Steve Lamb Wireless Security Let the Nightmare End
Steve Lamb Wireless Security – Let the Nightmare End! Technical Security Advisor http: //blogs. msdn. com/steve_ lamb stephlam@microsoft. com Alun Rogers Principal Consultant - Lynx alun. rogers@lynxtec. com
Agenda Public Key Infrastructure and Cryptography(PKI) What’s wrong with wireless out of the box? Protected Extensible Authentiction Protocol(PEAP) Extensible Authentiction Protocol - Transport Layer Security(EAP-TLS)
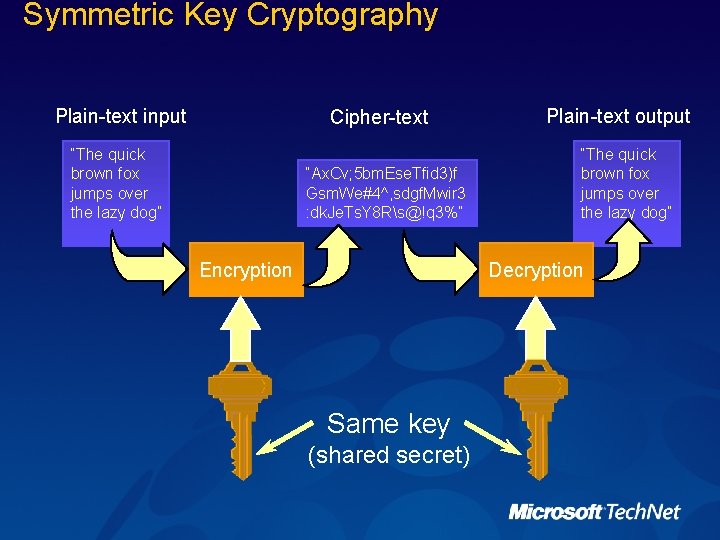
Symmetric Key Cryptography Plain-text input Cipher-text “The quick brown fox jumps over the lazy dog” “Ax. Cv; 5 bm. Ese. Tfid 3)f Gsm. We#4^, sdgf. Mwir 3 : dk. Je. Ts. Y 8 Rs@!q 3%” Encryption Plain-text output “The quick brown fox jumps over the lazy dog” Decryption Same key (shared secret)
Symmetric Pros and Cons Strength: Simple and really very fast (order of 1000 to 10000 faster than asymmetric mechanisms) Super-fast (and somewhat more secure) if done in hardware (DES, Rijndael) Weakness: Must agree the key beforehand Securely pass the key to the other party
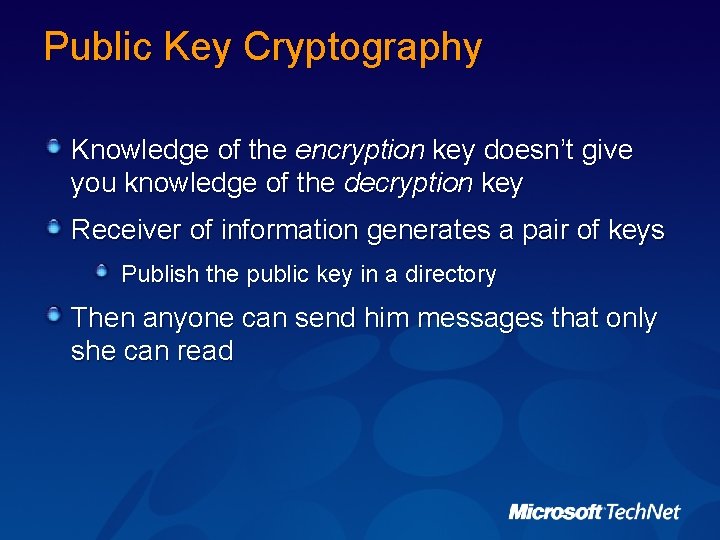
Public Key Cryptography Knowledge of the encryption key doesn’t give you knowledge of the decryption key Receiver of information generates a pair of keys Publish the public key in a directory Then anyone can send him messages that only she can read
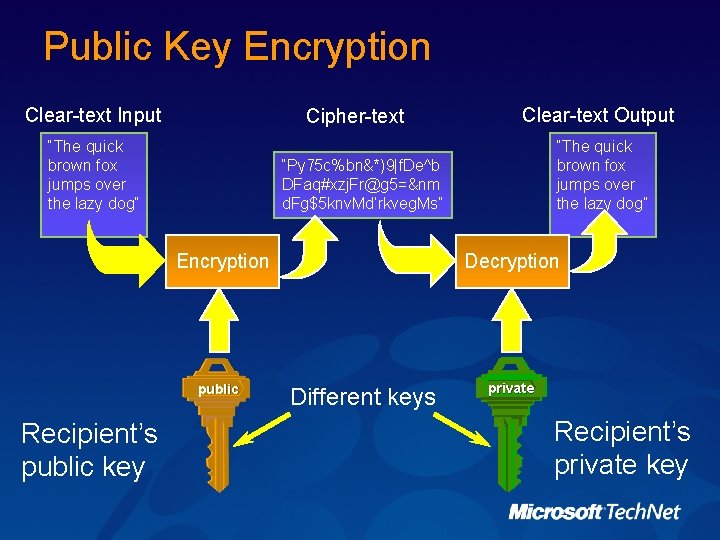
Public Key Encryption Clear-text Input Cipher-text “The quick brown fox jumps over the lazy dog” “Py 75 c%bn&*)9|f. De^b DFaq#xzj. Fr@g 5=&nm d. Fg$5 knv. Md’rkveg. Ms” Encryption public Recipient’s public key Clear-text Output Decryption Different keys private Recipient’s private key
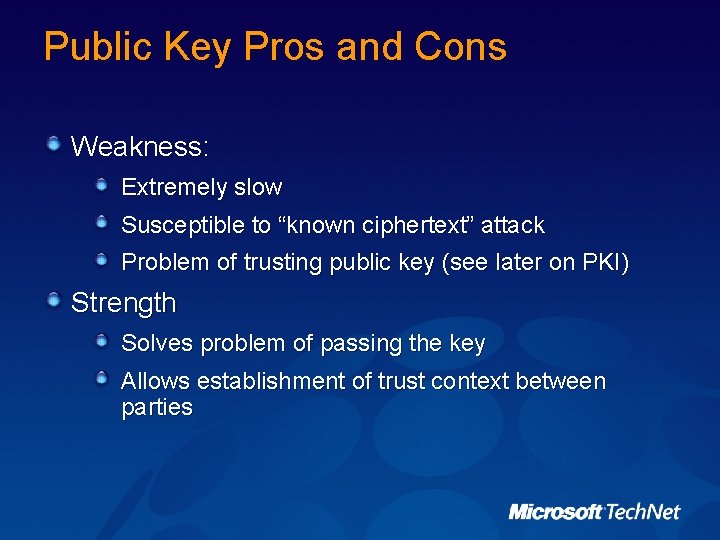
