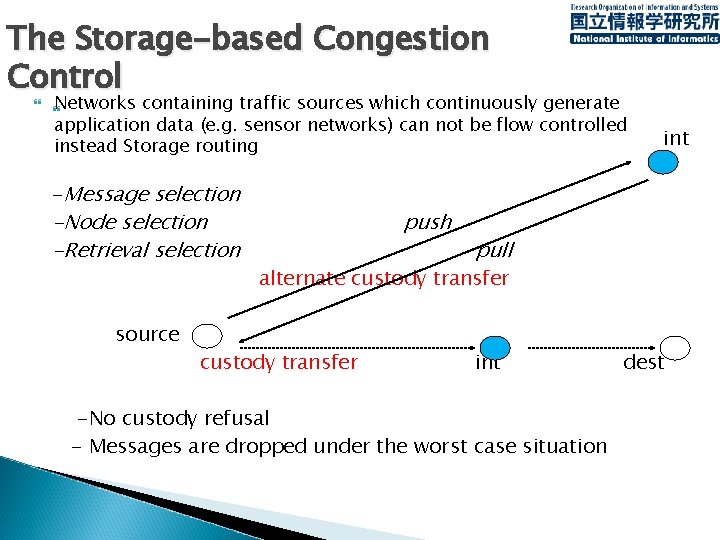
The Storage-based Congestion Control Networks containing traffic sources which continuously generate application data (e. g. sensor networks) can not be flow controlled instead Storage routing -Message selection -Node selection -Retrieval selection source push int pull alternate custody transfer int -No custody refusal - Messages are dropped under the worst case situation dest
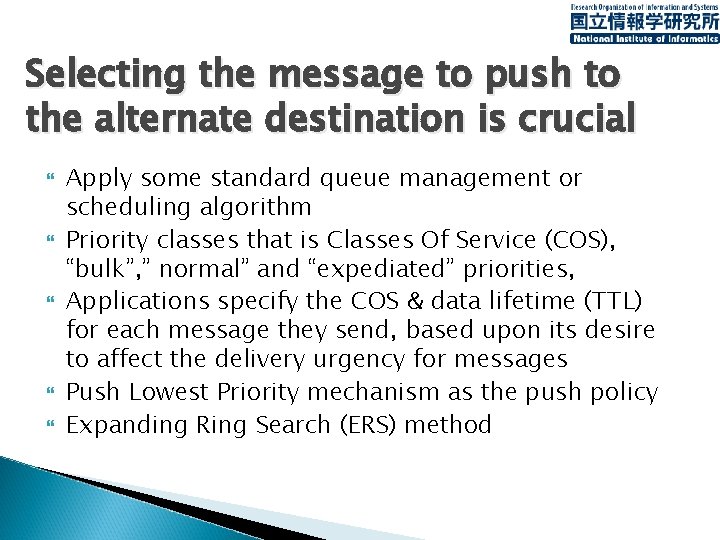
Selecting the message to push to the alternate destination is crucial Apply some standard queue management or scheduling algorithm Priority classes that is Classes Of Service (COS), “bulk”, ” normal” and “expediated” priorities, Applications specify the COS & data lifetime (TTL) for each message they send, based upon its desire to affect the delivery urgency for messages Push Lowest Priority mechanism as the push policy Expanding Ring Search (ERS) method
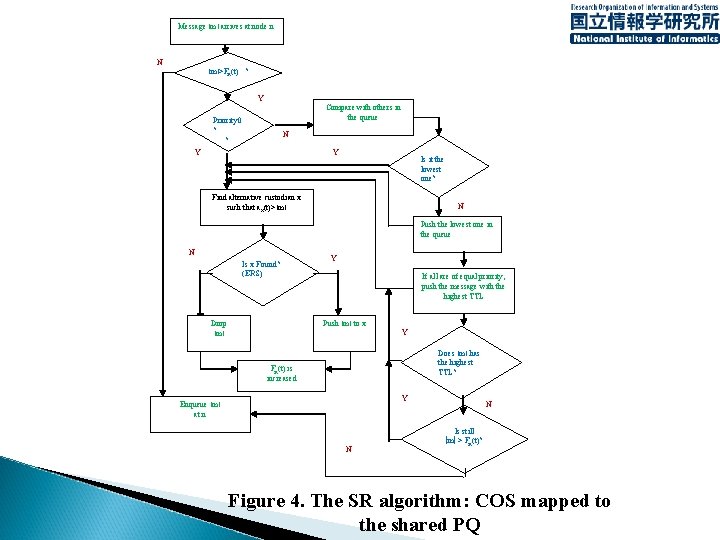
Message ׀ m ׀ arrives at node n N ׀ m >׀ Fn(t) ? Y Compare with others in the queue Priority 0 ? ? N Y Y Is it the lowest one? Find alternative custodian x such that ax(t)> ׀ m ׀ N Push the lowest one in the queue N Is x Found? (ERS) Drop ׀ m ׀ Y If all are of equal priority, push the message with the highest TTL Push ׀ m ׀ to x Y Does ׀ m ׀ has the highest TTL? Fn(t) is increased Y Enqueue ׀ m ׀ at n N N Is still |m| > Fn(t)? Figure 4. The SR algorithm: COS mapped to the shared PQ