Public Key Pros and Cons Weakness: Extremely slow Susceptible to “known ciphertext” attack Problem of trusting public key (see later on PKI) Strength Solves problem of passing the key Allows establishment of trust context between parties
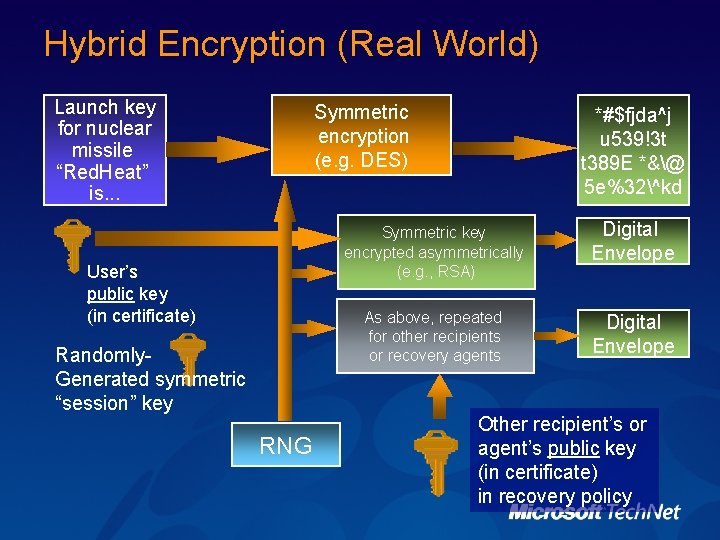
Hybrid Encryption (Real World) Launch key for nuclear missile “Red. Heat” is. . . Symmetric encryption (e. g. DES) User’s public key (in certificate) Randomly. Generated symmetric “session” key RNG *#$fjda^j u 539!3 t t 389 E *&@ 5 e%32^kd Symmetric key encrypted asymmetrically (e. g. , RSA) Digital Envelope As above, repeated for other recipients or recovery agents Digital Envelope Other recipient’s or agent’s public key (in certificate) in recovery policy
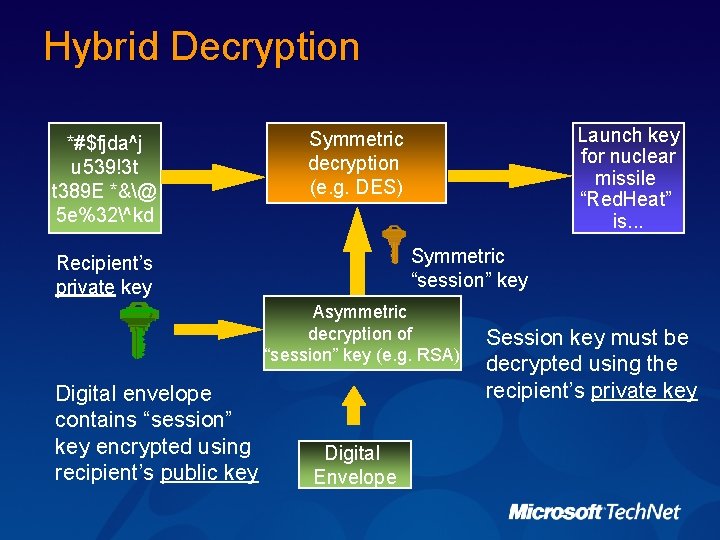
Hybrid Decryption *#$fjda^j u 539!3 t t 389 E *&@ 5 e%32^kd Launch key for nuclear missile “Red. Heat” is. . . Symmetric decryption (e. g. DES) Symmetric “session” key Recipient’s private key Asymmetric decryption of “session” key (e. g. RSA) Digital envelope contains “session” key encrypted using recipient’s public key Digital Envelope Session key must be decrypted using the recipient’s private key
PKI References "Best Practices for Implementing a Microsoft Windows Server 2003 Public Key Infrastructure" on http: //www. microsoft. com/pki
Agenda Public Key Infrastructure and Cryptography(PKI) What’s wrong with wireless out of the box? Protected Extensible Authentiction Protocol(PEAP) Extensible Authentiction Protocol - Transport Layer Security(EAP-TLS)
The challenge Huge fear of wireless Rooted in misunderstandings of security Wireless can be made secure Takes work Need to understand problem Need to plan for secure solution
Securing Wireless Need to control who and with what (authenticate) Need to control what they access (authorise) Ensure integrity of communications (Encrypt) Ensure safe transfer of credentials (Encrypt Authentication) Need to audit and report
WEP setup and RC 4 Secret key shared between access point and all clients Encrypts traffic before transmission Performs integrity check after transmission WEP uses RC 4, a stream cipher [key] XOR [plaintext] [ciphertext] XOR [key] [plaintext]
Common attacks Bit-flipping (encryption ≠ integrity) Flipping bit n in ciphertext flips same bit in plaintext Statistical attacks Multiple ciphertexts using same key permit determination of plaintext XOR Enables statistical attacks to recover plaintext More ciphertexts eases this Once one plaintext is known, recovering others is trivial
WEP’s “defenses” Integrity check (IC) field CRC-32 checksum, part of encrypted payload Not keyed Subject to bit-flipping can modify IC to make altered message appear valid Initialization vector (IV) added to key Alters key somewhat for each packet 24 -bit field; contained in plaintext portion Alas, this small keyspace guarantees reuse
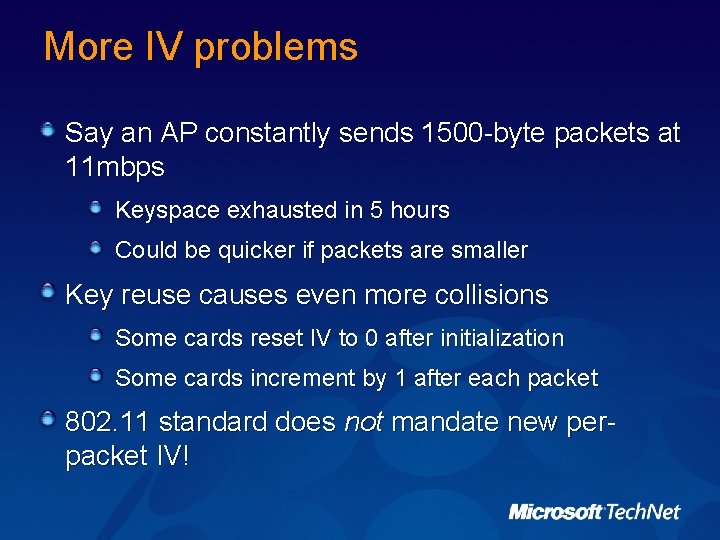
More IV problems Say an AP constantly sends 1500 -byte packets at 11 mbps Keyspace exhausted in 5 hours Could be quicker if packets are smaller Key reuse causes even more collisions Some cards reset IV to 0 after initialization Some cards increment by 1 after each packet 802. 11 standard does not mandate new perpacket IV!
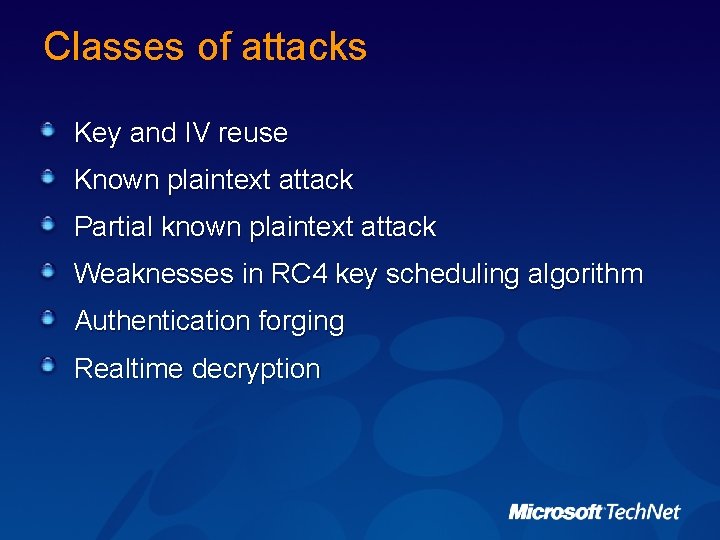
Classes of attacks Key and IV reuse Known plaintext attack Partial known plaintext attack Weaknesses in RC 4 key scheduling algorithm Authentication forging Realtime decryption
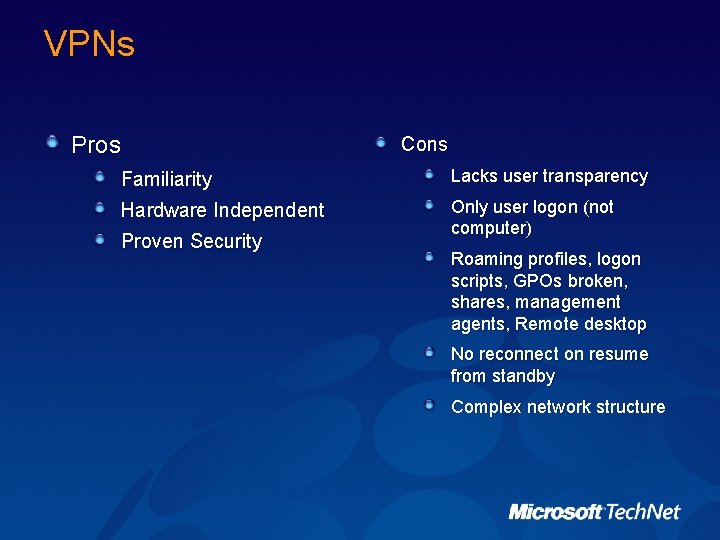