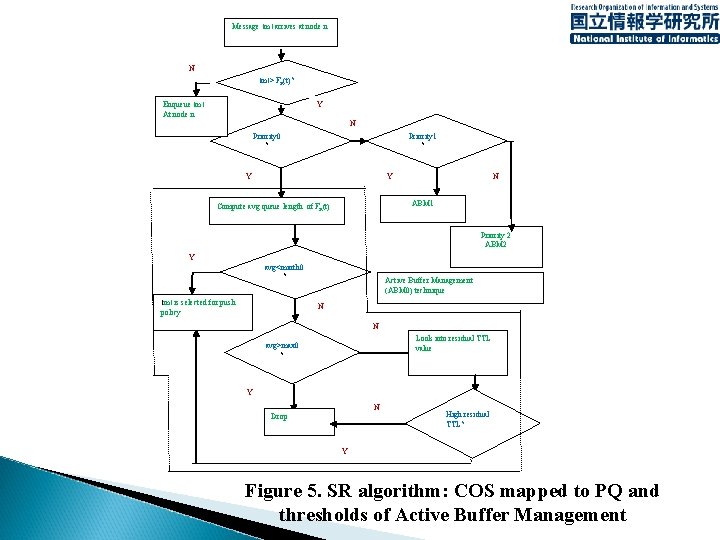
Message ׀ m ׀ arrives at node n N ׀ m >׀ Fn(t)? Enqueue ׀ m ׀ At node n Y N Priority 0 ? Priority 1 ? Y Y N ABM 1 Compute avg queue length of Fn(t) Priority 2 ABM 2 Y avg<minth 0 ? ׀ m ׀ is selected for push policy Active Buffer Management (ABM 0) technique N N Look into residual TTL value avg>max 0 ? Y N Drop High residual TTL? Y Figure 5. SR algorithm: COS mapped to PQ and thresholds of Active Buffer Management
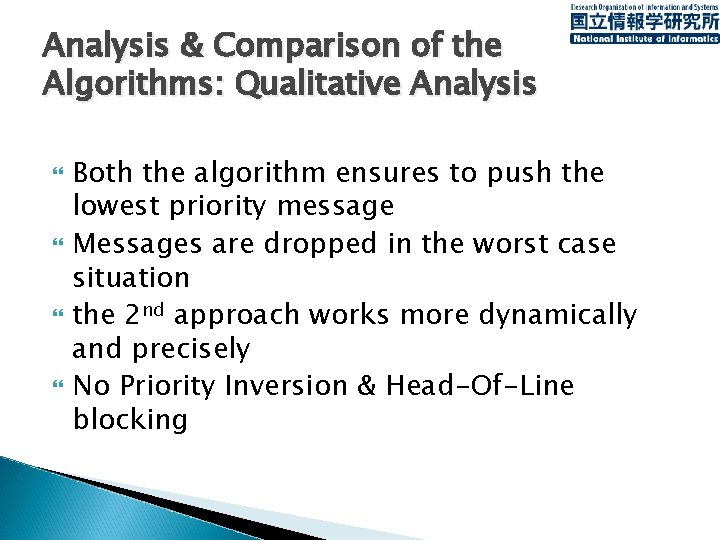
Analysis & Comparison of the Algorithms: Qualitative Analysis Both the algorithm ensures to push the lowest priority message Messages are dropped in the worst case situation the 2 nd approach works more dynamically and precisely No Priority Inversion & Head-Of-Line blocking
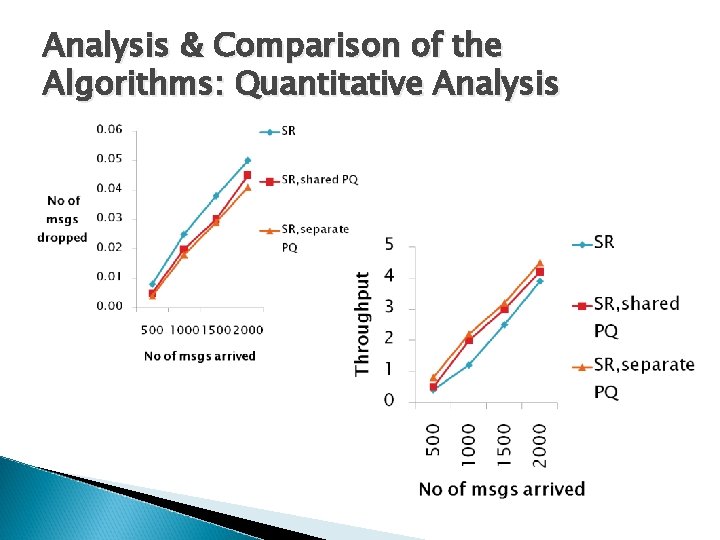
Analysis & Comparison of the Algorithms: Quantitative Analysis
Conclusion The value of Custody Transfer and DTN congestion remains to be fully understood… until the DTN architecture is widely deployed and carries significant traffic loads Similar story as TCP protocol specification included no management of congestion… more than 10 years after the 1 st experiments with Internet technology were performed.

Q&A?
- Slides: 14