VPNs Pros Cons Familiarity Lacks user transparency Hardware Independent Only user logon (not computer) Proven Security Roaming profiles, logon scripts, GPOs broken, shares, management agents, Remote desktop No reconnect on resume from standby Complex network structure
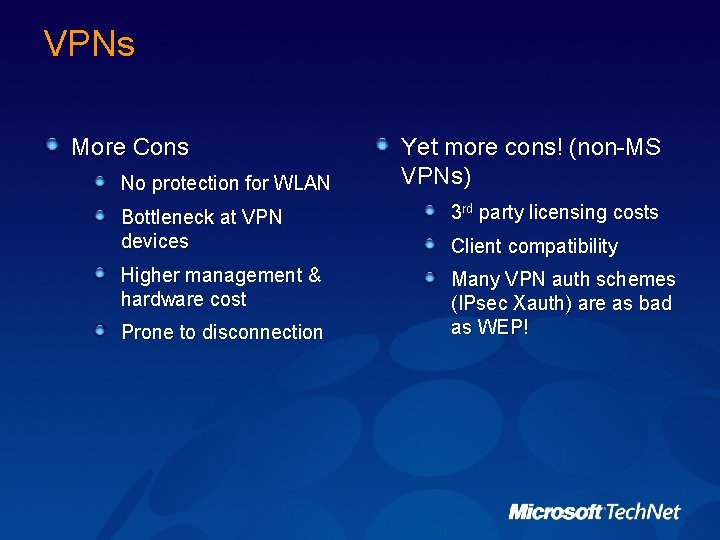
VPNs More Cons No protection for WLAN Yet more cons! (non-MS VPNs) Bottleneck at VPN devices 3 rd party licensing costs Higher management & hardware cost Many VPN auth schemes (IPsec Xauth) are as bad as WEP! Prone to disconnection Client compatibility
Agenda Public Key Infrastructure and Cryptography(PKI) What’s wrong with wireless out of the box? Protected Extensible Authentiction Protocol(PEAP) Extensible Authentiction Protocol - Transport Layer Security(EAP-TLS)
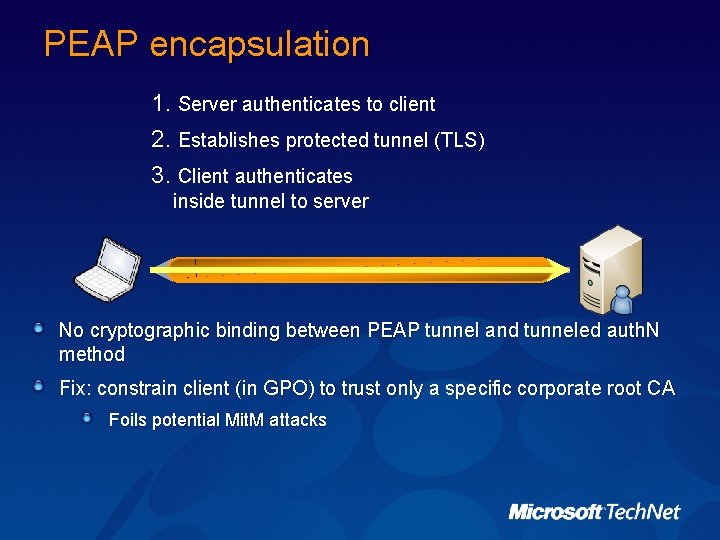
PEAP encapsulation 1. Server authenticates to client 2. Establishes protected tunnel (TLS) 3. Client authenticates inside tunnel to server No cryptographic binding between PEAP tunnel and tunneled auth. N method Fix: constrain client (in GPO) to trust only a specific corporate root CA Foils potential Mit. M attacks
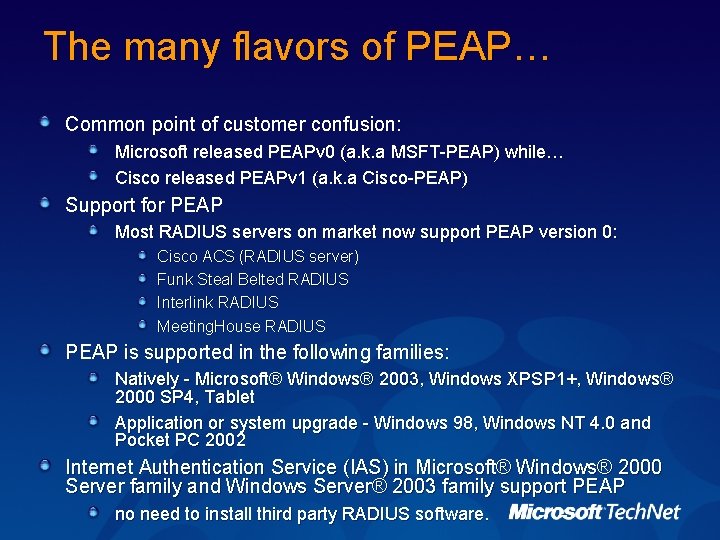
The many flavors of PEAP… Common point of customer confusion: Microsoft released PEAPv 0 (a. k. a MSFT-PEAP) while… Cisco released PEAPv 1 (a. k. a Cisco-PEAP) Support for PEAP Most RADIUS servers on market now support PEAP version 0: Cisco ACS (RADIUS server) Funk Steal Belted RADIUS Interlink RADIUS Meeting. House RADIUS PEAP is supported in the following families: Natively - Microsoft® Windows® 2003, Windows XPSP 1+, Windows® 2000 SP 4, Tablet Application or system upgrade - Windows 98, Windows NT 4. 0 and Pocket PC 2002 Internet Authentication Service (IAS) in Microsoft® Windows® 2000 Server family and Windows Server® 2003 family support PEAP no need to install third party RADIUS software.
Agenda Public Key Infrastructure and Cryptography(PKI) What’s wrong with wireless out of the box? Protected Extensible Authentiction Protocol(PEAP) Extensible Authentiction Protocol - Transport Layer Security(EAP-TLS)
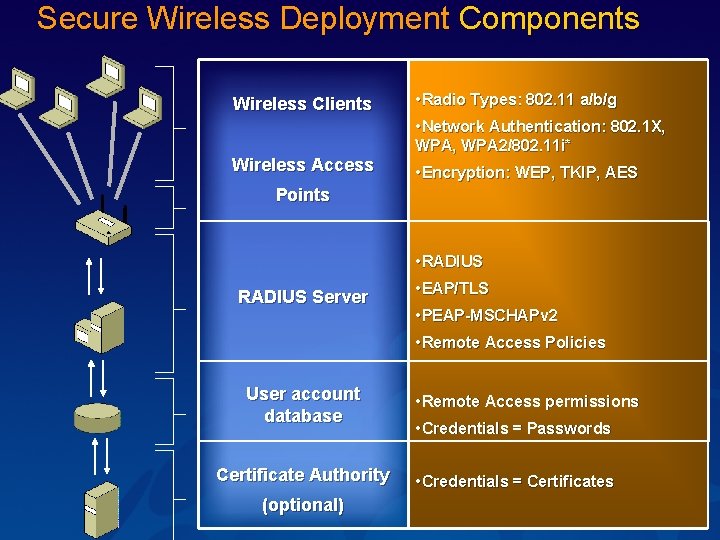
Secure Wireless Deployment Components Wireless Clients Wireless Access • Radio Types: 802. 11 a/b/g • Network Authentication: 802. 1 X, WPA 2/802. 11 i* • Encryption: WEP, TKIP, AES Points RADIUS Server User account database Certificate Authority (optional) • RADIUS • EAP/TLS • PEAP-MSCHAPv 2 • Remote Access Policies • Remote Access permissions • Credentials = Passwords • Credentials = Certificates
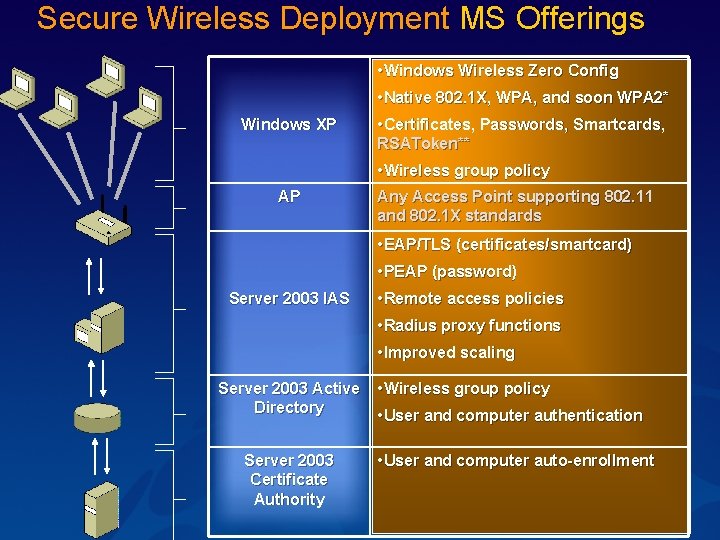
Secure Wireless Deployment MS Offerings Windows XP • Windows Wireless Zero Config • Native 802. 1 X, WPA, and soon WPA 2* • Certificates, Passwords, Smartcards, RSAToken** • Wireless group policy AP Server 2003 IAS Server 2003 Active Directory Server 2003 Certificate Authority Any Access Point supporting 802. 11 and 802. 1 X standards • EAP/TLS (certificates/smartcard) • PEAP (password) • Remote access policies • Radius proxy functions • Improved scaling • Wireless group policy • User and computer authentication • User and computer auto-enrollment
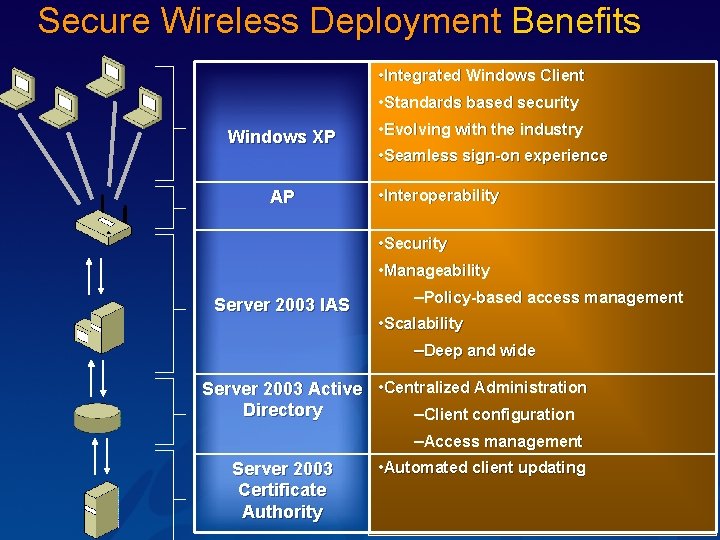
Secure Wireless Deployment Benefits Windows XP AP Server 2003 IAS • Integrated Windows Client • Standards based security • Evolving with the industry • Seamless sign-on experience • Interoperability • Security • Manageability –Policy-based access management • Scalability –Deep and wide Server 2003 Active • Centralized Administration Directory –Client configuration –Access management Server 2003 Certificate Authority • Automated client updating
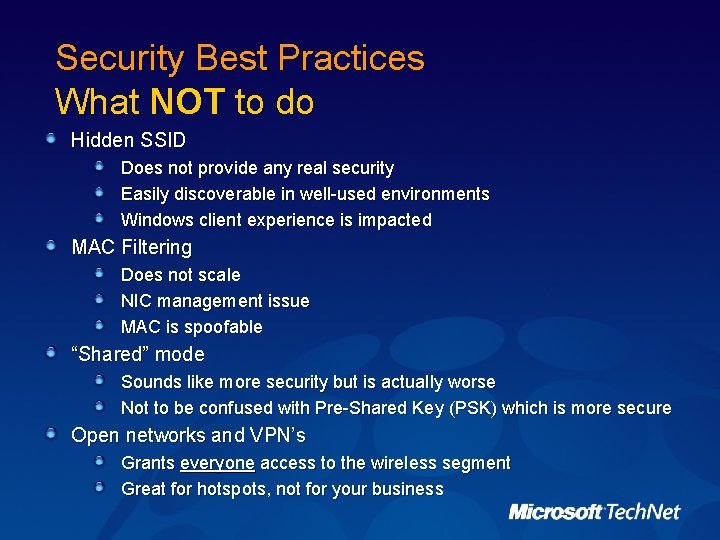
Security Best Practices What NOT to do Hidden SSID Does not provide any real security Easily discoverable in well-used environments Windows client experience is impacted MAC Filtering Does not scale NIC management issue MAC is spoofable “Shared” mode Sounds like more security but is actually worse Not to be confused with Pre-Shared Key (PSK) which is more secure Open networks and VPN’s Grants everyone access to the wireless segment Great for hotspots, not for your business
Security Best Practices What to do Chose a security authentication WPA with EAP-TLS and both user and computer certificates WPA with PEAP-MS-CHAP v 2 and enforce strong user passwords WEP with 802. 1 X authentication, EAP-TLS with both user and computer certificates, and periodic re-authentication WEP with 802. 1 X authentication, PEAP-MS-CHAP v 2, periodic reauthentication, enforce strong user passwords Preventing rogues User education and policy Ongoing Monitoring Don’t use Hidden SSIDs Do use Wireless Group Policy
Best Practices: Scalability Microsoft RADIUS – Internet Authentication Service (IAS) Install at least two IAS RADIUS servers For best performance, install IAS on domain controllers Use strong RADIUS shared secrets Use as many different RADIUS shared secrets as possible Use IAS RADIUS proxies to scale authentication traffic Use IAS RADIUS proxies for separate account databases
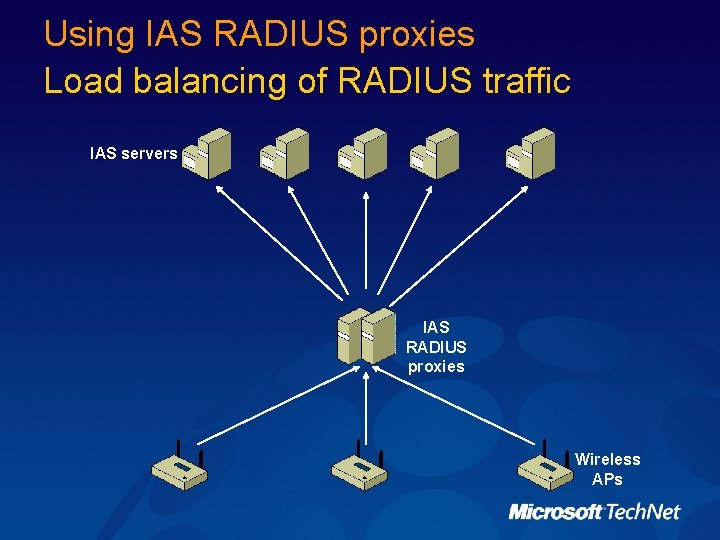
Using IAS RADIUS proxies Load balancing of RADIUS traffic IAS servers IAS RADIUS proxies Wireless APs
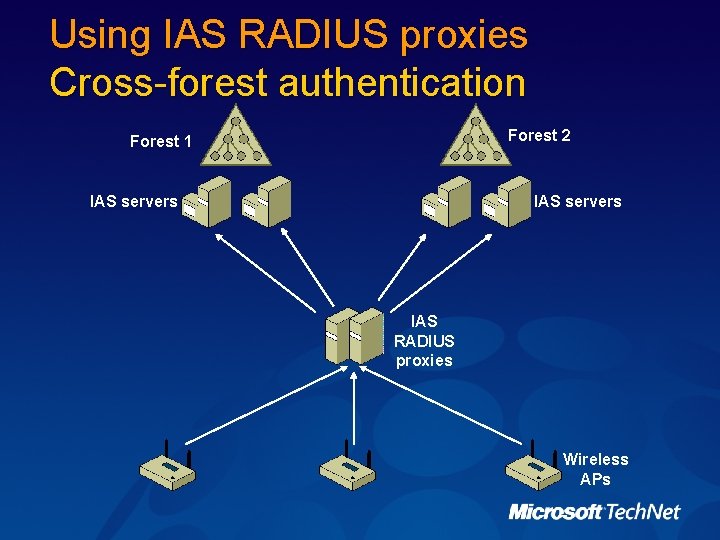
Using IAS RADIUS proxies Cross-forest authentication Forest 2 Forest 1 IAS servers IAS RADIUS proxies Wireless APs
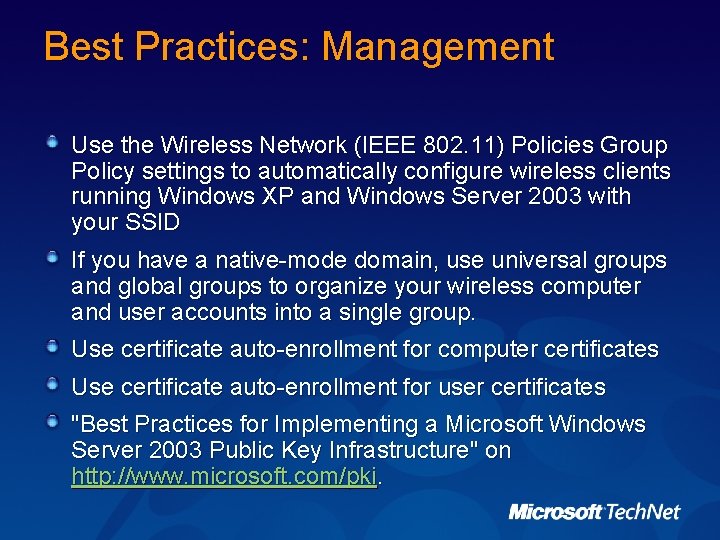
Best Practices: Management Use the Wireless Network (IEEE 802. 11) Policies Group Policy settings to automatically configure wireless clients running Windows XP and Windows Server 2003 with your SSID If you have a native-mode domain, use universal groups and global groups to organize your wireless computer and user accounts into a single group. Use certificate auto-enrollment for computer certificates Use certificate auto-enrollment for user certificates "Best Practices for Implementing a Microsoft Windows Server 2003 Public Key Infrastructure" on http: //www. microsoft. com/pki.
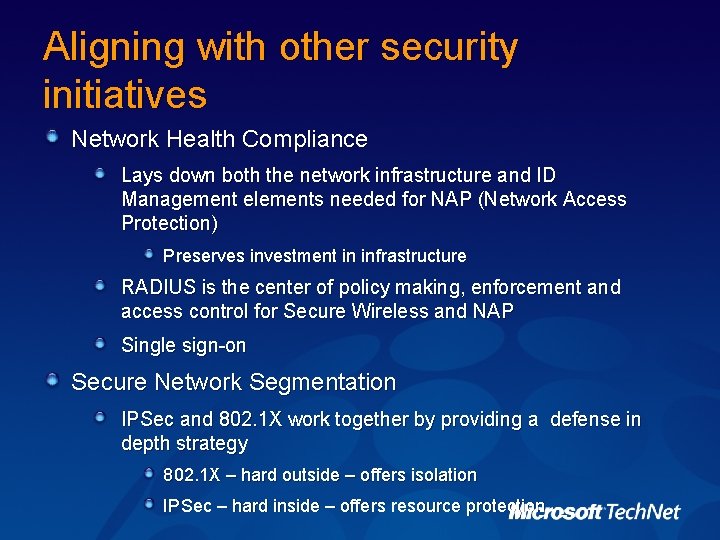
Aligning with other security initiatives Network Health Compliance Lays down both the network infrastructure and ID Management elements needed for NAP (Network Access Protection) Preserves investment in infrastructure RADIUS is the center of policy making, enforcement and access control for Secure Wireless and NAP Single sign-on Secure Network Segmentation IPSec and 802. 1 X work together by providing a defense in depth strategy 802. 1 X – hard outside – offers isolation IPSec – hard inside – offers resource protection

Best Practices as applied to Microsoft
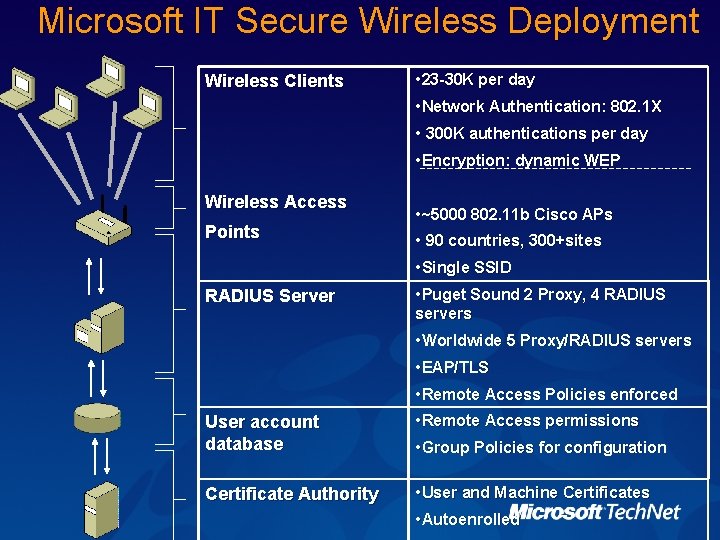
Microsoft IT Secure Wireless Deployment Wireless Clients Wireless Access • 23 -30 K per day • Network Authentication: 802. 1 X • 300 K authentications per day • Encryption: dynamic WEP RADIUS Server • ~5000 802. 11 b Cisco APs • 90 countries, 300+sites • Single SSID • Puget Sound 2 Proxy, 4 RADIUS User account database • Worldwide 5 Proxy/RADIUS servers • EAP/TLS • Remote Access Policies enforced • Remote Access permissions • Group Policies for configuration Points Certificate Authority servers • User and Machine Certificates • Autoenrolled
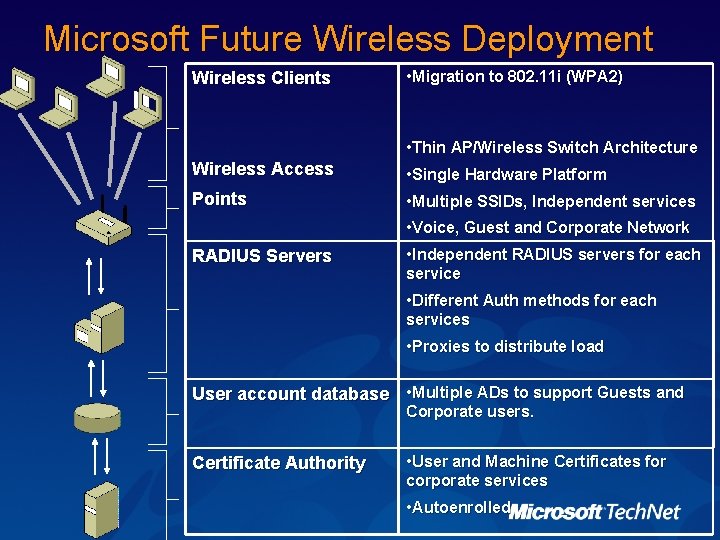
Microsoft Future Wireless Deployment Wireless Clients Wireless Access Points RADIUS Servers • Migration to 802. 11 i (WPA 2) • Thin AP/Wireless Switch Architecture • Single Hardware Platform • Multiple SSIDs, Independent services • Voice, Guest and Corporate Network • Independent RADIUS servers for each service • Different Auth methods for each services • Proxies to distribute load User account database • Multiple ADs to support Guests and Corporate users. Certificate Authority • User and Machine Certificates for corporate services • Autoenrolled
Tools WEPCrack—breaks 802. 11 keys http: //wepcrack. sourceforge. net/ Air. Snort—breaks 802. 11 keys Needs only 5 -10 million packets http: //airsnort. shmoo. com/ Net. Stumbler—access point reconnaissance http: //www. netstumbler. com
Resources The Advantages of Protected Extensible Authentication Protocol (PEAP) http: //www. microsoft. com/windowsserver 2003/techinfo/overvie w/peap. mspx Designing and Deploying Wireless LAN Connectivity for the Microsoft Corporate Network http: //www. microsoft. com/technet/prodtechnol/winxppro/deploy /wlandply. mspx "Best Practices for Implementing a Microsoft Windows Server 2003 Public Key Infrastructure" http: //www. microsoft. com/pki Best Practices article in Technet Magazine – Spring 2005 Discussion Alias = “wireless” *WPA 2 Beta = “wpa 2 beta”
© 2004 Microsoft Corporation. All rights reserved. This presentation is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS OR IMPLIED, IN THIS SUMMARY.
- Slides: 40